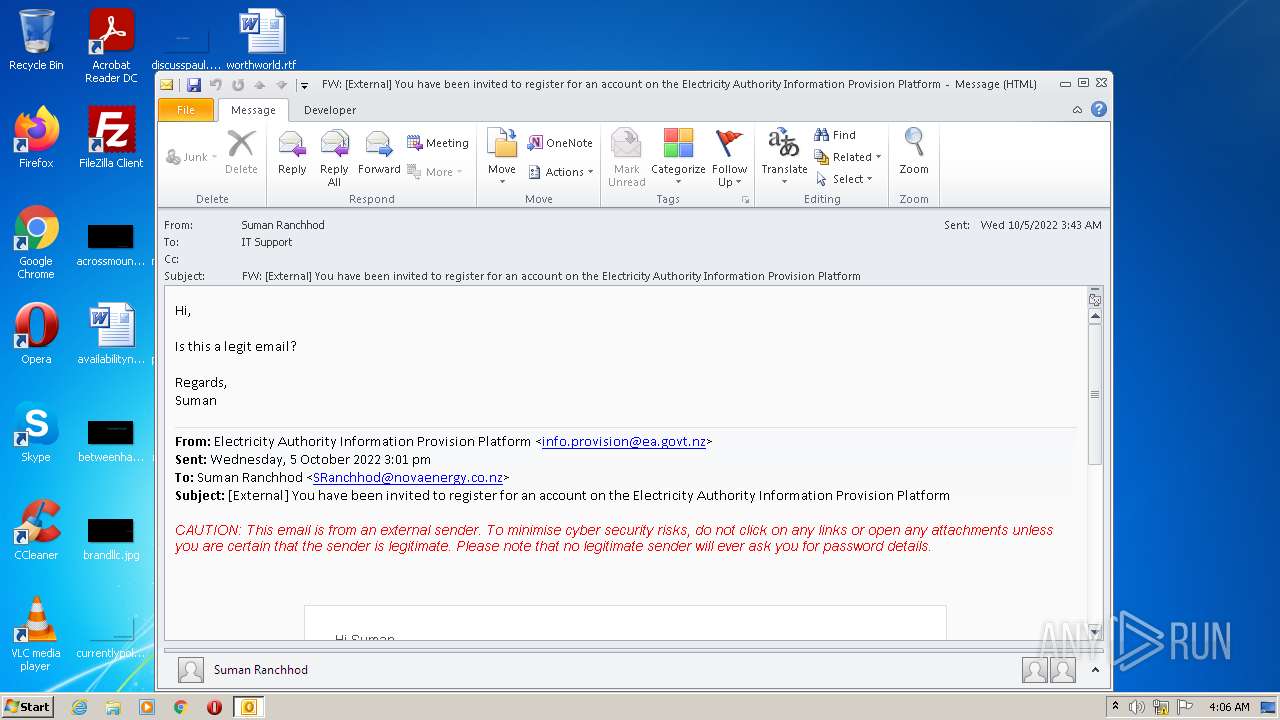
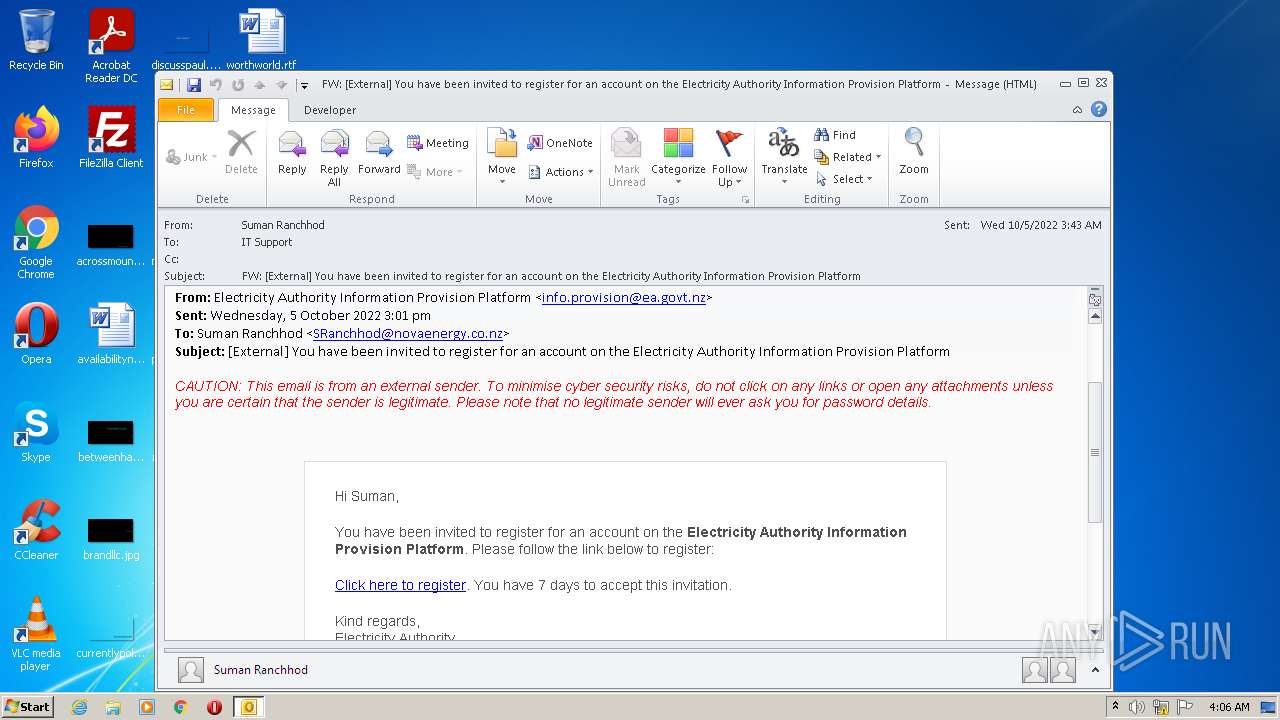
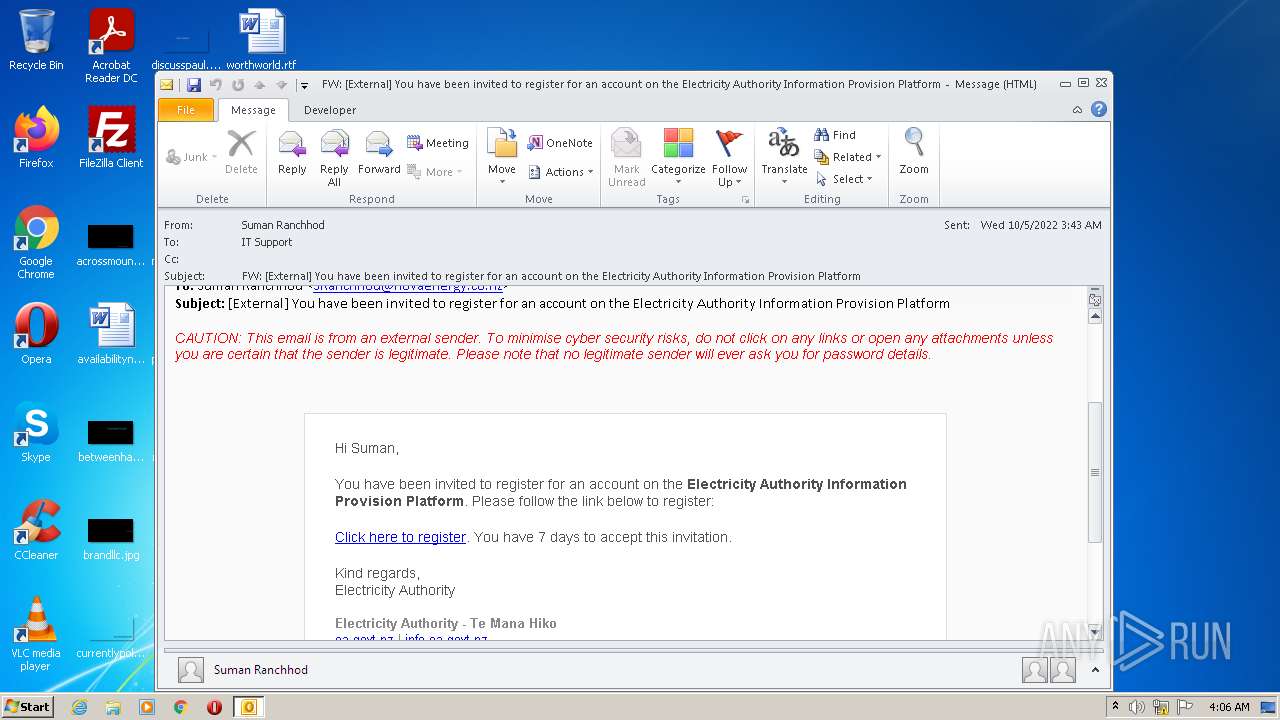
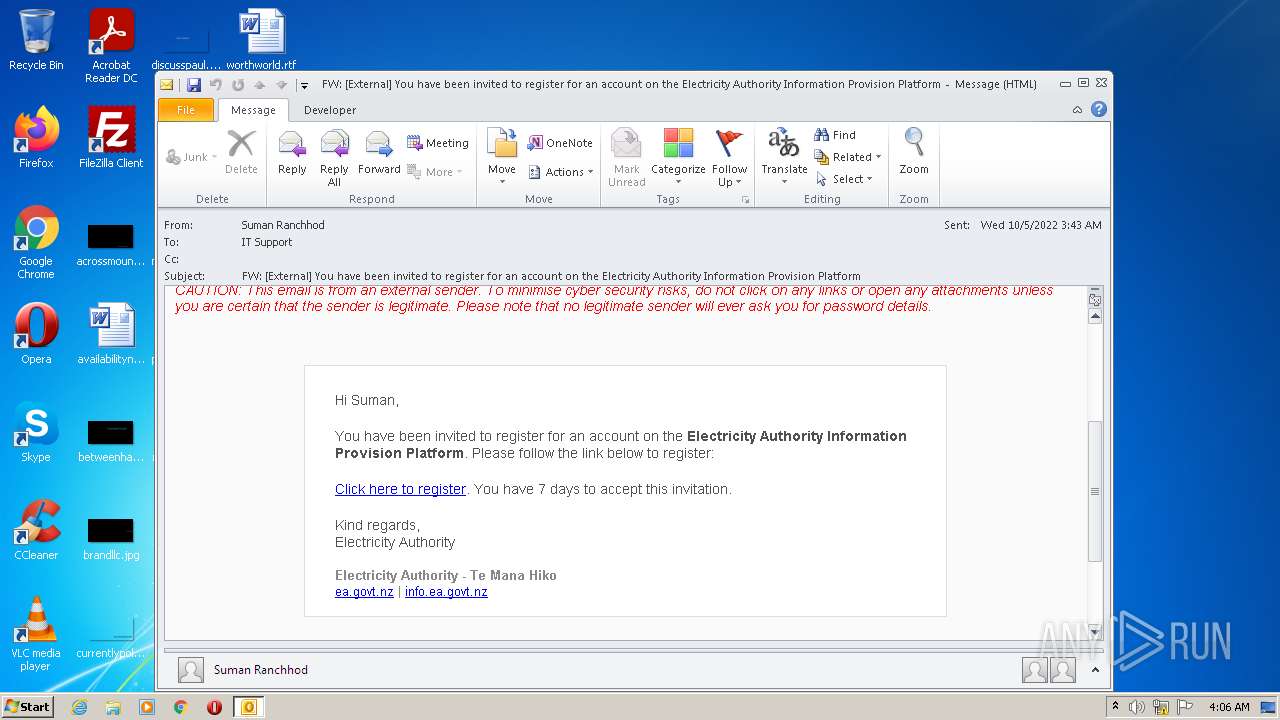
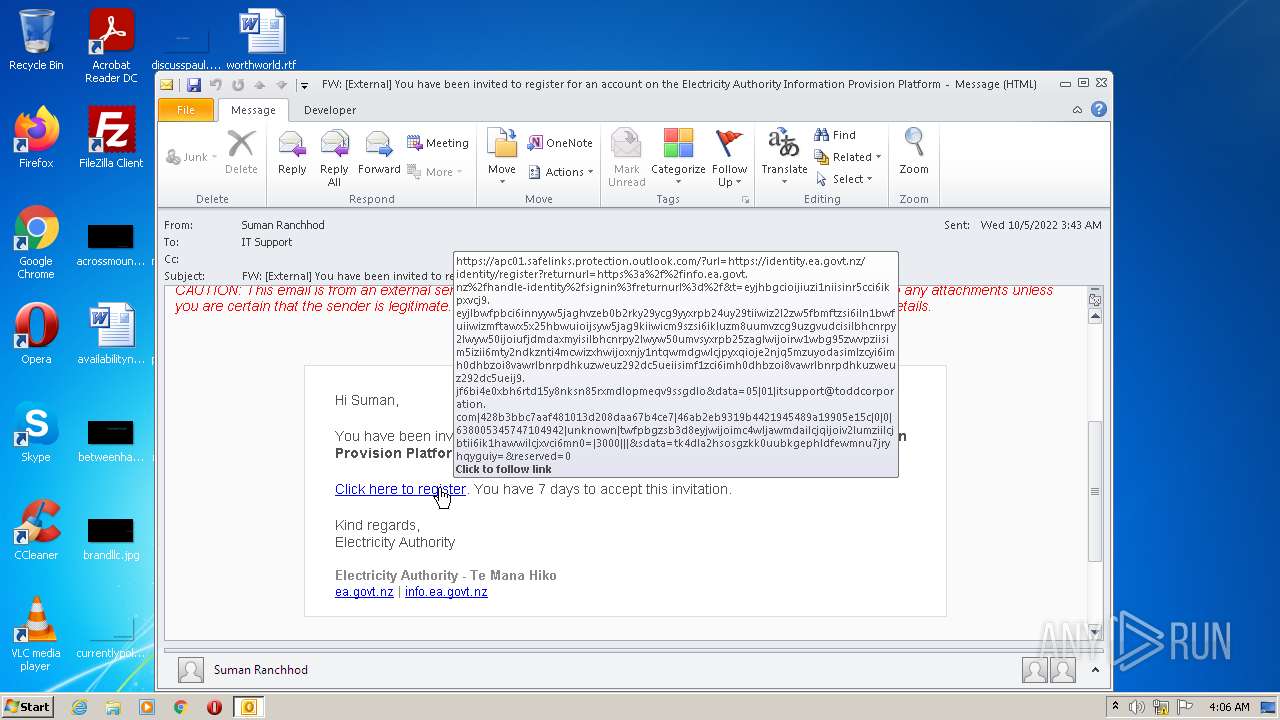
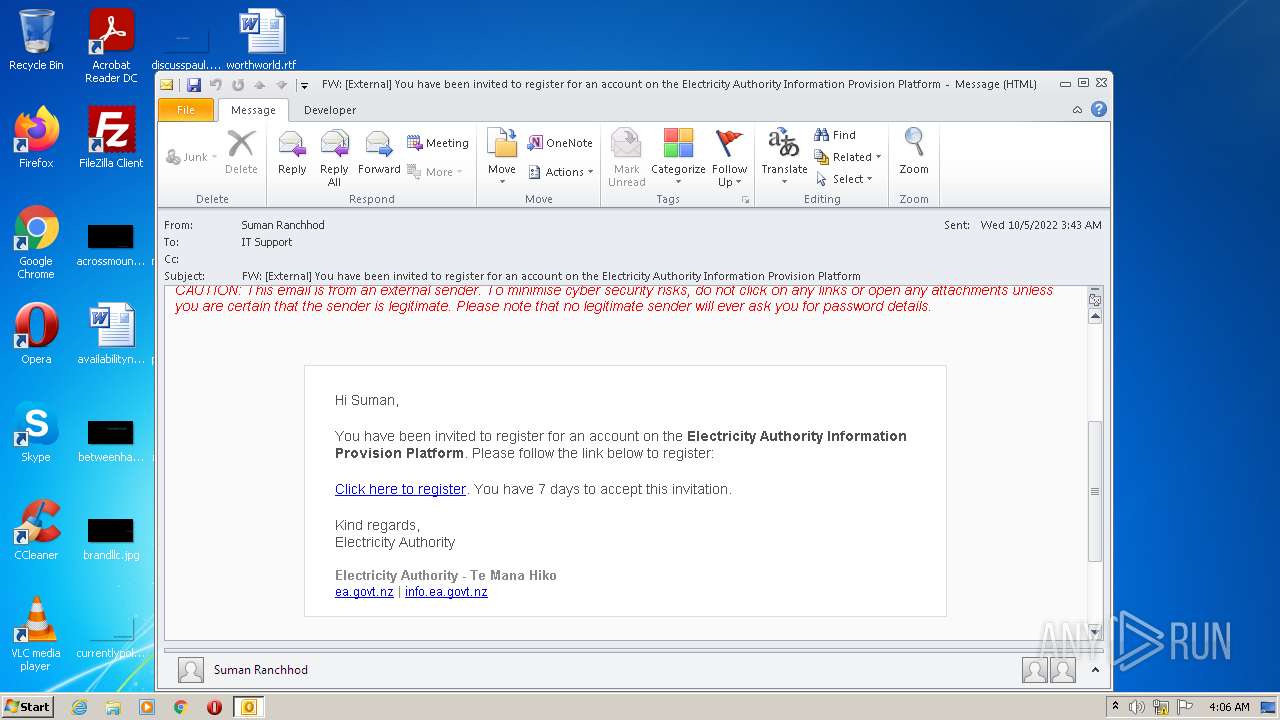
| File name: | FW_ _External_ You have been invited to register for an account on the Electricity Authority Information Provision Platform.msg |
| Full analysis: | https://app.any.run/tasks/a45f3192-1f66-45c9-bc2a-f03aff31349c |
| Verdict: | Malicious activity |
| Analysis date: | October 05, 2022, 03:06:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 16BCD4A0D371B738AA41DC4B9D8730AA |
| SHA1: | 727BBED41AEF7D44902421AFA5882C559547D585 |
| SHA256: | 3E72346D98A340E9C91581FD3F0EF2C98692B56EA9E4FAF8EA1BA8BD1861061B |
| SSDEEP: | 768:LMn4WMoeiZU7mWsKcWsKSW5KunKgTRb4sDNCkTyz1WsKkCLtYoVqwpp5c2WsKxWo:9iEmWUWaWemy5WMCJYo3TWZWJyGnR4 |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 3176)
SUSPICIOUS
Starts Internet Explorer
- OUTLOOK.EXE (PID: 3176)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 4060)
