| File name: | Instoil.exe |
| Full analysis: | https://app.any.run/tasks/81b12e23-7cdd-4939-a2ed-1c44008d6de5 |
| Verdict: | Malicious activity |
| Analysis date: | January 23, 2026, 00:35:39 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 11 sections |
| MD5: | E856ADFF8219DE7A207976763CE7A43B |
| SHA1: | 7EC3CA5DEDB46350B3DB8E6CD74B37B4E95700DF |
| SHA256: | 3E881B363AF7187B25159954D85D95467A3E64FF75B4083FA0A6908F59C62DAD |
| SSDEEP: | 98304:aPXS+DPCqpT/nobF7L79C1bD7S5biJg7nRH76WQyVP1ozTXk9q8os+o65/wAhNIT:GquR1Z6jwe4Jj/0x795a6r47XkTLxI2 |
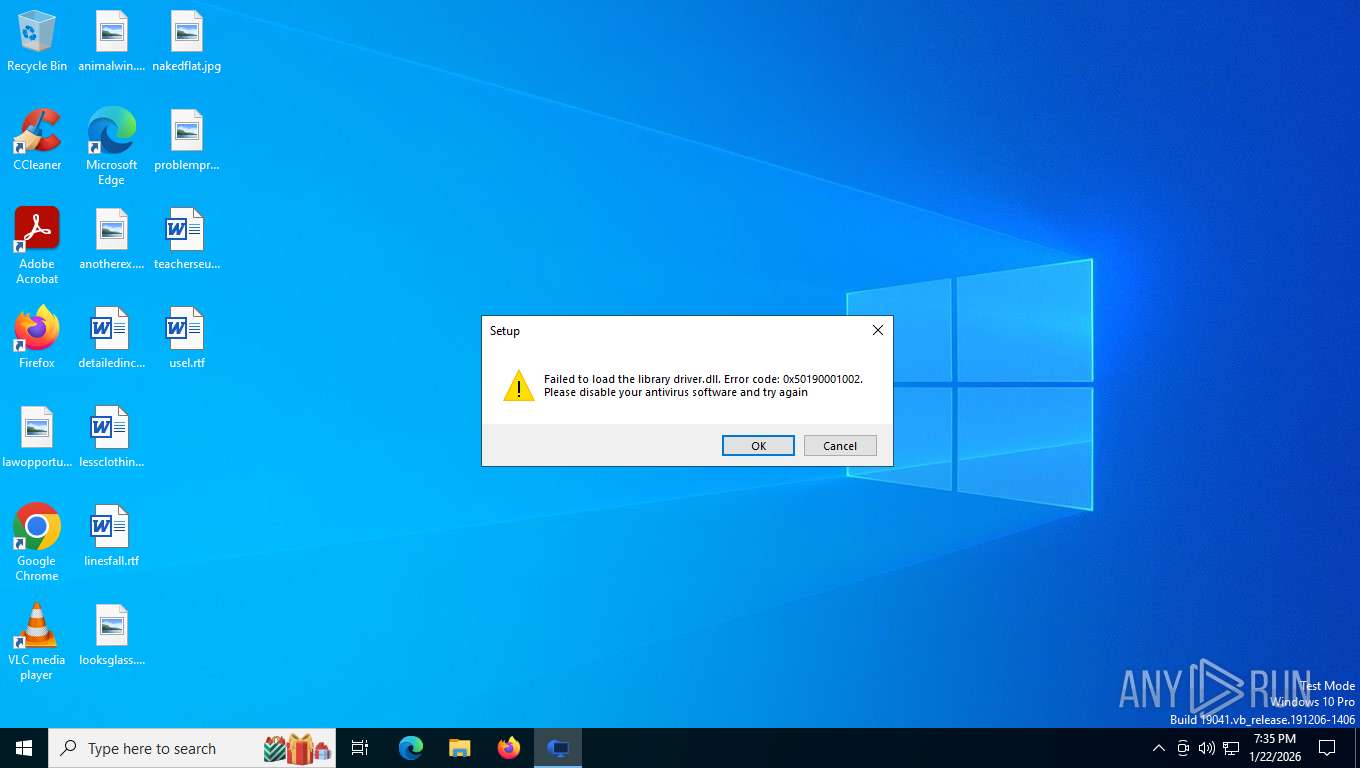
MALICIOUS
Changes settings of System certificates
- wire_guard.exe (PID: 8660)
SUSPICIOUS
Executable content was dropped or overwritten
- Instoil.exe (PID: 4948)
- Instoil.exe (PID: 7228)
- Instoil.tmp (PID: 7208)
- Instoil.exe (PID: 8568)
- Instoil.tmp (PID: 8704)
- wire_guard.exe (PID: 8660)
Reads the Windows owner or organization settings
- Instoil.tmp (PID: 7208)
- Instoil.tmp (PID: 8704)
Possible usage of Discord/Telegram API has been detected (YARA)
- Instoil.exe (PID: 8568)
- Instoil.tmp (PID: 8704)
Drops 7-zip archiver for unpacking
- Instoil.tmp (PID: 8704)
Adds/modifies Windows certificates
- wire_guard.exe (PID: 8660)
Executes as Windows Service
- VSSVC.exe (PID: 3976)
INFO
Checks supported languages
- Instoil.exe (PID: 4948)
- Instoil.tmp (PID: 7004)
- Instoil.exe (PID: 7228)
- Instoil.tmp (PID: 7208)
- Instoil.exe (PID: 8568)
- Instoil.tmp (PID: 8704)
- wire_guard.exe (PID: 8660)
- msiexec.exe (PID: 5168)
Create files in a temporary directory
- Instoil.exe (PID: 4948)
- Instoil.exe (PID: 7228)
- Instoil.tmp (PID: 7208)
- Instoil.exe (PID: 8568)
- Instoil.tmp (PID: 8704)
Reads the computer name
- Instoil.tmp (PID: 7004)
- Instoil.exe (PID: 7228)
- Instoil.tmp (PID: 7208)
- Instoil.exe (PID: 8568)
- Instoil.tmp (PID: 8704)
- wire_guard.exe (PID: 8660)
- msiexec.exe (PID: 5168)
Reads security settings of Internet Explorer
- Instoil.tmp (PID: 7004)
- Instoil.tmp (PID: 7208)
- wire_guard.exe (PID: 8660)
Process checks computer location settings
- Instoil.tmp (PID: 7004)
- Instoil.tmp (PID: 7208)
Checks proxy server information
- wire_guard.exe (PID: 8660)
Compiled with Borland Delphi (YARA)
- Instoil.exe (PID: 8568)
- Instoil.tmp (PID: 8704)
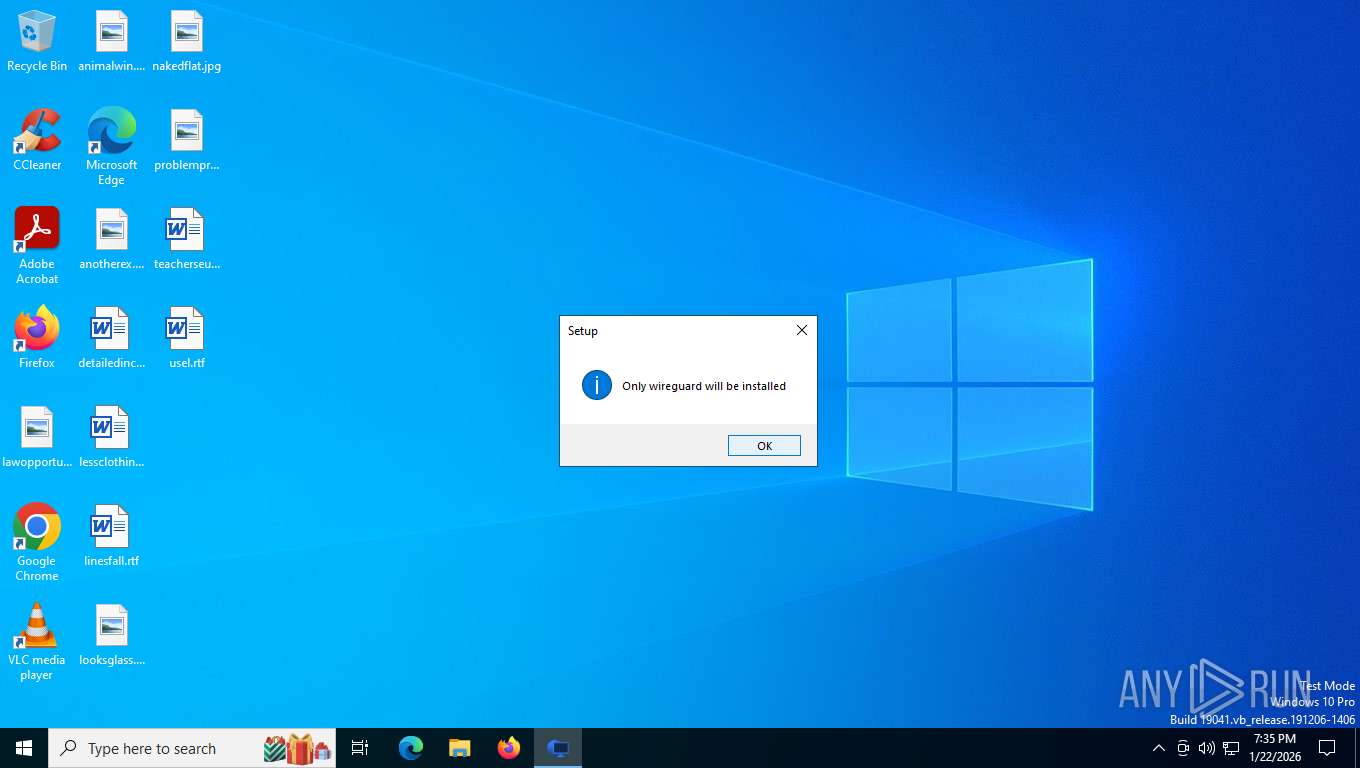
Detects InnoSetup installer (YARA)
- Instoil.exe (PID: 8568)
- Instoil.tmp (PID: 8704)
Creates a software uninstall entry
- Instoil.tmp (PID: 8704)
The sample compiled with english language support
- Instoil.tmp (PID: 8704)
- wire_guard.exe (PID: 8660)
Reads the machine GUID from the registry
- wire_guard.exe (PID: 8660)
The sample compiled with chinese language support
- wire_guard.exe (PID: 8660)
Creates files or folders in the user directory
- wire_guard.exe (PID: 8660)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (67.7) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (25.6) |
| .exe | | | Win32 Executable (generic) (2.7) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:09:11 13:05:07+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 716800 |
| InitializedDataSize: | 276992 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb0028 |
| OSVersion: | 6.1 |
| ImageVersion: | - |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 38.7.1.4 |
| ProductVersionNumber: | 39.9.1.3 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | https://www.gitlab.com |
| FileDescription: | Gitlab Setup |
| FileVersion: | 38.7.1.4 |
| LegalCopyright: | |
| OriginalFileName: | |
| ProductName: | Gitlab |
| ProductVersion: | 39.9.1.3 |
Total processes
153
Monitored processes
9
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3976 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4948 | "C:\Users\admin\AppData\Local\Temp\Instoil.exe" | C:\Users\admin\AppData\Local\Temp\Instoil.exe | explorer.exe | ||||||||||||
User: admin Company: https://www.gitlab.com Integrity Level: MEDIUM Description: Gitlab Setup Exit code: 1 Version: 38.7.1.4 Modules
| |||||||||||||||
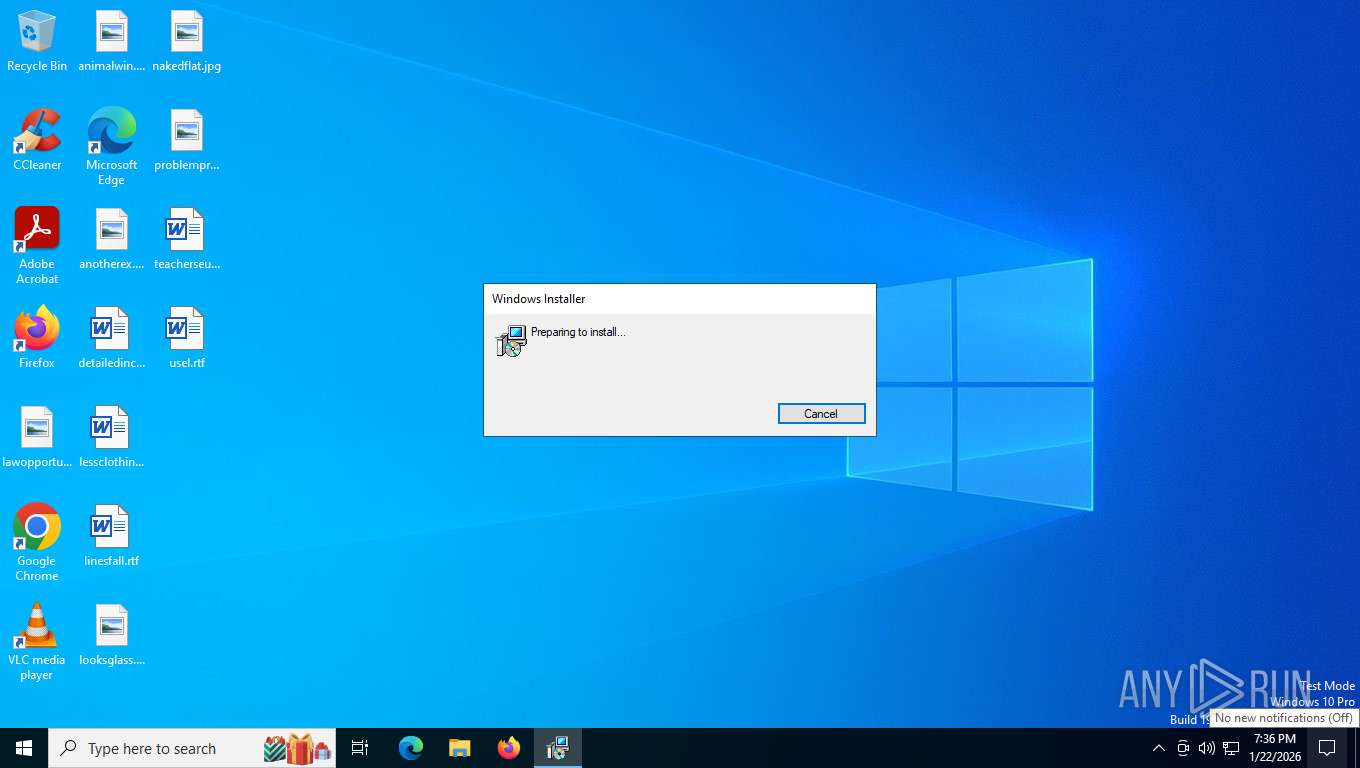
| 5168 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7004 | "C:\Users\admin\AppData\Local\Temp\is-P83AE.tmp\Instoil.tmp" /SL5="$D0062,15115241,994816,C:\Users\admin\AppData\Local\Temp\Instoil.exe" | C:\Users\admin\AppData\Local\Temp\is-P83AE.tmp\Instoil.tmp | — | Instoil.exe | |||||||||||
User: admin Company: https://www.gitlab.com Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 1 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 7208 | "C:\Users\admin\AppData\Local\Temp\is-RCPL2.tmp\Instoil.tmp" /SL5="$16038E,15115241,994816,C:\Users\admin\AppData\Local\Temp\Instoil.exe" /SPAWNWND=$F0246 /NOTIFYWND=$D0062 | C:\Users\admin\AppData\Local\Temp\is-RCPL2.tmp\Instoil.tmp | Instoil.exe | ||||||||||||
User: admin Company: https://www.gitlab.com Integrity Level: HIGH Description: Setup/Uninstall Exit code: 1 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 7228 | "C:\Users\admin\AppData\Local\Temp\Instoil.exe" /SPAWNWND=$F0246 /NOTIFYWND=$D0062 | C:\Users\admin\AppData\Local\Temp\Instoil.exe | Instoil.tmp | ||||||||||||
User: admin Company: https://www.gitlab.com Integrity Level: HIGH Description: Gitlab Setup Exit code: 1 Version: 38.7.1.4 Modules
| |||||||||||||||
| 8568 | "C:\Users\admin\AppData\Local\Temp\Instoil.exe" /VERYSILENT | C:\Users\admin\AppData\Local\Temp\Instoil.exe | Instoil.tmp | ||||||||||||
User: admin Company: https://www.gitlab.com Integrity Level: HIGH Description: Gitlab Setup Version: 38.7.1.4 Modules
| |||||||||||||||
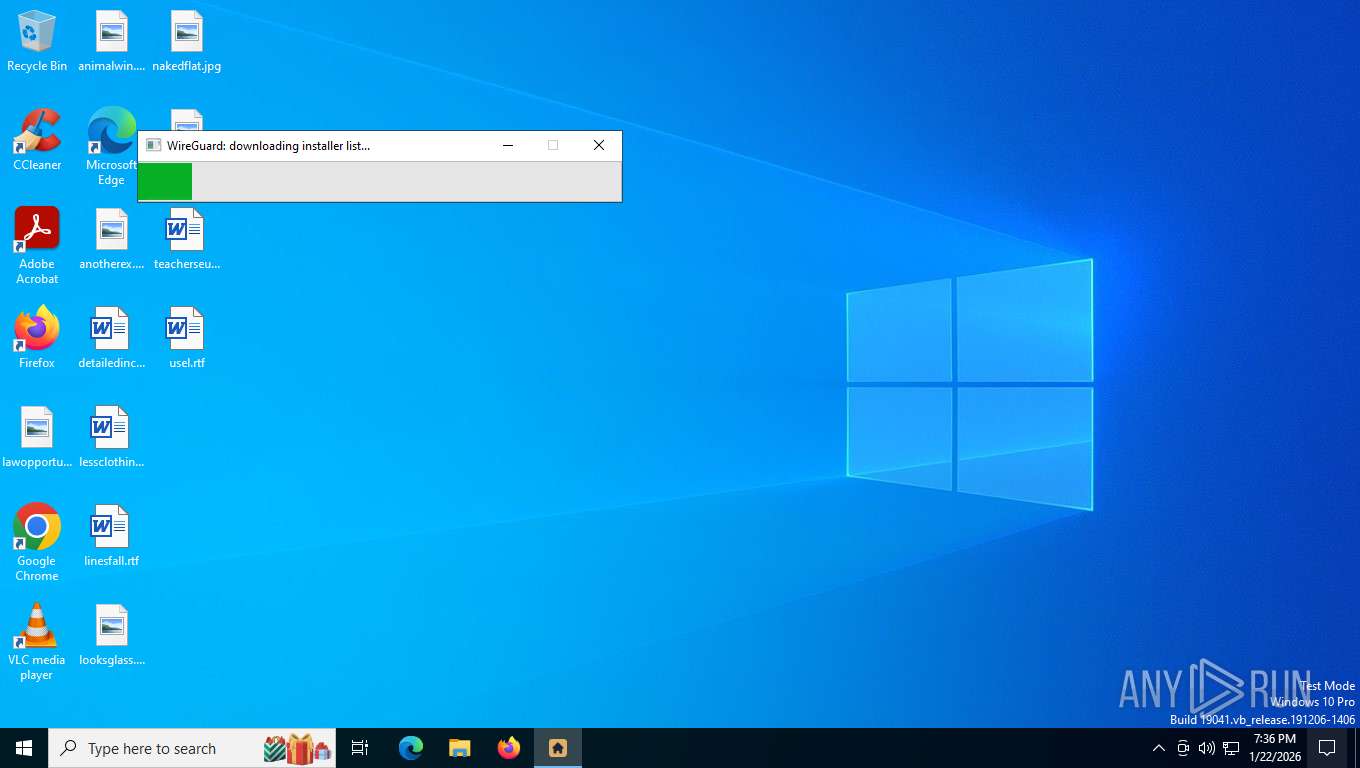
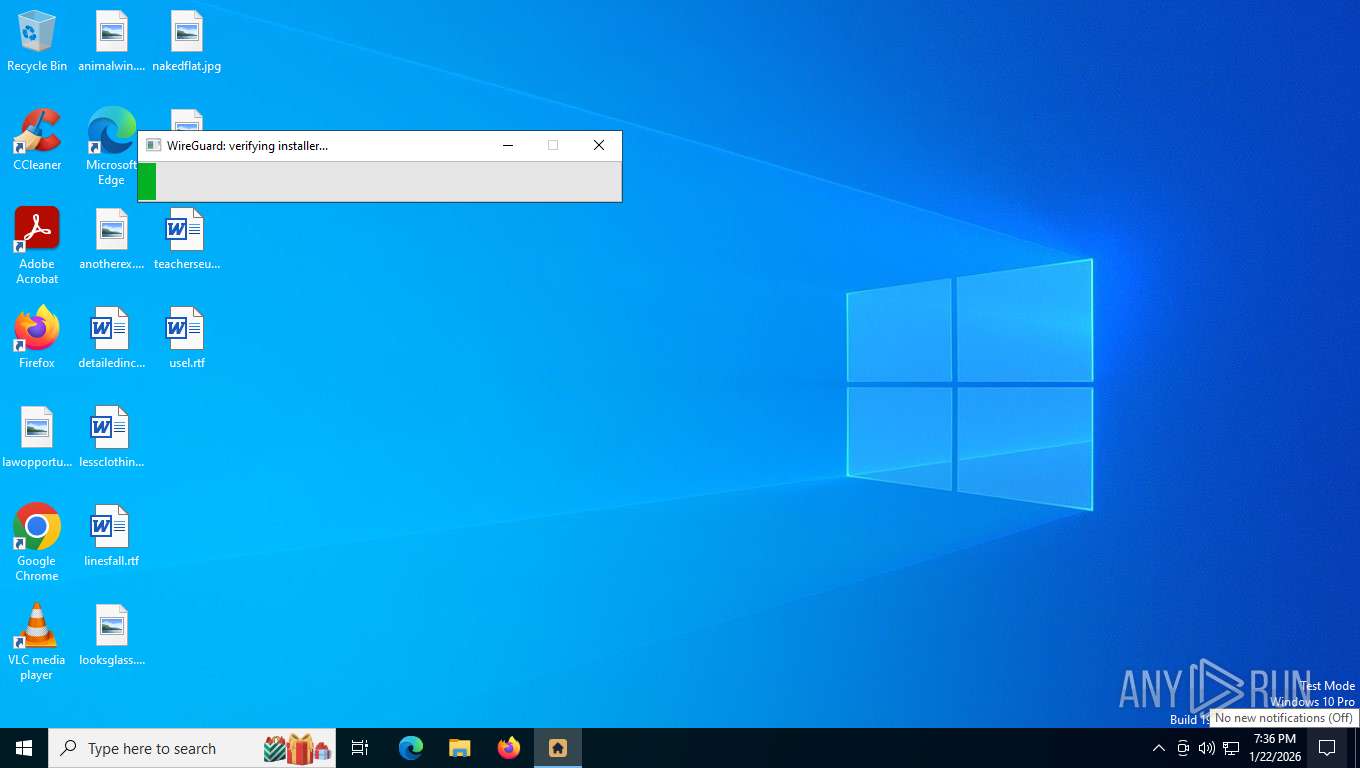
| 8660 | "C:\WINDOWS\wire_guard.exe" | C:\Windows\wire_guard.exe | Instoil.tmp | ||||||||||||
User: admin Company: WireGuard LLC Integrity Level: HIGH Description: WireGuard Installer: Fast, Modern, Secure VPN Tunnel Version: 1.0 Modules
| |||||||||||||||
| 8704 | "C:\Users\admin\AppData\Local\Temp\is-Q6SHR.tmp\Instoil.tmp" /SL5="$E0062,15115241,994816,C:\Users\admin\AppData\Local\Temp\Instoil.exe" /VERYSILENT | C:\Users\admin\AppData\Local\Temp\is-Q6SHR.tmp\Instoil.tmp | Instoil.exe | ||||||||||||
User: admin Company: https://www.gitlab.com Integrity Level: HIGH Description: Setup/Uninstall Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
6 890
Read events
6 772
Write events
105
Delete events
13
Modification events
| (PID) Process: | (8704) Instoil.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{0F9D3105-8171-4E4F-8642-87025C13998D}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.5.3 | |||
| (PID) Process: | (8704) Instoil.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{0F9D3105-8171-4E4F-8642-87025C13998D}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: | |||
| (PID) Process: | (8704) Instoil.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{0F9D3105-8171-4E4F-8642-87025C13998D}_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: (Default) | |||
| (PID) Process: | (8704) Instoil.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{0F9D3105-8171-4E4F-8642-87025C13998D}_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (8704) Instoil.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{0F9D3105-8171-4E4F-8642-87025C13998D}_is1 |
| Operation: | write | Name: | Inno Setup: Language |
Value: default | |||
| (PID) Process: | (8704) Instoil.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{0F9D3105-8171-4E4F-8642-87025C13998D}_is1 |
| Operation: | write | Name: | DisplayName |
Value: Gitlab version 60.0.7.4 | |||
| (PID) Process: | (8704) Instoil.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{0F9D3105-8171-4E4F-8642-87025C13998D}_is1 |
| Operation: | write | Name: | UninstallString |
Value: "C:\WINDOWS\unins000.exe" | |||
| (PID) Process: | (8704) Instoil.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{0F9D3105-8171-4E4F-8642-87025C13998D}_is1 |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\WINDOWS\unins000.exe" /SILENT | |||
| (PID) Process: | (8704) Instoil.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{0F9D3105-8171-4E4F-8642-87025C13998D}_is1 |
| Operation: | write | Name: | DisplayVersion |
Value: 60.0.7.4 | |||
| (PID) Process: | (8704) Instoil.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{0F9D3105-8171-4E4F-8642-87025C13998D}_is1 |
| Operation: | write | Name: | Publisher |
Value: https://www.gitlab.com | |||
Executable files
12
Suspicious files
17
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8704 | Instoil.tmp | C:\Windows\is-3QE37.tmp | — | |
MD5:— | SHA256:— | |||
| 8704 | Instoil.tmp | C:\Windows\Clear_Setup.7z | — | |
MD5:— | SHA256:— | |||
| 7228 | Instoil.exe | C:\Users\admin\AppData\Local\Temp\is-RCPL2.tmp\Instoil.tmp | executable | |
MD5:E54DF78D9DB4571C319B7B32EE0E8195 | SHA256:F60CB23DE2041A04C7413DBF0D0B7FF69458962A8B0D5FDBC2CBC18B9B053D9E | |||
| 8568 | Instoil.exe | C:\Users\admin\AppData\Local\Temp\is-Q6SHR.tmp\Instoil.tmp | executable | |
MD5:E54DF78D9DB4571C319B7B32EE0E8195 | SHA256:F60CB23DE2041A04C7413DBF0D0B7FF69458962A8B0D5FDBC2CBC18B9B053D9E | |||
| 4948 | Instoil.exe | C:\Users\admin\AppData\Local\Temp\is-P83AE.tmp\Instoil.tmp | executable | |
MD5:E54DF78D9DB4571C319B7B32EE0E8195 | SHA256:F60CB23DE2041A04C7413DBF0D0B7FF69458962A8B0D5FDBC2CBC18B9B053D9E | |||
| 8704 | Instoil.tmp | C:\Windows\unins000.exe | executable | |
MD5:51AF1CBFCA0B73895763E07B1B128607 | SHA256:8D9637D5C14E052377284729DF6C6A93738C70E441539A27A4AE0093E3B1A0D5 | |||
| 8704 | Instoil.tmp | C:\Windows\is-NLKVT.tmp | executable | |
MD5:BEA817F702E9B22C63319CF1CCA80F7C | SHA256:503F938314F1A22689F7CA93123A5473A00D5A3AB138C1169CBFD9CA7E029AC0 | |||
| 8704 | Instoil.tmp | C:\Users\admin\AppData\Local\Temp\is-VJV2P.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 8704 | Instoil.tmp | C:\Windows\system engine_1.2855.44_INSTALL.7z | compressed | |
MD5:26DE64AE954F6F8029046F5ECC3D41BC | SHA256:78A97272DE0D23456D7882FDEBC0AFEB7174F1A465CFDE21D5466235B8F616C1 | |||
| 8704 | Instoil.tmp | C:\Windows\7z-x64.exe | executable | |
MD5:5D22E5D47698DA4B1225C3231F28A838 | SHA256:78AFA2A1C773CAF3CF7EDF62F857D2A8A5DA55FB0FFF5DA416074C0D28B2B55F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
36
DNS requests
17
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 40.127.240.158:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
3988 | svchost.exe | GET | 304 | 40.127.240.158:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 304 | 40.127.240.158:443 | https://settings-win.data.microsoft.com/settings/v3.0/WaaS/FeatureManagement?IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&CurrentBranch=vb_release&AccountFirstChar=&ActivationChannel=Retail&OEMModel=DELL&FlightRing=Retail&AttrDataVer=186&InstallLanguage=en-US&OSUILocale=en-US&WebExperience=1&FlightingBranchName=&ChassisTypeId=1&OSSkuId=48&App=CDM&InstallDate=1661339444&AppVer=&OSArchitecture=AMD64&DefaultUserRegion=244&TelemetryLevel=1&OSVersion=10.0.19045.4046&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
5752 | SIHClient.exe | GET | 304 | 74.179.77.204:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | whitelisted |
5752 | SIHClient.exe | GET | 200 | 13.85.23.206:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | whitelisted |
5752 | SIHClient.exe | GET | 200 | 74.179.77.204:443 | https://slscr.update.microsoft.com/sls/ping | unknown | — | — | whitelisted |
5752 | SIHClient.exe | GET | 304 | 74.179.77.204:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | whitelisted |
8584 | svchost.exe | POST | 403 | 88.221.169.205:443 | https://go.microsoft.com/fwlink/?LinkID=2257403&clcid=0x409 | unknown | html | 386 b | whitelisted |
8584 | svchost.exe | POST | 403 | 88.221.169.205:443 | https://go.microsoft.com/fwlink/?LinkID=2257403&clcid=0x409 | unknown | html | 386 b | whitelisted |
4280 | svchost.exe | POST | 200 | 20.190.160.128:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
3988 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2360 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 184.86.251.22:443 | th.bing.com | AKAMAI-ASN1 | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3412 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4280 | svchost.exe | 20.190.160.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4280 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
3988 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
download.wireguard.com |
| whitelisted |
ocsp.entrust.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |