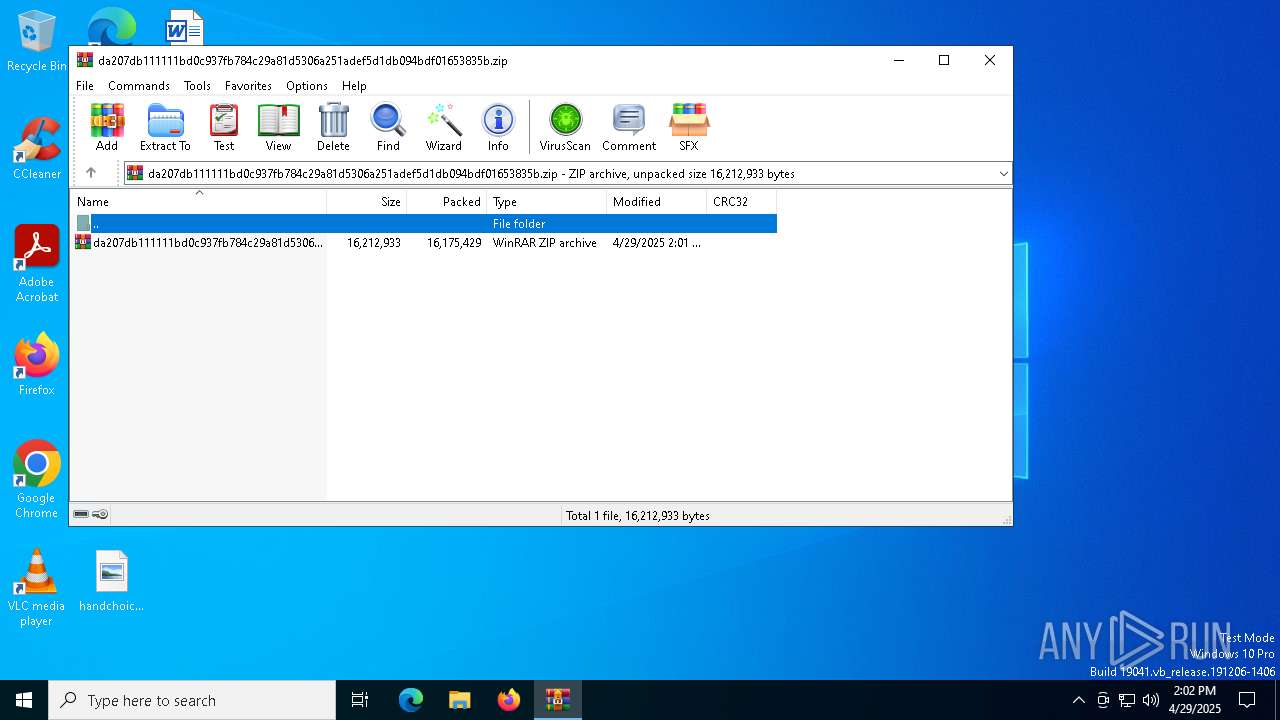
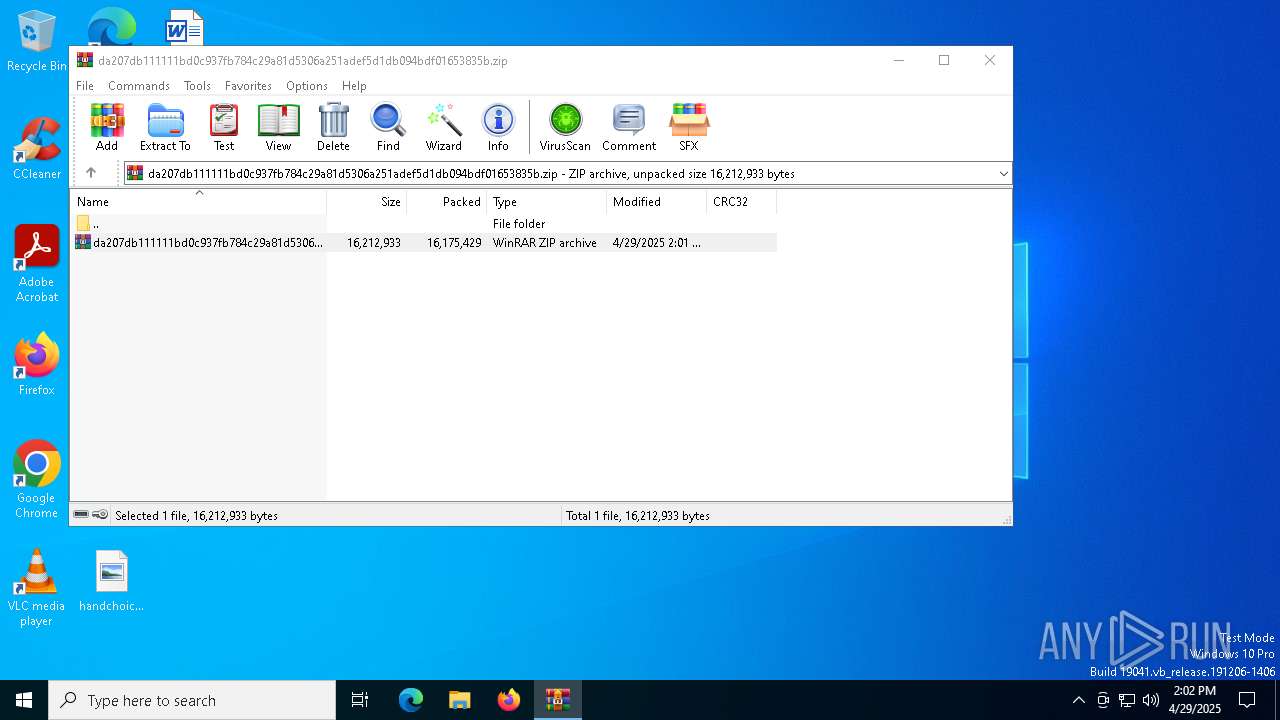
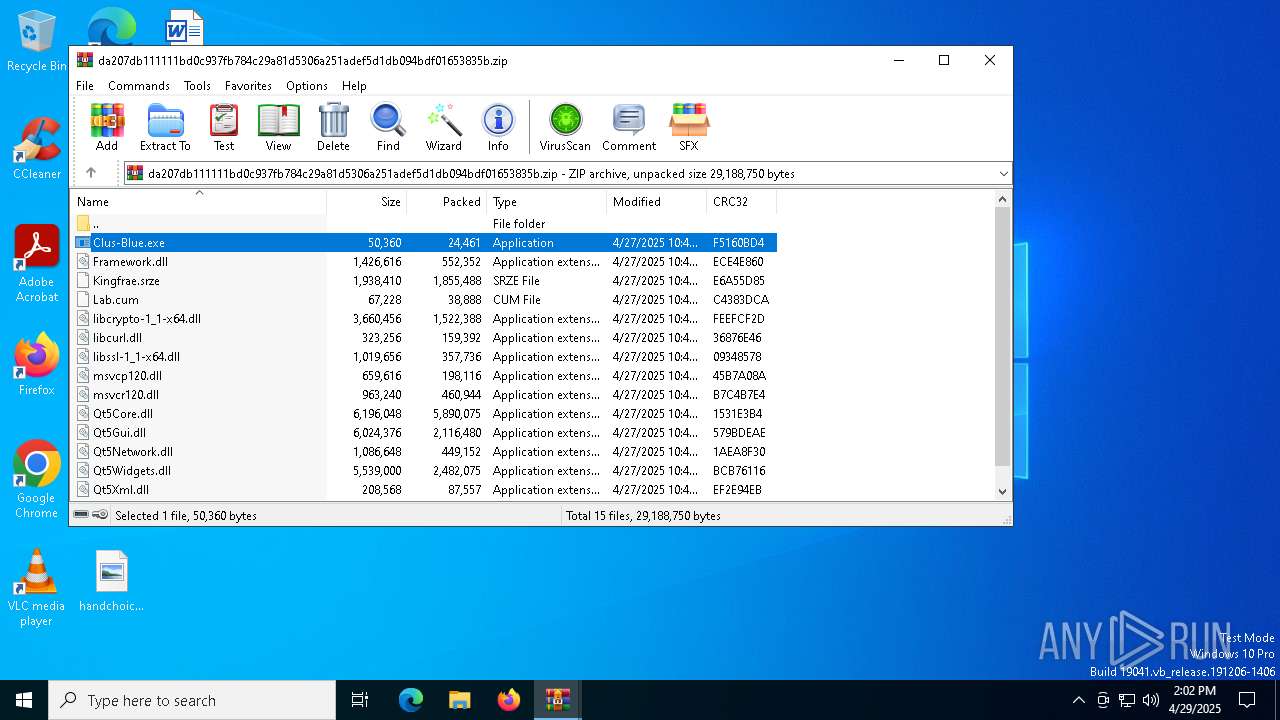
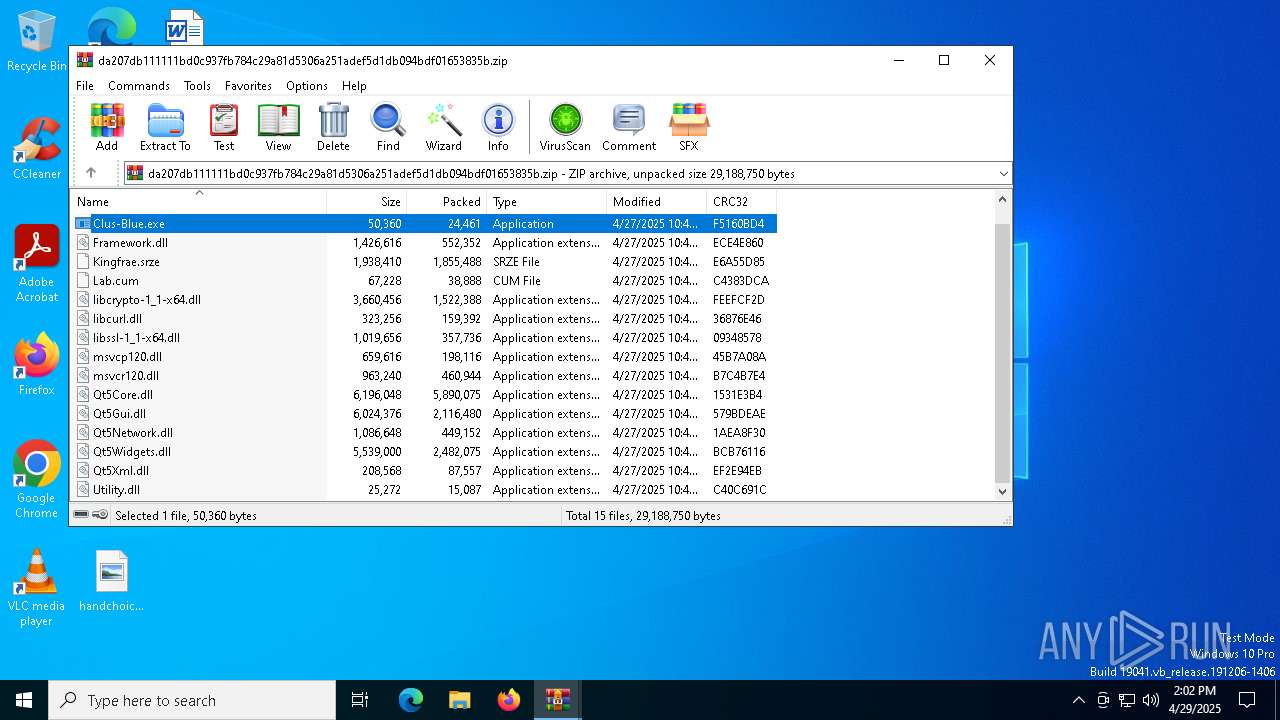
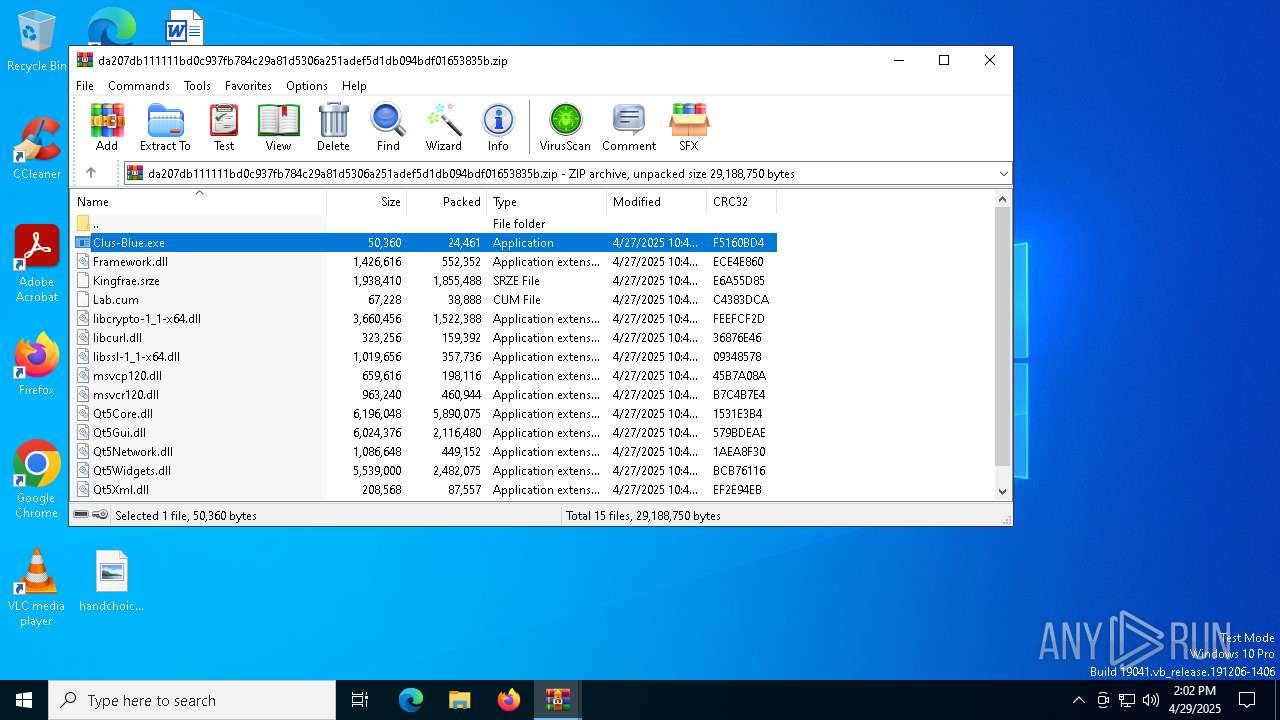
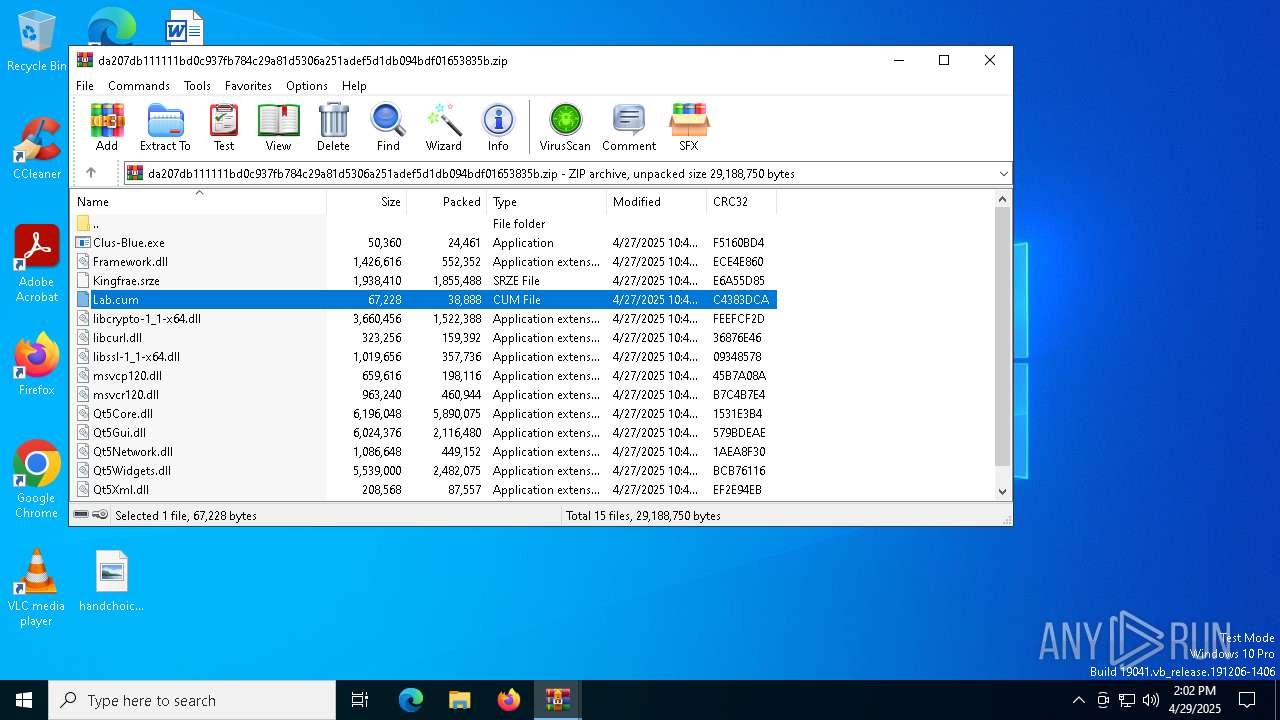
| File name: | da207db111111bd0c937fb784c29a81d5306a251adef5d1db094bdf01653835b.zip |
| Full analysis: | https://app.any.run/tasks/b585f3a3-e4a2-4db3-91ea-d78eef951faa |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 14:01:48 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
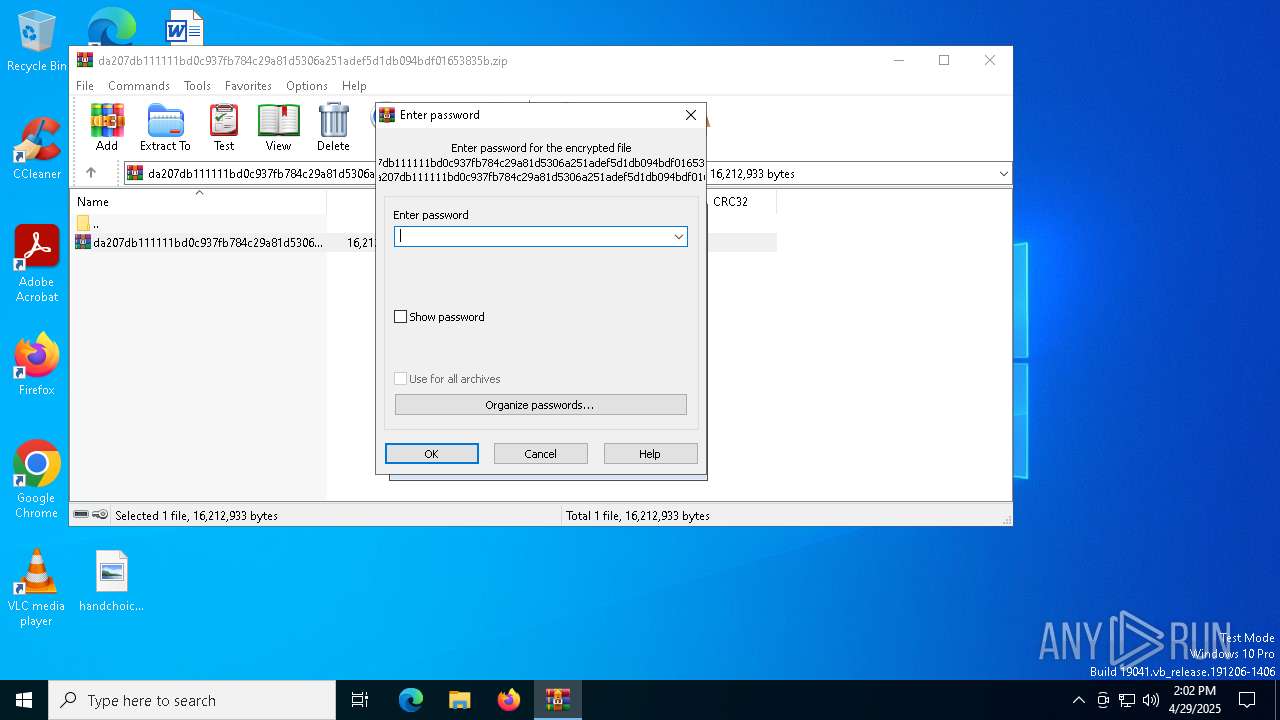
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | 0603223EB183E2A4050BA6D95808CCCC |
| SHA1: | 0F27B60D9AFAAF60313C829101CA45297D91E9B6 |
| SHA256: | 3E66F59E37B70A839A20D0DF5BBF84A3942D4D281EA6A4FA1EB2F04572A76DD9 |
| SSDEEP: | 98304:foXnoL/m2qz6XeuqqEVODR7OnZSzxIPbWHu7DtqBUE/Gc4xpfbWL1DilWMXeBQ+H:mEjDlXcvmIbKWJfUEjnS5QbDEdmyWm |
MALICIOUS
Known privilege escalation attack
- dllhost.exe (PID: 7420)
SUSPICIOUS
