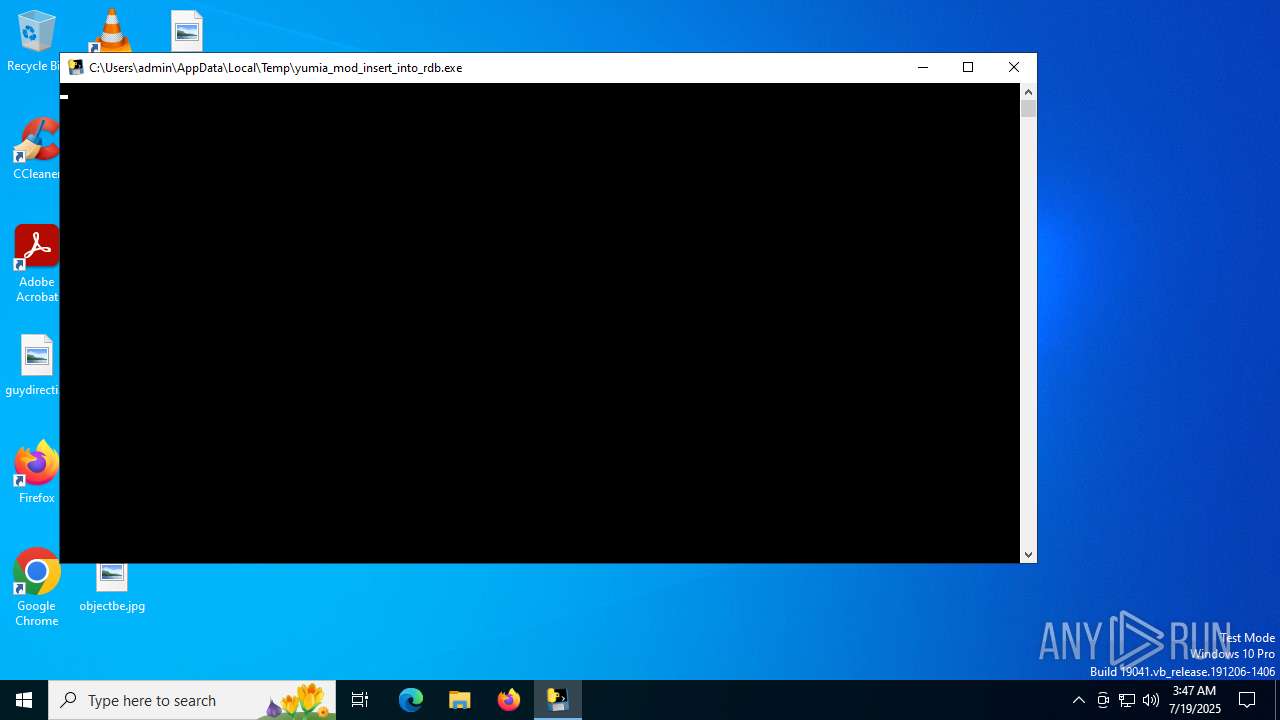
| File name: | yumia_mod_insert_into_rdb.exe |
| Full analysis: | https://app.any.run/tasks/4ae118dc-d6a5-4112-bc36-8c00701c084e |
| Verdict: | Malicious activity |
| Analysis date: | July 19, 2025, 03:47:12 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 6 sections |
| MD5: | BCD7CF54B9514D5B94151A31B7DD2B77 |
| SHA1: | A30476460FA5935706BF108165BADEF8402C7040 |
| SHA256: | 3E8EEDF3E284D978B15F543A7D8046BF9F3758E05CB64220801EDBE802A5100E |
| SSDEEP: | 98304:ODZ2BEWr7jARheQkHFwe8ir2ey9g8Ia5OxbrQiiHdMesSFVdGfR36BeA9T9iplOU:K/OO/bt5 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops legitimate windows executable
- yumia_mod_insert_into_rdb.exe (PID: 6680)
The process drops C-runtime libraries
- yumia_mod_insert_into_rdb.exe (PID: 6680)
Process drops python dynamic module
- yumia_mod_insert_into_rdb.exe (PID: 6680)
Executable content was dropped or overwritten
- yumia_mod_insert_into_rdb.exe (PID: 6680)
Application launched itself
- yumia_mod_insert_into_rdb.exe (PID: 6680)
Loads Python modules
- yumia_mod_insert_into_rdb.exe (PID: 3788)
INFO
Checks supported languages
- yumia_mod_insert_into_rdb.exe (PID: 6680)
- yumia_mod_insert_into_rdb.exe (PID: 3788)
Create files in a temporary directory
- yumia_mod_insert_into_rdb.exe (PID: 6680)
Reads the computer name
- yumia_mod_insert_into_rdb.exe (PID: 6680)
The sample compiled with english language support
- yumia_mod_insert_into_rdb.exe (PID: 6680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:04:10 04:58:55+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.4 |
| CodeSize: | 173056 |
| InitializedDataSize: | 151040 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb4d0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
140
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1036 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2324 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3788 | "C:\Users\admin\AppData\Local\Temp\yumia_mod_insert_into_rdb.exe" | C:\Users\admin\AppData\Local\Temp\yumia_mod_insert_into_rdb.exe | — | yumia_mod_insert_into_rdb.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 6128 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | yumia_mod_insert_into_rdb.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6680 | "C:\Users\admin\AppData\Local\Temp\yumia_mod_insert_into_rdb.exe" | C:\Users\admin\AppData\Local\Temp\yumia_mod_insert_into_rdb.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
Total events
308
Read events
308
Write events
0
Delete events
0
Modification events
Executable files
50
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6680 | yumia_mod_insert_into_rdb.exe | C:\Users\admin\AppData\Local\Temp\_MEI66802\_lzma.pyd | executable | |
MD5:2AE2464BFCC442083424BC05ED9BE7D2 | SHA256:64BA475A28781DCA81180A1B8722A81893704F8D8FAC0B022C846FDCF95B15B9 | |||
| 6680 | yumia_mod_insert_into_rdb.exe | C:\Users\admin\AppData\Local\Temp\_MEI66802\_hashlib.pyd | executable | |
MD5:534902BE1D8A57974EFD025AFF4F11EF | SHA256:30ADFB86513282E59D7E27968E1FF6686E43B8559994A50C17BE66D0789F82B3 | |||
| 6680 | yumia_mod_insert_into_rdb.exe | C:\Users\admin\AppData\Local\Temp\_MEI66802\VCRUNTIME140.dll | executable | |
MD5:BE8DBE2DC77EBE7F88F910C61AEC691A | SHA256:4D292623516F65C80482081E62D5DADB759DC16E851DE5DB24C3CBB57B87DB83 | |||
| 6680 | yumia_mod_insert_into_rdb.exe | C:\Users\admin\AppData\Local\Temp\_MEI66802\api-ms-win-core-datetime-l1-1-0.dll | executable | |
MD5:ADF9263B966CEA234762C0782ABA6E78 | SHA256:10CD6BF518350F93AB4643F701EFDAC851CDD7A26A0D8BCABFBB2BD273E1F529 | |||
| 6680 | yumia_mod_insert_into_rdb.exe | C:\Users\admin\AppData\Local\Temp\_MEI66802\api-ms-win-core-console-l1-1-0.dll | executable | |
MD5:A58F3FBBBBB1ECB4260D626B07BE2CDA | SHA256:89DD6FBEA61EDB8F1C934B7E5E822B4CE9BEA939FF585C83C197E06A1FD8311A | |||
| 6680 | yumia_mod_insert_into_rdb.exe | C:\Users\admin\AppData\Local\Temp\_MEI66802\api-ms-win-core-fibers-l1-1-0.dll | executable | |
MD5:221F63EE94E3FFB567D2342DF588BEBC | SHA256:FD7C5503AA81DEA1DE9BAEE318E6A53663F7A4634F42E116E83C6A0F36D11143 | |||
| 6680 | yumia_mod_insert_into_rdb.exe | C:\Users\admin\AppData\Local\Temp\_MEI66802\api-ms-win-core-file-l1-1-0.dll | executable | |
MD5:6EE268F365DC48D407C337D1C7924B0C | SHA256:EB50CC53863C5A1C0B2FE805D9ECEFEF3F2DBD0E749A6CC142F89406F4FFDB10 | |||
| 6680 | yumia_mod_insert_into_rdb.exe | C:\Users\admin\AppData\Local\Temp\_MEI66802\api-ms-win-core-memory-l1-1-0.dll | executable | |
MD5:3ABF2EB0C597131B05EE5B8550A13079 | SHA256:FF611CC2CB492C84748FA148EDA80DEC0CB23FC3B71828475ECEA29597C26CD8 | |||
| 6680 | yumia_mod_insert_into_rdb.exe | C:\Users\admin\AppData\Local\Temp\_MEI66802\api-ms-win-core-errorhandling-l1-1-0.dll | executable | |
MD5:586D46D392348AD2EE25404B9D005A4E | SHA256:2859FE2FE069E5F4300DD0106733750B1C8C67EE5D8788C4556B7D21C6DA651D | |||
| 6680 | yumia_mod_insert_into_rdb.exe | C:\Users\admin\AppData\Local\Temp\_MEI66802\api-ms-win-core-file-l1-2-0.dll | executable | |
MD5:852904535068E569E2B157F3BCA0C08F | SHA256:202B77CD363FCE7C09D9A59B5779F701767C8734CC17BBE8B9ECE5A0619F2225 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
22
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7104 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6236 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6236 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4460 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7104 | svchost.exe | 20.190.159.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7104 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |