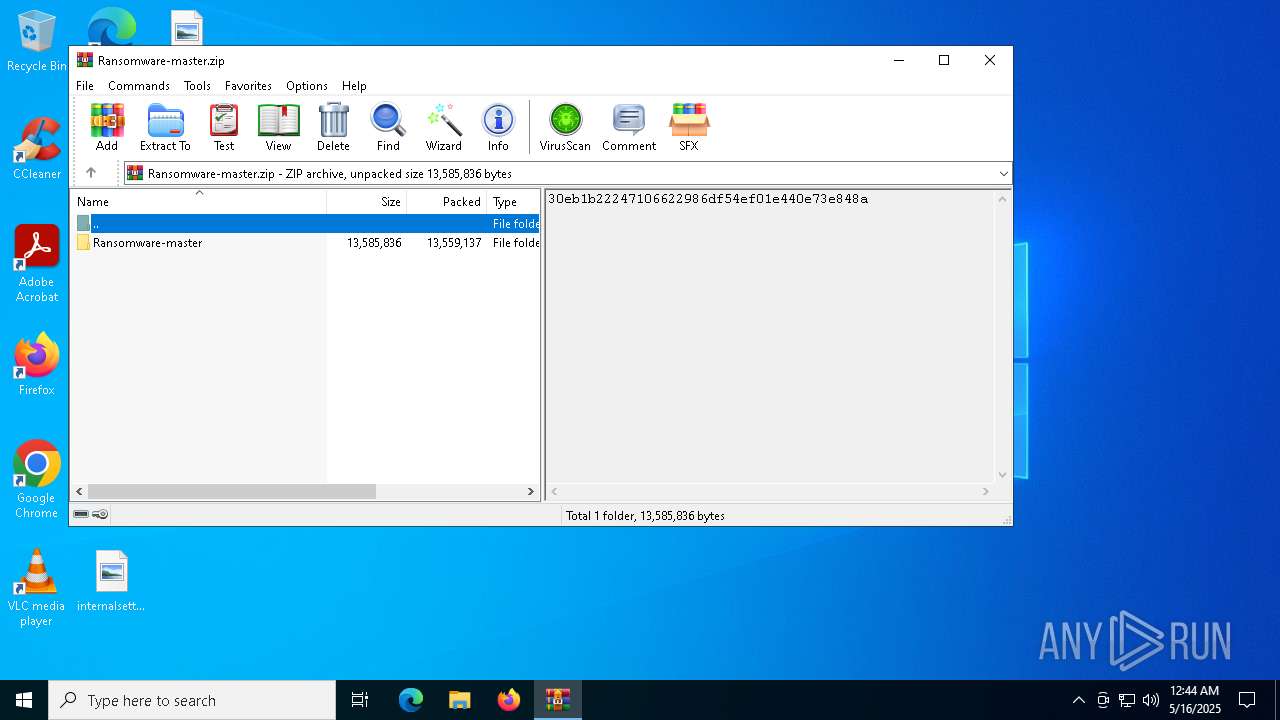
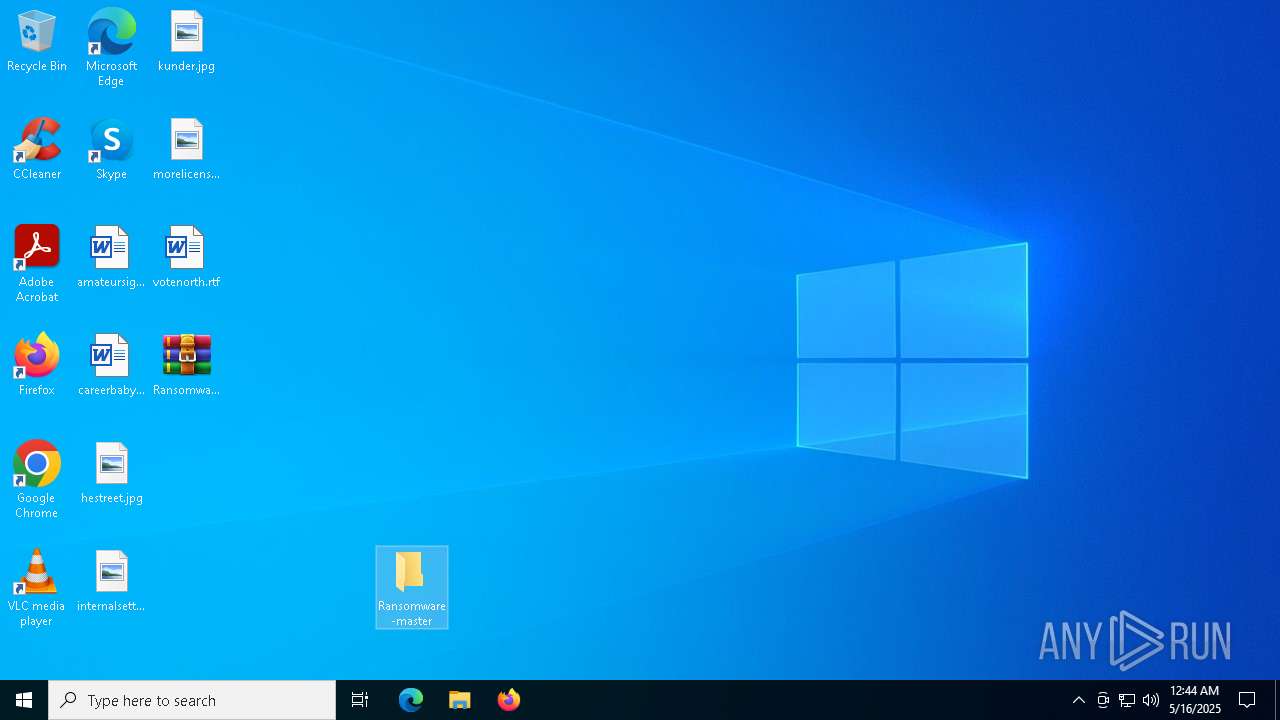
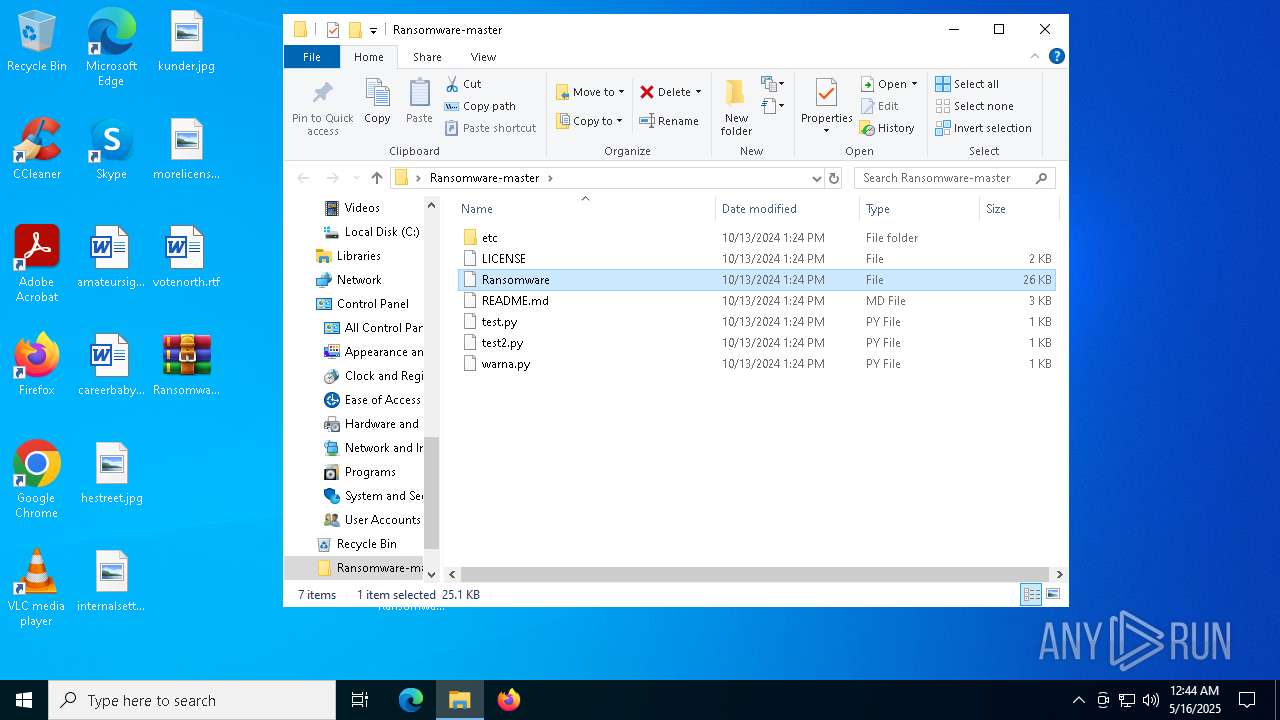
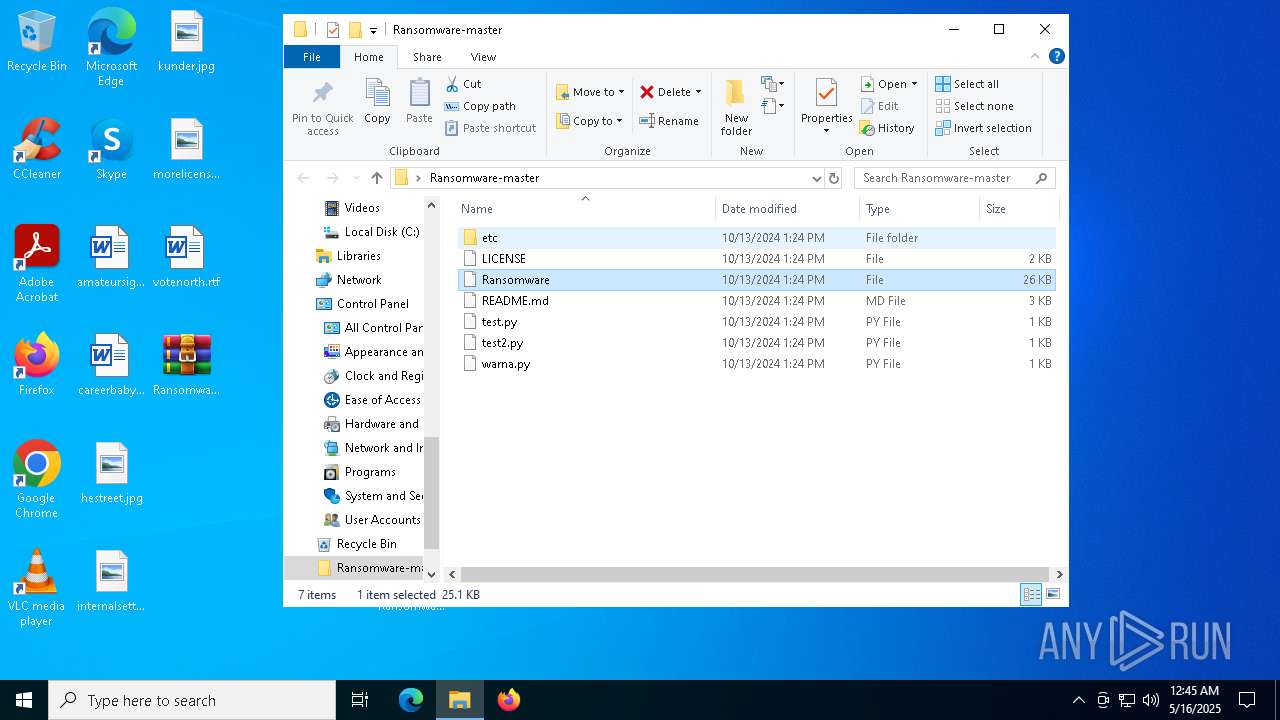
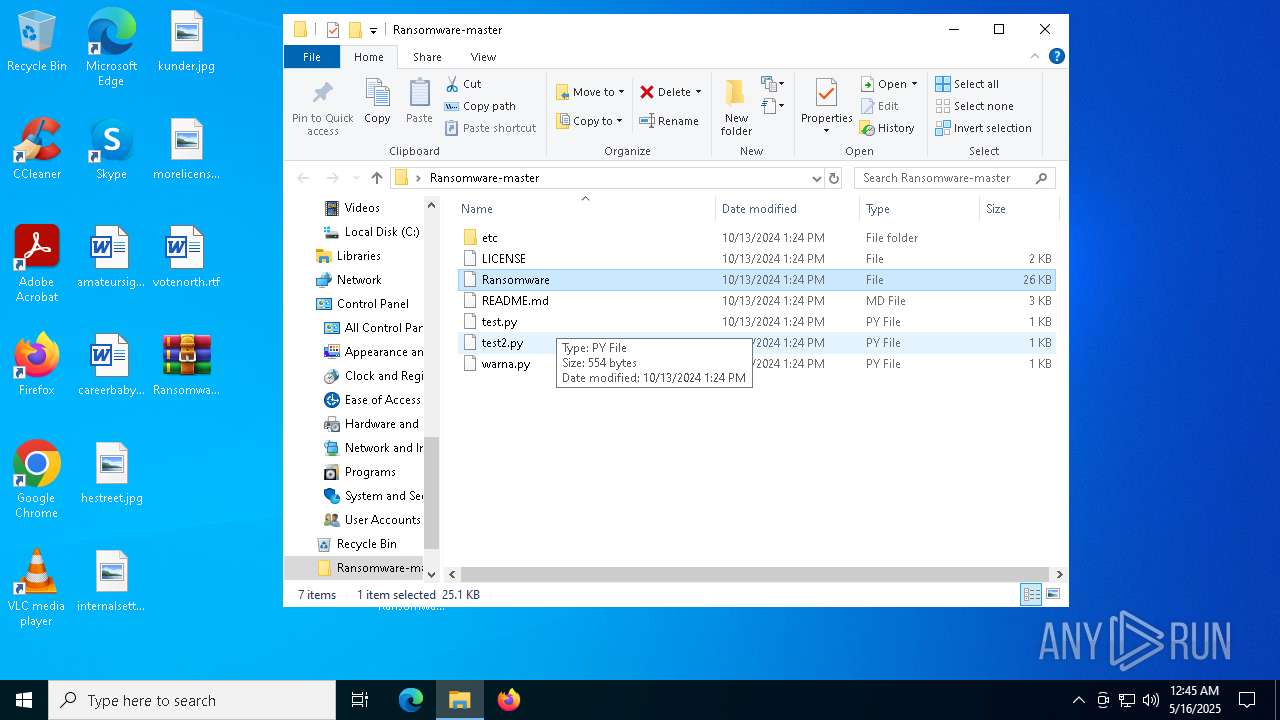
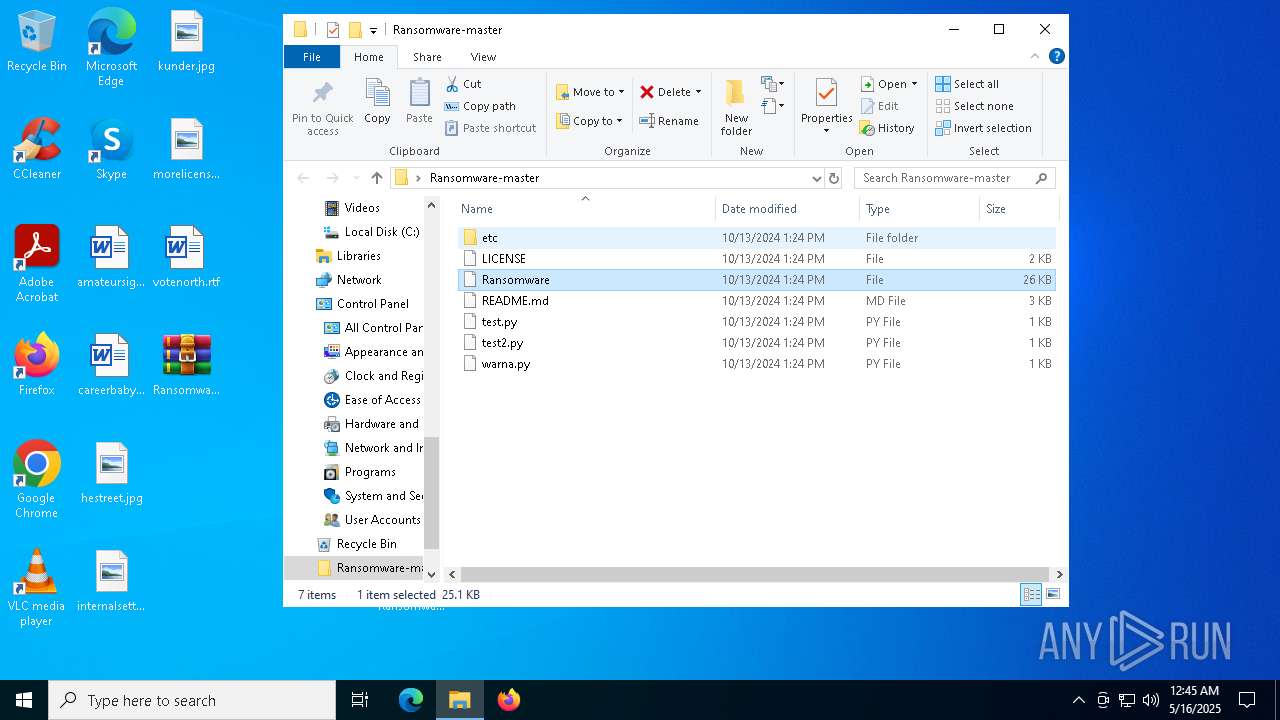
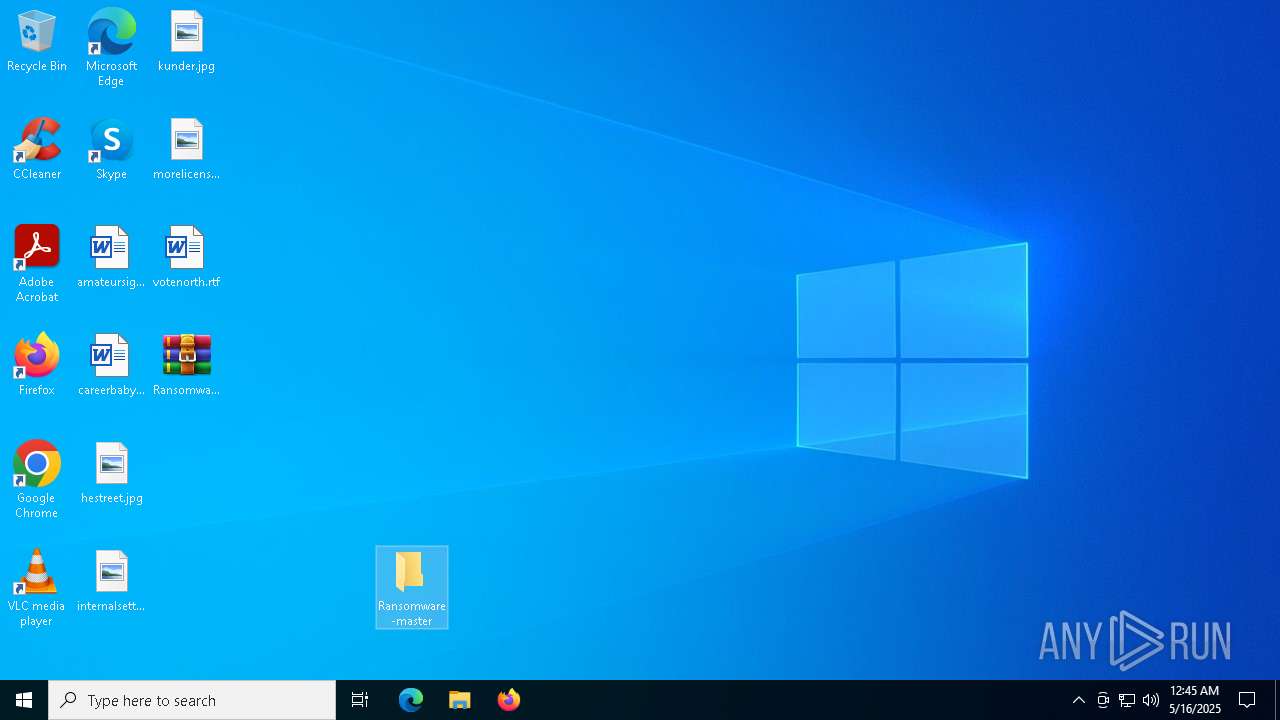
| File name: | Ransomware-master.zip |
| Full analysis: | https://app.any.run/tasks/dc4f1ab2-5696-4f88-a992-3c043fbdac8b |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 00:44:23 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 255FFABF0788A28C52889E9F9675C9DC |
| SHA1: | 4C61F9E16DF1705DB48EE91EC1A2AB3D84E2F107 |
| SHA256: | 3E2BA9A25E9891C6DCB75AD73C1262D523E09F0EB3D095EDE9EA9D11F42EBC28 |
| SSDEEP: | 98304:IT1mSeDqPOKpROCYrDkSYt7TTPT4tQs6sx1vqQU66tgFKk5jnnZFvPcnATMxRT/I:duA2RAdXI9mjaGOTaCprI |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 2392)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 2392)
INFO
The sample compiled with russian language support
- WinRAR.exe (PID: 2392)
The sample compiled with english language support
- WinRAR.exe (PID: 2392)
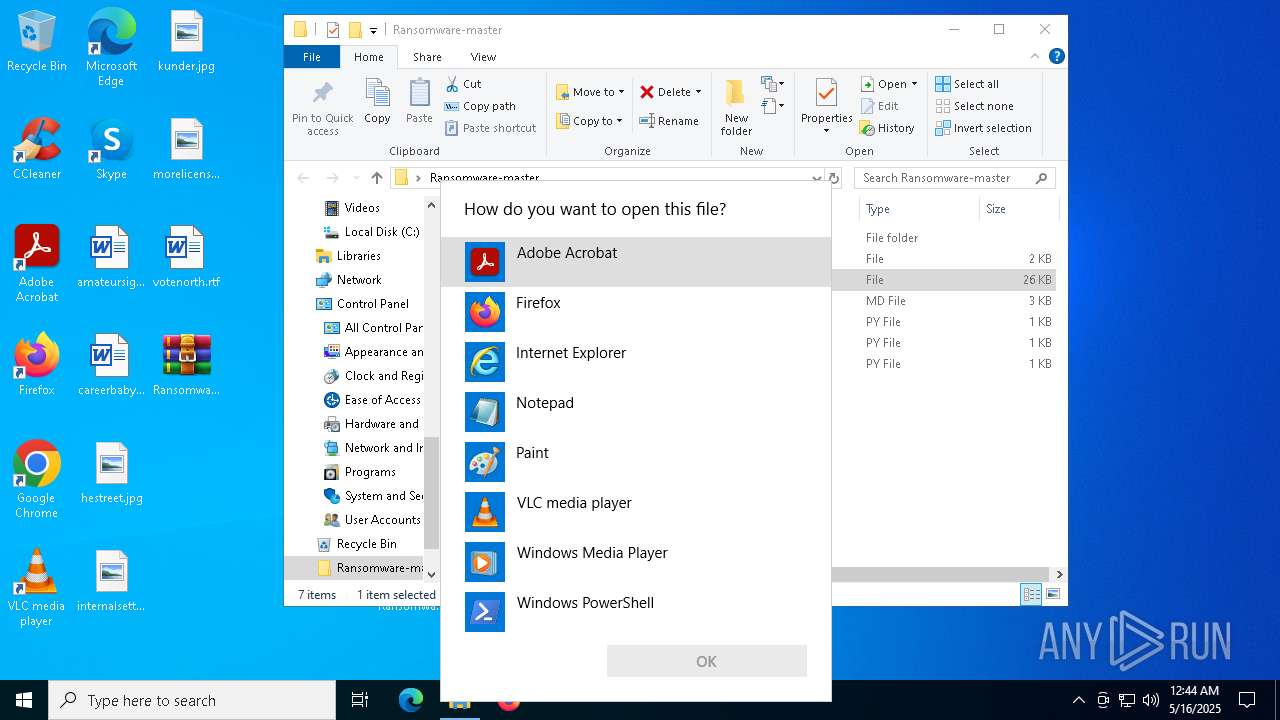
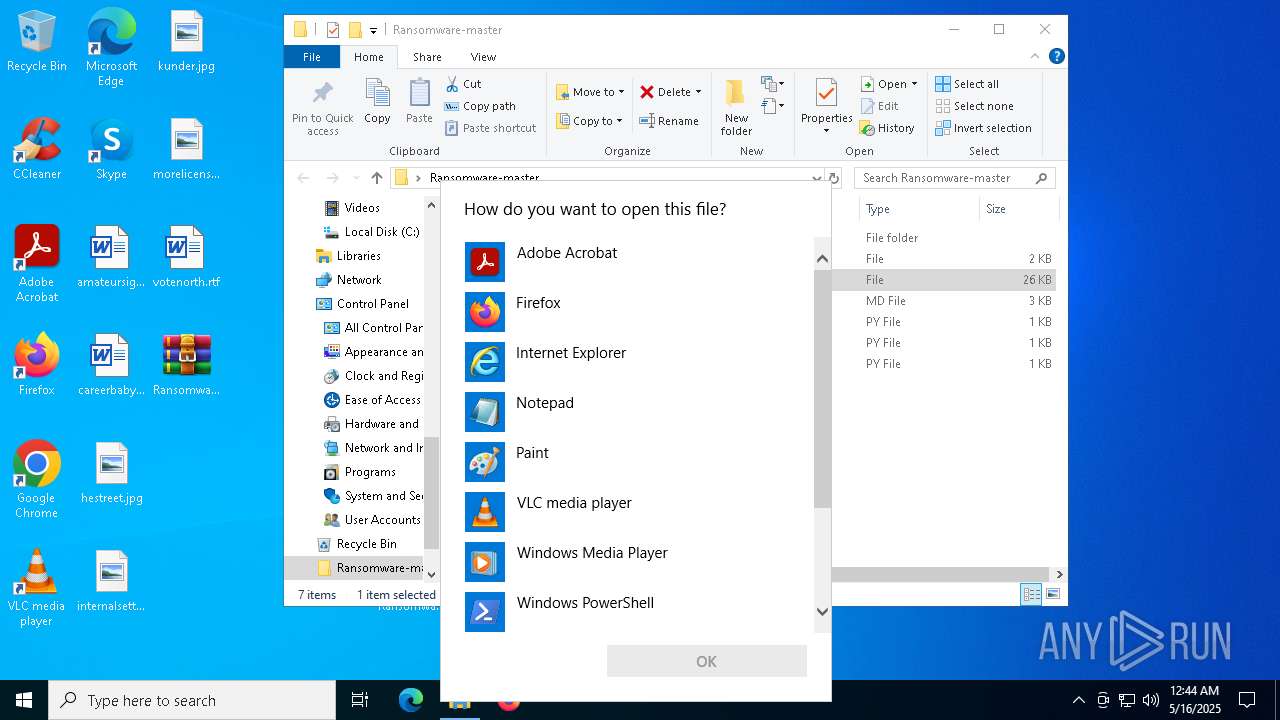
Manual execution by a user
- WinRAR.exe (PID: 632)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 5640)
Reads the software policy settings
- slui.exe (PID: 5436)
Checks proxy server information
- slui.exe (PID: 5436)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
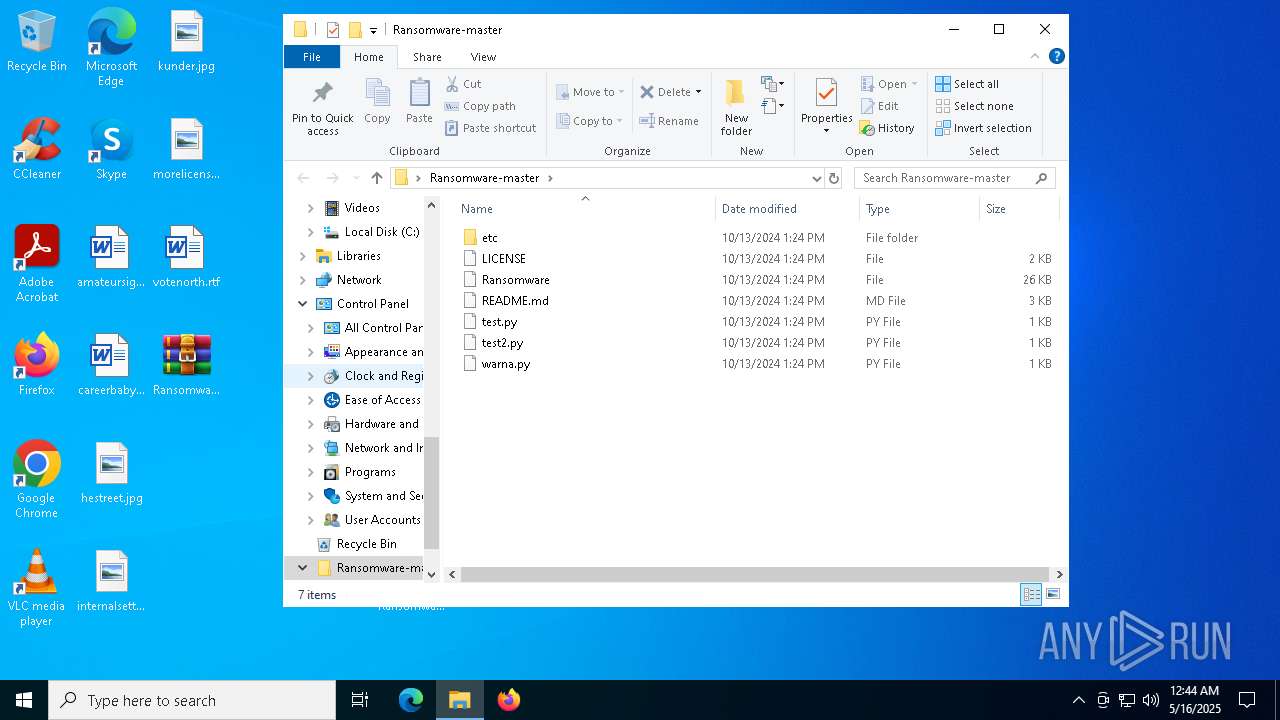
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:10:13 06:24:32 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Ransomware-master/ |
Total processes
148
Monitored processes
9
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
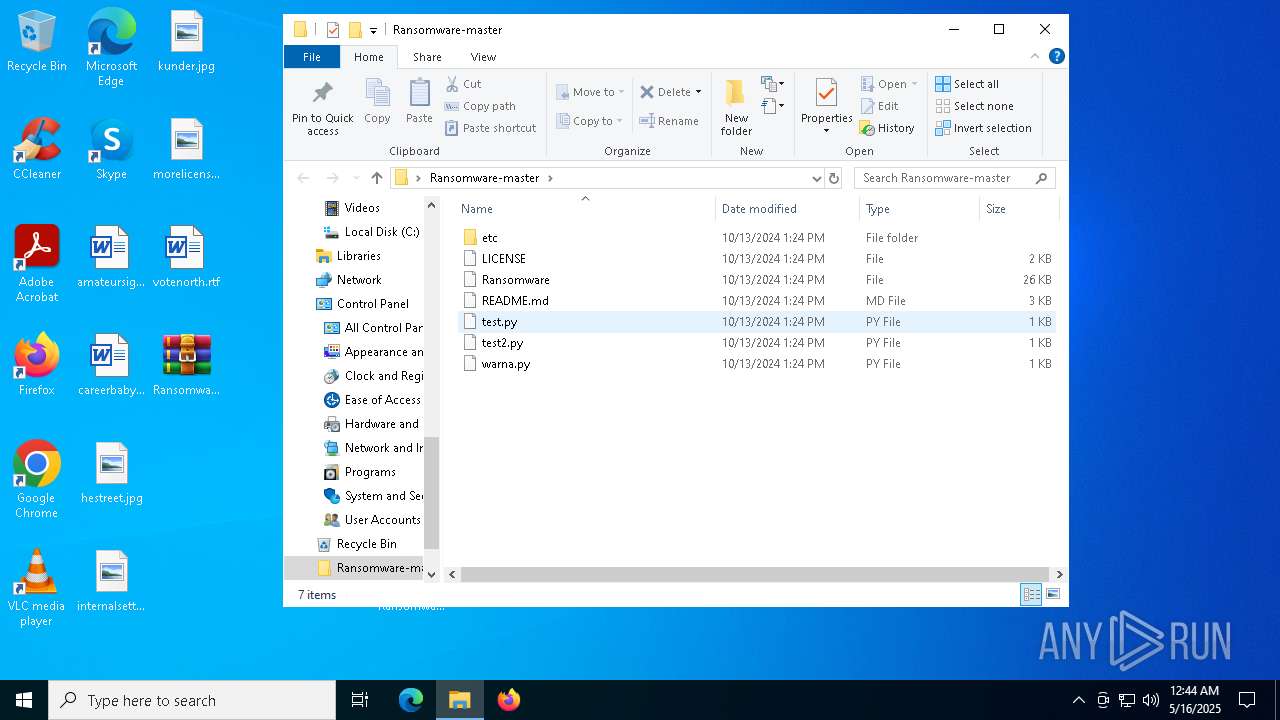
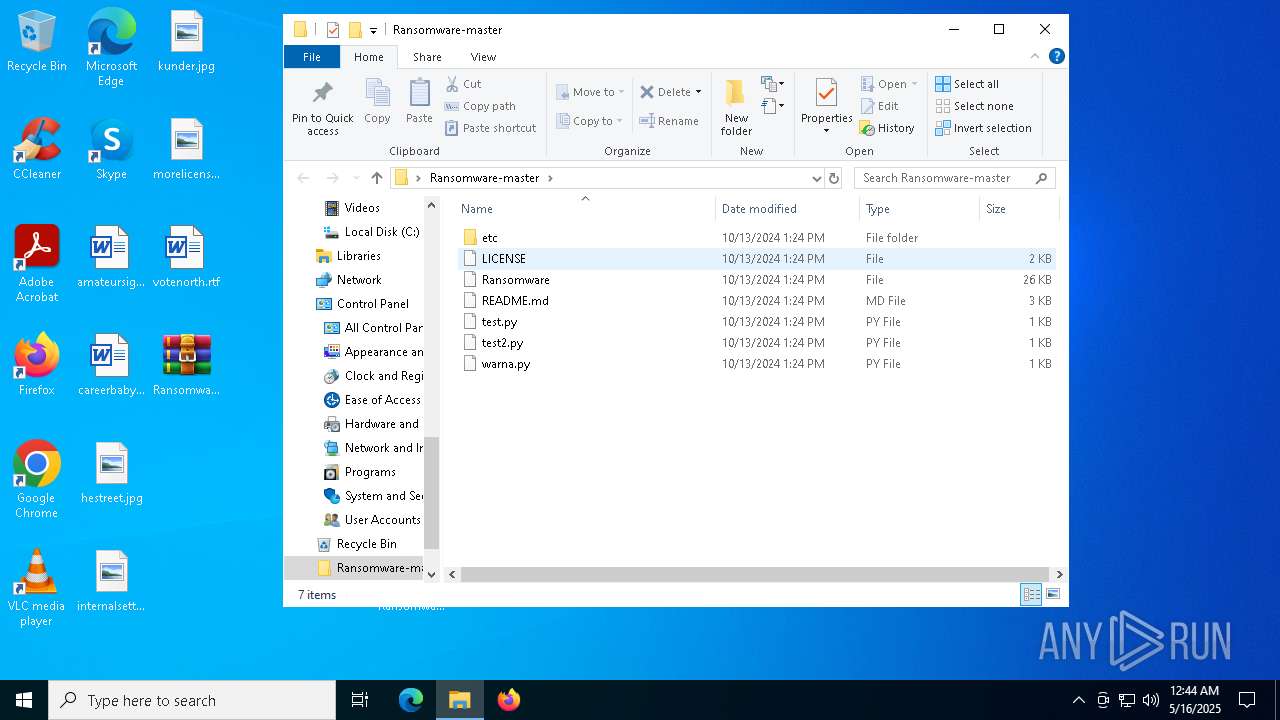
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
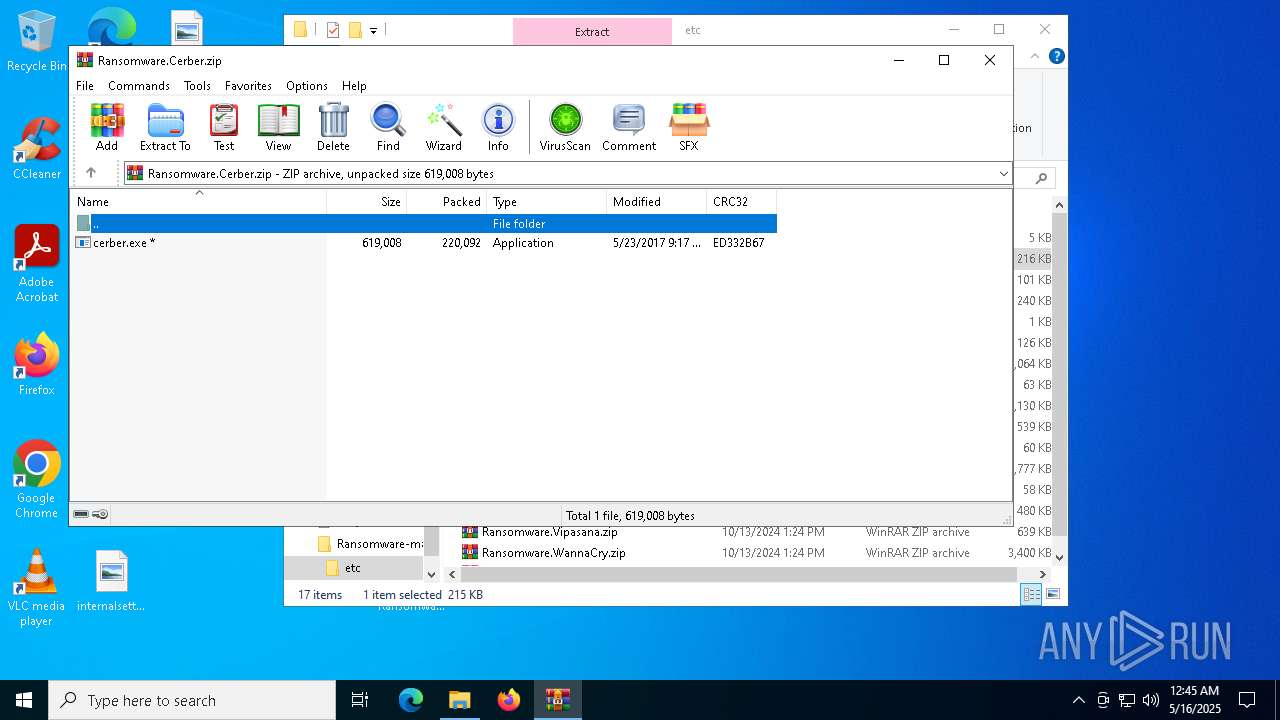
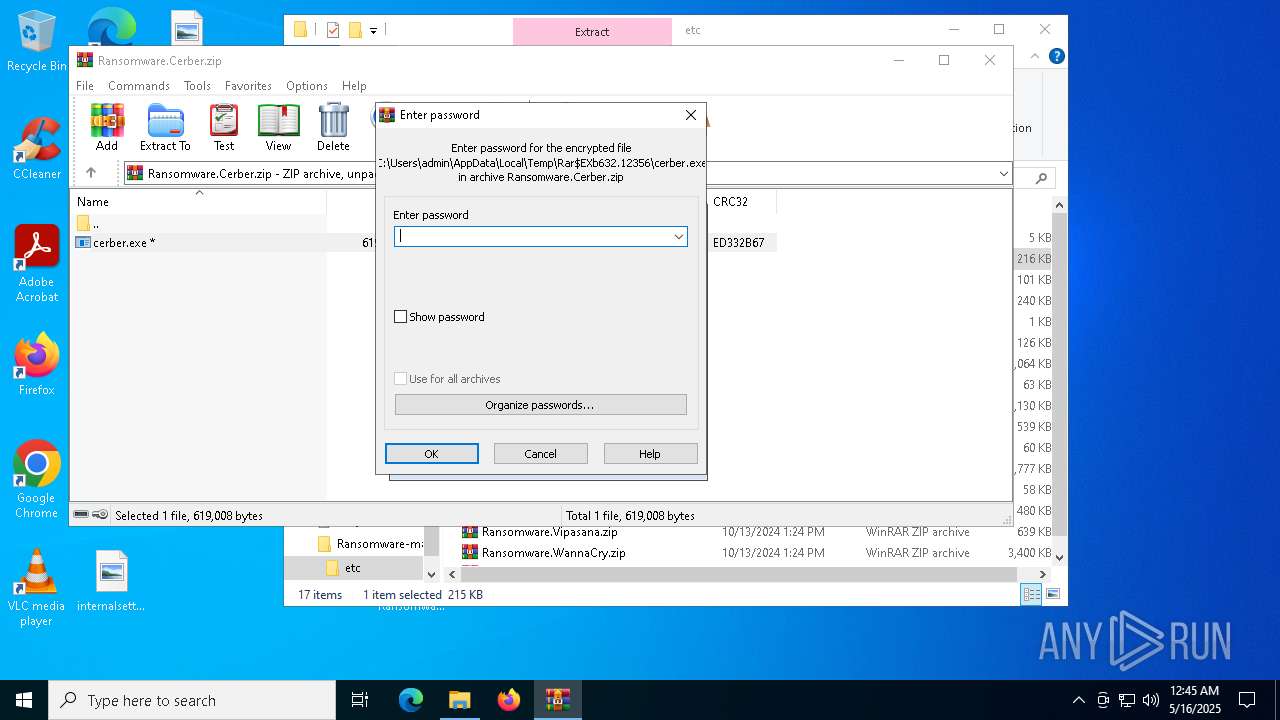
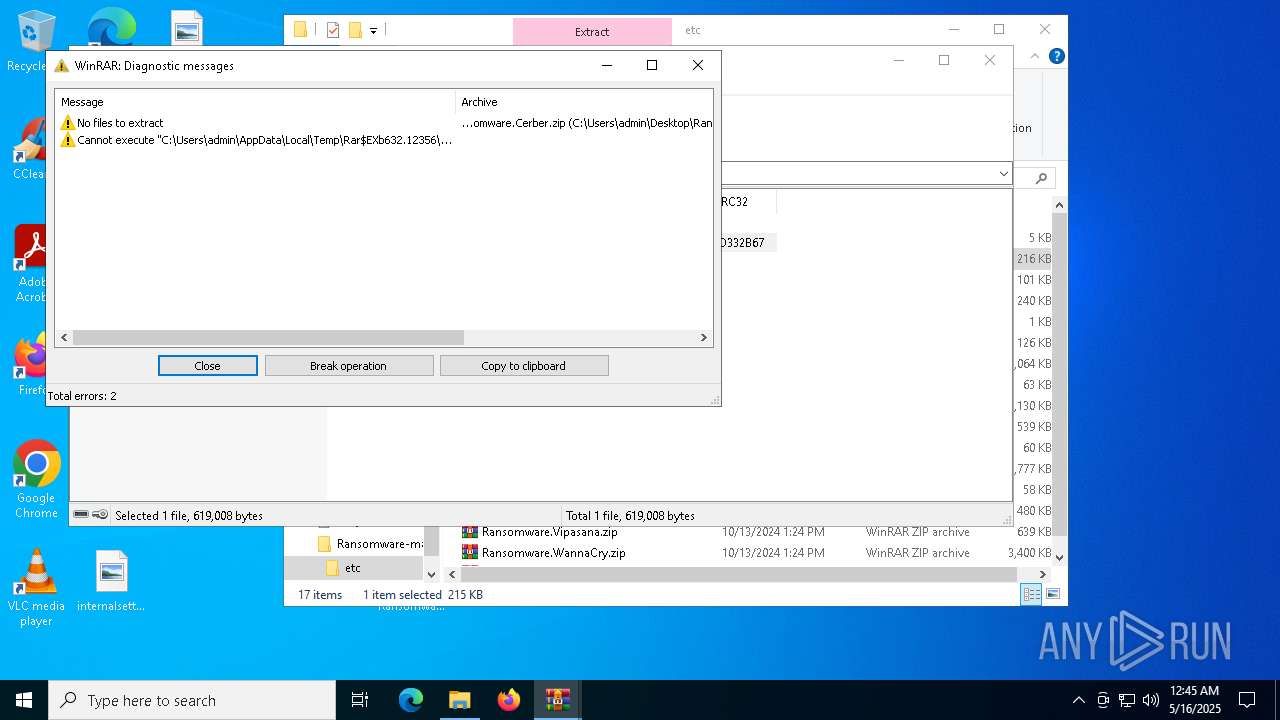
| 632 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Ransomware-master\etc\Ransomware.Cerber.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2332 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | UCPDMgr.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2392 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\Ransomware-master.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 4000 | "C:\WINDOWS\system32\UCPDMgr.exe" | C:\Windows\System32\UCPDMgr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: User Choice Protection Manager Exit code: 0 Version: 1.0.0.414301 Modules
| |||||||||||||||
| 4628 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5436 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5640 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6252 | "C:\WINDOWS\system32\UCPDMgr.exe" | C:\Windows\System32\UCPDMgr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: User Choice Protection Manager Exit code: 0 Version: 1.0.0.414301 Modules
| |||||||||||||||
| 7048 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | UCPDMgr.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 851
Read events
3 814
Write events
37
Delete events
0
Modification events
| (PID) Process: | (2392) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2392) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2392) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2392) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Ransomware-master.zip | |||
| (PID) Process: | (2392) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2392) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2392) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2392) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2392) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (2392) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
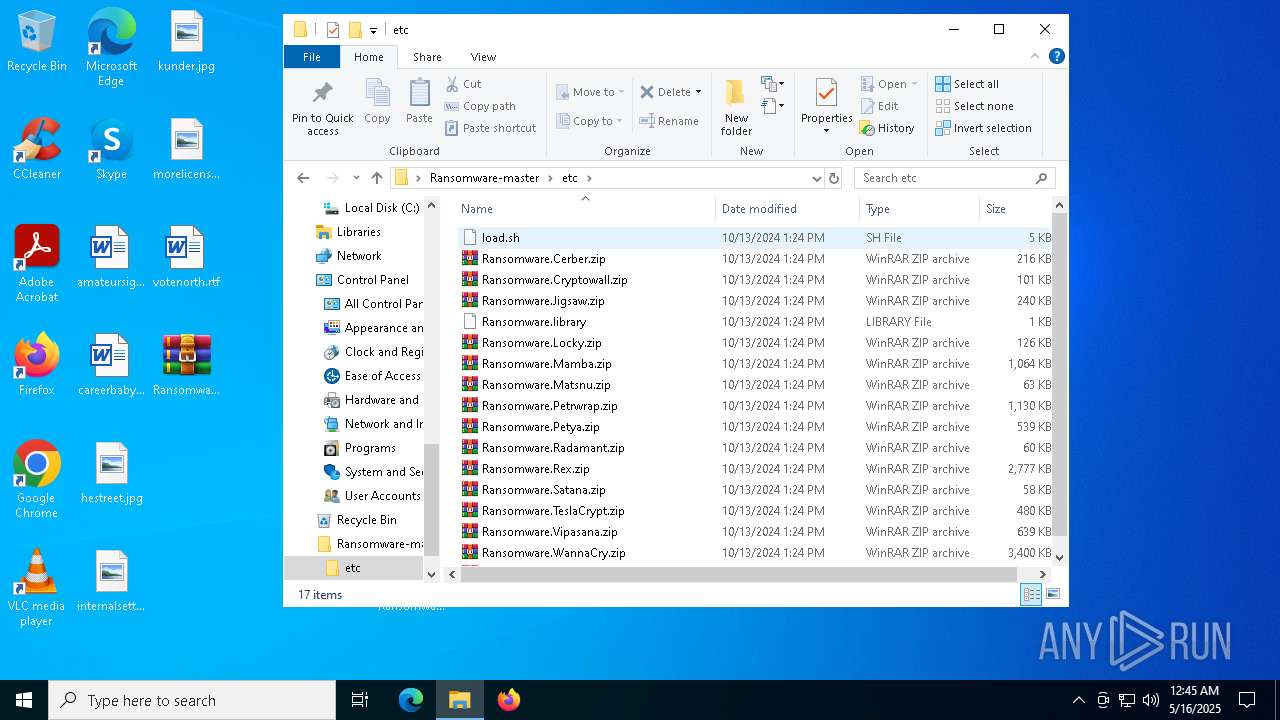
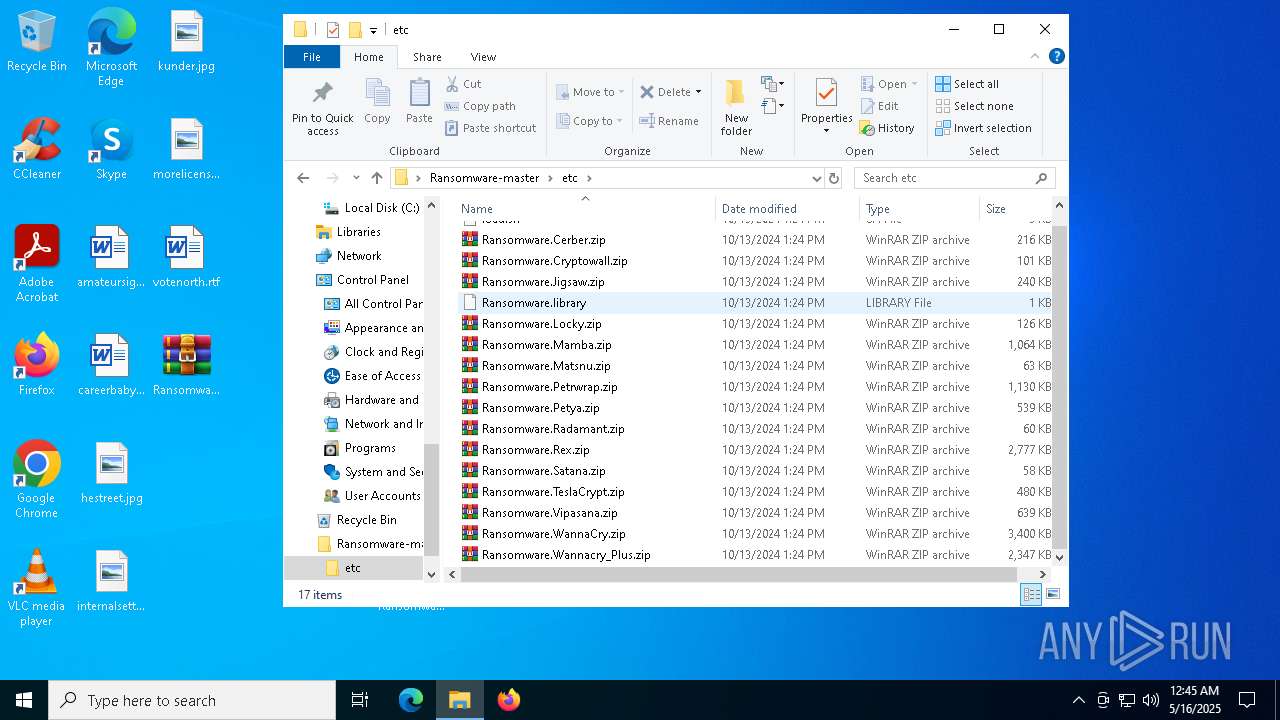
Executable files
0
Suspicious files
15
Text files
8
Unknown types
0
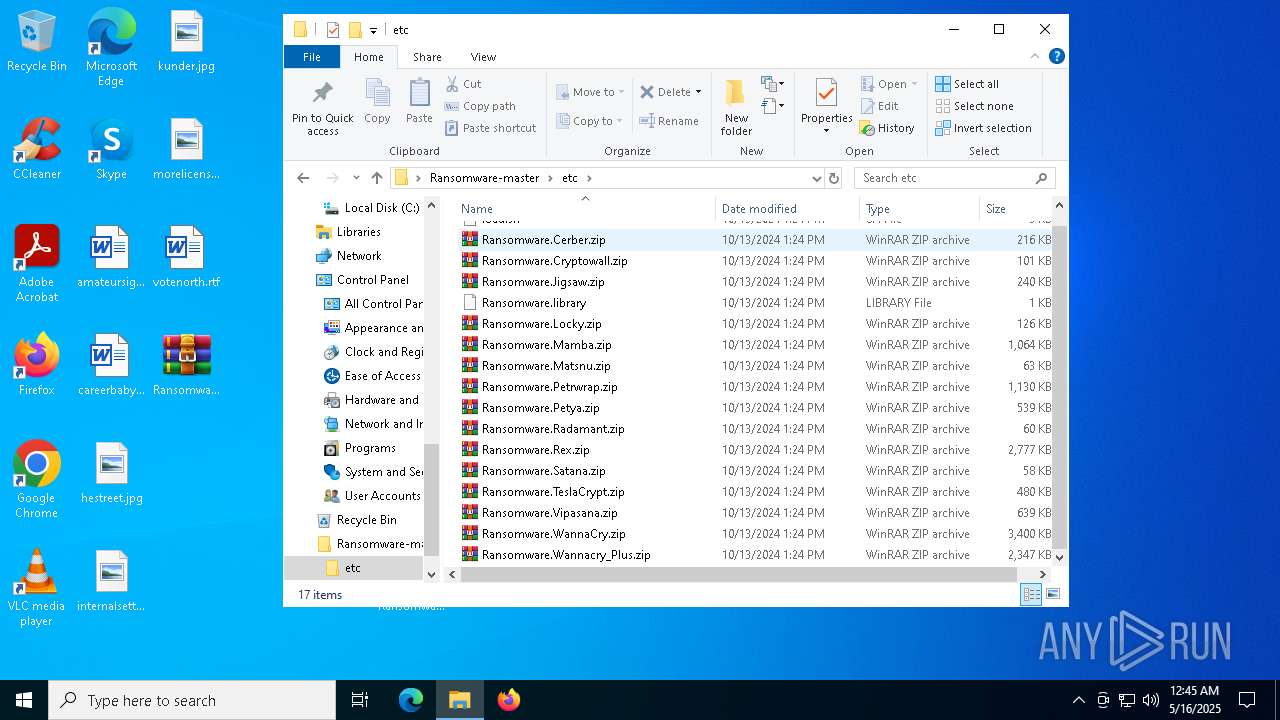
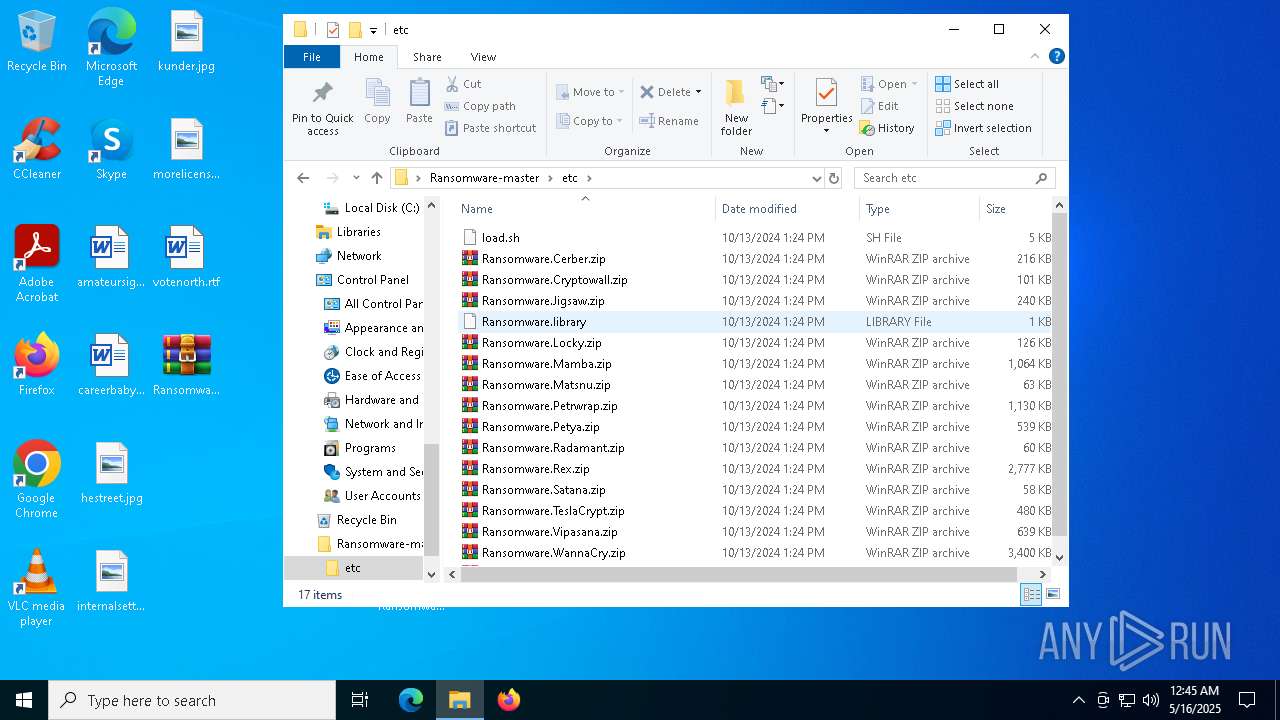
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
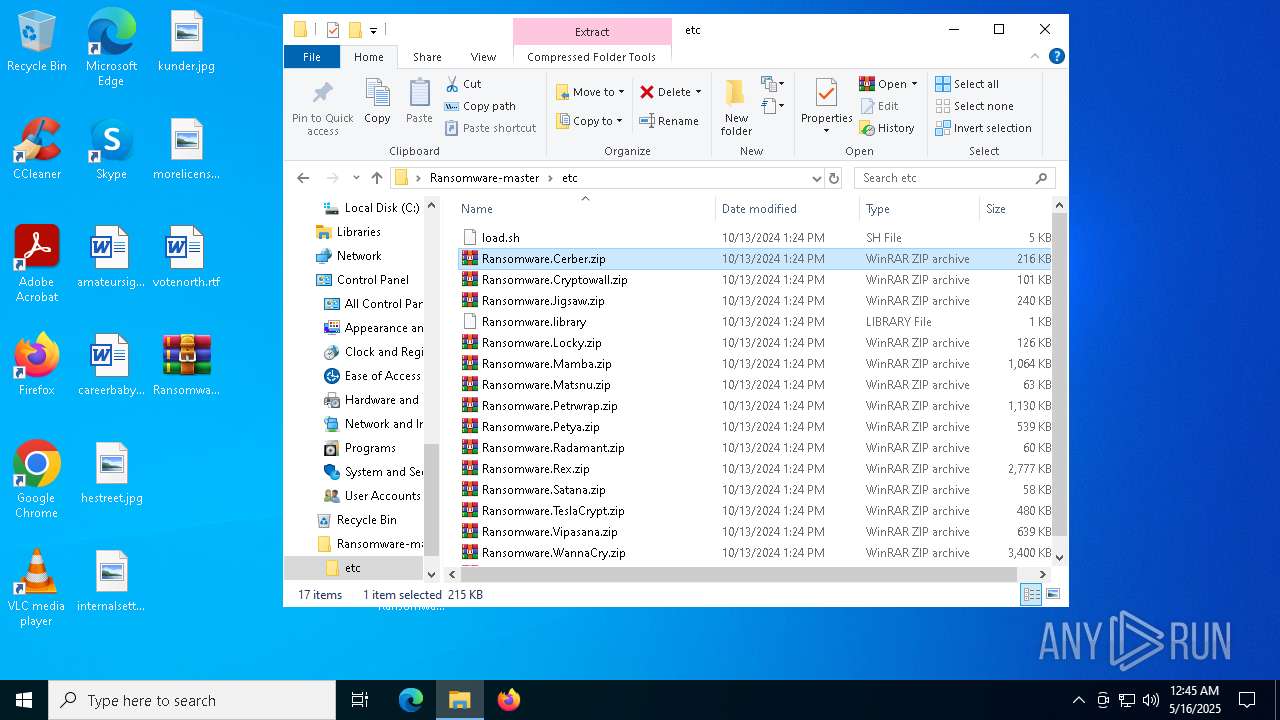
| 2392 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2392.9555\Ransomware-master\etc\Ransomware.Petrwrap.zip | compressed | |
MD5:6884A35803F2E795FA4B121F636332B4 | SHA256:CF01329C0463865422CAA595DE325E5FE3F7FBA44AABEBAAE11A6ADFEB78B91C | |||
| 2392 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2392.9555\Ransomware-master\etc\Ransomware.TeslaCrypt.zip | compressed | |
MD5:F755A44BBB97E9BA70BF38F1BDC67722 | SHA256:3B246FAA7E4B2A8550AA619F4DA893DB83721AACF62B46E5863644A5249AA87E | |||
| 2392 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2392.9555\Ransomware-master\etc\Ransomware.Cerber.zip | compressed | |
MD5:5C571C69DD75C30F95FE280CA6C624E9 | SHA256:416774BF62D9612D11D561D7E13203A3CBC352382A8E382ADE3332E3077E096C | |||
| 2392 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2392.9555\Ransomware-master\etc\Ransomware.Matsnu.zip | compressed | |
MD5:0A3487070911228115F3A13E9DA2CB89 | SHA256:F73027DD665772CC94DBE22B15938260BE61CBAAD753EFDCCB61C4FA464645E0 | |||
| 2392 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2392.9555\Ransomware-master\README.md | html | |
MD5:7C9E68A76F5C9E48ACD35736BA051EDA | SHA256:B9E98484CED89AD580EAF9E94F9C9499AA58D56E1F1EFA0B78B0CF8EA9C17C86 | |||
| 2392 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2392.9555\Ransomware-master\etc\Ransomware.Jigsaw.zip | compressed | |
MD5:3AD6374A3558149D09D74E6AF72344E3 | SHA256:86A391FE7A237F4F17846C53D71E45820411D1A9A6E0C16F22A11EBC491FF9FF | |||
| 2392 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2392.9555\Ransomware-master\etc\Ransomware.Mamba.zip | compressed | |
MD5:F94D1F4E2CE6C7CC81961361AAB8A144 | SHA256:610A52C340EBAFF31093C5EF0D76032AC2ACDC81A3431E68B244BF42905FD70A | |||
| 2392 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2392.9555\Ransomware-master\etc\Ransomware.Satana.zip | compressed | |
MD5:82F621944EE2639817400BEFABEDFFCF | SHA256:4785C134B128DF624760C02AD23C7E345A234A99828C3FECF58FBD6D5449897F | |||
| 2392 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2392.9555\Ransomware-master\etc\Ransomware.Locky.zip | compressed | |
MD5:B265305541DCE2A140DA7802442FBAC4 | SHA256:0537FA38B88755F39DF1CD774B907EC759DACAB2388DC0109F4DB9F0E9D191A0 | |||
| 2392 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2392.9555\Ransomware-master\etc\Ransomware.Petya.zip | compressed | |
MD5:E8FB95EBB7E0DB4C68A32947A74B5FF9 | SHA256:33CA487A65D38BAD82DCCFA0D076BAD071466E4183562D0B1AD1A2E954667FE9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
37
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2656 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2656 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2656 | SIHClient.exe | 52.149.20.212:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2656 | SIHClient.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2656 | SIHClient.exe | 20.242.39.171:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
login.live.com |
| whitelisted |