Application launched itself
- WinRAR.exe (PID: 7408)
Process drops legitimate windows executable
- WinRAR.exe (PID: 7408)
- WinRAR.exe (PID: 7692)
- Clus-Blue.exe (PID: 5384)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7408)
- WinRAR.exe (PID: 7692)
The process drops C-runtime libraries
- Clus-Blue.exe (PID: 5384)
Executable content was dropped or overwritten
- Clus-Blue.exe (PID: 5384)
- Clus-Blue.exe (PID: 2772)
- Clus-Blue.exe (PID: 7572)
Starts itself from another location
- Clus-Blue.exe (PID: 5384)
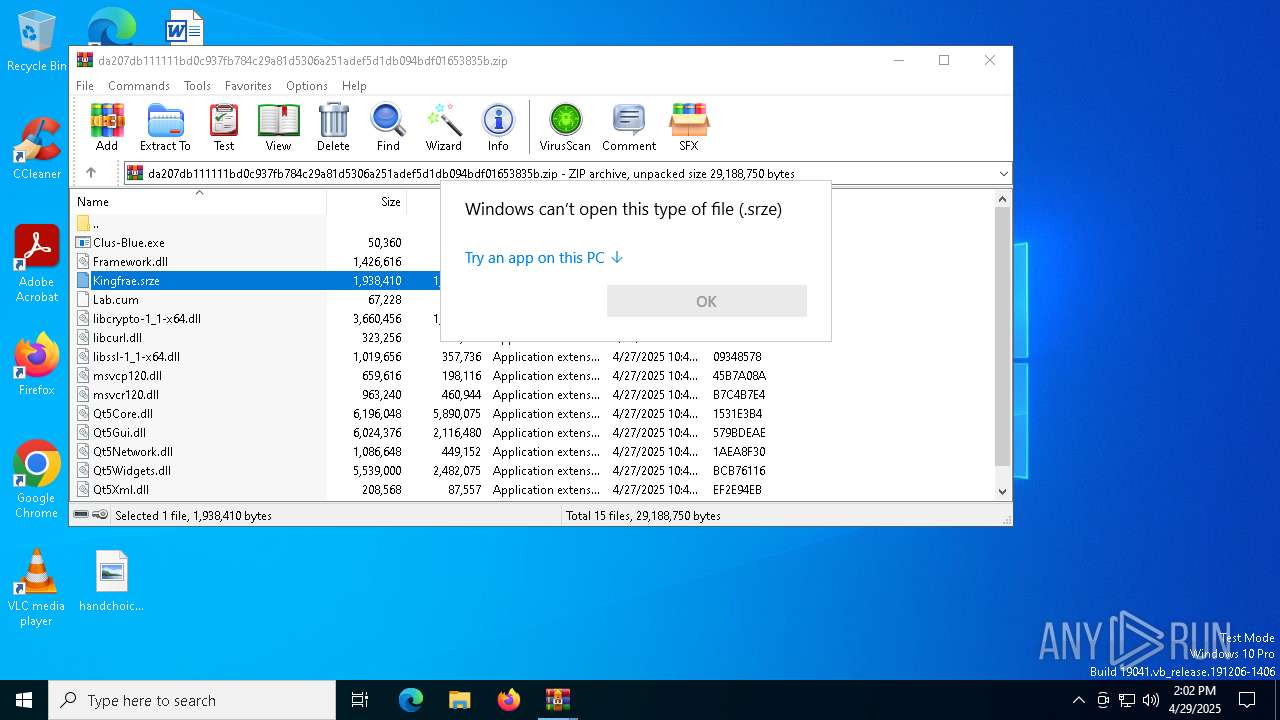
Starts application with an unusual extension
- Clus-Blue.exe (PID: 7572)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 7408)
- WinRAR.exe (PID: 7692)
- Clus-Blue.exe (PID: 5384)
Checks supported languages
- Clus-Blue.exe (PID: 5384)
- Clus-Blue.exe (PID: 7572)
- 360Tray.exe (PID: 5756)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7692)
Reads the computer name
- Clus-Blue.exe (PID: 5384)
- Clus-Blue.exe (PID: 2772)
- Clus-Blue.exe (PID: 7572)
- 360Tray.exe (PID: 5756)
- ping.com (PID: 2236)
Creates files in the program directory
- Clus-Blue.exe (PID: 5384)
- Clus-Blue.exe (PID: 2772)
The sample compiled with chinese language support
- Clus-Blue.exe (PID: 2772)
Create files in a temporary directory
- Clus-Blue.exe (PID: 2772)
- Clus-Blue.exe (PID: 7572)
Reads the machine GUID from the registry
- 360Tray.exe (PID: 5756)
Reads Microsoft Office registry keys
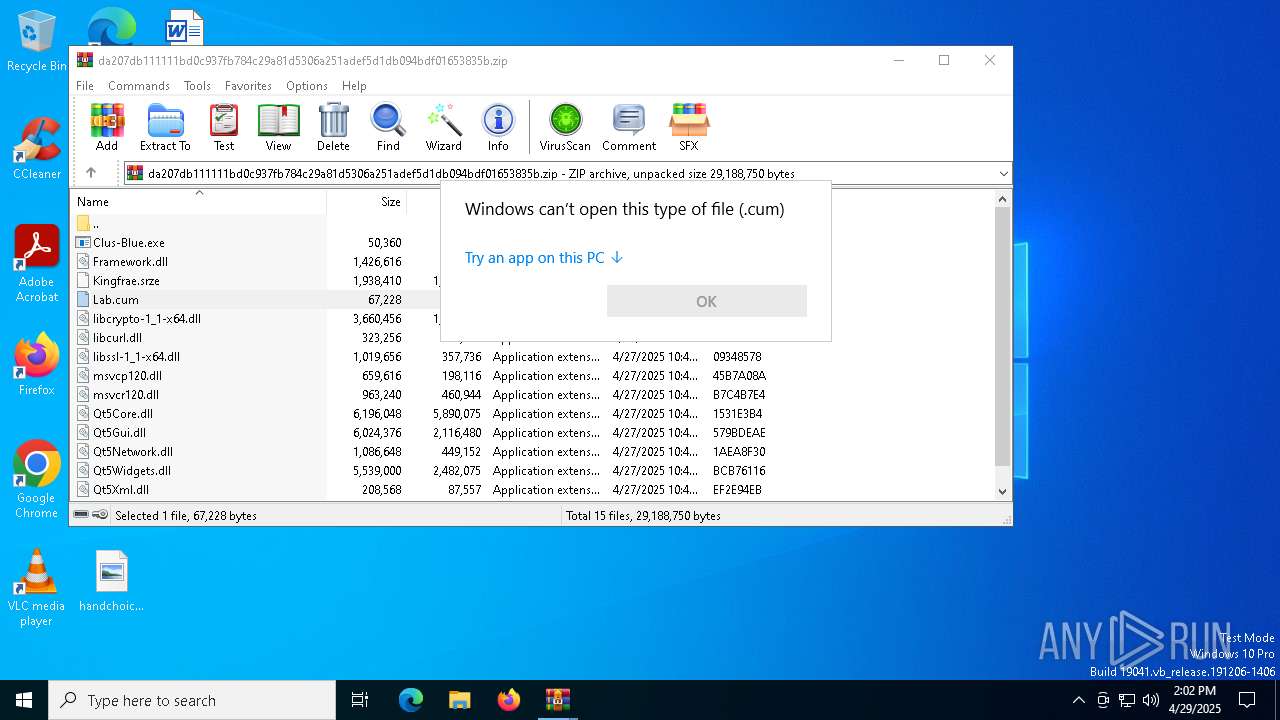
- OpenWith.exe (PID: 2096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:04:29 14:01:22 |
| ZipCRC: | 0x7dbacfc1 |
| ZipCompressedSize: | 16175429 |
| ZipUncompressedSize: | 16212933 |
| ZipFileName: | da207db111111bd0c937fb784c29a81d5306a251adef5d1db094bdf01653835b.zip |
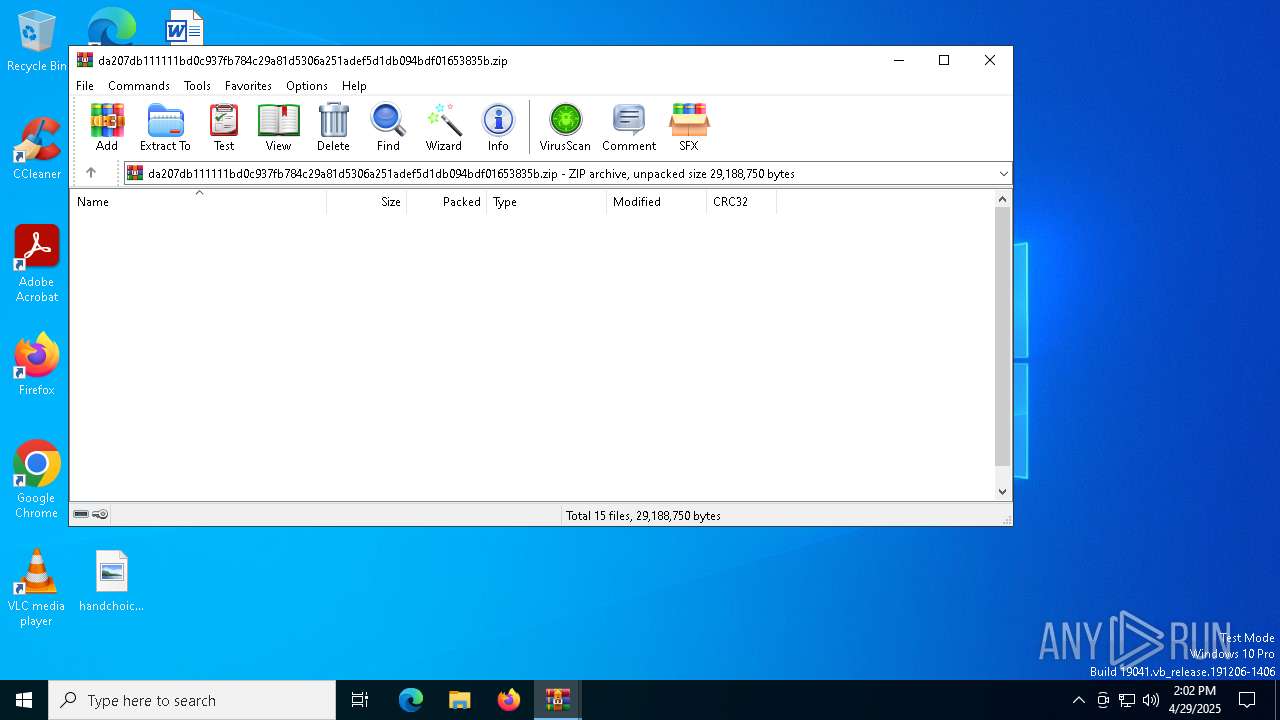
Total processes
143
Monitored processes
11
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
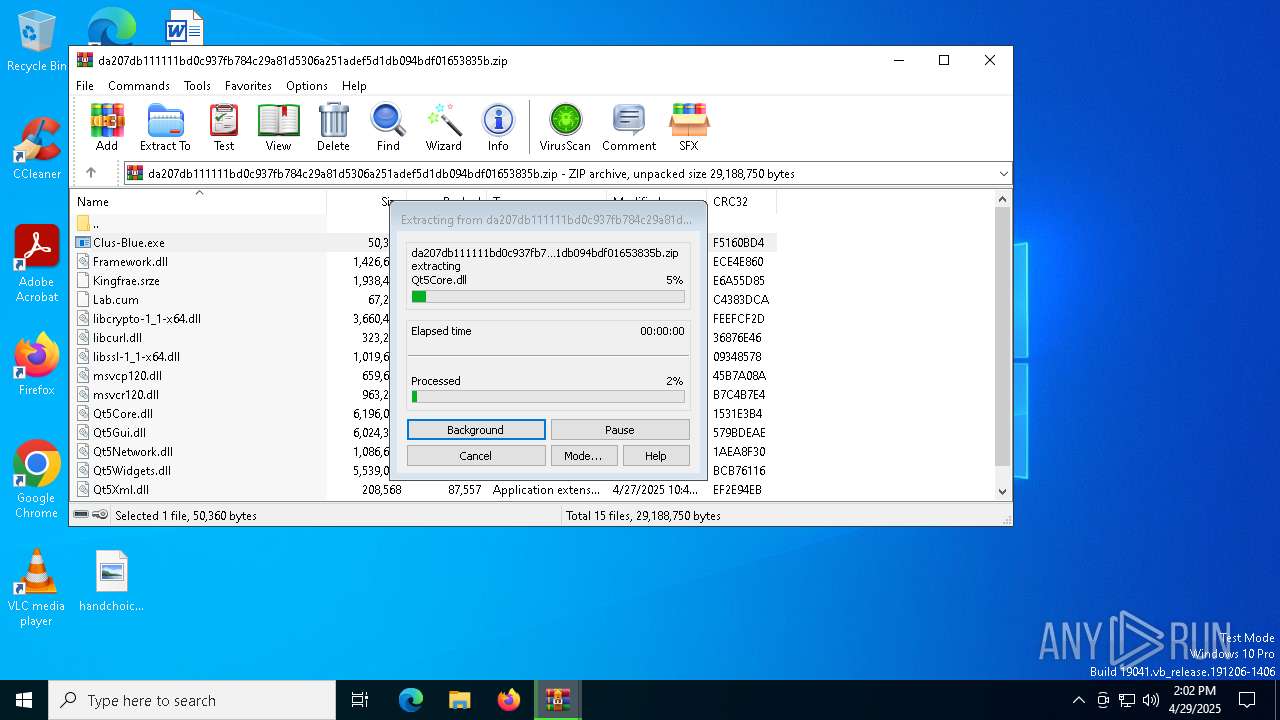
