| File name: | Virus.Win32.Hidrag.a |
| Full analysis: | https://app.any.run/tasks/b9366290-d1e9-4246-a69f-b94362d778f1 |
| Verdict: | Malicious activity |
| Analysis date: | August 25, 2021, 18:19:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | BE52F02B9F5B742BBCD30FD47F5814DB |
| SHA1: | F22D1BDB53AC1C99700AFDB58B0E51077C8C8841 |
| SHA256: | 3E78B345915F4E55C743DA03D7F253B2CEC49BB6BFDE9D2BA765C8E2533D96BD |
| SSDEEP: | 24576:Ea6EJgv8E32bpXnKKLA3FEQTdHUOD0/WkdmKaMaOhhS11EpsnS2dnY:vQ32l3tLtIHXAOkdmn42SV |
MALICIOUS
Drops executable file immediately after starts
- svchost.exe (PID: 2228)
- Virus.Win32.Hidrag.a.exe (PID: 1356)
Application was dropped or rewritten from another process
- Virus.Win32.Hidrag.a.exe (PID: 3268)
- svchost.exe (PID: 2228)
- svchost.exe (PID: 3452)
SUSPICIOUS
Executable content was dropped or overwritten
- Virus.Win32.Hidrag.a.exe (PID: 1356)
- svchost.exe (PID: 2228)
- svchost.exe (PID: 3452)
Creates executable files which already exist in Windows
- Virus.Win32.Hidrag.a.exe (PID: 1356)
Creates files in the Windows directory
- Virus.Win32.Hidrag.a.exe (PID: 1356)
Checks supported languages
- Virus.Win32.Hidrag.a.exe (PID: 1356)
- svchost.exe (PID: 2228)
- Virus.Win32.Hidrag.a.exe (PID: 3268)
- svchost.exe (PID: 3452)
Reads the computer name
- svchost.exe (PID: 2228)
- svchost.exe (PID: 3452)
- Virus.Win32.Hidrag.a.exe (PID: 3268)
Executed as Windows Service
- svchost.exe (PID: 3452)
Creates a software uninstall entry
- Virus.Win32.Hidrag.a.exe (PID: 3268)
Drops a file with too old compile date
- Virus.Win32.Hidrag.a.exe (PID: 1356)
- svchost.exe (PID: 2228)
- svchost.exe (PID: 3452)
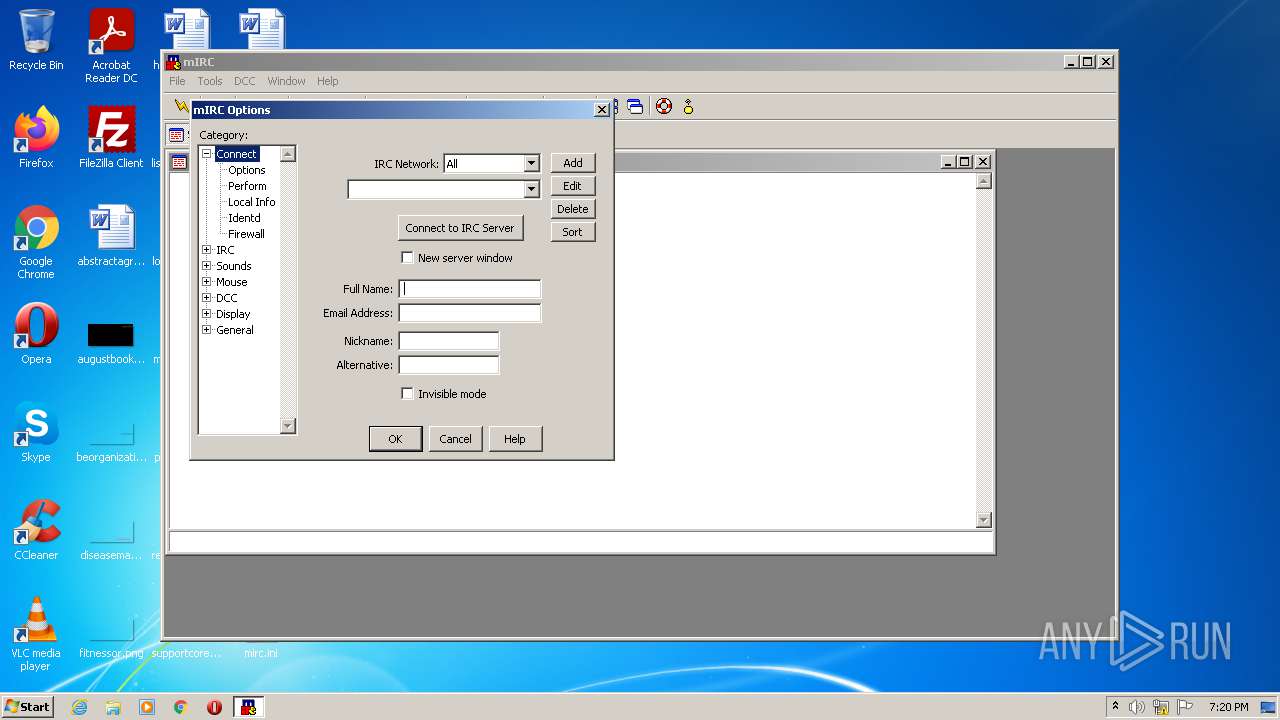
Changes default file association
- Virus.Win32.Hidrag.a.exe (PID: 3268)
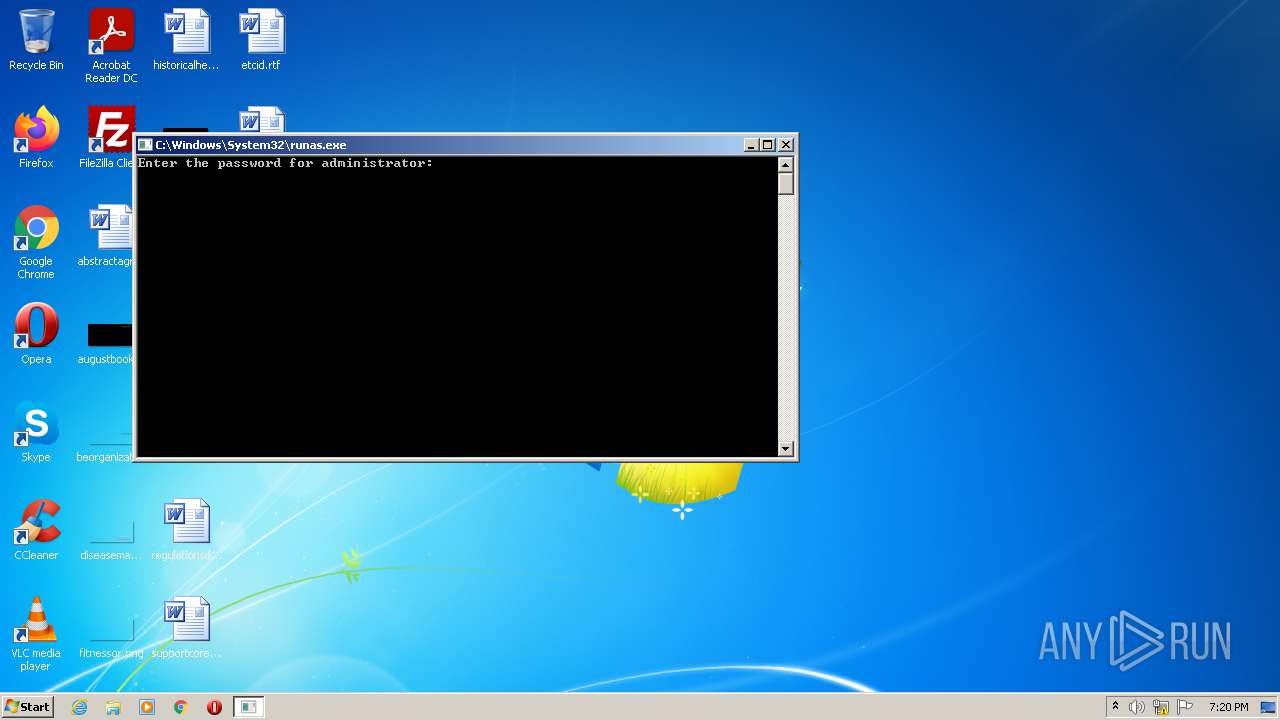
INFO
Reads the computer name
- runas.exe (PID: 2268)
Checks supported languages
- runas.exe (PID: 2268)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (29.6) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (21.4) |
| .exe | | | Win64 Executable (generic) (19) |
| .scr | | | Windows screen saver (9) |
| .exe | | | DOS Executable Borland C++ (8.9) |
EXIF
EXE
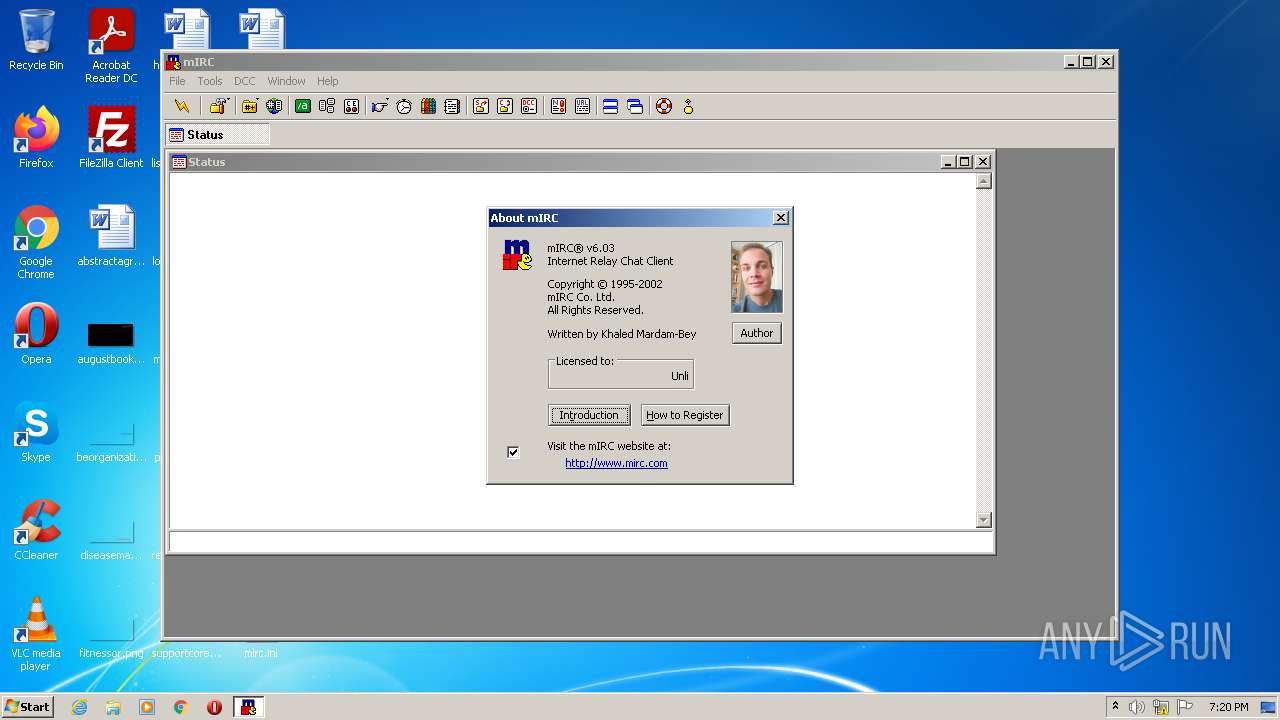
| ProductVersion: | 6.03 |
|---|---|
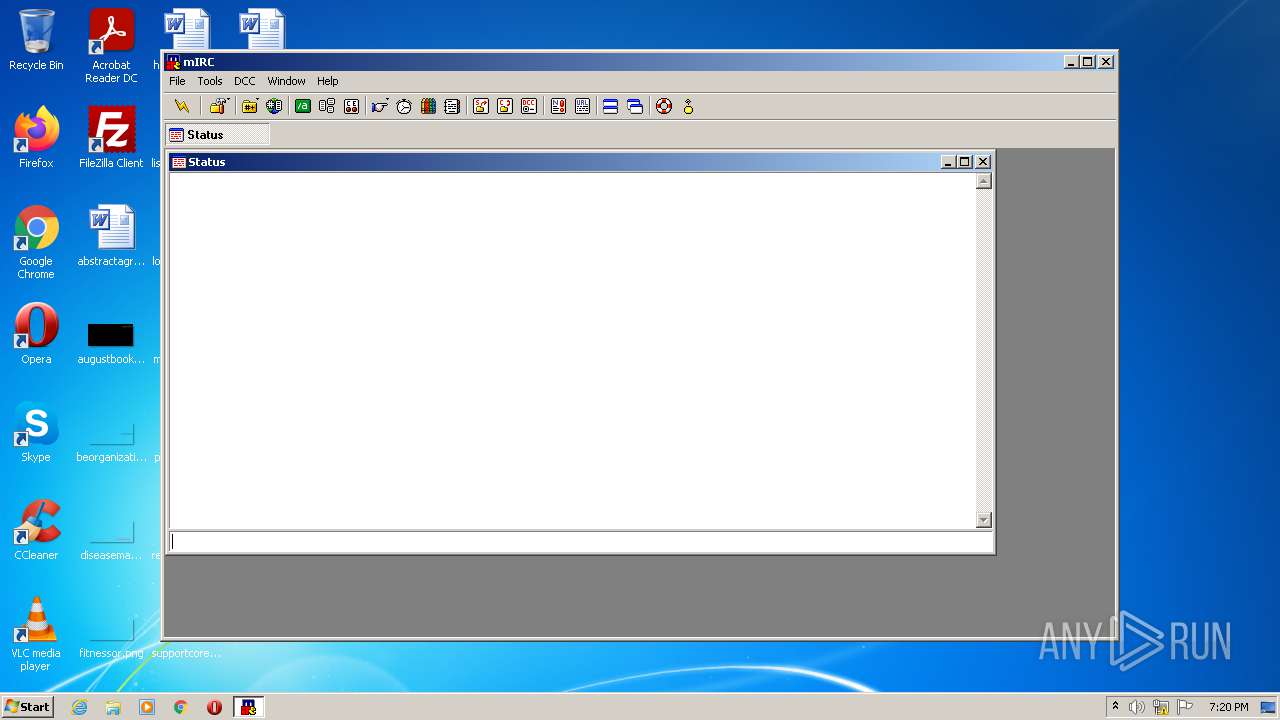
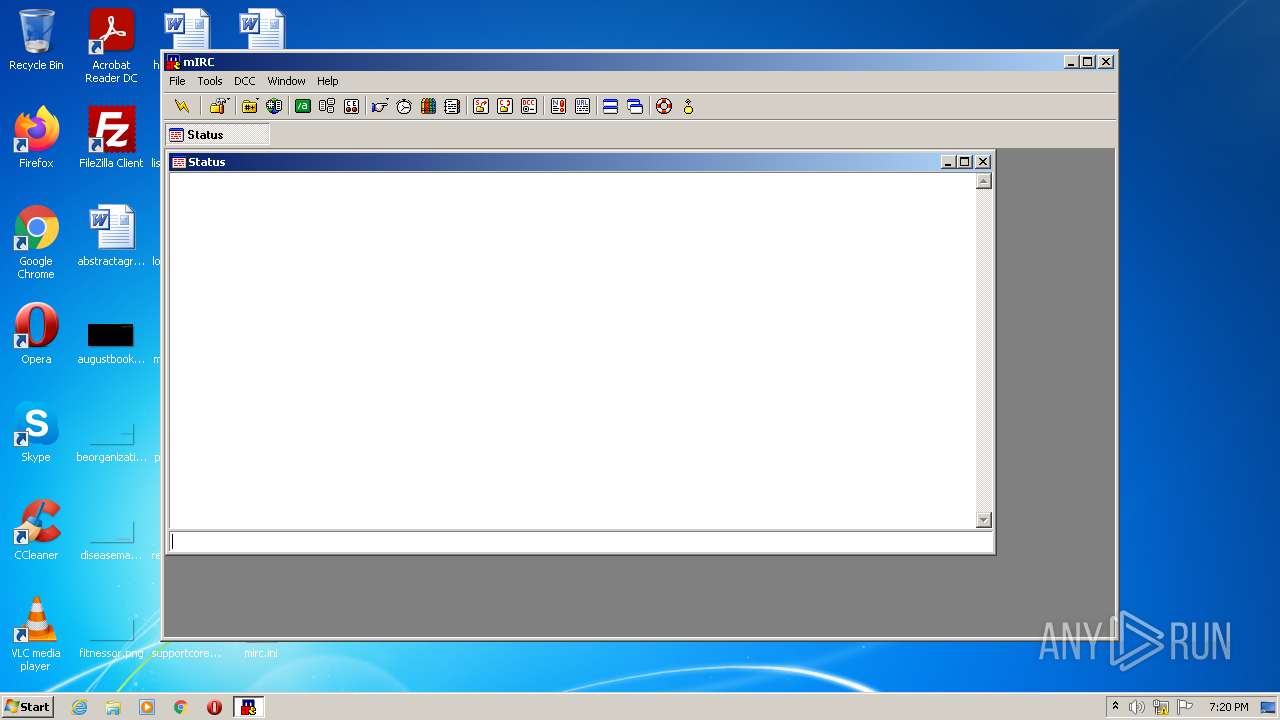
| ProductName: | mIRC |
| OriginalFileName: | mirc.exe |
| LegalTrademarks: | mIRC® is a Registered Trademark of mIRC Co. Ltd. |
| LegalCopyright: | Copyright © 1995-2002 mIRC Co. Ltd. |
| InternalName: | mIRC |
| FileVersion: | 6.03 |
| FileDescription: | mIRC |
| CompanyName: | mIRC Co. Ltd. |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 6.0.3.0 |
| FileVersionNumber: | 6.0.3.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 1 |
| OSVersion: | 4 |
| EntryPoint: | 0x11f0 |
| UninitializedDataSize: | 1024 |
| InitializedDataSize: | 4608 |
| CodeSize: | 33280 |
| LinkerVersion: | 2.55 |
| PEType: | PE32 |
| TimeStamp: | 2001:08:24 17:00:00+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Aug-2001 15:00:00 |
| Detected languages: |
|
| CompanyName: | mIRC Co. Ltd. |
| FileDescription: | mIRC |
| FileVersion: | 6.03 |
| InternalName: | mIRC |
| LegalCopyright: | Copyright © 1995-2002 mIRC Co. Ltd. |
| LegalTrademarks: | mIRC® is a Registered Trademark of mIRC Co. Ltd. |
| OriginalFilename: | mirc.exe |
| ProductName: | mIRC |
| ProductVersion: | 6.03 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 24-Aug-2001 15:00:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00007670 | 0x00007800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.20228 |
.data | 0x00009000 | 0x0000022C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.35554 |
.bss | 0x0000A000 | 0x00000224 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000B000 | 0x000008E4 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.33531 |
.rsrc | 0x0000C000 | 0x0003A000 | 0x00039E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.44003 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.17701 | 544 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 2.47702 | 34 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
3 | 2.32322 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
4 | 2.71232 | 34 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
5 | 2.6535 | 34 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
6 | 2.71232 | 34 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
7 | 2.71232 | 34 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
8 | 2.71232 | 34 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
9 | 2.61687 | 34 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
10 | 2.71232 | 34 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
ADVAPI32.DLL |
KERNEL32.dll |
msvcrt.dll |
Total processes
42
Monitored processes
5
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1356 | C:\Users\admin\Desktop\Virus.Win32.Hidrag.a.exe | C:\Users\admin\Desktop\Virus.Win32.Hidrag.a.exe | runas.exe | ||||||||||||
User: Administrator Company: mIRC Co. Ltd. Integrity Level: HIGH Description: mIRC Exit code: 0 Version: 6.03 Modules
| |||||||||||||||
| 2228 | "C:\Windows\svchost.exe" "C:\Users\admin\Desktop\Virus.Win32.Hidrag.a.exe" | C:\Windows\svchost.exe | Virus.Win32.Hidrag.a.exe | ||||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: HIGH Description: Generic Host Process for Win32 Services Exit code: 0 Version: 5.1.0.0 Modules
| |||||||||||||||
| 2268 | "C:\Windows\System32\runas.exe" /user:administrator C:\Users\admin\Desktop\Virus.Win32.Hidrag.a.exe | C:\Windows\System32\runas.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Run As Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3268 | "C:\Users\admin\Desktop\Virus.Win32.Hidrag.a.exe" | C:\Users\admin\Desktop\Virus.Win32.Hidrag.a.exe | — | svchost.exe | |||||||||||
User: Administrator Company: mIRC Co. Ltd. Integrity Level: HIGH Description: mIRC Exit code: 0 Version: 6.03 Modules
| |||||||||||||||
| 3452 | C:\Windows\svchost.exe | C:\Windows\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Generic Host Process for Win32 Services Exit code: 0 Version: 5.1.0.0 Modules
| |||||||||||||||
Total events
210
Read events
189
Write events
21
Delete events
0
Modification events
| (PID) Process: | (3268) Virus.Win32.Hidrag.a.exe | Key: | HKEY_CURRENT_USER\Software\mIRC\DateUsed |
| Operation: | write | Name: | (default) |
Value: 1629915607 | |||
| (PID) Process: | (3268) Virus.Win32.Hidrag.a.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\mIRC |
| Operation: | write | Name: | DisplayName |
Value: mIRC | |||
| (PID) Process: | (3268) Virus.Win32.Hidrag.a.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\mIRC |
| Operation: | write | Name: | UninstallString |
Value: "C:\Users\admin\Desktop\Virus.Win32.Hidrag.a.exe" -uninstall | |||
| (PID) Process: | (3268) Virus.Win32.Hidrag.a.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.cha |
| Operation: | write | Name: | (default) |
Value: ChatFile | |||
| (PID) Process: | (3268) Virus.Win32.Hidrag.a.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.chat |
| Operation: | write | Name: | (default) |
Value: ChatFile | |||
| (PID) Process: | (3268) Virus.Win32.Hidrag.a.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\ChatFile |
| Operation: | write | Name: | (default) |
Value: Chat File | |||
| (PID) Process: | (3268) Virus.Win32.Hidrag.a.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\ChatFile\DefaultIcon |
| Operation: | write | Name: | (default) |
Value: "C:\Users\admin\Desktop\Virus.Win32.Hidrag.a.exe" | |||
| (PID) Process: | (3268) Virus.Win32.Hidrag.a.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\ChatFile\Shell\open\command |
| Operation: | write | Name: | (default) |
Value: "C:\Users\admin\Desktop\Virus.Win32.Hidrag.a.exe" -noconnect | |||
| (PID) Process: | (3268) Virus.Win32.Hidrag.a.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\ChatFile\Shell\open\ddeexec |
| Operation: | write | Name: | (default) |
Value: %1 | |||
| (PID) Process: | (3268) Virus.Win32.Hidrag.a.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\ChatFile\Shell\open\ddeexec\Application |
| Operation: | write | Name: | (default) |
Value: mIRC | |||
Executable files
4
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2228 | svchost.exe | C:\Users\admin\Desktop\Virus.Win32.Hidrag.a.exe | executable | |
MD5:B766003F431CAD186BD115F5761592D1 | SHA256:22BDB2606020B82349A629248B599B64235C91E8B450E355A245EF09ECE57E1D | |||
| 1356 | Virus.Win32.Hidrag.a.exe | C:\Windows\svchost.exe | executable | |
MD5:9E3C13B6556D5636B745D3E466D47467 | SHA256:20AF03ADD533A6870D524A7C4753B42BFCEB56CDDD46016C051E23581BA743F8 | |||
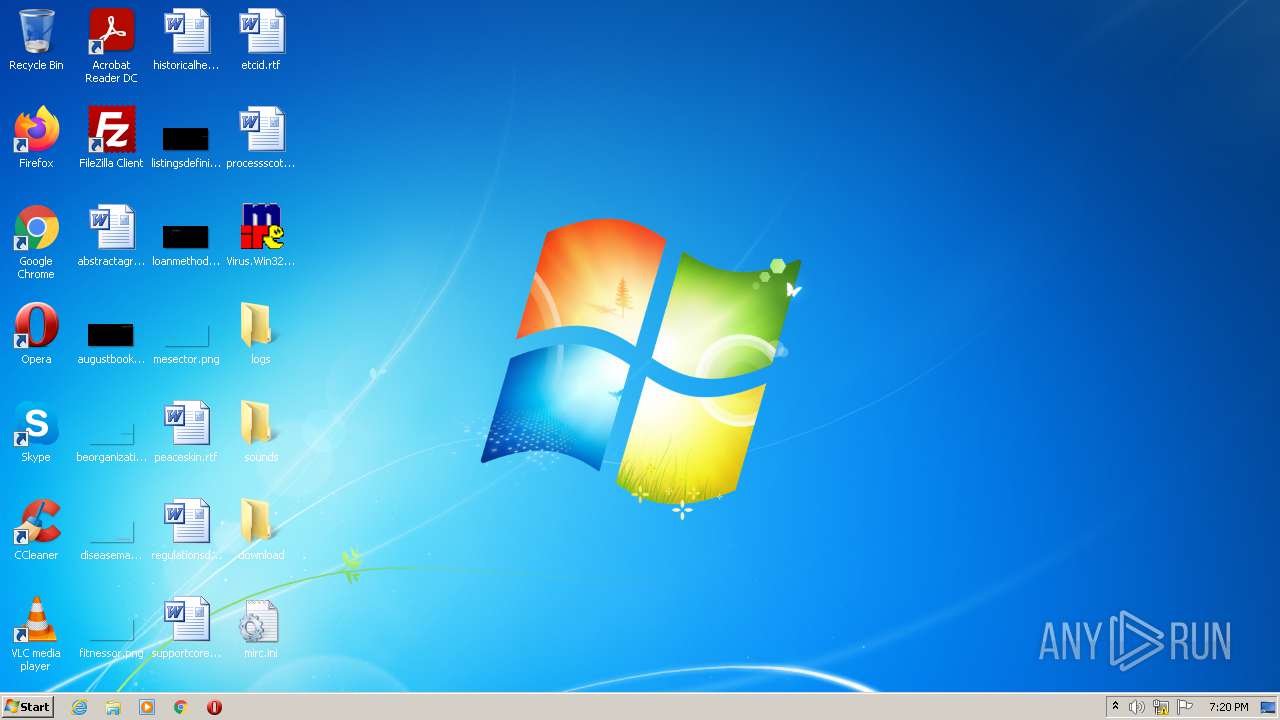
| 3268 | Virus.Win32.Hidrag.a.exe | C:\Users\admin\Desktop\mirc.ini | text | |
MD5:E9DDAD736058215D31F40268C138A6EB | SHA256:5E00F18D2B81682D061777D4FF5BBBB725FCCD944BB7AAD96A078E7C6D5428DC | |||
| 3452 | svchost.exe | C:\MSOCache\All Users\{90140000-003D-0000-0000-0000000FF1CE}-C\setup.exe | executable | |
MD5:15E2192B38B8C6162F477113B8CE027D | SHA256:4A20C212912CB30990048B595BB1BD396672200F97518E01CC810D4566BB3A52 | |||
| 3452 | svchost.exe | C:\MSOCache\All Users\{90140000-006E-0407-0000-0000000FF1CE}-C\DW20.EXE | executable | |
MD5:E1652E8351D699AAC37C60F06283E988 | SHA256:54663AD35E54992AFF1E0FD89A15AF5EEBF33A9605C44977F4AE82DCBFB7844F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report