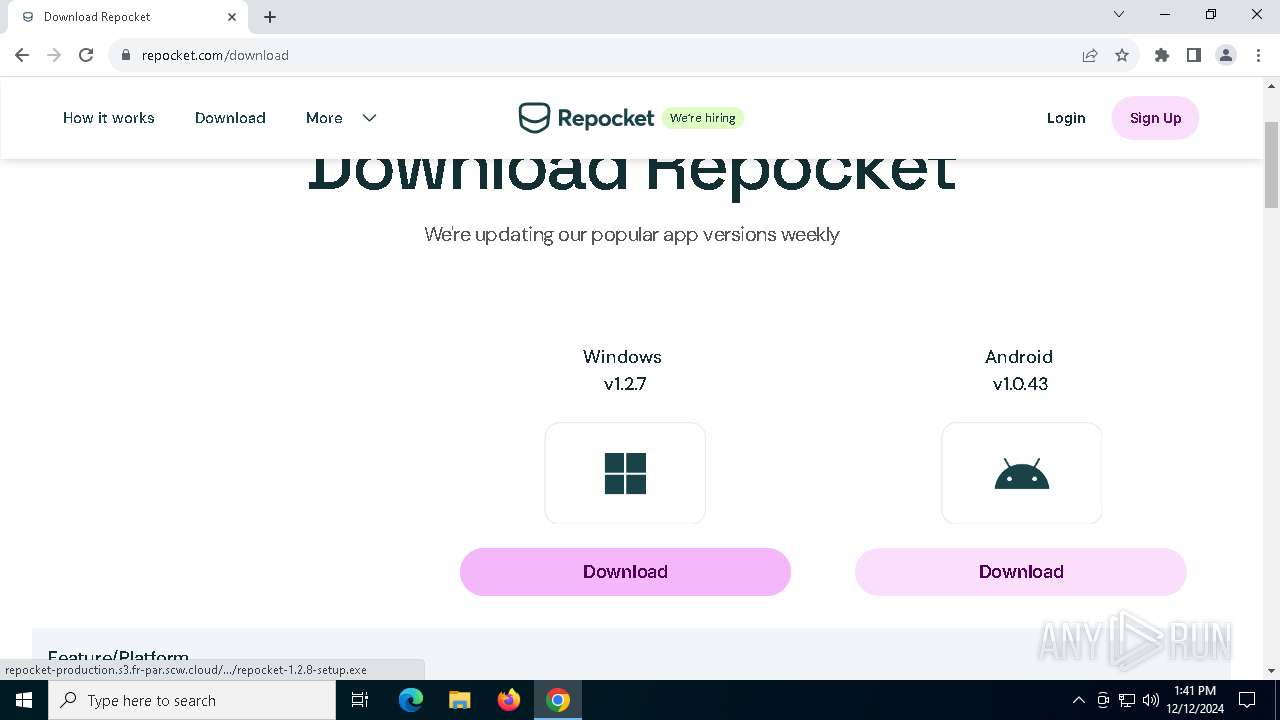
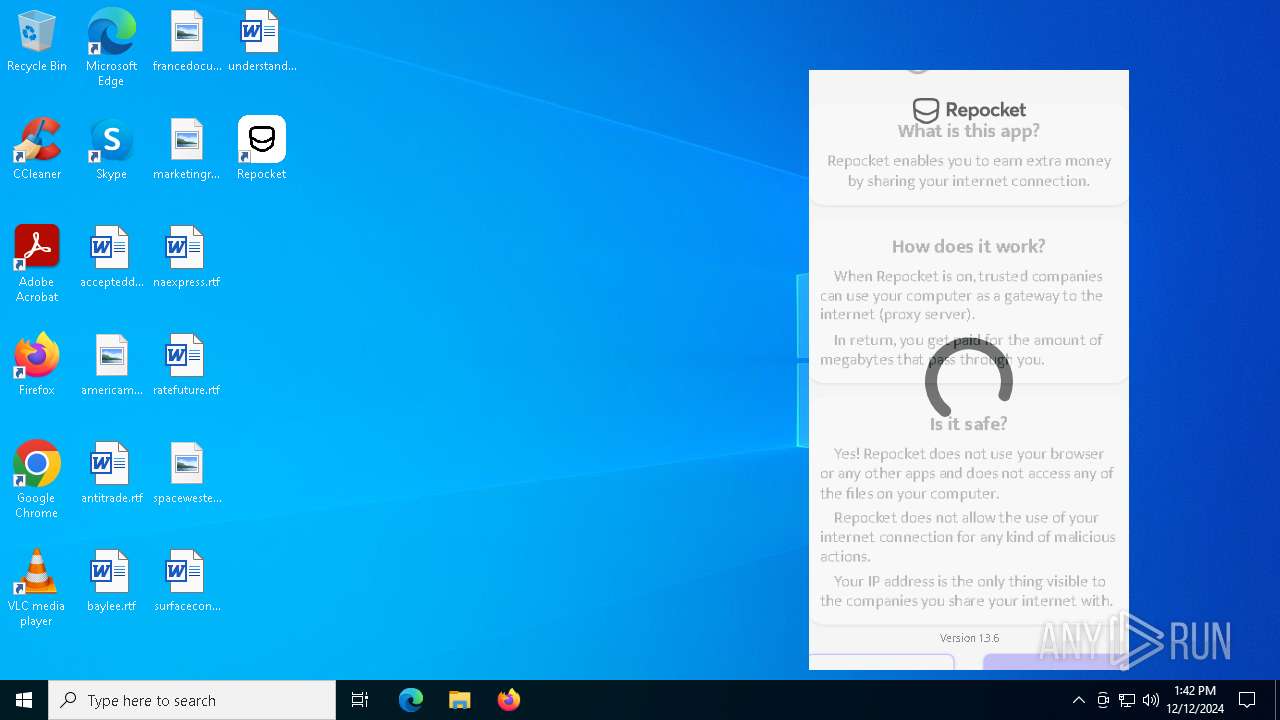
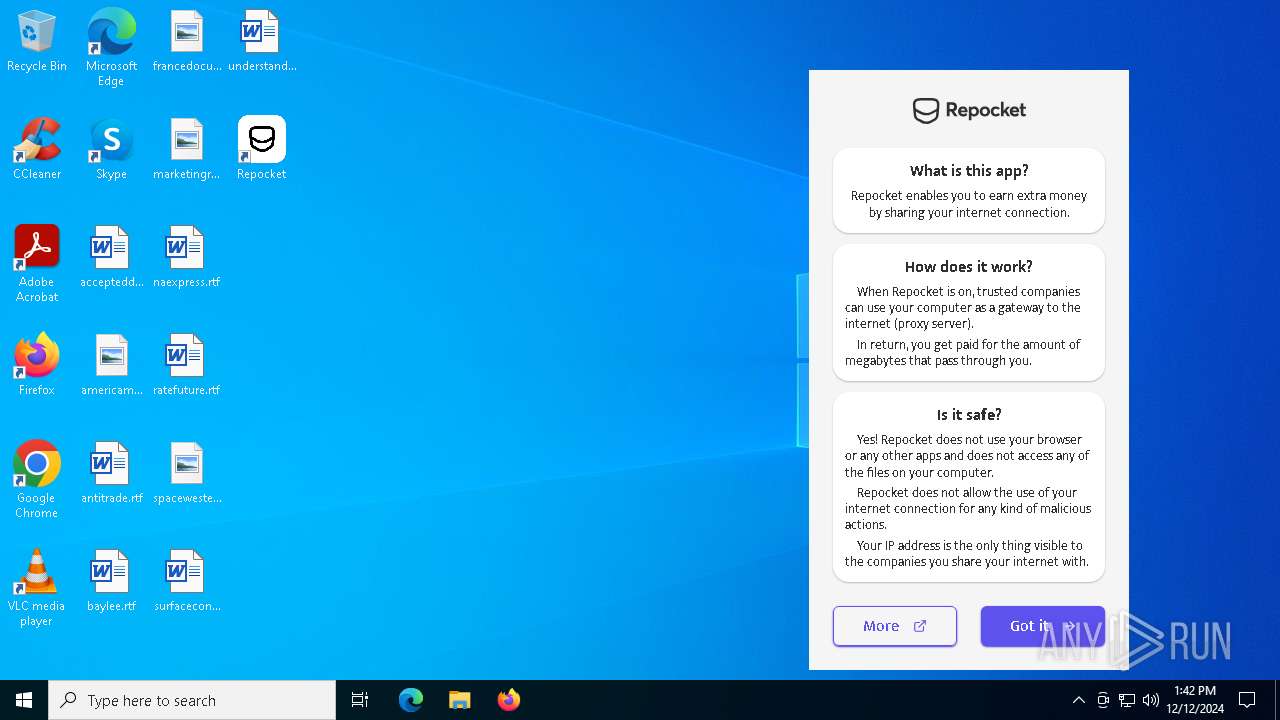
| URL: | https://repocket.com/how-it-works |
| Full analysis: | https://app.any.run/tasks/9e179a26-46c9-48d3-be91-7bec2e39e937 |
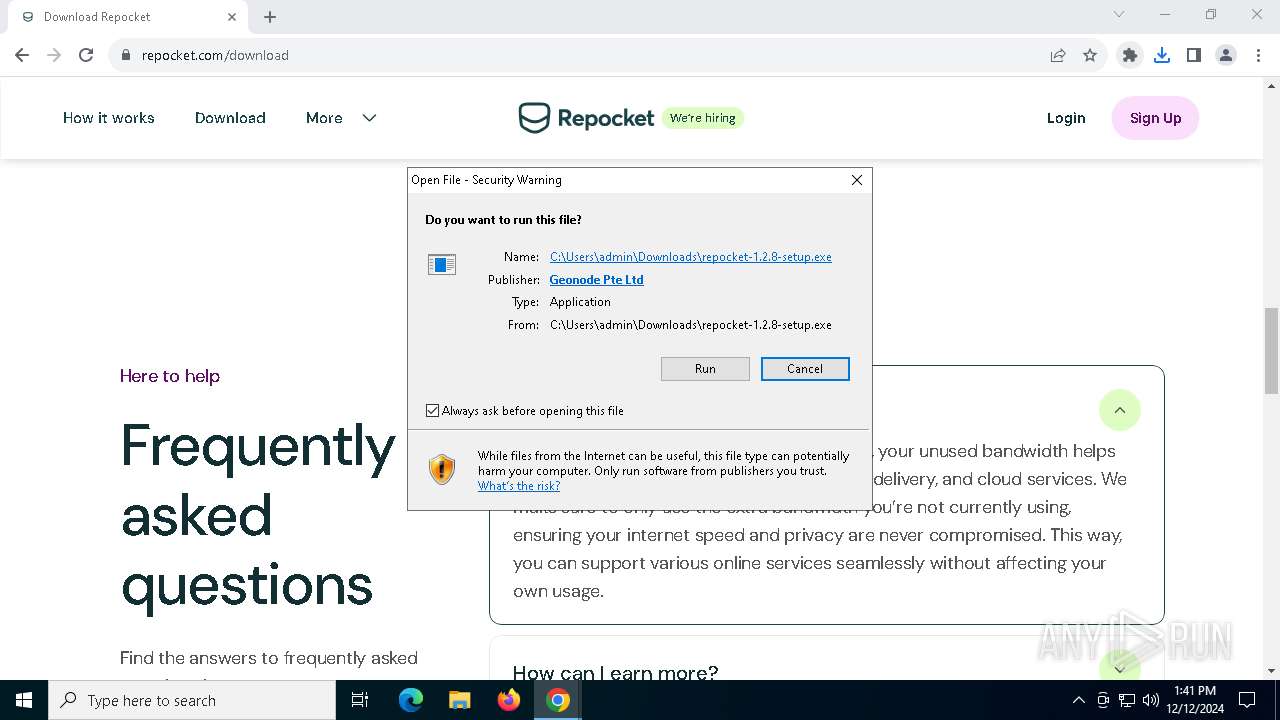
| Verdict: | Malicious activity |
| Analysis date: | December 12, 2024, 13:40:17 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | EB3EB8C14B66087D7DFBE90F46F037BB |
| SHA1: | E555DA54D47B2798C1A75B13BE89683968810FAF |
| SHA256: | 3E2BEEA839D00A5826B183514879271CAD5035500C6CF16519CD9009E6B37D5E |
| SSDEEP: | 3:N8LVKoIIJ:2BKobJ |
MALICIOUS
No malicious indicators.SUSPICIOUS
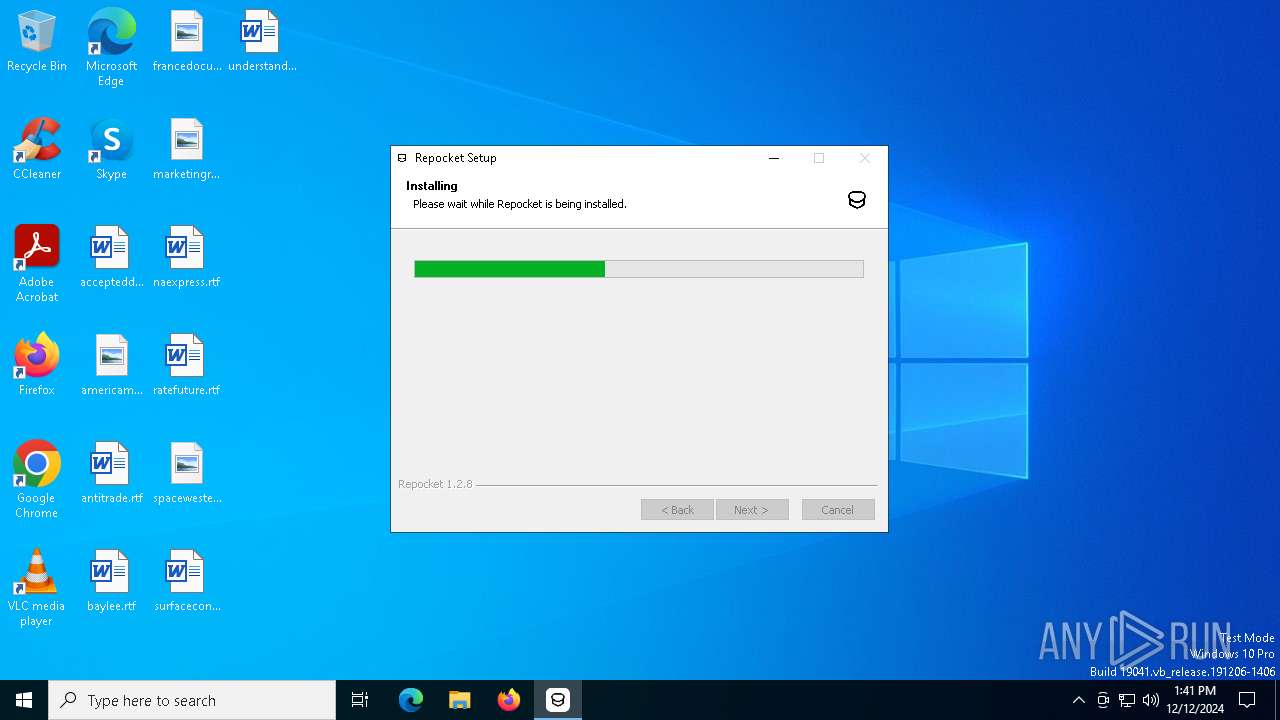
Malware-specific behavior (creating "System.dll" in Temp)
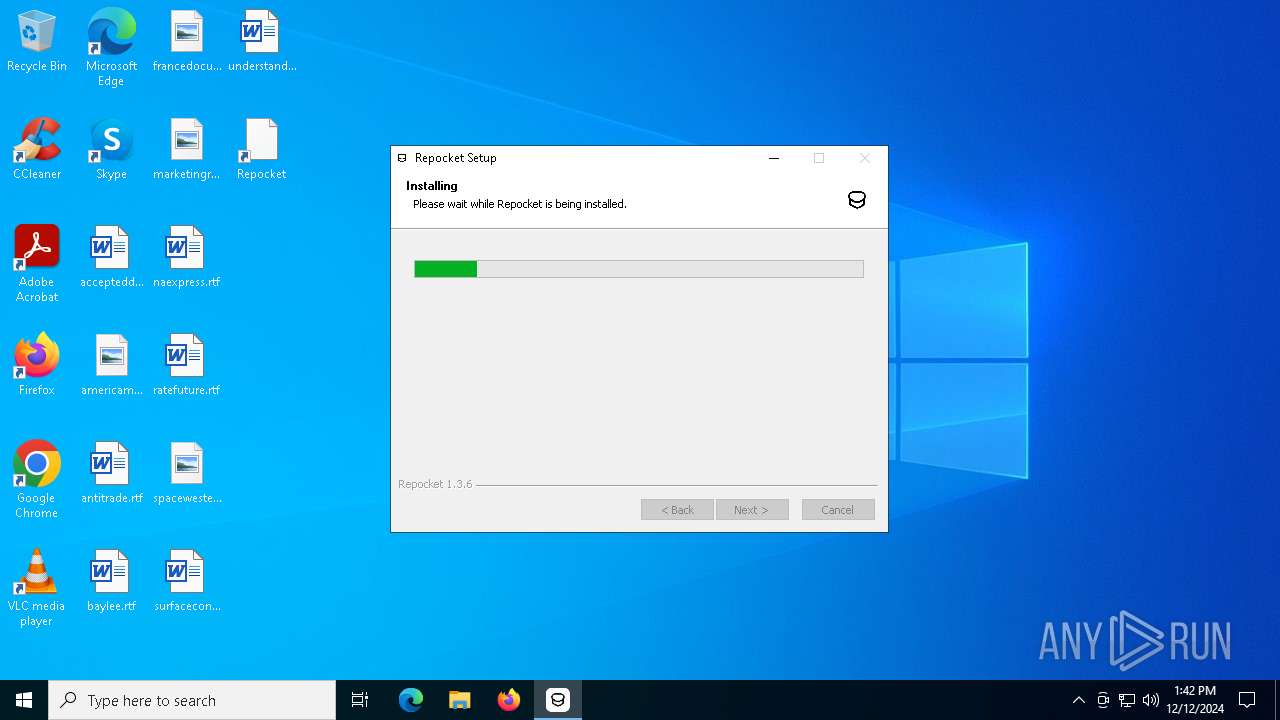
- repocket-1.2.8-setup.exe (PID: 5588)
- repocket-1.3.6-setup.exe (PID: 644)
- old-uninstaller.exe (PID: 6768)
Executable content was dropped or overwritten
- repocket-1.2.8-setup.exe (PID: 5588)
- repocket-1.3.6-setup.exe (PID: 644)
- old-uninstaller.exe (PID: 6768)
The process creates files with name similar to system file names
- repocket-1.2.8-setup.exe (PID: 5588)
Get information on the list of running processes
- repocket-1.2.8-setup.exe (PID: 5588)
- cmd.exe (PID: 7092)
- repocket-1.3.6-setup.exe (PID: 644)
- cmd.exe (PID: 3632)
- old-uninstaller.exe (PID: 6768)
- cmd.exe (PID: 6640)
Starts CMD.EXE for commands execution
- repocket-1.2.8-setup.exe (PID: 5588)
- repocket.exe (PID: 7100)