INFO
Reads the computer name
- OUTLOOK.EXE (PID: 3176)
- iexplore.exe (PID: 1804)
- iexplore.exe (PID: 4060)
Checks supported languages
- OUTLOOK.EXE (PID: 3176)
- iexplore.exe (PID: 4060)
- iexplore.exe (PID: 1804)
Searches for installed software
- OUTLOOK.EXE (PID: 3176)
Application launched itself
- iexplore.exe (PID: 1804)
Checks Windows Trust Settings
- iexplore.exe (PID: 4060)
- iexplore.exe (PID: 1804)
Creates files in the user directory
- OUTLOOK.EXE (PID: 3176)
Changes internet zones settings
- iexplore.exe (PID: 1804)
Reads settings of System Certificates
- iexplore.exe (PID: 4060)
- iexplore.exe (PID: 1804)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1804)
Reads internet explorer settings
- iexplore.exe (PID: 4060)
Changes settings of System certificates
- iexplore.exe (PID: 1804)
Reads the date of Windows installation
- iexplore.exe (PID: 1804)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3176)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
41
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
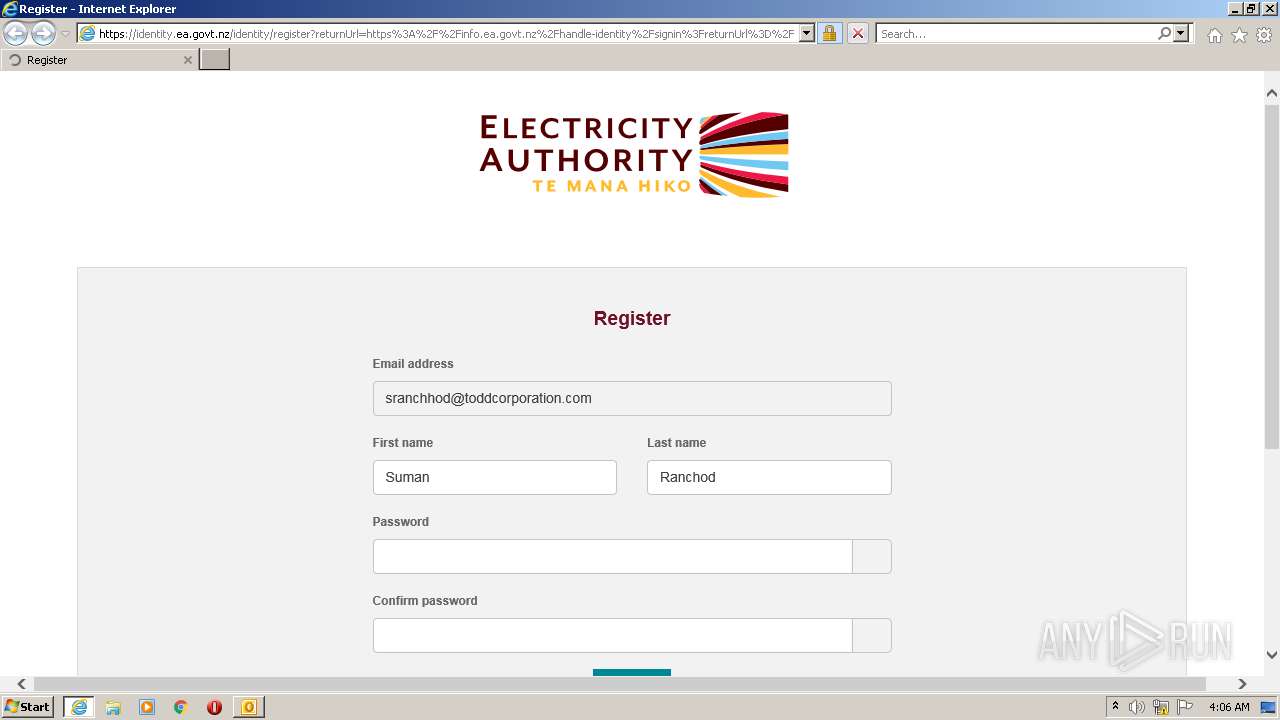
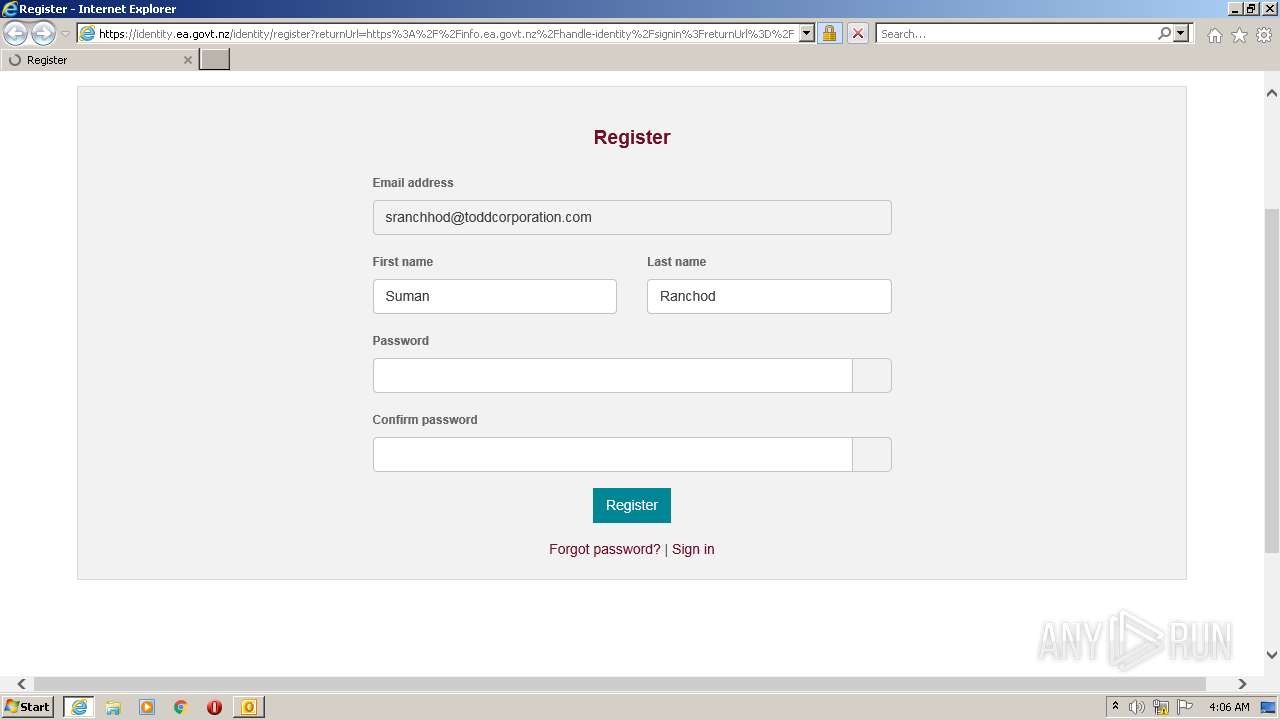
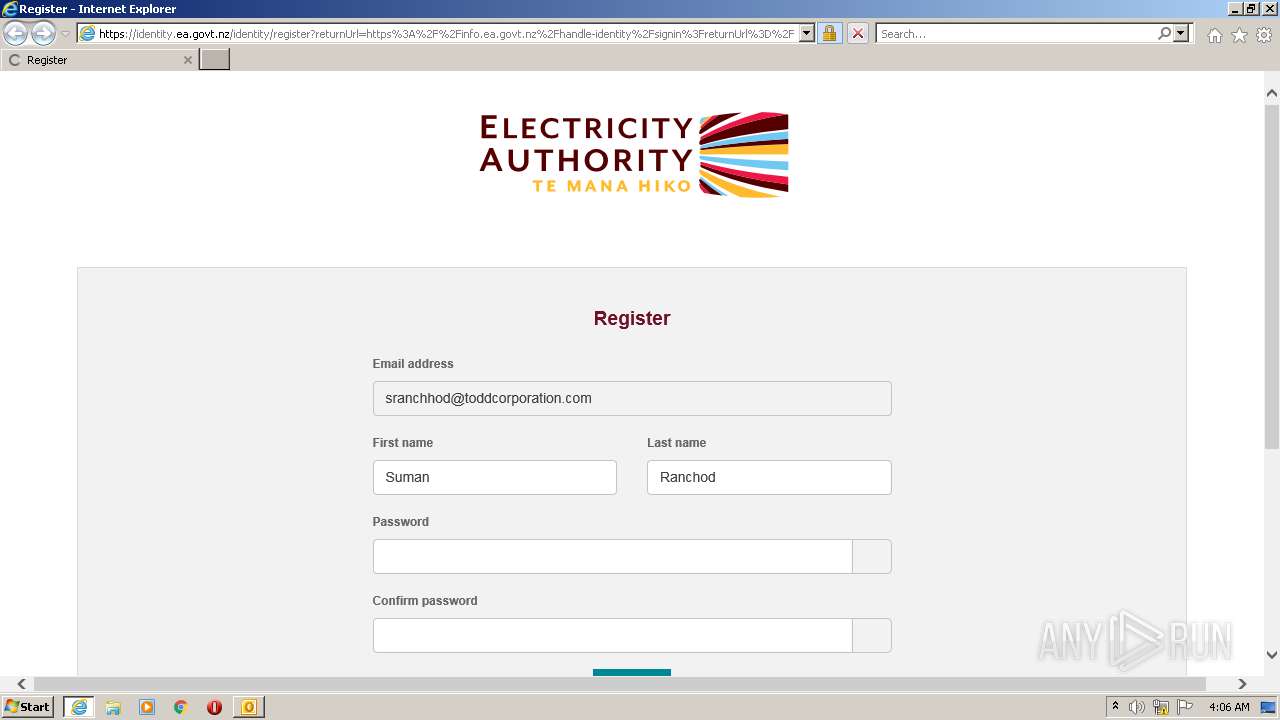
| 1804 | "C:\Program Files\Internet Explorer\iexplore.exe" https://apc01.safelinks.protection.outlook.com/?url=https%3A%2F%2Fidentity.ea.govt.nz%2Fidentity%2Fregister%3FreturnUrl%3Dhttps%253A%252F%252Finfo.ea.govt.nz%252Fhandle-identity%252Fsignin%253FreturnUrl%253D%252F%26t%3DeyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJlbWFpbCI6InNyYW5jaGhvZEB0b2RkY29ycG9yYXRpb24uY29tIiwiZ2l2ZW5fbmFtZSI6IlN1bWFuIiwiZmFtaWx5X25hbWUiOiJSYW5jaG9kIiwicm9sZSI6IkluZm8uUmVzcG9uZGVudCIsIlBhcnRpY2lwYW50IjoiUFJDMDAxMyIsIlBhcnRpY2lwYW50UmVsYXRpb25zaGlwIjoiRW1wbG95ZWVPZiIsIm5iZiI6MTY2NDkzNTI4MCwiZXhwIjoxNjY1NTQwMDgwLCJpYXQiOjE2NjQ5MzUyODAsImlzcyI6Imh0dHBzOi8vaWRlbnRpdHkuZWEuZ292dC5ueiIsImF1ZCI6Imh0dHBzOi8vaWRlbnRpdHkuZWEuZ292dC5ueiJ9.jF6bI4e0xbH6Rtd15Y8NKSn85RxmDlOPmeqV9ssGDlo&data=05%7C01%7CITSupport%40toddcorporation.com%7C428b3bbc7aaf481013d208daa67b4ce7%7C46ab2eb9319b4421945489a19905e15c%7C0%7C0%7C638005345747104