| File name: | AppMarket.exe |
| Full analysis: | https://app.any.run/tasks/a532869c-264e-48c3-bc55-80af942d0fe7 |
| Verdict: | No threats detected |
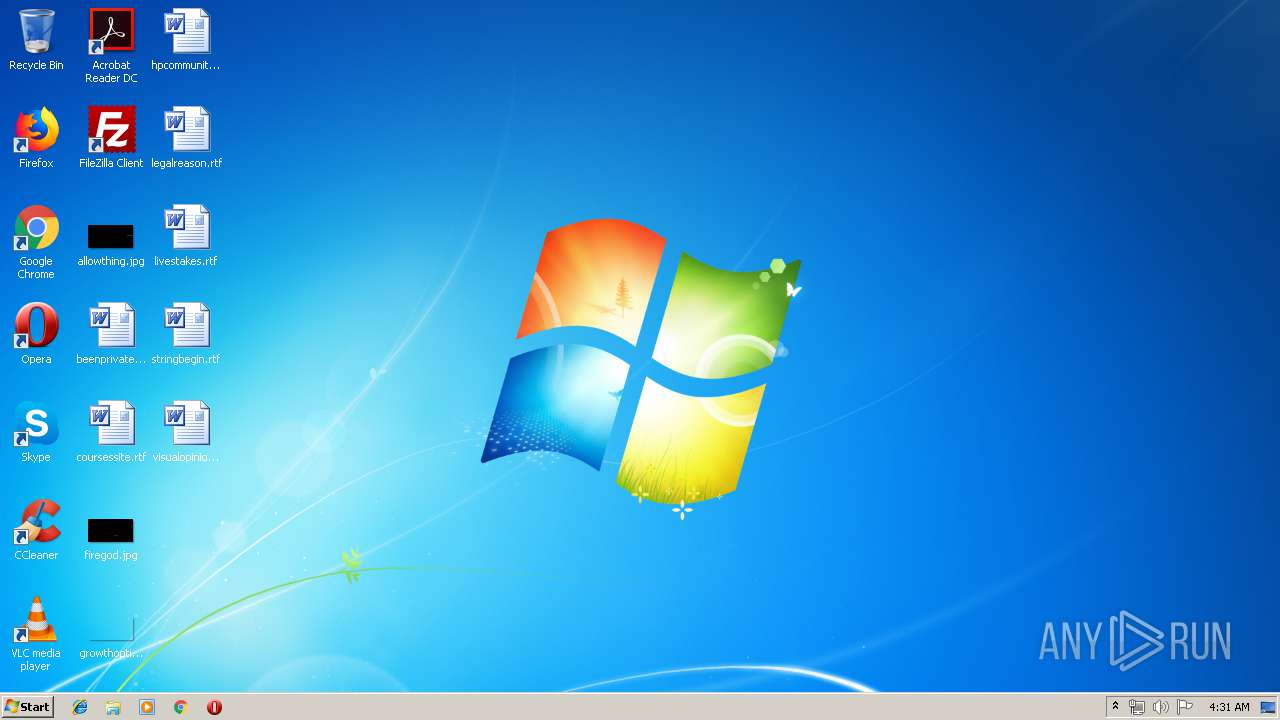
| Analysis date: | August 06, 2019, 03:31:34 |
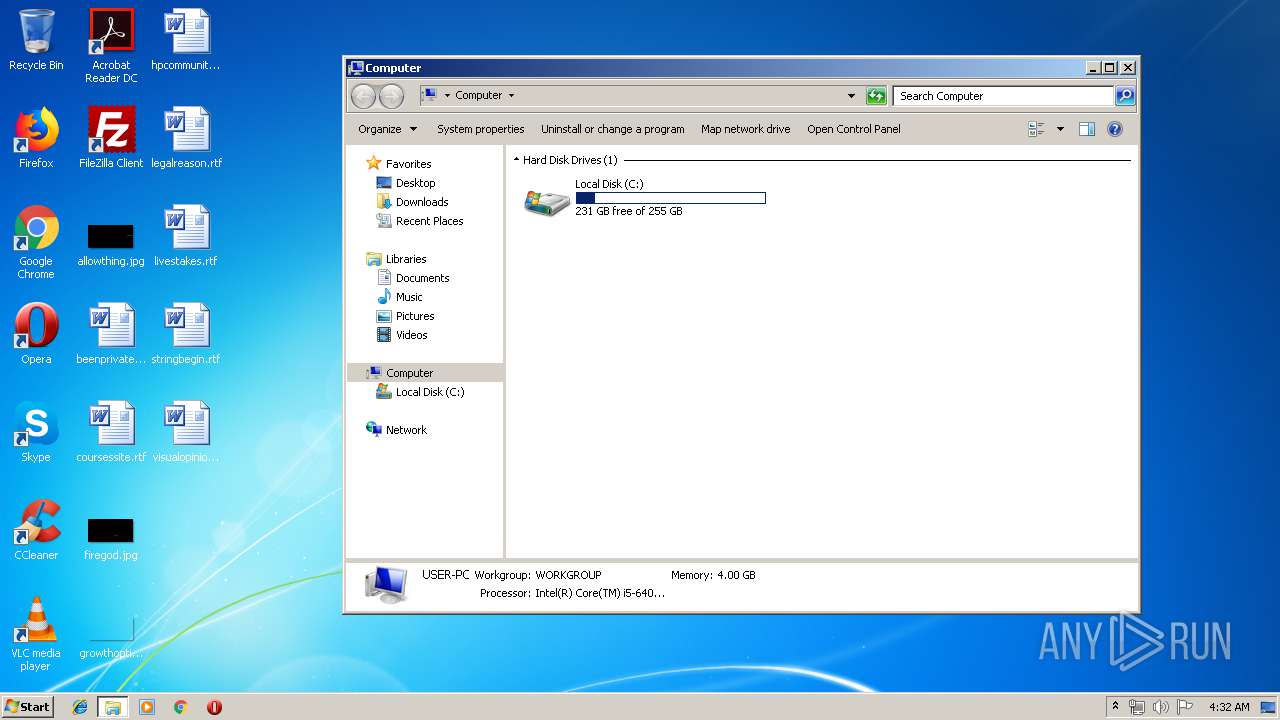
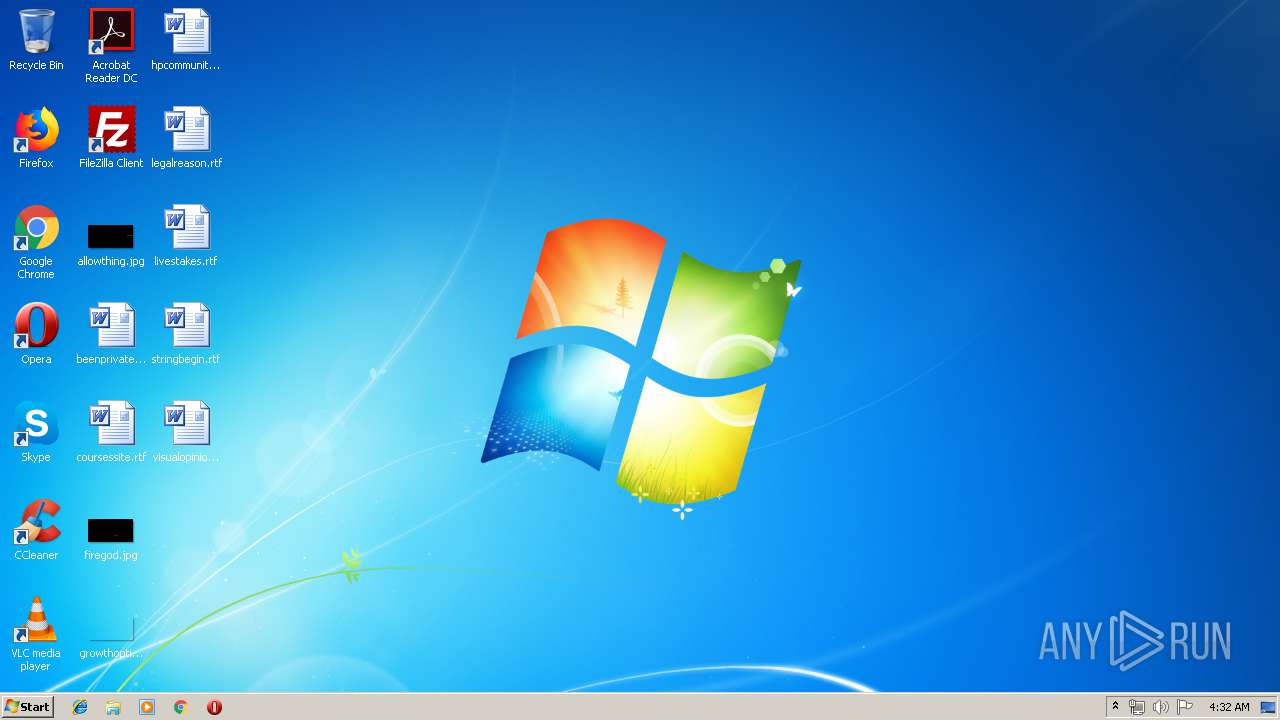
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 5717CFBD4EEDB14B7108D16BE2C2E578 |
| SHA1: | 5ADFE4EDB1190114D7B2F8212D091C400A71C16E |
| SHA256: | 3ED02EA8849F08F06BAC274CF2714EF32CDA19E5999FDB96891221143BD1B328 |
| SSDEEP: | 49152:GdkB6KfbX10WS8X6mPRaAbrWSsSpFUoGXDGW3WMFTLdlecfk/KIXuRm:G2JfbV7TZaAeSsSpuobW3lFTRlecc/ |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
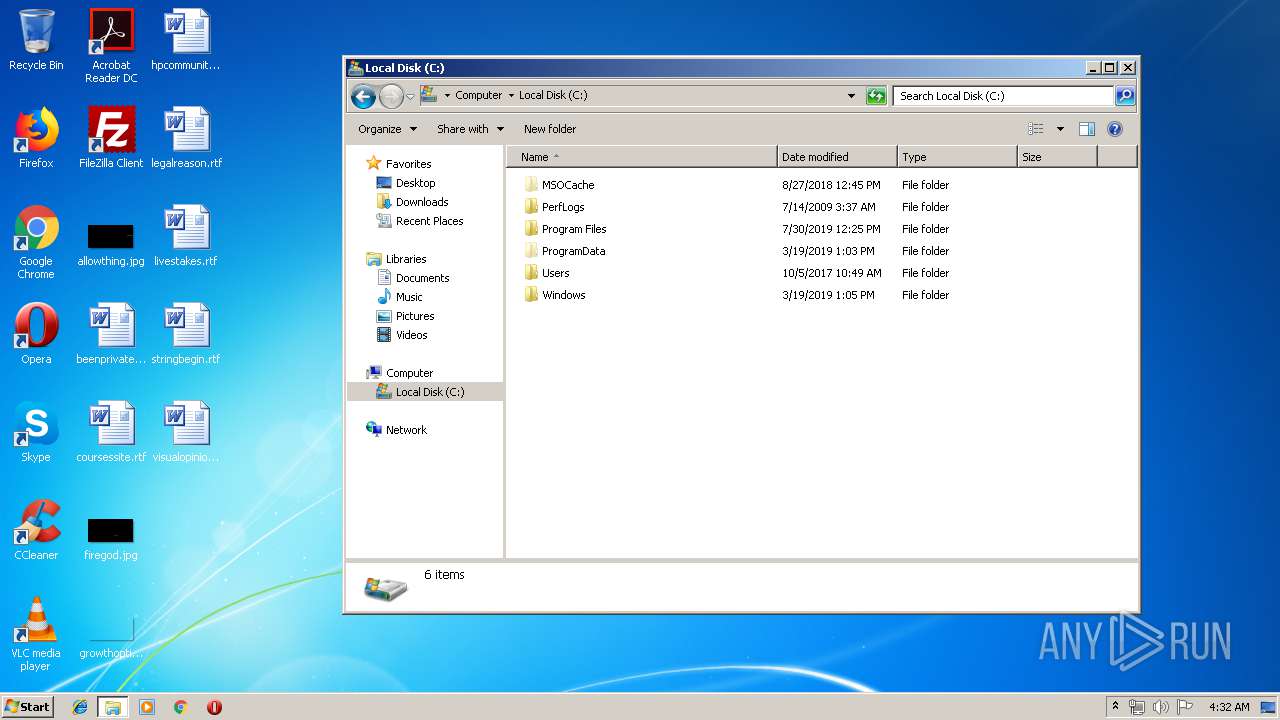
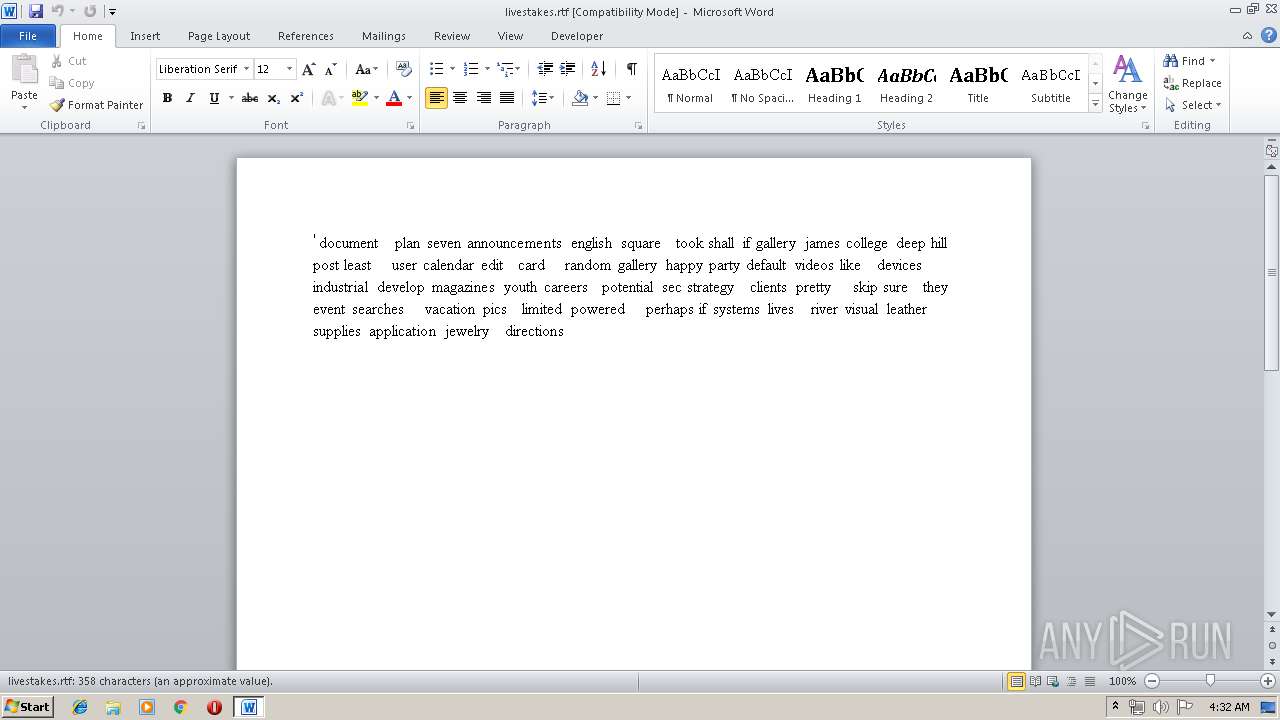
Creates files in the user directory
- WINWORD.EXE (PID: 2812)
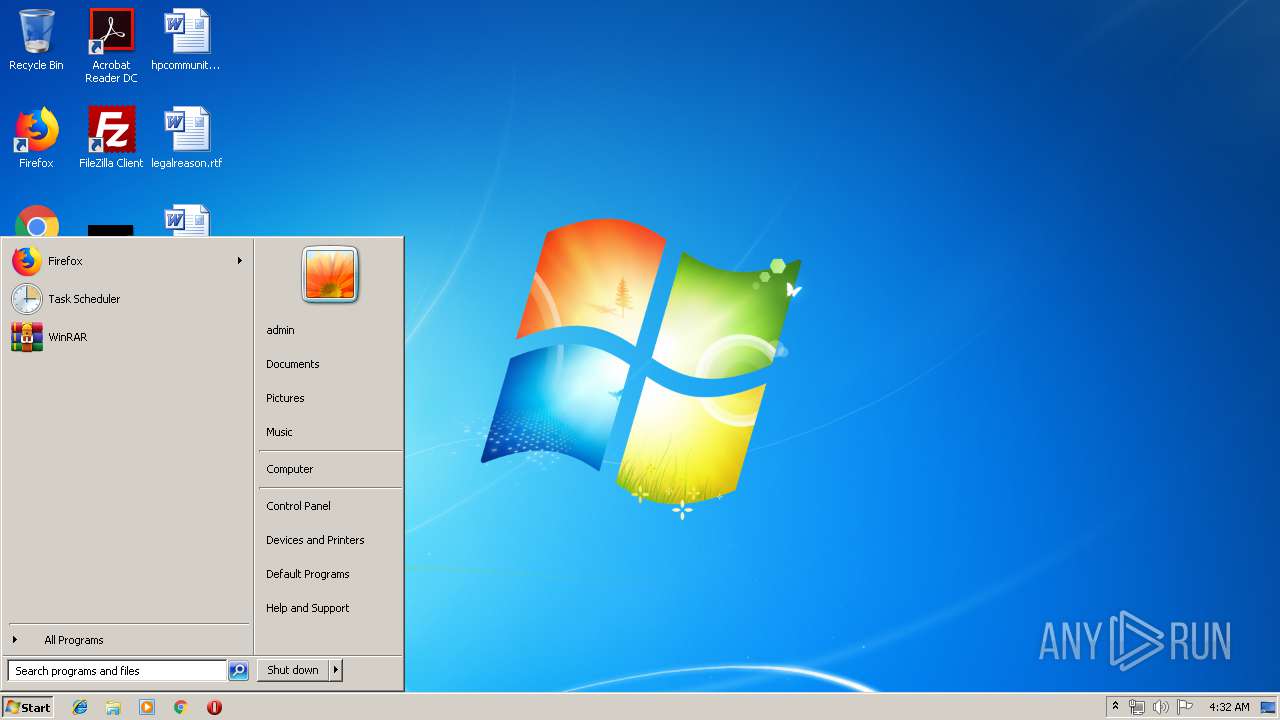
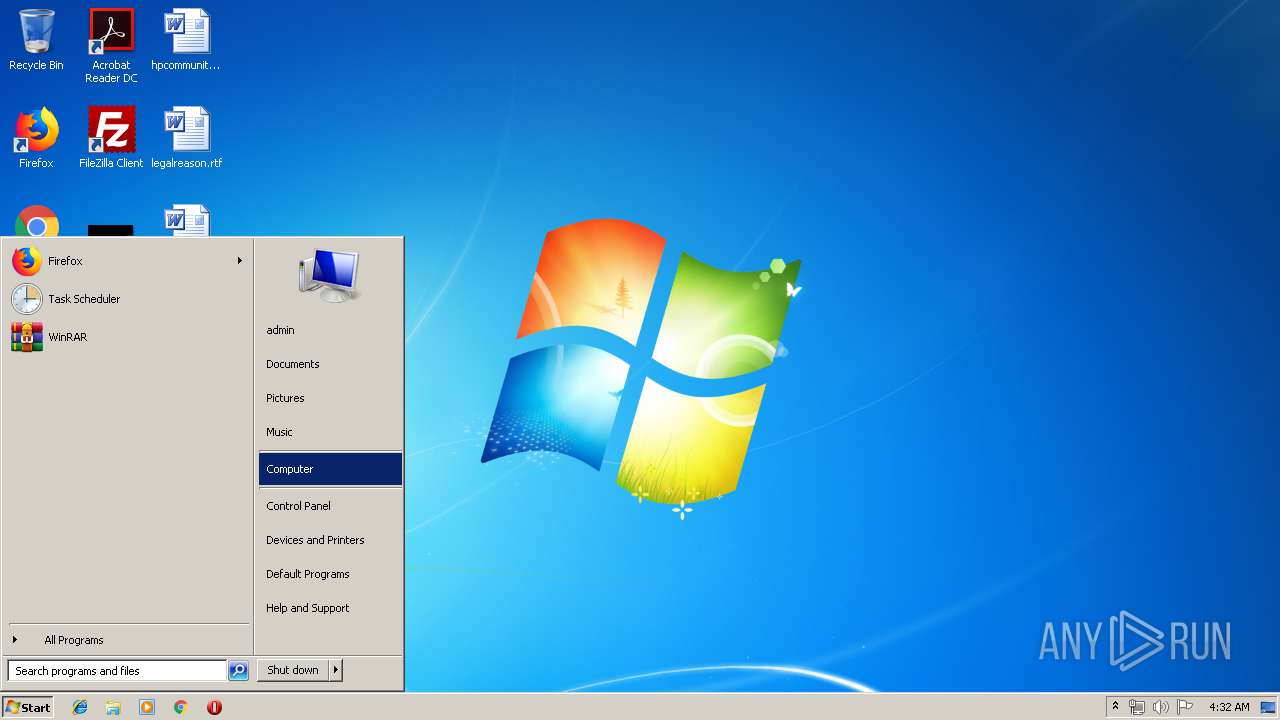
Manual execution by user
- WINWORD.EXE (PID: 2812)
- explorer.exe (PID: 3652)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2812)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (4.9) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (3.4) |
| .exe | | | Generic Win/DOS Executable (1.5) |
| .exe | | | DOS Executable Generic (1.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:07:25 07:47:23+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 2434560 |
| InitializedDataSize: | 1128960 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x231e06 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.12411.123 |
| ProductVersionNumber: | 2.0.12411.123 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Tencent |
| FileDescription: | Gameloop |
| FileVersion: | 2.0.12411.123 |
| InternalName: | AppMarket |
| LegalCopyright: | Copyright © 2017 Tencent. All Rights Reserved. |
| OriginalFileName: | AppMarket.exe |
| ProductName: | Gameloop |
| ProductVersion: | 2,0,12411,123 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Jul-2019 05:47:23 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Tencent |
| FileDescription: | Gameloop |
| FileVersion: | 2.0.12411.123 |
| InternalName: | AppMarket |
| LegalCopyright: | Copyright © 2017 Tencent. All Rights Reserved. |
| OriginalFilename: | AppMarket.exe |
| ProductName: | Gameloop |
| ProductVersion: | 2,0,12411,123 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000148 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 25-Jul-2019 05:47:23 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0025255E | 0x00252600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.21455 |
.rdata | 0x00254000 | 0x00068F30 | 0x00069000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.68596 |
.data | 0x002BD000 | 0x00007A7C | 0x00004A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.35159 |
.gfids | 0x002C5000 | 0x0000006C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.530073 |
.tls | 0x002C6000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x002C7000 | 0x00088F50 | 0x00089000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.93523 |
.reloc | 0x00350000 | 0x00019900 | 0x00019A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.6787 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.06216 | 651 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.73139 | 2440 | UNKNOWN | Chinese - PRC | RT_ICON |
3 | 5.67525 | 4264 | UNKNOWN | Chinese - PRC | RT_ICON |
4 | 5.48921 | 9640 | UNKNOWN | Chinese - PRC | RT_ICON |
5 | 5.4101 | 16936 | UNKNOWN | Chinese - PRC | RT_ICON |
6 | 5.36521 | 38056 | UNKNOWN | Chinese - PRC | RT_ICON |
7 | 5.25768 | 67624 | UNKNOWN | Chinese - PRC | RT_ICON |
8 | 5.18484 | 270376 | UNKNOWN | Chinese - PRC | RT_ICON |
9 | 7.98782 | 47050 | UNKNOWN | Chinese - PRC | RT_ICON |
10 | 4.65642 | 3752 | UNKNOWN | Chinese - PRC | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
Common.dll |
GDI32.dll |
GF.dll |
IMM32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MSVCP140.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
GetModuleHandle64 | 1 | 0x00225460 |
GetProcAddress64 | 2 | 0x00225610 |
X64Call | 3 | 0x00225270 |
Total processes
43
Monitored processes
4
Malicious processes
0
Suspicious processes
0
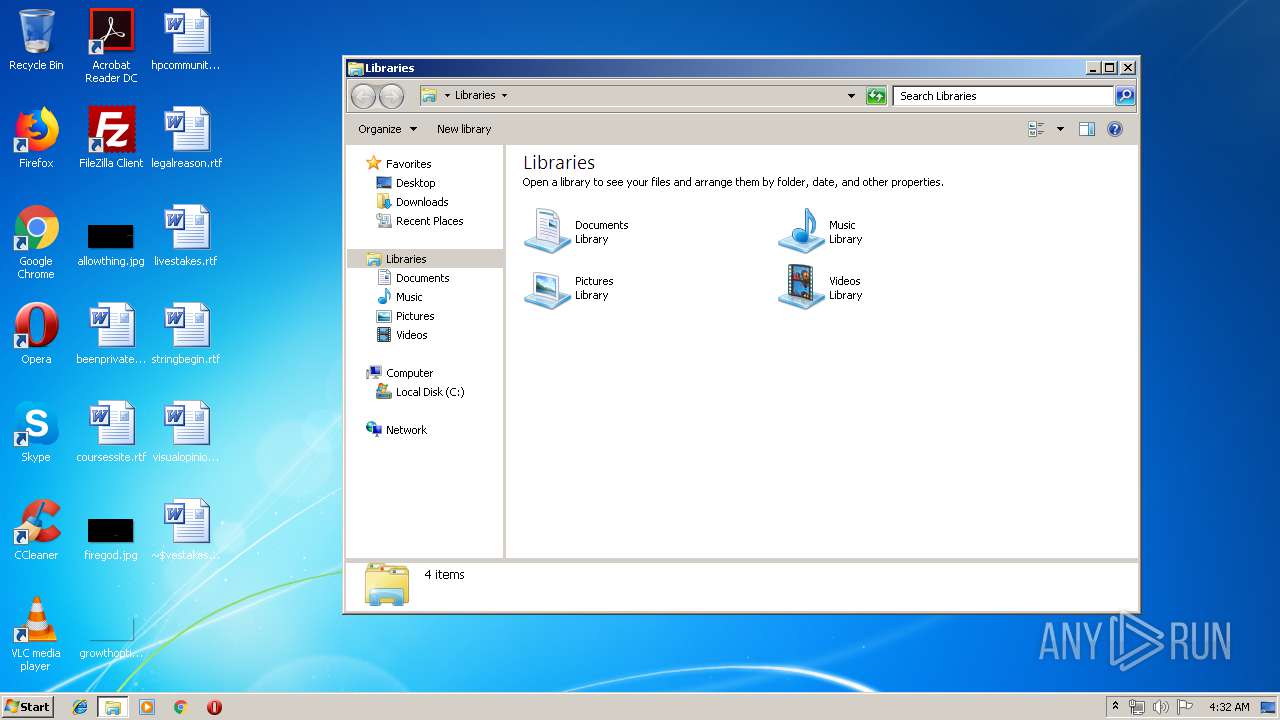
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
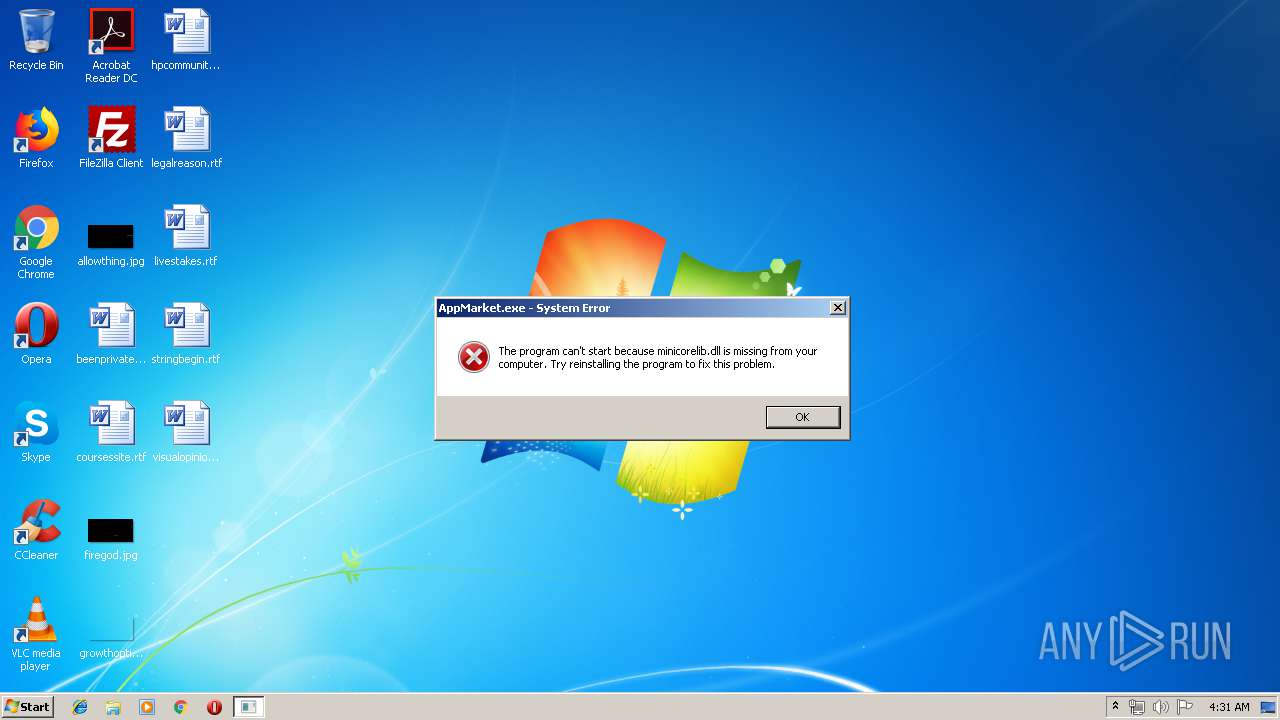
| 2132 | "C:\Users\admin\AppData\Local\Temp\AppMarket.exe" | C:\Users\admin\AppData\Local\Temp\AppMarket.exe | — | explorer.exe | |||||||||||
User: admin Company: Tencent Integrity Level: MEDIUM Description: Gameloop Exit code: 3221226540 Version: 2.0.12411.123 Modules
| |||||||||||||||
| 2776 | "C:\Users\admin\AppData\Local\Temp\AppMarket.exe" | C:\Users\admin\AppData\Local\Temp\AppMarket.exe | explorer.exe | ||||||||||||
User: admin Company: Tencent Integrity Level: HIGH Description: Gameloop Exit code: 3221225781 Version: 2.0.12411.123 Modules
| |||||||||||||||
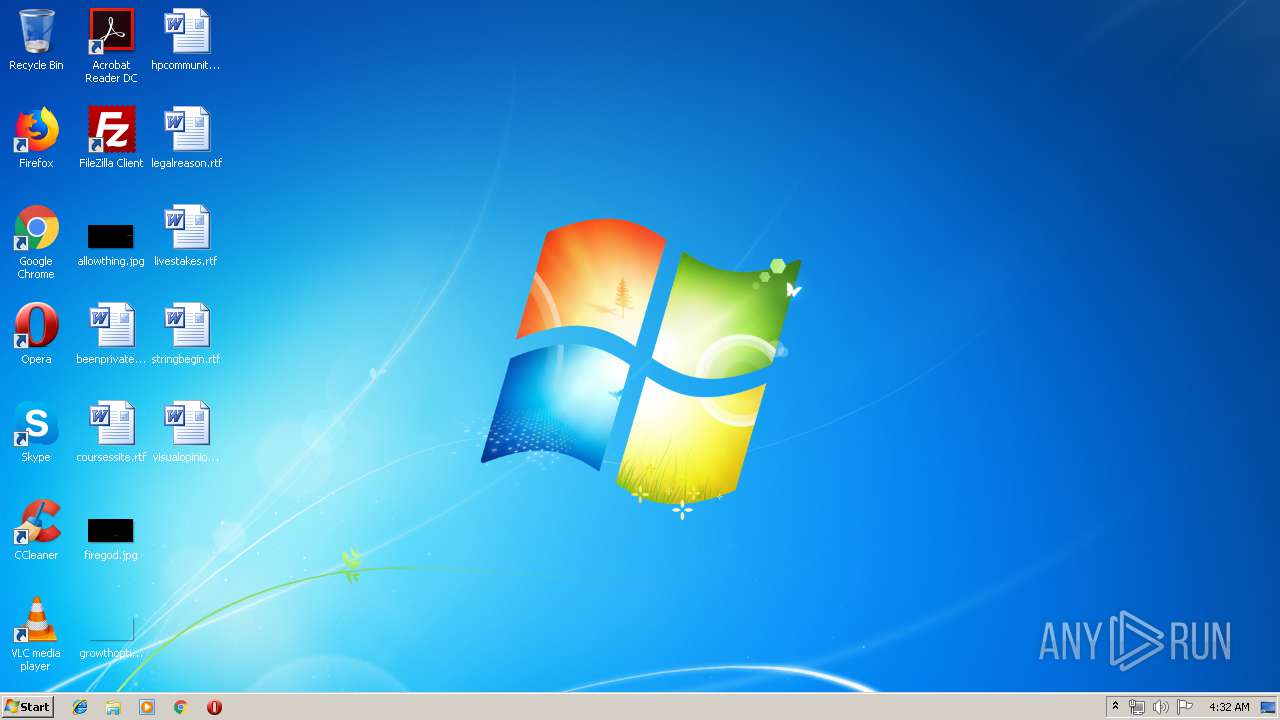
| 2812 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\livestakes.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3652 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
703
Read events
647
Write events
45
Delete events
11
Modification events
| (PID) Process: | (2812) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 71` |
Value: 37316000FC0A0000010000000000000000000000 | |||
| (PID) Process: | (2812) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2812) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2812) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1325793311 | |||
| (PID) Process: | (2812) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1325793424 | |||
| (PID) Process: | (2812) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1325793425 | |||
| (PID) Process: | (2812) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: FC0A0000BD76B797074CD50100000000 | |||
| (PID) Process: | (2812) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | m3` |
Value: 6D336000FC0A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2812) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | m3` |
Value: 6D336000FC0A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2812) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
4
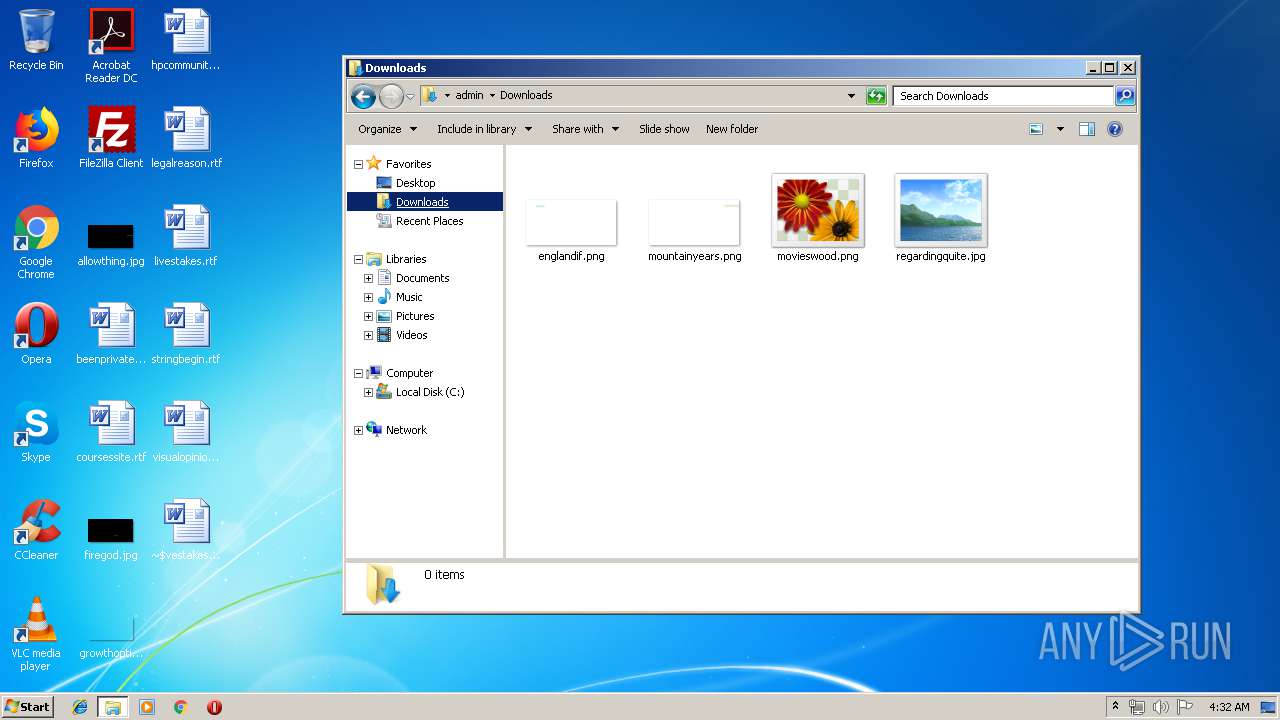
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2812 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR81B7.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2812 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{907FF93C-013B-4B8E-BDF4-62AEDBC4A71A}.tmp | — | |
MD5:— | SHA256:— | |||
| 2812 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{951A587D-97E2-488A-AB1B-D2B96CAF59C0}.tmp | — | |
MD5:— | SHA256:— | |||
| 2812 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2812 | WINWORD.EXE | C:\Users\admin\Desktop\~$vestakes.rtf | pgc | |
MD5:— | SHA256:— | |||
| 2812 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2812 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\livestakes.rtf.LNK | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report