- repocket-1.3.6-setup.exe (PID: 644)
- old-uninstaller.exe (PID: 6768)
- repocket.exe (PID: 6404)
Drops 7-zip archiver for unpacking
- repocket-1.2.8-setup.exe (PID: 5588)
- repocket-1.3.6-setup.exe (PID: 644)
Process drops legitimate windows executable
- repocket-1.2.8-setup.exe (PID: 5588)
- old-uninstaller.exe (PID: 6768)
- repocket-1.3.6-setup.exe (PID: 644)
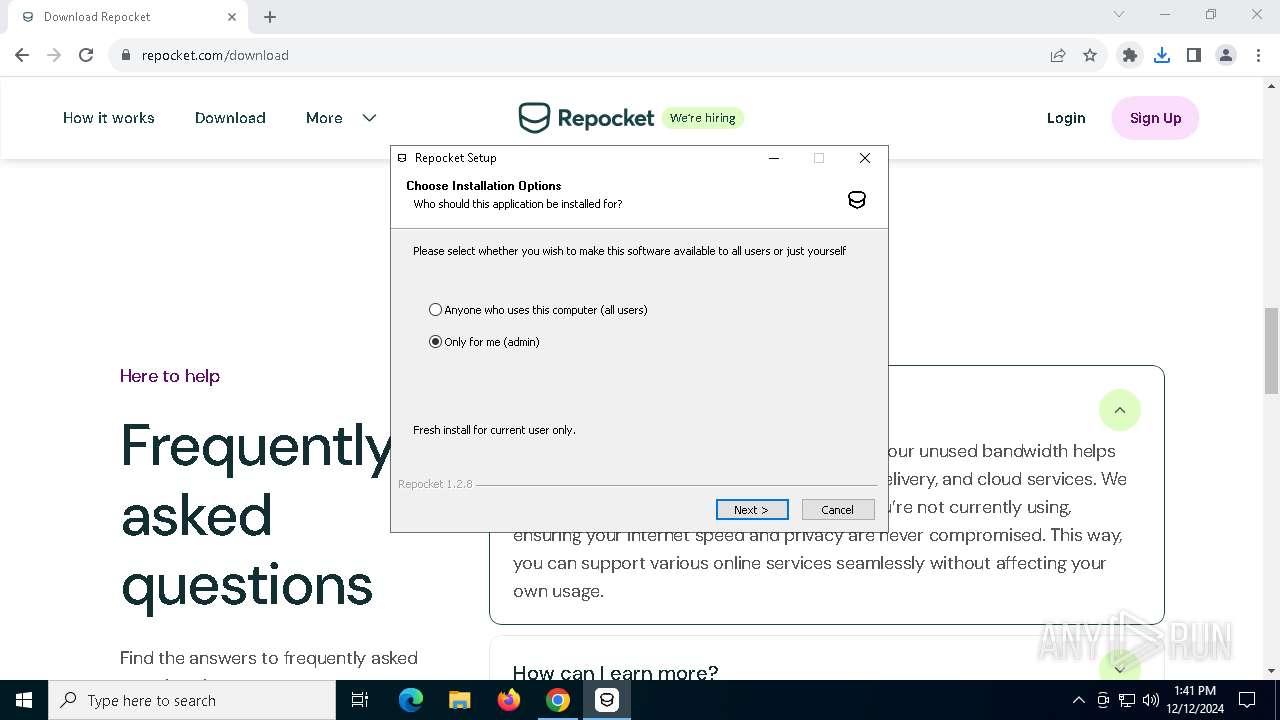
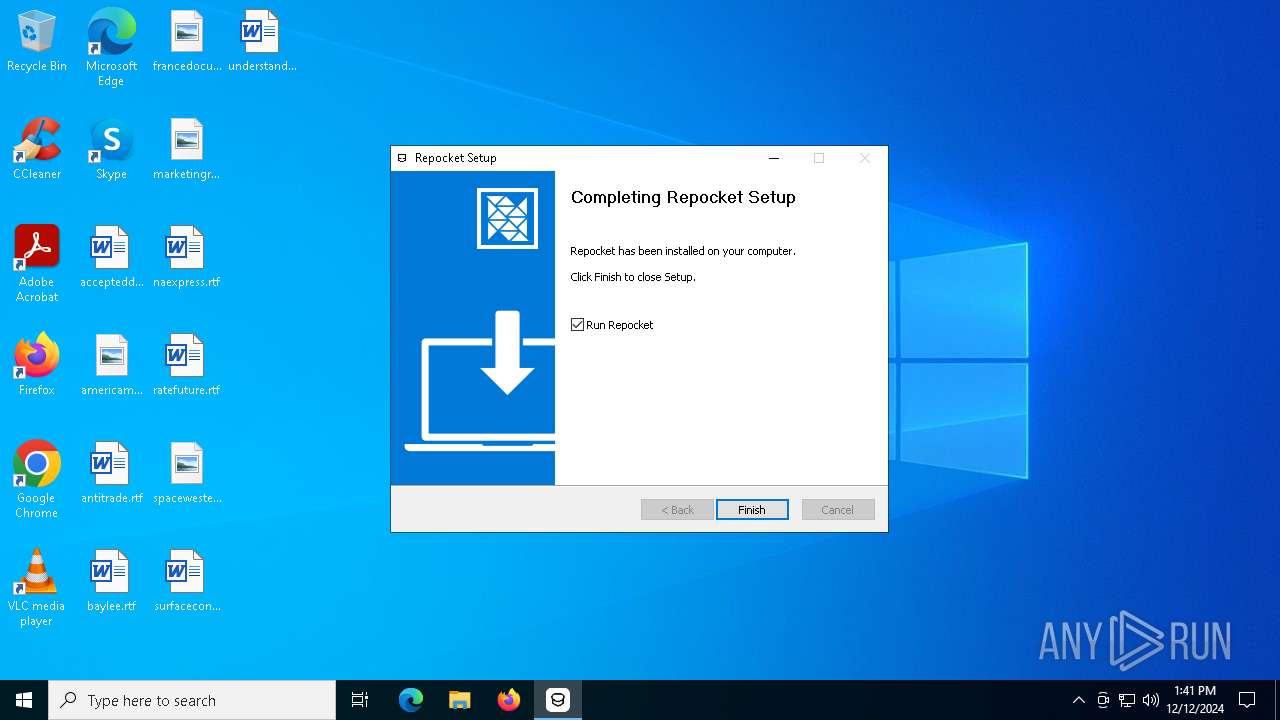
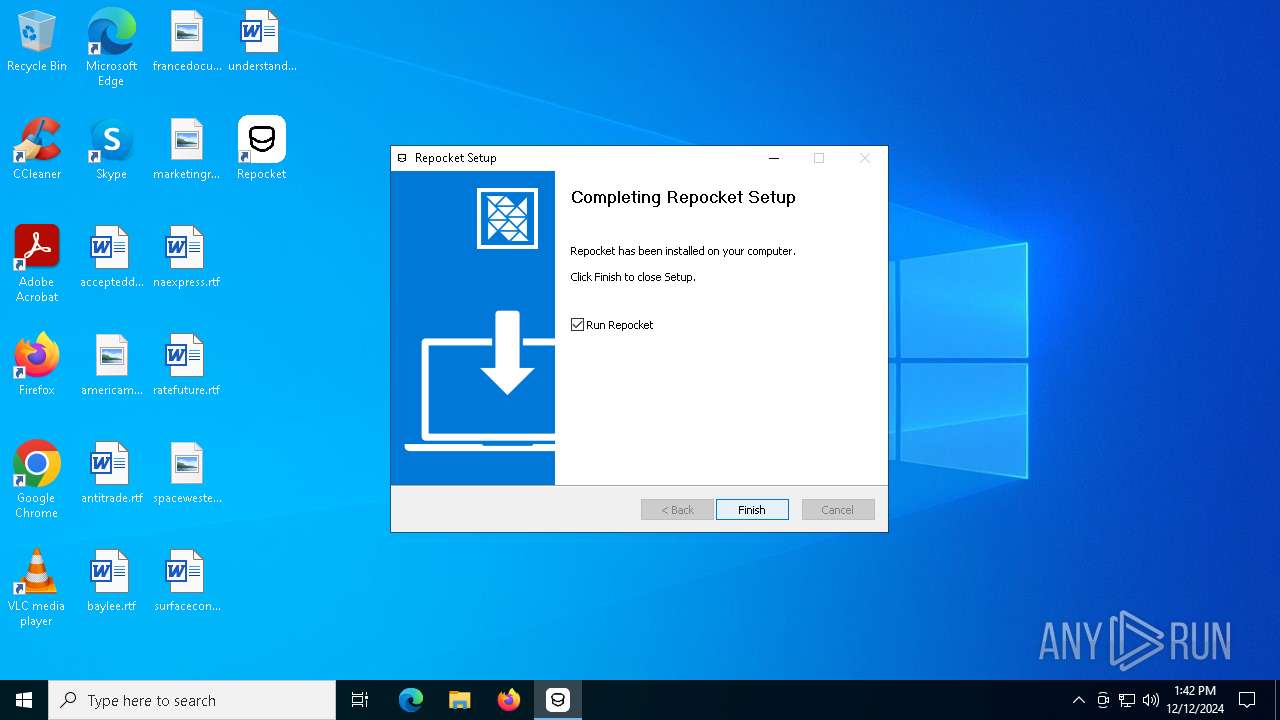
Creates a software uninstall entry
- repocket-1.2.8-setup.exe (PID: 5588)
- repocket-1.3.6-setup.exe (PID: 644)
Reads security settings of Internet Explorer
- repocket-1.2.8-setup.exe (PID: 5588)
- repocket-1.3.6-setup.exe (PID: 644)
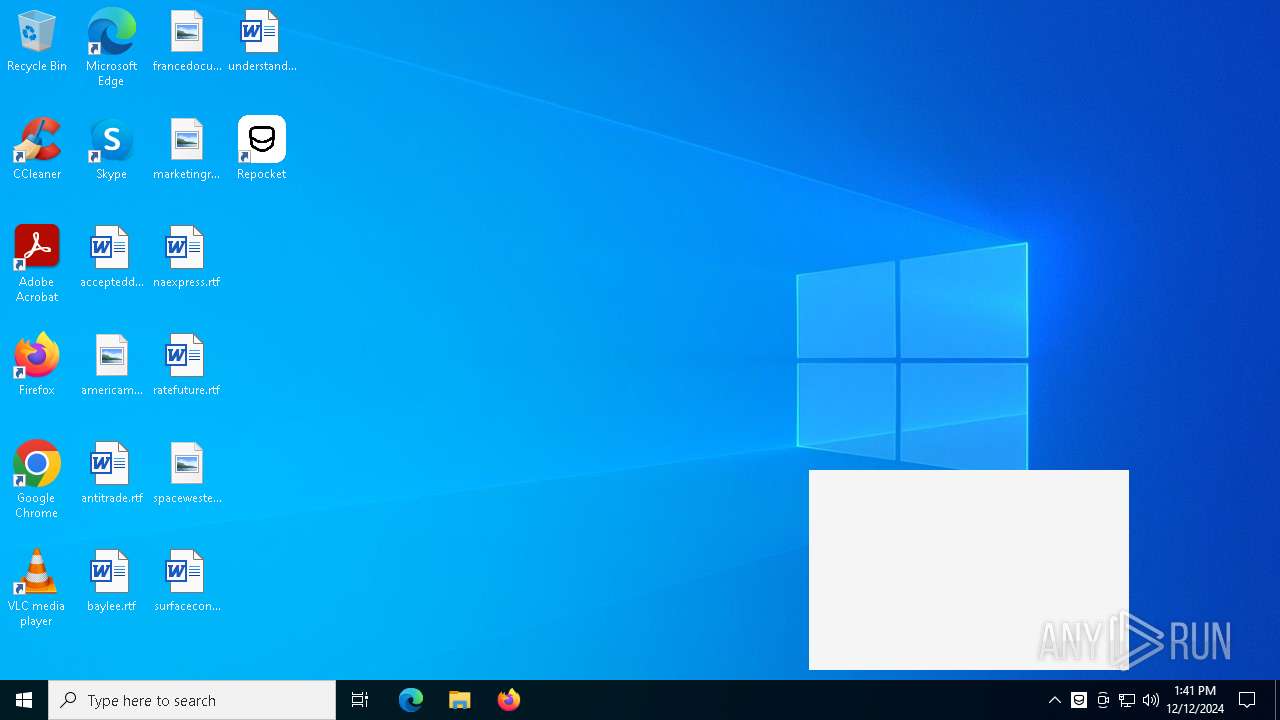
Application launched itself
- repocket.exe (PID: 7100)
- repocket.exe (PID: 6404)
Hides command output
- cmd.exe (PID: 2976)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2976)
Starts application with an unusual extension
- cmd.exe (PID: 2976)
- cmd.exe (PID: 6484)
The process hide an interactive prompt from the user
- cmd.exe (PID: 2976)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 2976)
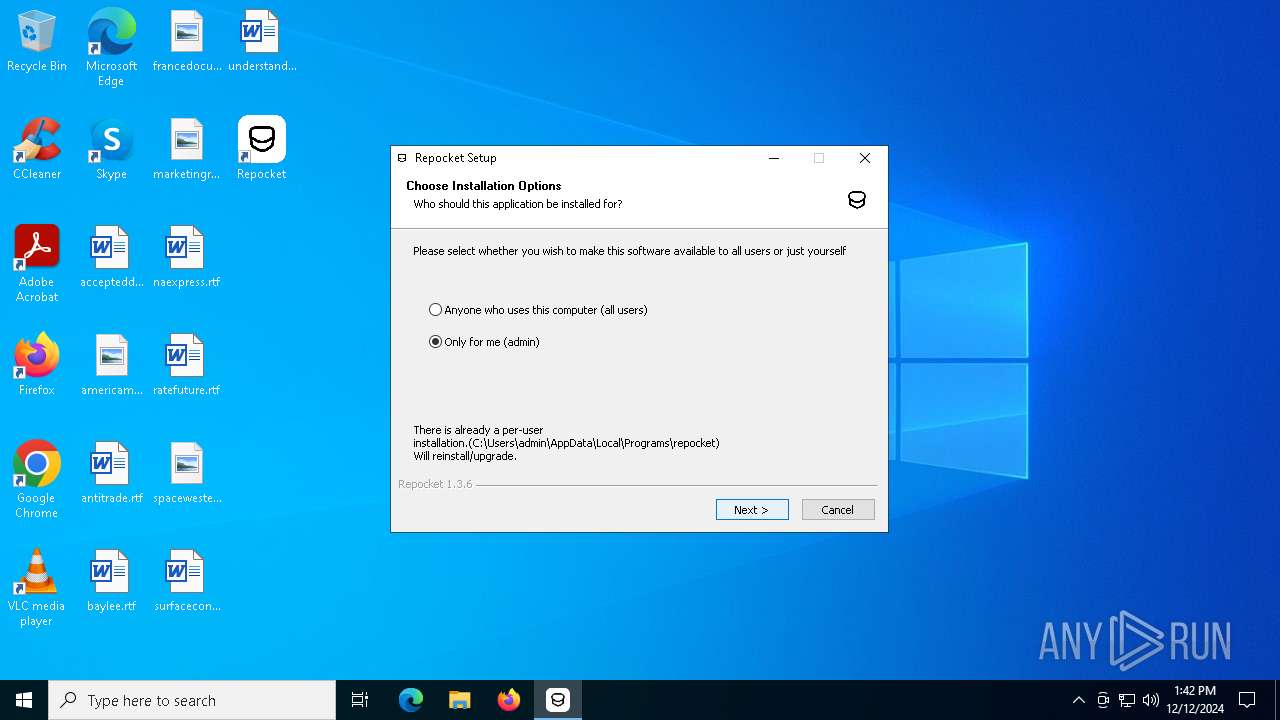
Searches for installed software
- repocket-1.3.6-setup.exe (PID: 644)
INFO
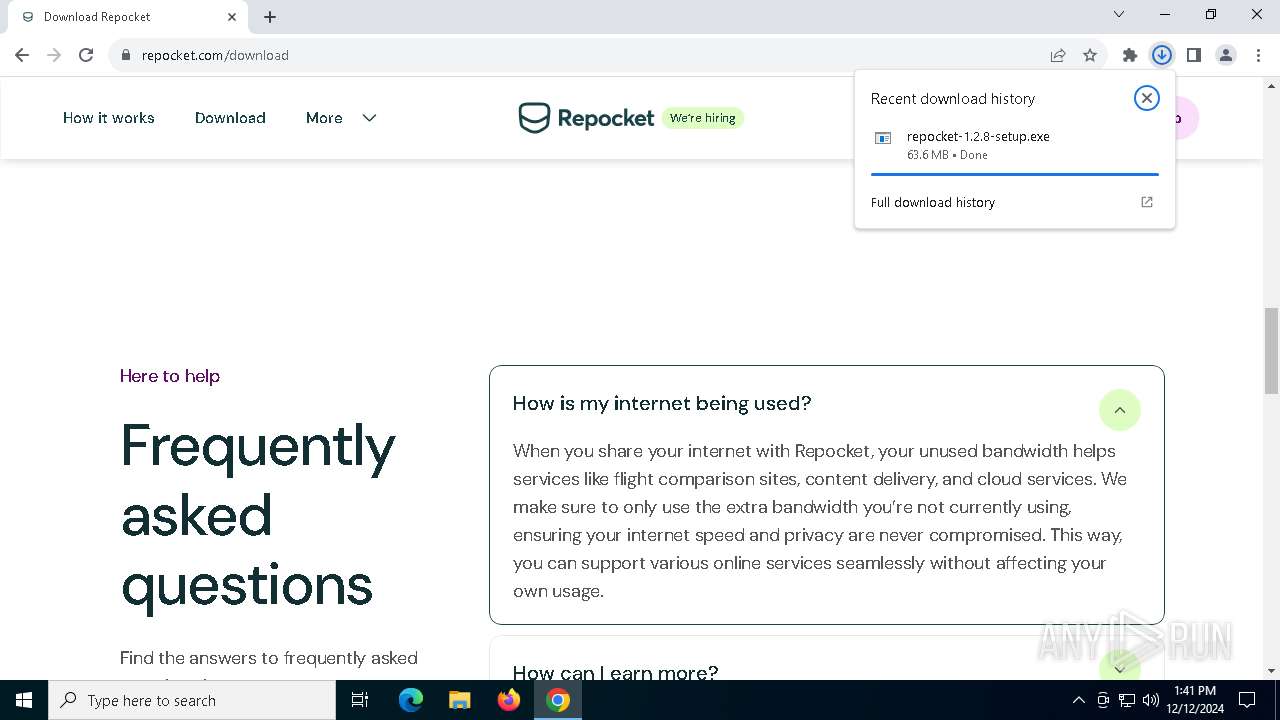
The process uses the downloaded file
- chrome.exe (PID: 4668)
- repocket-1.2.8-setup.exe (PID: 5588)
- powershell.exe (PID: 4132)
Executable content was dropped or overwritten
- chrome.exe (PID: 4668)
The sample compiled with english language support
- repocket-1.2.8-setup.exe (PID: 5588)
- repocket-1.3.6-setup.exe (PID: 644)
- old-uninstaller.exe (PID: 6768)
Checks supported languages
- repocket-1.2.8-setup.exe (PID: 5588)
- repocket.exe (PID: 1192)
- repocket.exe (PID: 7100)
- repocket.exe (PID: 2512)
- old-uninstaller.exe (PID: 6768)
- repocket.exe (PID: 6368)
- chcp.com (PID: 3724)
- repocket.exe (PID: 6404)
- repocket.exe (PID: 6252)
- repocket.exe (PID: 2092)
- repocket.exe (PID: 6832)
Reads the computer name
- repocket-1.2.8-setup.exe (PID: 5588)
- repocket.exe (PID: 1192)
- repocket.exe (PID: 432)
- repocket-1.3.6-setup.exe (PID: 644)
- repocket.exe (PID: 6368)
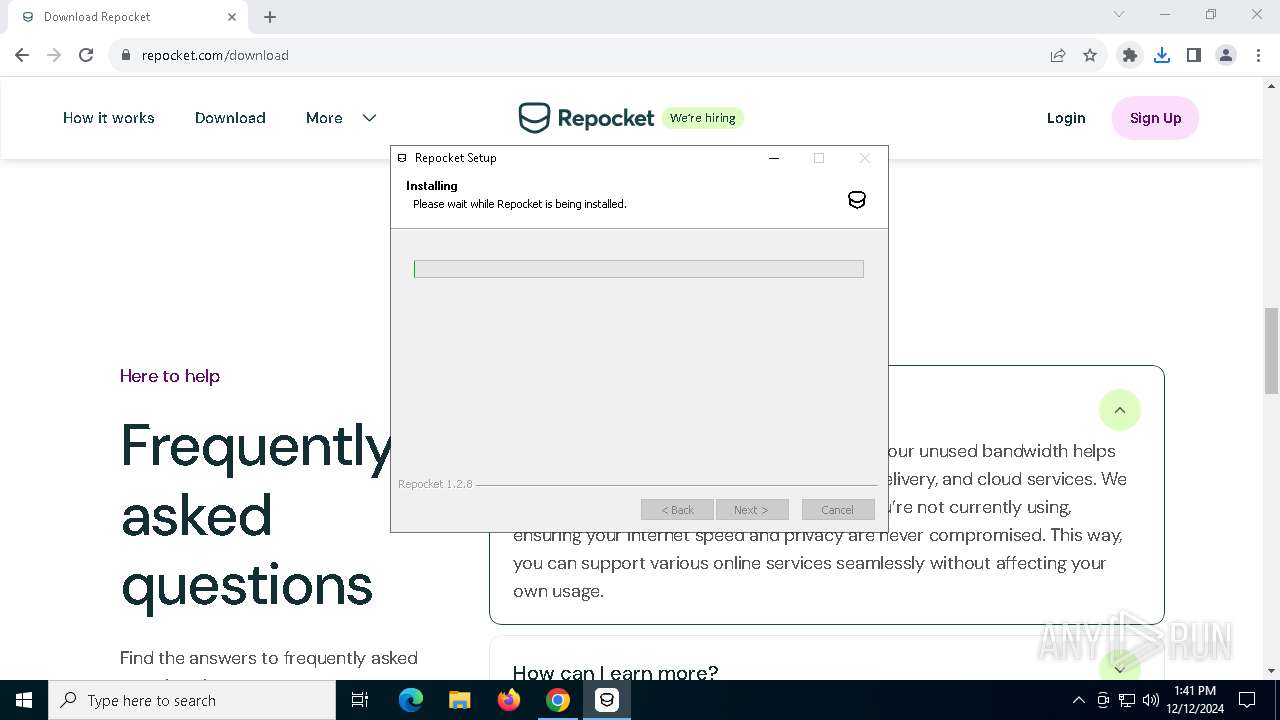
Create files in a temporary directory
- repocket-1.2.8-setup.exe (PID: 5588)
- repocket-1.3.6-setup.exe (PID: 644)
- old-uninstaller.exe (PID: 6768)
Application launched itself
- chrome.exe (PID: 4668)
Creates files or folders in the user directory
- repocket-1.2.8-setup.exe (PID: 5588)
- repocket.exe (PID: 7100)
- repocket.exe (PID: 1192)
- repocket-1.3.6-setup.exe (PID: 644)
- repocket.exe (PID: 6404)
Manual execution by a user
- repocket.exe (PID: 7100)
- repocket.exe (PID: 6404)
Checks proxy server information
- repocket.exe (PID: 7100)
- repocket.exe (PID: 6404)
Reads the machine GUID from the registry
- repocket.exe (PID: 7100)
Changes the display of characters in the console
- cmd.exe (PID: 2976)
- cmd.exe (PID: 6484)
Process checks computer location settings
- repocket.exe (PID: 2512)
- repocket.exe (PID: 6404)
- repocket.exe (PID: 2092)
Node.js compiler has been detected
- repocket.exe (PID: 432)
- repocket.exe (PID: 7100)
- repocket.exe (PID: 1192)
- repocket.exe (PID: 6404)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
180
Monitored processes
43
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 420 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 420 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 432 | "C:\Users\admin\AppData\Local\Programs\repocket\repocket.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Roaming\repocket" --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1796 --field-trial-handle=1788,i,5508416029494541316,9324610347855034727,262144 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:2 | C:\Users\admin\AppData\Local\Programs\repocket\repocket.exe | — | repocket.exe | |||||||||||
User: admin Company: Geonode Pte Ltd Integrity Level: LOW Description: Repocket Exit code: 0 Version: 1.2.8 Modules
| |||||||||||||||
| 640 | C:\WINDOWS\System32\find.exe "repocket.exe" | C:\Windows\SysWOW64\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | C:\Users\admin\AppData\Local\repocket-updater\pending\repocket-1.3.6-setup.exe --updated --force-run | C:\Users\admin\AppData\Local\repocket-updater\pending\repocket-1.3.6-setup.exe | repocket.exe | ||||||||||||
User: admin Company: Geonode Pte Ltd Integrity Level: MEDIUM Description: Earn money by sharing your internet Exit code: 0 Version: 1.3.6 Modules
| |||||||||||||||
| 1192 | "C:\Users\admin\AppData\Local\Programs\repocket\repocket.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --user-data-dir="C:\Users\admin\AppData\Roaming\repocket" --mojo-platform-channel-handle=2100 --field-trial-handle=1788,i,5508416029494541316,9324610347855034727,262144 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:8 | C:\Users\admin\AppData\Local\Programs\repocket\repocket.exe | repocket.exe | ||||||||||||
User: admin Company: Geonode Pte Ltd Integrity Level: MEDIUM Description: Repocket Exit code: 0 Version: 1.2.8 Modules
| |||||||||||||||
| 1988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --mojo-platform-channel-handle=5328 --field-trial-handle=2056,i,8972736937586264430,3392285111118568355,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2092 | "C:\Users\admin\AppData\Local\Programs\repocket\repocket.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\repocket" --app-user-model-id=co.repocket.desktop --app-path="C:\Users\admin\AppData\Local\Programs\repocket\resources\app.asar" --no-sandbox --no-zygote --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --mojo-platform-channel-handle=3184 --field-trial-handle=1880,i,1342934390361915579,5593336162538960580,262144 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:1 | C:\Users\admin\AppData\Local\Programs\repocket\repocket.exe | — | repocket.exe | |||||||||||
User: admin Company: Geonode Pte Ltd Integrity Level: MEDIUM Description: Repocket Version: 1.3.6 Modules
| |||||||||||||||
| 2512 | "C:\Users\admin\AppData\Local\Programs\repocket\repocket.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\repocket" --app-user-model-id=co.repocket.desktop --app-path="C:\Users\admin\AppData\Local\Programs\repocket\resources\app.asar" --no-sandbox --no-zygote --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --mojo-platform-channel-handle=3200 --field-trial-handle=1788,i,5508416029494541316,9324610347855034727,262144 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:1 | C:\Users\admin\AppData\Local\Programs\repocket\repocket.exe | — | repocket.exe | |||||||||||
User: admin Company: Geonode Pte Ltd Integrity Level: MEDIUM Description: Repocket Exit code: 0 Version: 1.2.8 Modules
| |||||||||||||||
| 2976 | C:\WINDOWS\system32\cmd.exe /d /s /c "chcp 65001 >NUL & powershell.exe -NoProfile -NonInteractive -InputFormat None -Command "Get-AuthenticodeSignature -LiteralPath 'C:\Users\admin\AppData\Local\repocket-updater\pending\temp-repocket-1.3.6-setup.exe' | ConvertTo-Json -Compress"" | C:\Windows\SysWOW64\cmd.exe | — | repocket.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
17 330
Read events
17 256
Write events
35
Delete events
39
Modification events
| (PID) Process: | (4668) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4668) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4668) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4668) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4668) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (5076) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000DAFD4F879B4CDB01 | |||
| (PID) Process: | (4668) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (4668) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | GoogleChromeAutoLaunch_A822CA3D40D4B8944864CFEA751D8D57 |
Value: | |||
| (PID) Process: | (5588) repocket-1.2.8-setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\11cee988-8d91-53d8-ab0b-897648027146 |
| Operation: | write | Name: | ShortcutName |
Value: Repocket | |||
| (PID) Process: | (5588) repocket-1.2.8-setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\11cee988-8d91-53d8-ab0b-897648027146 |
| Operation: | write | Name: | DisplayName |
Value: Repocket | |||
Executable files
58
Suspicious files
384
Text files
89
Unknown types
44
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF136082.TMP | — | |
MD5:— | SHA256:— | |||
| 4668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF136082.TMP | — | |
MD5:— | SHA256:— | |||
| 4668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF136082.TMP | — | |
MD5:— | SHA256:— | |||
| 4668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF136082.TMP | — | |
MD5:— | SHA256:— | |||
| 4668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF136082.TMP | — | |
MD5:— | SHA256:— | |||
| 4668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
65
DNS requests
57
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 313 b | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
7160 | SIHClient.exe | GET | 200 | 88.221.125.143:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 418 b | whitelisted |
7160 | SIHClient.exe | GET | 200 | 88.221.125.143:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
4668 | chrome.exe | GET | 200 | 18.173.205.76:80 | http://ocsps.ssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQg3SSkKA74hABkhmlBtJTz8w3hlAQU%2BWC71OPVNPa49QaAJadz20ZpqJ4CEEJLalPOx2YUHCpjsaUcQQQ%3D | US | binary | 727 b | whitelisted |
2940 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/mnmfg3uh3qubjayuhjlbbayyfi_9384/hfnkpimlhhgieaddgfemjhofmfblmnib_9384_all_adkdb2kafm7wypedreawal6xxuha.crx3 | US | — | — | whitelisted |
4668 | chrome.exe | GET | 200 | 18.173.205.76:80 | http://ocsps.ssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSoEwb5tith0jIBy9frSyNGB1lsAAQUNr1J%2FzEs669qQP6ZwBbtuvxI3V8CEGtwkNe8gVzD7rgr3kHe9hk%3D | US | binary | 727 b | whitelisted |
6344 | backgroundTaskHost.exe | GET | — | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | — | — | whitelisted |
2940 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/mnmfg3uh3qubjayuhjlbbayyfi_9384/hfnkpimlhhgieaddgfemjhofmfblmnib_9384_all_adkdb2kafm7wypedreawal6xxuha.crx3 | US | binary | 1.09 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.113:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2736 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5064 | SearchApp.exe | 2.23.209.158:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3884 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
repocket.com |
| unknown |
accounts.google.com |
| whitelisted |
framerusercontent.com |
| unknown |