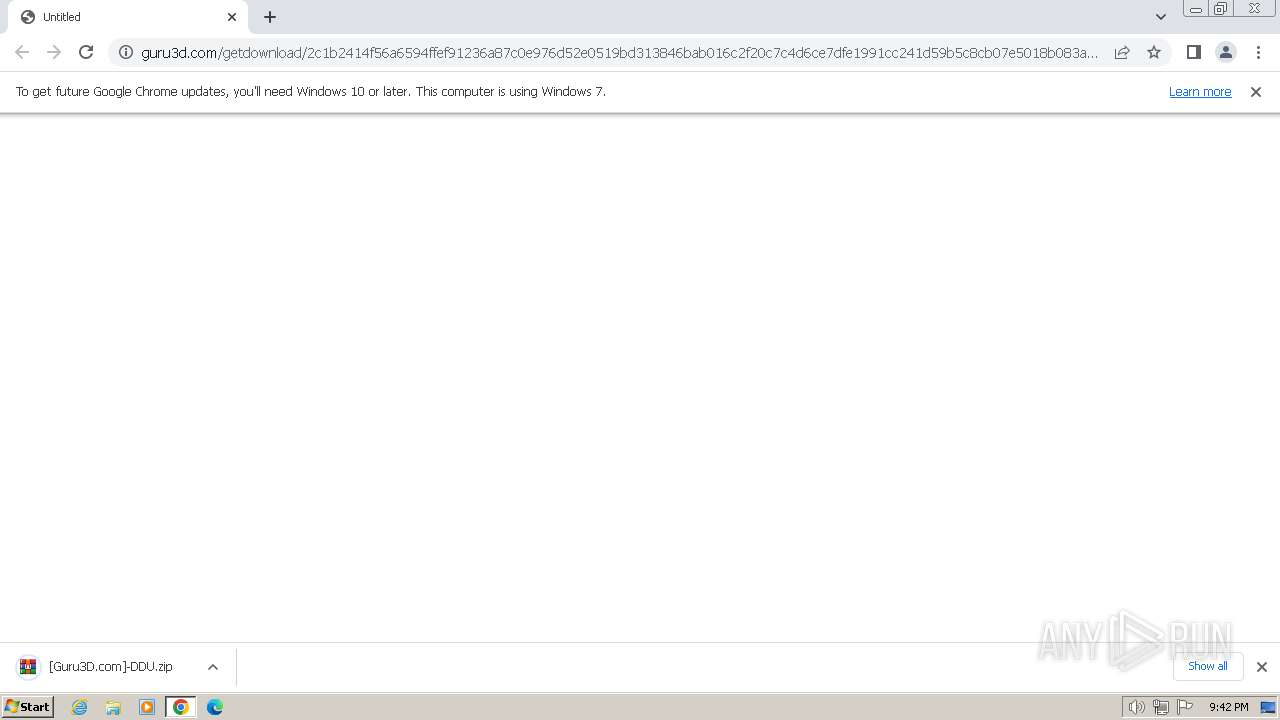
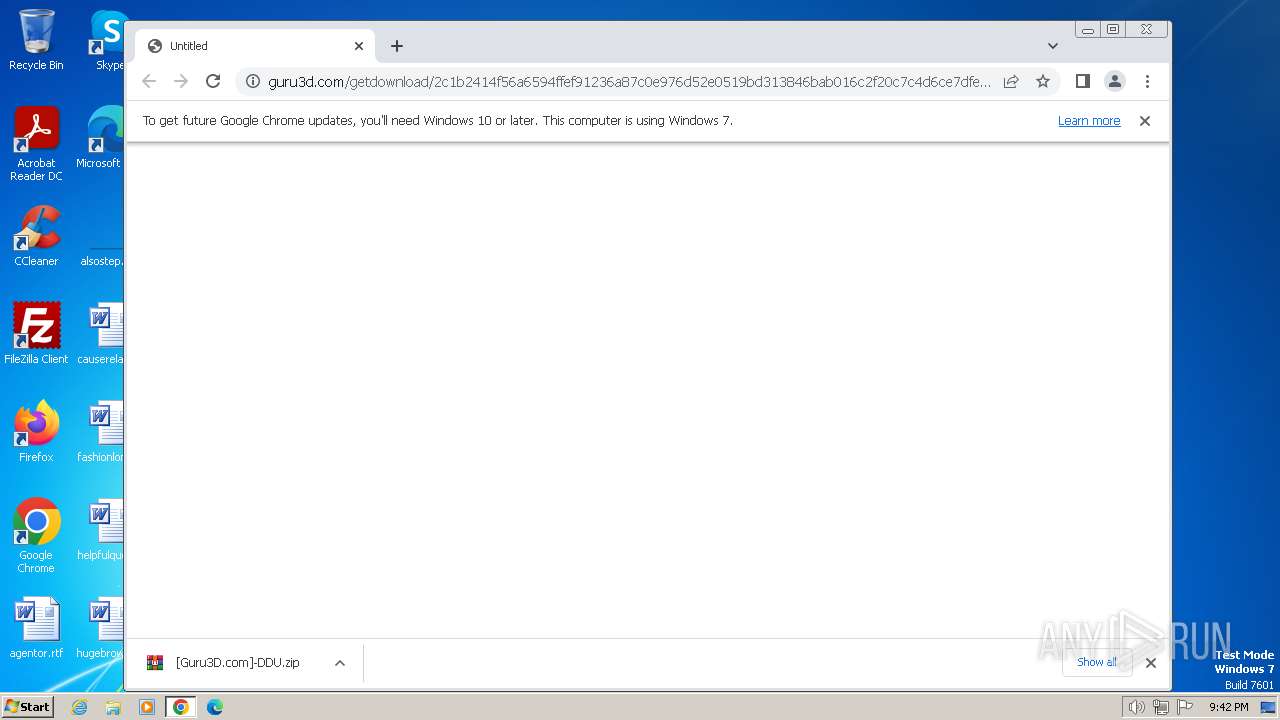
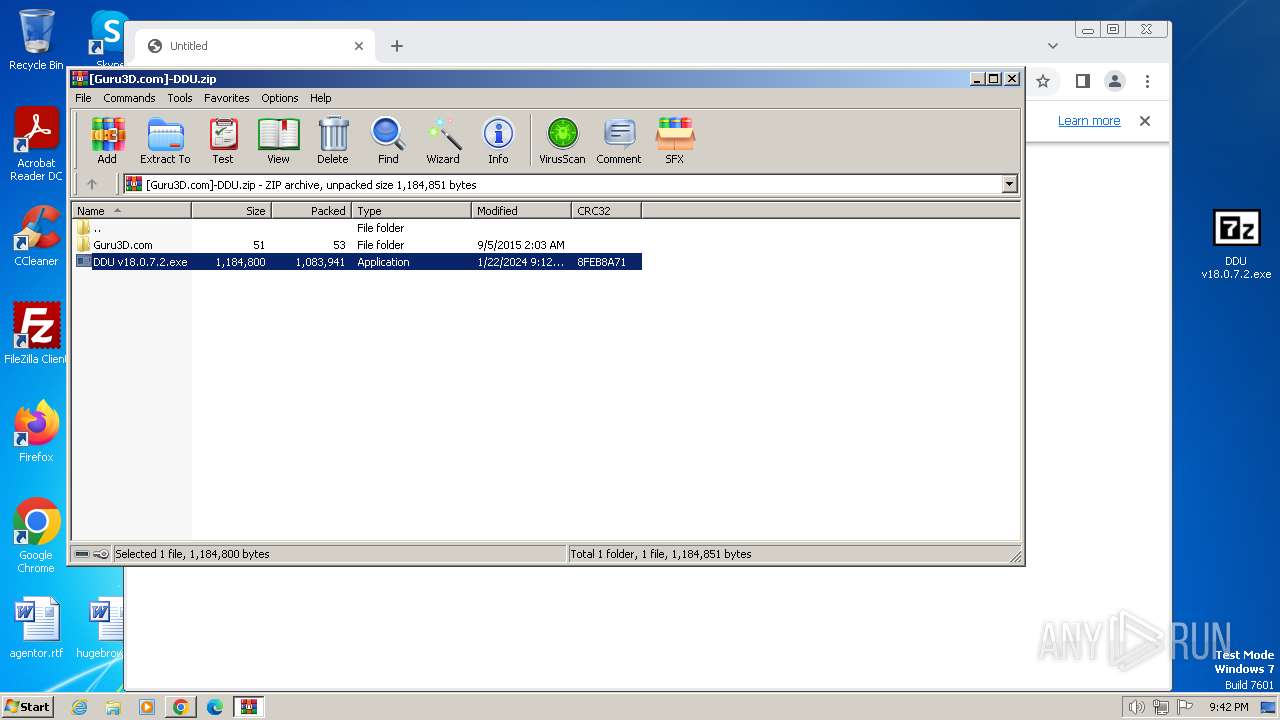
| URL: | https://www.guru3d.com/getdownload/2c1b2414f56a6594ffef91236a87c0e976d52e0519bd313846bab016c2f20c7c4d6ce7dfe1991cc241d59b5c8cb07e5018b083a5902ac6c67fbe3b852ca022b0f73541638028a2d270eb576309b5208d7642bced763e8806fd9c5a9bca00d71e03e3f895d9924372aebbd01f8d3b8f4f22025884306c24b2230caaa33278d26e6030e42d33f8ae57a577520f01ba2e5ff243d0a889a561ab49c3ea2dd6c91d6ccaf1dfc1e0b09be33209add14c096f4a22ab |
| Full analysis: | https://app.any.run/tasks/18759210-819e-4b01-bc12-d3d3376e1087 |
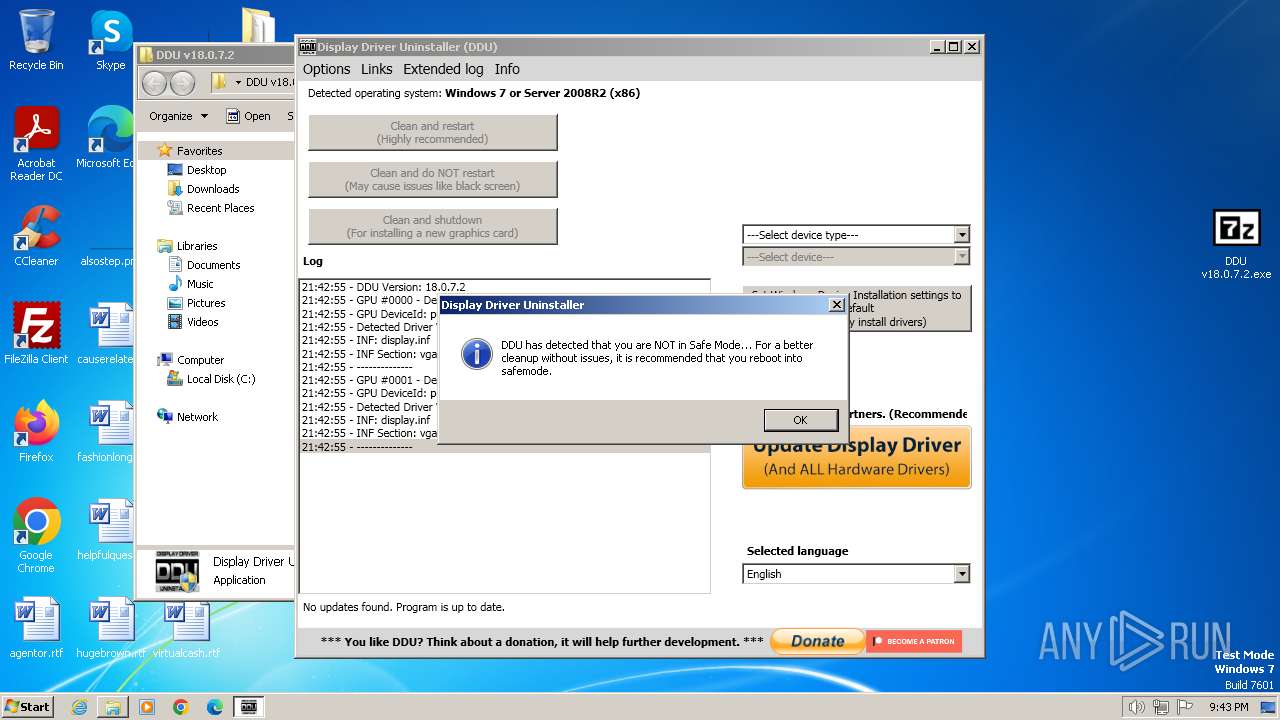
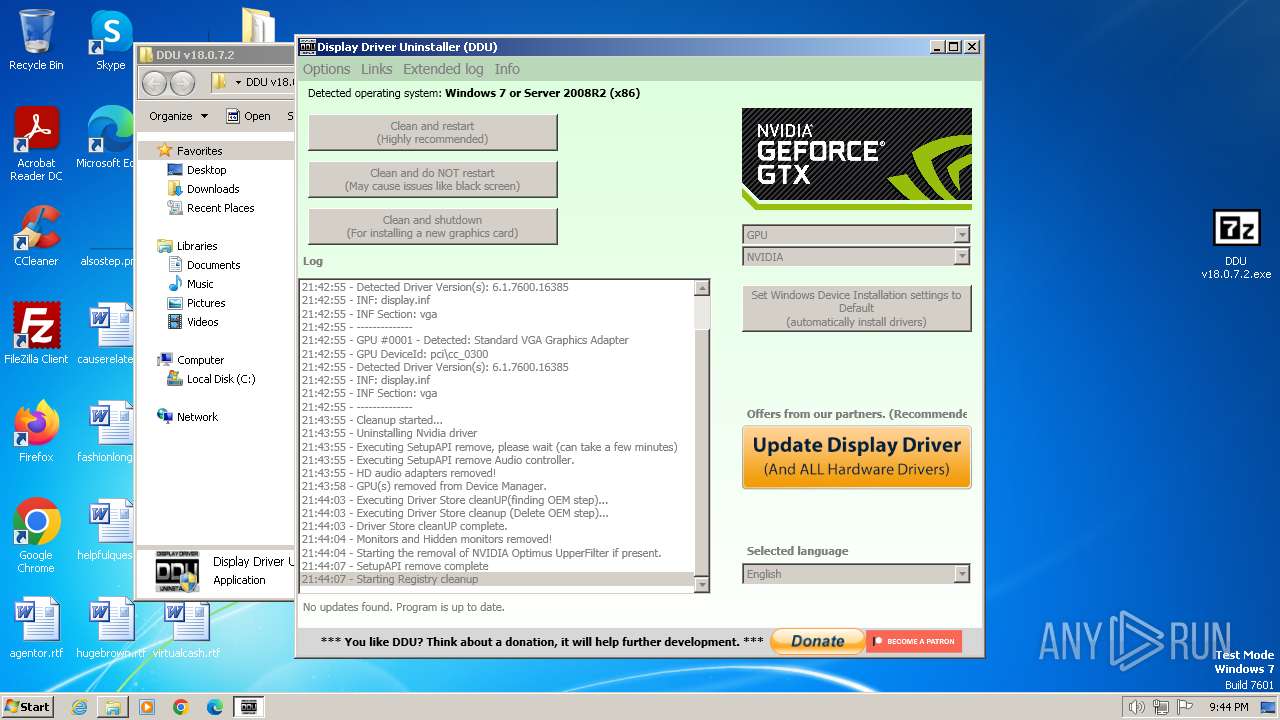
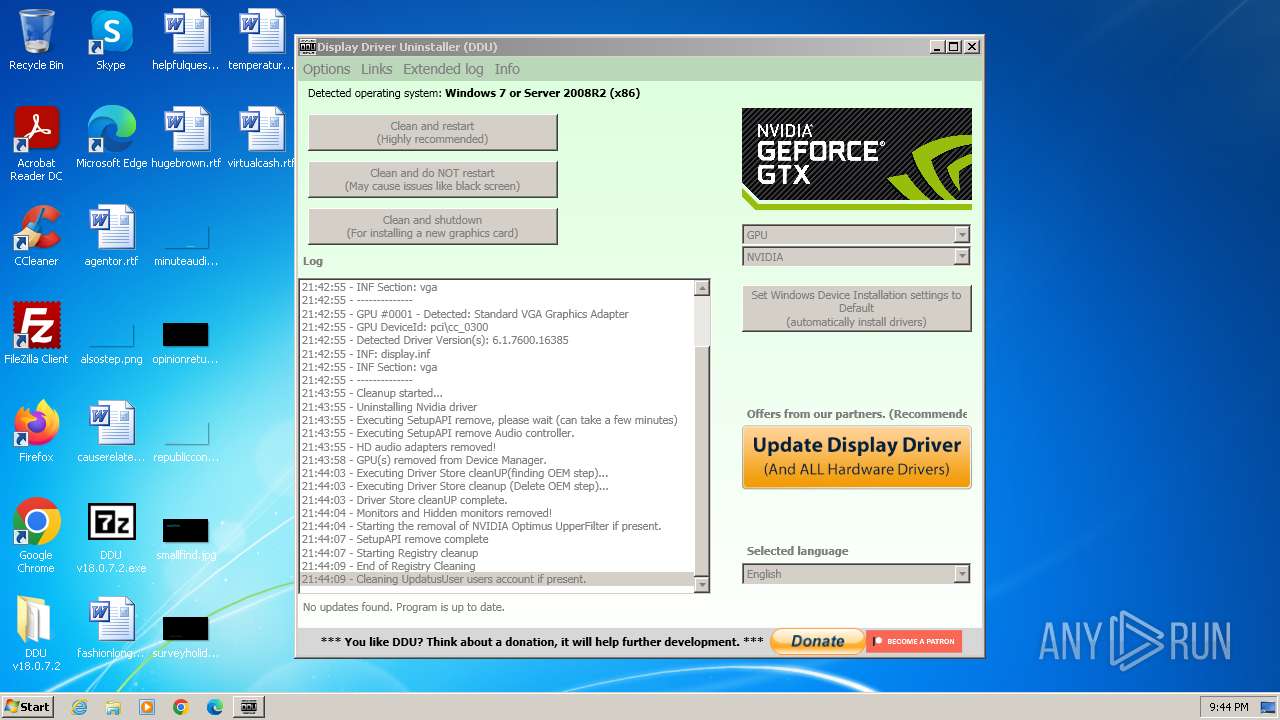
| Verdict: | Malicious activity |
| Analysis date: | January 29, 2024, 21:42:23 |
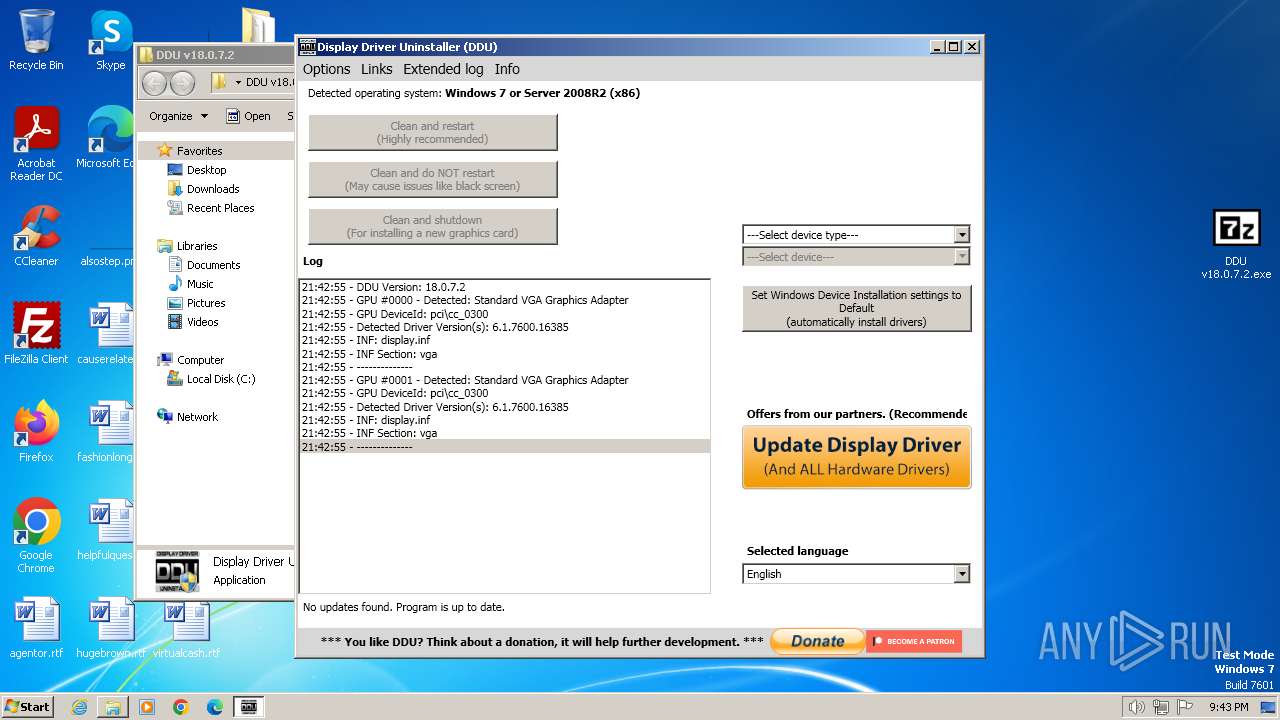
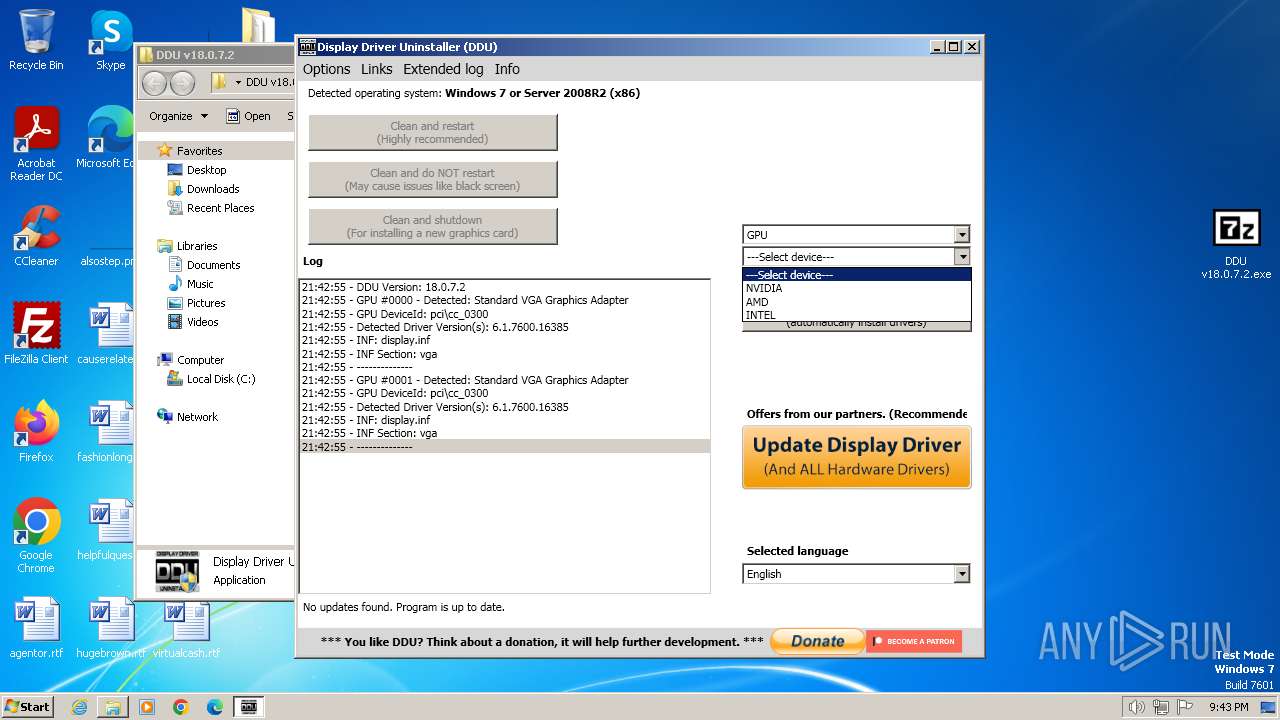
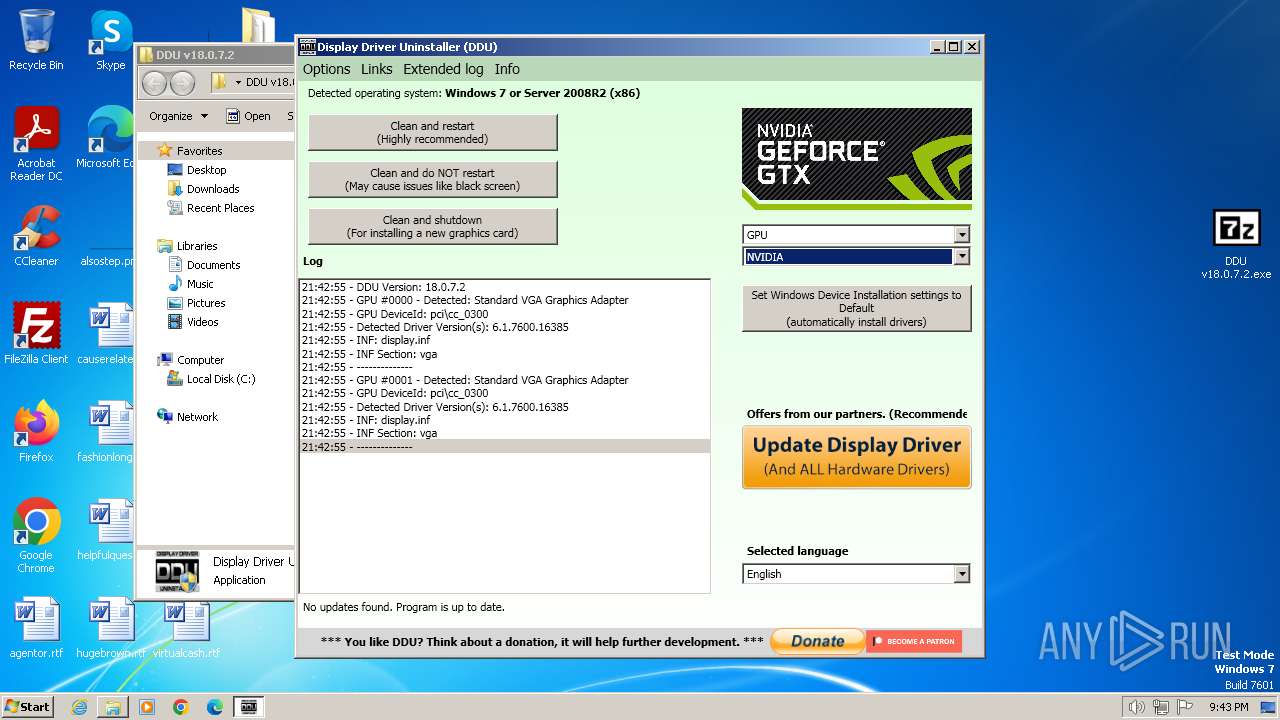
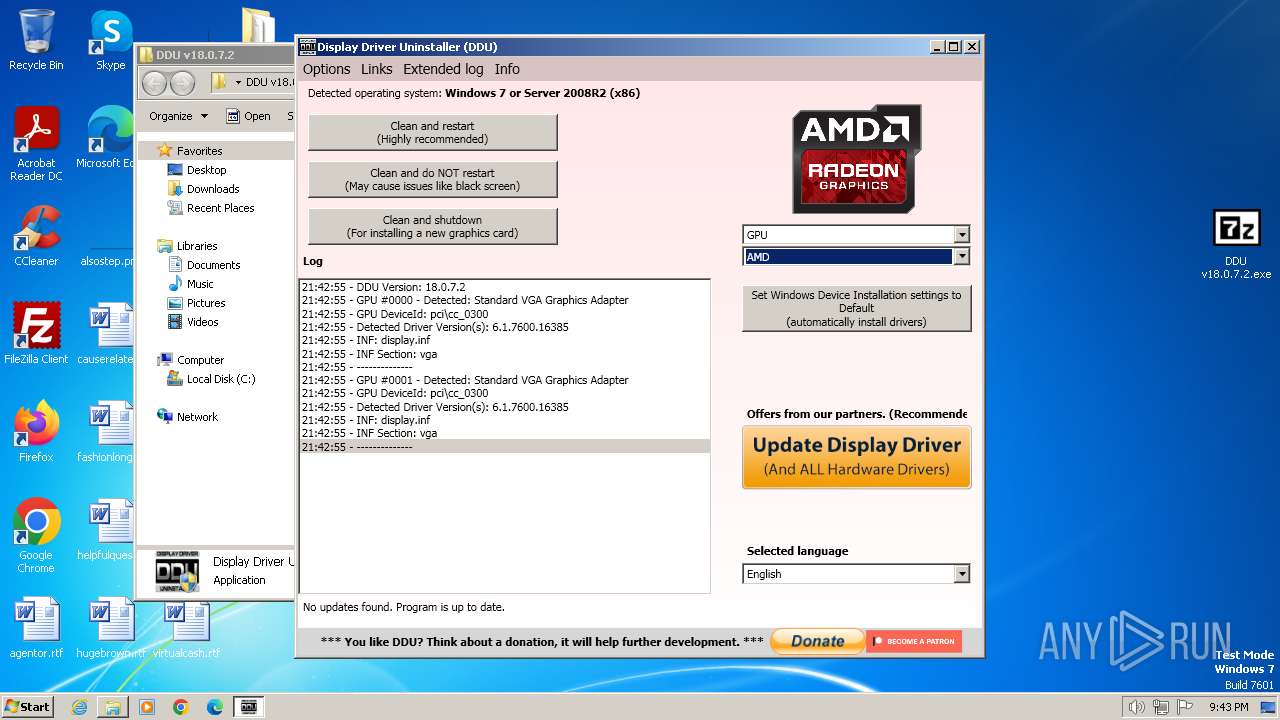
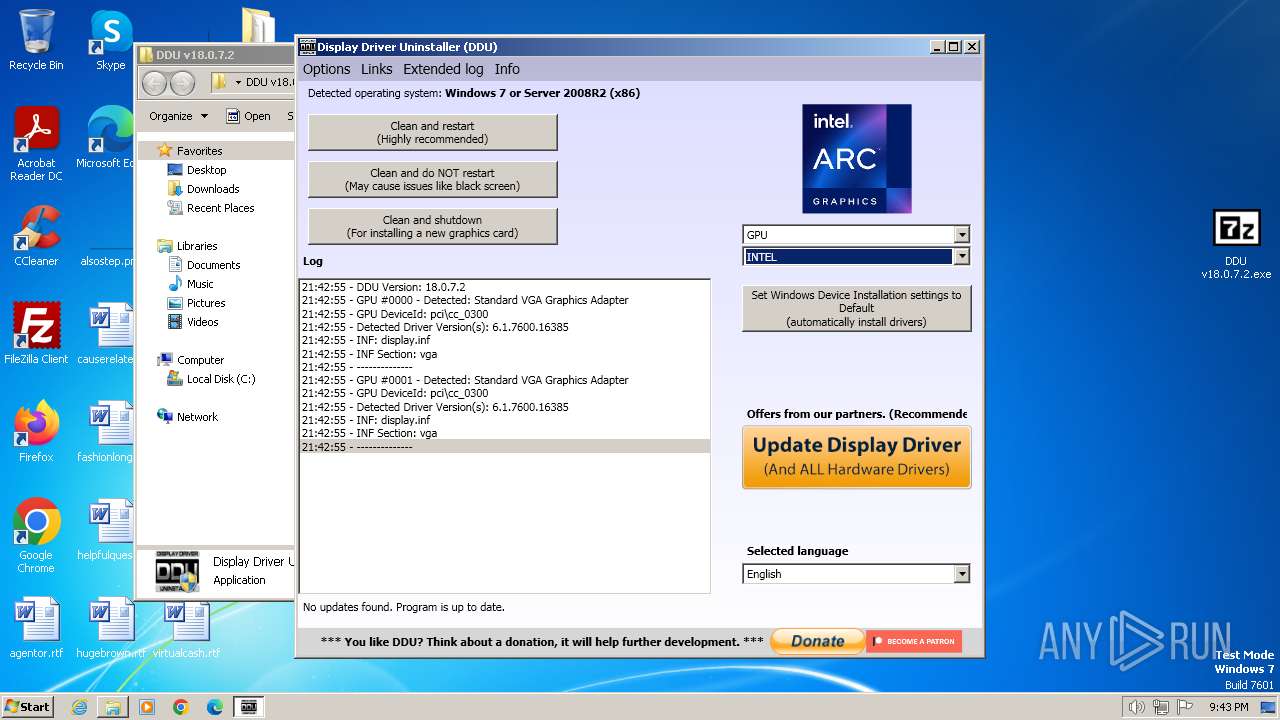
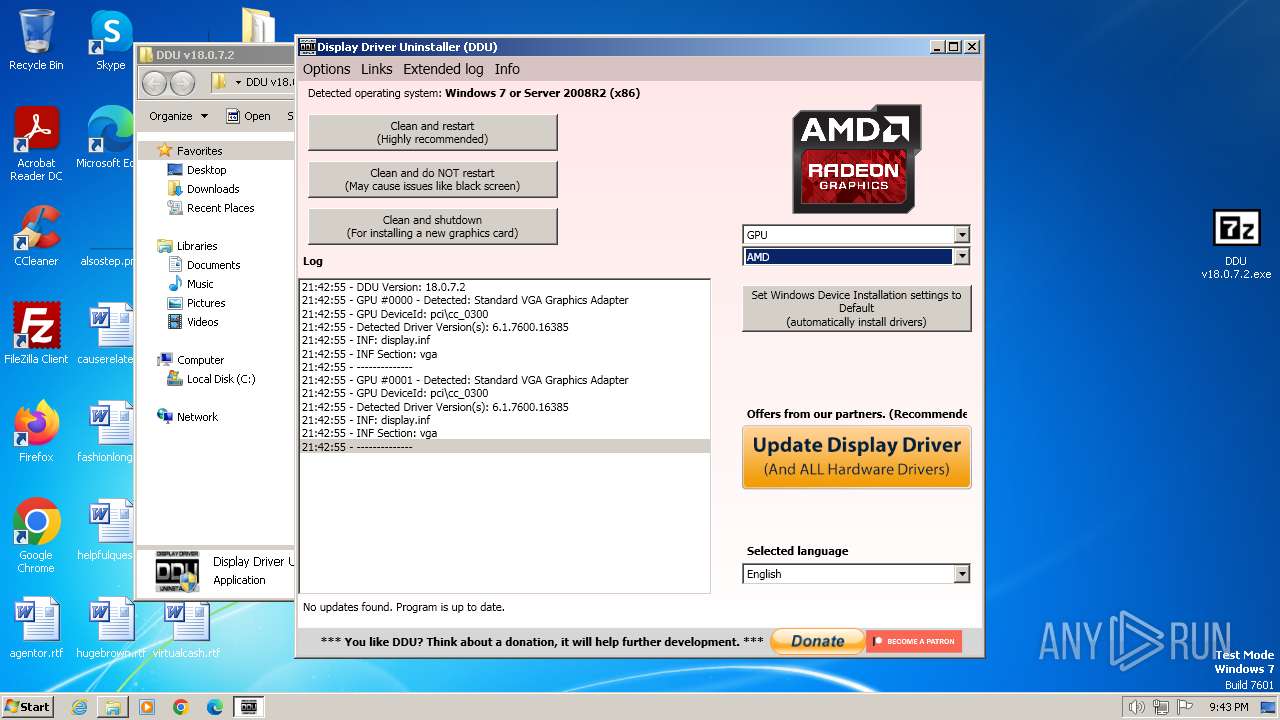
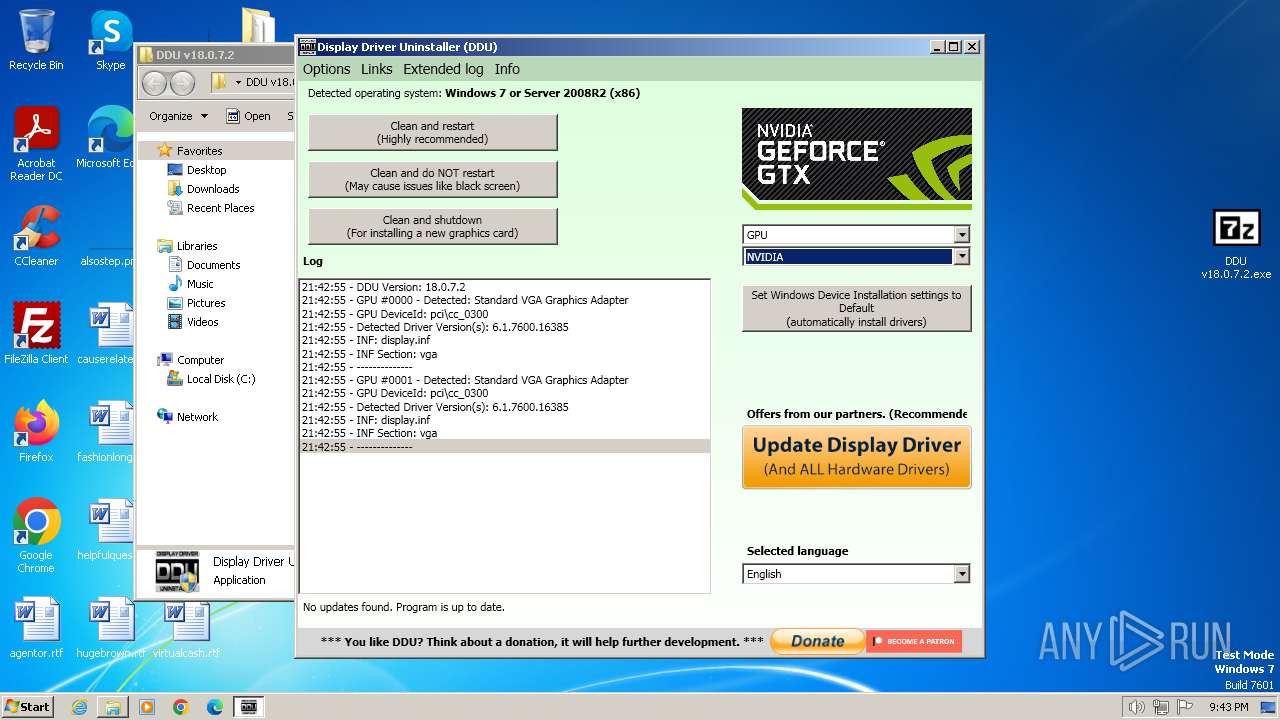
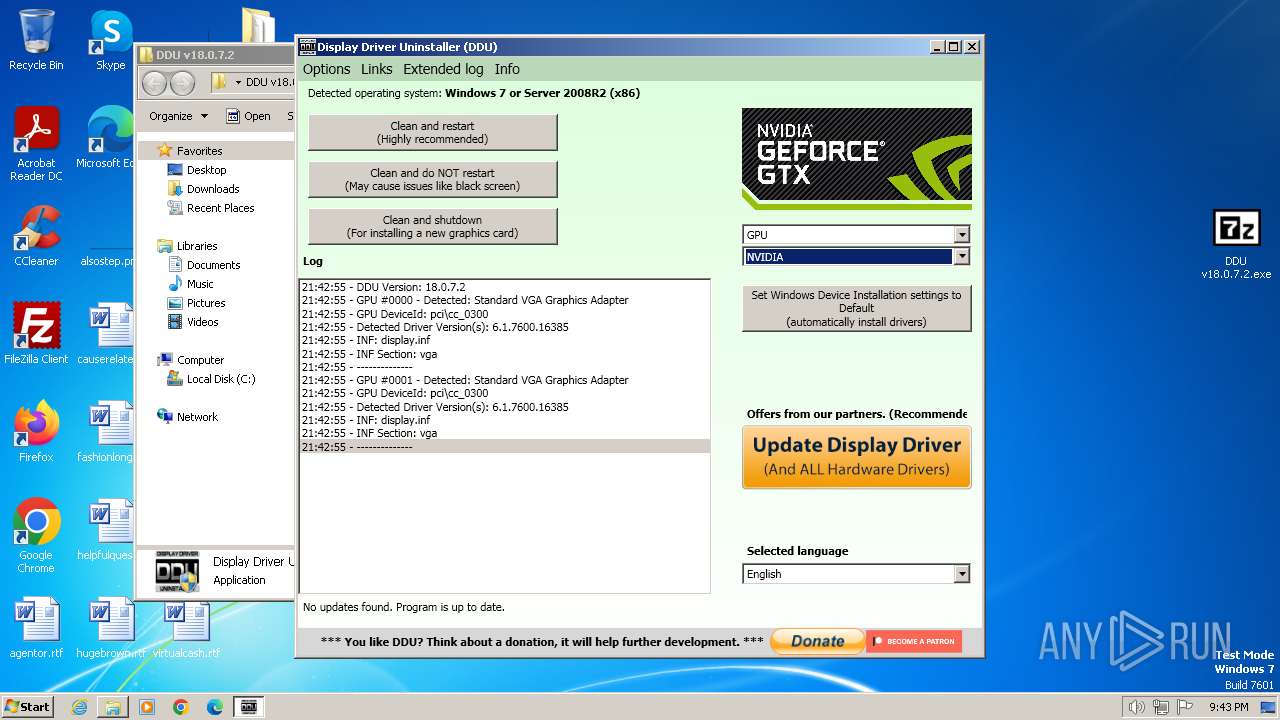
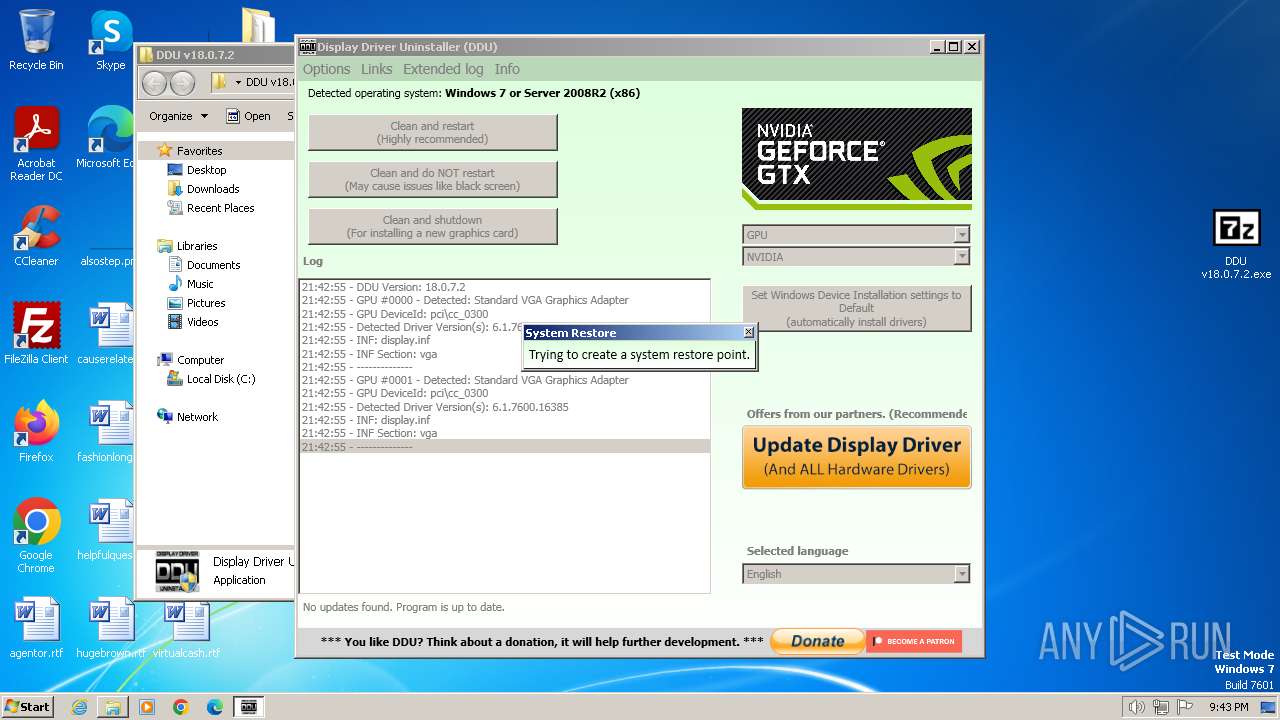
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 84C35DEAEF90138C34C865F6CE91AC7F |
| SHA1: | 27CD6D6441A1B943D2FECAE6F098AFBA2B76E069 |
| SHA256: | 3EFBD5E7063E1A07996494311F124B4CAE7815267D5EC8517BC01A0700AD52D6 |
| SSDEEP: | 12:2PaDW9GNctgiQERa3G4e0ofS5AyHD0wsu9CXZ:2Pp9GNaWG4enfSrHD08Cp |
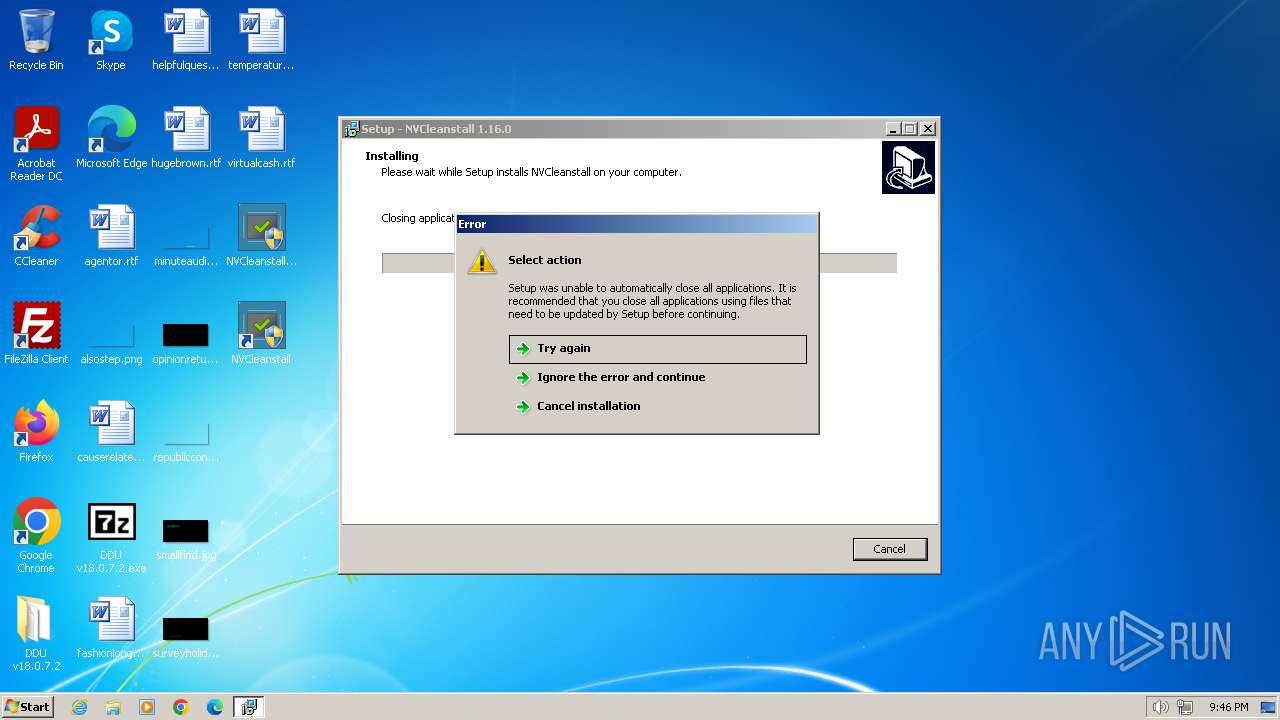
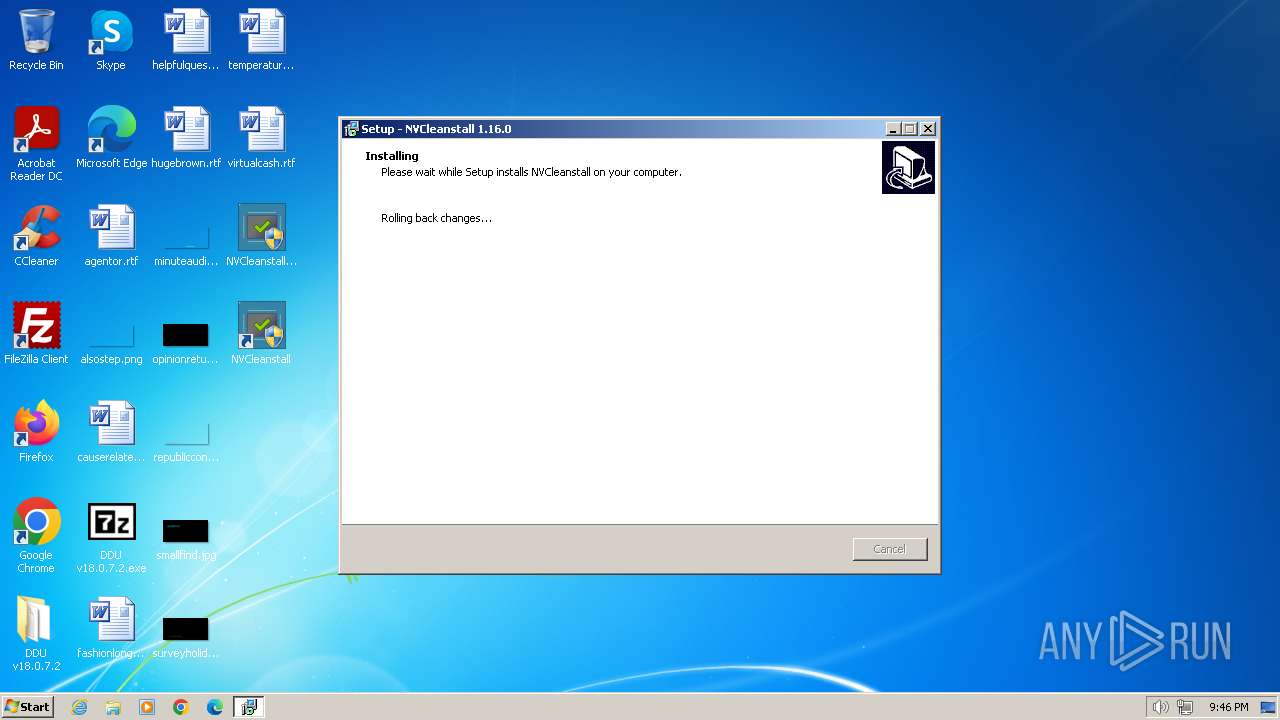
MALICIOUS
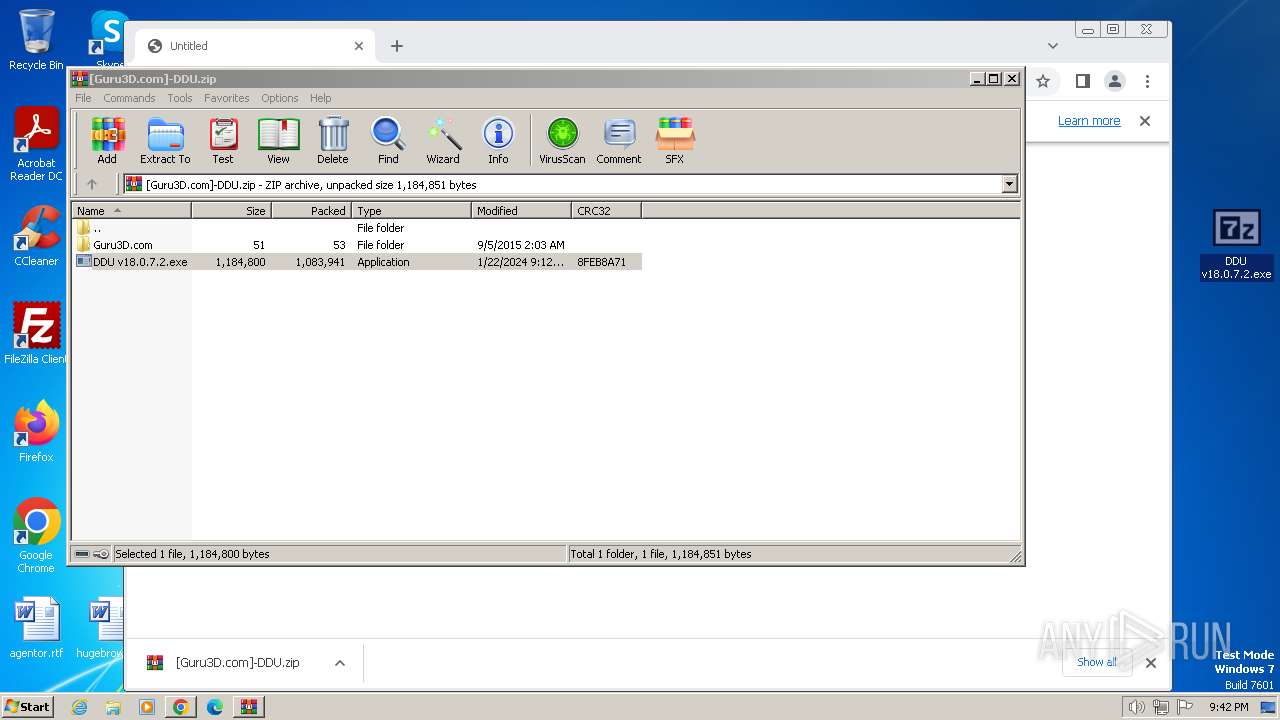
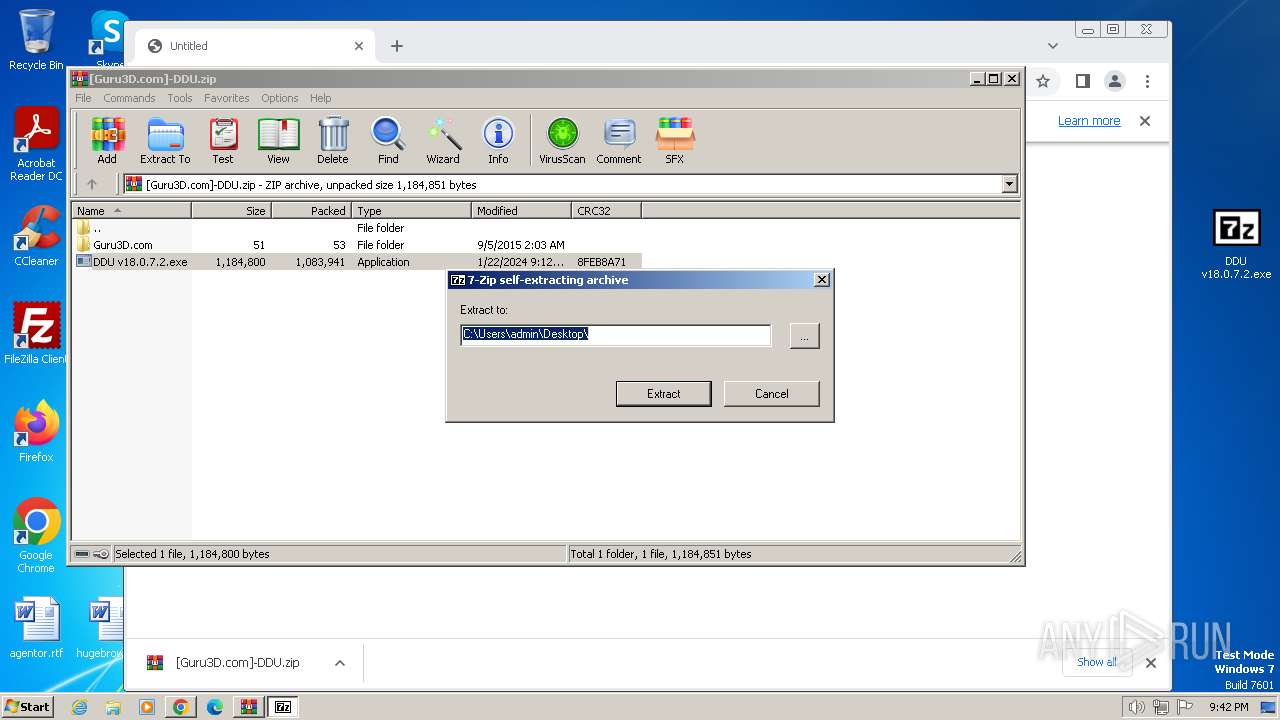
Drops the executable file immediately after the start
- DDU v18.0.7.2.exe (PID: 3892)
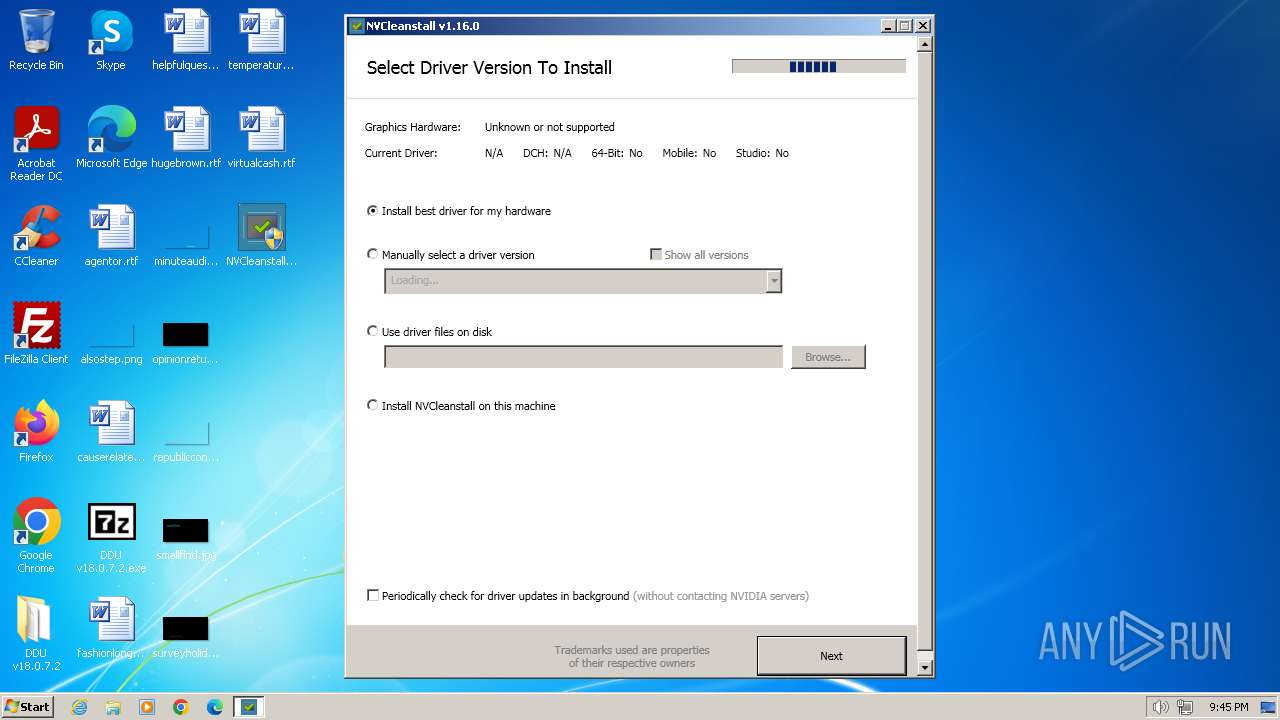
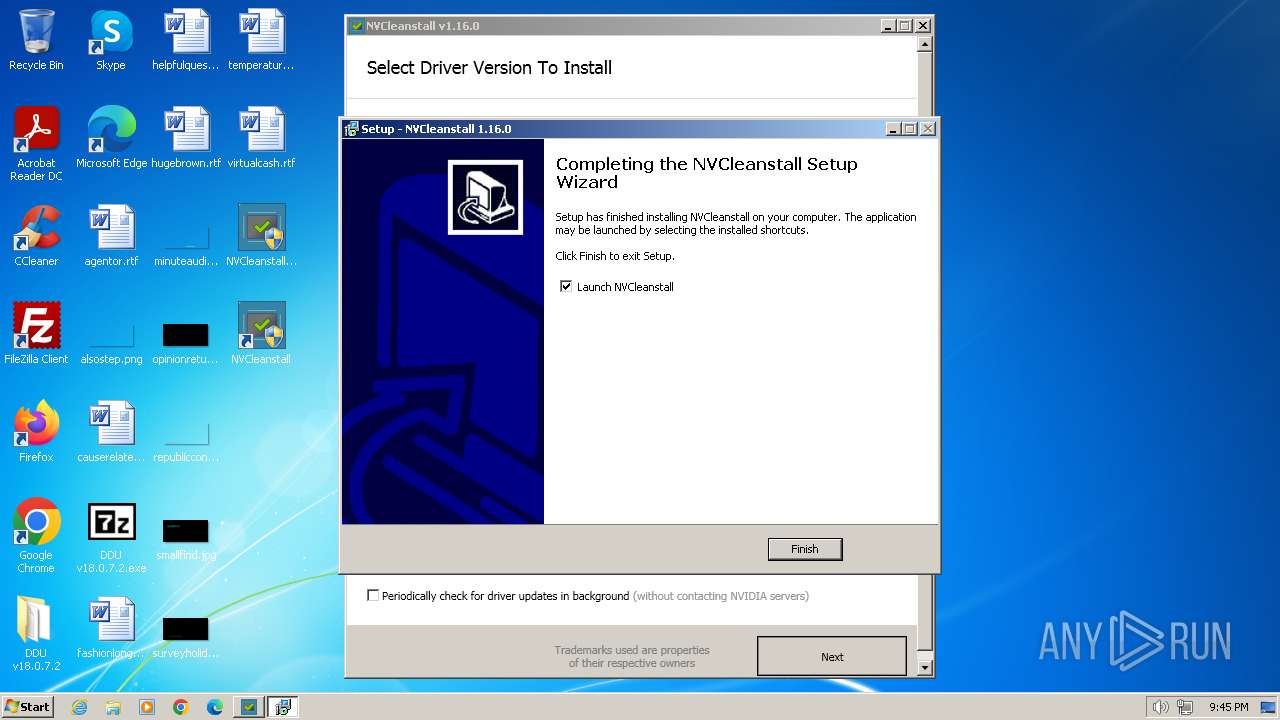
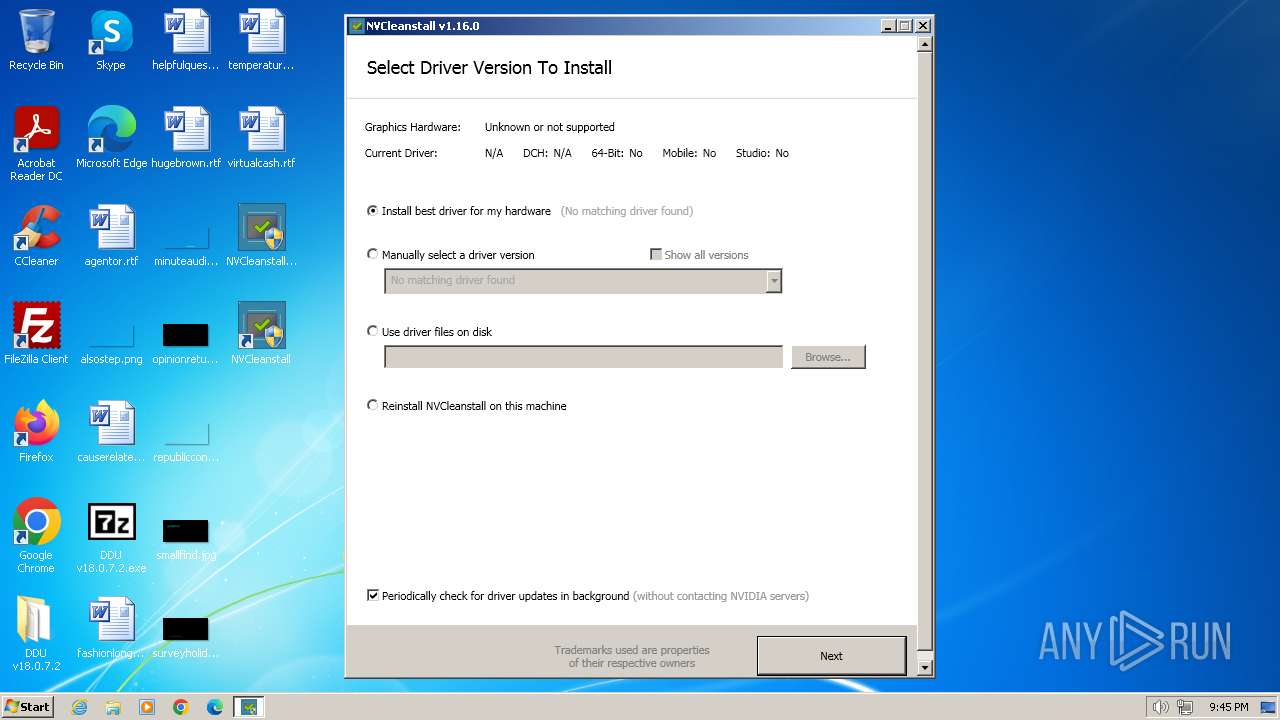
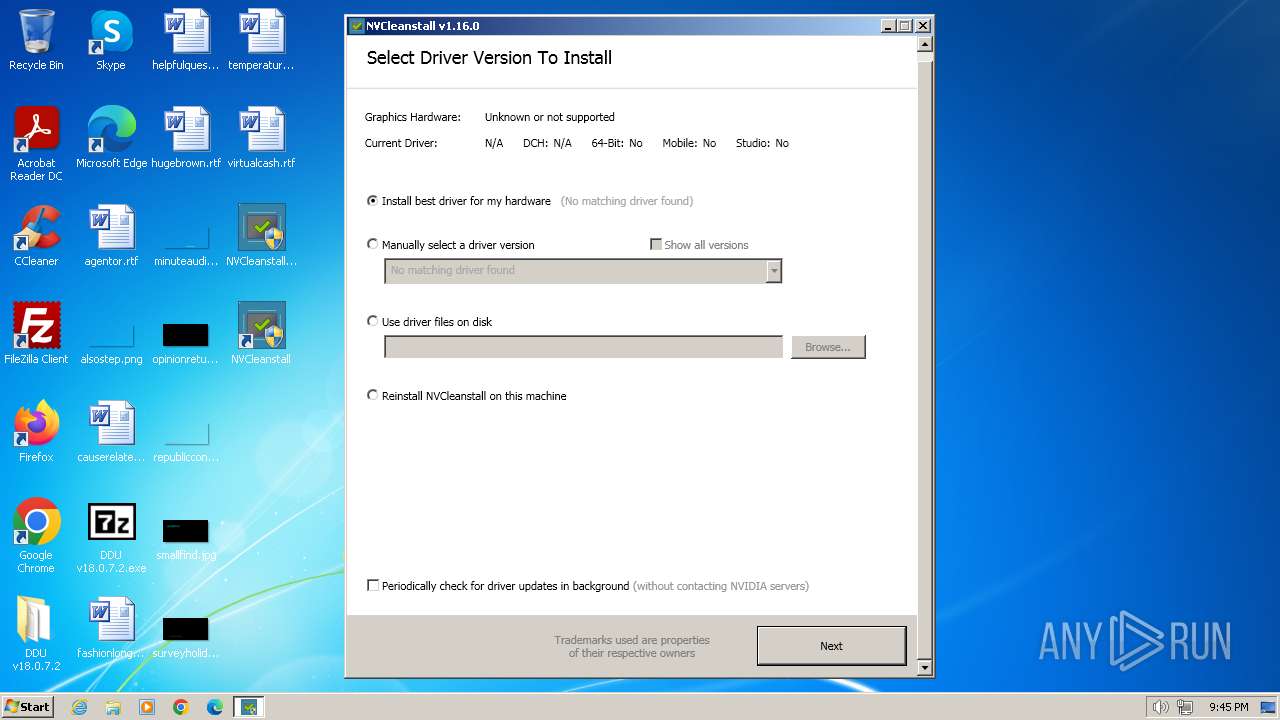
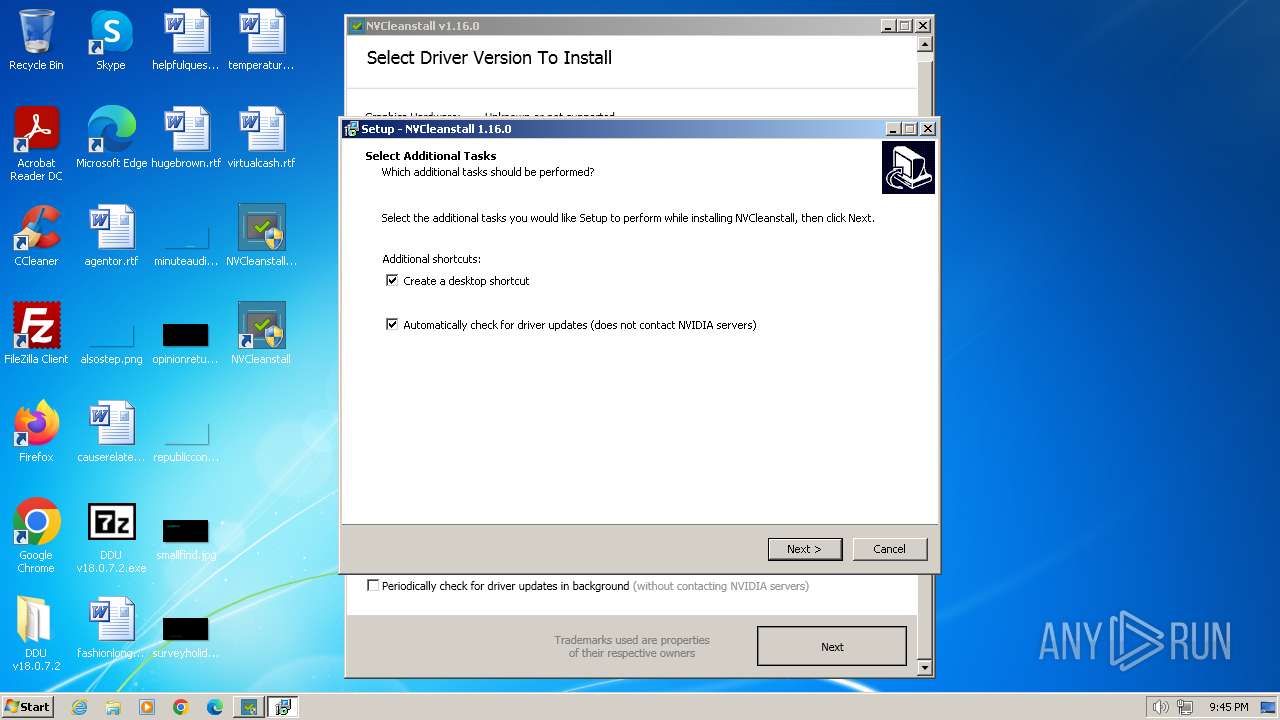
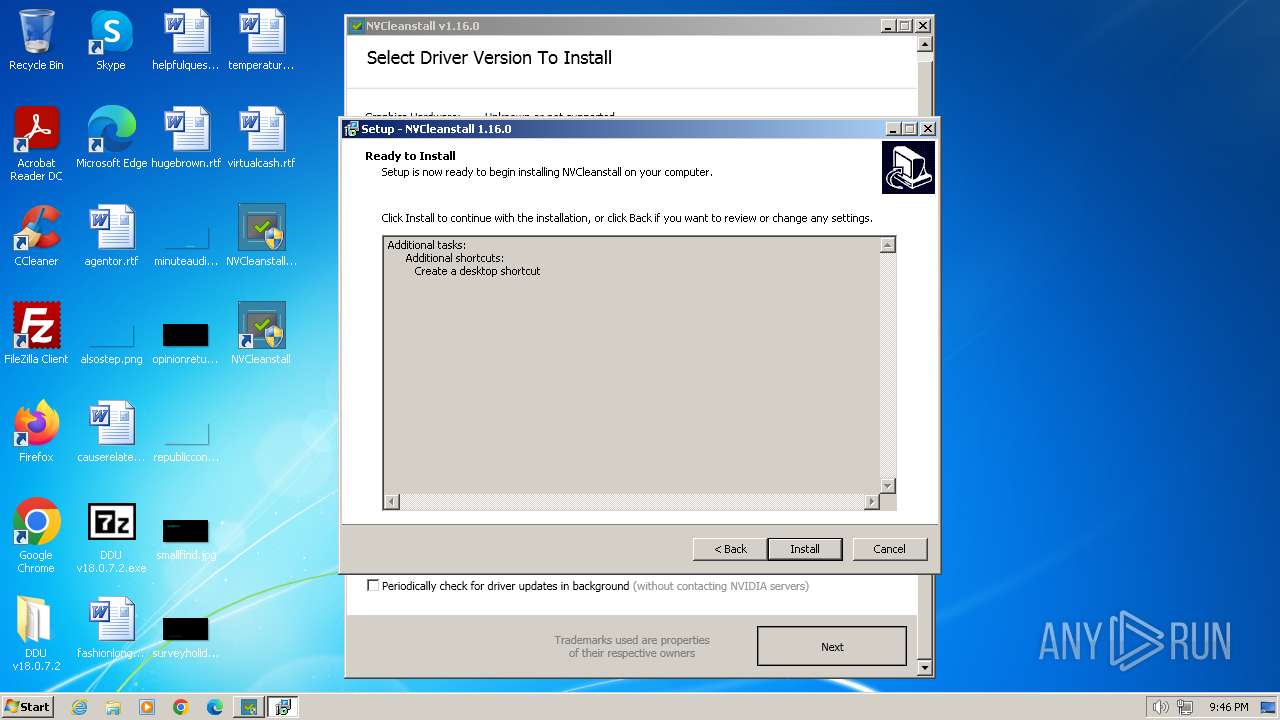
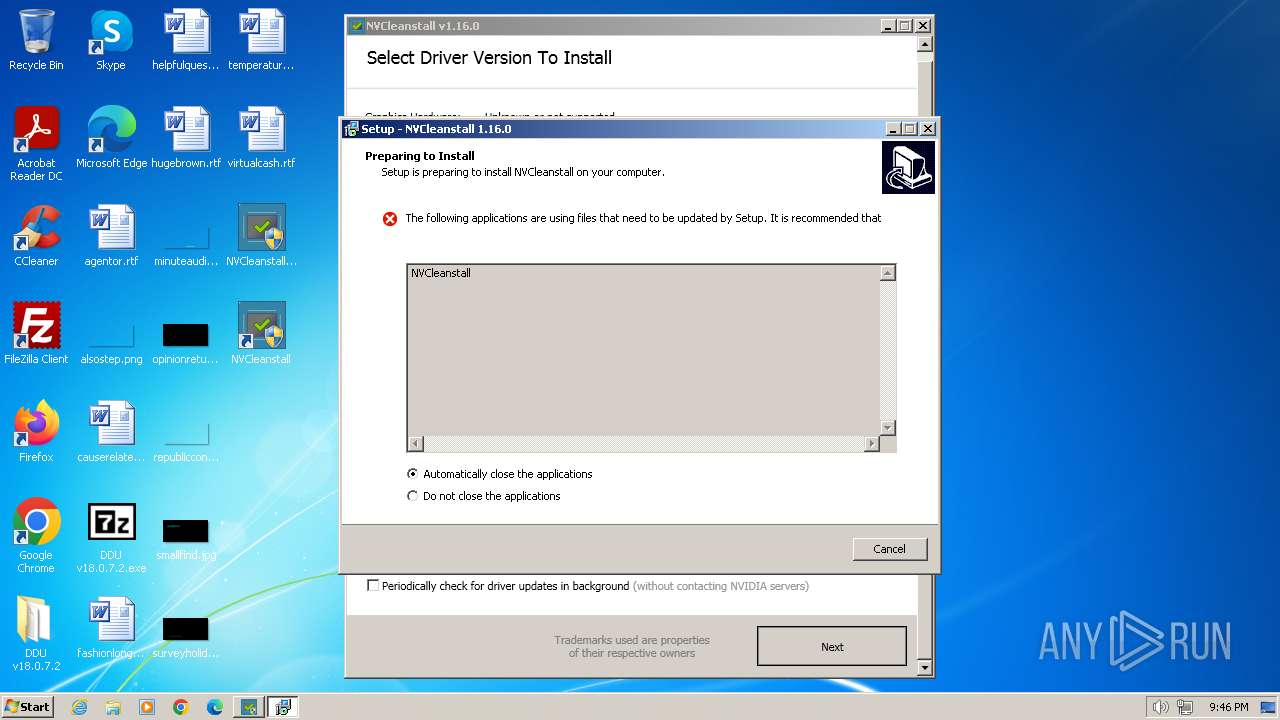
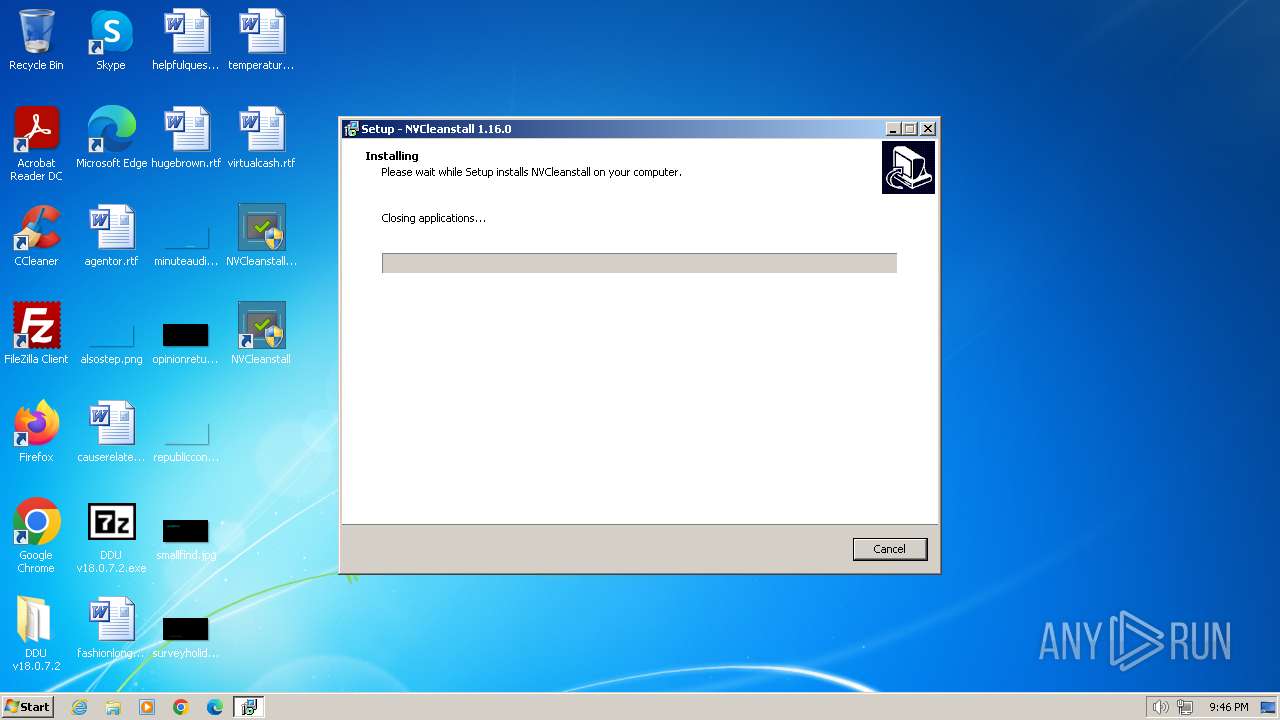
- NVCleanstall_1.16.0.exe (PID: 2764)
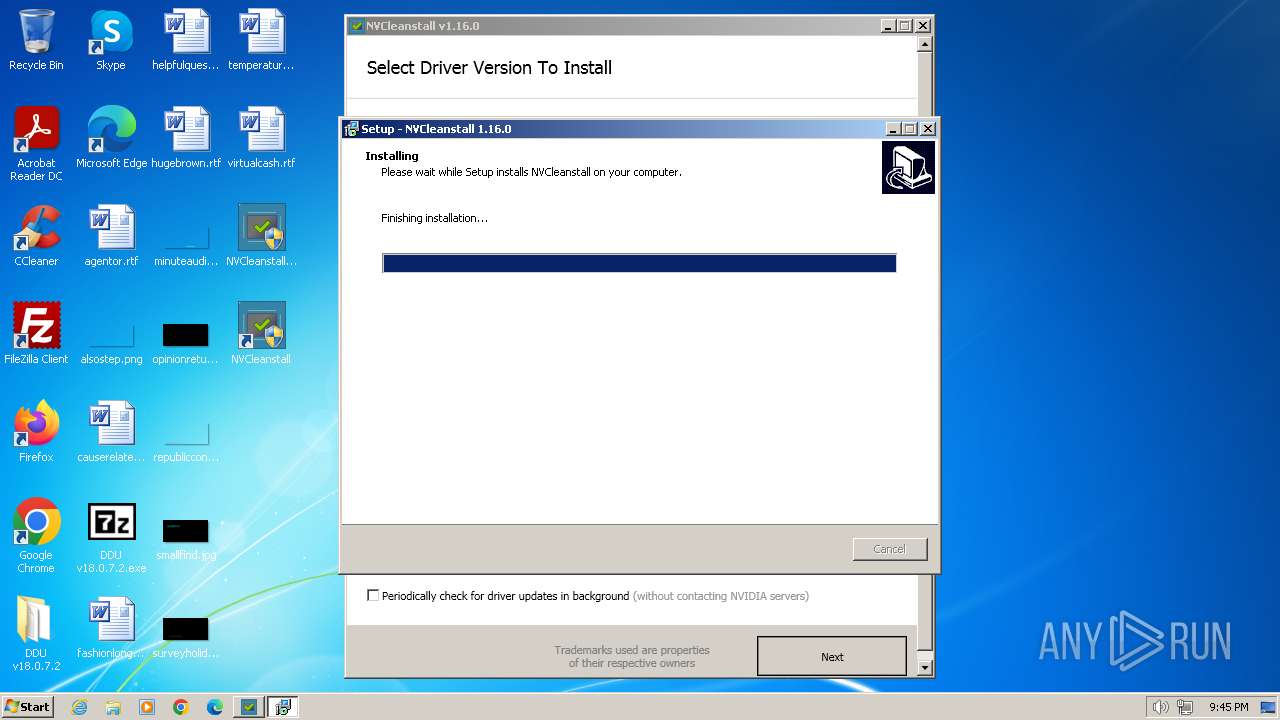
- NVCleanstall_Installer.tmp (PID: 2900)
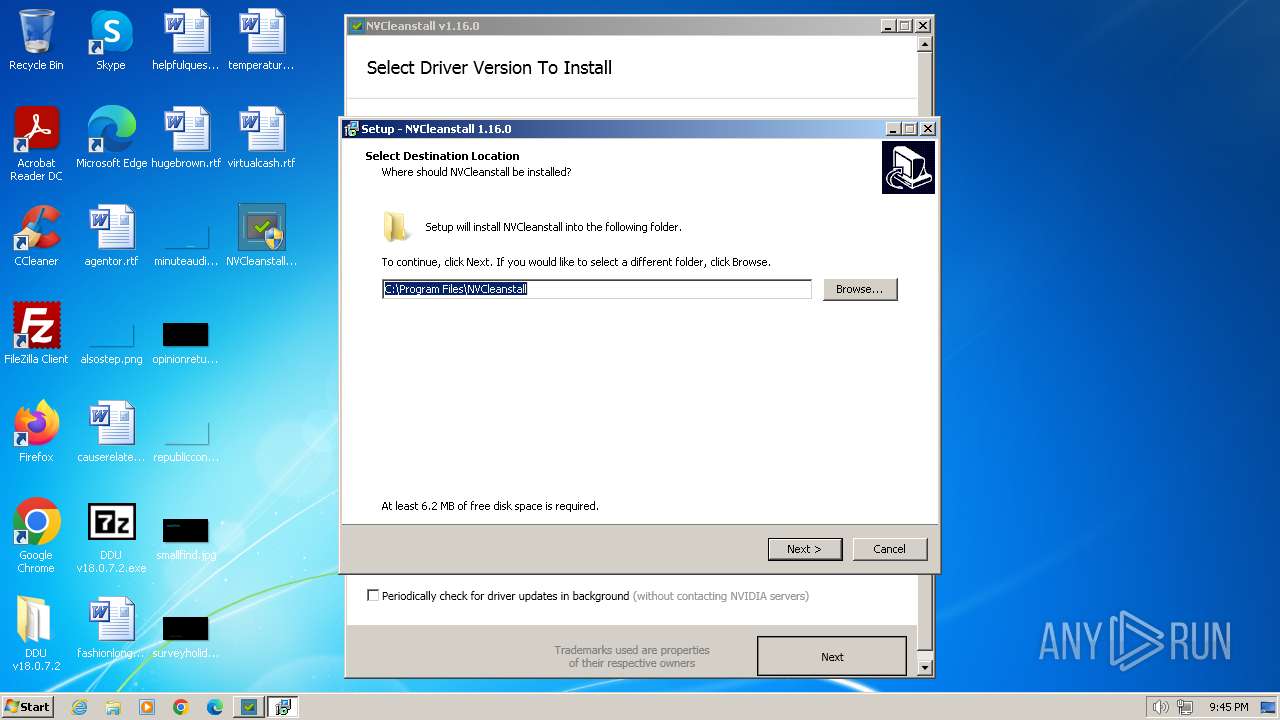
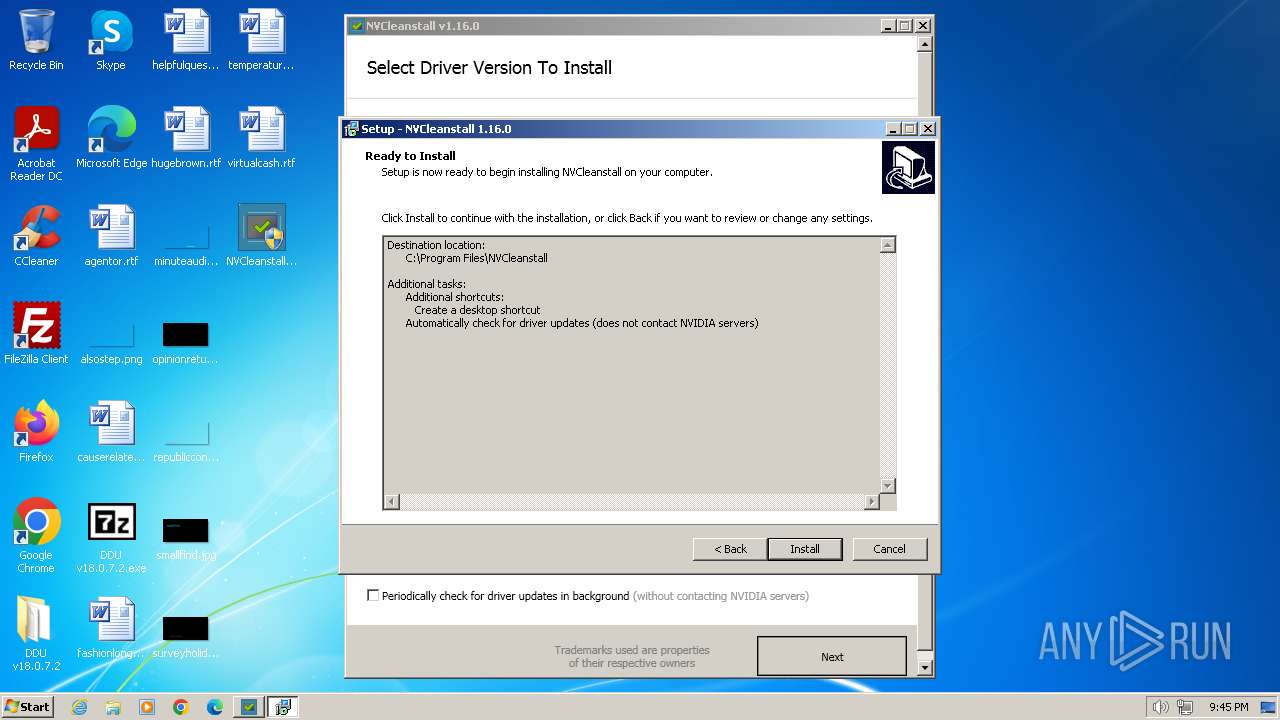
- NVCleanstall_Installer.exe (PID: 2892)
- NVCleanstall.exe (PID: 3016)
- NVCleanstall_Installer.exe (PID: 3208)
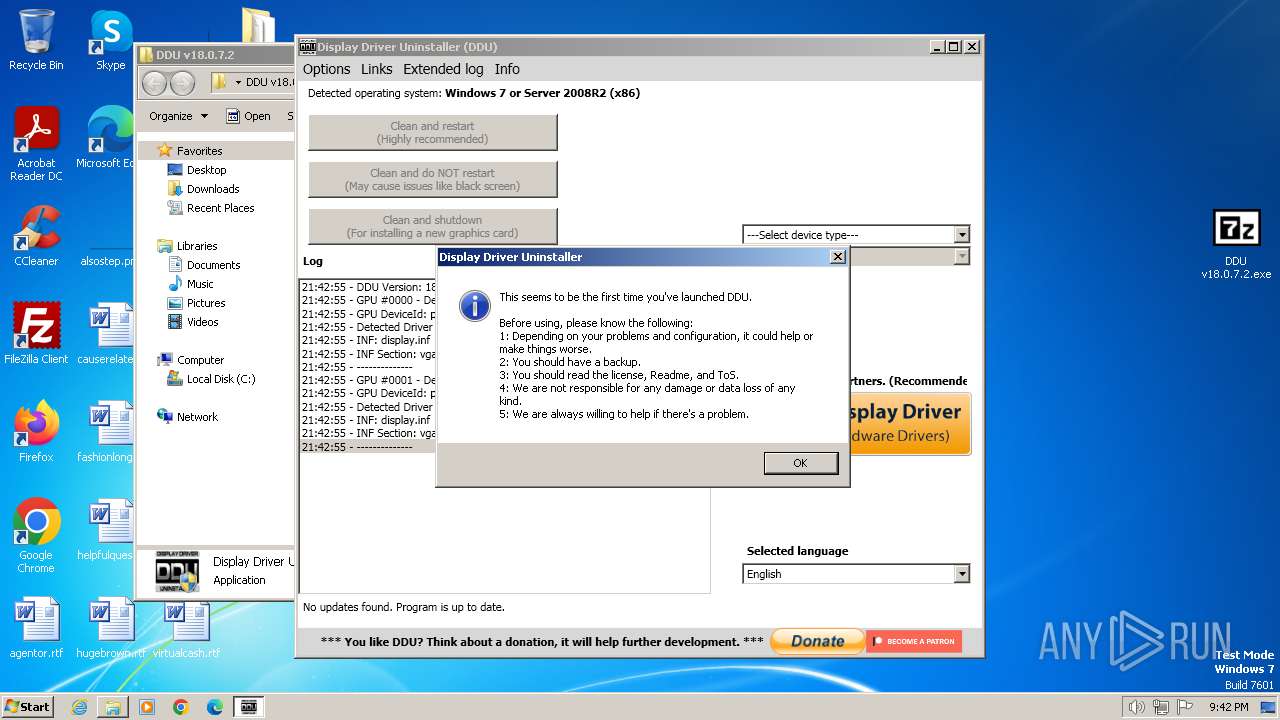
Changes the AppInit_DLLs value (autorun option)
- Display Driver Uninstaller.exe (PID: 3276)
SUSPICIOUS
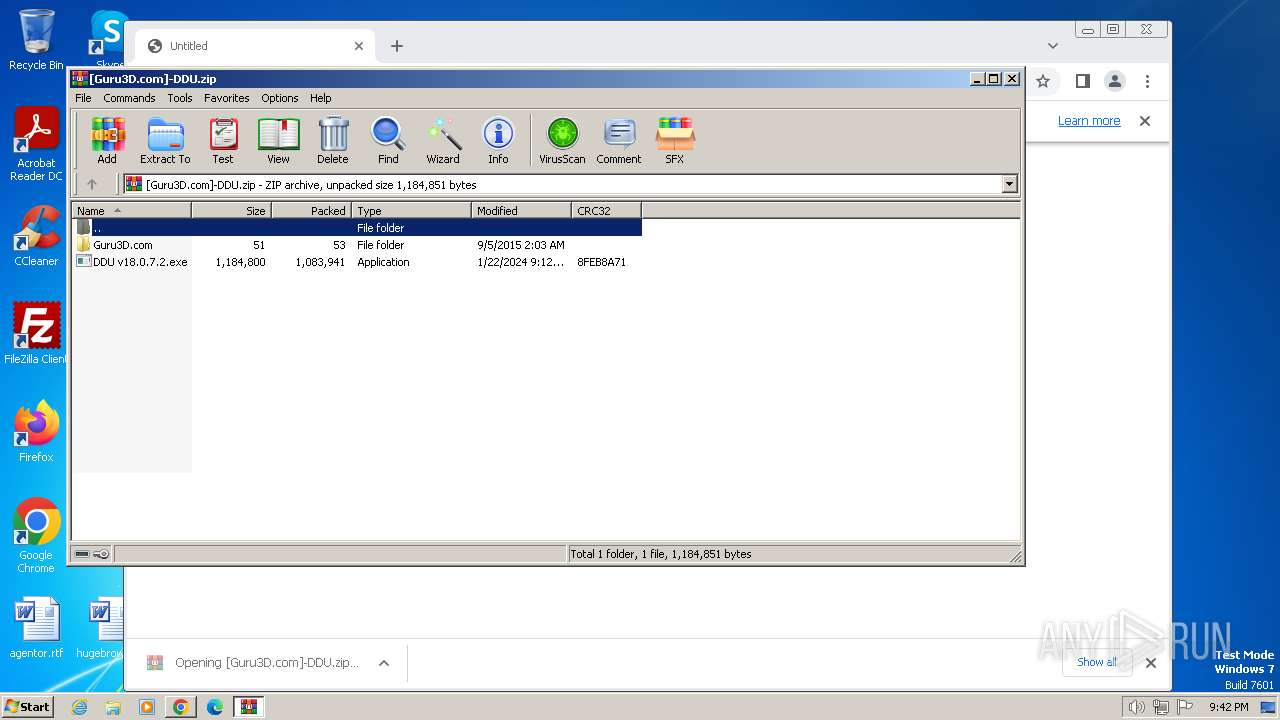
Drops 7-zip archiver for unpacking
- WinRAR.exe (PID: 1384)
- chrome.exe (PID: 3920)
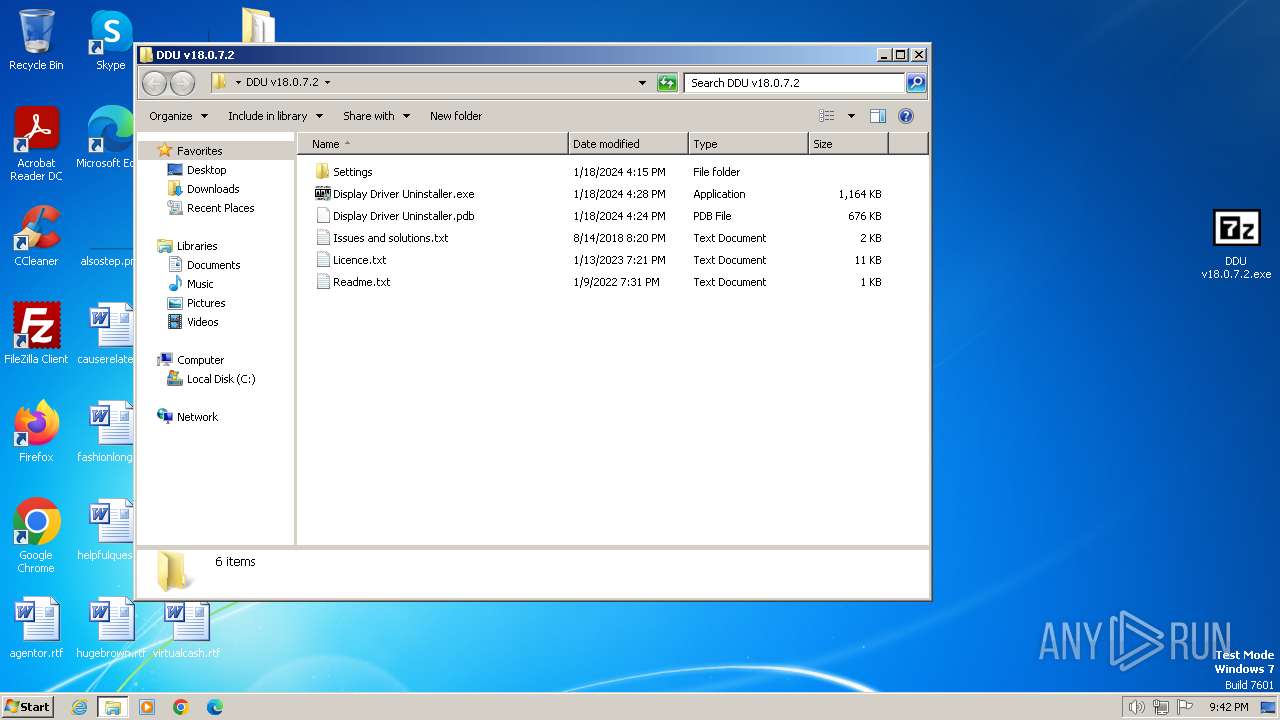
Executable content was dropped or overwritten
- DDU v18.0.7.2.exe (PID: 3892)
- NVCleanstall_1.16.0.exe (PID: 2764)
- NVCleanstall_Installer.exe (PID: 2892)
- NVCleanstall_Installer.tmp (PID: 2900)
- NVCleanstall.exe (PID: 3016)
- NVCleanstall_Installer.exe (PID: 3208)
Reads the Internet Settings
- Display Driver Uninstaller.exe (PID: 3276)
- sipnotify.exe (PID: 120)
- NVCleanstall_Installer.tmp (PID: 2900)
- NVCleanstall.exe (PID: 3016)
- NVCleanstall.exe (PID: 3692)
- NVCleanstall_1.16.0.exe (PID: 2764)
Reads settings of System Certificates
- Display Driver Uninstaller.exe (PID: 3276)
- sipnotify.exe (PID: 120)
- NVCleanstall_1.16.0.exe (PID: 2764)
- NVCleanstall.exe (PID: 3016)
- NVCleanstall.exe (PID: 3692)
Searches for installed software
- dllhost.exe (PID: 1808)
- Display Driver Uninstaller.exe (PID: 3276)
- NVCleanstall_Installer.tmp (PID: 3216)
Executes as Windows Service
- VSSVC.exe (PID: 1976)
Reads security settings of Internet Explorer
- Display Driver Uninstaller.exe (PID: 3276)
Application launched itself
- Display Driver Uninstaller.exe (PID: 3276)
Checks Windows Trust Settings
- Display Driver Uninstaller.exe (PID: 3276)
- drvinst.exe (PID: 2952)
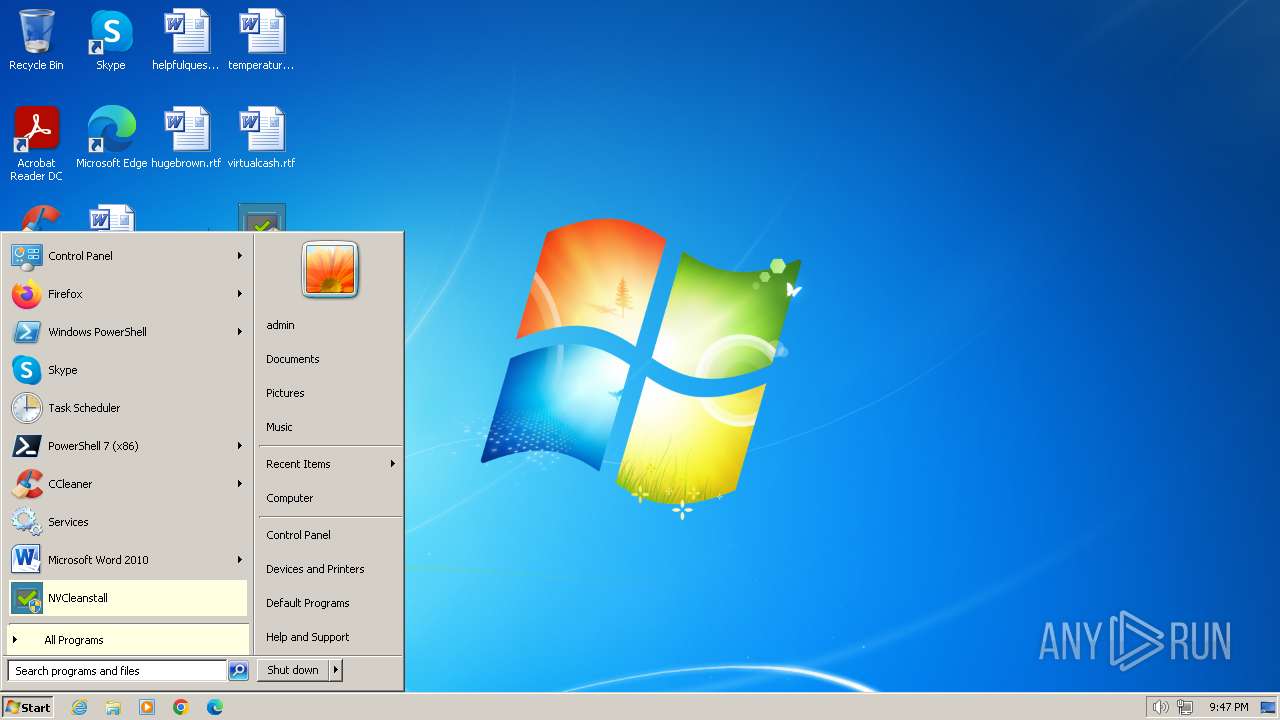
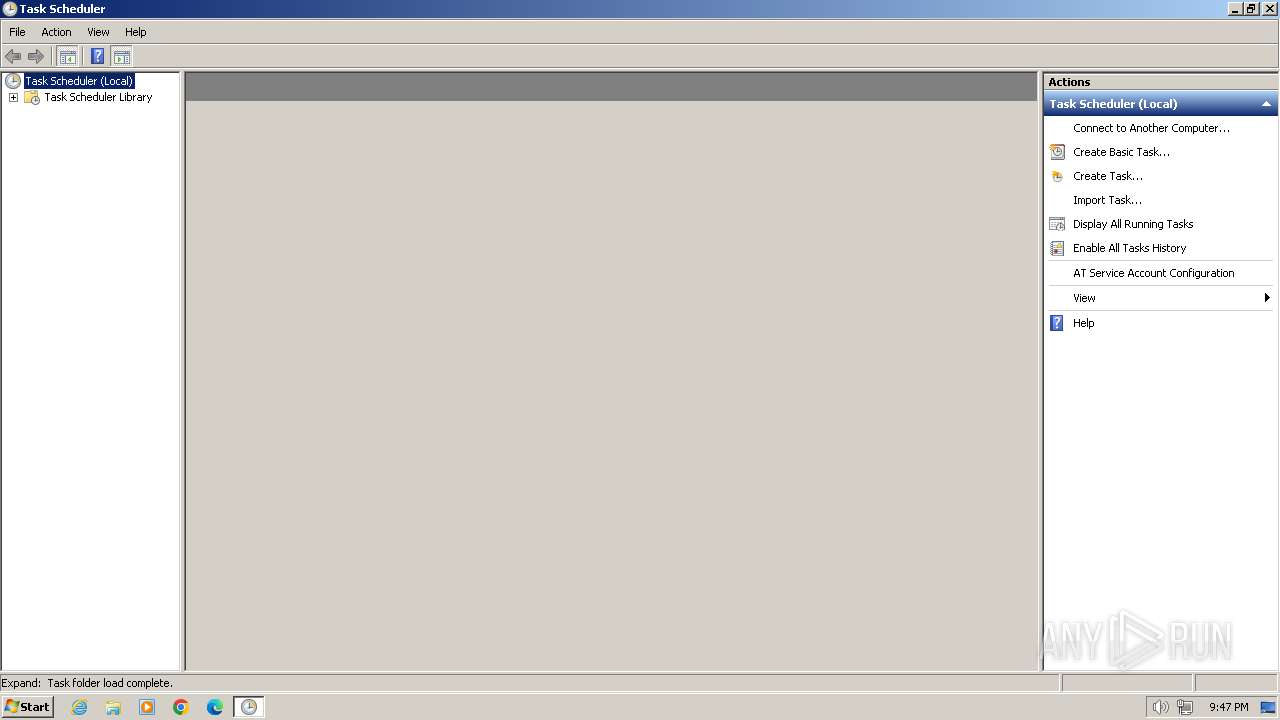
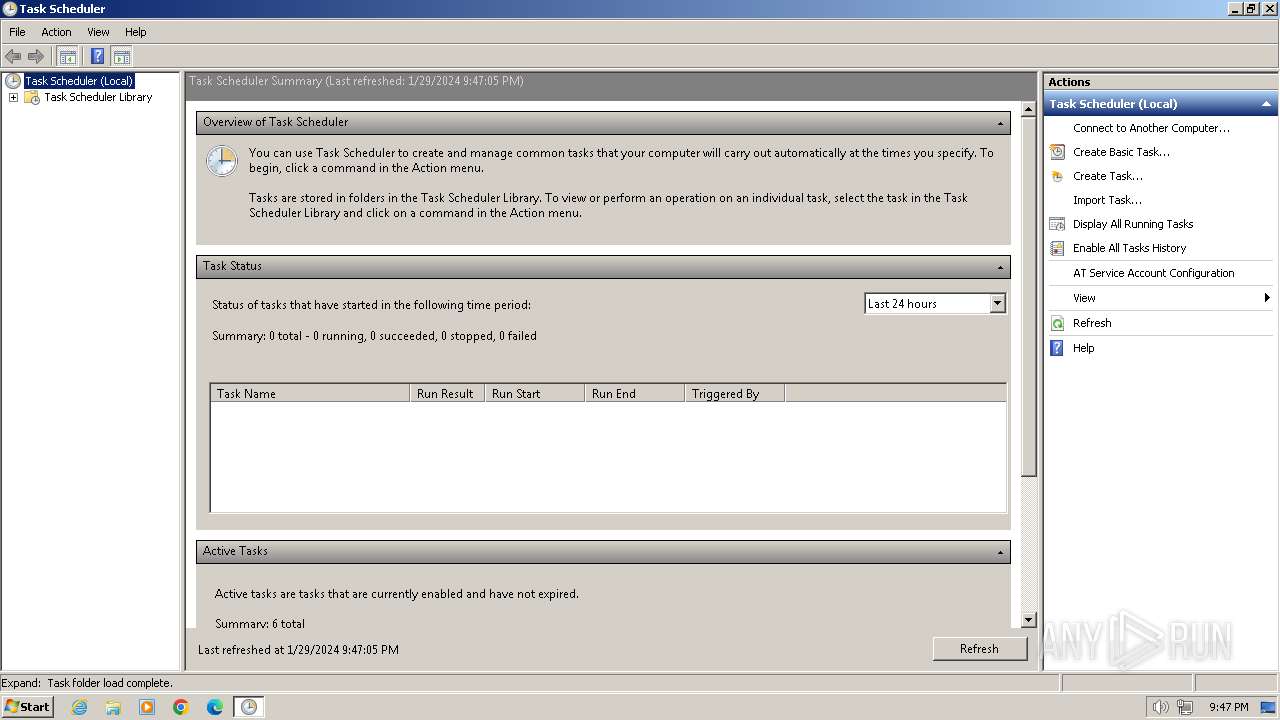
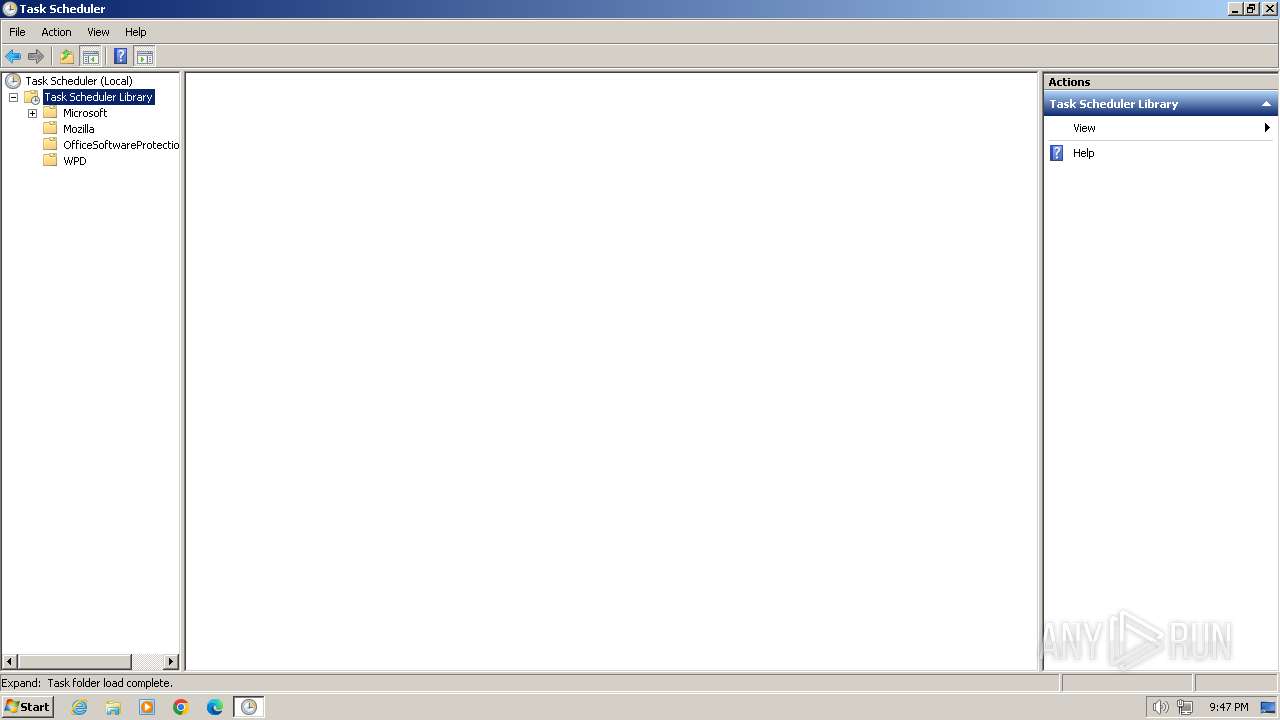
The process executes via Task Scheduler
- ctfmon.exe (PID: 448)
- sipnotify.exe (PID: 120)
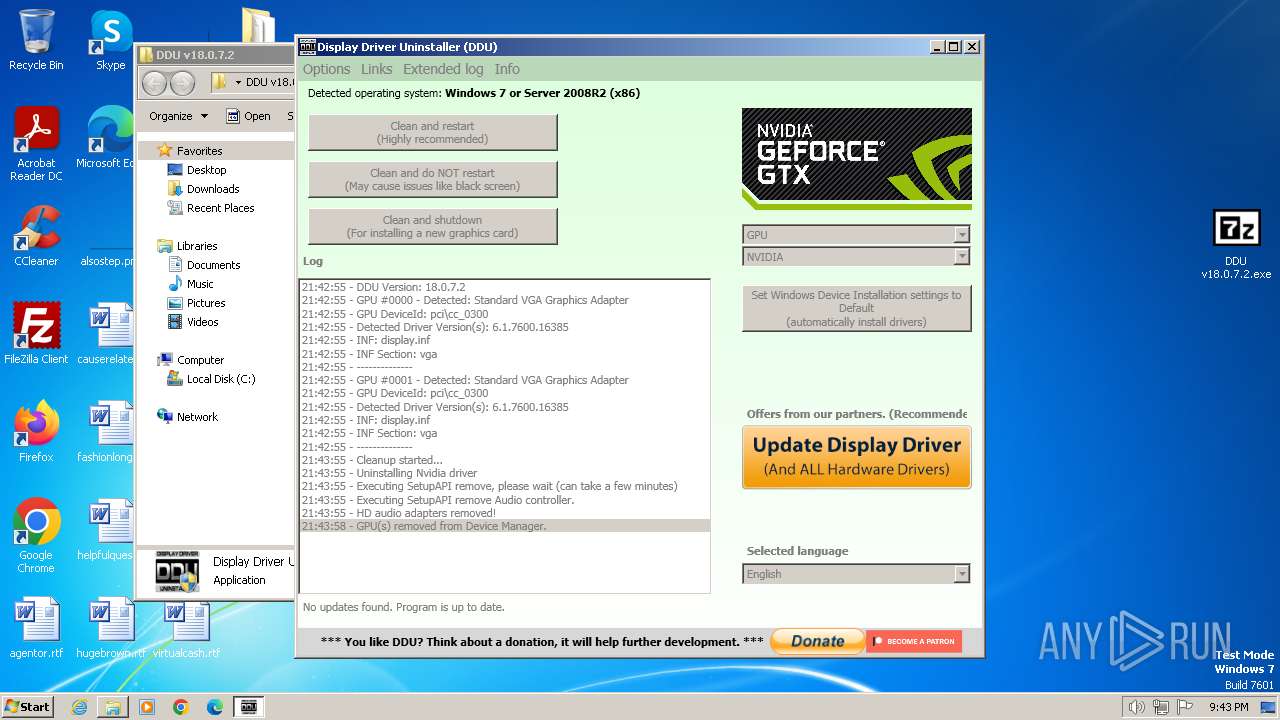
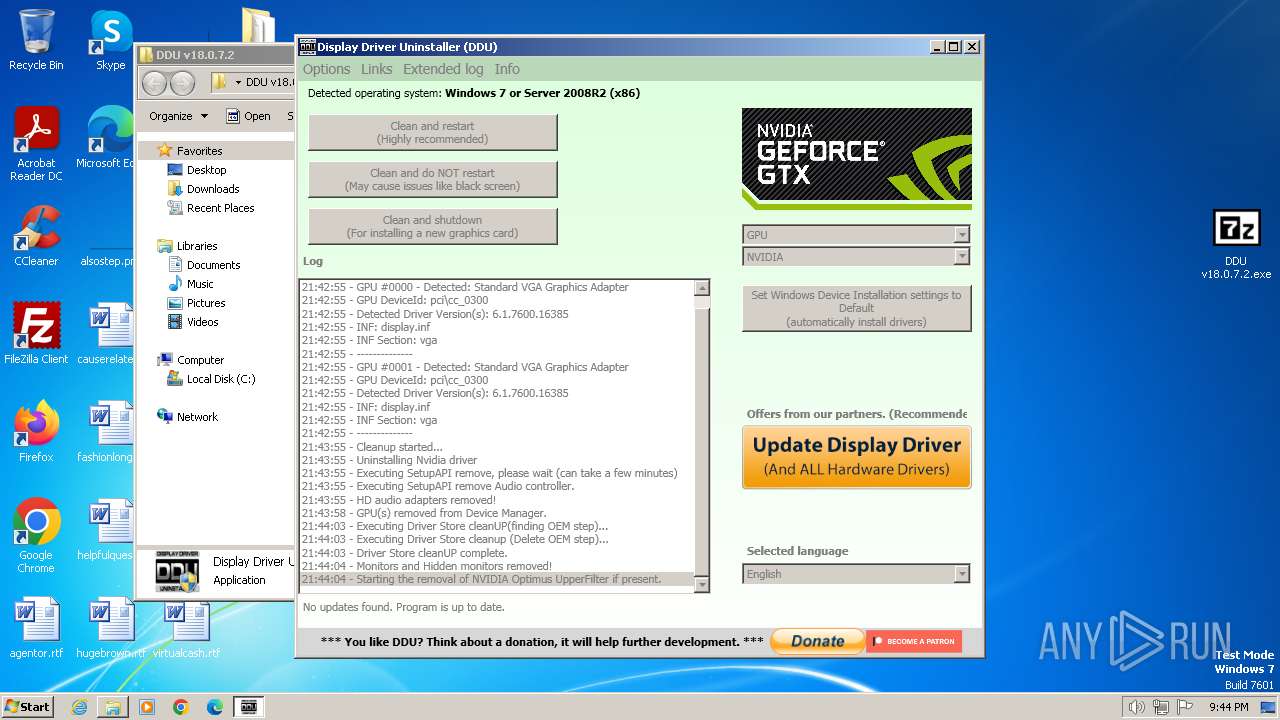
The system shut down or reboot
- Display Driver Uninstaller.exe (PID: 3700)
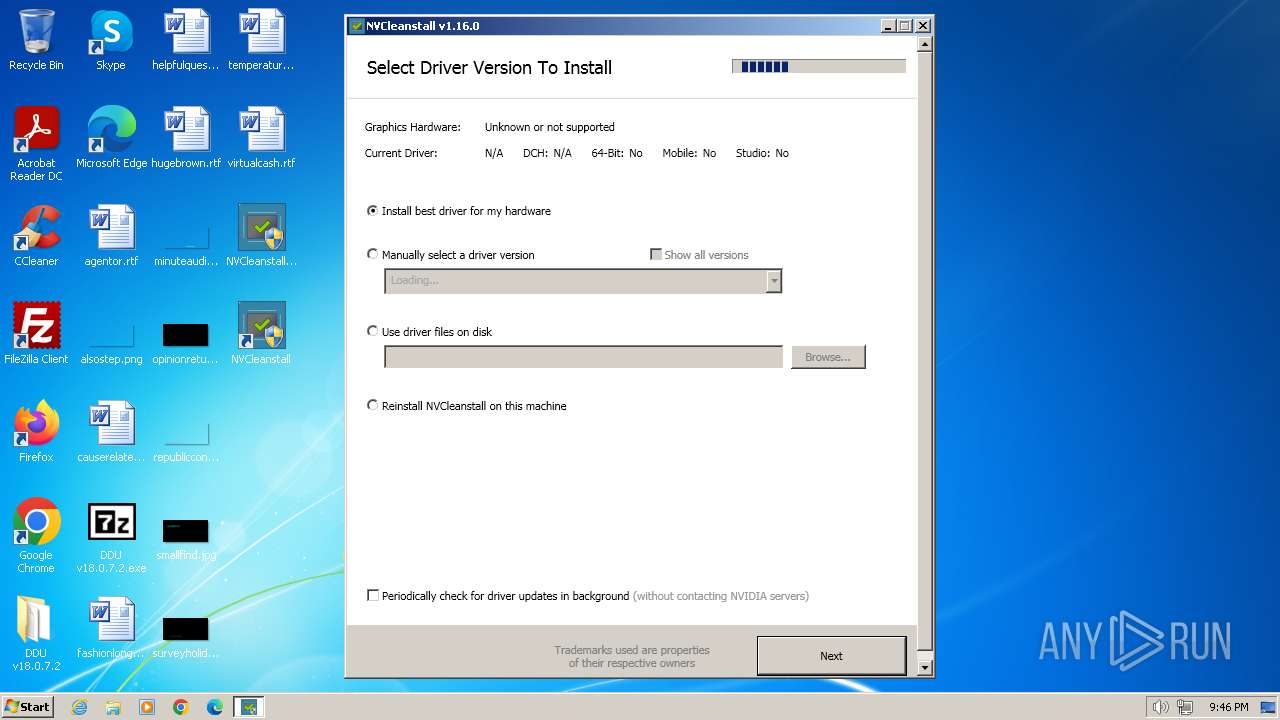
Process requests binary or script from the Internet
- NVCleanstall_1.16.0.exe (PID: 2764)
- NVCleanstall.exe (PID: 3016)
- NVCleanstall.exe (PID: 3692)
Adds/modifies Windows certificates
- NVCleanstall_1.16.0.exe (PID: 2764)
Reads the Windows owner or organization settings
- NVCleanstall_Installer.tmp (PID: 2900)
- NVCleanstall_Installer.tmp (PID: 3216)
Executing commands from a ".bat" file
- NVCleanstall_Installer.tmp (PID: 2900)
Starts CMD.EXE for commands execution
- NVCleanstall_Installer.tmp (PID: 2900)
INFO
Application launched itself
- chrome.exe (PID: 1264)
The process uses the downloaded file
- WinRAR.exe (PID: 1384)
- chrome.exe (PID: 1196)
Executable content was dropped or overwritten
- chrome.exe (PID: 3920)
- WinRAR.exe (PID: 1384)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 1384)
- chrome.exe (PID: 3920)
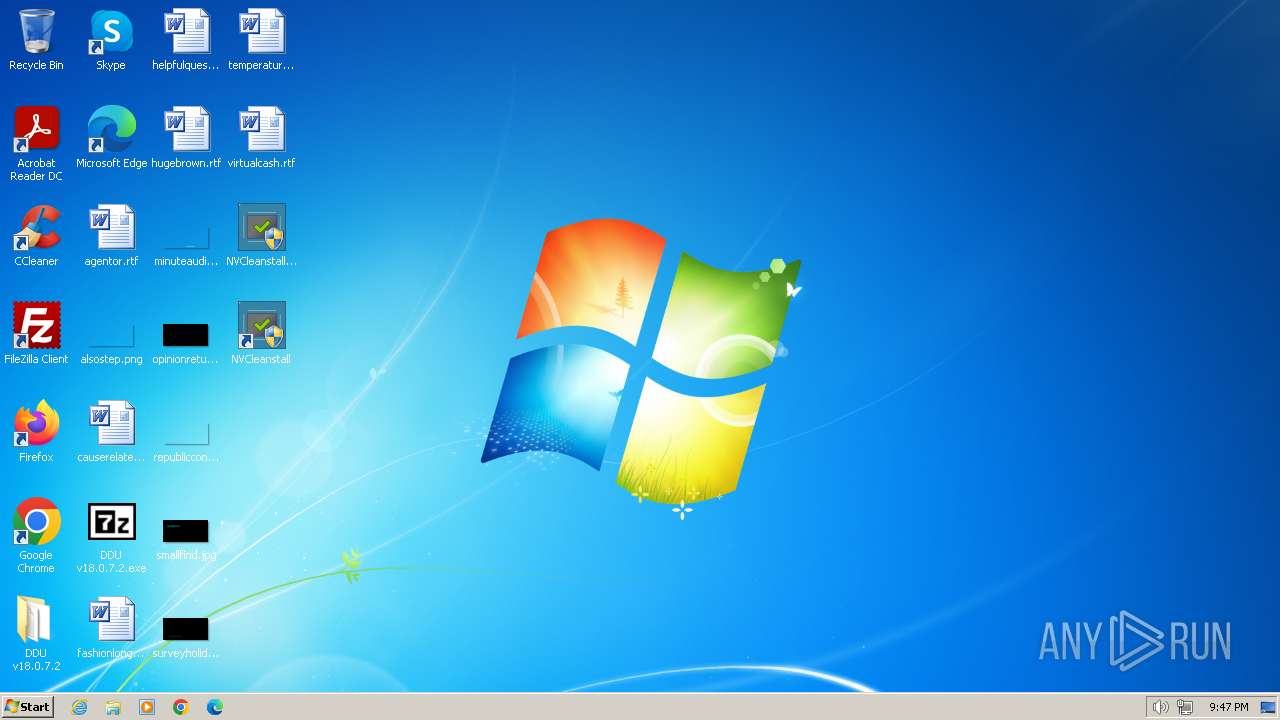
Manual execution by a user
- DDU v18.0.7.2.exe (PID: 3892)
- Display Driver Uninstaller.exe (PID: 3304)
- Display Driver Uninstaller.exe (PID: 3276)
- wmpnscfg.exe (PID: 3636)
- wmpnscfg.exe (PID: 3420)
- IMEKLMG.EXE (PID: 2068)
- IMEKLMG.EXE (PID: 2060)
- wmpnscfg.exe (PID: 2376)
- wmpnscfg.exe (PID: 2396)
- NVCleanstall_1.16.0.exe (PID: 2764)
- NVCleanstall.exe (PID: 3580)
- NVCleanstall.exe (PID: 3692)
- mmc.exe (PID: 2084)
- NVCleanstall_1.16.0.exe (PID: 2652)
- WINWORD.EXE (PID: 3820)
- mmc.exe (PID: 4004)
- rundll32.exe (PID: 2136)
Checks supported languages
- Display Driver Uninstaller.exe (PID: 3276)
- DDU v18.0.7.2.exe (PID: 3892)
- drvinst.exe (PID: 2952)
- Display Driver Uninstaller.exe (PID: 3700)
- wmpnscfg.exe (PID: 3636)
- wmpnscfg.exe (PID: 3420)
- IMEKLMG.EXE (PID: 2060)
- IMEKLMG.EXE (PID: 2068)
- wmpnscfg.exe (PID: 2376)
- NVCleanstall_1.16.0.exe (PID: 2764)
- wmpnscfg.exe (PID: 2396)
- NVCleanstall_Installer.exe (PID: 2892)
- NVCleanstall_Installer.tmp (PID: 2900)
- NVCleanstall.exe (PID: 2924)
- NVCleanstall.exe (PID: 3016)
- NVCleanstall.exe (PID: 3692)
- NVCleanstall_Installer.exe (PID: 3208)
- NVCleanstall_Installer.tmp (PID: 3216)
Reads the machine GUID from the registry
- Display Driver Uninstaller.exe (PID: 3276)
- Display Driver Uninstaller.exe (PID: 3700)
- NVCleanstall_1.16.0.exe (PID: 2764)
- drvinst.exe (PID: 2952)
- NVCleanstall.exe (PID: 2924)
- NVCleanstall.exe (PID: 3016)
- NVCleanstall.exe (PID: 3692)
Reads the computer name
- Display Driver Uninstaller.exe (PID: 3276)
- drvinst.exe (PID: 2952)
- Display Driver Uninstaller.exe (PID: 3700)
- wmpnscfg.exe (PID: 3420)
- wmpnscfg.exe (PID: 3636)
- IMEKLMG.EXE (PID: 2060)
- IMEKLMG.EXE (PID: 2068)
- wmpnscfg.exe (PID: 2376)
- wmpnscfg.exe (PID: 2396)
- NVCleanstall_Installer.tmp (PID: 2900)
- NVCleanstall.exe (PID: 2924)
- NVCleanstall.exe (PID: 3016)
- NVCleanstall.exe (PID: 3692)
- NVCleanstall_Installer.tmp (PID: 3216)
- NVCleanstall_1.16.0.exe (PID: 2764)
Reads Environment values
- Display Driver Uninstaller.exe (PID: 3276)
- NVCleanstall_1.16.0.exe (PID: 2764)
- NVCleanstall.exe (PID: 3016)
- NVCleanstall.exe (PID: 3692)
Process checks whether UAC notifications are on
- IMEKLMG.EXE (PID: 2060)
- IMEKLMG.EXE (PID: 2068)
Reads security settings of Internet Explorer
- sipnotify.exe (PID: 120)
Create files in a temporary directory
- NVCleanstall_1.16.0.exe (PID: 2764)
- NVCleanstall_Installer.exe (PID: 2892)
- NVCleanstall_Installer.tmp (PID: 2900)
- NVCleanstall.exe (PID: 3016)
- NVCleanstall_Installer.exe (PID: 3208)
Creates files in the program directory
- NVCleanstall_Installer.tmp (PID: 2900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
149
Monitored processes
44
Malicious processes
8
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | C:\Windows\system32\sipnotify.exe -LogonOrUnlock | C:\Windows\System32\sipnotify.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: sipnotify Exit code: 0 Version: 6.1.7602.20480 (win7sp1_ldr_escrow.191010-1716) Modules
| |||||||||||||||
| 448 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1196 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3620 --field-trial-handle=1192,i,11523477776586508599,13250136904640288745,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1264 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://www.guru3d.com/getdownload/2c1b2414f56a6594ffef91236a87c0e976d52e0519bd313846bab016c2f20c7c4d6ce7dfe1991cc241d59b5c8cb07e5018b083a5902ac6c67fbe3b852ca022b0f73541638028a2d270eb576309b5208d7642bced763e8806fd9c5a9bca00d71e03e3f895d9924372aebbd01f8d3b8f4f22025884306c24b2230caaa33278d26e6030e42d33f8ae57a577520f01ba2e5ff243d0a889a561ab49c3ea2dd6c91d6ccaf1dfc1e0b09be33209add14c096f4a22ab" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1532 --field-trial-handle=1192,i,11523477776586508599,13250136904640288745,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1384 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\[Guru3D.com]-DDU.zip" | C:\Program Files\WinRAR\WinRAR.exe | chrome.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6bcd8b38,0x6bcd8b48,0x6bcd8b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1176 --field-trial-handle=1192,i,11523477776586508599,13250136904640288745,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1808 | C:\Windows\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1976 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
39 365
Read events
38 805
Write events
404
Delete events
156
Modification events
| (PID) Process: | (1264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (1264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1264) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (1264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
15
Suspicious files
66
Text files
110
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF163472.TMP | — | |
MD5:— | SHA256:— | |||
| 1264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 1264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 1264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1634a1.TMP | text | |
MD5:ADB669AB4CD1C63883C64FB0DBA2C7DA | SHA256:18BFF89047EC5B122573D089B3DC7A7DD14A5A7A515B2D8141584B41E723253F | |||
| 1264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF163482.TMP | text | |
MD5:05CF4C3C5148DA6355D3561A9EAA5E8A | SHA256:8D720243F6876898E4F197C8867C4CEE69F1C7335C55B8A29C120B1028D93E41 | |||
| 1264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RF163e56.TMP | — | |
MD5:— | SHA256:— | |||
| 1264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF163609.TMP | text | |
MD5:C5B082BC8EA6A9BD1DC6782C00A79605 | SHA256:6168A9E585264DE05DEE1B67427B1BC277F1B83B9297184EFACC5D3BB061ABDE | |||
| 1264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:358570F689377CE6838812643E03734B | SHA256:5B41FCC2E1A843AEAB9437B06E27B798870FF10D86A51B163BF48862BCD32590 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
30
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
120 | sipnotify.exe | HEAD | 200 | 23.212.215.38:80 | http://query.prod.cms.rt.microsoft.com/cms/api/am/binary/RE2JgkA?v=133510382753900000 | unknown | — | — | unknown |
2764 | NVCleanstall_1.16.0.exe | GET | 200 | 188.114.97.3:80 | http://gpu.me/v1/message.json | unknown | text | 131 b | unknown |
3016 | NVCleanstall.exe | GET | 200 | 188.114.97.3:80 | http://gpu.me/v1/message.json | unknown | text | 131 b | unknown |
2764 | NVCleanstall_1.16.0.exe | GET | 200 | 188.114.97.3:80 | http://gpu.me/v1/index2.json | unknown | — | 2.36 Mb | unknown |
3692 | NVCleanstall.exe | GET | 200 | 188.114.97.3:80 | http://gpu.me/v1/index2.json | unknown | — | 2.36 Mb | unknown |
3692 | NVCleanstall.exe | GET | 200 | 188.114.97.3:80 | http://gpu.me/v1/message.json | unknown | text | 131 b | unknown |
3016 | NVCleanstall.exe | GET | 200 | 188.114.97.3:80 | http://gpu.me/v1/index2.json | unknown | — | 2.36 Mb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3248 | chrome.exe | 142.250.110.84:443 | accounts.google.com | GOOGLE | US | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1264 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
3248 | chrome.exe | 144.91.87.188:443 | www.guru3d.com | Contabo GmbH | DE | unknown |
3248 | chrome.exe | 145.220.21.40:443 | ftp.nluug.nl | SURF B.V. | NL | unknown |
1264 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
3248 | chrome.exe | 172.217.18.14:443 | sb-ssl.google.com | GOOGLE | US | whitelisted |
3248 | chrome.exe | 172.217.16.132:443 | www.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
www.guru3d.com |
| unknown |
ftp.nluug.nl |
| unknown |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| whitelisted |
www.wagnardsoft.com |
| unknown |
query.prod.cms.rt.microsoft.com |
| whitelisted |
gpu.me |
| unknown |
www.techpowerup.com |
| unknown |