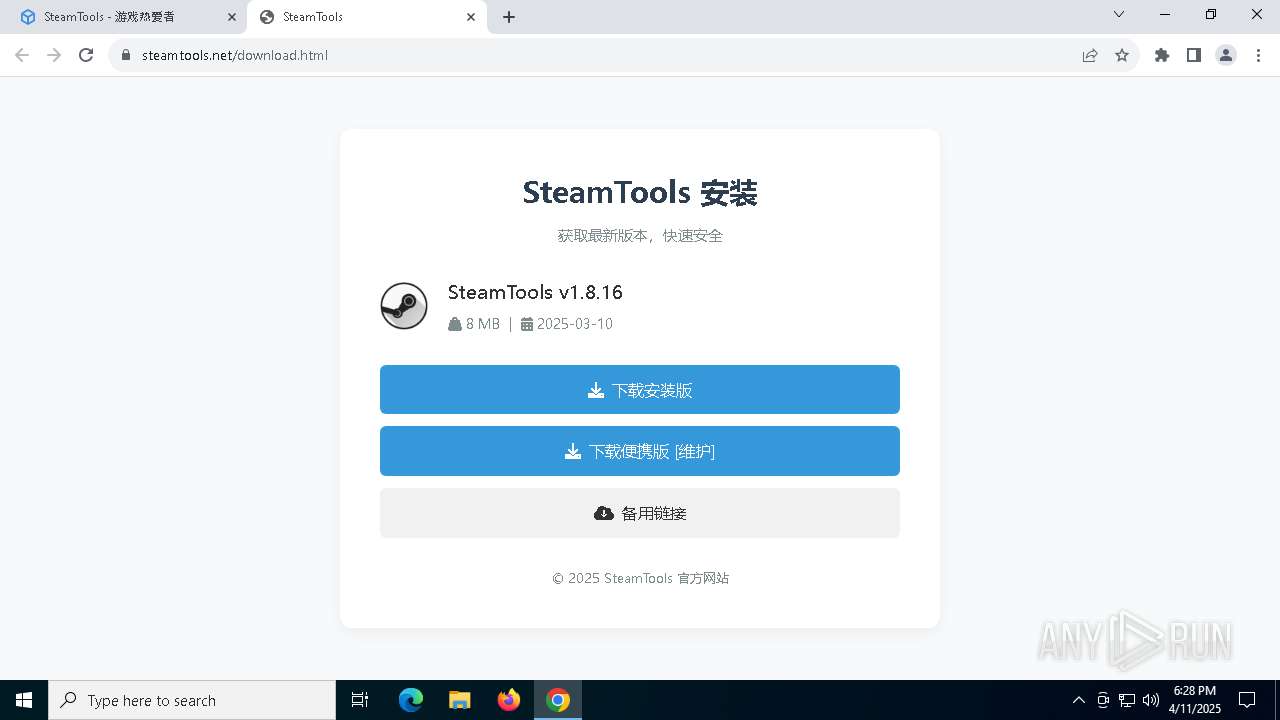
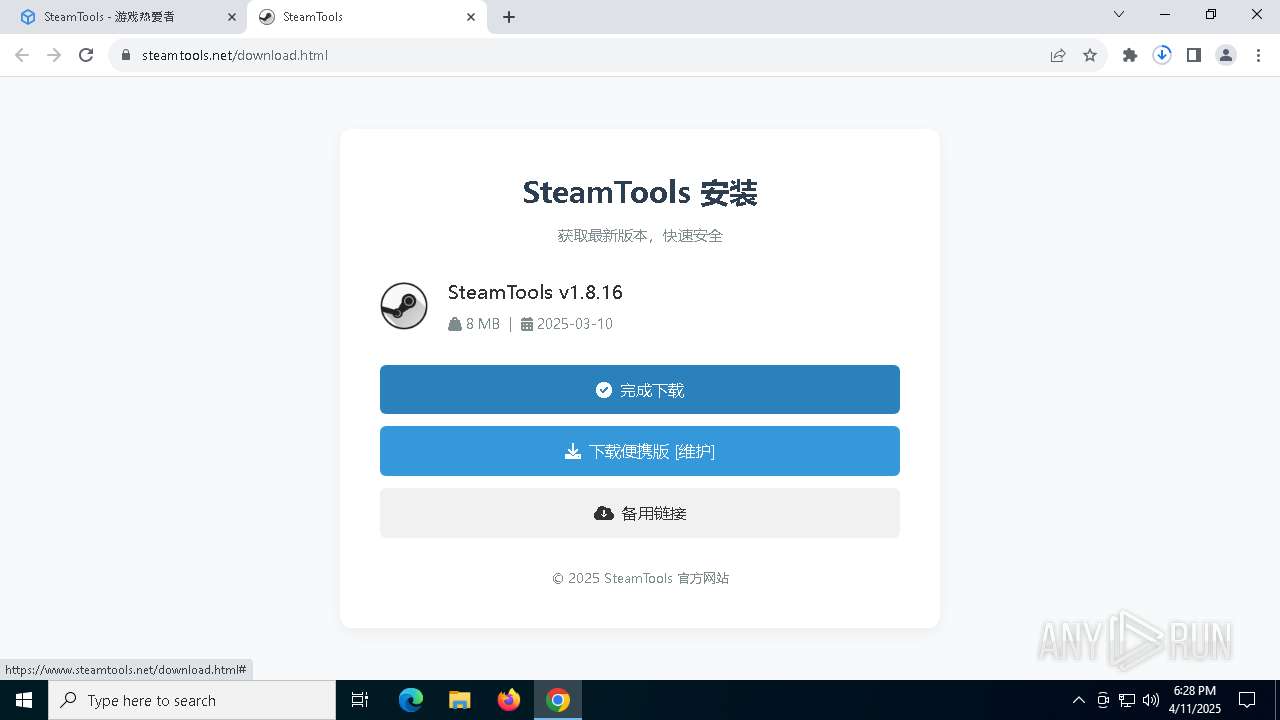
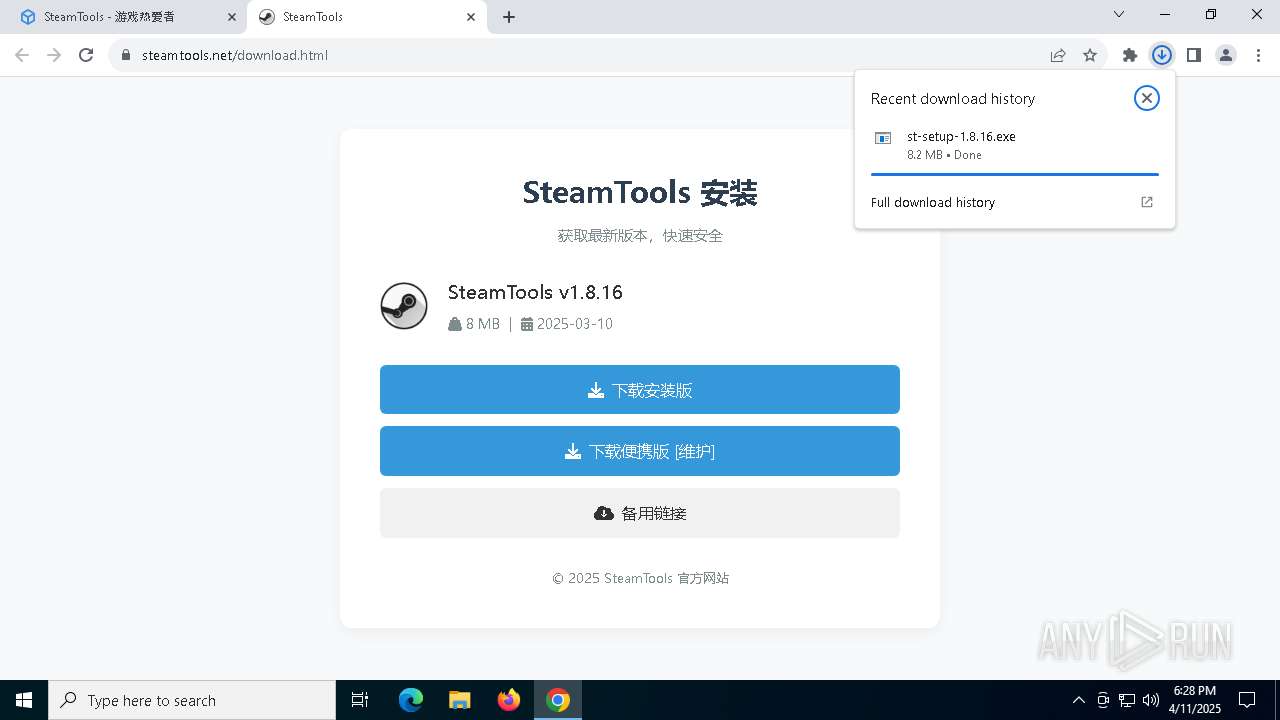
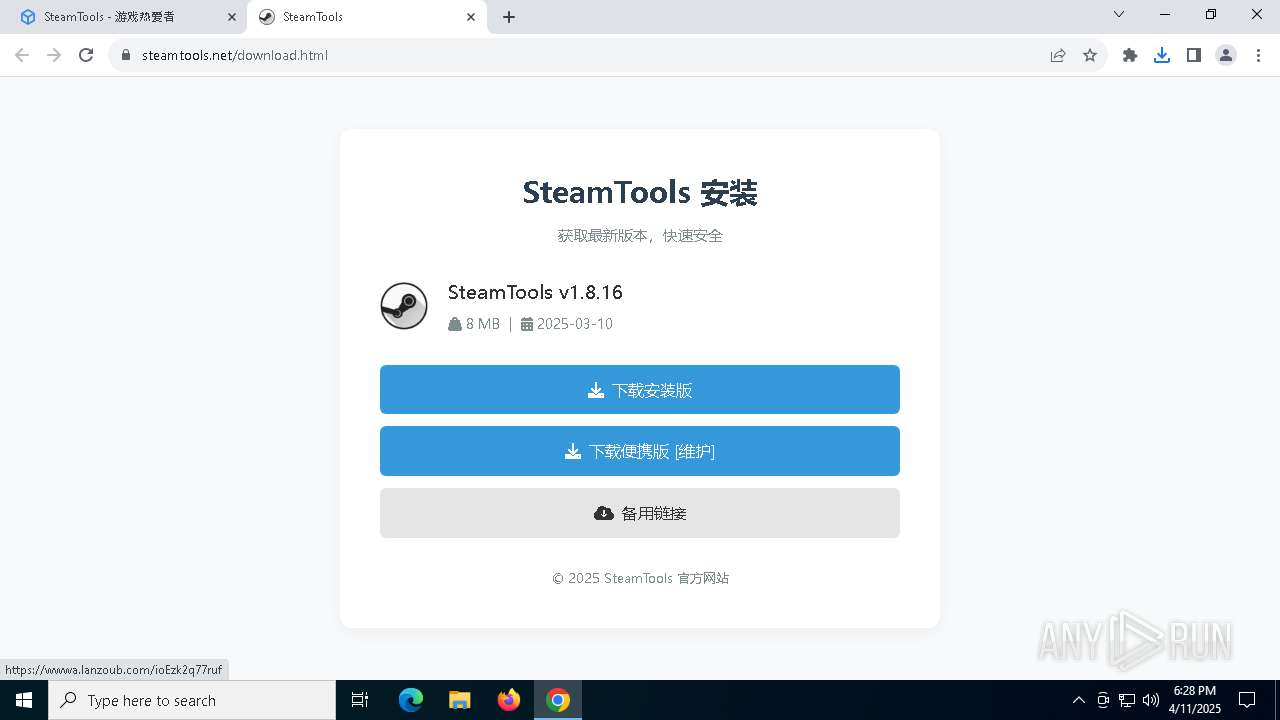
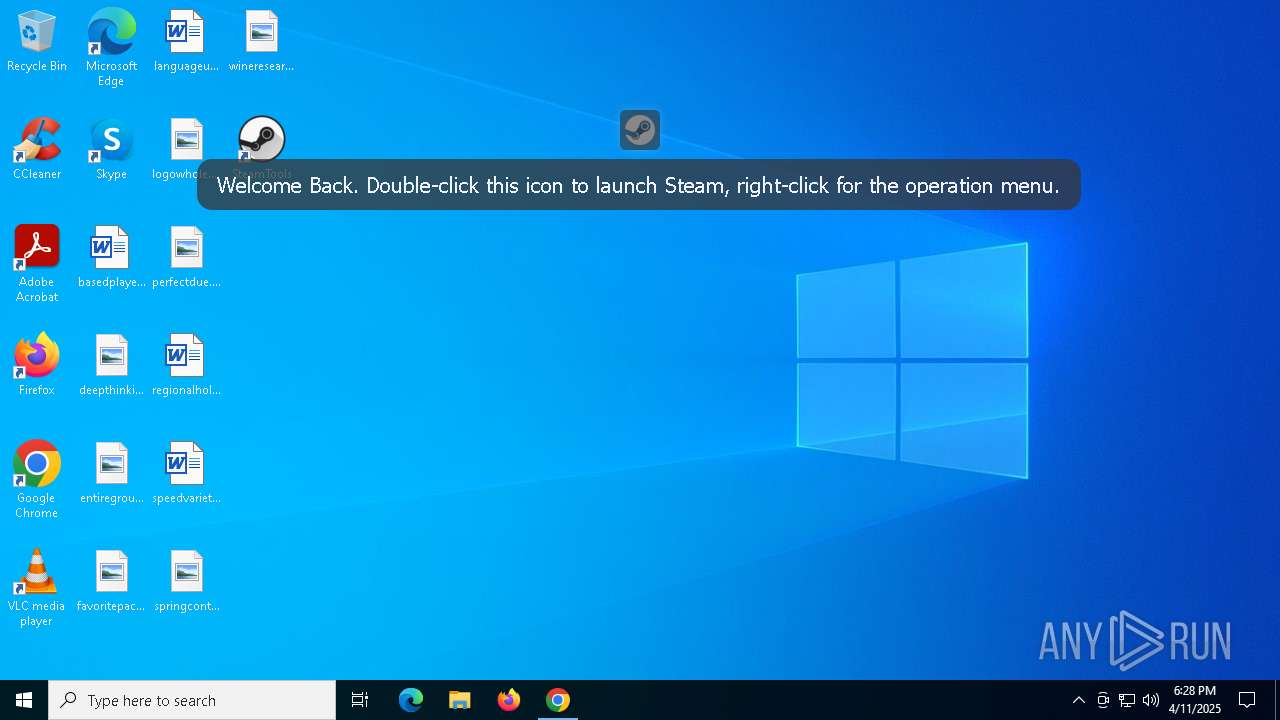
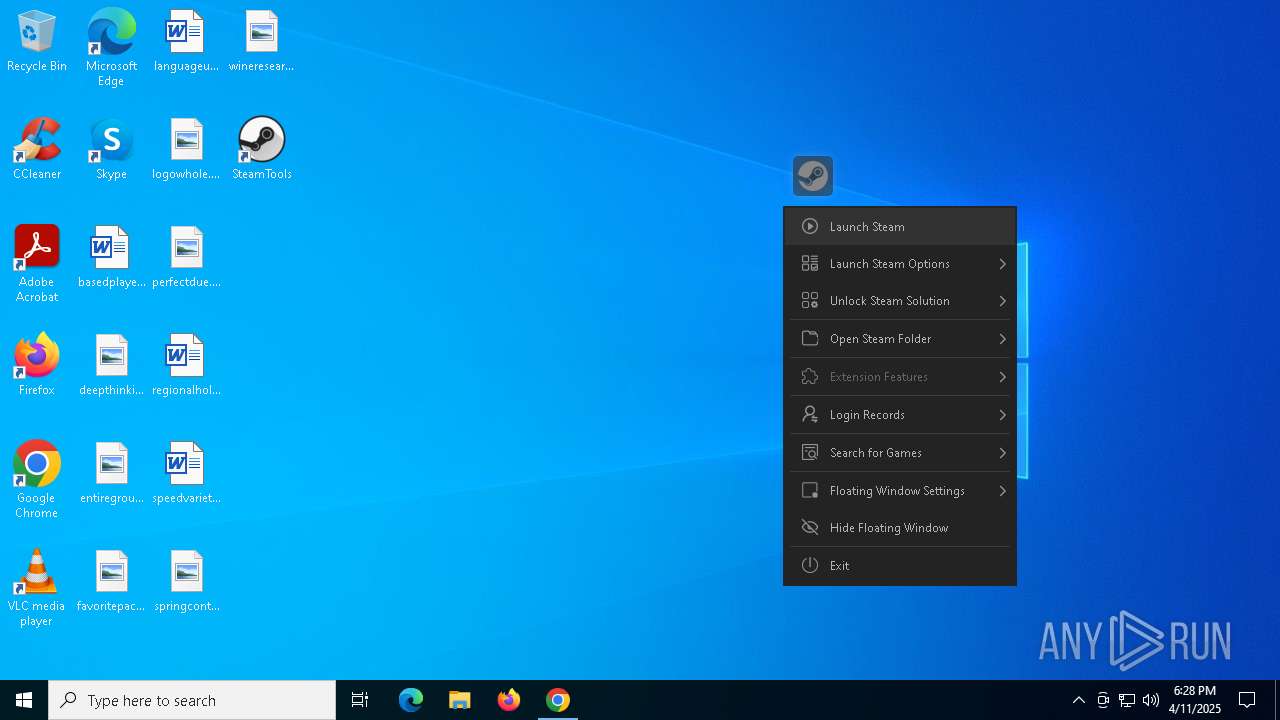
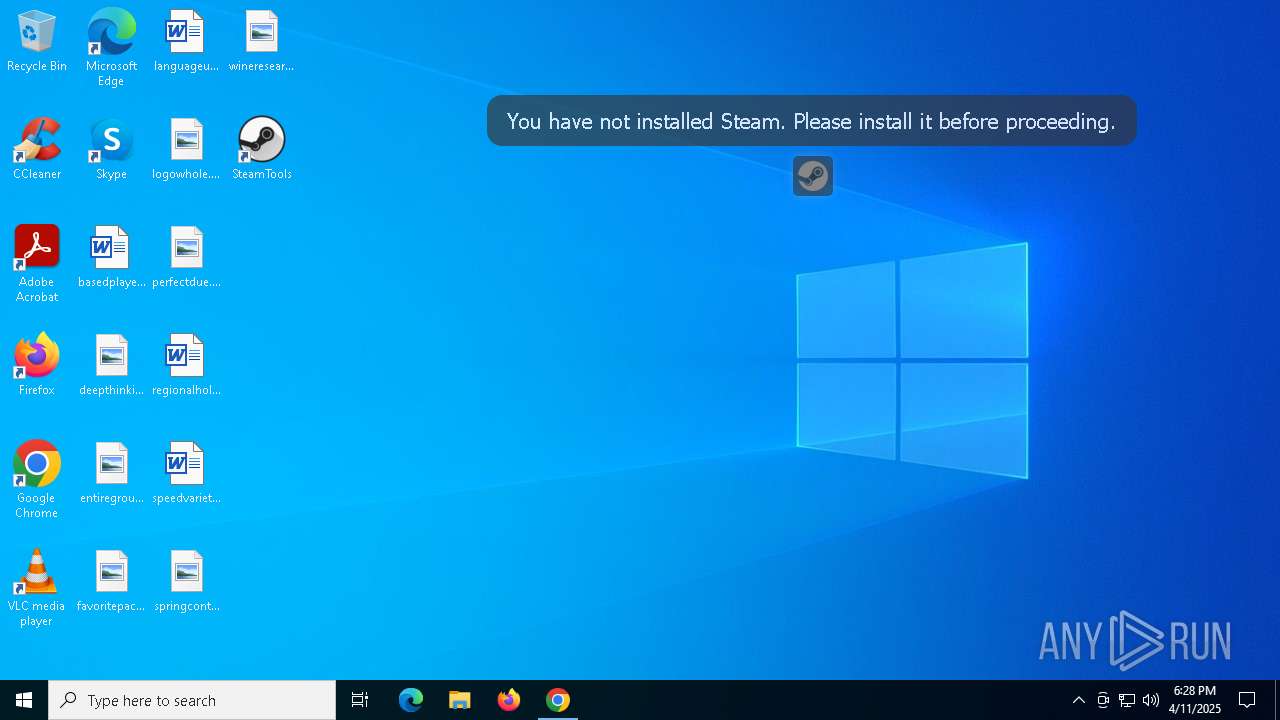
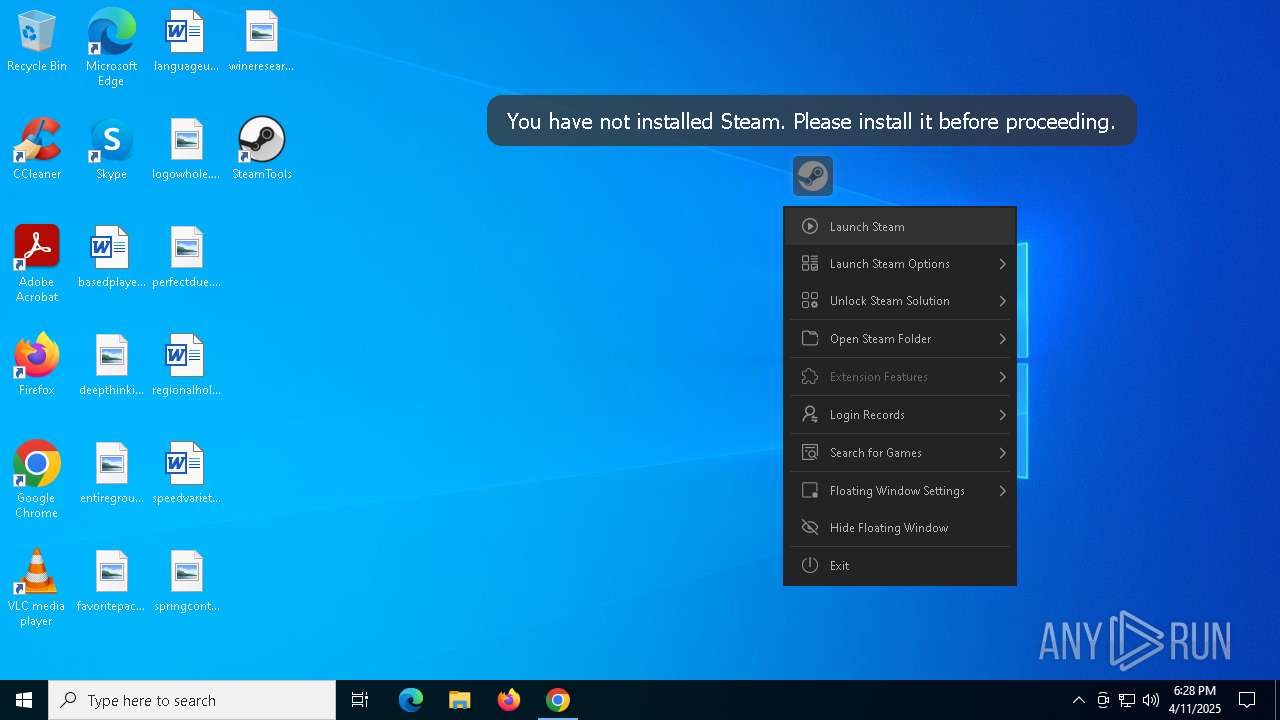
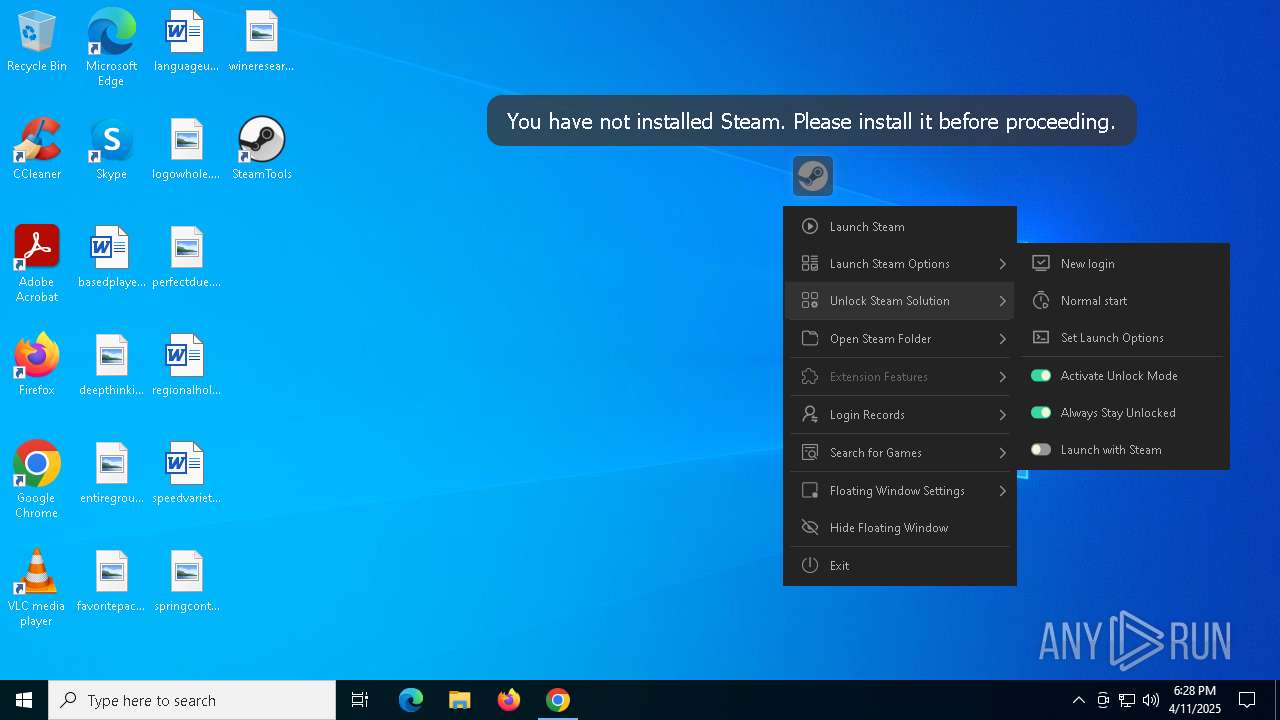
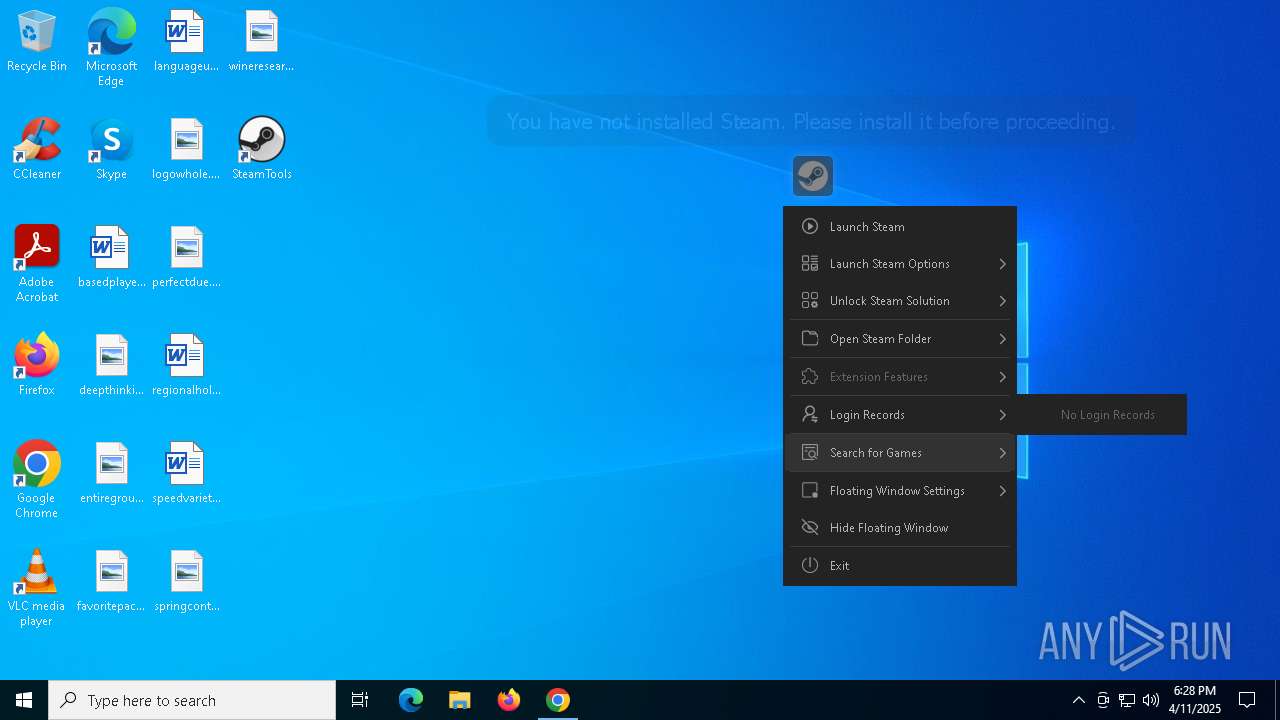
| URL: | https://www.steamtools.net |
| Full analysis: | https://app.any.run/tasks/cdc21127-a16c-4e86-a755-3e268e416b08 |
| Verdict: | Malicious activity |
| Analysis date: | April 11, 2025, 18:27:42 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 07A56162BBDE35E609FE71C6FF544541 |
| SHA1: | A2C4BC3B2364D755B47B31DC012705BDC493A24C |
| SHA256: | 3EBAAD0B82EEFB0D4A102CDE1B96DE86271F316034C1A91D1B21ABCA82367039 |
| SSDEEP: | 3:N8DSLBRNn:2OLnNn |
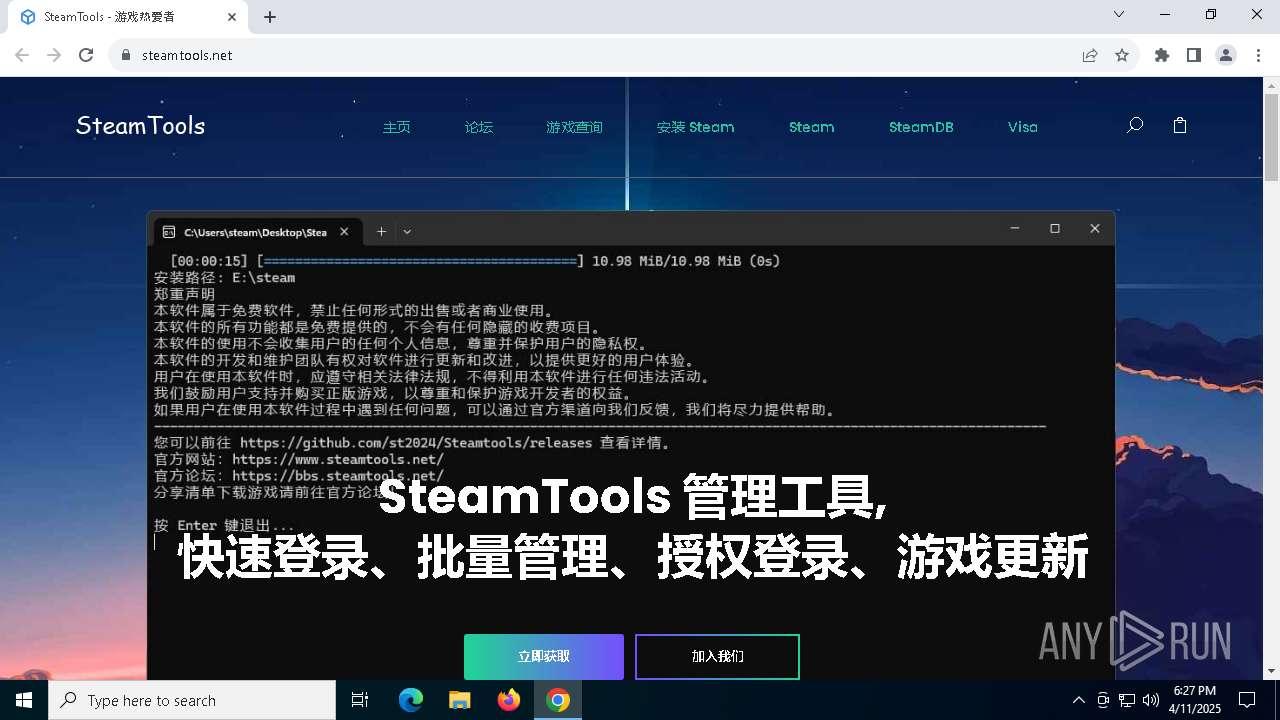
MALICIOUS
No malicious indicators.SUSPICIOUS
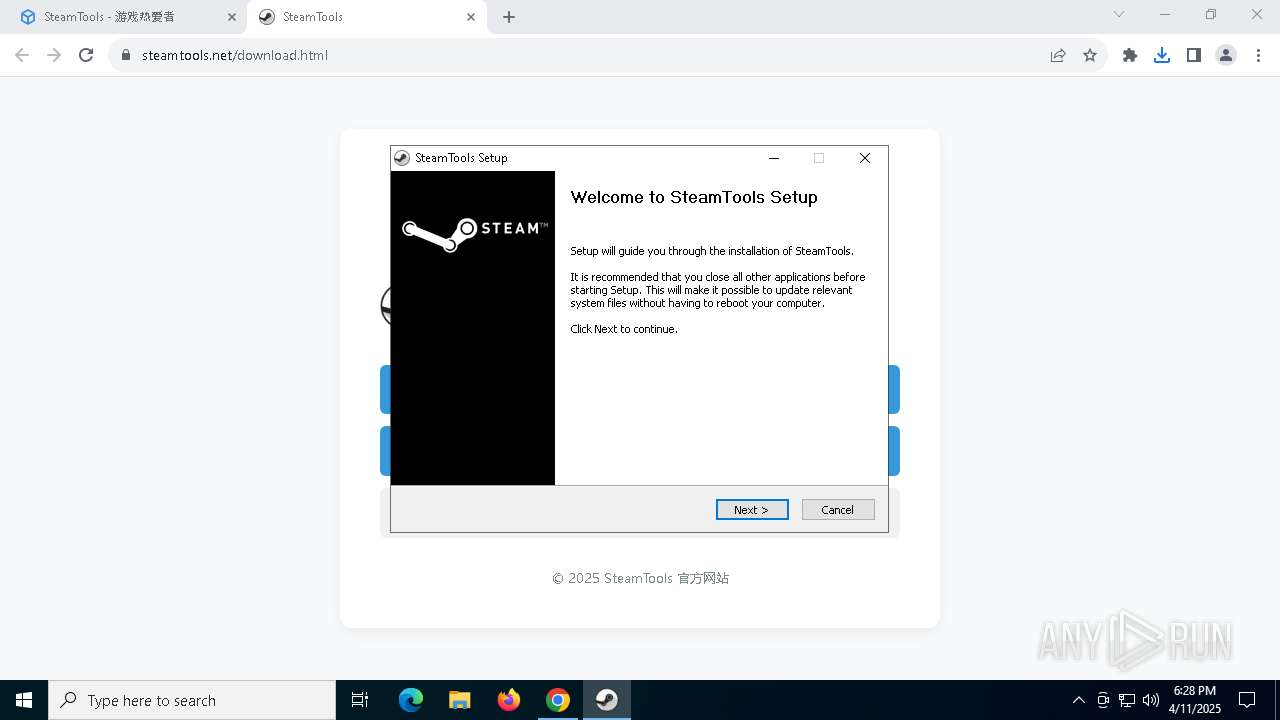
