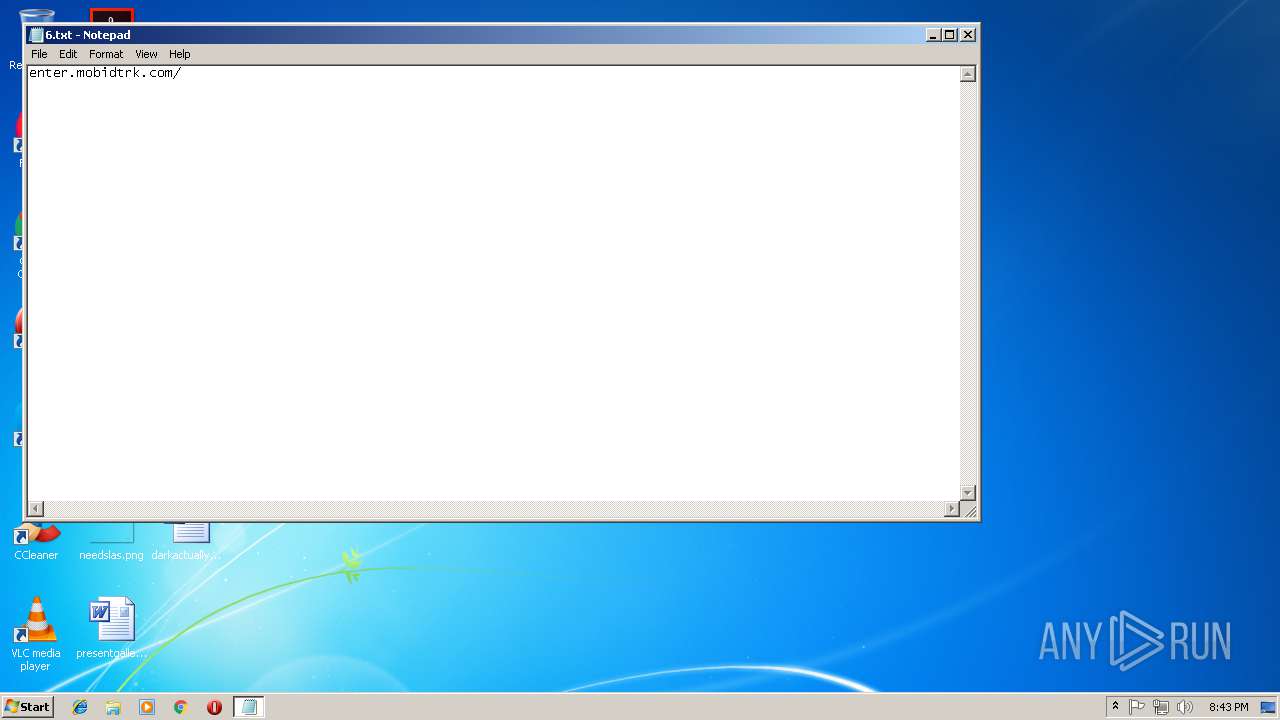
| File name: | 6.txt |
| Full analysis: | https://app.any.run/tasks/61b63448-978a-4195-aa8d-e1b4c8d0fc88 |
| Verdict: | Malicious activity |
| Analysis date: | November 15, 2018, 20:43:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with no line terminators |
| MD5: | A05CE868B42E7E37423E4B0A4D02576C |
| SHA1: | 73679B030D0F4A3602D96D592D2C7876B7DCF466 |
| SHA256: | 3EFCC542432F74F2CD93683B9EF7E59191466D2562CA272D8E59BC7557150B04 |
| SSDEEP: | 3:umbIcMBRe:uOEe |
MALICIOUS
Connects to CnC server
- chrome.exe (PID: 1764)
SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 1764)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
42
Monitored processes
12
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1736 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,12275559619331646079,6687606976431187092,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=9C6186E961D6A925A30B1D5D0E3B9FE4 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9C6186E961D6A925A30B1D5D0E3B9FE4 --renderer-client-id=6 --mojo-platform-channel-handle=3572 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=904,12275559619331646079,6687606976431187092,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=E9979B83DC3AAFB4C9C4783E73272916 --mojo-platform-channel-handle=608 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1840 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\6.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=904,12275559619331646079,6687606976431187092,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6D59711FBA7F729B857DC007FDD50EBF --mojo-platform-channel-handle=3884 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,12275559619331646079,6687606976431187092,131072 --enable-features=PasswordImport --service-pipe-token=DBE640066E1C52CCD781B6AB5DFB043D --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=DBE640066E1C52CCD781B6AB5DFB043D --renderer-client-id=5 --mojo-platform-channel-handle=1888 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=904,12275559619331646079,6687606976431187092,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=8D7385B450B2C56F96FBC979B24F0845 --mojo-platform-channel-handle=3956 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=904,12275559619331646079,6687606976431187092,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=DE63B1A921A449FE0DB1C5280E1F9B40 --mojo-platform-channel-handle=3908 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x701100b0,0x701100c0,0x701100cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
541
Read events
475
Write events
62
Delete events
4
Modification events
| (PID) Process: | (1764) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1764) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1764) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1764) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1764) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1764) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (1764) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1764-13186788229449375 |
Value: 259 | |||
| (PID) Process: | (1764) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1764) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (1764) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
0
Suspicious files
59
Text files
87
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1764 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\178e2293-9ba0-413c-8ec0-a0820c27fbfe.tmp | — | |
MD5:— | SHA256:— | |||
| 1764 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1764 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1764 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6a8d172e-a273-4b6b-b09d-1d01b6dca499.tmp | — | |
MD5:— | SHA256:— | |||
| 1764 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF5dd08a.TMP | text | |
MD5:— | SHA256:— | |||
| 1764 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF5dd05b.TMP | text | |
MD5:— | SHA256:— | |||
| 1764 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\CacheStorage\e6622492fa163609ddd4212f54512baa07929ed3\caecb3bd-7969-4305-84d6-3a376453ec73\index-dir\temp-index | — | |
MD5:— | SHA256:— | |||
| 1764 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF5dd09a.TMP | text | |
MD5:— | SHA256:— | |||
| 1764 | chrome.exe | C:\Users\admin\AppData\Roaming\Microsoft\SystemCertificates\My\Certificates\E02357FC7708441D4B0BE5F371F4B28961870F70 | binary | |
MD5:— | SHA256:— | |||
| 1764 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Thumbnails\LOG.old~RF5dd0b9.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
44
DNS requests
23
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
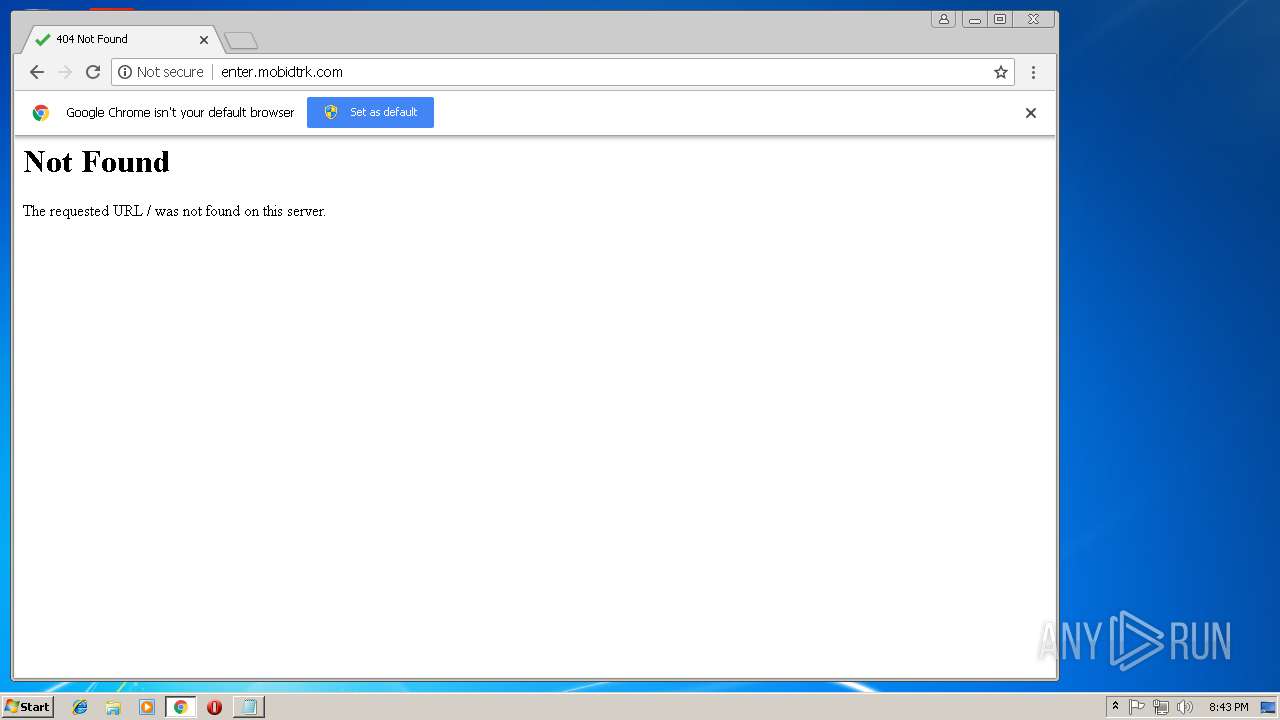
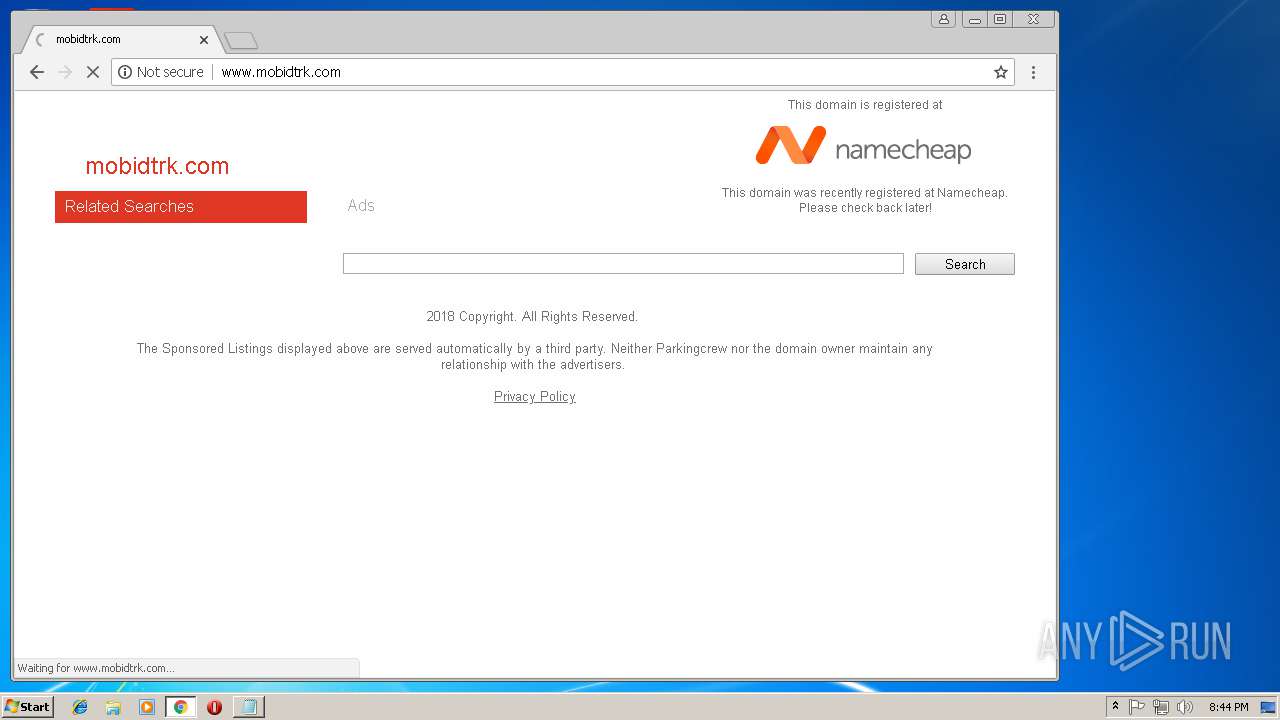
1764 | chrome.exe | GET | — | 198.54.117.212:80 | http://www.mobidtrk.com/favicon.ico | US | — | — | malicious |
1764 | chrome.exe | GET | — | 198.54.117.212:80 | http://www.mobidtrk.com/favicon.ico | US | — | — | malicious |
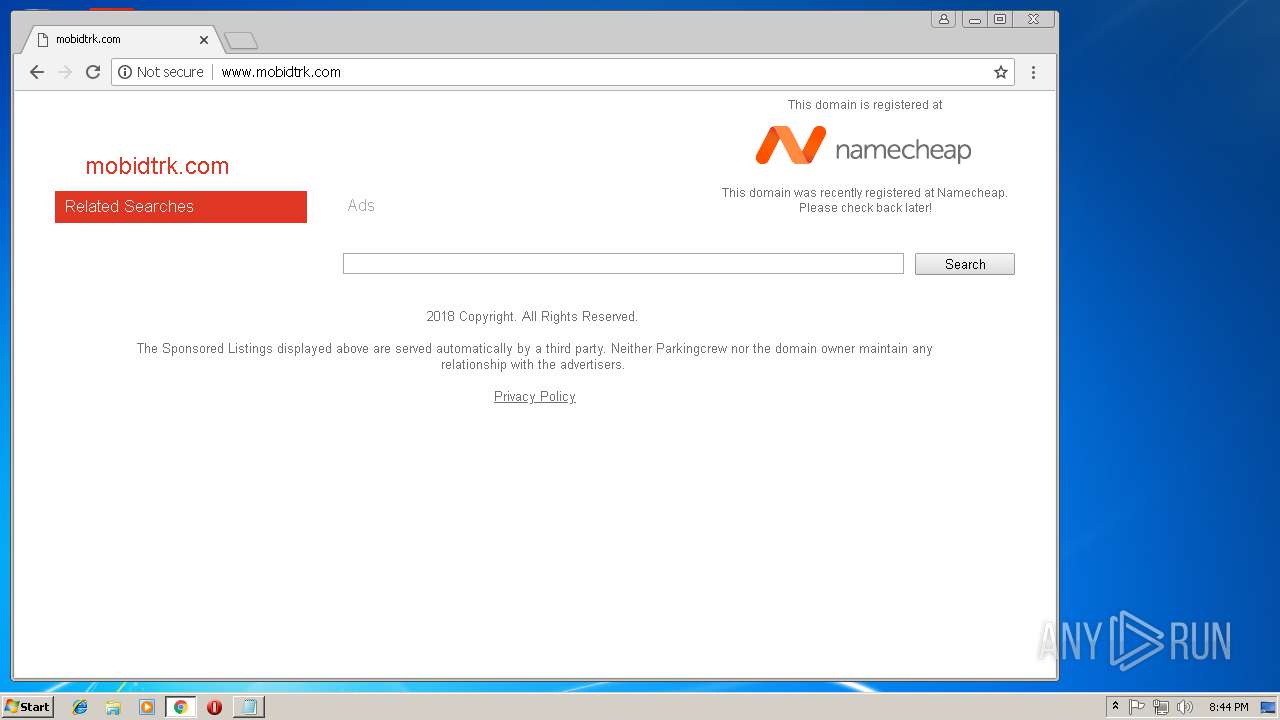
1764 | chrome.exe | GET | 200 | 198.54.117.212:80 | http://www.mobidtrk.com/ | US | html | 4.81 Kb | malicious |
1764 | chrome.exe | POST | 201 | 185.53.178.30:80 | http://js.parkingcrew.net/ls.php | DE | — | — | whitelisted |
1764 | chrome.exe | GET | 200 | 143.204.101.82:80 | http://i.cdnpark.com/themes/assets/style.css | US | text | 343 b | whitelisted |
1764 | chrome.exe | GET | 200 | 185.53.178.30:80 | http://js.parkingcrew.net/scripts/feedmeCaf.php?q=&ip=82.102.22.109&max=10&hl=no&d=mobidtrk.com&ron=0&adult=0 | DE | text | 285 b | whitelisted |
1764 | chrome.exe | GET | 200 | 185.53.178.30:80 | http://js.parkingcrew.net/assets/scripts/tier2caf.js | DE | text | 28.2 Kb | whitelisted |
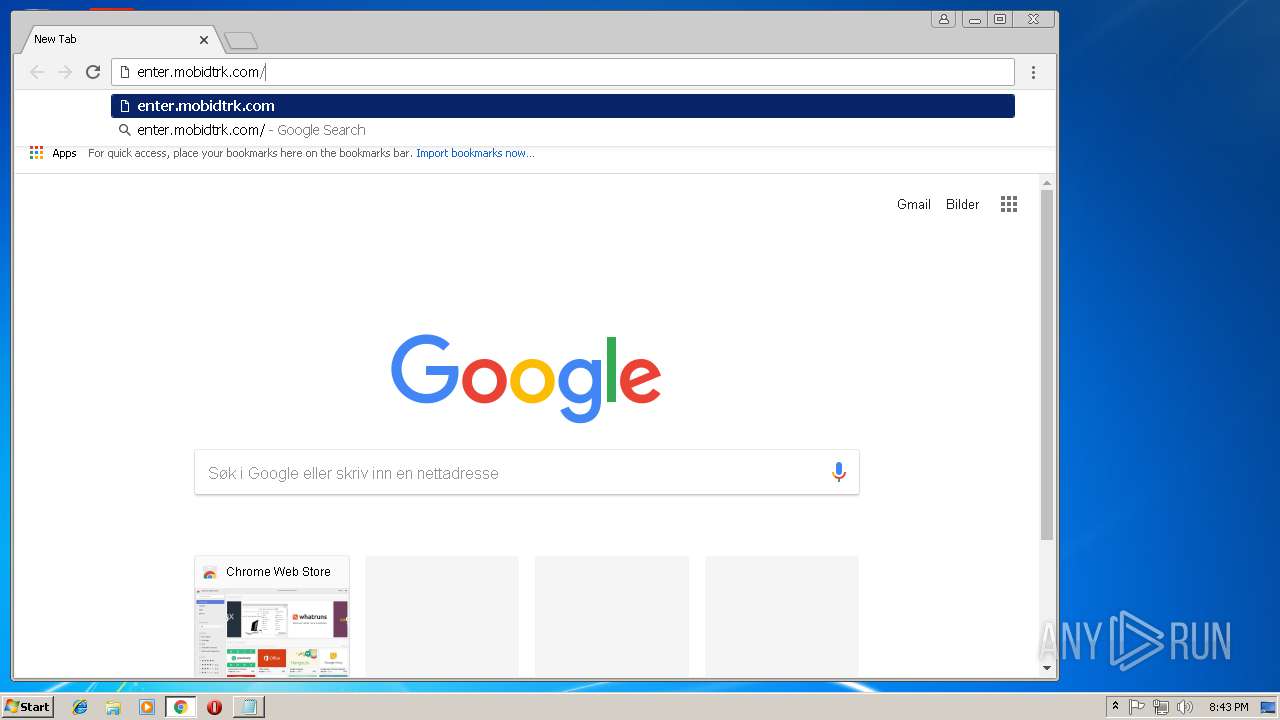
1764 | chrome.exe | GET | 200 | 184.154.47.14:80 | http://enter.mobidtrk.com/favicon.ico | US | image | 1.12 Kb | suspicious |
1764 | chrome.exe | GET | 304 | 143.204.101.82:80 | http://i.cdnpark.com/themes/registrar/images/logo_namecheap.png | US | compressed | 343 b | whitelisted |
