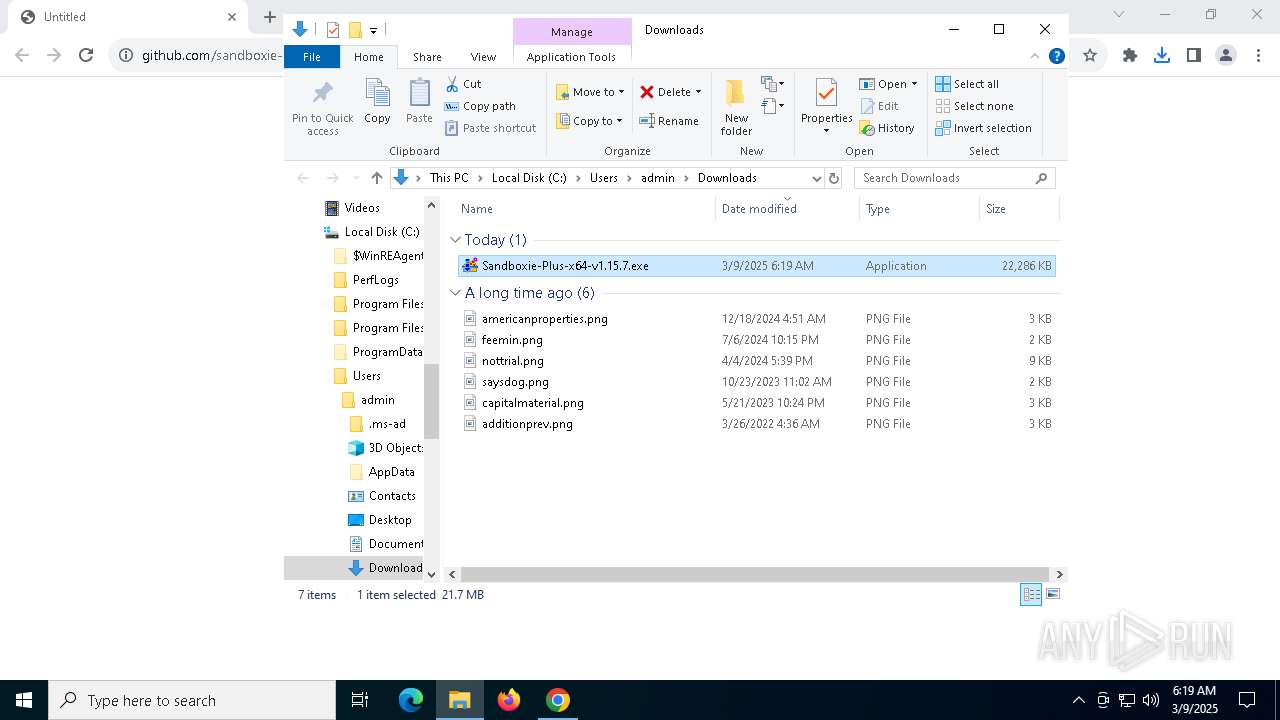
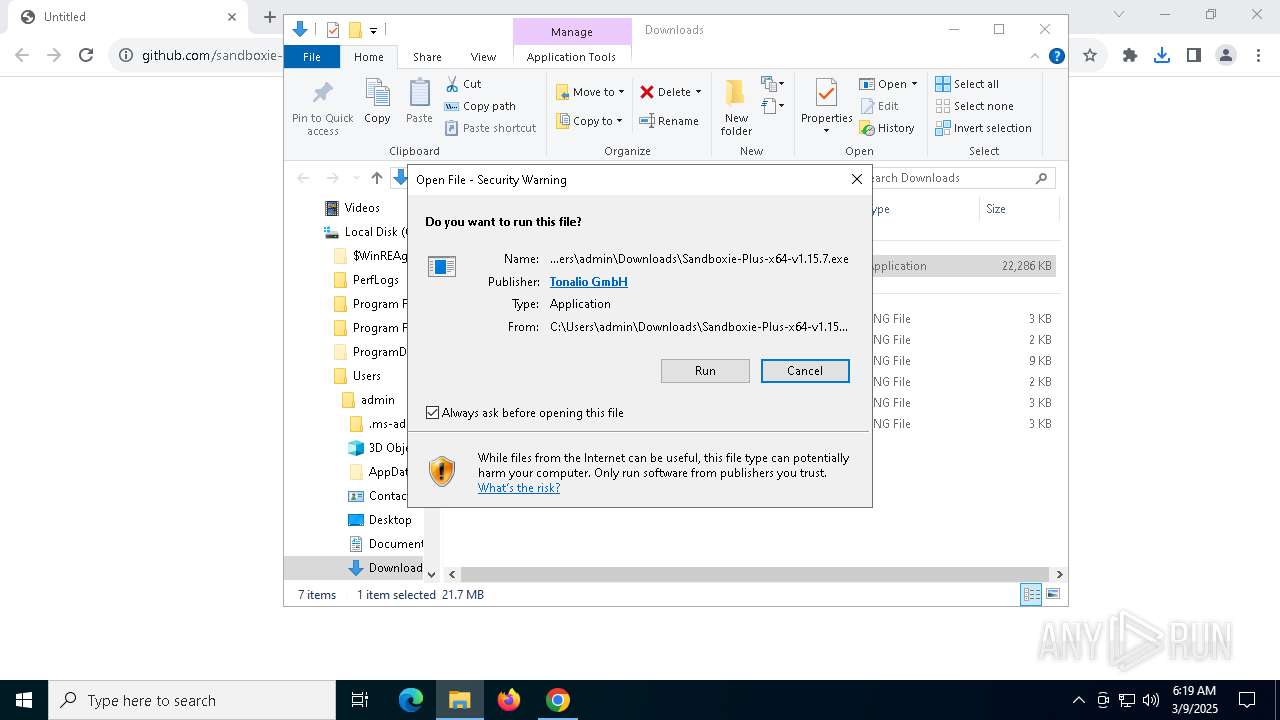
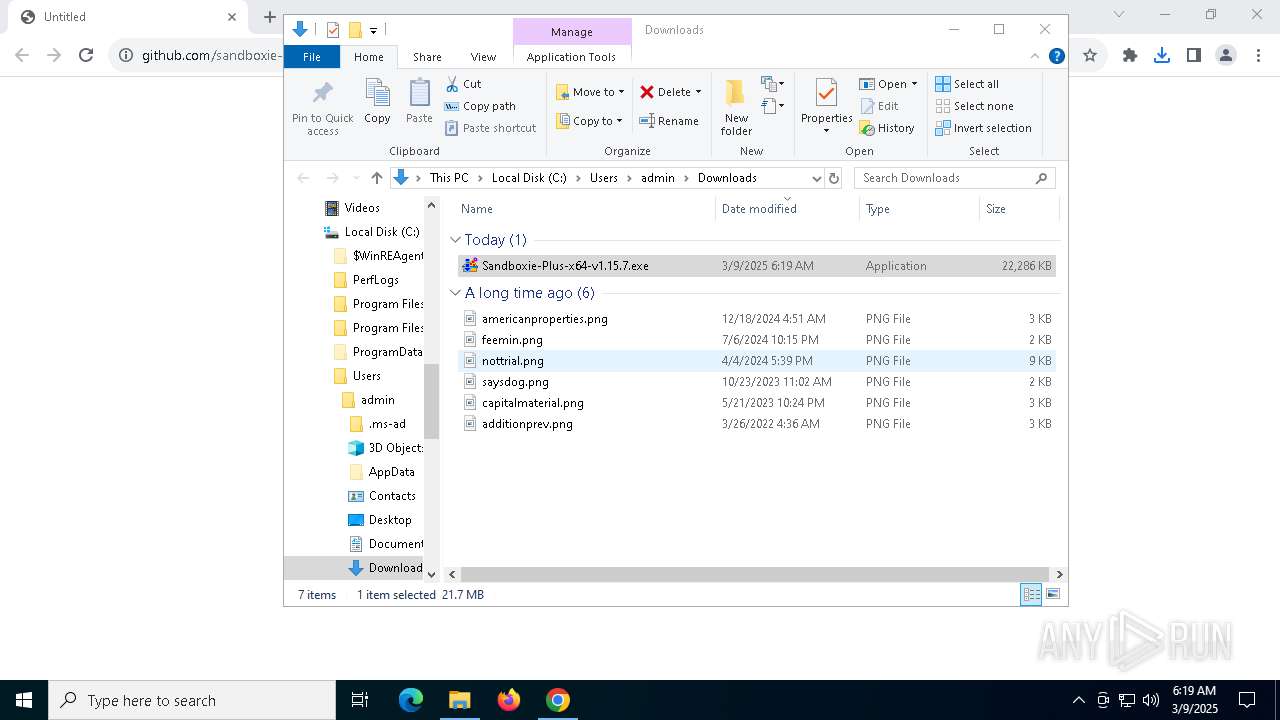
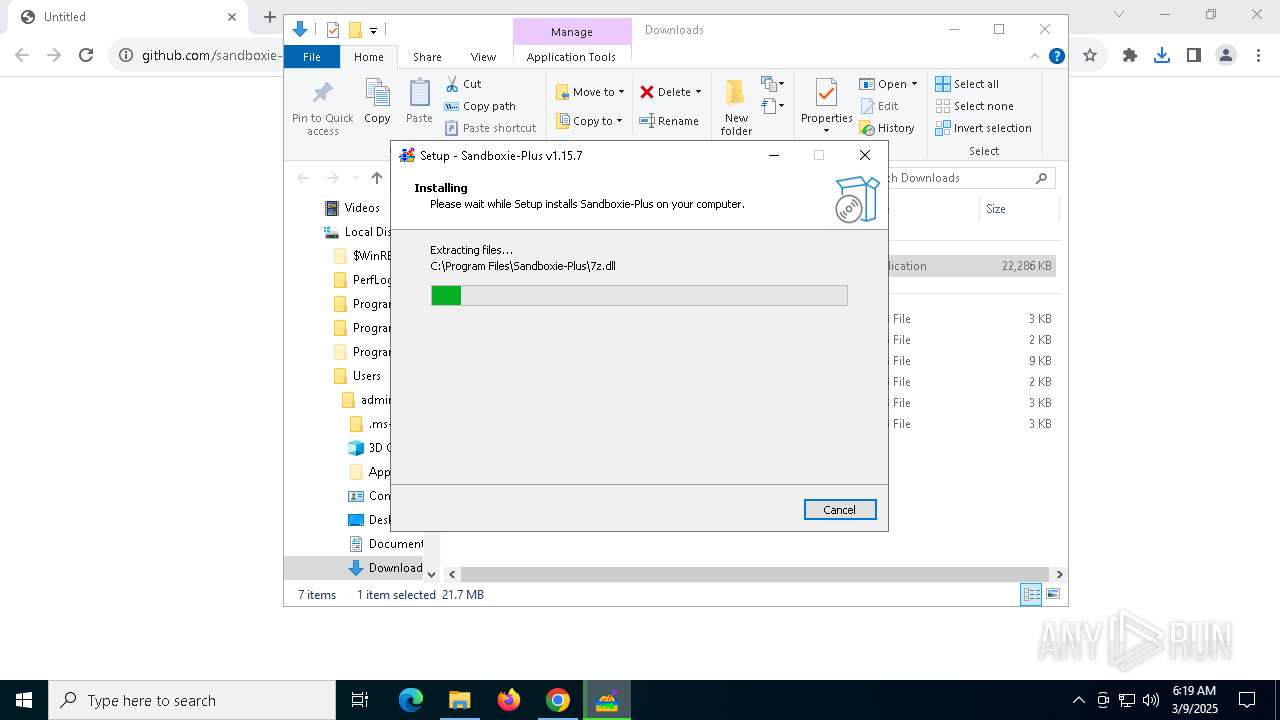
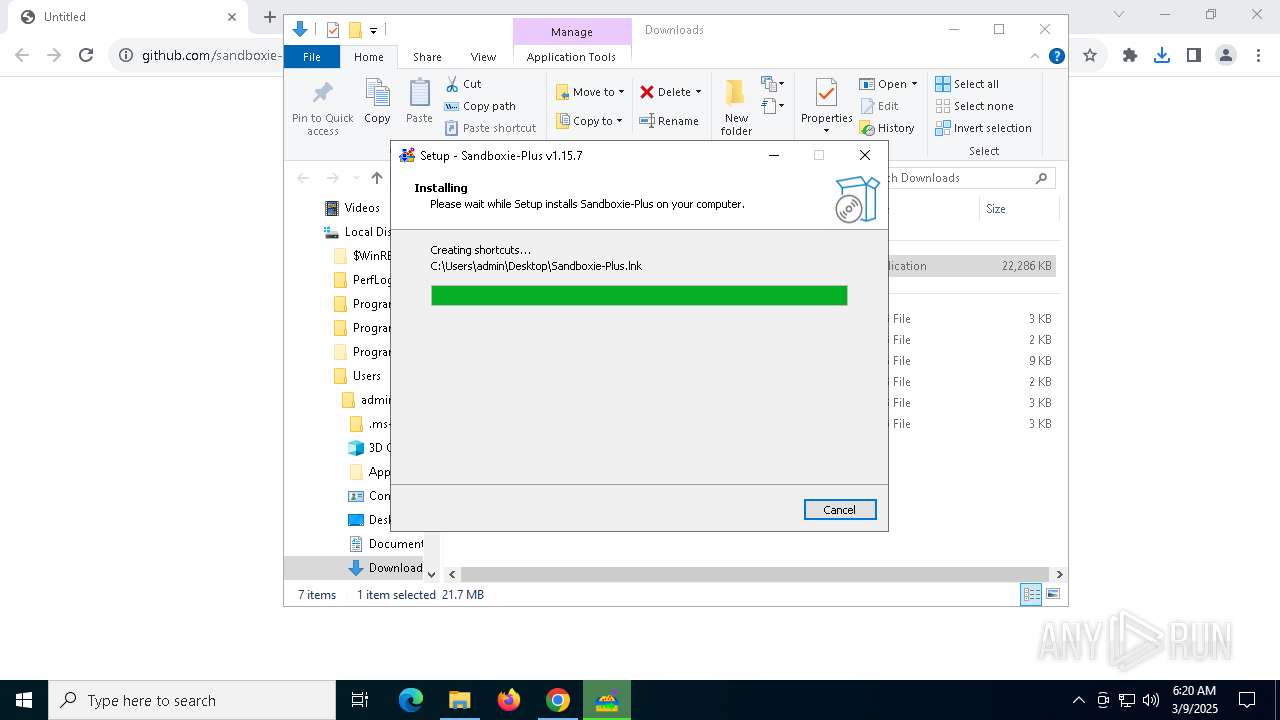
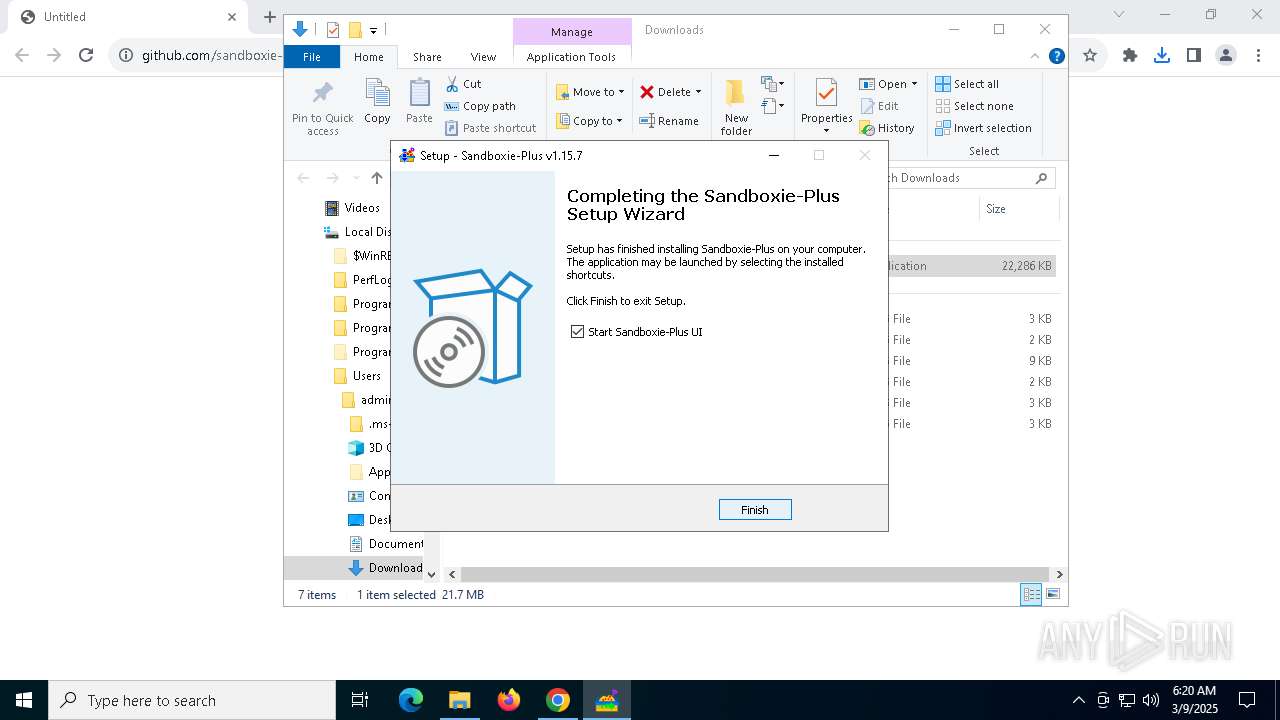
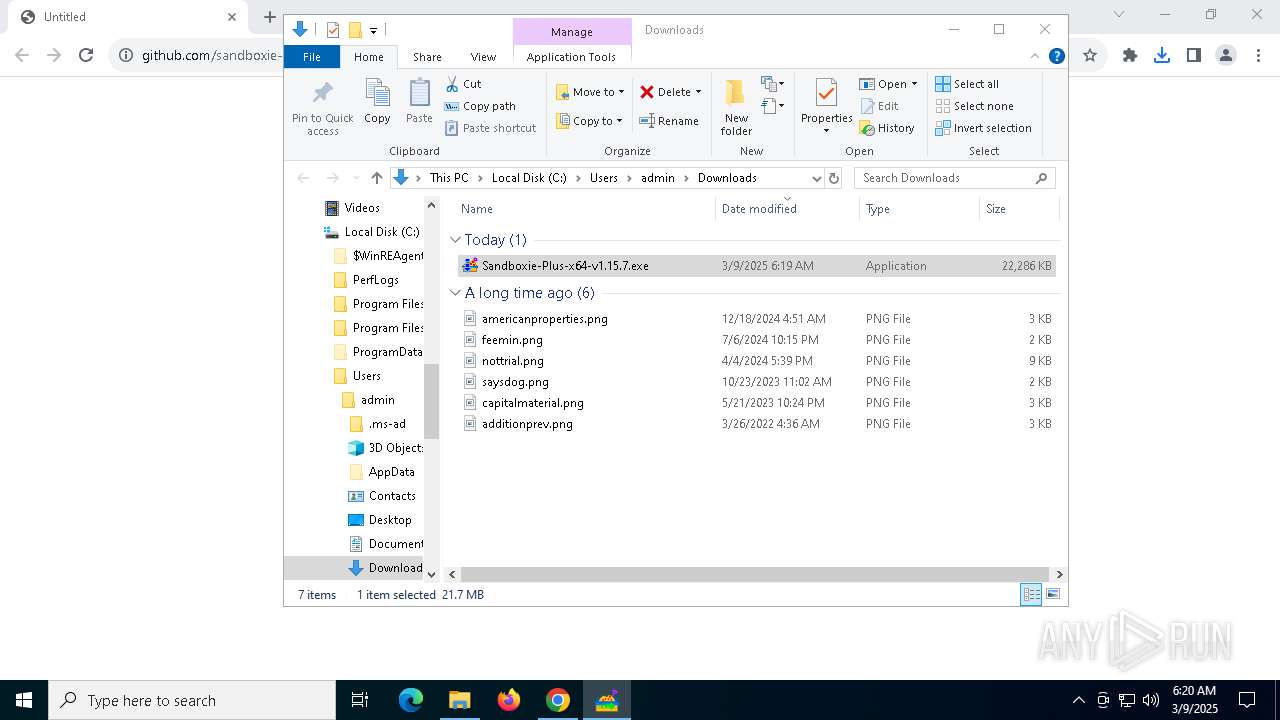
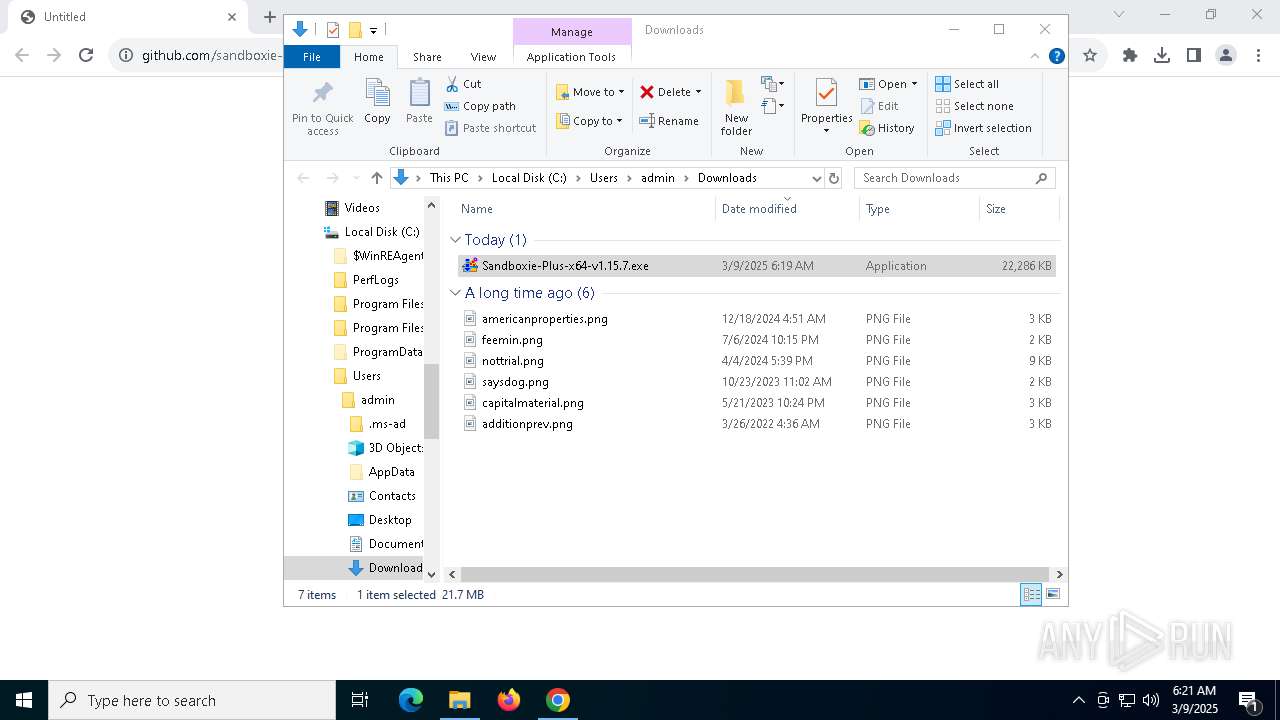
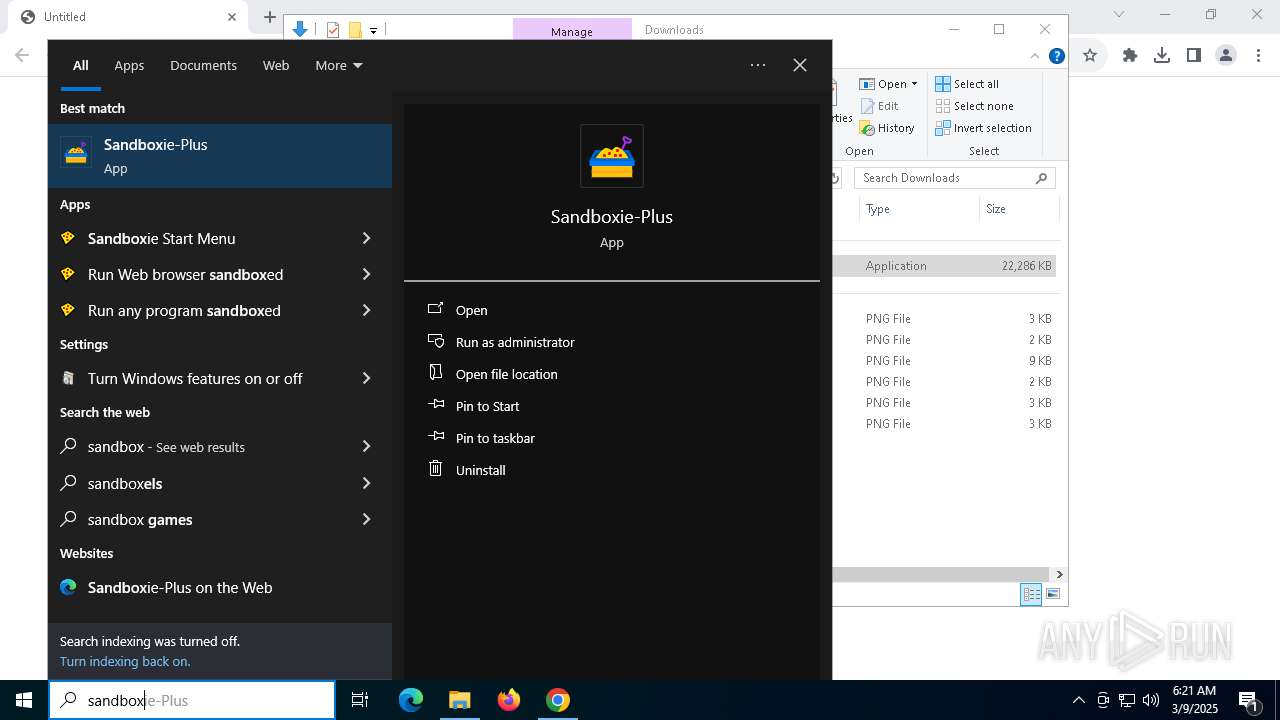
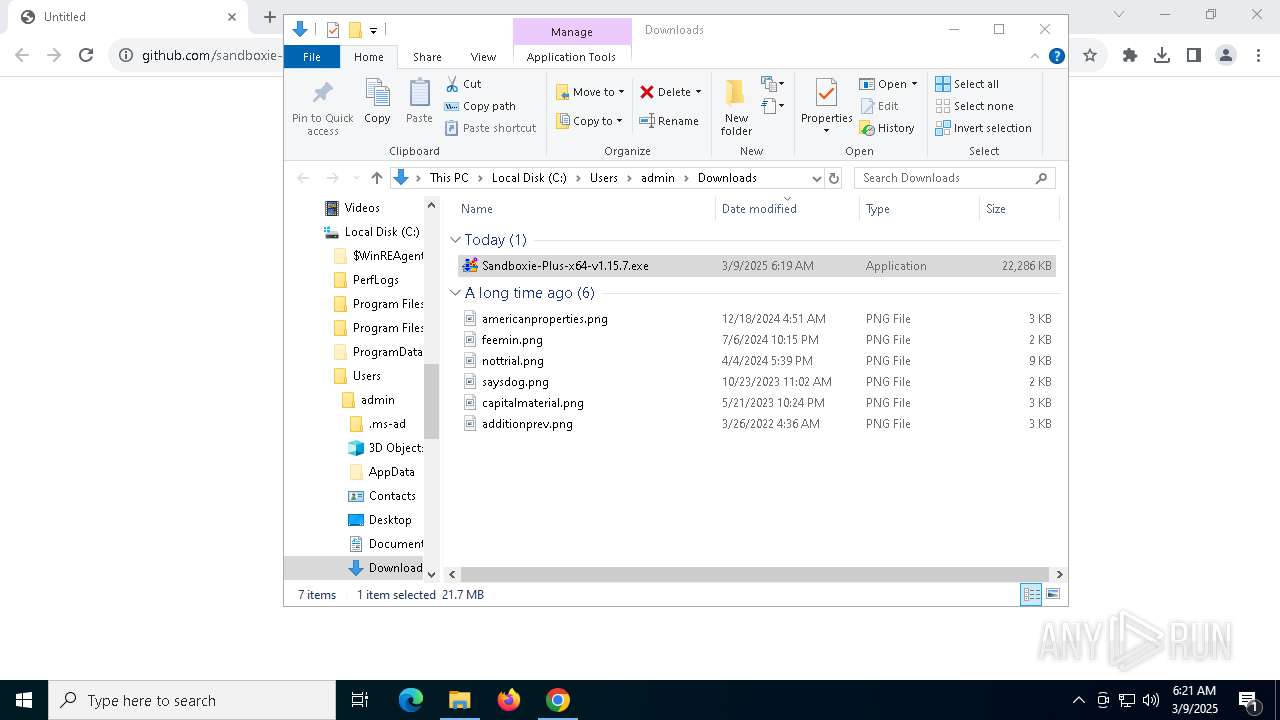
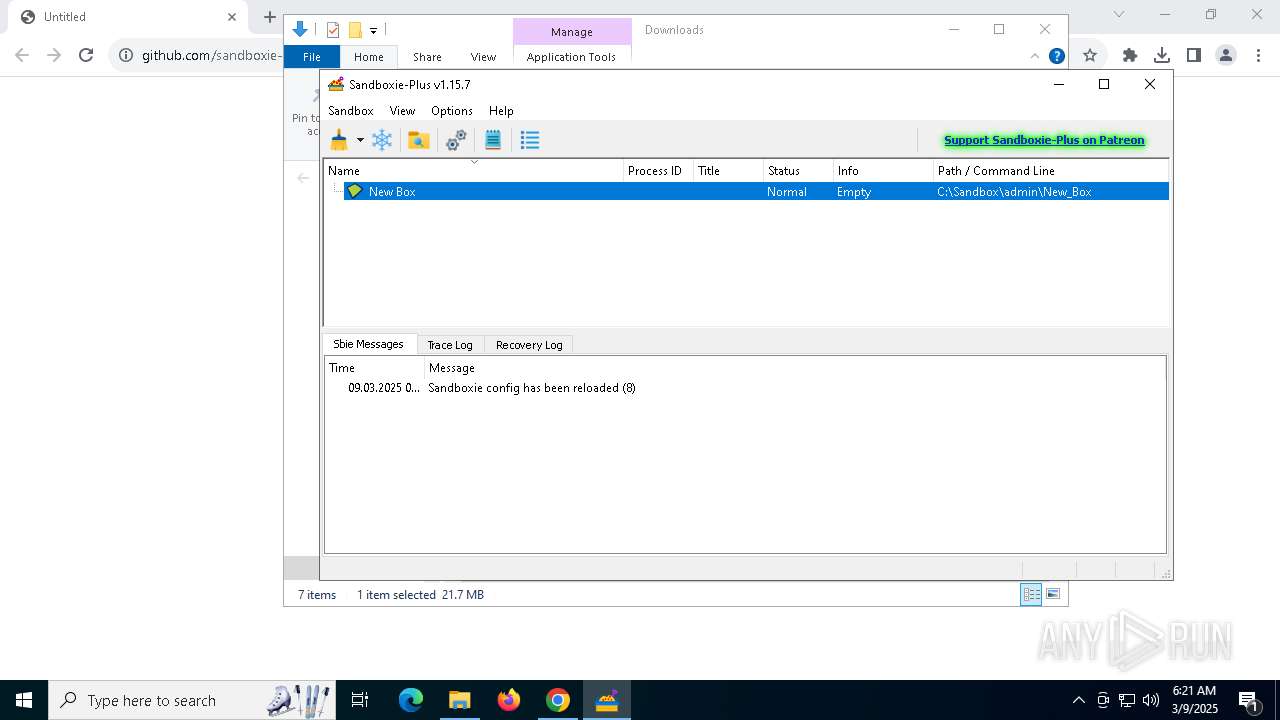
| URL: | https://github.com/sandboxie-plus/Sandboxie/releases/download/v1.15.7/Sandboxie-Plus-x64-v1.15.7.exe |
| Full analysis: | https://app.any.run/tasks/8f3427c1-dc7c-47ee-b68c-baa38653c18b |
| Verdict: | Malicious activity |
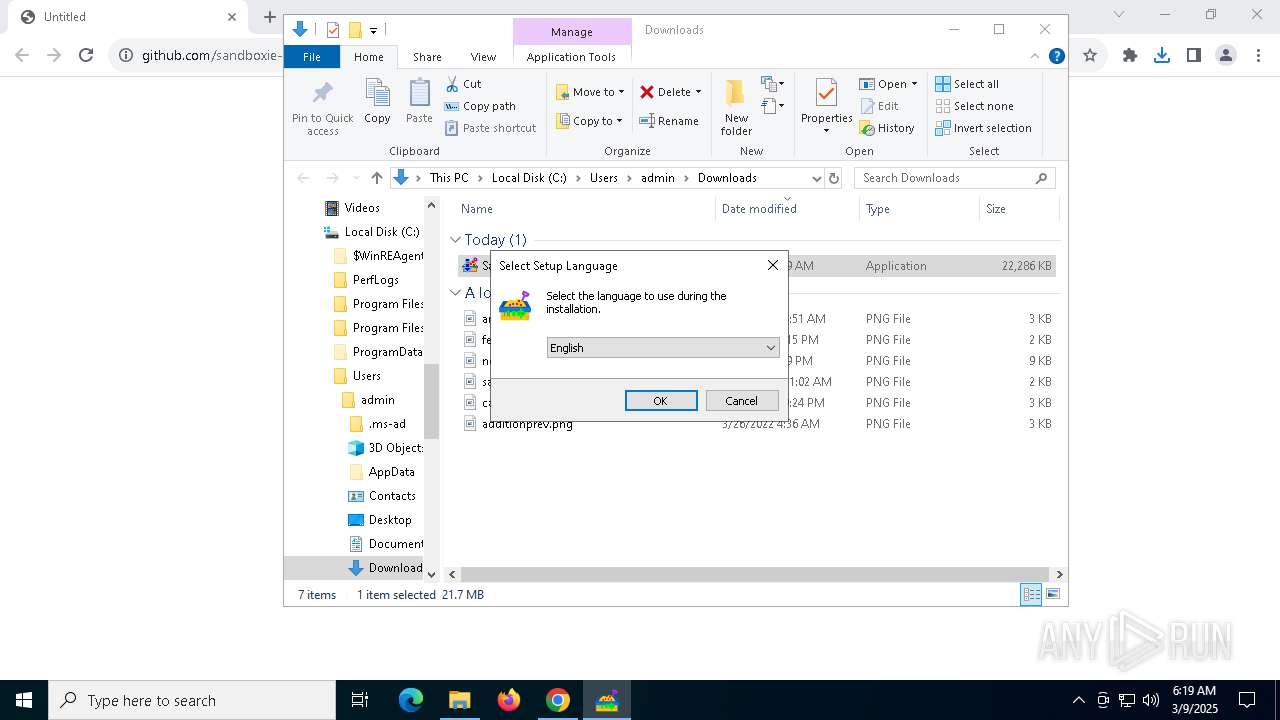
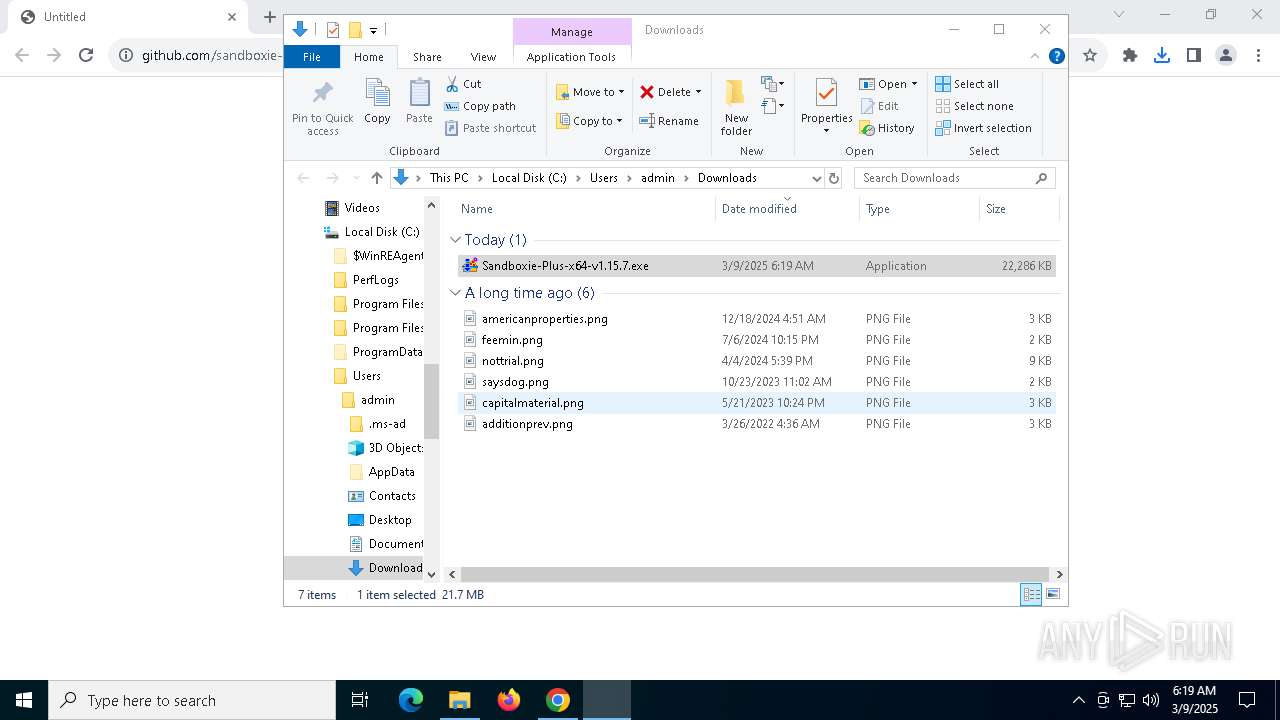
| Analysis date: | March 09, 2025, 06:19:17 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C51C8EF58C8EF36EE76F942E980D1CC1 |
| SHA1: | 7B8F16F10A6AD759F401C7D1456D76607C1F7ED7 |
| SHA256: | 3EAD49F88FB6E0604E55810434DA08648AC77991D8E31E1B20C5234EC0270C5D |
| SSDEEP: | 3:N8tEdmELxKdM674KkCmJLo6pEIn+dA:2uwi9CFsFo6pPiA |
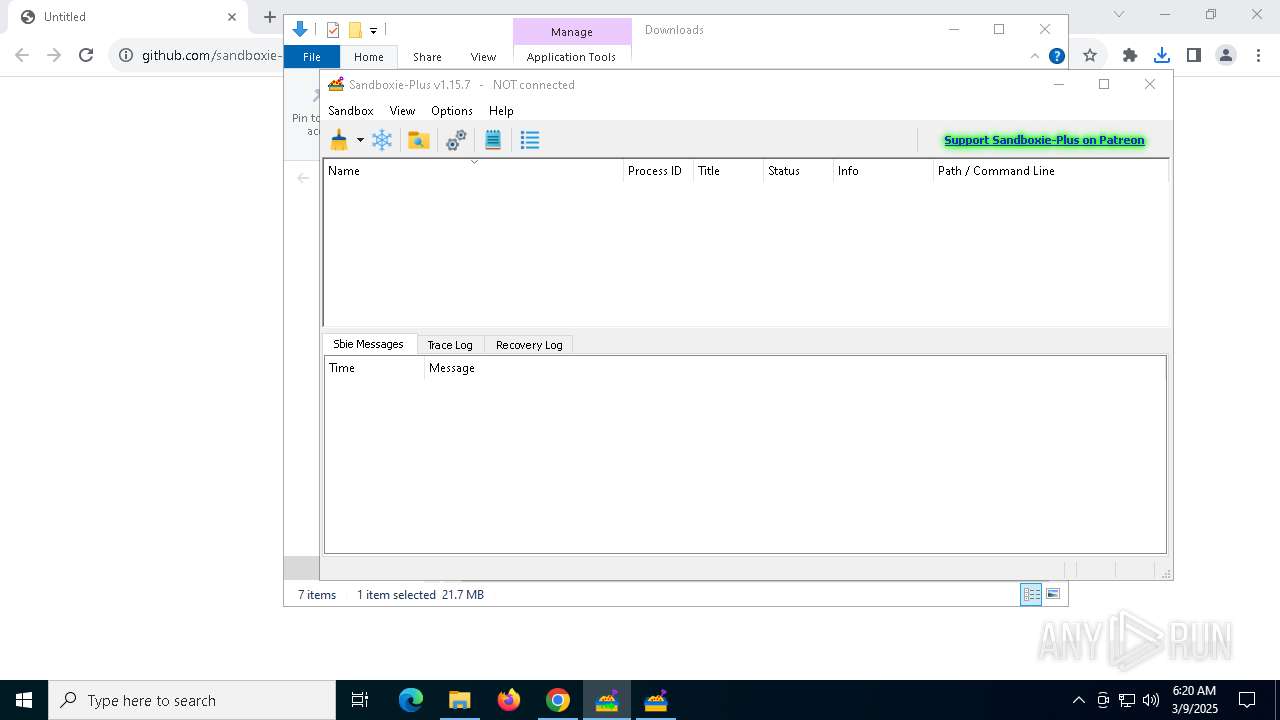
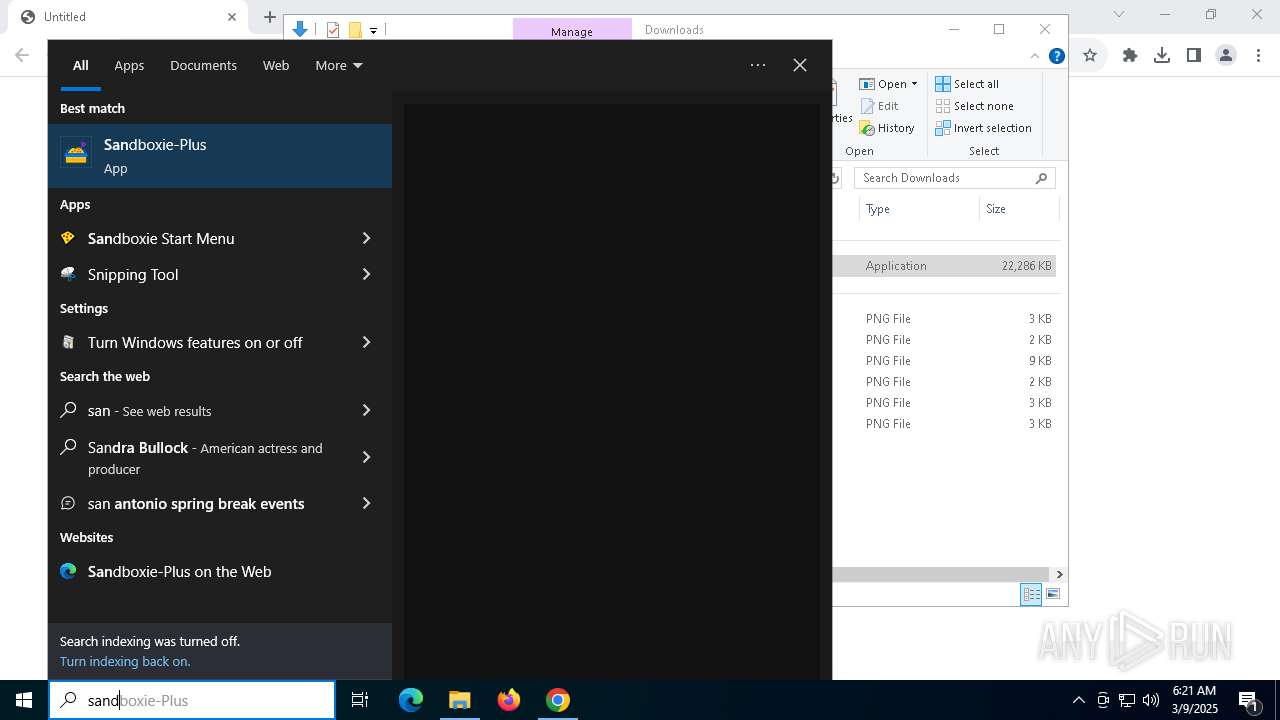
MALICIOUS
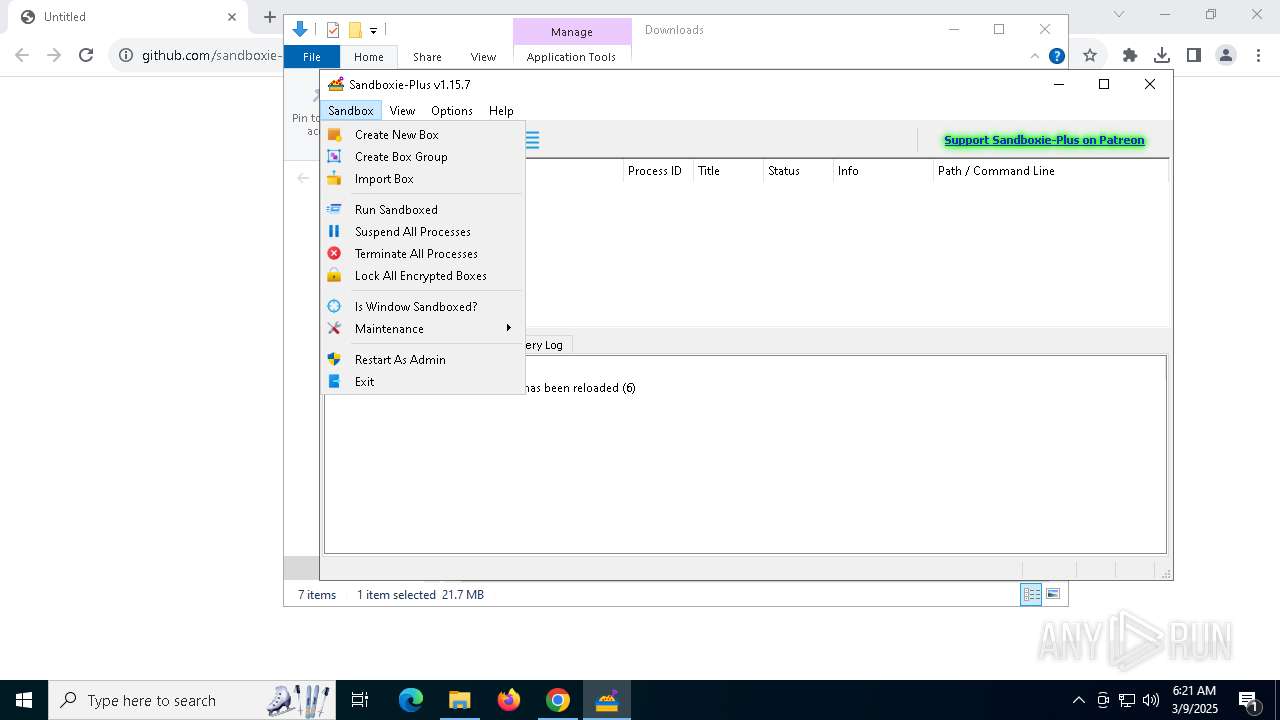
Changes the autorun value in the registry
- SandMan.exe (PID: 2320)
SUSPICIOUS
Reads security settings of Internet Explorer
- Sandboxie-Plus-x64-v1.15.7.tmp (PID: 1020)
- ShellExperienceHost.exe (PID: 6744)
Creates file in the systems drive root
- explorer.exe (PID: 5492)
Uses TASKKILL.EXE to kill process
- Sandboxie-Plus-x64-v1.15.7.tmp (PID: 2316)
Executable content was dropped or overwritten
- Sandboxie-Plus-x64-v1.15.7.exe (PID: 6268)
- Sandboxie-Plus-x64-v1.15.7.exe (PID: 6416)
- Sandboxie-Plus-x64-v1.15.7.tmp (PID: 2316)
Reads the Windows owner or organization settings
- Sandboxie-Plus-x64-v1.15.7.tmp (PID: 2316)
Drops a system driver (possible attempt to evade defenses)
- Sandboxie-Plus-x64-v1.15.7.tmp (PID: 2316)
Creates or modifies Windows services
- Sandboxie-Plus-x64-v1.15.7.tmp (PID: 2316)
- KmdUtil.exe (PID: 3140)
Process drops legitimate windows executable
- Sandboxie-Plus-x64-v1.15.7.tmp (PID: 2316)
Drops 7-zip archiver for unpacking
- Sandboxie-Plus-x64-v1.15.7.tmp (PID: 2316)
The process drops C-runtime libraries
- Sandboxie-Plus-x64-v1.15.7.tmp (PID: 2316)
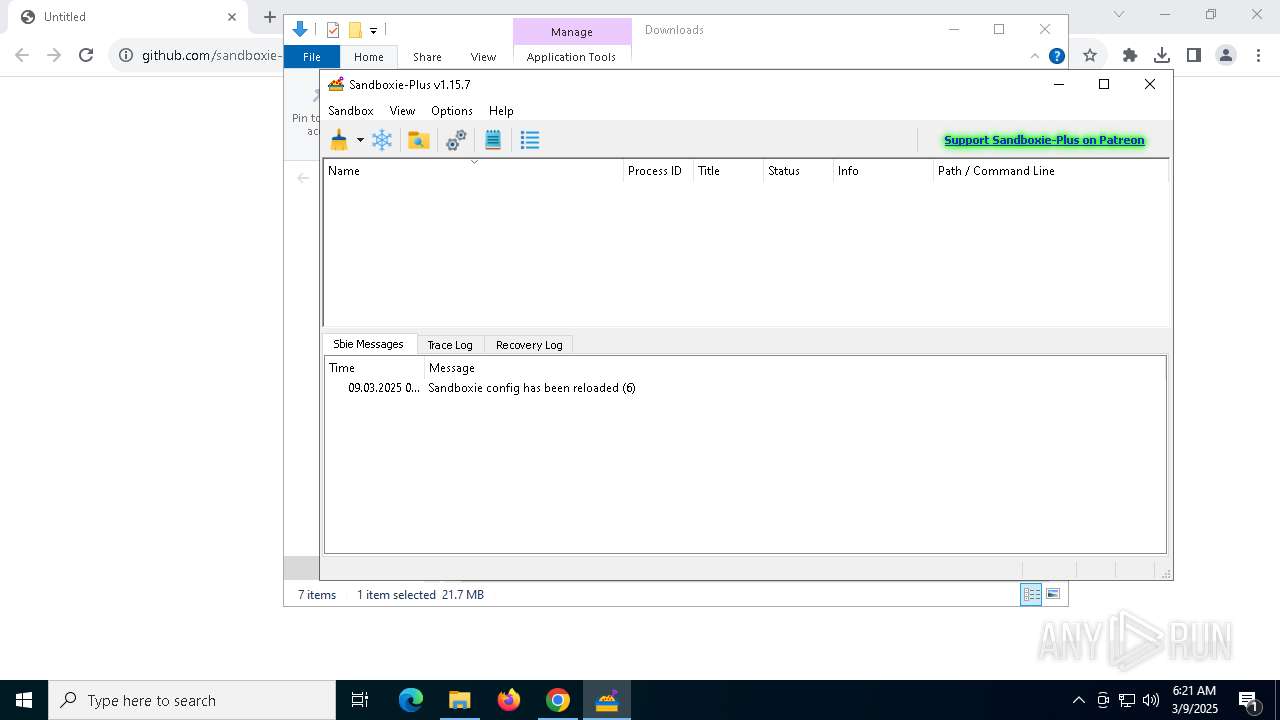
Executes as Windows Service
- SbieSvc.exe (PID: 5968)
There is functionality for taking screenshot (YARA)
- SbieSvc.exe (PID: 5968)
INFO
Checks proxy server information
- BackgroundTransferHost.exe (PID: 5504)
- explorer.exe (PID: 5492)
- UpdUtil.exe (PID: 1180)
- SandMan.exe (PID: 2320)
- slui.exe (PID: 7144)
Reads the software policy settings
- explorer.exe (PID: 5492)
- BackgroundTransferHost.exe (PID: 5504)
- UpdUtil.exe (PID: 1180)
- slui.exe (PID: 8152)
- slui.exe (PID: 7144)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 7148)
- BackgroundTransferHost.exe (PID: 6132)
- explorer.exe (PID: 5492)
- BackgroundTransferHost.exe (PID: 7284)
- BackgroundTransferHost.exe (PID: 5504)
- BackgroundTransferHost.exe (PID: 5776)
Checks supported languages
- Sandboxie-Plus-x64-v1.15.7.exe (PID: 6268)
- Sandboxie-Plus-x64-v1.15.7.tmp (PID: 1020)
- Sandboxie-Plus-x64-v1.15.7.exe (PID: 6416)
- Sandboxie-Plus-x64-v1.15.7.tmp (PID: 2316)
- KmdUtil.exe (PID: 3140)
- KmdUtil.exe (PID: 5008)
- UpdUtil.exe (PID: 1180)
- Start.exe (PID: 2040)
- KmdUtil.exe (PID: 7284)
- SbieSvc.exe (PID: 5968)
- SandMan.exe (PID: 2320)
- ShellExperienceHost.exe (PID: 6744)
- SandMan.exe (PID: 8092)
Create files in a temporary directory
- Sandboxie-Plus-x64-v1.15.7.exe (PID: 6268)
- Sandboxie-Plus-x64-v1.15.7.exe (PID: 6416)
- Sandboxie-Plus-x64-v1.15.7.tmp (PID: 2316)
- SandMan.exe (PID: 2320)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 5504)
- explorer.exe (PID: 5492)
- Sandboxie-Plus-x64-v1.15.7.tmp (PID: 2316)
- SandMan.exe (PID: 2320)
Reads the computer name
- Sandboxie-Plus-x64-v1.15.7.tmp (PID: 1020)
- Sandboxie-Plus-x64-v1.15.7.exe (PID: 6416)
- Sandboxie-Plus-x64-v1.15.7.tmp (PID: 2316)
- KmdUtil.exe (PID: 3140)
- UpdUtil.exe (PID: 1180)
- KmdUtil.exe (PID: 5008)
- KmdUtil.exe (PID: 7284)
- SbieSvc.exe (PID: 5968)
- SandMan.exe (PID: 2320)
- ShellExperienceHost.exe (PID: 6744)
Executable content was dropped or overwritten
- chrome.exe (PID: 7296)
- chrome.exe (PID: 680)
Application launched itself
- chrome.exe (PID: 7296)
Creates files in the program directory
- Sandboxie-Plus-x64-v1.15.7.tmp (PID: 2316)
Process checks computer location settings
- Sandboxie-Plus-x64-v1.15.7.tmp (PID: 1020)
Compiled with Borland Delphi (YARA)
- Sandboxie-Plus-x64-v1.15.7.exe (PID: 6268)
- Sandboxie-Plus-x64-v1.15.7.tmp (PID: 1020)
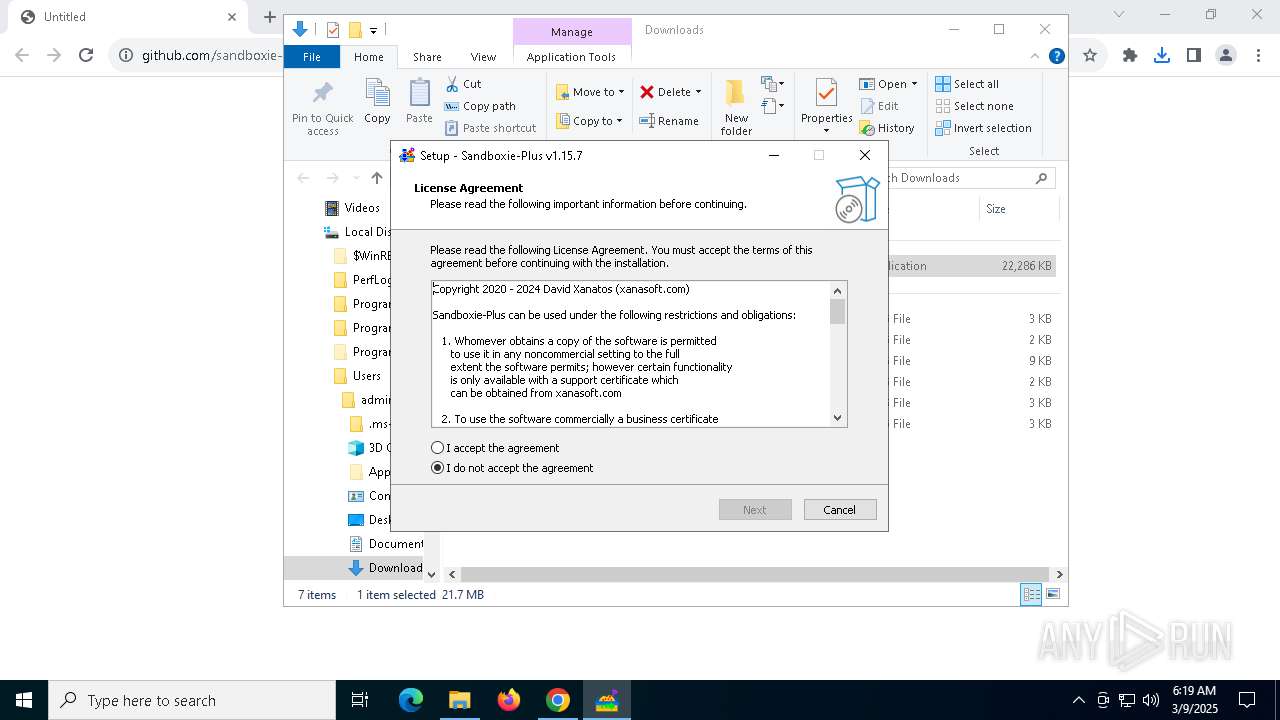
Detects InnoSetup installer (YARA)
- Sandboxie-Plus-x64-v1.15.7.tmp (PID: 1020)
- Sandboxie-Plus-x64-v1.15.7.exe (PID: 6268)
Creates a software uninstall entry
- Sandboxie-Plus-x64-v1.15.7.tmp (PID: 2316)
The sample compiled with english language support
- Sandboxie-Plus-x64-v1.15.7.tmp (PID: 2316)
- chrome.exe (PID: 680)
Local mutex for internet shortcut management
- explorer.exe (PID: 5492)
Reads Environment values
- SandMan.exe (PID: 2320)
Qt framework related mutex has been found
- SandMan.exe (PID: 2320)
- SandMan.exe (PID: 8092)
Reads the machine GUID from the registry
- SandMan.exe (PID: 2320)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
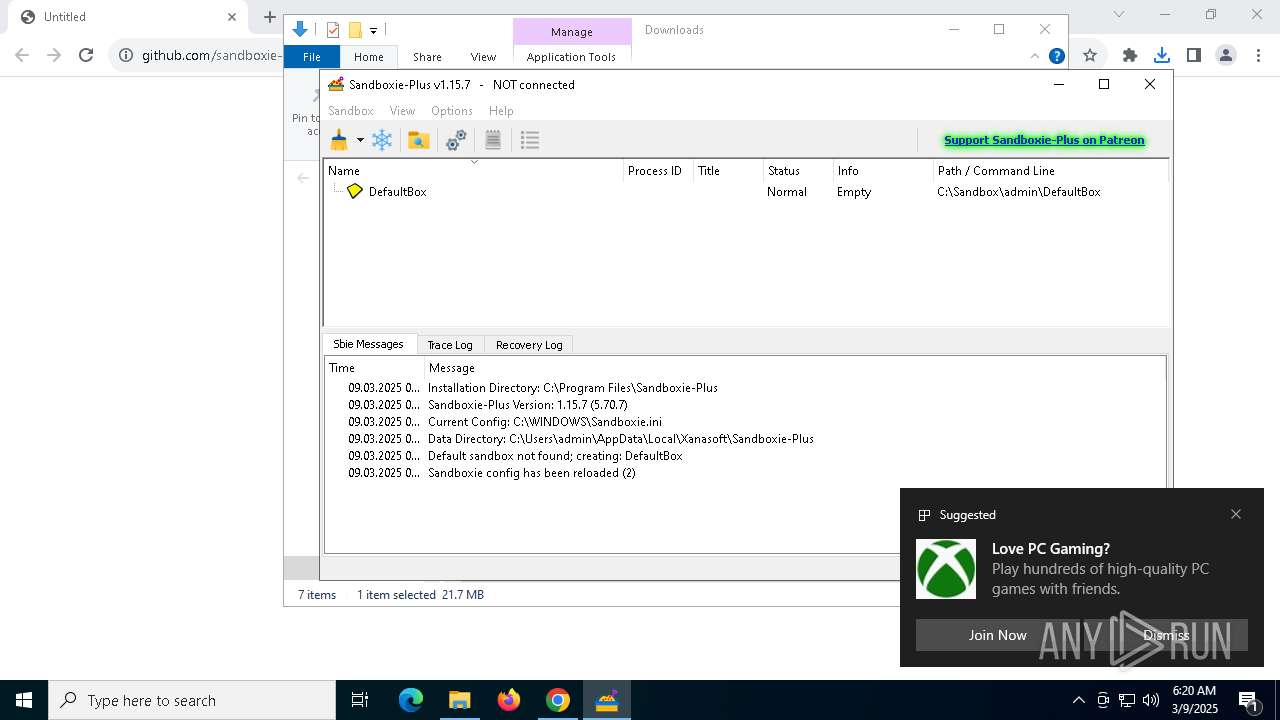
Total processes
190
Monitored processes
42
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=5384 --field-trial-handle=1840,i,14675242968685904883,2652574560518376845,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6088 --field-trial-handle=1840,i,14675242968685904883,2652574560518376845,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1020 | "C:\Users\admin\AppData\Local\Temp\is-HUMQ0.tmp\Sandboxie-Plus-x64-v1.15.7.tmp" /SL5="$3033C,21768942,805376,C:\Users\admin\Downloads\Sandboxie-Plus-x64-v1.15.7.exe" | C:\Users\admin\AppData\Local\Temp\is-HUMQ0.tmp\Sandboxie-Plus-x64-v1.15.7.tmp | — | Sandboxie-Plus-x64-v1.15.7.exe | |||||||||||
User: admin Company: http://xanasoft.com/ Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5384 --field-trial-handle=1840,i,14675242968685904883,2652574560518376845,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1180 | "C:\Program Files\Sandboxie-Plus\UpdUtil.exe" install sandboxie-plus /embedded /scope:meta /version:1.15.7 | C:\Program Files\Sandboxie-Plus\UpdUtil.exe | Sandboxie-Plus-x64-v1.15.7.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2040 | "C:\Program Files\Sandboxie-Plus\Start.exe" open_agent:sandman.exe | C:\Program Files\Sandboxie-Plus\Start.exe | — | Sandboxie-Plus-x64-v1.15.7.tmp | |||||||||||
User: admin Company: Sandboxie-Plus.com Integrity Level: MEDIUM Description: Sandboxie Start Exit code: 0 Version: 5.70.7 Modules
| |||||||||||||||
| 2136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=3568 --field-trial-handle=1840,i,14675242968685904883,2652574560518376845,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2316 | "C:\Users\admin\AppData\Local\Temp\is-8HF0V.tmp\Sandboxie-Plus-x64-v1.15.7.tmp" /SL5="$4032A,21768942,805376,C:\Users\admin\Downloads\Sandboxie-Plus-x64-v1.15.7.exe" /SPAWNWND=$30328 /NOTIFYWND=$3033C | C:\Users\admin\AppData\Local\Temp\is-8HF0V.tmp\Sandboxie-Plus-x64-v1.15.7.tmp | Sandboxie-Plus-x64-v1.15.7.exe | ||||||||||||
User: admin Company: http://xanasoft.com/ Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
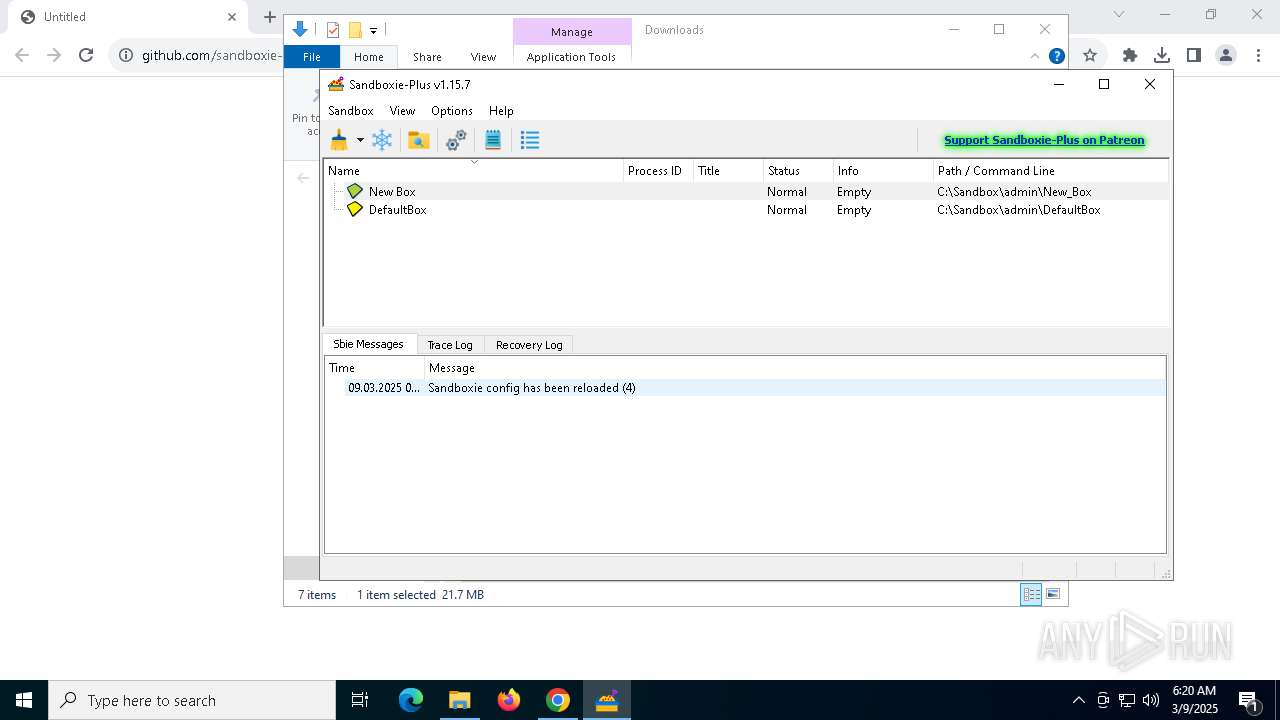
| 2320 | "C:\Program Files\Sandboxie-Plus\sandman.exe" | C:\Program Files\Sandboxie-Plus\SandMan.exe | SbieSvc.exe | ||||||||||||
User: admin Company: sandboxie-plus.com Integrity Level: MEDIUM Description: Sandboxie Manager Version: 1.15.7 Modules
| |||||||||||||||
| 2908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5904 --field-trial-handle=1840,i,14675242968685904883,2652574560518376845,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
36 988
Read events
36 840
Write events
137
Delete events
11
Modification events
| (PID) Process: | (7296) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7296) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7296) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7296) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7296) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\5\ApplicationViewManagement\W32:000000000003025C |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456BFA0DB55E4278845B426357D5B5F97B3 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FeatureUsage\AppBadgeUpdated |
| Operation: | write | Name: | Chrome |
Value: 6 | |||
| (PID) Process: | (6736) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000D5ACAD3BBB90DB01 | |||
| (PID) Process: | (7284) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7284) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
107
Suspicious files
187
Text files
69
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10dcb6.TMP | — | |
MD5:— | SHA256:— | |||
| 7296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10dcb6.TMP | — | |
MD5:— | SHA256:— | |||
| 7296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10dcb6.TMP | — | |
MD5:— | SHA256:— | |||
| 7296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10dcb6.TMP | — | |
MD5:— | SHA256:— | |||
| 7296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10dcc5.TMP | — | |
MD5:— | SHA256:— | |||
| 7296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
59
DNS requests
40
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6632 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adp7lmscefogeldj4te6xerqth3a_9.55.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.55.0_all_ocm7dvbavb37zglvqhfr5kszse.crx3 | unknown | — | — | whitelisted |
6632 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/inc4skbz6ysglh4mhehkajf2mq_20250226.732734858.14/obedbbhbpmojnkanicioggnmelmoomoc_20250226.732734858.14_all_ENUS500000_d4mh7j3vuvobdneldly6emsmfq.crx3 | unknown | — | — | whitelisted |
6632 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/inc4skbz6ysglh4mhehkajf2mq_20250226.732734858.14/obedbbhbpmojnkanicioggnmelmoomoc_20250226.732734858.14_all_ENUS500000_d4mh7j3vuvobdneldly6emsmfq.crx3 | unknown | — | — | whitelisted |
6632 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/inc4skbz6ysglh4mhehkajf2mq_20250226.732734858.14/obedbbhbpmojnkanicioggnmelmoomoc_20250226.732734858.14_all_ENUS500000_d4mh7j3vuvobdneldly6emsmfq.crx3 | unknown | — | — | whitelisted |
