| File name: | asdaada.pdf |
| Full analysis: | https://app.any.run/tasks/17b92012-0635-41be-a7d5-046e9d7fdf5d |
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 17:18:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/pdf |
| File info: | PDF document, version 1.7 |
| MD5: | CE7218134BB58C2C5D92E7EFA9AAD4B7 |
| SHA1: | FF8F207DADC4A4EDB90C07D3BAF8FCD02C22EA76 |
| SHA256: | 3EF1952D25D23A698C6AAFF0CEE873137016D424AC3988A6809EFBDF32058C85 |
| SSDEEP: | 768:wjm0P/TNJu46hZ6tLqwWDdUIxoJ/4PXtHyYtLIg8flET:kmE/T246j6lqwWDdMfq |
MALICIOUS
No malicious indicators.SUSPICIOUS
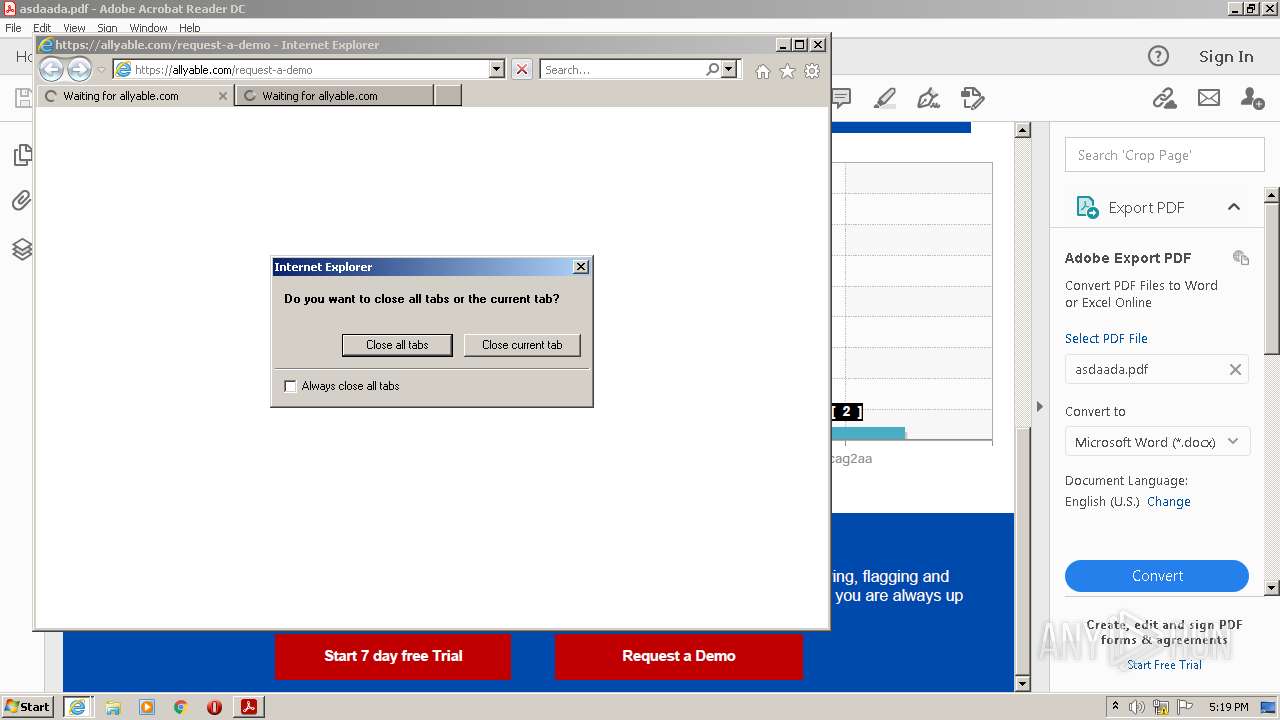
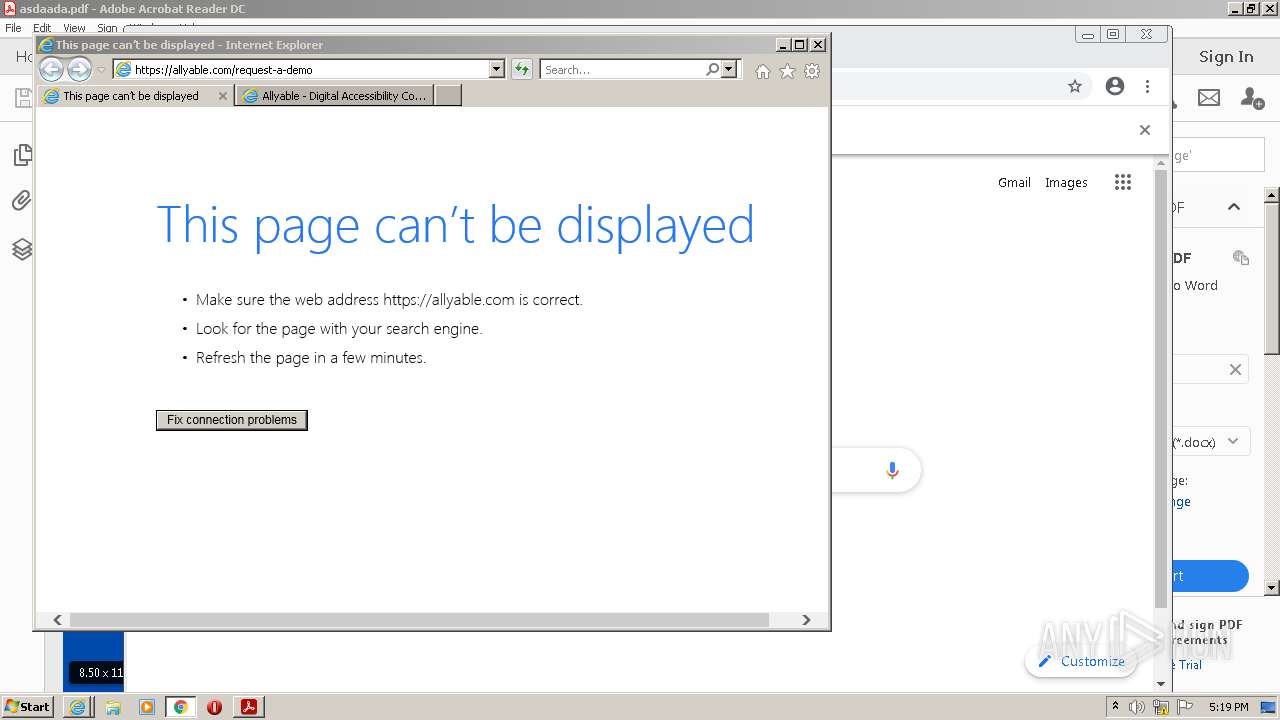
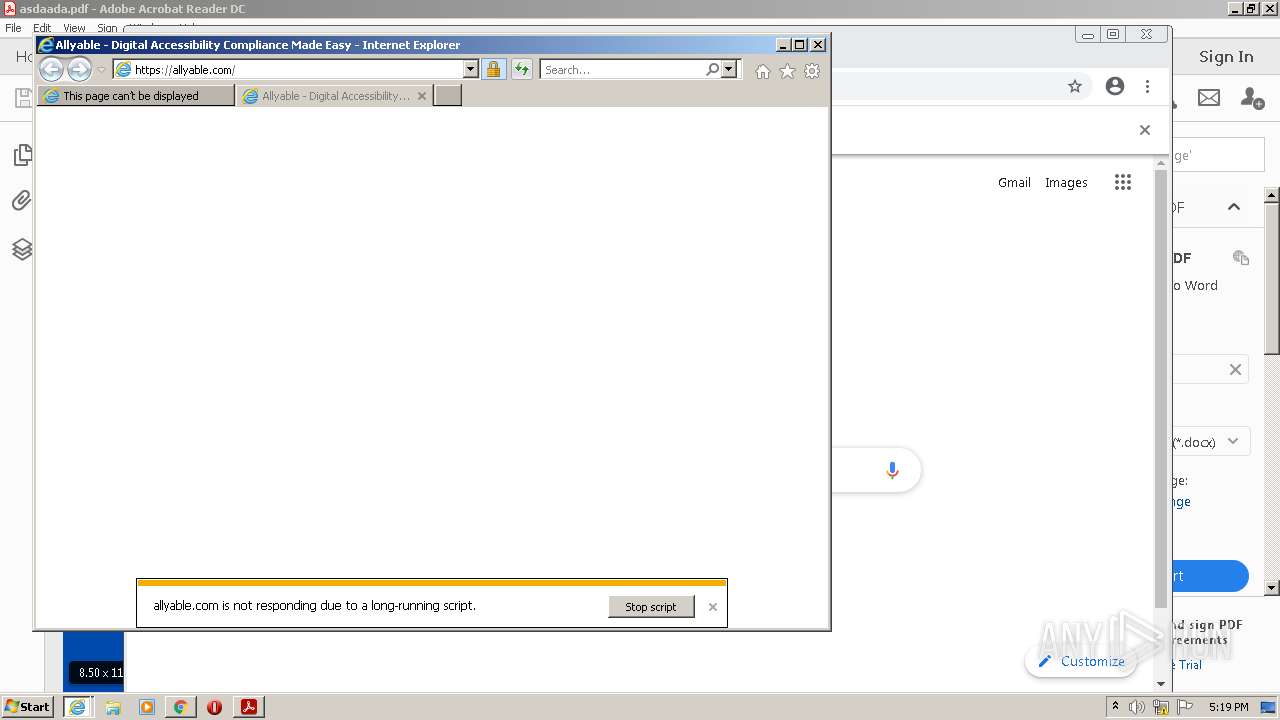
Starts Internet Explorer
- AcroRd32.exe (PID: 1108)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3456)
- iexplore.exe (PID: 756)
Checks supported languages
- AdobeARM.exe (PID: 3704)
- Reader_sl.exe (PID: 908)
Reads the computer name
- AdobeARM.exe (PID: 3704)
Creates files in the program directory
- AdobeARM.exe (PID: 3704)
Executable content was dropped or overwritten
- AdobeARM.exe (PID: 3704)
INFO
Checks supported languages
- AcroRd32.exe (PID: 1108)
- RdrCEF.exe (PID: 1948)
- RdrCEF.exe (PID: 3504)
- RdrCEF.exe (PID: 336)
- RdrCEF.exe (PID: 2464)
- AcroRd32.exe (PID: 3360)
- RdrCEF.exe (PID: 2428)
- RdrCEF.exe (PID: 2960)
- RdrCEF.exe (PID: 2480)
- RdrCEF.exe (PID: 3176)
- iexplore.exe (PID: 3844)
- iexplore.exe (PID: 3456)
- iexplore.exe (PID: 756)
- chrome.exe (PID: 2836)
