| File name: | Chrome.apk |
| Full analysis: | https://app.any.run/tasks/ee420108-f8c2-4982-97ac-ba9dea87b3ff |
| Verdict: | Malicious activity |
| Threats: | Octo malware, also known as ExobotCompact or Coper, is a sophisticated Android banking trojan that has evolved from earlier malware family Exobot. It poses a significant threat to financial institutions, mobile users, and enterprise networks. |
| Analysis date: | December 13, 2025, 20:54:38 |
| OS: | Android 14 |
| Tags: | |
| MIME: | application/vnd.android.package-archive |
| File info: | Android package (APK), with gradle app-metadata.properties, with APK Signing Block |
| MD5: | D8AB0A645BABB4E1FE652C443989B7C7 |
| SHA1: | 5F0FD2AD4E7D187ABB01B59D025DF17243D51904 |
| SHA256: | 3E67C60A59312EA8B49065F455E1D4AF52BB02A80E515C1B55989683ED64CAF1 |
| SSDEEP: | 98304:9IpqFoM0x5x0zcbdJYAVPprt1NPtnVIWMraSPLMpP0Z59qYXNuydQG9IRAnaNVDJ:VcjppI2GM |
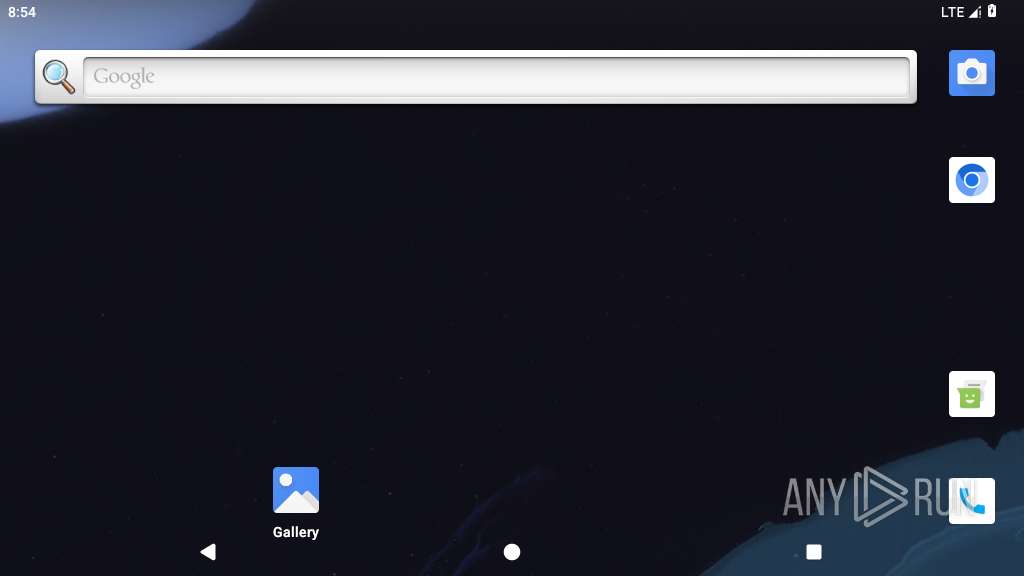
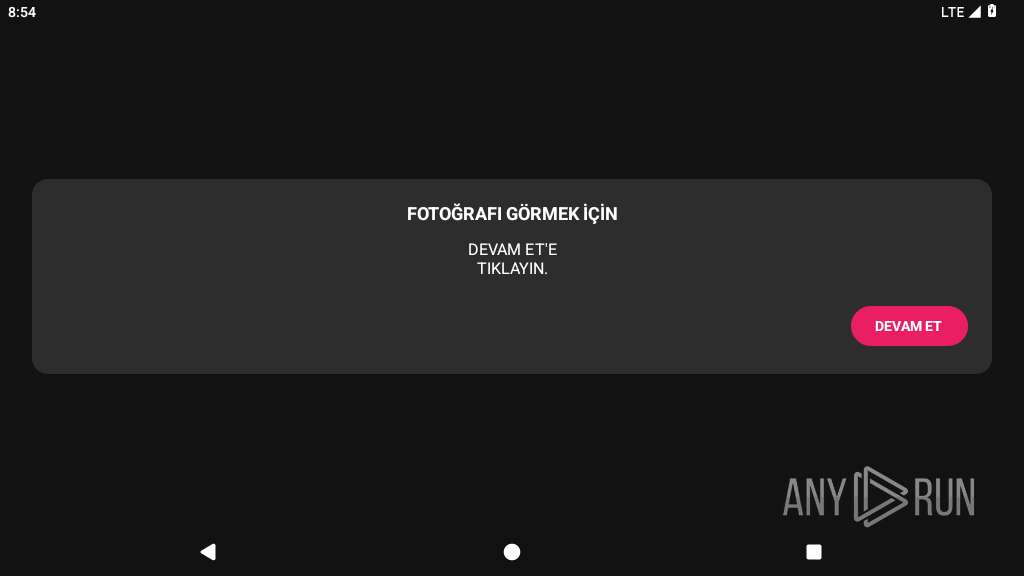
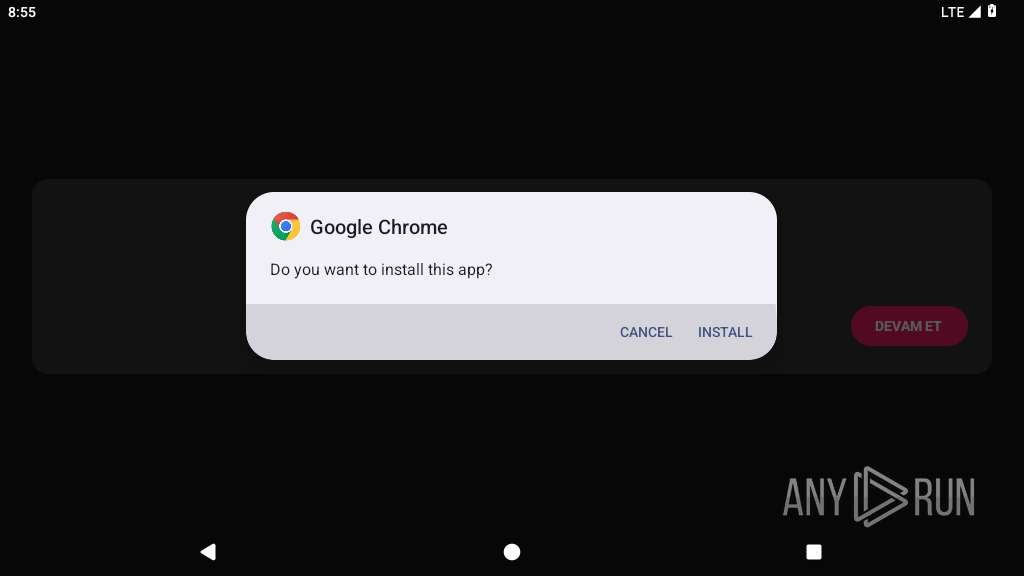
MALICIOUS
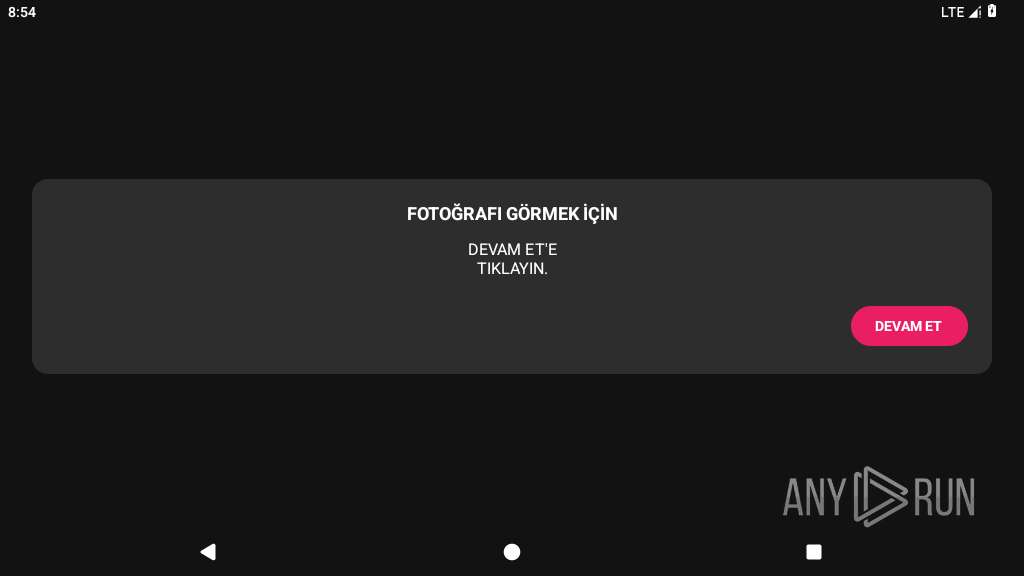
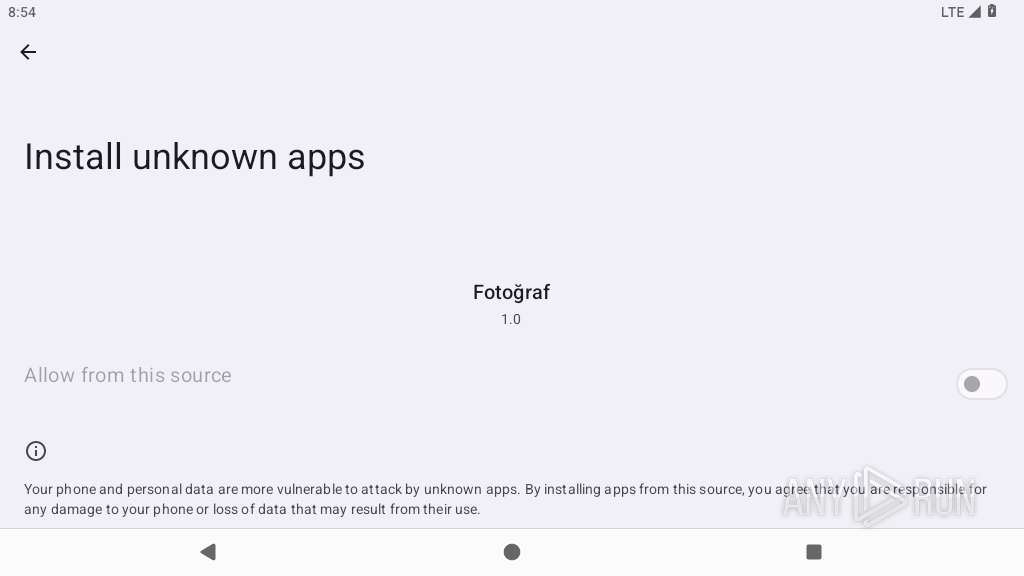
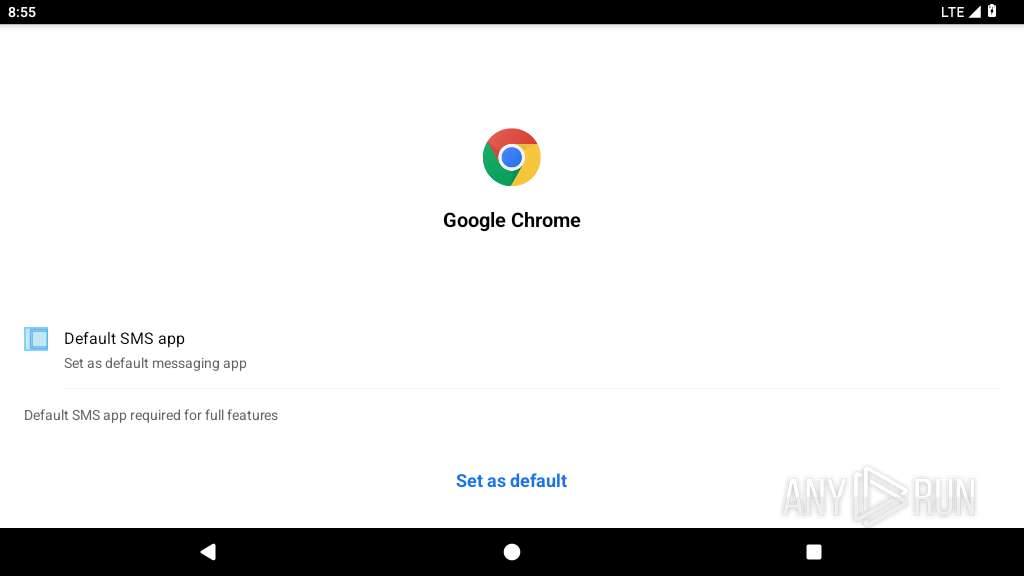
Initiates background APK installation
- app_process64 (PID: 4014)
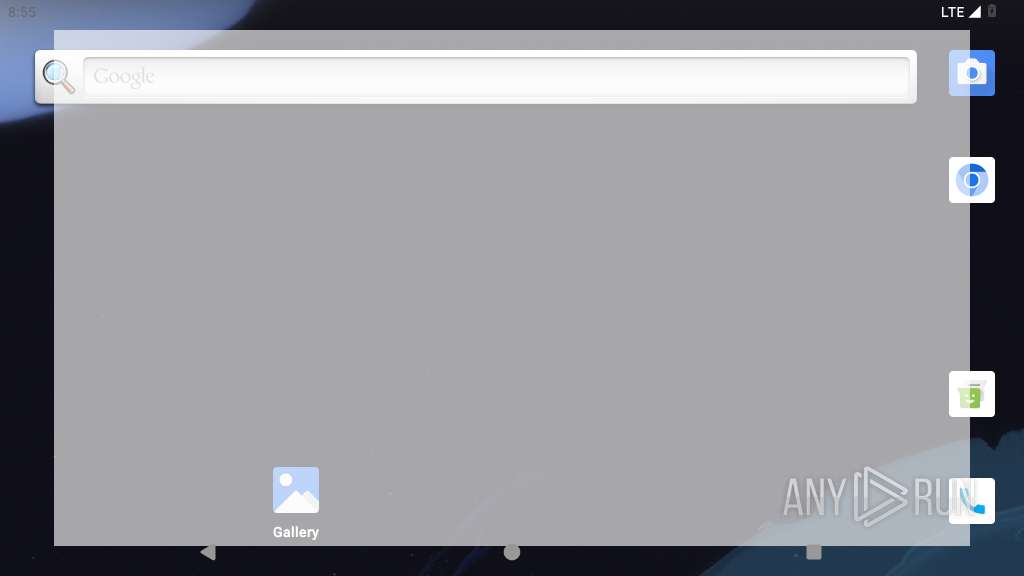
OCTO has been detected
- app_process64 (PID: 4207)
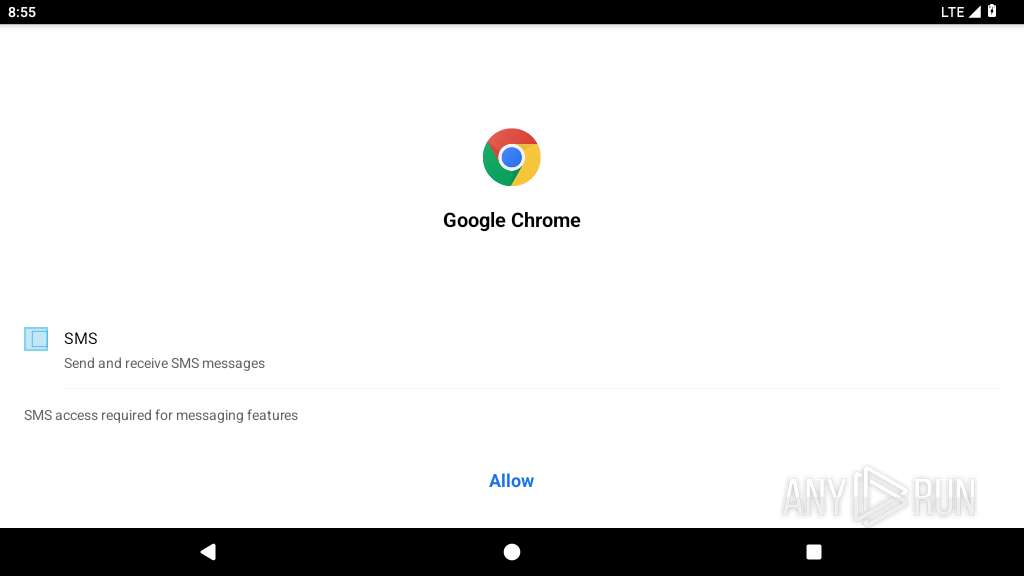
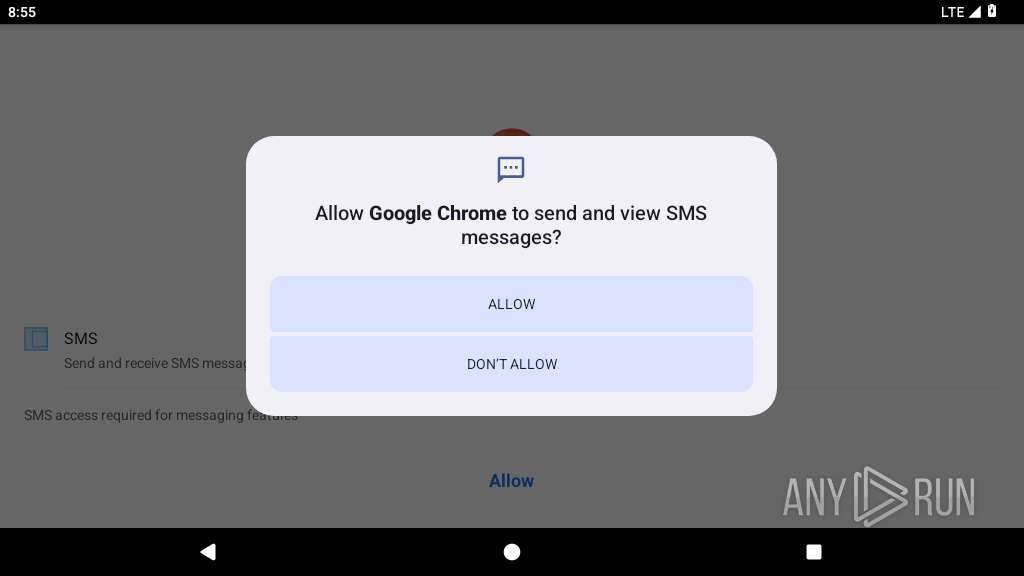