6632 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/inc4skbz6ysglh4mhehkajf2mq_20250226.732734858.14/obedbbhbpmojnkanicioggnmelmoomoc_20250226.732734858.14_all_ENUS500000_d4mh7j3vuvobdneldly6emsmfq.crx3 | unknown | — | — | whitelisted |
7200 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6632 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/inc4skbz6ysglh4mhehkajf2mq_20250226.732734858.14/obedbbhbpmojnkanicioggnmelmoomoc_20250226.732734858.14_all_ENUS500000_d4mh7j3vuvobdneldly6emsmfq.crx3 | unknown | — | — | whitelisted |
5492 | explorer.exe | GET | 200 | 146.75.122.133:80 | http://ocsp.globalsign.com/gsgccr45evcodesignca2020/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQaCbVYh07WONuW4e63Ydlu4AlbDAQUJZ3Q%2FFkJhmPF7POxEztXHAOSNhECDDDkxbDF133BX%2FrKdw%3D%3D | unknown | — | — | whitelisted |
7396 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6632 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adp7lmscefogeldj4te6xerqth3a_9.55.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.55.0_all_ocm7dvbavb37zglvqhfr5kszse.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7296 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7636 | chrome.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
7636 | chrome.exe | 108.177.127.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
7636 | chrome.exe | 185.199.110.133:443 | objects.githubusercontent.com | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
github.com |
| whitelisted |
accounts.google.com |
| whitelisted |
objects.githubusercontent.com |
| whitelisted |
www.google.com |
| whitelisted |
arc.msn.com |
| whitelisted |