- chrome.exe (PID: 2008)
- chrome.exe (PID: 916)
- chrome.exe (PID: 376)
- chrome.exe (PID: 2904)
- chrome.exe (PID: 2808)
- chrome.exe (PID: 276)
- chrome.exe (PID: 2752)
- chrome.exe (PID: 2972)
- chrome.exe (PID: 2928)
- chrome.exe (PID: 2232)
- chrome.exe (PID: 3364)
- chrome.exe (PID: 1992)
- chrome.exe (PID: 3416)
- chrome.exe (PID: 1248)
- chrome.exe (PID: 2068)
Reads the computer name
- AcroRd32.exe (PID: 3360)
- RdrCEF.exe (PID: 1948)
- AcroRd32.exe (PID: 1108)
- iexplore.exe (PID: 3844)
- iexplore.exe (PID: 756)
- iexplore.exe (PID: 3456)
- chrome.exe (PID: 2836)
- chrome.exe (PID: 276)
- chrome.exe (PID: 376)
- chrome.exe (PID: 2928)
- chrome.exe (PID: 1248)
Reads CPU info
- AcroRd32.exe (PID: 3360)
Application launched itself
- AcroRd32.exe (PID: 1108)
- RdrCEF.exe (PID: 1948)
- iexplore.exe (PID: 3844)
- chrome.exe (PID: 2836)
Searches for installed software
- AcroRd32.exe (PID: 1108)
- AcroRd32.exe (PID: 3360)
Reads settings of System Certificates
- AcroRd32.exe (PID: 1108)
- RdrCEF.exe (PID: 1948)
- iexplore.exe (PID: 756)
- iexplore.exe (PID: 3844)
- iexplore.exe (PID: 3456)
- chrome.exe (PID: 376)
- AdobeARM.exe (PID: 3704)
Checks Windows Trust Settings
- AcroRd32.exe (PID: 1108)
- iexplore.exe (PID: 3844)
- iexplore.exe (PID: 3456)
- iexplore.exe (PID: 756)
- AdobeARM.exe (PID: 3704)
Reads the hosts file
- RdrCEF.exe (PID: 1948)
- chrome.exe (PID: 2836)
- chrome.exe (PID: 376)
Reads internet explorer settings
- iexplore.exe (PID: 3456)
- iexplore.exe (PID: 756)
Changes internet zones settings