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2096 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2236 | C:\Users\admin\AppData\Local\Temp\47165984\ping.com | C:\Users\admin\AppData\Local\Temp\47165984\ping.com | — | Clus-Blue.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 2772 | C:\ProgramData\Fidl\Clus-Blue.exe | C:\ProgramData\Fidl\Clus-Blue.exe | Clus-Blue.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 5384 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa7692.15658\Clus-Blue.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa7692.15658\Clus-Blue.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 5756 | "C:\ProgramData\Fidl\360Tray.exe" "C:\ProgramData\Fidl\360Tray.exe" /onui | C:\ProgramData\Fidl\360Tray.exe | — | Clus-Blue.exe | |||||||||||
User: admin Company: 360.cn Integrity Level: MEDIUM Description: 360安全卫士 安全防护中心模块 Exit code: 0 Version: 12, 0, 0, 1761 Modules
| |||||||||||||||
| 6272 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7208 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
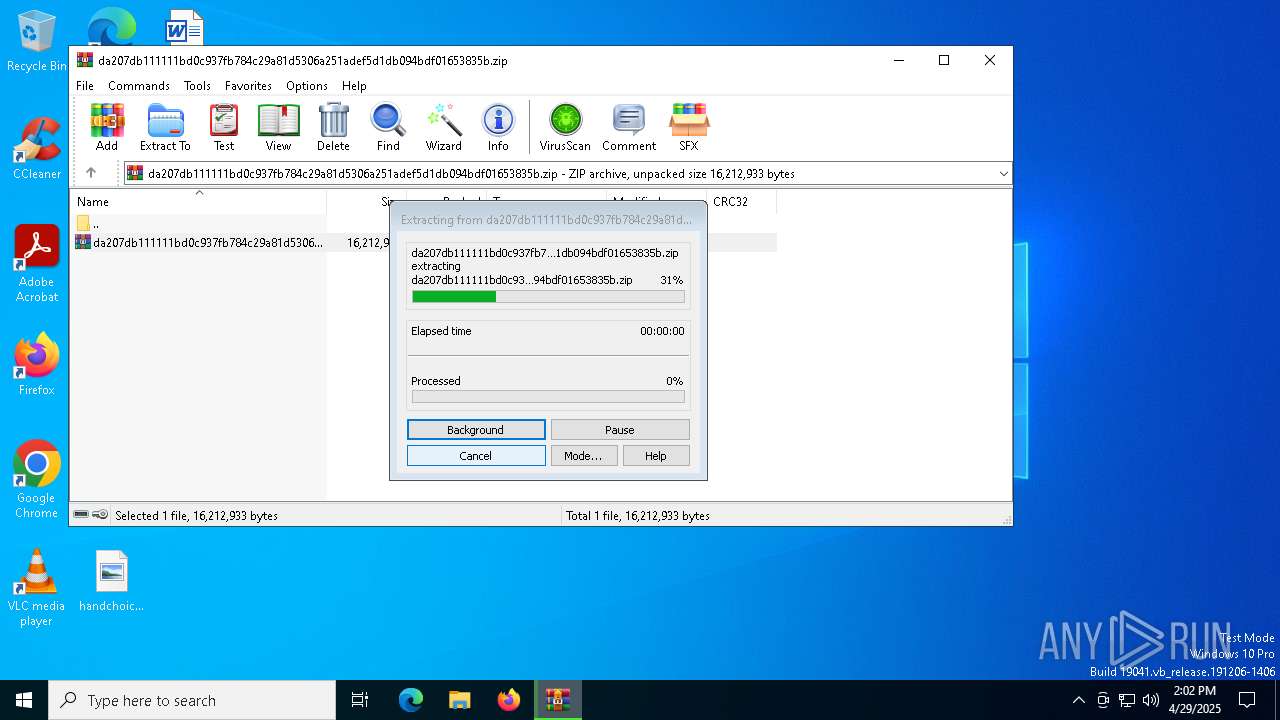
| 7408 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\da207db111111bd0c937fb784c29a81d5306a251adef5d1db094bdf01653835b.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7420 | C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\SysWOW64\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7572 | "C:\ProgramData\Fidl\Clus-Blue.exe" | C:\ProgramData\Fidl\Clus-Blue.exe | dllhost.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
Total events
5 852
Read events
5 834
Write events
18
Delete events
0
Modification events
| (PID) Process: | (7408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\da207db111111bd0c937fb784c29a81d5306a251adef5d1db094bdf01653835b.zip | |||
| (PID) Process: | (7408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (7692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
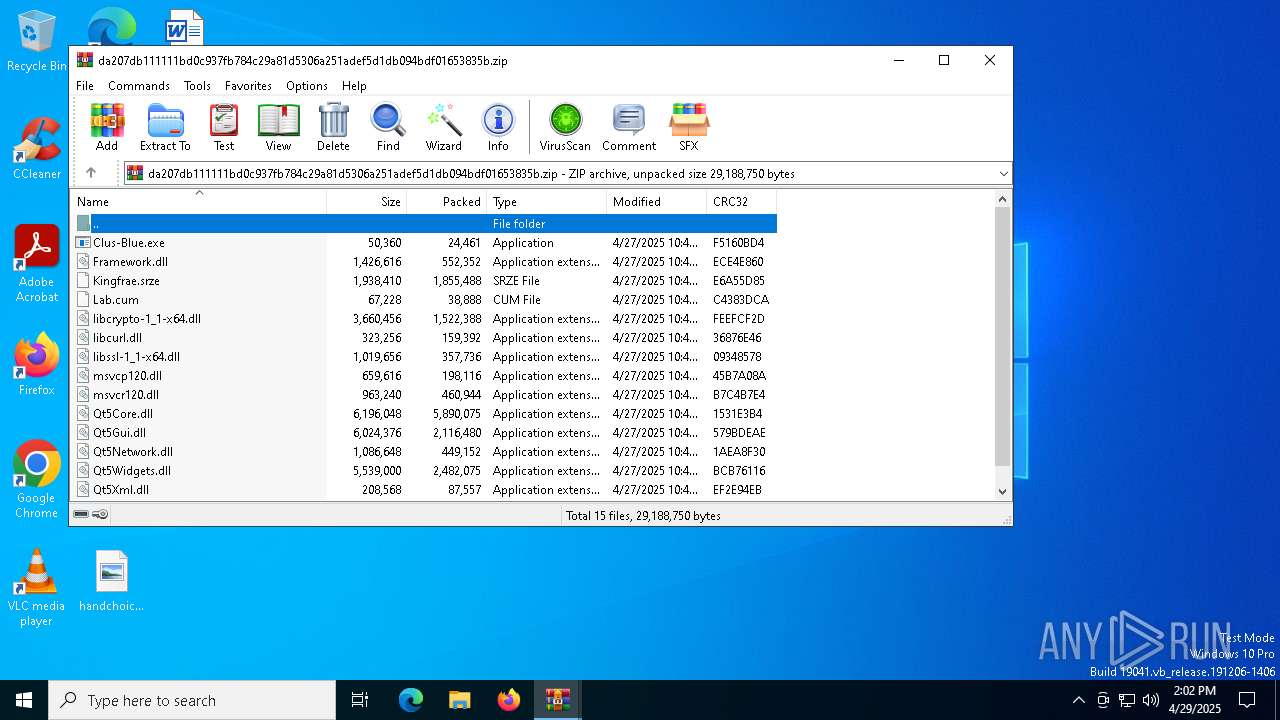
Executable files
28
Suspicious files
11
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7408 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb7408.14071\da207db111111bd0c937fb784c29a81d5306a251adef5d1db094bdf01653835b.zip | compressed | |
MD5:0C3F83B455AAFD1FA11B4FB436B36393 | SHA256:DA207DB111111BD0C937FB784C29A81D5306A251ADEF5D1DB094BDF01653835B | |||
| 7692 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7692.15658\msvcr120.dll | executable | |
MD5:AEB29CCC27E16C4FD223A00189B44524 | SHA256:D28C7AB34842B6149609BD4E6B566DDAB8B891F0D5062480A253EF20A6A2CAAA | |||
| 7692 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7692.15658\Qt5Gui.dll | executable | |
MD5:72AC63E9E9F015D6471DDE58297A4FC6 | SHA256:6B8A49B6B37D69213762C8F2C8A9970014364F4055F08A850D27C0343FBE00DE | |||
| 7692 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7692.15658\Qt5Core.dll | executable | |
MD5:5AF1A8D3E720C2ECD7C835510429DA9F | SHA256:45A830C44F93ABA5658E5E9697DE42B3F3EB383BBBF174ADE65A78F9A6C7D8B2 | |||
| 5384 | Clus-Blue.exe | C:\ProgramData\Fidl\Clus-Blue.exe | executable | |
MD5:20BC61AA222AA74059F4D42872A76EB5 | SHA256:B1465F5CE1D0F83EF9B6086C81D8788B50C09BD329374BD3D04DC61807551435 | |||
| 7692 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7692.15658\libssl-1_1-x64.dll | executable | |
MD5:2574E9E3159CD45194EAC2591EADC73A | SHA256:2D7208FAE6767F5F01664448F4EA89C8009F75DB4C20FECDEA508A498A6A1223 | |||
| 7692 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7692.15658\Kingfrae.srze | binary | |
MD5:FA90A001C2F9BDC09DF22B6A8106FEA3 | SHA256:F957352080219828DCBC012B60736C624D7340D6CEEE97AABB5C505B68F3694B | |||
| 7692 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7692.15658\msvcp120.dll | executable | |
MD5:EDEF53778EAAFE476EE523BE5C2AB67F | SHA256:92FAEDD18A29E1BD2DD27A1D805EA5AA3E73B954A625AF45A74F49D49506D20F | |||
| 5384 | Clus-Blue.exe | C:\ProgramData\Fidl\Framework.dll | executable | |
MD5:2207332818329E3CE4E5E020BA1B1F04 | SHA256:C554A0BD610BA0B10D8D92BB588FC86893B59985E4ED9316D340781C482FCAA2 | |||
| 5384 | Clus-Blue.exe | C:\ProgramData\Fidl\Lab.cum | binary | |
MD5:7CB269327E0287F8258AB2A1B4735207 | SHA256:2ABC5BD527D19B41EE95A26DAD8D77E292FC5152A141BCDBF588C5D3433C02D8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
21
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.32.238.34:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
— | — | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
8064 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
8064 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.32.238.34:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6544 | svchost.exe | 40.126.31.67:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
— | — | 172.211.123.250:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | FR | unknown |
5496 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6404 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5304 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |