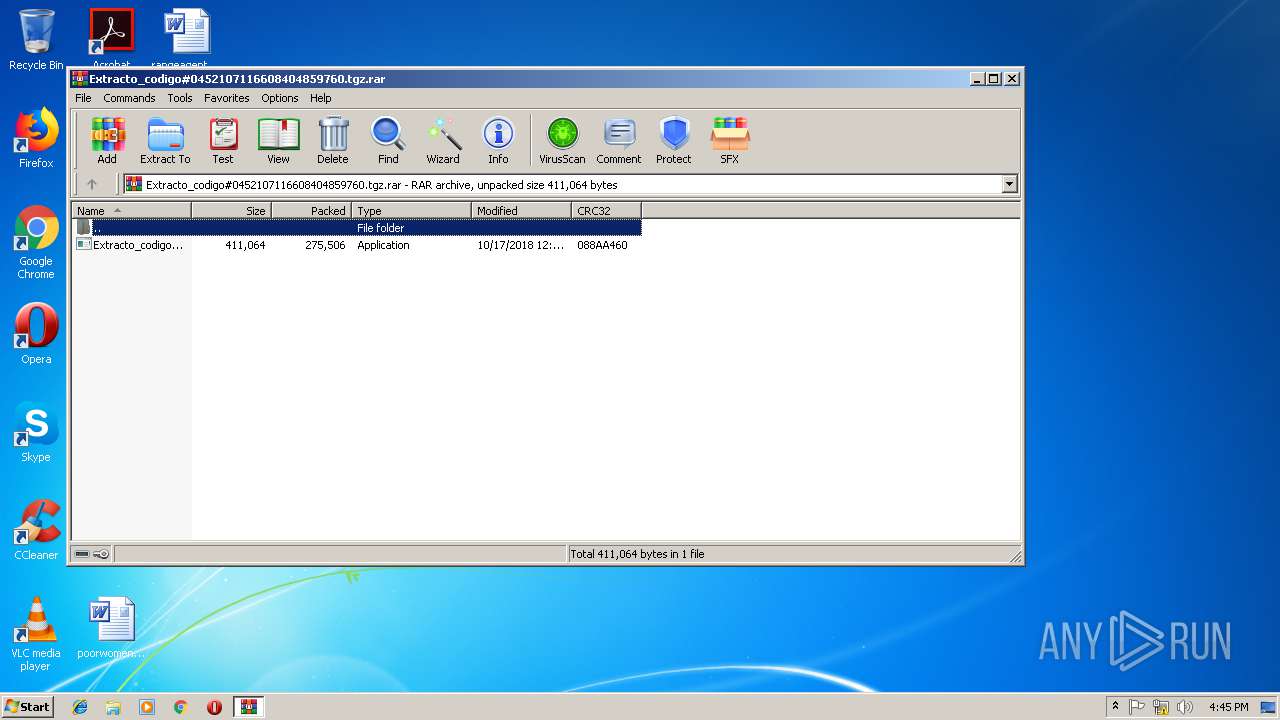
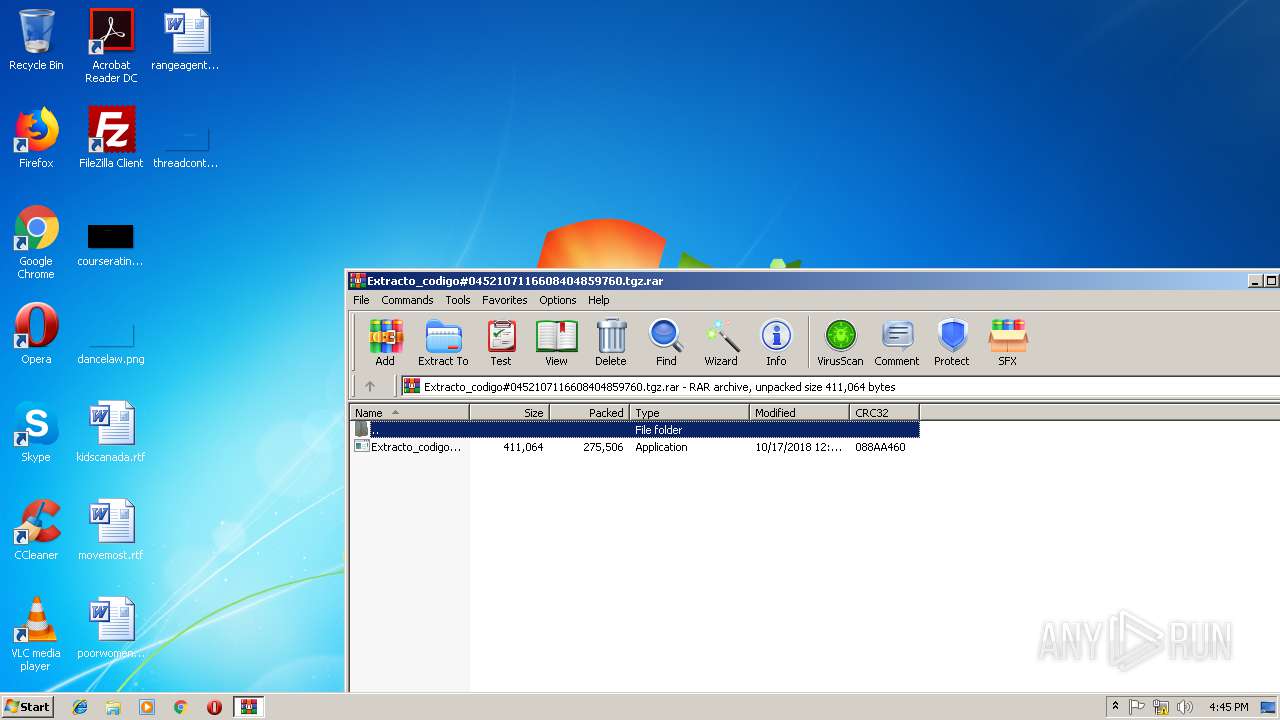
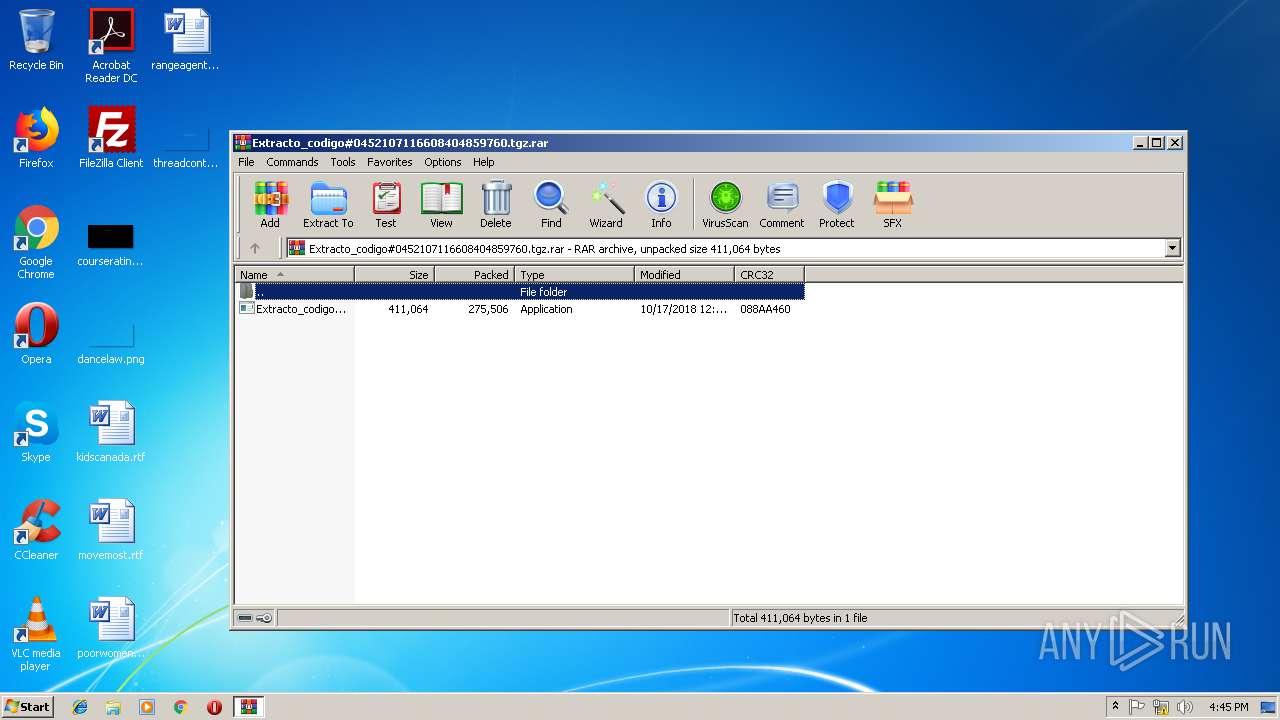
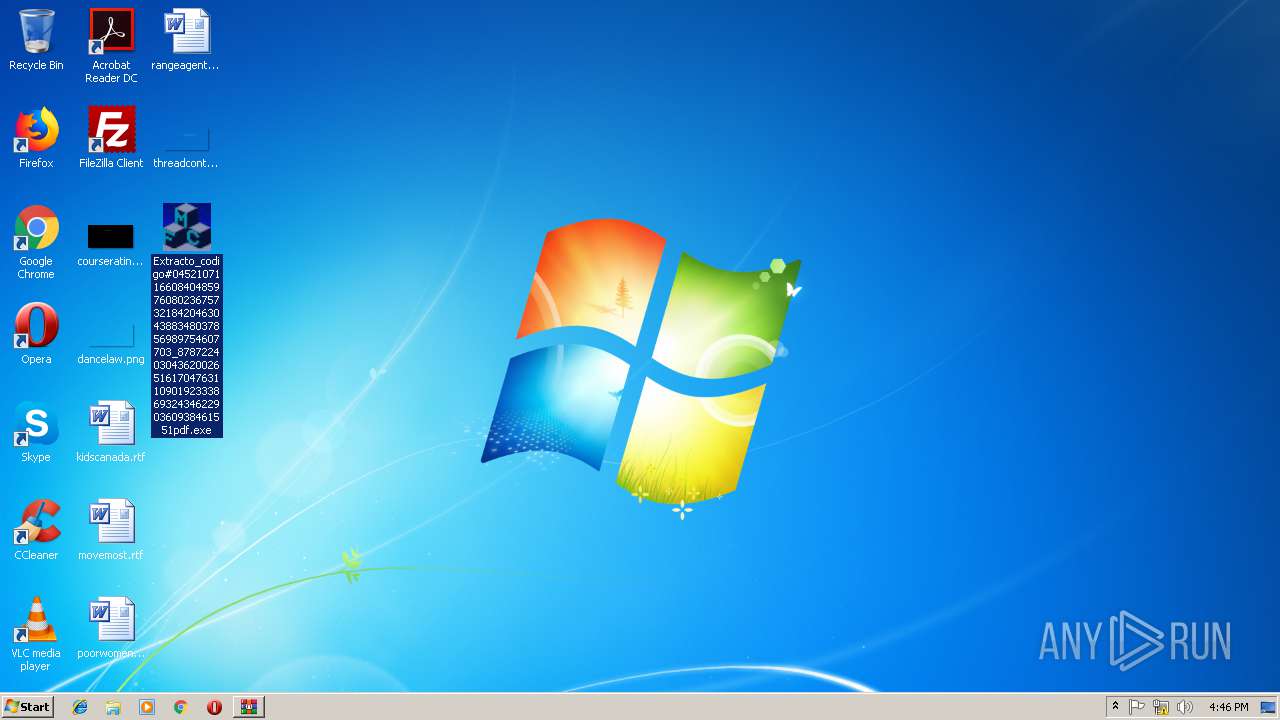
| File name: | Extracto_codigo#0452107116608404859760.tgz |
| Full analysis: | https://app.any.run/tasks/fea180e2-1161-45b3-a4f9-f46db1b24fb3 |
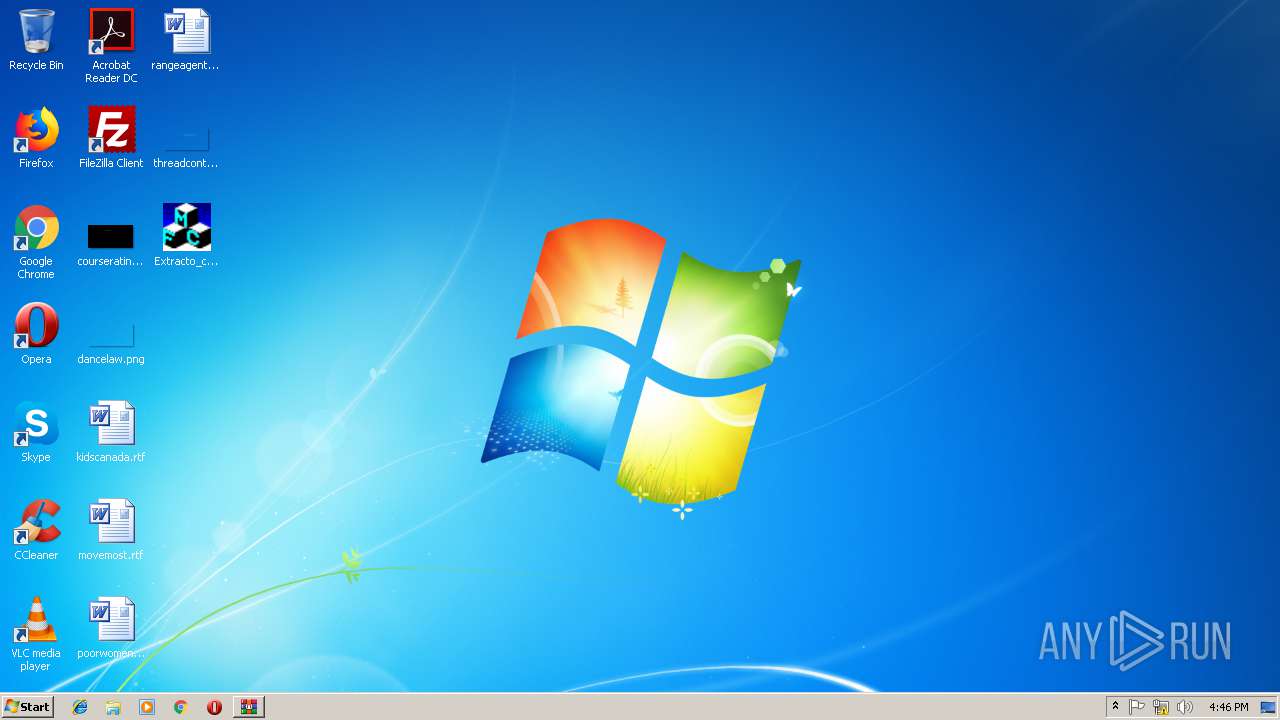
| Verdict: | Malicious activity |
| Analysis date: | November 15, 2018, 16:45:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | BE54B84ECC598EB7E02464B575BB894C |
| SHA1: | A74256F4FFE8AFCE51E3D234A7858297DF53BF9F |
| SHA256: | 3EAD5826E63B641144F4CA1E1675FAE15960E1BEABC1D31D6F1F4838657B382E |
| SSDEEP: | 6144:hHVJ4VONwdw+F2uebVtEbKGJIWg2wP6CY0v+tcepHCFqox:TJ4bBhkVt4/JIJyE+S |
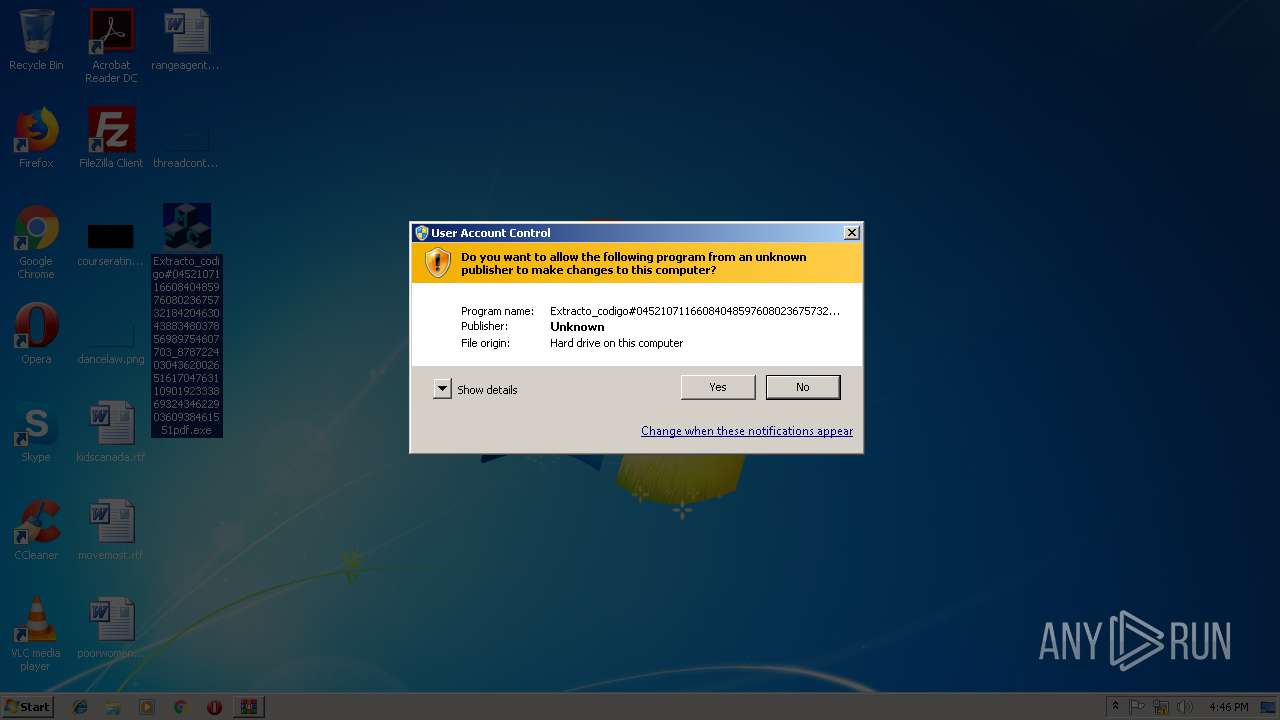
MALICIOUS
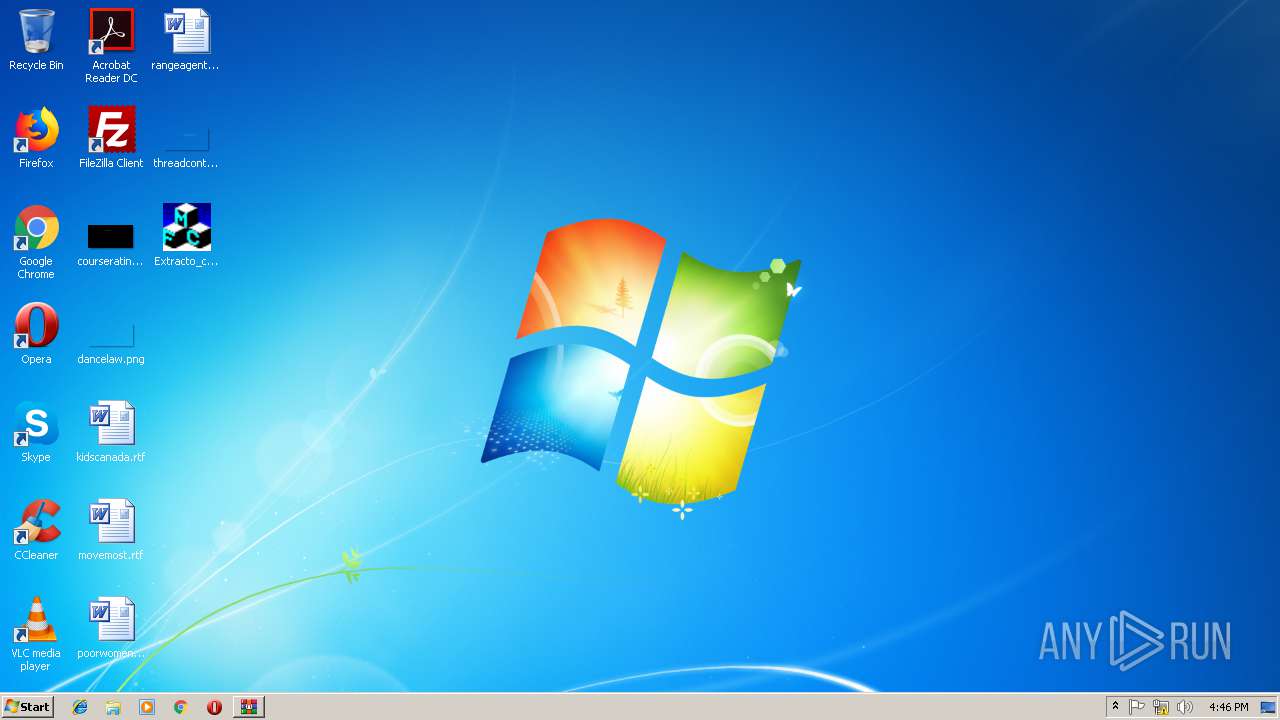
Application was dropped or rewritten from another process
- Extracto_codigo#045210711660840485976080236757321842046304388348037856989754607703_8787224030436200265161704763110901923338693243462290360938461551pdf.exe (PID: 2640)
- Extracto_codigo#045210711660840485976080236757321842046304388348037856989754607703_8787224030436200265161704763110901923338693243462290360938461551pdf.exe (PID: 2528)
- Extracto_codigo#045210711660840485976080236757321842046304388348037856989754607703_8787224030436200265161704763110901923338693243462290360938461551pdf.exe (PID: 3564)
- Extracto_codigo#045210711660840485976080236757321842046304388348037856989754607703_8787224030436200265161704763110901923338693243462290360938461551pdf.exe (PID: 3924)
- Extracto_codigo#045210711660840485976080236757321842046304388348037856989754607703_8787224030436200265161704763110901923338693243462290360938461551pdf.exe (PID: 1852)
Changes the autorun value in the registry
- Extracto_codigo#045210711660840485976080236757321842046304388348037856989754607703_8787224030436200265161704763110901923338693243462290360938461551pdf.exe (PID: 3564)
- Extracto_codigo#045210711660840485976080236757321842046304388348037856989754607703_8787224030436200265161704763110901923338693243462290360938461551pdf.exe (PID: 1852)
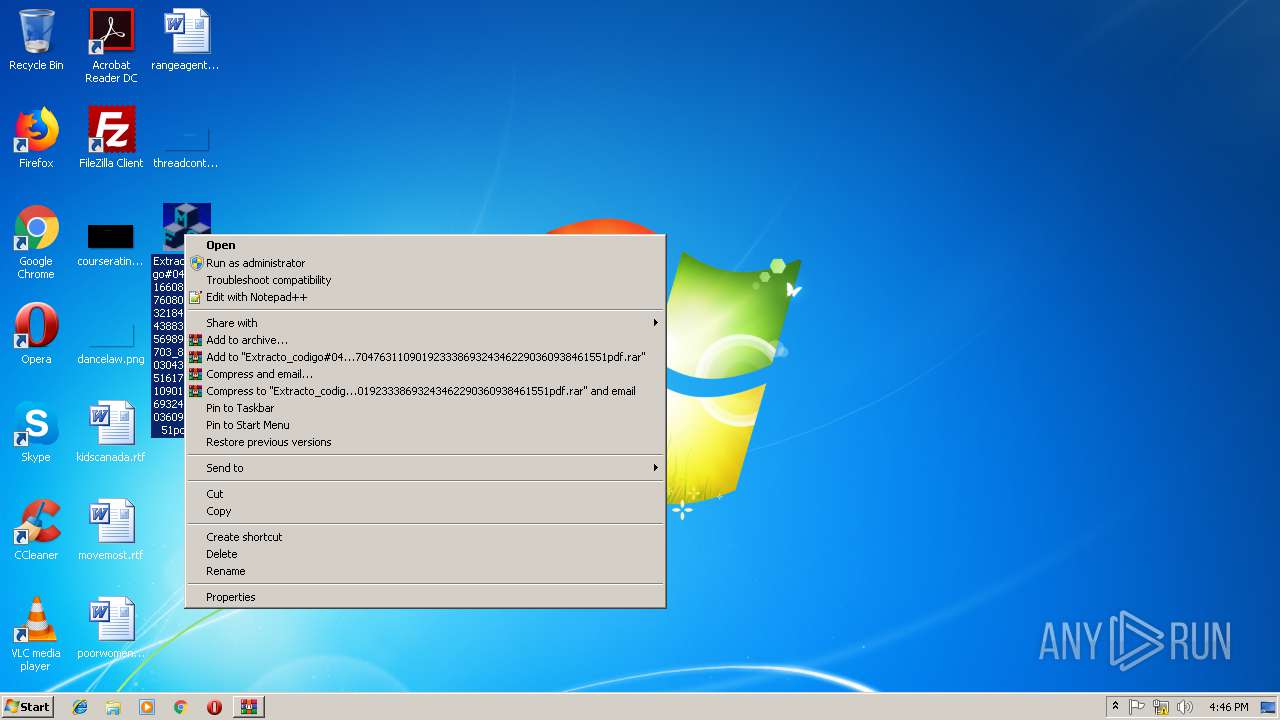
SUSPICIOUS
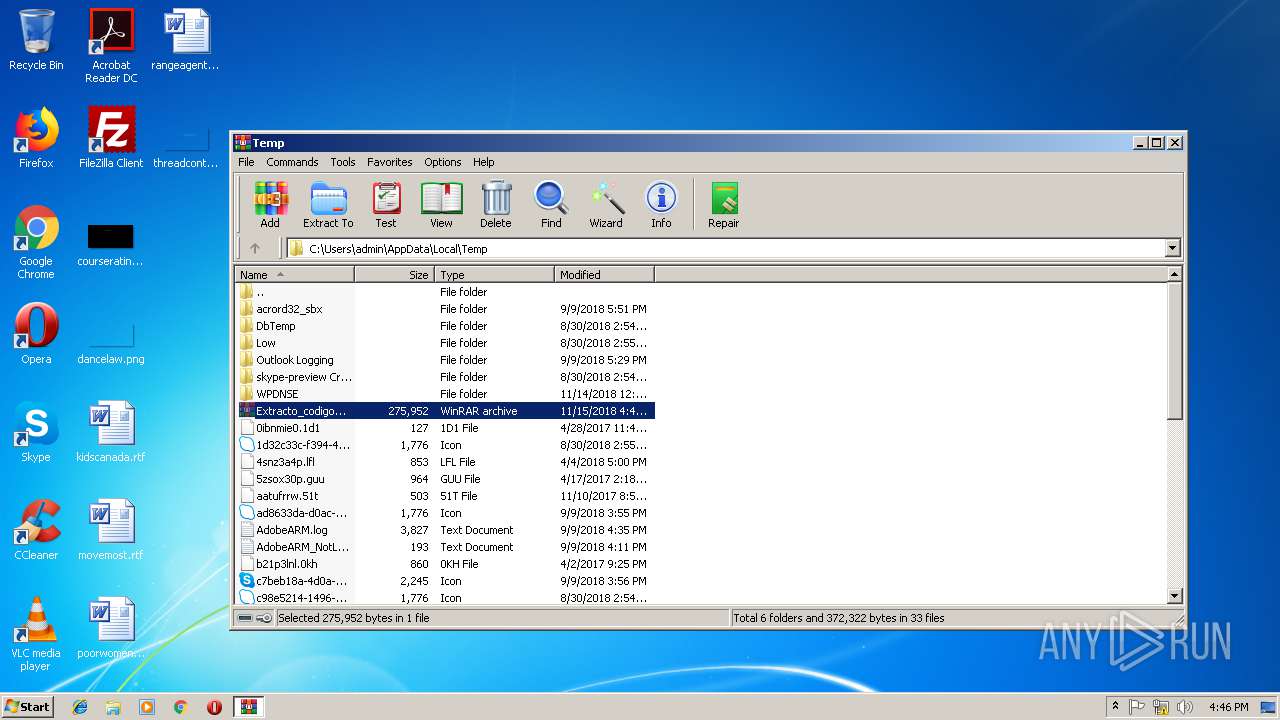
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3244)
- Extracto_codigo#045210711660840485976080236757321842046304388348037856989754607703_8787224030436200265161704763110901923338693243462290360938461551pdf.exe (PID: 3564)
Application launched itself
- Extracto_codigo#045210711660840485976080236757321842046304388348037856989754607703_8787224030436200265161704763110901923338693243462290360938461551pdf.exe (PID: 2640)
- Extracto_codigo#045210711660840485976080236757321842046304388348037856989754607703_8787224030436200265161704763110901923338693243462290360938461551pdf.exe (PID: 2528)
Creates files in the user directory
- Extracto_codigo#045210711660840485976080236757321842046304388348037856989754607703_8787224030436200265161704763110901923338693243462290360938461551pdf.exe (PID: 3564)
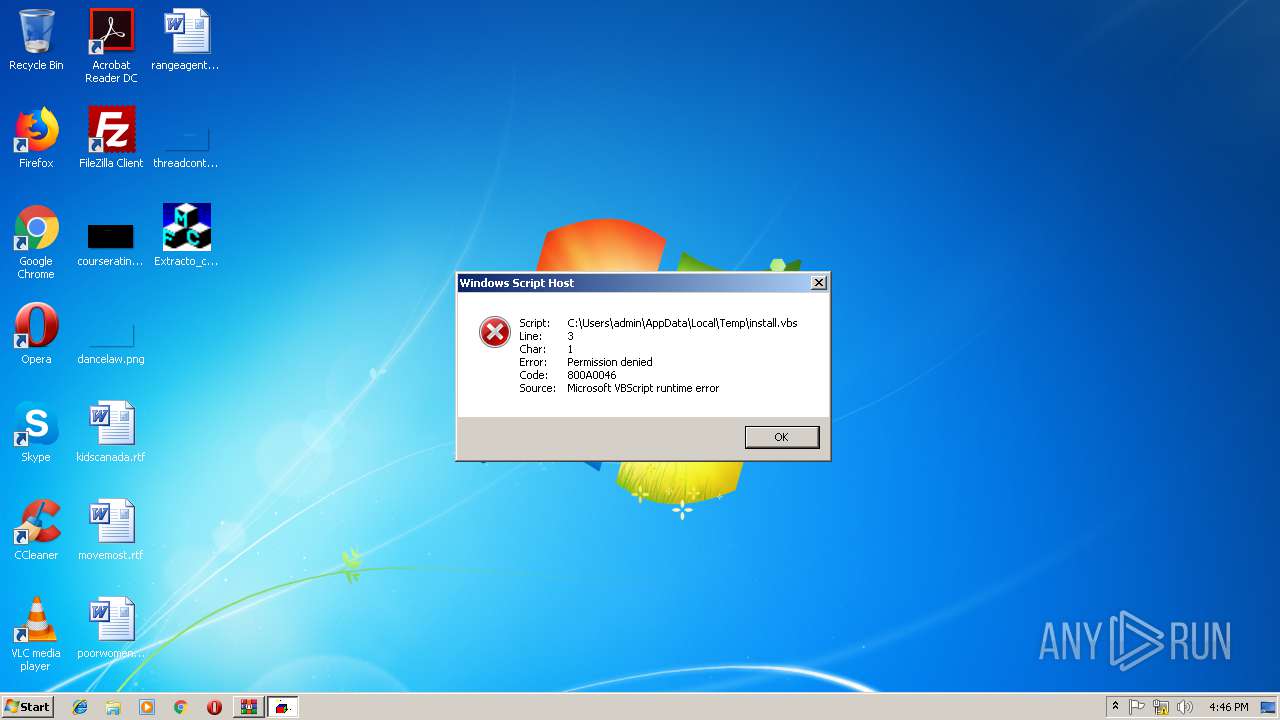
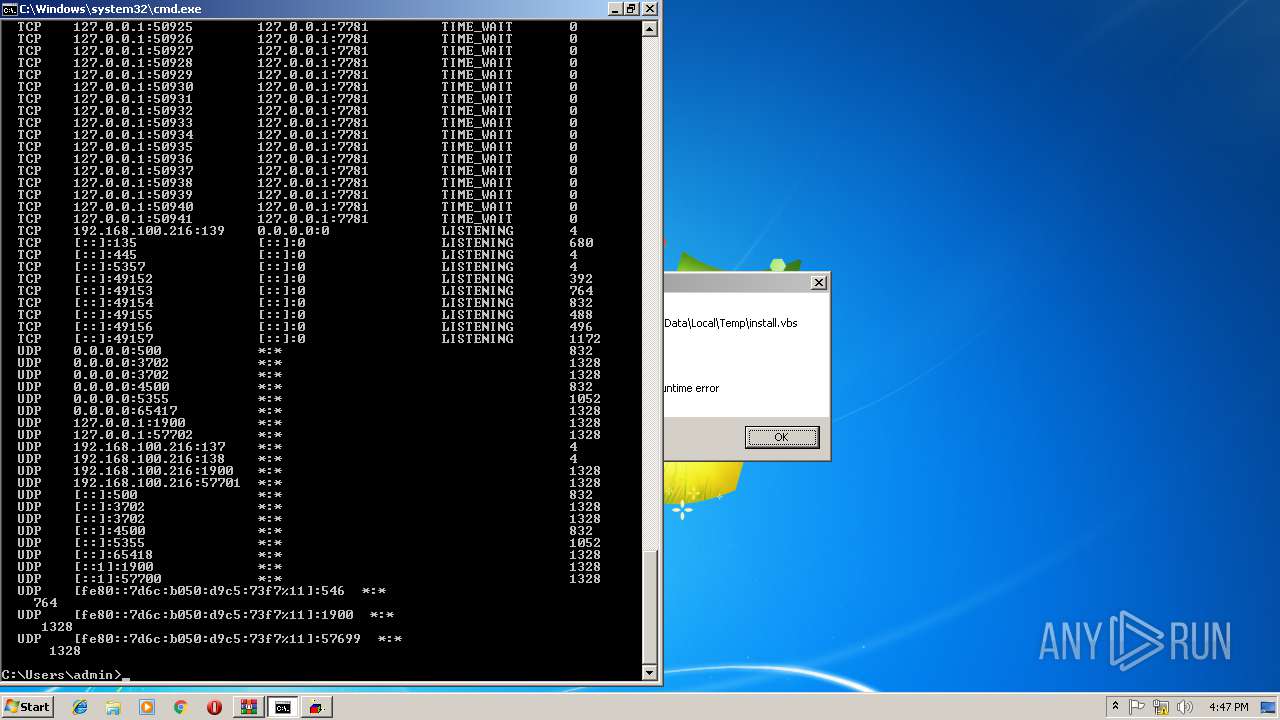
Executes scripts
- Extracto_codigo#045210711660840485976080236757321842046304388348037856989754607703_8787224030436200265161704763110901923338693243462290360938461551pdf.exe (PID: 3564)
- Extracto_codigo#045210711660840485976080236757321842046304388348037856989754607703_8787224030436200265161704763110901923338693243462290360938461551pdf.exe (PID: 1852)
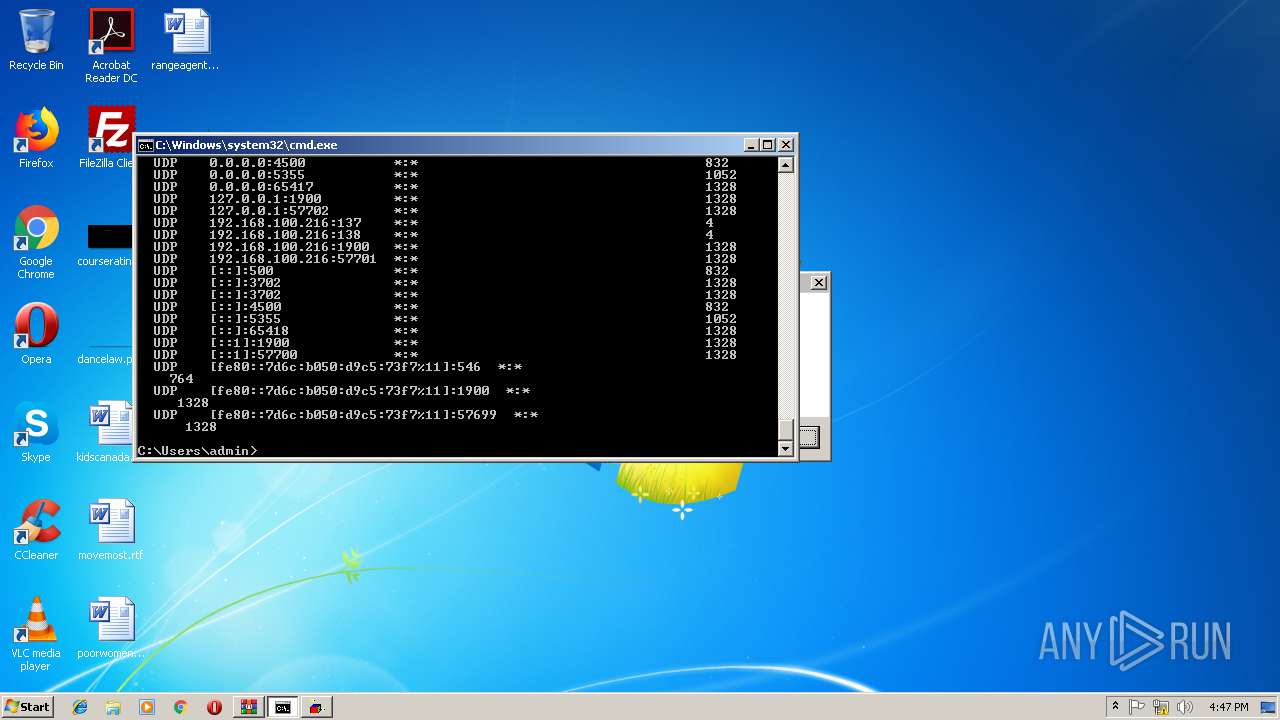
Uses NETSTAT.EXE to discover network connections