1764 | chrome.exe | GET | 200 | 185.53.178.30:80 | http://js.parkingcrew.net/assets/scripts/jsparkcaf.js | DE | text | 5.51 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1764 | chrome.exe | 172.217.168.3:443 | www.google.de | Google Inc. | US | whitelisted |
1764 | chrome.exe | 216.58.215.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
1764 | chrome.exe | 216.58.215.238:443 | apis.google.com | Google Inc. | US | whitelisted |
1764 | chrome.exe | 184.154.47.14:80 | enter.mobidtrk.com | SingleHop, Inc. | US | suspicious |
1764 | chrome.exe | 192.64.119.52:80 | mobidtrk.com | Namecheap, Inc. | US | suspicious |
1764 | chrome.exe | 143.204.101.82:80 | i.cdnpark.com | — | US | suspicious |
1764 | chrome.exe | 185.53.179.29:80 | parkingcrew.net | Team Internet AG | DE | malicious |
1764 | chrome.exe | 104.16.99.56:80 | www.namecheap.com | Cloudflare Inc | US | shared |
1764 | chrome.exe | 2.16.186.32:80 | ocsp.usertrust.com | Akamai International B.V. | — | whitelisted |
1764 | chrome.exe | 185.53.178.30:80 | js.parkingcrew.net | Team Internet AG | DE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.de |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
enter.mobidtrk.com |
| suspicious |
www.google.com |
| malicious |
www.google.no |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1764 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Parkingcrew Monetize Tracker Checkin |