942%7CUnknown%7CTWFpbGZsb3d8eyJWIjoiMC4wLjAwMDAiLCJQIjoiV2luMzIiLCJBTiI6Ik1haWwiLCJXVCI6Mn0%3D%7C3000%7C%7C%7C&sdata=tk4Dla2hSoSgZkk0UUbkgEPhLDFeWMnU7jrYHQYgUiY%3D&reserved=0 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3176 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\05c5e714-0a11-492f-a74d-ef2b845789e7.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 4060 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1804 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
20 779
Read events
20 024
Write events
729
Delete events
26
Modification events
| (PID) Process: | (3176) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3176) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3176) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3176) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3176) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3176) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3176) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3176) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3176) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (3176) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
23
Text files
47
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3176 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR5F4A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3176 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 3176 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3176 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 3176 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_F2A32EF6ACE5DF4E907A1AE68D4AF9D2.dat | xml | |
MD5:EEAA832C12F20DE6AAAA9C7B77626E72 | SHA256:C4C9A90F2C961D9EE79CF08FBEE647ED7DE0202288E876C7BAAD00F4CA29CA16 | |||
| 3176 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_WorkHours_1_2D504F485221884994A2398933D6BF0A.dat | xml | |
MD5:807EF0FC900FEB3DA82927990083D6E7 | SHA256:4411E7DC978011222764943081500FFF0E43CBF7CCD44264BD1AB6306CA68913 | |||
| 3176 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_Calendar_2_922CAA510FC6AB40B4BC1F96EE39F4C5.dat | xml | |