- iexplore.exe (PID: 3844)
Creates files in the user directory
- iexplore.exe (PID: 756)
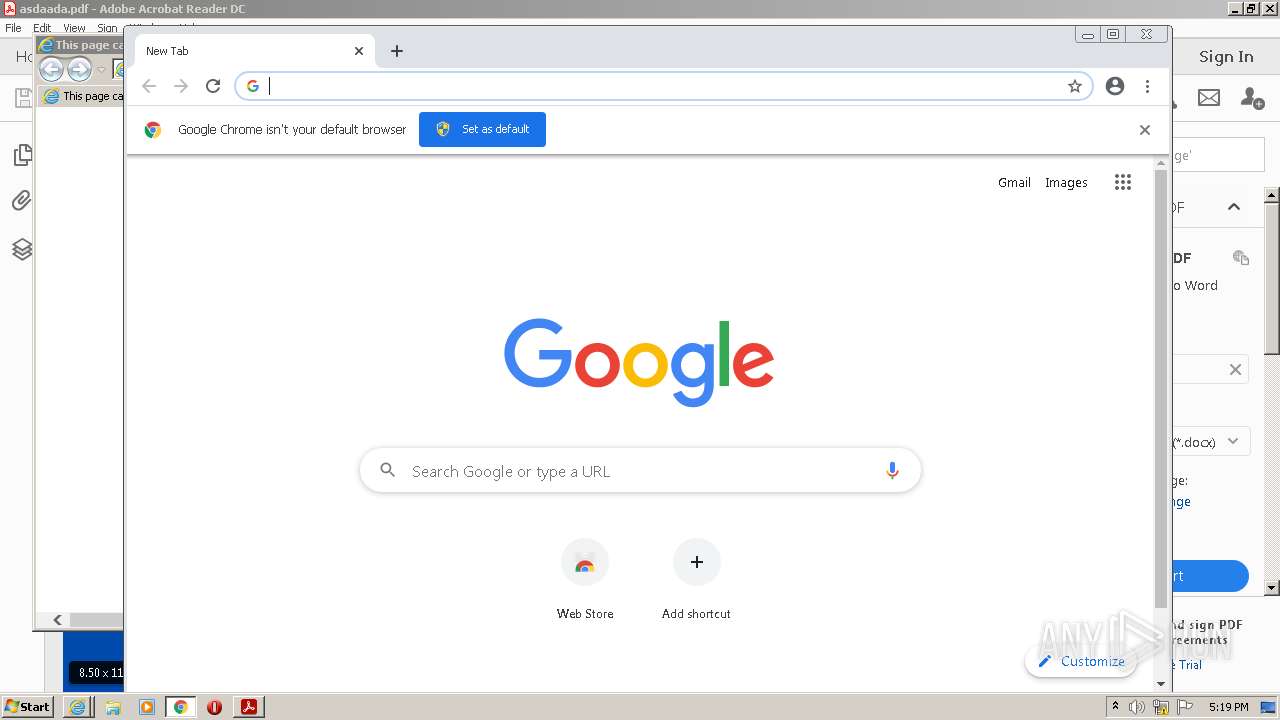
Manual execution by user
- chrome.exe (PID: 2836)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| | | Adobe Portable Document Format (100) |
EXIF
XMP
| Keywords: | - |
|---|---|
| Producer: | Stimulsoft Reports |
| InstanceID: | uuid:08098c45-ee79-20cb-4668-a502b5413366 |
| DocumentID: | uuid:08098c45-ee79-20cb-4668-a502b5413366 |
| Subject: | - |
| Creator: | - |
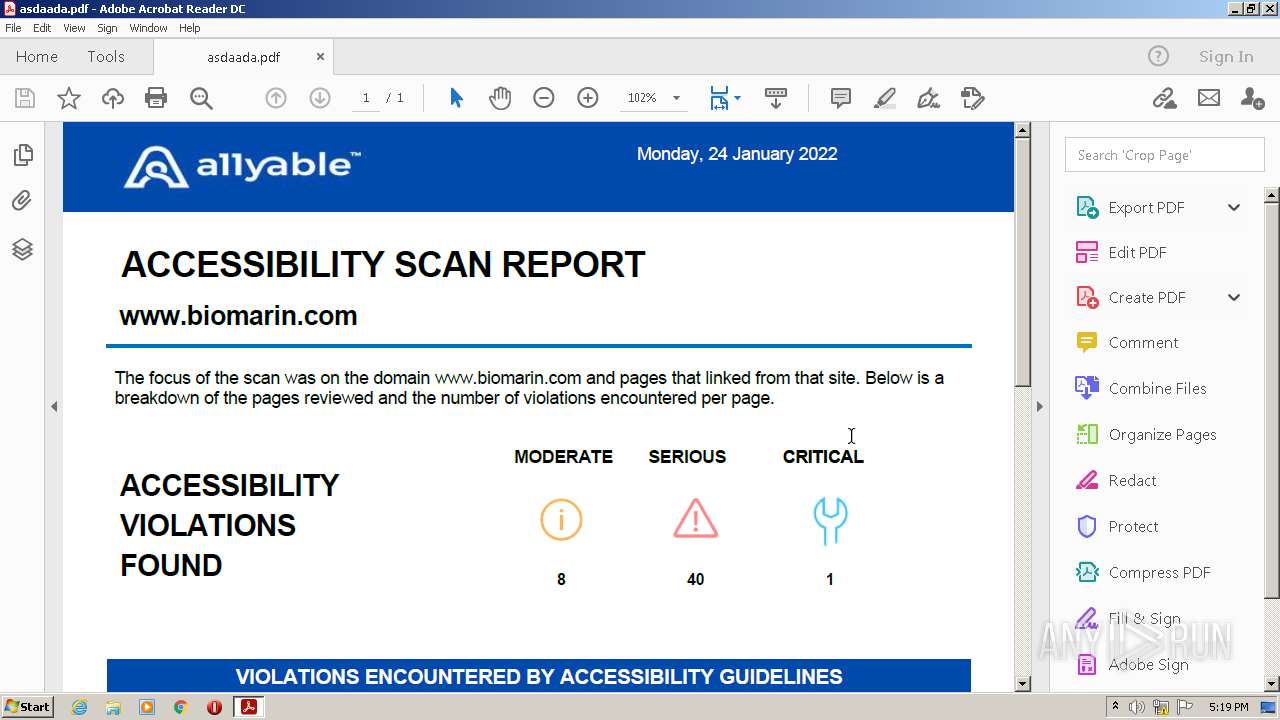
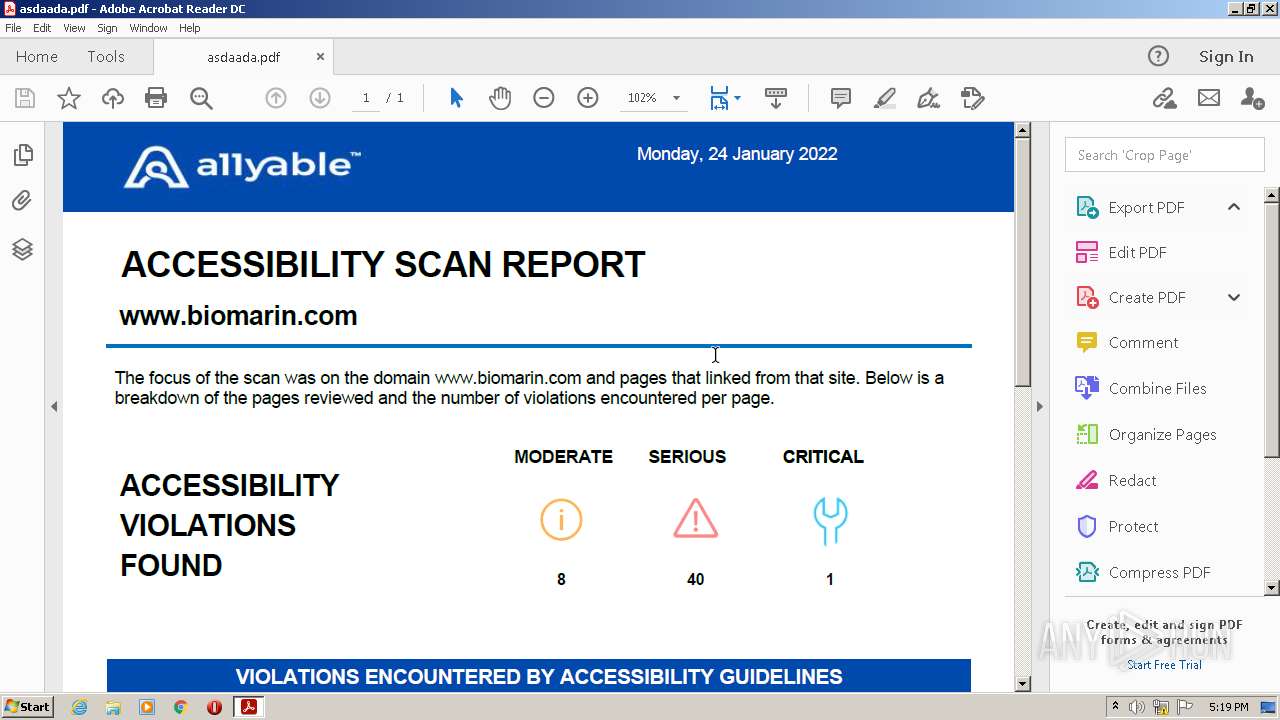
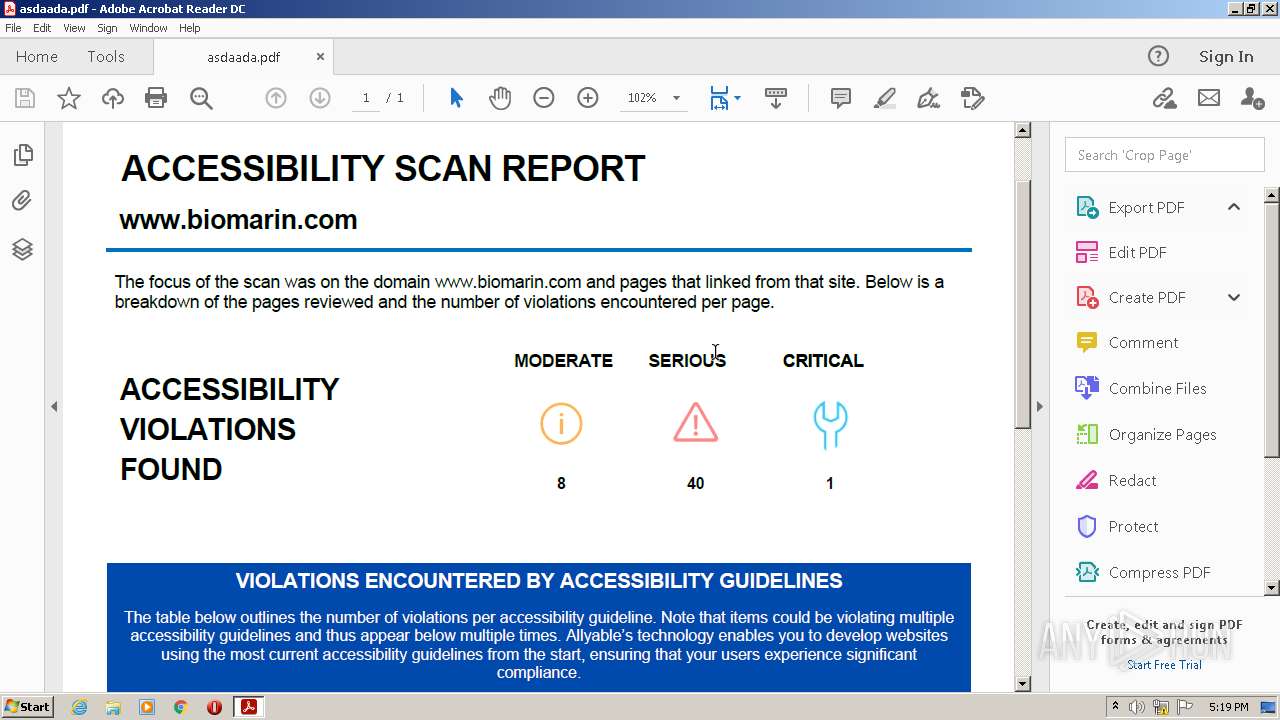
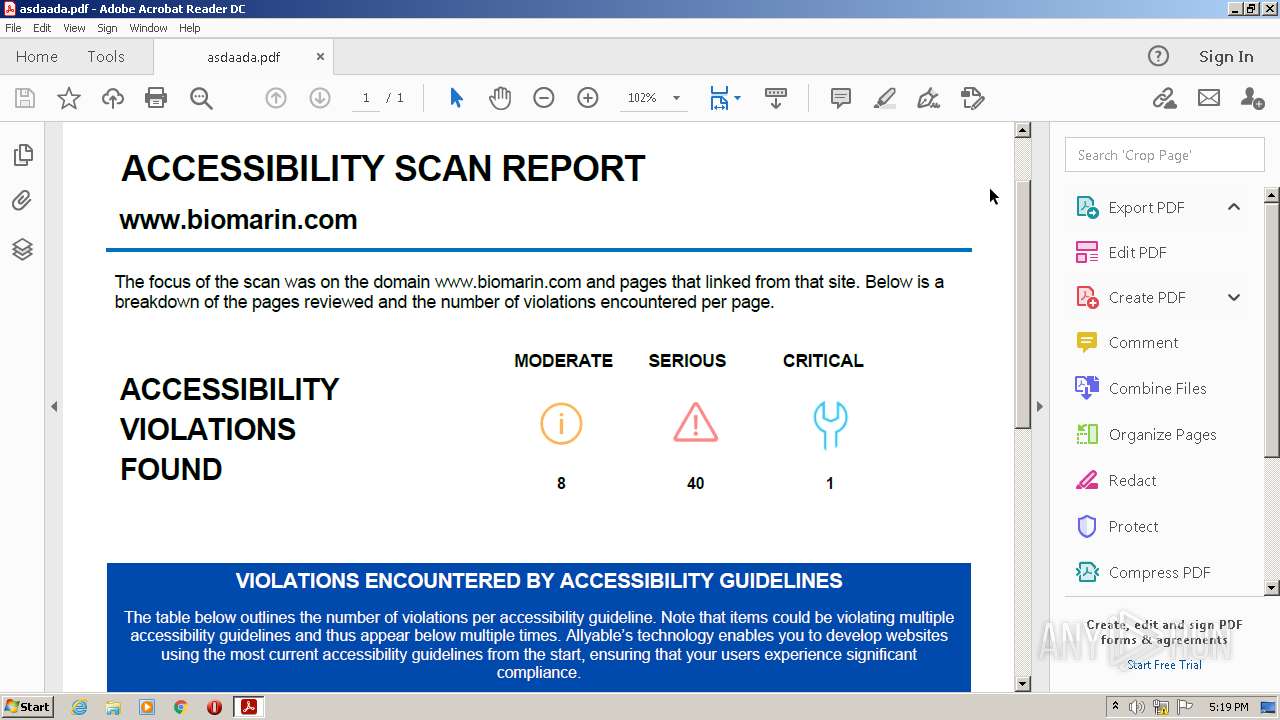
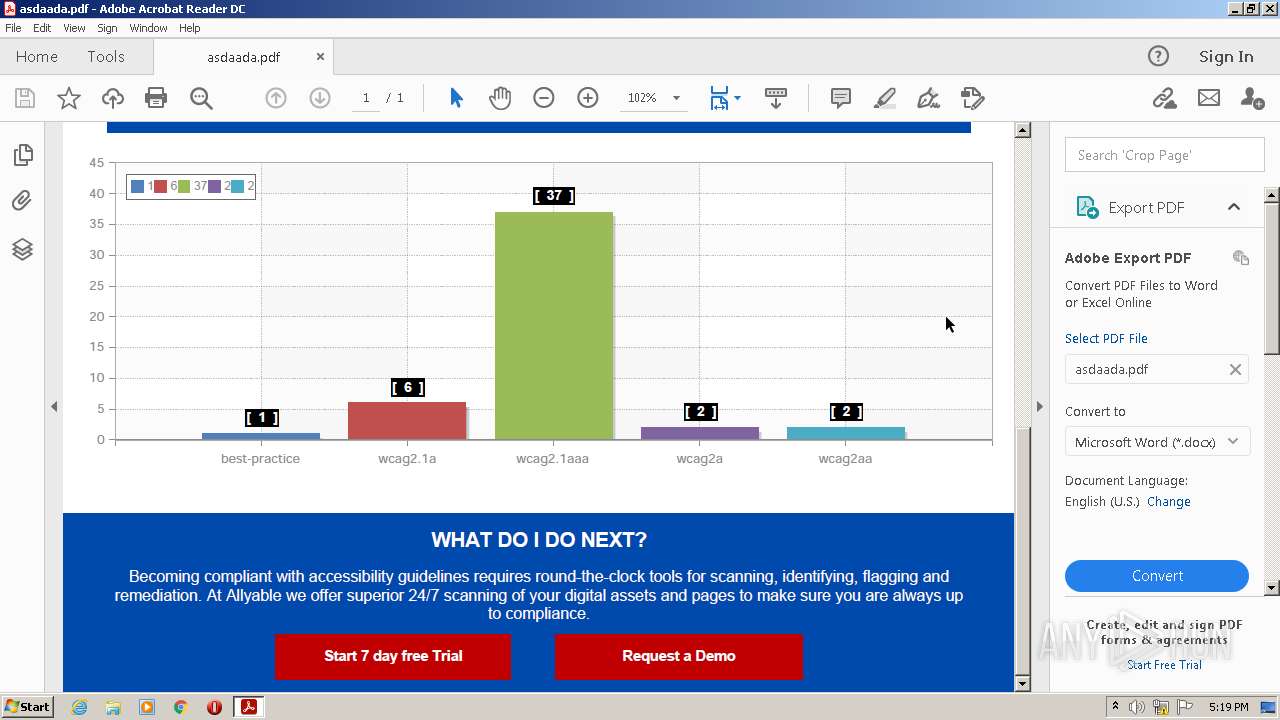
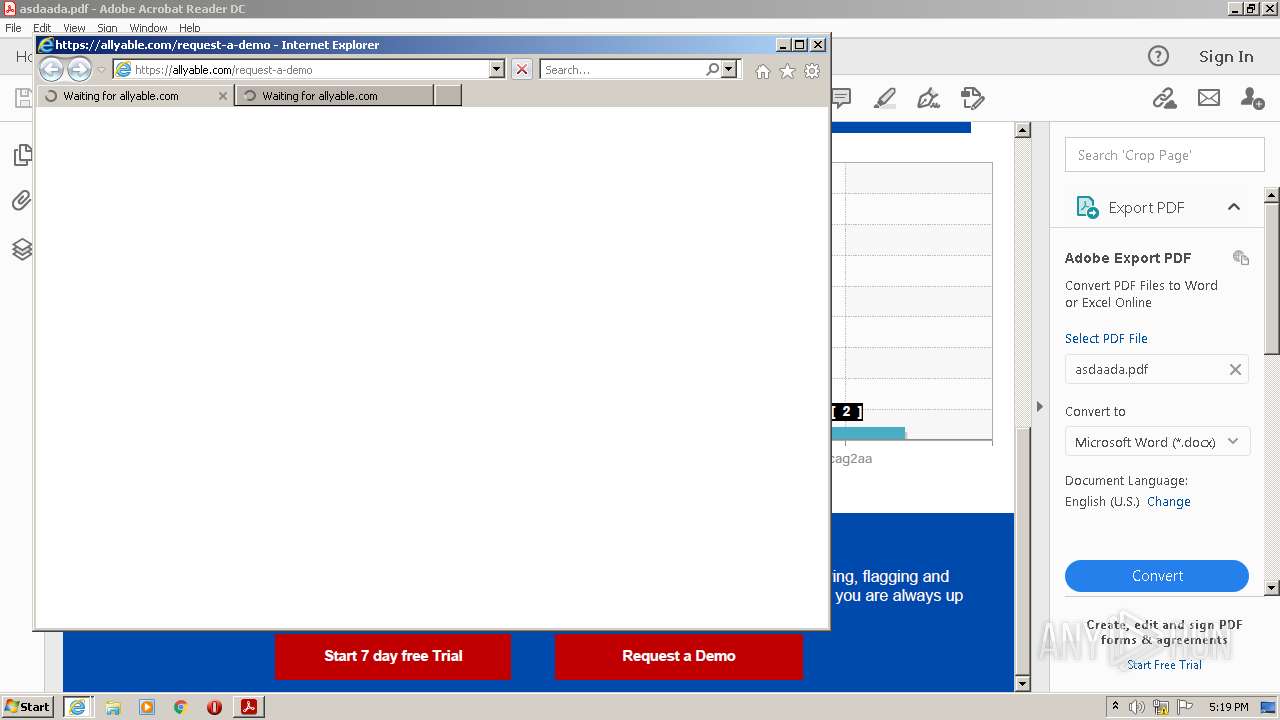
| Description: | Allyable Site Scanner Report |
| Title: | Allyable Site Scanner Report |
| Format: | application/pdf |
| CreatorTool: | Stimulsoft Reports 2020.4.2 from 11 September 2020 |
| MetadataDate: | 2022:01:24 13:56:24+00:00 |
| CreateDate: | 2022:01:24 13:56:24+00:00 |
| ModifyDate: | 2022:01:24 13:56:24+00:00 |
| XMPToolkit: | Adobe XMP Core 4.0-c316 44.253921, Sun Oct 01 2006 17:14:39 |
| ModifyDate: | 2022:01:24 13:56:24+00:00 |
|---|---|
| CreateDate: | 2022:01:24 13:56:24+00:00 |
| Title: | Allyable Site Scanner Report |
| Subject: | Allyable Site Scanner Report |
| Creator: | Stimulsoft Reports 2020.4.2 from 11 September 2020 |
| Producer: | Stimulsoft Reports |
| PageMode: | UseNone |
| TaggedPDF: | Yes |
| PageCount: | 1 |
| Linearized: | No |
| PDFVersion: | 1.7 |
Total processes
66
Monitored processes
31
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1008,11358646846445129763,3158180977379663404,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1028 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 336 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --touch-events=enabled --field-trial-handle=1172,2163605391252318908,16789924796374828868,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-gpu-compositing --lang=en-US --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1976844492038735901 --renderer-client-id=2 --mojo-platform-channel-handle=1180 --allow-no-sandbox-job /prefetch:1 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1008,11358646846445129763,3158180977379663404,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1320 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 756 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3844 CREDAT:201999 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 908 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe | — | AdobeARM.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat SpeedLauncher Exit code: 0 Version: 20.12.20041.394260 Modules
| |||||||||||||||
| 916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,11358646846445129763,3158180977379663404,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2296 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1108 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" "C:\Users\admin\AppData\Local\Temp\asdaada.pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | Explorer.EXE | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1008,11358646846445129763,3158180977379663404,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3284 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1948 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --backgroundcolor=16514043 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | AcroRd32.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 1992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,11358646846445129763,3158180977379663404,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3136 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
49 172
Read events
48 487
Write events
682
Delete events
3
Modification events
| (PID) Process: | (3360) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\ExitSection |
| Operation: | write | Name: | bLastExitNormal |
Value: 0 | |||
| (PID) Process: | (3360) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral |
| Operation: | write | Name: | iNumReaderLaunches |
Value: 2 | |||
| (PID) Process: | (3360) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\FTEDialog |
| Operation: | write | Name: | bShowUpdateFTE |
Value: 1 | |||
| (PID) Process: | (3360) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\HomeWelcome |
| Operation: | write | Name: | bIsAcrobatUpdated |
Value: 1 | |||
| (PID) Process: | (3360) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\HomeWelcomeFirstMileReader |
| Operation: | write | Name: | iCardCountShown |
Value: 2 | |||
| (PID) Process: | (3360) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\FTEDialog |
| Operation: | delete value | Name: | iLastCardShown |
Value: 0 | |||
| (PID) Process: | (1108) AcroRd32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3360) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\SessionManagement |
| Operation: | write | Name: | bNormalExit |
Value: 0 | |||
| (PID) Process: | (3360) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\SessionManagement\cWindowsCurrent\cWin0 |
| Operation: | write | Name: | iTabCount |
Value: 0 | |||
| (PID) Process: | (3360) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\SessionManagement\cWindowsCurrent |
| Operation: | write | Name: | iWinCount |
Value: 1 | |||
Executable files
1
Suspicious files
258
Text files
246
Unknown types
85
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1948 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\983b7a3da8f39a46_0 | binary | |
MD5:— | SHA256:— | |||
| 1948 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\86b8040b7132b608_0 | binary | |
MD5:— | SHA256:— | |||
| 1948 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\0786087c3c360803_0 | binary | |
MD5:— | SHA256:— | |||
| 1948 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\bba29d2e6197e2f4_0 | binary | |
MD5:— | SHA256:— | |||
| 1948 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\8e417e79df3bf0e9_0 | binary | |
MD5:— | SHA256:— | |||
| 1948 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\4a0e94571d979b3c_0 | binary | |
MD5:— | SHA256:— | |||
| 1948 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\fd17b2d8331c91e8_0 | binary | |
MD5:— | SHA256:— | |||
| 1948 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\72d9f526d2e2e7c8_0 | binary | |
MD5:— | SHA256:— | |||
| 1948 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\8c84d92a9dbce3e0_0 | binary | |
MD5:— | SHA256:— | |||
| 1948 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\946896ee27df7947_0 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
198
DNS requests
101
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
756 | iexplore.exe | GET | — | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQC04WHG3wyS9QoAAAABK3x8 | US | — | — | whitelisted |
756 | iexplore.exe | GET | 200 | 104.18.31.182:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEGfe9D7xe9riT%2FWUBgbSwIQ%3D | US | der | 471 b | whitelisted |
756 | iexplore.exe | GET | 200 | 104.18.31.182:80 | http://ocsp.comodoca.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCEQDwHUvue3yjezwFZqwFlyRY | US | der | 728 b | whitelisted |
756 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
756 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQC04WHG3wyS9QoAAAABK3x8 | US | der | 472 b | whitelisted |
3844 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
1108 | AcroRd32.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertGlobalRootCA.crl | US | der | 631 b | whitelisted |
756 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
756 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCrvyQ4GllugQoAAAABK4Az | US | der | 472 b | whitelisted |
756 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1948 | RdrCEF.exe | 184.30.20.134:443 | armmf.adobe.com | GTT Communications Inc. | US | suspicious |
1948 | RdrCEF.exe | 72.247.224.199:443 | geo2.adobe.com | Akamai Technologies, Inc. | US | whitelisted |
1108 | AcroRd32.exe | 23.32.238.178:80 | ctldl.windowsupdate.com | XO Communications | US | suspicious |
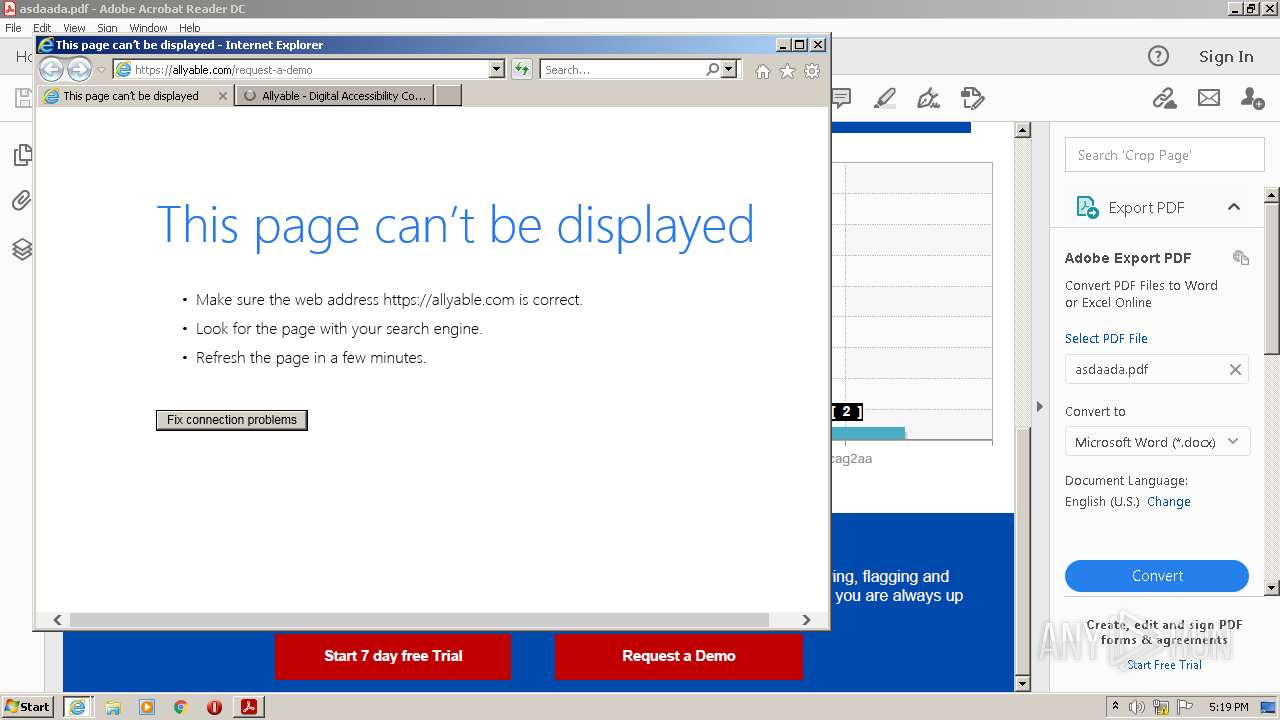
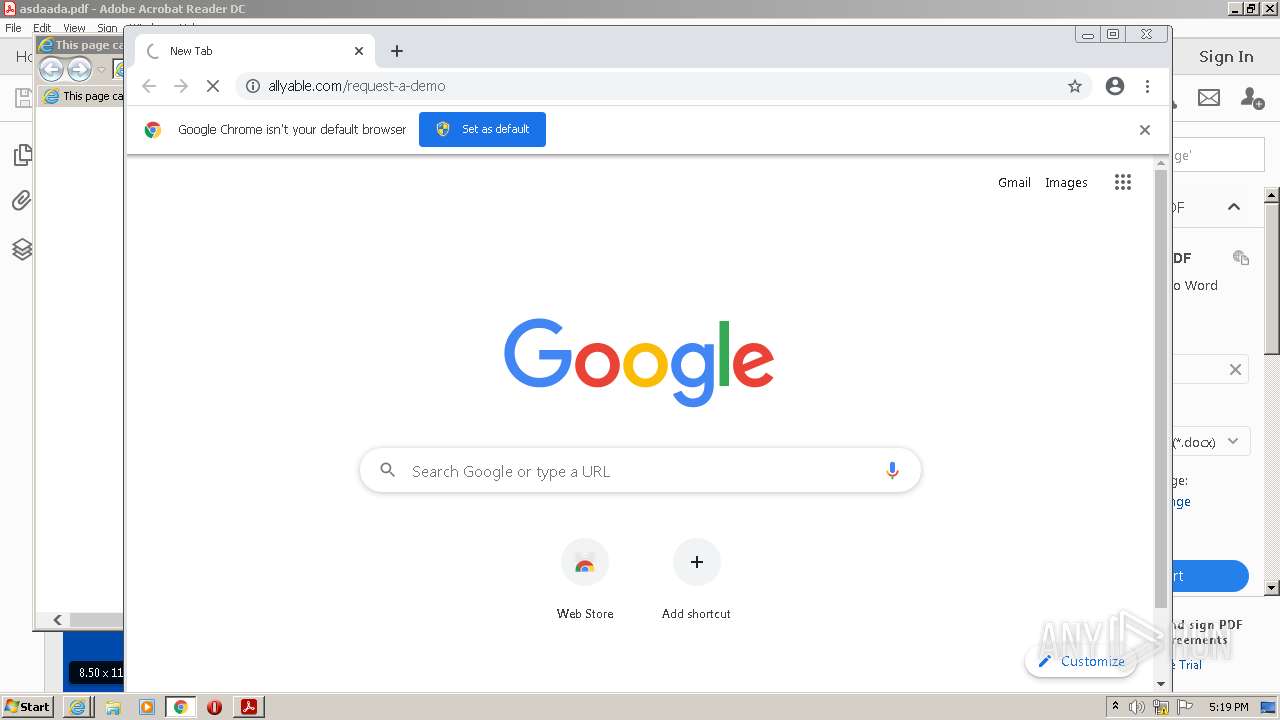
3456 | iexplore.exe | 40.123.39.40:443 | allyable.com | Microsoft Corporation | US | unknown |
756 | iexplore.exe | 40.123.39.40:443 | allyable.com | Microsoft Corporation | US | unknown |
1108 | AcroRd32.exe | 23.32.238.131:443 | acroipm2.adobe.com | XO Communications | US | suspicious |
1108 | AcroRd32.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3844 | iexplore.exe | 13.107.22.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
756 | iexplore.exe | 104.18.31.182:80 | ocsp.comodoca.com | Cloudflare Inc | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
geo2.adobe.com |
| whitelisted |
p13n.adobe.io |
| whitelisted |
armmf.adobe.com |
| whitelisted |
acroipm2.adobe.com |
| whitelisted |
allyable.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
860 | svchost.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |