| URL: | http://rusvesna.su |
| Full analysis: | https://app.any.run/tasks/6402845e-ebfe-4ad2-b9a6-cc27ac7e1753 |
| Verdict: | Malicious activity |
| Analysis date: | February 20, 2019, 07:58:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4123CE7D8B2810FD6A20E4104C79DDBE |
| SHA1: | 927482E2EAE1B2DDFC84F769000D80717D968EF9 |
| SHA256: | 3E573DFF79DE642C902C034996DA41FB0F17B73513AFFA8840E20EE2C2B9F643 |
| SSDEEP: | 3:N1KMcLWQn:CMcz |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 2904)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2904)
Reads settings of System Certificates
- chrome.exe (PID: 2904)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
8
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=932,7358489227563244169,12394431903020360121,131072 --enable-features=PasswordImport --service-pipe-token=19AB4E5C600EE1E38D9CE321EB1B1376 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=19AB4E5C600EE1E38D9CE321EB1B1376 --renderer-client-id=4 --mojo-platform-channel-handle=1896 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=932,7358489227563244169,12394431903020360121,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=96330B2905D25CE00ED86E2FB43D783A --mojo-platform-channel-handle=5024 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2908 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://rusvesna.su | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=932,7358489227563244169,12394431903020360121,131072 --enable-features=PasswordImport --service-pipe-token=8CE6459909630871E402E93051F602F7 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8CE6459909630871E402E93051F602F7 --renderer-client-id=3 --mojo-platform-channel-handle=2156 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=932,7358489227563244169,12394431903020360121,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=8C1103BB4567480E19E2684AE65ABE56 --mojo-platform-channel-handle=4988 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6feb00b0,0x6feb00c0,0x6feb00cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 4012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=932,7358489227563244169,12394431903020360121,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=8593F8F35E58DC355323114D3D5705DE --mojo-platform-channel-handle=1004 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
509
Read events
465
Write events
41
Delete events
3
Modification events
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2872) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2904-13195123128512750 |
Value: 259 | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2904-13195123128512750 |
Value: 259 | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
67
Text files
103
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\aa9fc74b-2fd4-47ce-8f31-42e7cab3b320.tmp | — | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\64284807-8ce7-4435-8672-4b64899e105a.tmp | — | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF1ae4c4.TMP | text | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Thumbnails\LOG.old~RF1ae560.TMP | text | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
520
TCP/UDP connections
321
DNS requests
179
Threats
167
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
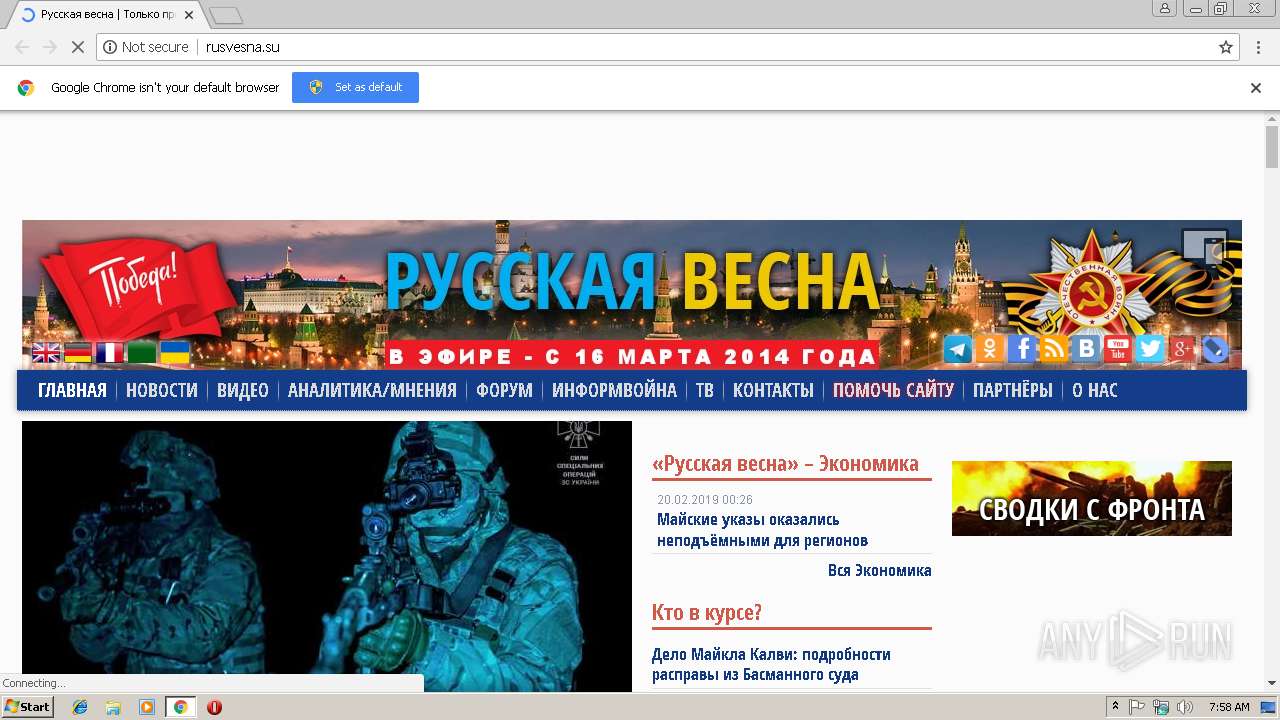
2904 | chrome.exe | GET | 200 | 104.20.92.220:80 | http://rusvesna.su/ | US | html | 28.4 Kb | suspicious |
2904 | chrome.exe | GET | 200 | 104.20.92.220:80 | http://rusvesna.su/sites/default/files/css/css_PifEUBxtWzIwOvj-zUm21ywmptmpv8qj2xd-BMEgHGg.css | US | text | 10.7 Kb | suspicious |
2904 | chrome.exe | GET | 200 | 104.20.92.220:80 | http://rusvesna.su/sites/default/files/js/js_ePK26NQ-wvQETpPMoPNiyVyKuom1YFI6Iu6TglaEwAA.js | US | text | 2.00 Kb | suspicious |
2904 | chrome.exe | GET | 200 | 104.20.92.220:80 | http://rusvesna.su/sites/default/files/js/js_MpKfe1sTh5JIVGCZ17DsAuT1rqAC38MLLlkjqjQ1X_k.js | US | text | 34.0 Kb | suspicious |
2904 | chrome.exe | GET | 200 | 104.20.92.220:80 | http://rusvesna.su/sites/default/files/ar_2.png | US | image | 234 b | suspicious |
2904 | chrome.exe | GET | 200 | 172.217.21.234:80 | http://fonts.googleapis.com/css?family=Open+Sans+Condensed:700&subset=latin,cyrillic-ext | US | text | 564 b | whitelisted |
2904 | chrome.exe | GET | 200 | 104.20.92.220:80 | http://rusvesna.su/sites/all/themes/rspringw/script.js | US | text | 8.73 Kb | suspicious |
2904 | chrome.exe | GET | 200 | 104.20.92.220:80 | http://rusvesna.su/sites/default/files/header-004.jpg?123 | US | image | 100 Kb | suspicious |
2904 | chrome.exe | GET | 200 | 104.20.92.220:80 | http://rusvesna.su/sites/default/files/fr.png | US | image | 542 b | suspicious |
2904 | chrome.exe | GET | 200 | 104.20.92.220:80 | http://rusvesna.su/sites/default/files/css/css_xE-rWrJf-fncB6ztZfd2huxqgxu4WO-qwma6Xer30m4.css | US | text | 2.13 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2904 | chrome.exe | 172.217.22.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2904 | chrome.exe | 216.58.207.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2904 | chrome.exe | 87.240.180.136:80 | vk.com | VKontakte Ltd | RU | unknown |
2904 | chrome.exe | 172.217.21.227:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2904 | chrome.exe | 88.212.196.113:80 | mediametrics.ru | United Network LLC | RU | unknown |
2904 | chrome.exe | 109.248.237.51:80 | s.luxupcdna.com | Centre of server systems Ltd | RU | unknown |
2904 | chrome.exe | 109.248.237.37:80 | luxupcdnc.com | Centre of server systems Ltd | RU | unknown |
2904 | chrome.exe | 37.252.172.12:80 | ib.adnxs.com | AppNexus, Inc | — | unknown |
2904 | chrome.exe | 213.180.204.90:80 | an.yandex.ru | YANDEX LLC | RU | whitelisted |
2904 | chrome.exe | 185.86.139.59:80 | prg.smartadserver.com | SmartAdServer SAS | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
rusvesna.su |
| suspicious |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
vk.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
mediametrics.ru |
| whitelisted |
s.luxupcdna.com |
| unknown |
s.luxupcdnc.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1064 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
2904 | chrome.exe | A Network Trojan was detected | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
2904 | chrome.exe | A Network Trojan was detected | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
2904 | chrome.exe | A Network Trojan was detected | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
2904 | chrome.exe | A Network Trojan was detected | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
2904 | chrome.exe | A Network Trojan was detected | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
2904 | chrome.exe | A Network Trojan was detected | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
2904 | chrome.exe | A Network Trojan was detected | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
2904 | chrome.exe | A Network Trojan was detected | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
2904 | chrome.exe | A Network Trojan was detected | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |