| File name: | contract.doc |
| Full analysis: | https://app.any.run/tasks/4627e4f0-1779-4bbe-82c6-f84404d21f67 |
| Verdict: | Malicious activity |
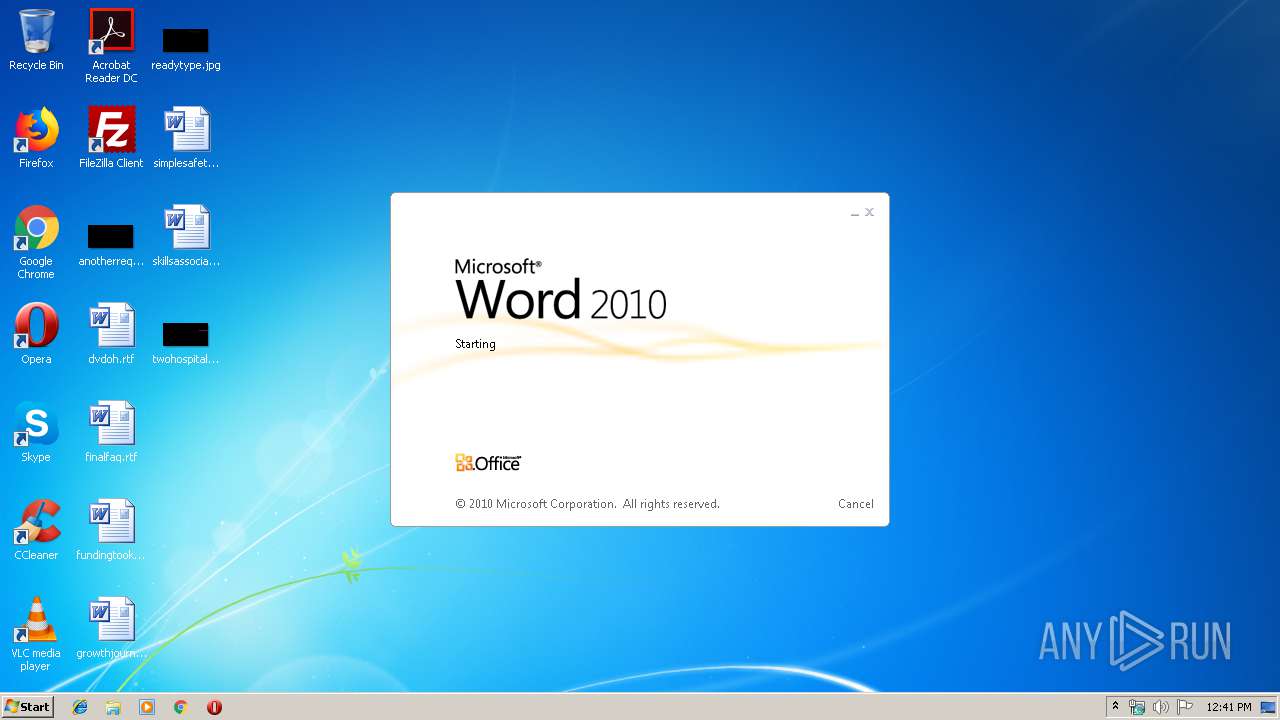
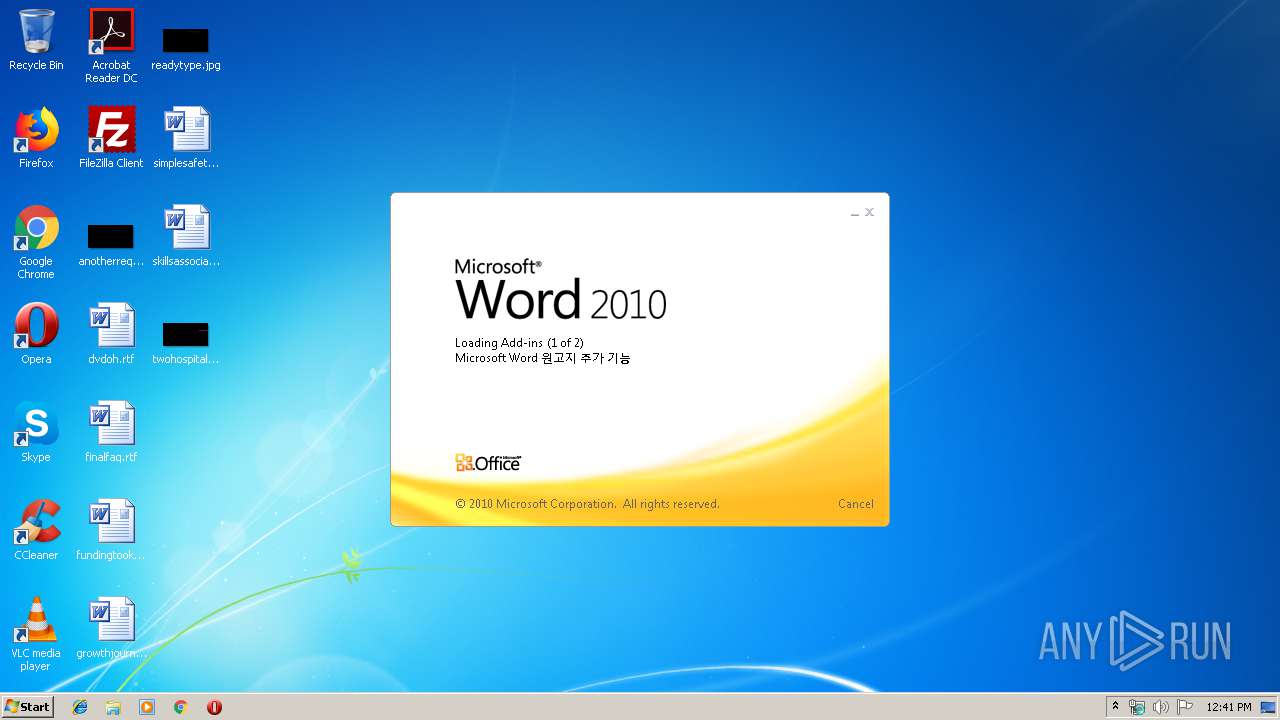
| Analysis date: | November 08, 2019, 12:41:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: nRDOuPL, Subject: PbmbDeE, Author: ttSvkth, Template: Normal, Last Saved By: J, Revision Number: 2, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Nov 8 11:46:00 2019, Last Saved Time/Date: Fri Nov 8 11:46:00 2019, Number of Pages: 1, Number of Words: 6, Number of Characters: 37, Security: 0 |
| MD5: | 97FCBD21803E98AA48CE4675CF37EAB8 |
| SHA1: | B991A2EE721075F03E634803318DE59C0C7A8B66 |
| SHA256: | 3EAC791138339A1B0E1052A5ADFA2DE12AE3DF38431C10D59C3740ECBCA3B3F5 |
| SSDEEP: | 12288:kRQ6X9GDapmG7H+9vo4karcaXv2CAwz0NASBY196ID+9b5O:kRQ6tld/4kc/vAi0NASi65DO |
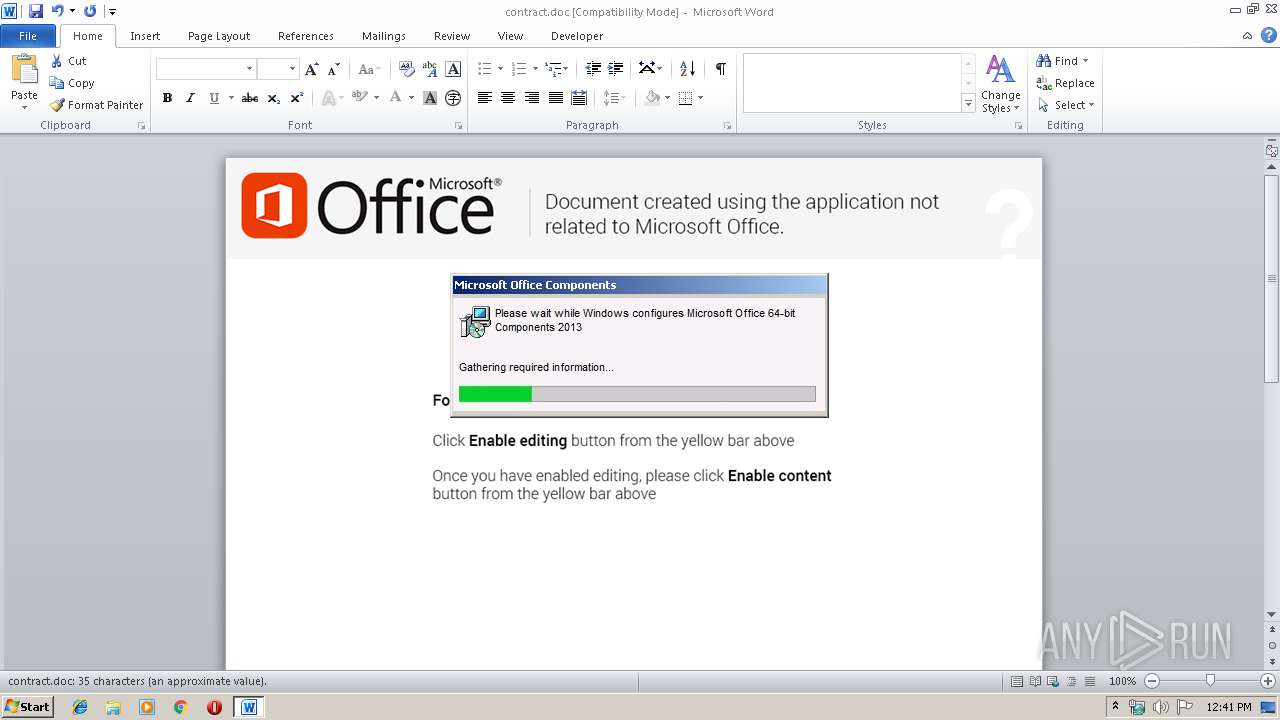
MALICIOUS
Loads dropped or rewritten executable
- WINWORD.EXE (PID: 2168)
Executable content was dropped or overwritten
- WINWORD.EXE (PID: 2168)
SUSPICIOUS
No suspicious indicators.INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2168)
Creates files in the user directory
- WINWORD.EXE (PID: 2168)
Reads settings of System Certificates
- WINWORD.EXE (PID: 2168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | nRDOuPL |
|---|---|
| Subject: | PbmbDeE |
| Author: | ttSvkth |
| Keywords: | - |
| Comments: | - |
| Template: | Normal |
| LastModifiedBy: | J |
| RevisionNumber: | 2 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:11:08 11:46:00 |
| ModifyDate: | 2019:11:08 11:46:00 |
| Pages: | 1 |
| Words: | 6 |
| Characters: | 37 |
| Security: | None |
| Company: | - |
| Bytes: | 35418 |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 42 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Windows Latin 1 (Western European) |
| HIhyglW: | YN?Q;ecD9]i8-~YsMqN_e@QmQ#O |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
35
Monitored processes
1
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2168 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\contract.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
954
Read events
716
Write events
180
Delete events
58
Modification events
| (PID) Process: | (2168) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | |x= |
Value: 7C783D0078080000010000000000000000000000 | |||
| (PID) Process: | (2168) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2168) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2168) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2168) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2168) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2168) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2168) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2168) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2168) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1332215870 | |||
Executable files
1
Suspicious files
3
Text files
0
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2168 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA8FC.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2168 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~WRD0000.tmp | — | |
MD5:— | SHA256:— | |||
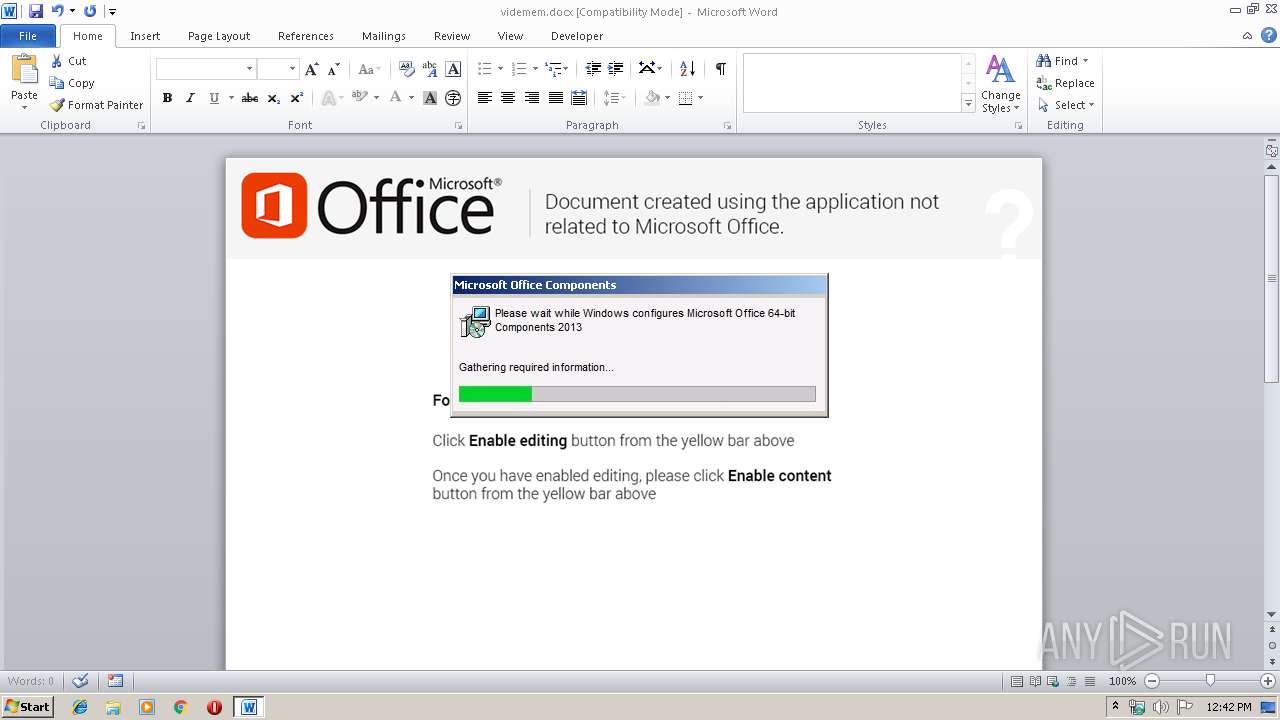
| 2168 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$demem.docx.zip | — | |
MD5:— | SHA256:— | |||
| 2168 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~WRD0001.tmp | — | |
MD5:— | SHA256:— | |||
| 2168 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\4BEAA7F0.emf | emf | |
MD5:— | SHA256:— | |||
| 2168 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$ntract.doc | pgc | |
MD5:— | SHA256:— | |||
| 2168 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\videmem.docx.zip | document | |
MD5:— | SHA256:— | |||
| 2168 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\videmem.docx | document | |
MD5:— | SHA256:— | |||
| 2168 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2168 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2168 | WINWORD.EXE | 195.123.246.12:443 | microsoft-hub-us.com | — | UA | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
microsoft-hub-us.com |
| unknown |