Returns the phone's primary line number (MSISDN)
- app_process64 (PID: 4207)
Determines whether a component is an active device admin
- app_process64 (PID: 4207)
SUSPICIOUS
Retrieves Android OS build information
- app_process64 (PID: 4014)
Accesses system-level resources
- app_process64 (PID: 4014)
Collects data about the device's environment (JVM version)
- app_process64 (PID: 4014)
Abuses foreground service for persistence
- app_process64 (PID: 4014)
- app_process64 (PID: 4207)
Launches a new activity
- app_process64 (PID: 4014)
- app_process64 (PID: 4207)
Executes dynamic code using class loader
- app_process64 (PID: 4207)
Monitors user physical activity status
- app_process64 (PID: 4207)
Updates data in the storage of application settings (SharedPreferences)
- app_process64 (PID: 4207)
Retrieves the ISO country code of the current network
- app_process64 (PID: 4207)
Checks if the device's lock screen is showing
- app_process64 (PID: 4207)
Retrieves the MCC and MNC of the SIM card operator
- app_process64 (PID: 4207)
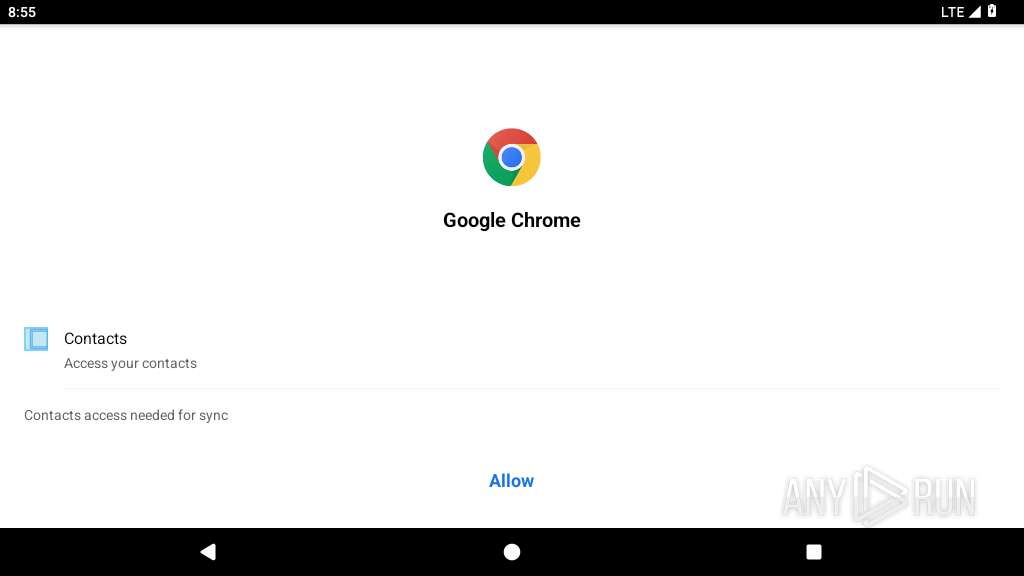
Retrieves installed applications on device
- app_process64 (PID: 4207)
Acquires a wake lock to keep the device awake
- app_process64 (PID: 4207)
Creates a WakeLock to manage power state
- app_process64 (PID: 4207)
Starts a service
- app_process64 (PID: 4207)
Uses encryption API functions
- app_process64 (PID: 4207)
Activates a regular task at set intervals
- app_process64 (PID: 4207)
Checks exemption from battery optimization
- app_process64 (PID: 4207)
Triggers notification to user
- app_process64 (PID: 4207)
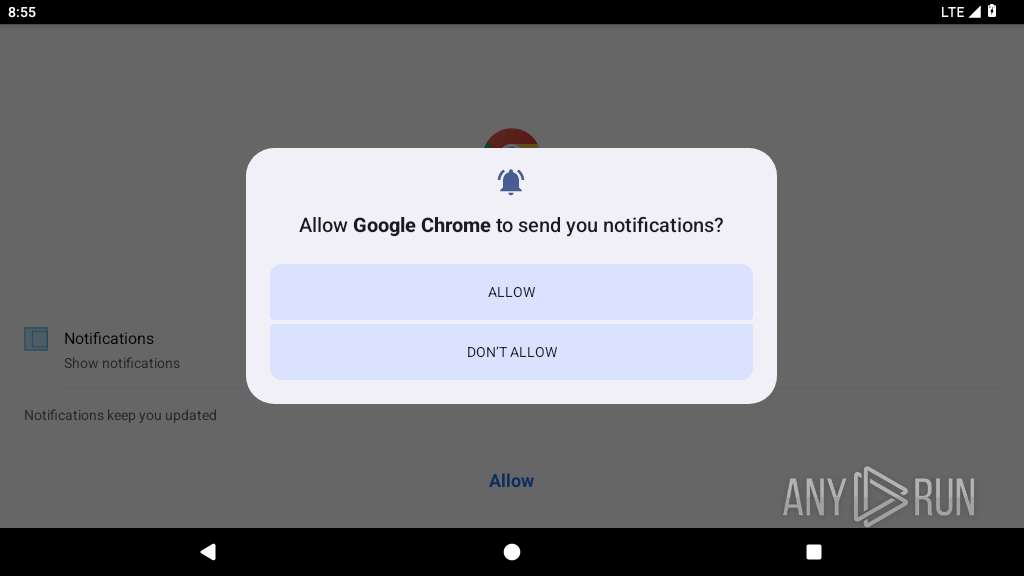
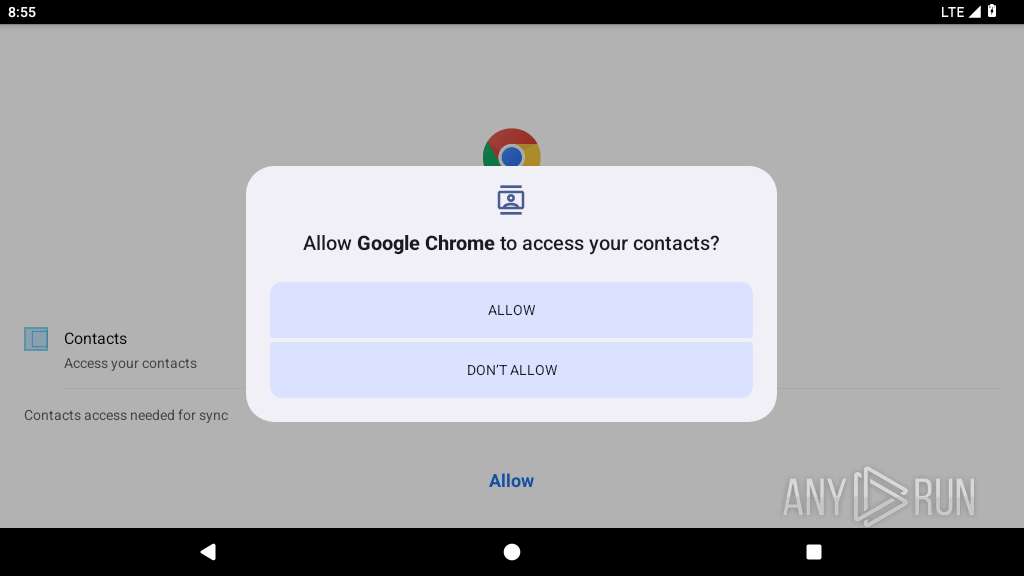
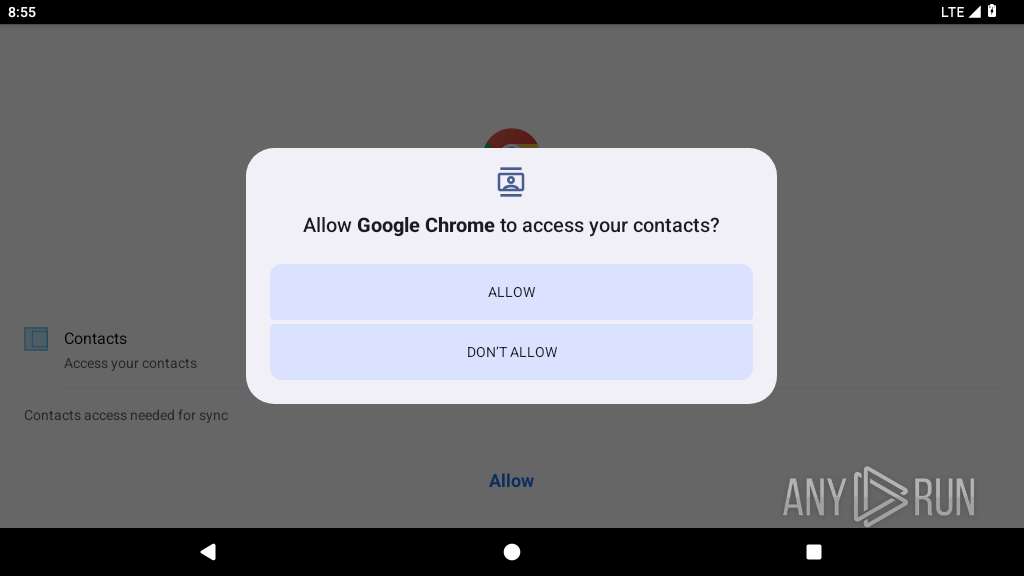
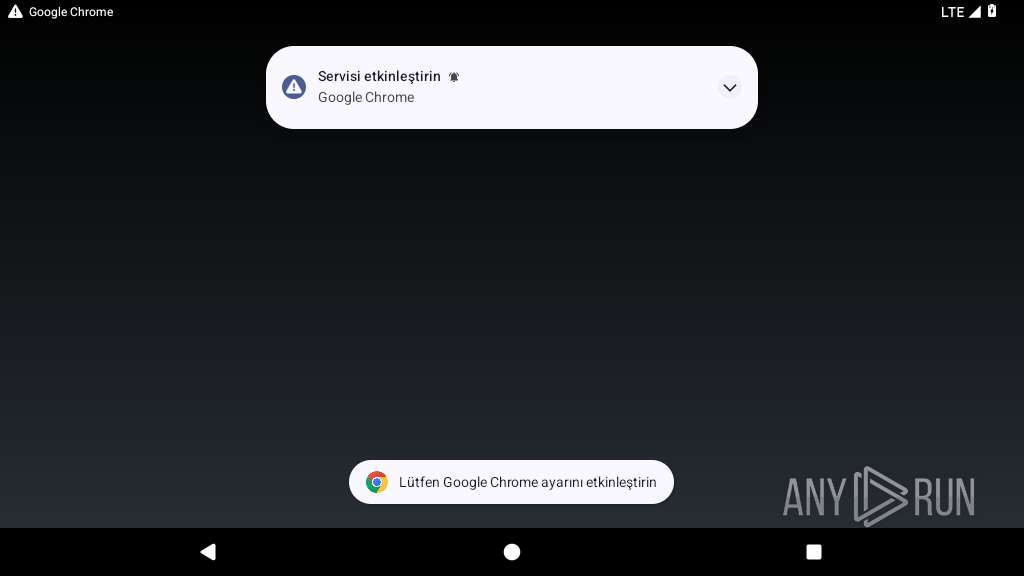
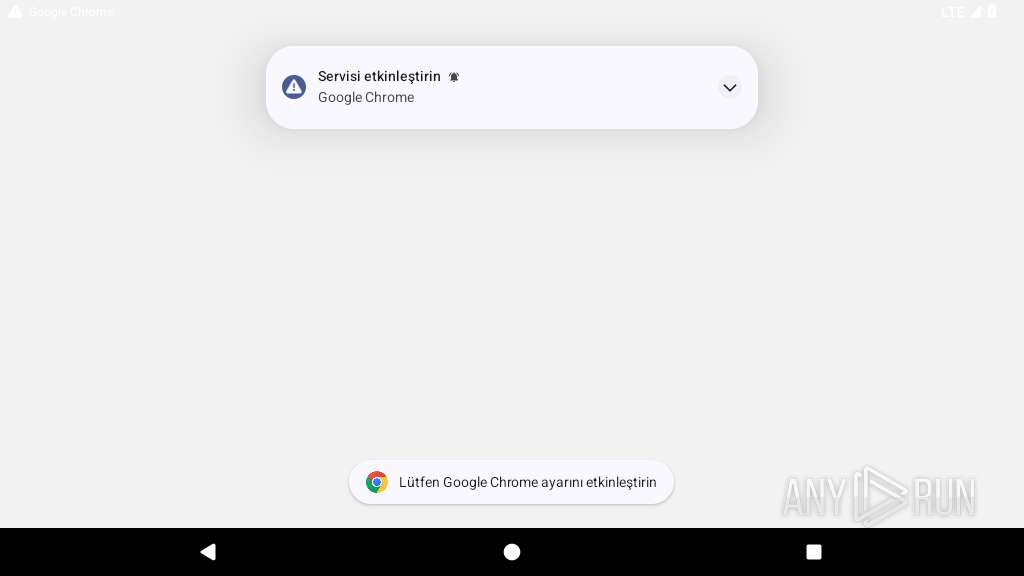
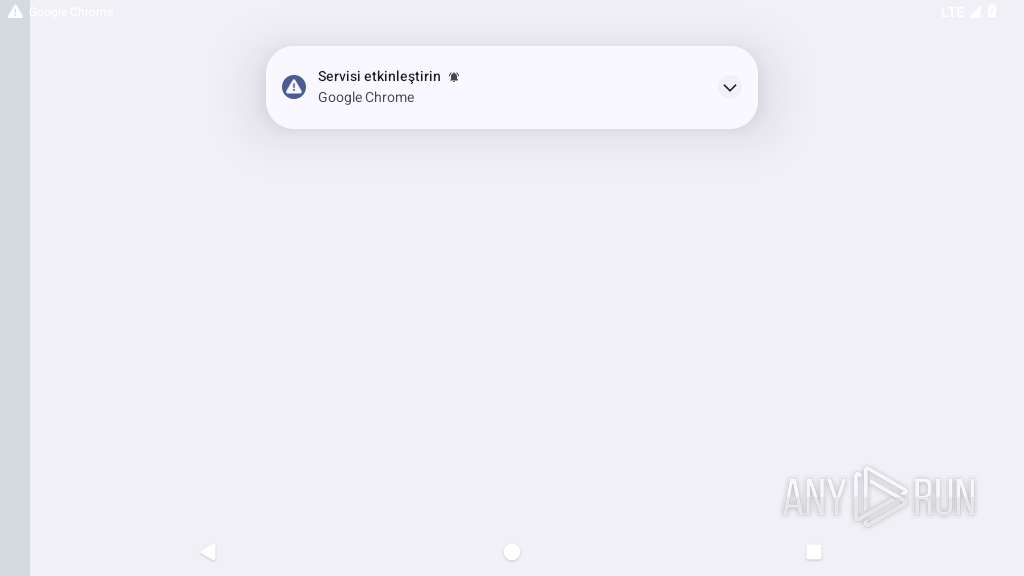
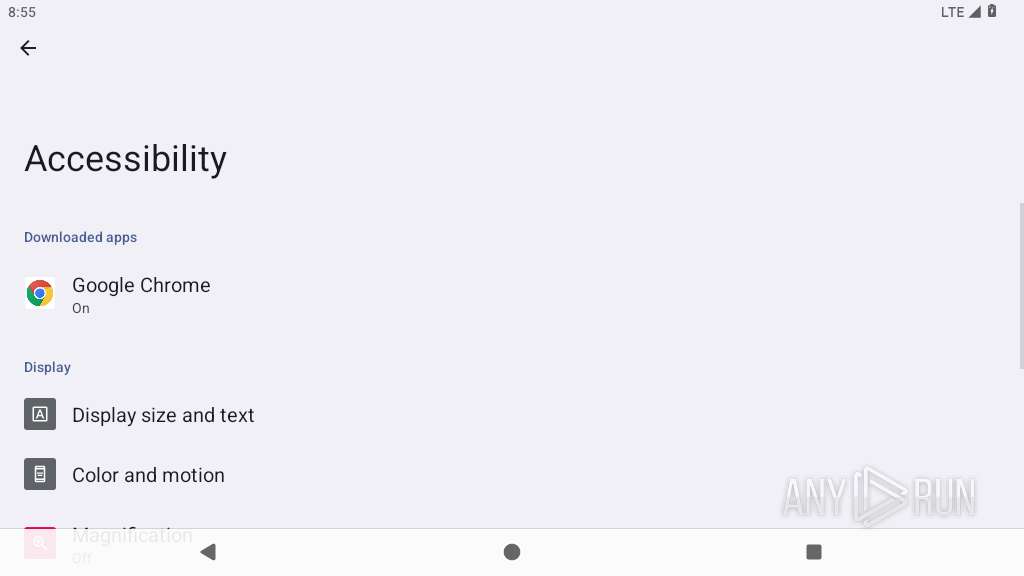
Requests access to accessibility settings
- app_process64 (PID: 4207)
Attempts to activate device administrator
- app_process64 (PID: 4207)
Intercepts events for accessibility services
- app_process64 (PID: 4207)
Scans for installed antivirus apps
- app_process64 (PID: 4207)
Prevents its uninstallation by user
- app_process64 (PID: 4207)
INFO
Dynamically inspects or modifies classes, methods, and fields at runtime
- app_process64 (PID: 4014)
- app_process64 (PID: 4207)
Dynamically registers broadcast event listeners
- app_process64 (PID: 4014)
- app_process64 (PID: 4207)
Gets the display metrics associated with the device's screen
- app_process64 (PID: 4014)
Dynamically loads a class in Java
- app_process64 (PID: 4014)
Gets file name without full path
- app_process64 (PID: 4014)
Loads a native library into the application
- app_process64 (PID: 4207)