Executable content was dropped or overwritten
- st-setup-1.8.16.exe (PID: 8116)
The process creates files with name similar to system file names
- st-setup-1.8.16.exe (PID: 8116)
Malware-specific behavior (creating "System.dll" in Temp)
- st-setup-1.8.16.exe (PID: 8116)
Process drops legitimate windows executable
- st-setup-1.8.16.exe (PID: 8116)
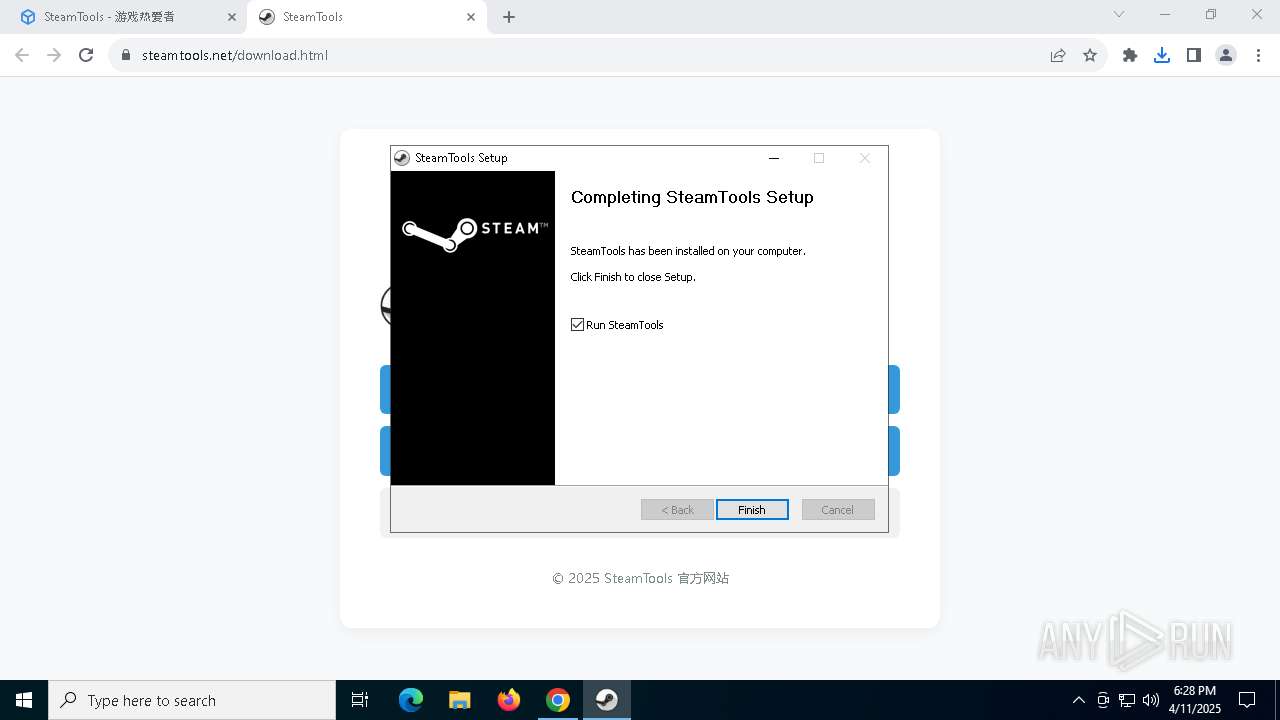
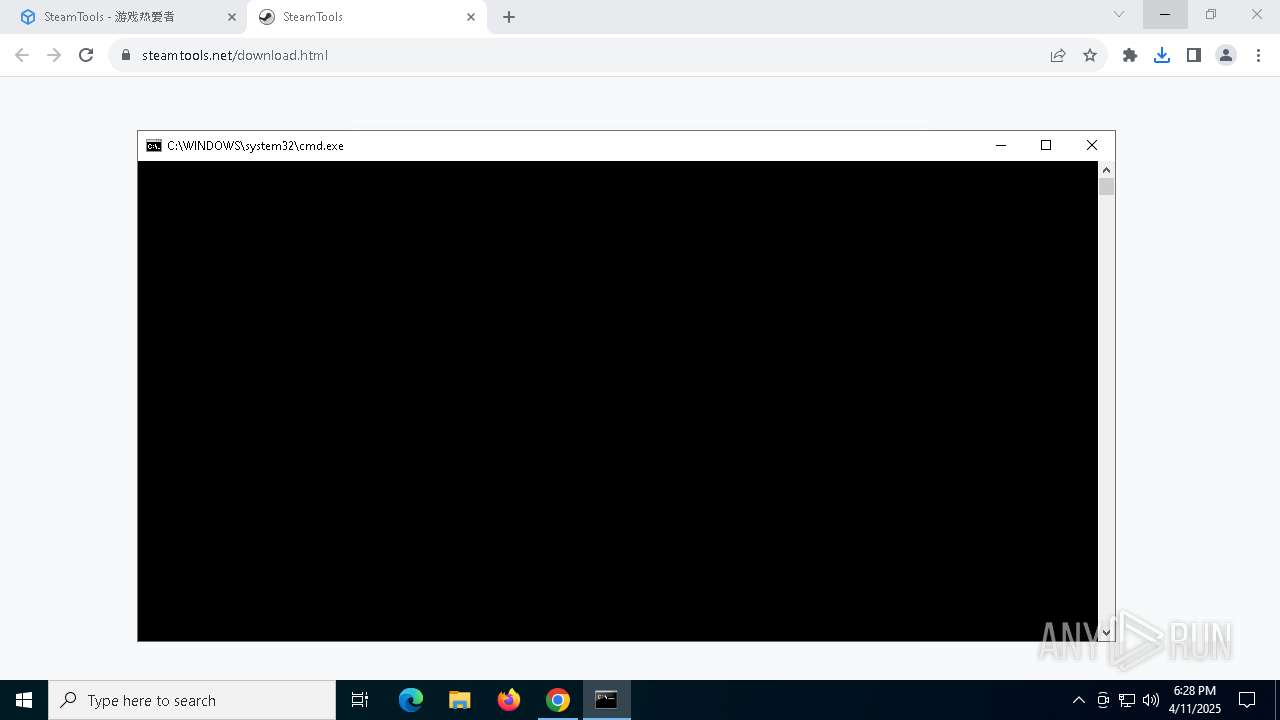
Executing commands from a ".bat" file
- explorer.exe (PID: 2236)
Starts CMD.EXE for commands execution
- explorer.exe (PID: 2236)
The process drops C-runtime libraries
- st-setup-1.8.16.exe (PID: 8116)
Creates a software uninstall entry
- st-setup-1.8.16.exe (PID: 8116)
Explorer used for Indirect Command Execution
- explorer.exe (PID: 6240)
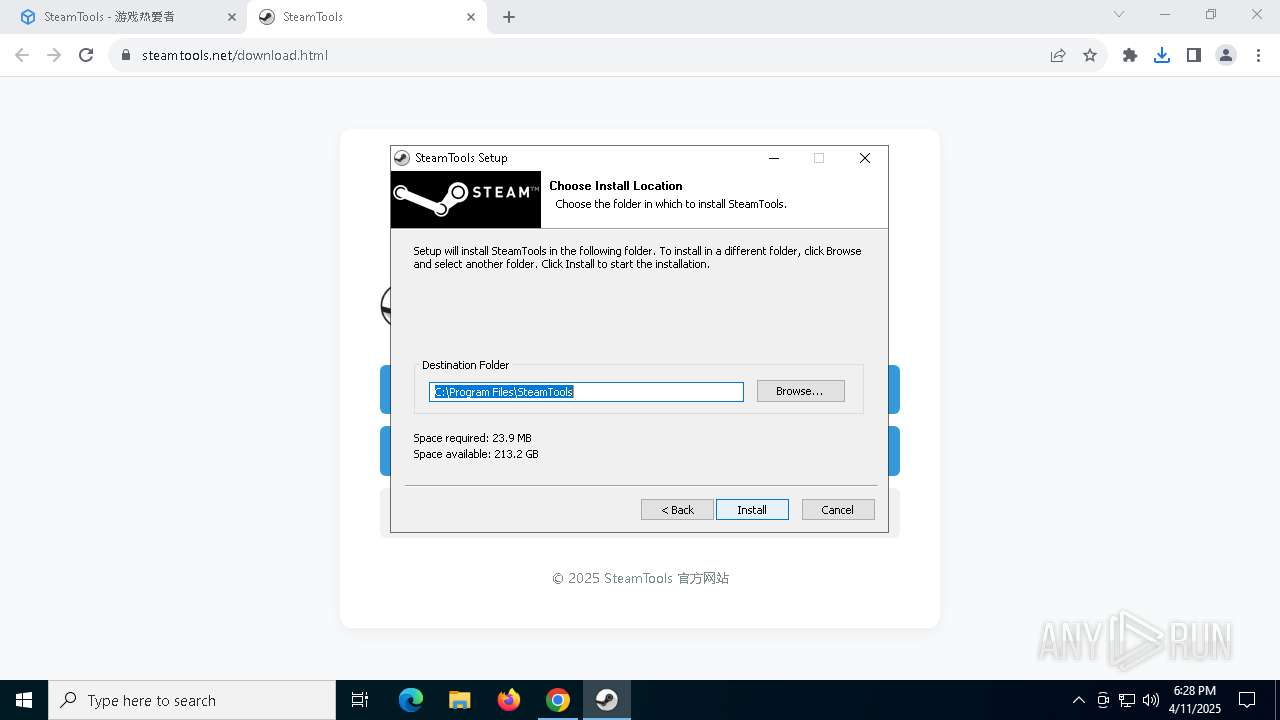
Uses ICACLS.EXE to modify access control lists
- st-setup-1.8.16.exe (PID: 8116)
INFO
Executable content was dropped or overwritten
- chrome.exe (PID: 7192)
Application launched itself
- chrome.exe (PID: 7192)
Reads the computer name
- st-setup-1.8.16.exe (PID: 8116)
- SteamTools.exe (PID: 5772)
Checks supported languages
- st-setup-1.8.16.exe (PID: 8116)
- SteamTools.exe (PID: 5772)
Autorun file from Downloads
- chrome.exe (PID: 7192)
- chrome.exe (PID: 5344)
Create files in a temporary directory
- st-setup-1.8.16.exe (PID: 8116)
Creates files in the program directory
- st-setup-1.8.16.exe (PID: 8116)
Reads security settings of Internet Explorer
- explorer.exe (PID: 2236)
Checks proxy server information
- SteamTools.exe (PID: 5772)
The sample compiled with english language support
- st-setup-1.8.16.exe (PID: 8116)
Creates files or folders in the user directory
- st-setup-1.8.16.exe (PID: 8116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
165
Monitored processes
29
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1568 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | icacls.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1804 | icacls "C:\Program Files\SteamTools" /grant:r "*S-1-5-32-545:(OI)(CI)F" /T | C:\Windows\System32\icacls.exe | — | st-setup-1.8.16.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2236 | C:\WINDOWS\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5688 --field-trial-handle=1860,i,14358515233685263115,993297863580164132,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 5344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6708 --field-trial-handle=1860,i,14358515233685263115,993297863580164132,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 5512 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | icacls.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5588 | icacls "C:\Program Files\SteamTools\*.*" /grant:r "*S-1-5-32-545:(OI)(CI)F" | C:\Windows\System32\icacls.exe | — | st-setup-1.8.16.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5684 --field-trial-handle=1860,i,14358515233685263115,993297863580164132,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 5772 | "C:\Program Files\SteamTools\SteamTools.exe" | C:\Program Files\SteamTools\SteamTools.exe | cmd.exe | ||||||||||||
User: admin Company: steamtools.net Integrity Level: MEDIUM Description: Steamtools Version: 1.8.1.5 Modules
| |||||||||||||||
| 5800 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\SteamTools_launcher.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 738
Read events
8 718
Write events
20
Delete events
0
Modification events
| (PID) Process: | (7192) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7192) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7192) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7192) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7192) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (5344) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 01000000000000003B2829790FABDB01 | |||
| (PID) Process: | (8116) st-setup-1.8.16.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\SteamTools |
| Operation: | write | Name: | DisplayName |
Value: SteamTools | |||
| (PID) Process: | (8116) st-setup-1.8.16.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\SteamTools |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\SteamTools\Uninstall.exe" | |||
| (PID) Process: | (8116) st-setup-1.8.16.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\SteamTools |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Program Files\SteamTools\Uninstall.exe" /S | |||
| (PID) Process: | (8116) st-setup-1.8.16.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\SteamTools |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\SteamTools | |||
Executable files
21
Suspicious files
42
Text files
22
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10dad1.TMP | — | |
MD5:— | SHA256:— | |||
| 7192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10dae1.TMP | — | |
MD5:— | SHA256:— | |||
| 7192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10dae1.TMP | — | |
MD5:— | SHA256:— | |||
| 7192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10dae1.TMP | — | |
MD5:— | SHA256:— | |||
| 7192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10dae1.TMP | — | |
MD5:— | SHA256:— | |||
| 7192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
76
DNS requests
89
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.158:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1240 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5772 | SteamTools.exe | GET | 302 | 119.188.209.185:80 | http://new-service.biliapi.net/picture/chatres/update/version2.txt | unknown | — | — | unknown |
1240 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5772 | SteamTools.exe | GET | 200 | 8.133.135.83:80 | http://stools.oss-cn-shanghai.aliyuncs.com/version2.txt | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.158:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7192 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7360 | chrome.exe | 172.67.74.16:443 | www.steamtools.net | CLOUDFLARENET | US | malicious |
7360 | chrome.exe | 142.250.153.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
7360 | chrome.exe | 104.16.80.73:443 | static.cloudflareinsights.com | CLOUDFLARENET | — | whitelisted |
7360 | chrome.exe | 216.58.206.74:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
7360 | chrome.exe | 142.250.186.131:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.steamtools.net |
| malicious |
accounts.google.com |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7360 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7360 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7360 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7360 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
5772 | SteamTools.exe | Misc activity | INFO [ANY.RUN] USER_AGENTS Suspicious User-Agent (Mozilla/5.0) |
2196 | svchost.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
5772 | SteamTools.exe | Misc activity | INFO [ANY.RUN] USER_AGENTS Suspicious User-Agent (Mozilla/5.0) |
7360 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7360 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |