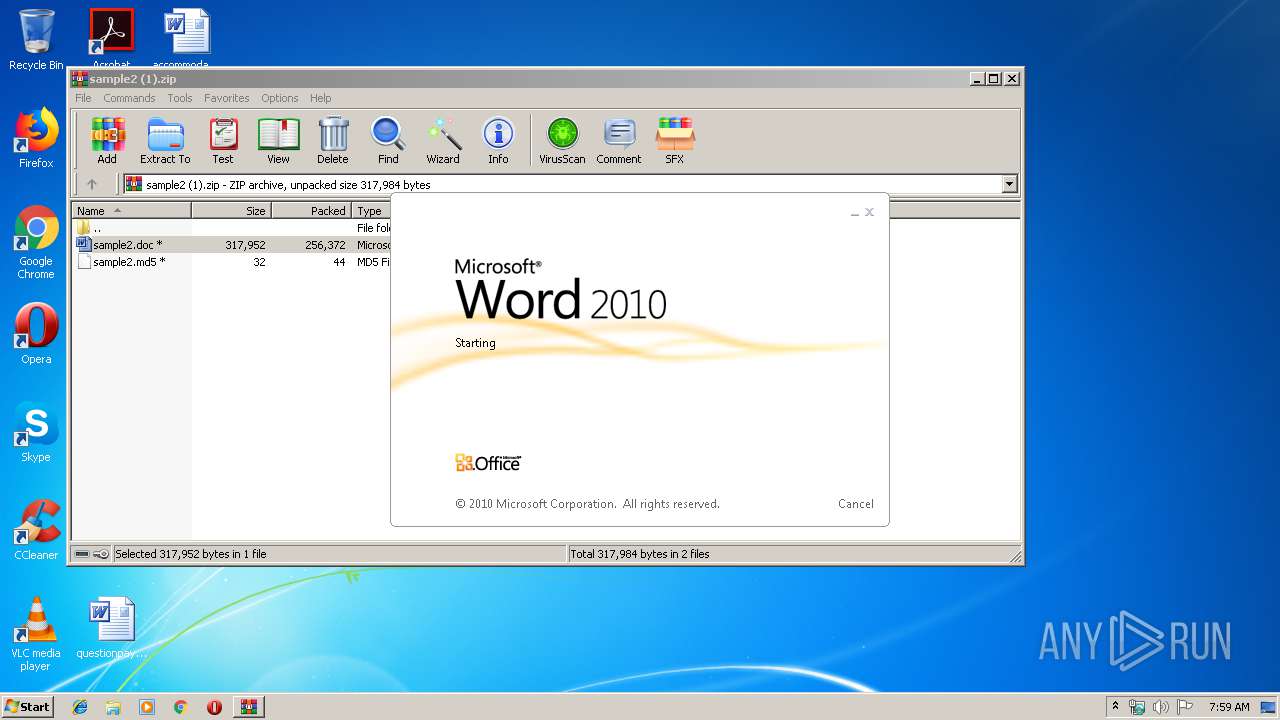
| File name: | sample2 (1).zip |
| Full analysis: | https://app.any.run/tasks/75b45588-64ae-47b2-ac98-7302a4c90ca5 |
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2019, 06:59:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 5F9528D0C9B23469E11C53FB23B1DC2C |
| SHA1: | 6C2CFC368B5FE8B8BC7360DE2AE1D2A59DBD6635 |
| SHA256: | 3EE06373A9379930A4C76E6E0DCDC4A53BB71B79272C252CD5478A9A3DD4F95F |
| SSDEEP: | 6144:RR0nDBq9NL9hIiC0n9WIrwtjwnj48M1aICiBdC:RR0ONLfC09pUto48AaYBdC |
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3128)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3756)
- cmd.exe (PID: 4052)
- cmd.exe (PID: 352)
- cmd.exe (PID: 3008)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3128)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2744)
- schtasks.exe (PID: 2304)
- schtasks.exe (PID: 2704)
- schtasks.exe (PID: 3224)
Executes PowerShell scripts
- cmd.exe (PID: 2592)
SUSPICIOUS
Starts Microsoft Office Application
- WinRAR.exe (PID: 2820)
Creates files in the user directory
- cmd.exe (PID: 3688)
- powershell.exe (PID: 3292)
Executed via Task Scheduler
- wscript.EXE (PID: 3480)
Starts CMD.EXE for commands execution
- wscript.EXE (PID: 3480)
- powershell.exe (PID: 3292)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3128)
Creates files in the user directory
- WINWORD.EXE (PID: 3128)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
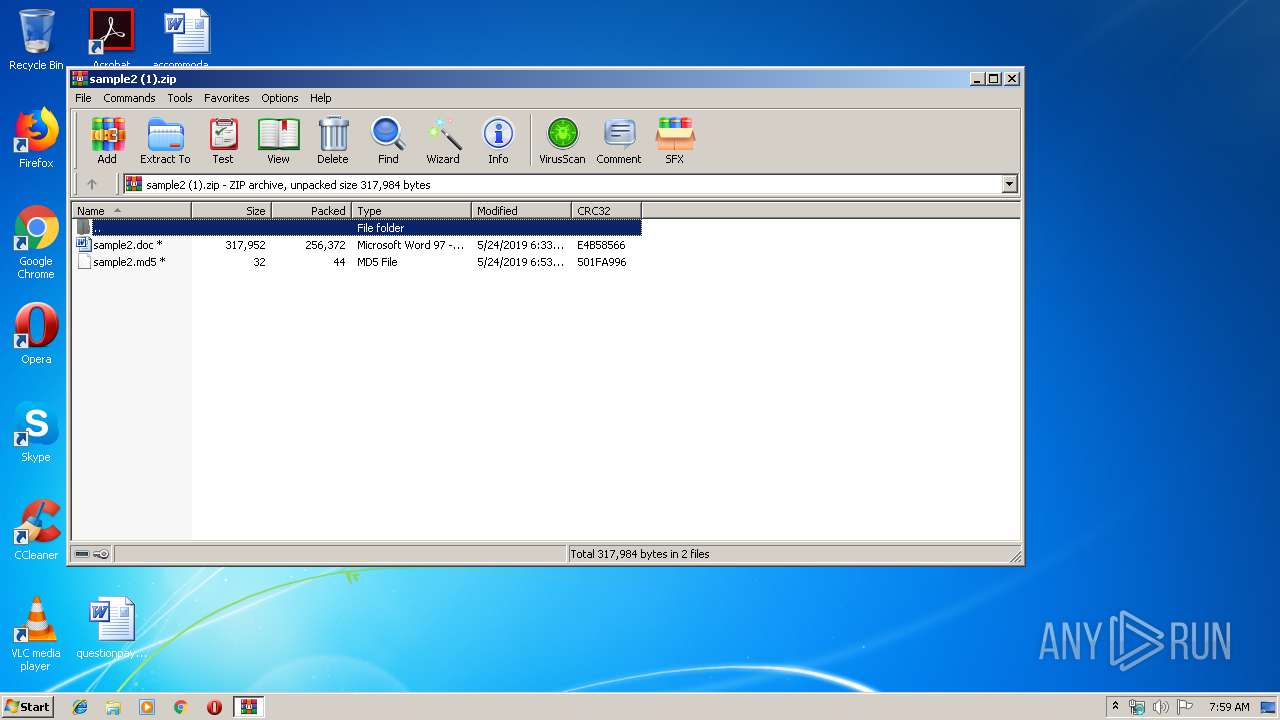
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:05:24 11:03:24 |
| ZipCRC: | 0xe4b58566 |
| ZipCompressedSize: | 256372 |
| ZipUncompressedSize: | 317952 |
| ZipFileName: | sample2.doc |
Total processes
49
Monitored processes
15
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | "C:\Windows\system32\cmd.exe" /c start /b schtasks /query /fo csv | C:\Windows\system32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2304 | schtasks /delete /tn Conhost /f | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2532 | "C:\Windows\system32\findstr.exe" AdobeAcrobatLicenseVerify | C:\Windows\system32\findstr.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2592 | "C:\Windows\System32\cmd.exe" /c Powershell -exec bypass -Windowstyle hidden -File C:\Users\admin\AppData\Roaming\AdobeAcrobatLicenseVerify.ps1 | C:\Windows\System32\cmd.exe | — | wscript.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2704 | schtasks /query /fo csv | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2744 | SchTasks /Create /SC MINUTE /MO 1 /TN "Conhost" /TR "wscript C:\Users\admin\AppData\Roaming\AdobeAcrobatLicenseVerify.vbs" | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
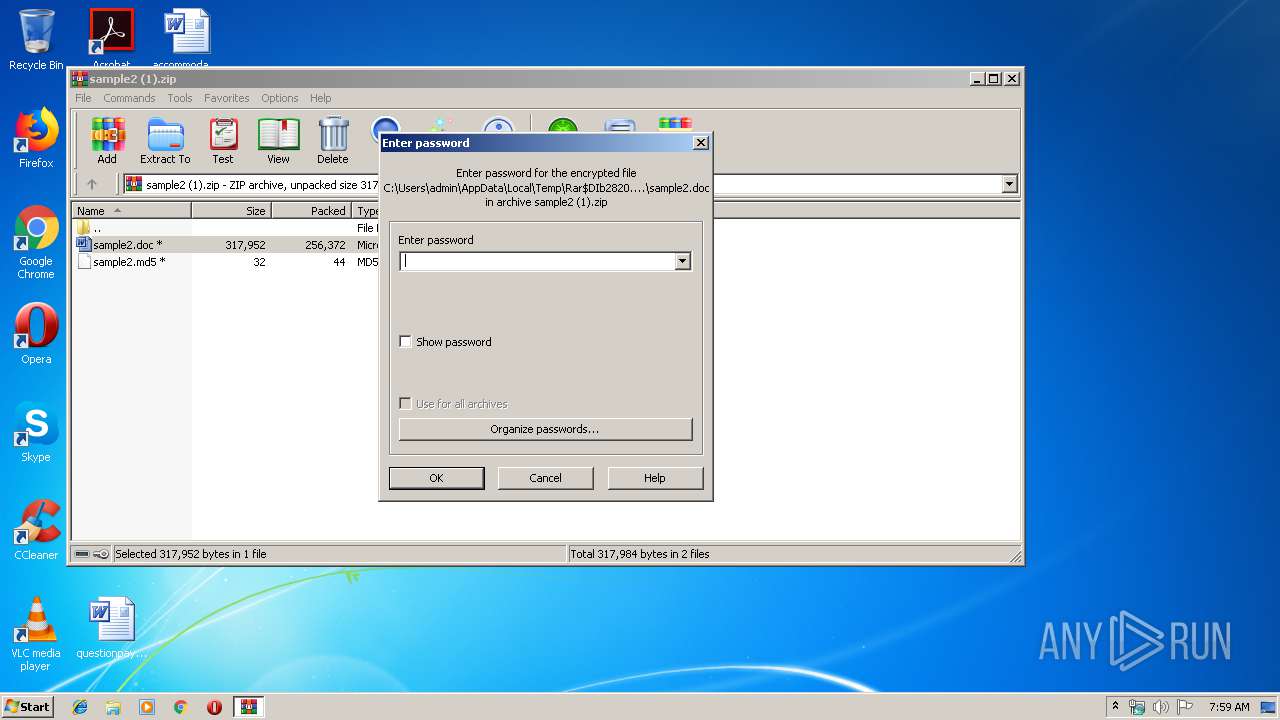
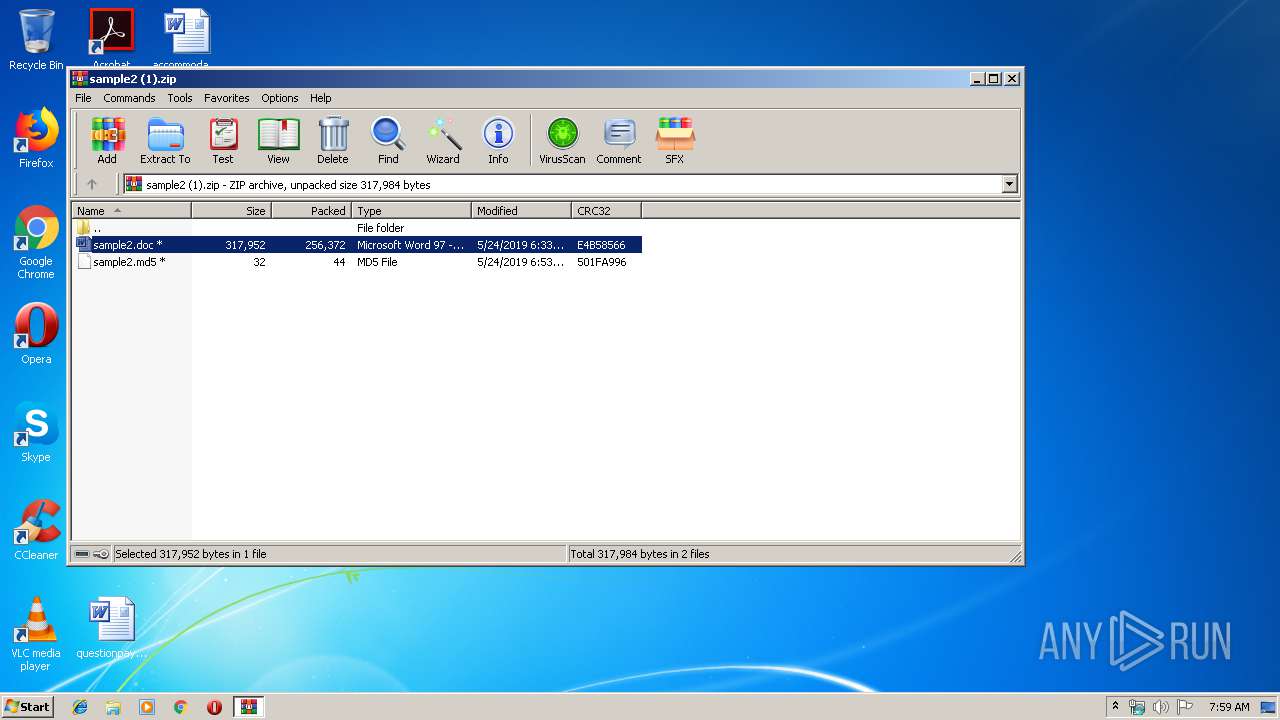
| 2820 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\sample2 (1).zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3008 | "C:\Windows\system32\cmd.exe" /c start /b schtasks /create /sc minute /mo 5 /tn AdobeAcrobatLicenseVerify /tr "wscript.exe "C:\Users\admin\AppData\Local\Temp\AdobeAcrobatLicenseVerify.vbs" \"powershell.exe -ExecutionPolicy bypass -WindowStyle hidden -NoProfile 'C:\Users\admin\AppData\Roaming\AdobeAcrobatLicenseVerify.ps1' \"" | C:\Windows\system32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3128 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb2820.17822\sample2.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3224 | schtasks /create /sc minute /mo 5 /tn AdobeAcrobatLicenseVerify /tr "wscript.exe "C:\Users\admin\AppData\Local\Temp\AdobeAcrobatLicenseVerify.vbs" \"powershell.exe -ExecutionPolicy bypass -WindowStyle hidden -NoProfile 'C:\Users\admin\AppData\Roaming\AdobeAcrobatLicenseVerify.ps1' \"" | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 859
Read events
1 449
Write events
405
Delete events
5
Modification events
| (PID) Process: | (2820) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2820) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2820) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2820) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\sample2 (1).zip | |||
| (PID) Process: | (2820) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2820) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2820) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2820) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2820) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2820) WinRAR.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1320681502 | |||
Executable files
0
Suspicious files
3
Text files
3
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3128 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR2034.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3292 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\1BF5D6YL2GXIOGK7V5S9.temp | — | |
MD5:— | SHA256:— | |||
| 3128 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Rar$DIb2820.17822\~$ample2.doc | pgc | |
MD5:— | SHA256:— | |||
| 3292 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3292 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF155f5f.TMP | binary | |
MD5:— | SHA256:— | |||
| 3128 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3292 | powershell.exe | C:\Users\admin\AppData\Local\Temp\AdobeAcrobatLicenseVerify.vbs | text | |
MD5:05609DE5C12BF51D325C0CC5E438CFC8 | SHA256:C2A7EA6D1EBB5822D07CF27F6DA4DEF3DF6968F50B4777321724903E527129A2 | |||
| 3128 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\AdobeAcrobatLicenseVerify.ps1 | text | |
MD5:93B79FEA62A774DD781E3278CDDAE898 | SHA256:322C502CBE74FA99FA1F162CC6AC6CE1D9594945E68584DC326D39298589B328 | |||
| 2820 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb2820.17822\sample2.doc | document | |
MD5:486BDF835A453C6FFB5F56647E697871 | SHA256:1F6369B42A76D02F32558912B57EDE4F5FF0A90B18D3B96A4FE24120FA2C300C | |||
| 3688 | cmd.exe | C:\Users\admin\AppData\Roaming\AdobeAcrobatLicenseVerify.vbs | text | |
MD5:BA2B36EC76F13B0B6CC3B263EF9D3026 | SHA256:B7DFDBC89FABF327F9A6AAEB233030B04A7AF202CC72559BD9BEE39A98ADFD4C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3292 | powershell.exe | GET | 200 | 204.11.56.48:80 | http://www.acrobatverify.com/ | VG | html | 738 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3292 | powershell.exe | 204.11.56.48:443 | www.acrobatverify.com | Confluence Networks Inc | VG | malicious |
3292 | powershell.exe | 204.11.56.48:80 | www.acrobatverify.com | Confluence Networks Inc | VG | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.acrobatverify.com |
| malicious |