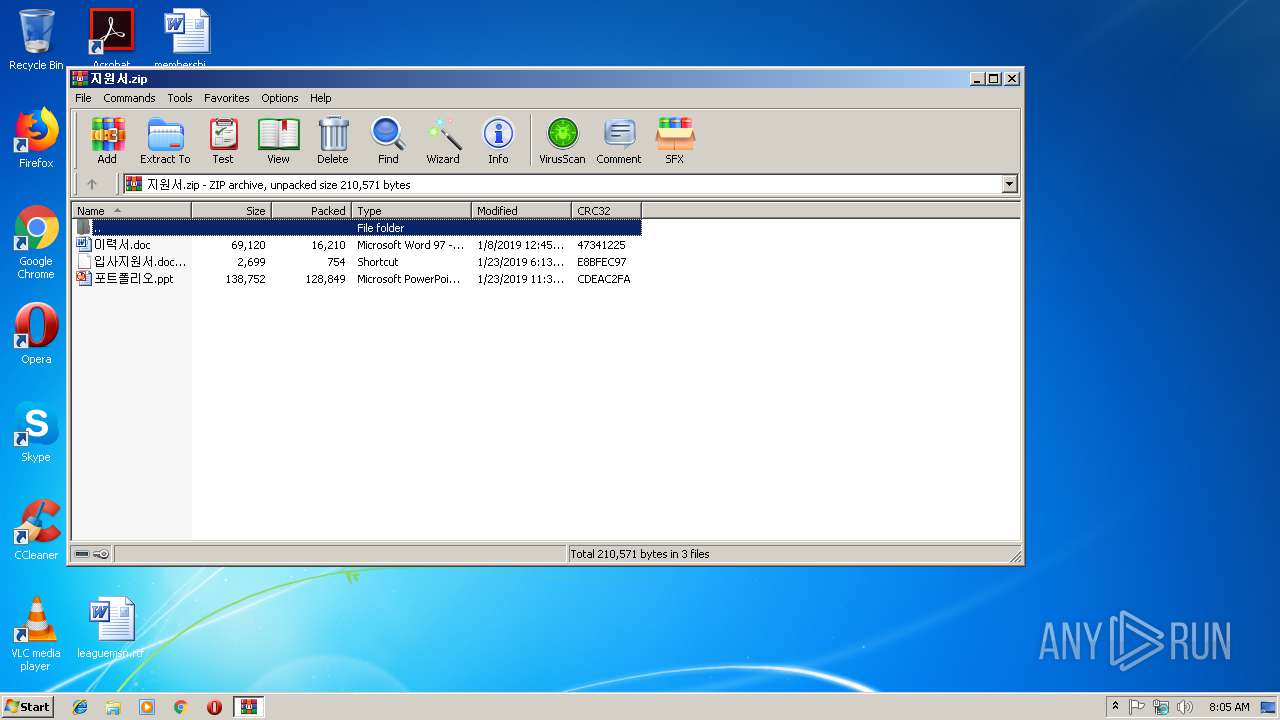
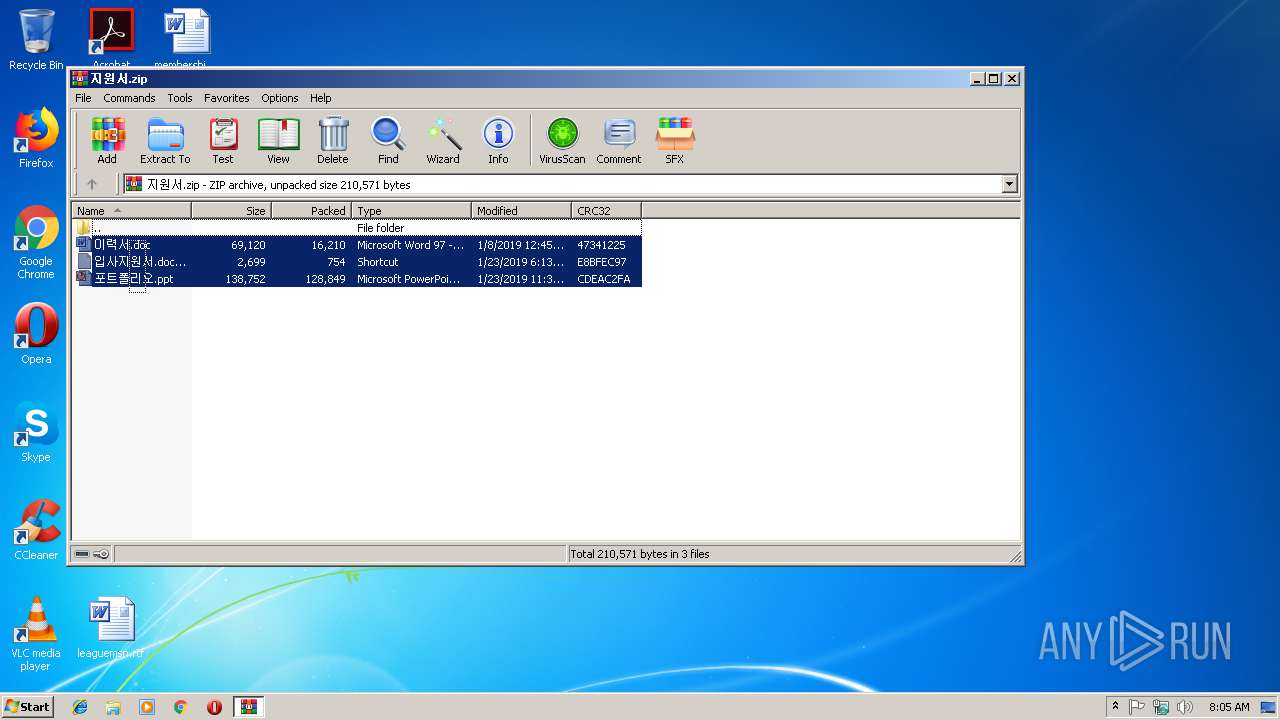
| File name: | 지원서.zip |
| Full analysis: | https://app.any.run/tasks/fa1e7f52-db88-4aec-94e0-fcb67f7dbe15 |
| Verdict: | Malicious activity |
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | January 23, 2019, 08:05:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | F1F48AAB9A3C99ECD264E6E5B926C90B |
| SHA1: | 9437D51C99CD9D88C416F98708934E89D273D3E7 |
| SHA256: | 3ECFADC4DC354EC842FFD36D8F01D5C06639E113334257D43A18E36B8B9A9429 |
| SSDEEP: | 3072:VsHxCzrbggxYpDLBcQe/ikBI8Q4AUvHO6wl6tPcbkSix:+RCzrbpxYpD1U/E8QpUvHx8pc |
MALICIOUS
Application was dropped or rewritten from another process
- 포트폴리오.ppt (PID: 2552)
GandCrab keys found
- 포트폴리오.ppt (PID: 2552)
Actions looks like stealing of personal data
- 포트폴리오.ppt (PID: 2552)
Writes file to Word startup folder
- 포트폴리오.ppt (PID: 2552)
Renames files like Ransomware
- 포트폴리오.ppt (PID: 2552)
Deletes shadow copies
- 포트폴리오.ppt (PID: 2552)
Dropped file may contain instructions of ransomware
- 포트폴리오.ppt (PID: 2552)
Changes settings of System certificates
- 포트폴리오.ppt (PID: 2552)
SUSPICIOUS
Starts application with an unusual extension
- cmd.exe (PID: 3924)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3924)
Starts Microsoft Office Application
- cmd.exe (PID: 2672)
Creates files in the program directory
- 포트폴리오.ppt (PID: 2552)
Reads the cookies of Mozilla Firefox
- 포트폴리오.ppt (PID: 2552)
Creates files like Ransomware instruction
- 포트폴리오.ppt (PID: 2552)
Adds / modifies Windows certificates
- 포트폴리오.ppt (PID: 2552)
Creates files in the user directory
- 포트폴리오.ppt (PID: 2552)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3800)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3800)
Dropped object may contain TOR URL's
- 포트폴리오.ppt (PID: 2552)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
Total processes
42
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2284 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | 포트폴리오.ppt | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2304 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2552 | 포트폴리오.ppt | C:\Users\admin\Desktop\포트폴리오.ppt | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
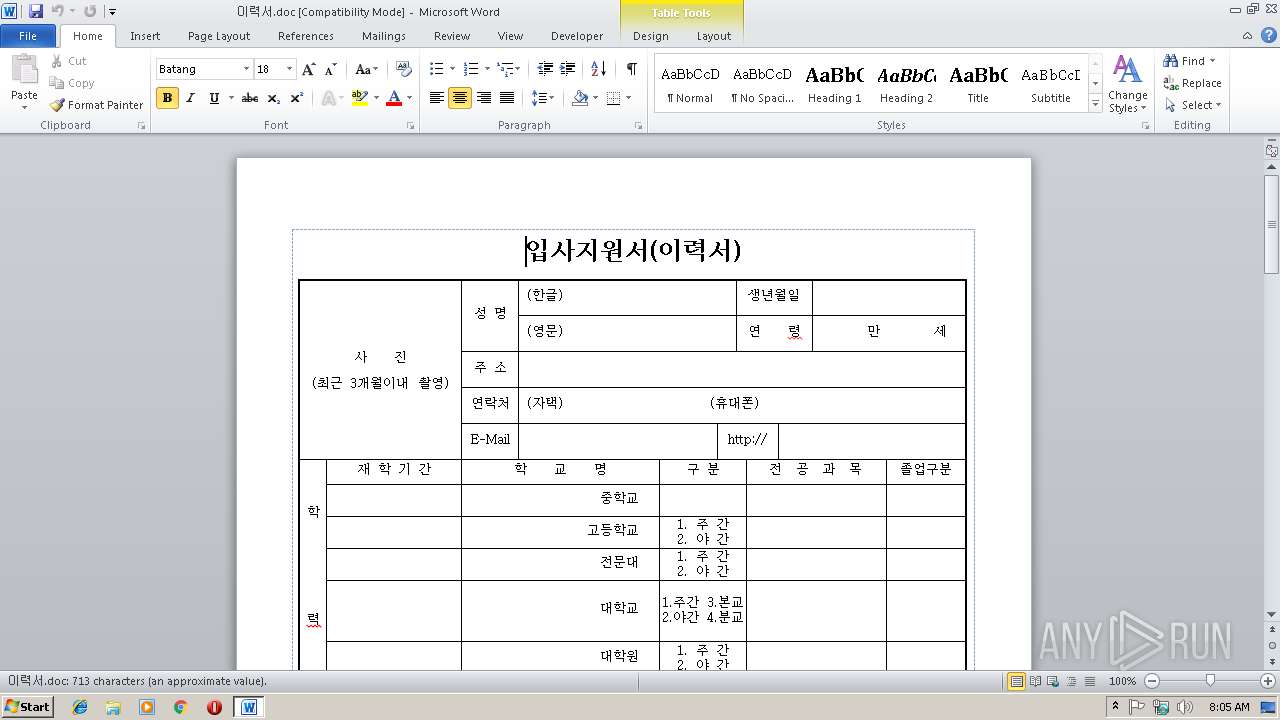
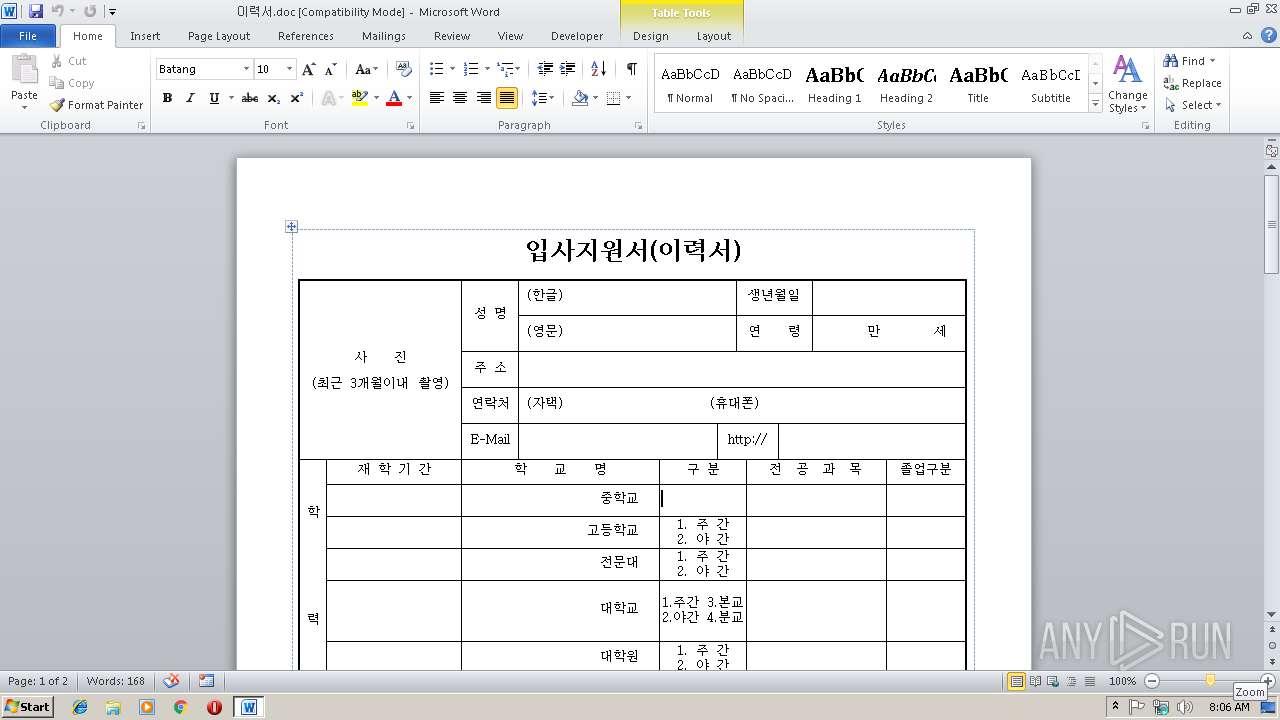
| 2672 | cmd /c @start 이력서.doc | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
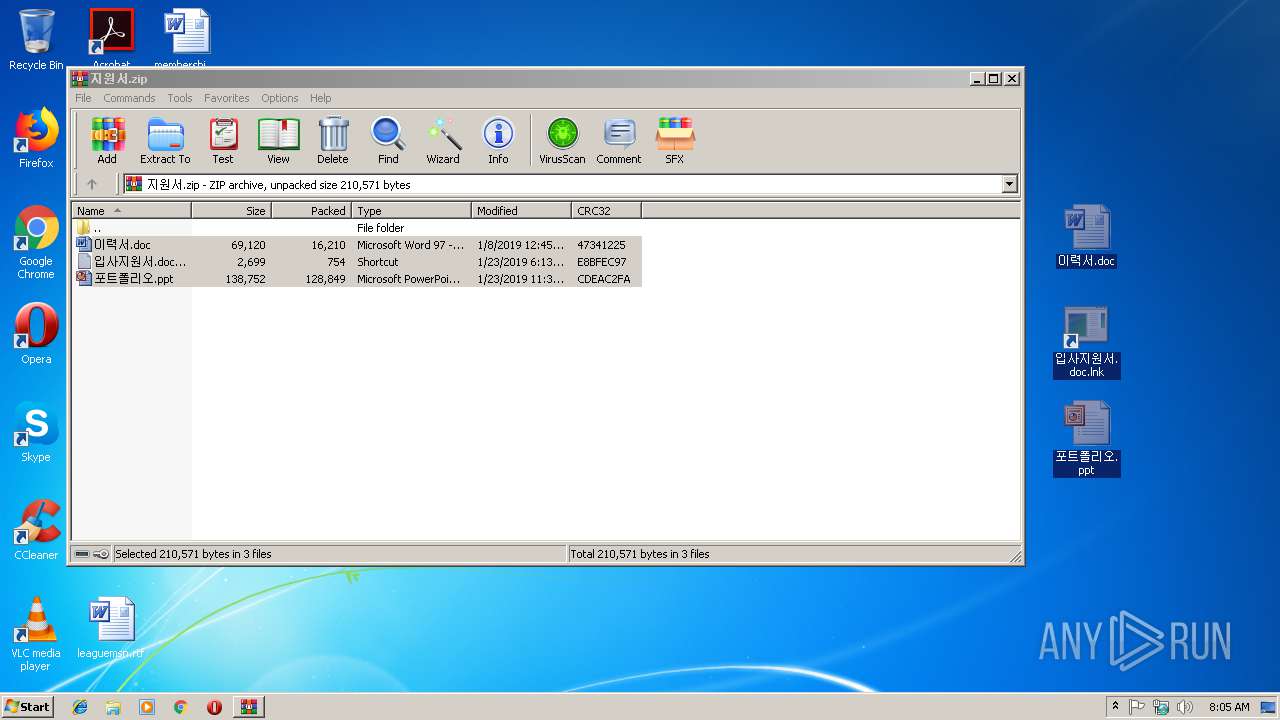
| 2912 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\지원서.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
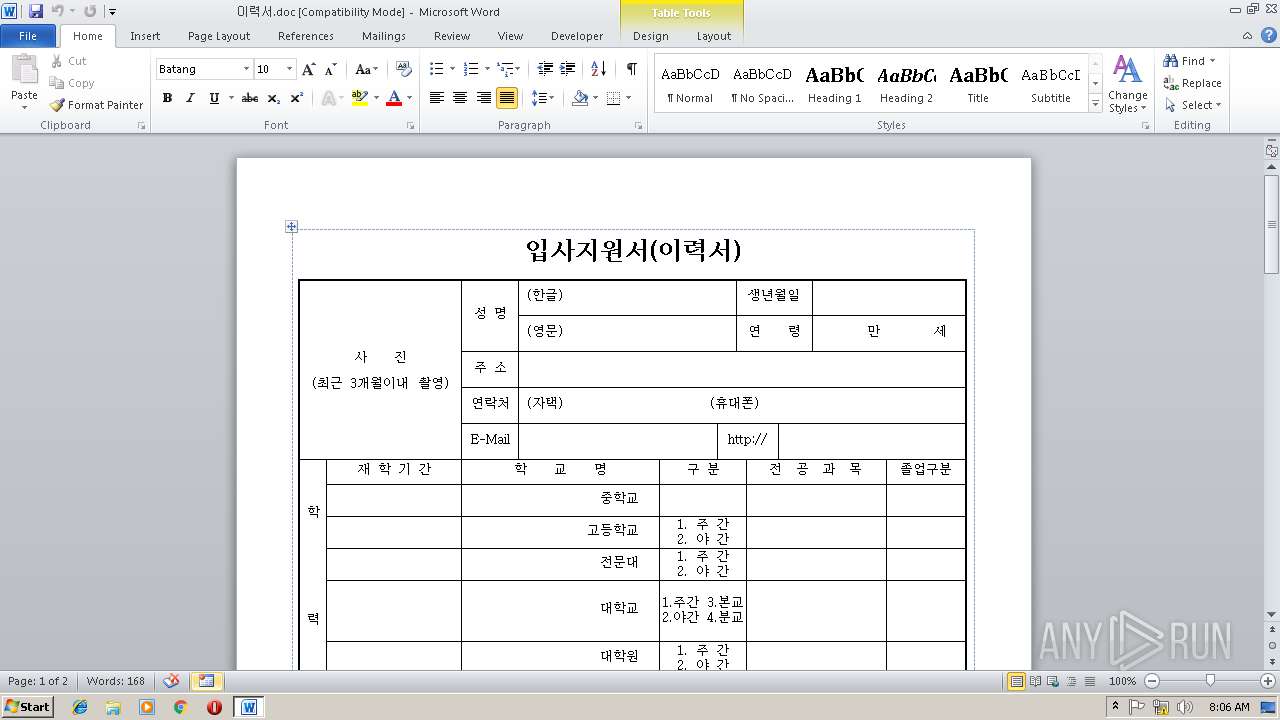
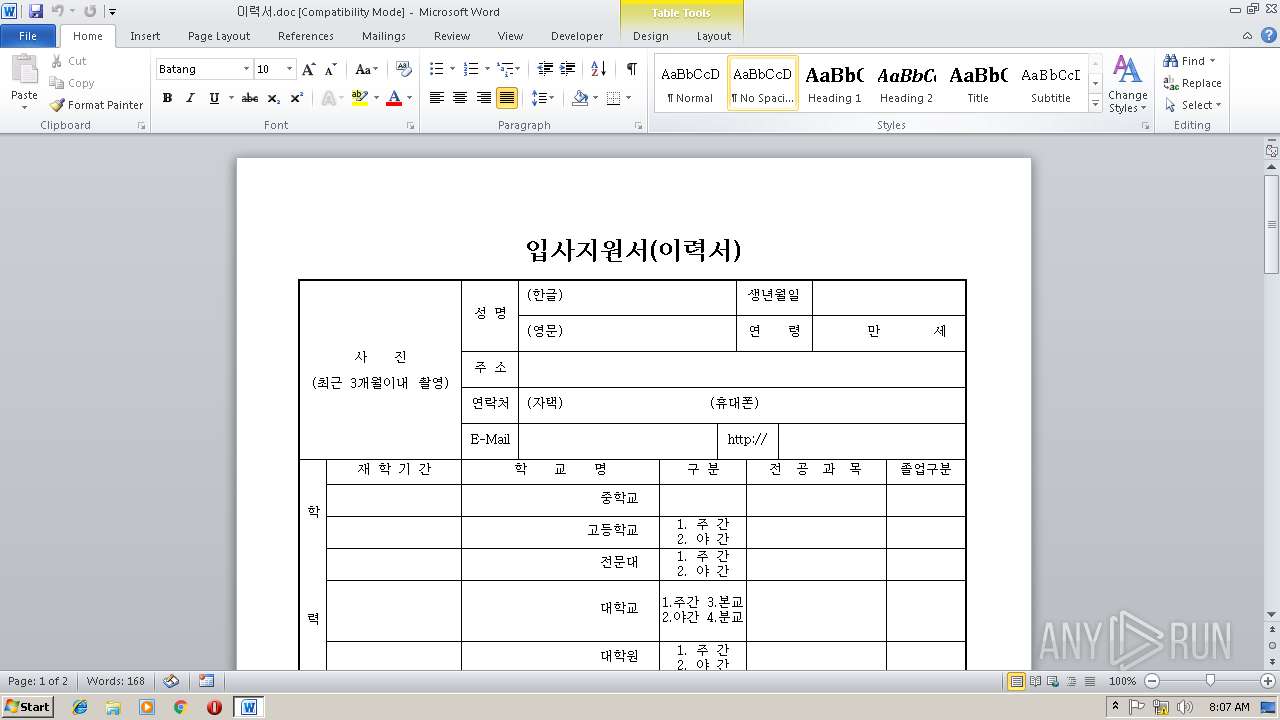
| 3800 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\이력서.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
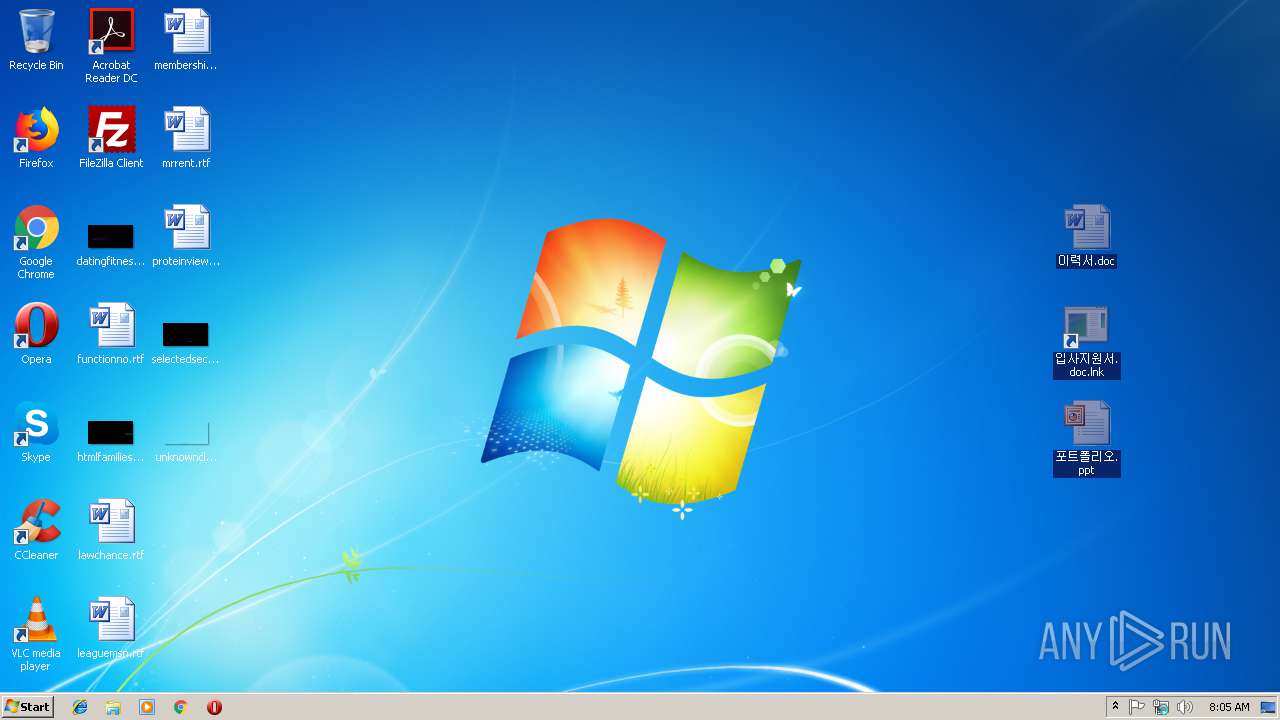
| 3924 | "C:\Windows\System32\cmd.exe" hidden cmd /c @start 포트폴리오.ppt & cmd /c @start 이력서.doc | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 611
Read events
1 217
Write events
387
Delete events
7
Modification events
| (PID) Process: | (2912) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2912) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2912) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2912) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\지원서.zip | |||
| (PID) Process: | (2912) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2912) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2912) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2912) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2912) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (2912) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
0
Suspicious files
428
Text files
319
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2912 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2912.23467\이력서.doc | — | |
MD5:— | SHA256:— | |||
| 2912 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2912.23467\입사지원서.doc.lnk.lnk | — | |
MD5:— | SHA256:— | |||
| 2912 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2912.23467\포트폴리오.ppt | — | |
MD5:— | SHA256:— | |||
| 3800 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR12EB.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3800 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFB38F2D59B211B215.TMP | — | |
MD5:— | SHA256:— | |||
| 3800 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF14ED574443D5FECD.TMP | — | |
MD5:— | SHA256:— | |||
| 2552 | 포트폴리오.ppt | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\boot.sdi | — | |
MD5:— | SHA256:— | |||
| 2552 | 포트폴리오.ppt | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim | — | |
MD5:— | SHA256:— | |||
| 2552 | 포트폴리오.ppt | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim.nljag | — | |
MD5:— | SHA256:— | |||
| 3800 | WINWORD.EXE | C:\Users\admin\Desktop\~$이력서.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2552 | 포트폴리오.ppt | GET | 301 | 138.201.162.99:80 | http://www.kakaocorp.link/ | DE | html | 162 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2552 | 포트폴리오.ppt | 138.201.162.99:443 | www.kakaocorp.link | Hetzner Online GmbH | DE | malicious |
2552 | 포트폴리오.ppt | 138.201.162.99:80 | www.kakaocorp.link | Hetzner Online GmbH | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.kakaocorp.link |
| malicious |