Listens for changes in airplane mode status
- app_process64 (PID: 4207)
Retrieves data from storage of application settings (SharedPreferences)
- app_process64 (PID: 4207)
Detects device power status
- app_process64 (PID: 4207)
Creates and writes local files
- app_process64 (PID: 4207)
Retrieves the value of a secure system setting
- app_process64 (PID: 4207)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .apk | | | Android Package (73.9) |
|---|---|---|
| .jar | | | Java Archive (20.4) |
| .zip | | | ZIP compressed archive (5.6) |
EXIF
ZIP
| ZipRequiredVersion: | - |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1981:01:01 01:01:02 |
| ZipCRC: | 0x2b084705 |
| ZipCompressedSize: | 52 |
| ZipUncompressedSize: | 56 |
| ZipFileName: | META-INF/com/android/build/gradle/app-metadata.properties |
Total processes
138
Monitored processes
8
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 4014 | com.android.ip4hwdx | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4196 | /apex/com.android.art/bin/artd | /apex/com.android.art/bin/artd | — | init |
User: artd Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4200 | /apex/com.android.art/bin/dex2oat32 --zip-fd=6 --zip-location=/data/app/~~Poya1rt5sDuLfADoh1LrNQ==/com.baselistenvzx-nTGmpwuK3t4n8pozwjfXXQ==/base.apk --oat-fd=7 --oat-location=/data/app/~~Poya1rt5sDuLfADoh1LrNQ==/com.baselistenvzx-nTGmpwuK3t4n8pozwjfXXQ==/oat/arm64/base.odex --output-vdex-fd=8 --swap-fd=9 --class-loader-context=PCL[] --classpath-dir=/data/app/~~Poya1rt5sDuLfADoh1LrNQ==/com.baselistenvzx-nTGmpwuK3t4n8pozwjfXXQ== --instruction-set=arm64 --instruction-set-features=default --instruction-set-variant=cortex-a53 --compiler-filter=verify --compilation-reason=install --compact-dex-level=none --max-image-block-size=524288 --resolve-startup-const-strings=true --generate-mini-debug-info --runtime-arg -Xtarget-sdk-version:33 --runtime-arg -Xhidden-api-policy:enabled --runtime-arg -Xms64m --runtime-arg -Xmx512m --comments=app-version-name:1.4,app-version-code:3,art-version:340090000 | /apex/com.android.art/bin/dex2oat32 | — | artd |
User: artd Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4207 | com.baselistenvzx | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4300 | com.android.webview:webview_service | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4311 | webview_zygote | /system/bin/app_process32 | — | app_process32 |
User: webview_zygote Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4349 | com.android.webview:webview_apk | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4443 | <pre-initialized> | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
29
Text files
85
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4014 | app_process64 | /data/data/com.android.ip4hwdx/cache/oat_primary/arm64/base.4014.tmp | binary | |
MD5:— | SHA256:— | |||
| 4014 | app_process64 | /data/data/com.android.ip4hwdx/files/profileinstaller_profileWrittenFor_lastUpdateTime.dat | binary | |
MD5:— | SHA256:— | |||
| 4014 | app_process64 | /data/data/com.android.ip4hwdx/files/profileInstalled | binary | |
MD5:— | SHA256:— | |||
| 4207 | app_process64 | /data/data/com.baselistenvzx/cache/jreyot | binary | |
MD5:— | SHA256:— | |||
| 4207 | app_process64 | /data/data/com.baselistenvzx/shared_prefs/main.xml | xml | |
MD5:— | SHA256:— | |||
| 4207 | app_process64 | /data/data/com.baselistenvzx/cache/oat_primary/arm64/base.4207.tmp | binary | |
MD5:— | SHA256:— | |||
| 4207 | app_process64 | /data/data/com.baselistenvzx/app_webview/last-exit-info | binary | |
MD5:— | SHA256:— | |||
| 4207 | app_process64 | /data/data/com.baselistenvzx/shared_prefs/WebViewChromiumPrefs.xml | xml | |
MD5:— | SHA256:— | |||
| 4207 | app_process64 | /data/data/com.baselistenvzx/app_webview/Default/Web Data-journal | binary | |
MD5:— | SHA256:— | |||
| 4207 | app_process64 | /data/data/com.baselistenvzx/cache/WebView/Default/HTTP Cache/Code Cache/js/index | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
13
DNS requests
7
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1921 | app_process64 | GET | 204 | 142.250.185.100:443 | https://www.google.com/generate_204 | unknown | — | — | whitelisted |
— | — | GET | 204 | 142.250.185.100:80 | http://www.google.com/gen_204 | unknown | — | — | whitelisted |
1921 | app_process64 | GET | 204 | 142.250.184.195:80 | http://connectivitycheck.gstatic.com/generate_204 | unknown | — | — | whitelisted |
2931 | app_process64 | POST | 200 | 142.250.102.129:443 | https://staging-remoteprovisioning.sandbox.googleapis.com/v1:fetchEekChain | unknown | binary | 778 b | whitelisted |
2931 | app_process64 | POST | 200 | 142.250.102.129:443 | https://staging-remoteprovisioning.sandbox.googleapis.com/v1:signCertificates?challenge=AAABmxl-sVQBILStY99idBeFs1-1cuWE53zeA8w=&request_id=4f8da94c-6b4d-486b-83b9-bbc19f72c1cf | unknown | binary | 11.8 Kb | whitelisted |
4207 | app_process64 | POST | 200 | 45.86.86.118:443 | https://45.86.86.118/MDJmZGFkZjA1OGYz/ | unknown | text | 22.4 Kb | unknown |
4207 | app_process64 | POST | 200 | 45.86.86.118:443 | https://45.86.86.118/MDJmZGFkZjA1OGYz/ | unknown | text | 90.0 Kb | unknown |
4300 | app_process32 | GET | 200 | 142.250.185.195:443 | https://clientservices.googleapis.com/chrome-variations/seed?osname=android_webview&milestone=137 | unknown | compressed | 12.5 Kb | whitelisted |
4349 | app_process32 | POST | 200 | 142.250.184.227:443 | https://update.googleapis.com/service/update2/json?cup2key=15:kmGsjhA4WWWW8JRzV4zXpk8_t6URaX_BmF0wSjCIHzU&cup2hreq=312f8ef1937319bfc34f51b1580d74b17f35c520c40535c3dae9e6484d11f189 | unknown | text | 482 b | whitelisted |
4207 | app_process64 | POST | 200 | 45.86.86.118:443 | https://45.86.86.118/MDJmZGFkZjA1OGYz/ | unknown | text | 216 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 142.250.185.100:80 | www.google.com | GOOGLE | US | whitelisted |
452 | mdnsd | 224.0.0.251:5353 | — | — | — | whitelisted |
— | — | 142.250.184.195:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
— | — | 142.250.185.100:443 | www.google.com | GOOGLE | US | whitelisted |
1921 | app_process64 | 142.250.184.195:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
580 | app_process64 | 216.239.35.0:123 | time.android.com | GOOGLE | US | whitelisted |
1921 | app_process64 | 142.250.185.100:443 | www.google.com | GOOGLE | US | whitelisted |
2931 | app_process64 | 142.250.102.129:443 | staging-remoteprovisioning.sandbox.googleapis.com | GOOGLE | US | whitelisted |
4207 | app_process64 | 45.86.86.118:443 | — | ALEXHOST | MD | unknown |
4300 | app_process32 | 142.250.185.195:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
www.google.com |
| whitelisted |
connectivitycheck.gstatic.com |
| whitelisted |
time.android.com |
| whitelisted |
staging-remoteprovisioning.sandbox.googleapis.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1921 | app_process64 | Misc activity | ET INFO Android Device Connectivity Check |