- cmd.exe (PID: 2276)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
46
Monitored processes
10
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1852 | "C:\Users\admin\Desktop\Extracto_codigo#045210711660840485976080236757321842046304388348037856989754607703_8787224030436200265161704763110901923338693243462290360938461551pdf.exe" | C:\Users\admin\Desktop\Extracto_codigo#045210711660840485976080236757321842046304388348037856989754607703_8787224030436200265161704763110901923338693243462290360938461551pdf.exe | Extracto_codigo#045210711660840485976080236757321842046304388348037856989754607703_8787224030436200265161704763110901923338693243462290360938461551pdf.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Demo2_CPropertyGrid_Lib Microsoft 基础类应用程序 Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2276 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2300 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\install.vbs" | C:\Windows\System32\WScript.exe | — | Extracto_codigo#045210711660840485976080236757321842046304388348037856989754607703_8787224030436200265161704763110901923338693243462290360938461551pdf.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2528 | "C:\Users\admin\Desktop\Extracto_codigo#045210711660840485976080236757321842046304388348037856989754607703_8787224030436200265161704763110901923338693243462290360938461551pdf.exe" | C:\Users\admin\Desktop\Extracto_codigo#045210711660840485976080236757321842046304388348037856989754607703_8787224030436200265161704763110901923338693243462290360938461551pdf.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Demo2_CPropertyGrid_Lib Microsoft 基础类应用程序 Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2640 | "C:\Users\admin\Desktop\Extracto_codigo#045210711660840485976080236757321842046304388348037856989754607703_8787224030436200265161704763110901923338693243462290360938461551pdf.exe" | C:\Users\admin\Desktop\Extracto_codigo#045210711660840485976080236757321842046304388348037856989754607703_8787224030436200265161704763110901923338693243462290360938461551pdf.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Demo2_CPropertyGrid_Lib Microsoft 基础类应用程序 Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2772 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\install.vbs" | C:\Windows\System32\WScript.exe | — | Extracto_codigo#045210711660840485976080236757321842046304388348037856989754607703_8787224030436200265161704763110901923338693243462290360938461551pdf.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3156 | netstat -ano | C:\Windows\system32\NETSTAT.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Netstat Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3244 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Extracto_codigo#0452107116608404859760.tgz.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3564 | "C:\Users\admin\Desktop\Extracto_codigo#045210711660840485976080236757321842046304388348037856989754607703_8787224030436200265161704763110901923338693243462290360938461551pdf.exe" | C:\Users\admin\Desktop\Extracto_codigo#045210711660840485976080236757321842046304388348037856989754607703_8787224030436200265161704763110901923338693243462290360938461551pdf.exe | Extracto_codigo#045210711660840485976080236757321842046304388348037856989754607703_8787224030436200265161704763110901923338693243462290360938461551pdf.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Demo2_CPropertyGrid_Lib Microsoft 基础类应用程序 Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3924 | "C:\Users\admin\Desktop\Extracto_codigo#045210711660840485976080236757321842046304388348037856989754607703_8787224030436200265161704763110901923338693243462290360938461551pdf.exe" | C:\Users\admin\Desktop\Extracto_codigo#045210711660840485976080236757321842046304388348037856989754607703_8787224030436200265161704763110901923338693243462290360938461551pdf.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Demo2_CPropertyGrid_Lib Microsoft 基础类应用程序 Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
1 182
Read events
1 153
Write events
29
Delete events
0
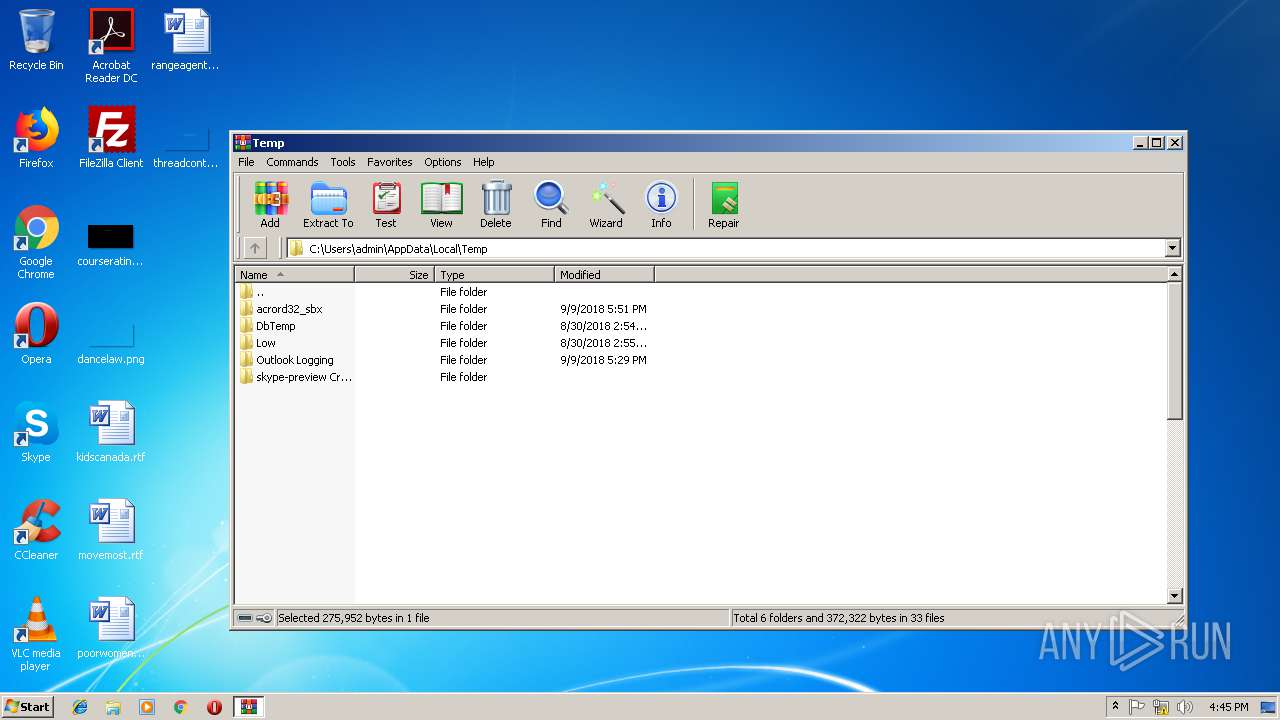
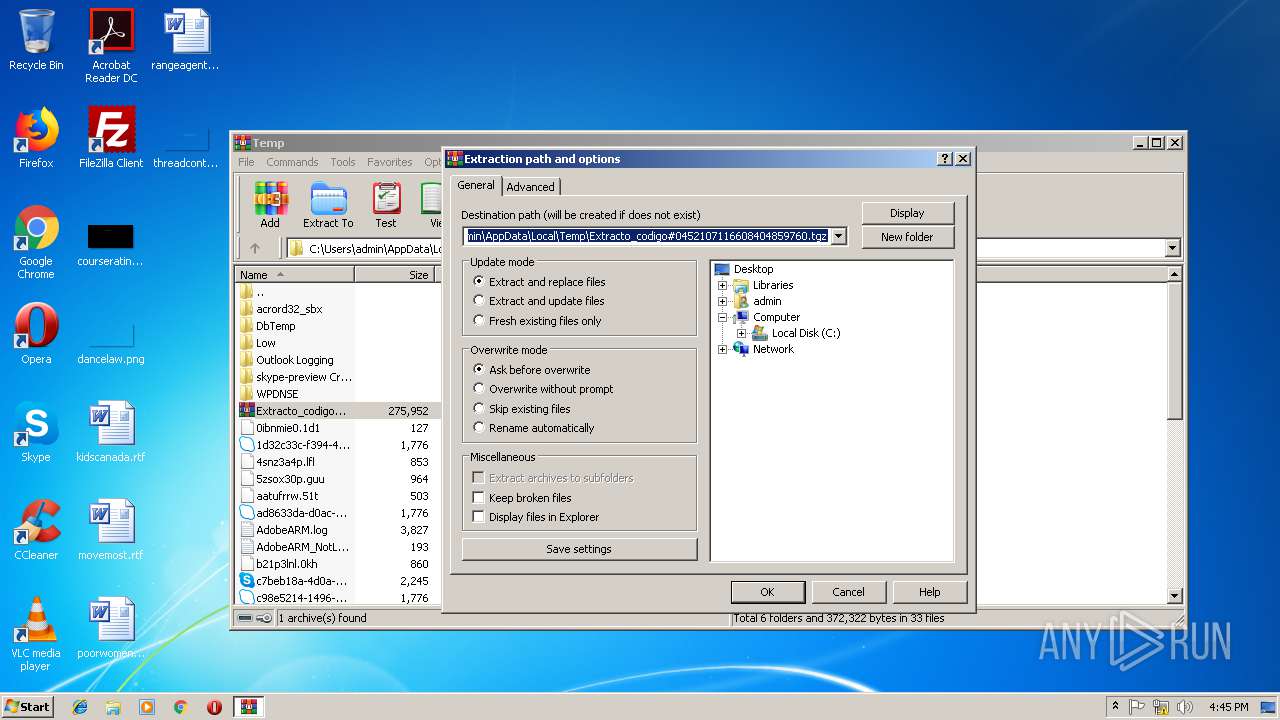
Modification events
| (PID) Process: | (3244) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3244) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3244) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3244) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Extracto_codigo#0452107116608404859760.tgz.rar | |||
| (PID) Process: | (3244) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3244) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3244) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3244) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3244) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3244) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1852 | Extracto_codigo#045210711660840485976080236757321842046304388348037856989754607703_8787224030436200265161704763110901923338693243462290360938461551pdf.exe | C:\Users\admin\AppData\Local\Temp\install.vbs | binary | |
MD5:— | SHA256:— | |||
| 3244 | WinRAR.exe | C:\Users\admin\Desktop\Extracto_codigo#045210711660840485976080236757321842046304388348037856989754607703_8787224030436200265161704763110901923338693243462290360938461551pdf.exe | executable | |
MD5:— | SHA256:— | |||
| 3564 | Extracto_codigo#045210711660840485976080236757321842046304388348037856989754607703_8787224030436200265161704763110901923338693243462290360938461551pdf.exe | C:\Users\admin\AppData\Local\Temp\install.vbs | binary | |
MD5:— | SHA256:— | |||
| 3564 | Extracto_codigo#045210711660840485976080236757321842046304388348037856989754607703_8787224030436200265161704763110901923338693243462290360938461551pdf.exe | C:\Users\admin\AppData\Roaming\System32\task.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report