MD5:B21ED3BD946332FF6EBC41A87776C6BB | SHA256:B1AAC4E817CD10670B785EF8E5523C4A883F44138E50486987DC73054A46F6F4 | |||
| 3176 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_ConversationPrefs_2_7B55903753F35043B40C9C42BB127DD9.dat | xml | |
MD5:57F30B1BCA811C2FCB81F4C13F6A927B | SHA256:612BAD93621991CB09C347FF01EC600B46617247D5C041311FF459E247D8C2D3 | |||
| 3176 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_TCPrefs_2_CCD0A0413EE52E41BC05226F00E4C8B9.dat | xml | |
MD5:F194B1FA12F9B6F46A47391FAE8BEEC2 | SHA256:FCD8D7E030BE6EA7588E5C6CB568E3F1BDFC263942074B693942A27DF9521A74 | |||
| 4060 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\2F23D0F5E4D72862517E1CB26A329742_F6FACC49395CFA949BCE851E73323C49 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
30
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3176 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
4060 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEFZnHQTqT5lMbxCBR1nSdZQ%3D | US | der | 1.42 Kb | whitelisted |
4060 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
4060 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://ocsp.usertrust.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBSr83eyJy3njhjVpn5bEpfc6MXawQQUOuEJhtTPGcKWdnRJdtzgNcZjY5oCEQDzZE5rbgBQI34JRr174fUd | US | der | 980 b | whitelisted |
4060 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTPlNxcMEqnlIVyH5VuZ4lawhZX3QQU9oUKOxGG4QR9DqoLLNLuzGR7e64CEQCRtTitXiQkOziJKSeIF%2BrW | US | der | 282 b | whitelisted |
4060 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
1804 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
4060 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQD6a7qQTCYd8hJU9n3M3mXb | US | der | 472 b | whitelisted |
4060 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAGewca9P1l7sgwzOOVR2Hc%3D | US | der | 471 b | whitelisted |
4060 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEBJBetlj4ZeUEqggpI8HVMI%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4060 | iexplore.exe | 104.47.110.28:443 | apc01.safelinks.protection.outlook.com | MICROSOFT-CORP-MSN-AS-BLOCK | JP | suspicious |
4060 | iexplore.exe | 95.140.236.128:80 | ctldl.windowsupdate.com | LLNW | US | malicious |
4060 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
4060 | iexplore.exe | 13.75.147.201:443 | identity.ea.govt.nz | MICROSOFT-CORP-MSN-AS-BLOCK | AU | unknown |
1804 | iexplore.exe | 204.79.197.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1804 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
4060 | iexplore.exe | 104.18.32.68:80 | ocsp.comodoca.com | CLOUDFLARENET | — | suspicious |
4060 | iexplore.exe | 142.250.185.100:443 | www.google.com | GOOGLE | US | whitelisted |
4060 | iexplore.exe | 216.58.212.163:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
4060 | iexplore.exe | 172.217.17.131:443 | www.gstatic.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |
config.messenger.msn.com |
| whitelisted |
apc01.safelinks.protection.outlook.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
identity.ea.govt.nz |
| unknown |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |