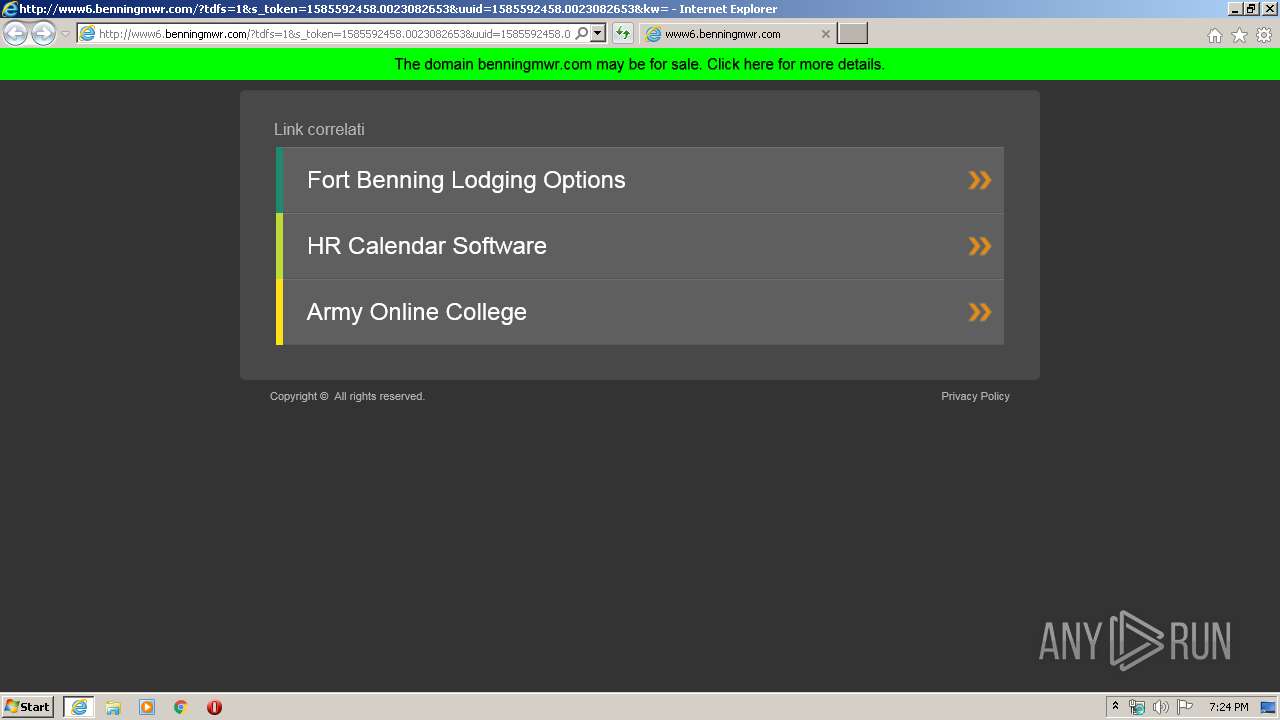
| URL: | http://www6.benningmwr.com/?tdfs=1&s_token=1585592458.0023082653&uuid=1585592458.0023082653&kw=Fort+Benning+Lodging+Options&term=Fort%20Benning%20Lodging%20Options&term=HR%20Calendar%20Software&term=Army%20Online%20College&backfill=0 |
| Full analysis: | https://app.any.run/tasks/19da1a80-ee18-4d2f-b1aa-188fd61c387c |
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2020, 18:24:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7E5AA173A25CE60A947DF7F686F18A3D |
| SHA1: | D618A37743CD33DE78379593F2F7FE676C52DDE6 |
| SHA256: | 3E29C59E5CACE681403A12113C911D79F810C29808E426B9B3C39EDD73AFA652 |
| SSDEEP: | 6:CcgVCKKA5XRy9XRyUm9/jKwSetKx8nloekgHVn:ACt6By9By7gwzKx8nug1n |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2884)
- iexplore.exe (PID: 2764)
Creates files in the user directory
- iexplore.exe (PID: 2764)
Reads internet explorer settings
- iexplore.exe (PID: 2764)
Changes internet zones settings
- iexplore.exe (PID: 2884)
Reads settings of System Certificates
- iexplore.exe (PID: 2884)
- iexplore.exe (PID: 2764)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2884)
Changes settings of System certificates
- iexplore.exe (PID: 2884)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2764 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2884 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2884 | "C:\Program Files\Internet Explorer\iexplore.exe" http://www6.benningmwr.com/?tdfs=1&s_token=1585592458.0023082653&uuid=1585592458.0023082653&kw=Fort+Benning+Lodging+Options&term=Fort%20Benning%20Lodging%20Options&term=HR%20Calendar%20Software&term=Army%20Online%20College&backfill=0 | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
8 175
Read events
1 415
Write events
4 516
Delete events
2 244
Modification events
| (PID) Process: | (2884) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2345142942 | |||
| (PID) Process: | (2884) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30803648 | |||
| (PID) Process: | (2884) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2884) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2884) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2884) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2884) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2884) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2884) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2884) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
37
Text files
12
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2764 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab7288.tmp | — | |
MD5:— | SHA256:— | |||
| 2764 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar7289.tmp | — | |
MD5:— | SHA256:— | |||
| 2764 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\JN5A2QUW.txt | — | |
MD5:— | SHA256:— | |||
| 2764 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\IUCECT67.txt | — | |
MD5:— | SHA256:— | |||
| 2764 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8828F39C7C0CE9A14B25C7EB321181BA_BD8B98368542C3BBAE3413A0EF3BB623 | binary | |
MD5:— | SHA256:— | |||
| 2764 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | der | |
MD5:— | SHA256:— | |||
| 2764 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\8QU1CQCK.htm | html | |
MD5:— | SHA256:— | |||
| 2764 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\BE8B021F9E811DFC8C8A28572A17C05A_B4E256AEE3EBA21D6B1078B3E1B79532 | der | |
MD5:— | SHA256:— | |||
| 2764 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | binary | |
MD5:— | SHA256:— | |||
| 2764 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\BE8B021F9E811DFC8C8A28572A17C05A_B4E256AEE3EBA21D6B1078B3E1B79532 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
33
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2764 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEC4G%2Bv2mHN8jAgAAAABcZ3g%3D | US | der | 471 b | whitelisted |
2764 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAyO4MkNaokViAQGHuJB%2Ba8%3D | US | der | 471 b | whitelisted |
2764 | iexplore.exe | GET | 200 | 23.37.43.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEGMYDTj7gJd4qdA1oxYY%2BEA%3D | NL | der | 1.71 Kb | shared |
2764 | iexplore.exe | GET | 200 | 192.124.249.24:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
2764 | iexplore.exe | GET | 200 | 192.124.249.24:80 | http://ocsp.godaddy.com//MEowSDBGMEQwQjAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCQDIf69pKhNfQw%3D%3D | US | der | 1.74 Kb | whitelisted |
2764 | iexplore.exe | GET | 200 | 192.124.249.24:80 | http://ocsp.godaddy.com//MEowSDBGMEQwQjAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCQD3%2Fz9kKgyC7Q%3D%3D | US | der | 1.74 Kb | whitelisted |
2764 | iexplore.exe | GET | 200 | 2.16.186.27:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgPBFREIN5Y29jTsR1GTvWoFPg%3D%3D | unknown | der | 527 b | whitelisted |
2884 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2764 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEFOOHQjK5IlqCAAAAAAyCmA%3D | US | der | 471 b | whitelisted |
2764 | iexplore.exe | GET | 200 | 192.124.249.24:80 | http://ocsp.godaddy.com//MEowSDBGMEQwQjAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCQDIf69pKhNfQw%3D%3D | US | der | 1.74 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2764 | iexplore.exe | 35.186.238.101:80 | — | Google Inc. | US | whitelisted |
2764 | iexplore.exe | 172.217.22.36:443 | www.google.com | Google Inc. | US | whitelisted |
2764 | iexplore.exe | 143.204.98.134:443 | d1hi41nc56pmug.cloudfront.net | — | US | unknown |
2764 | iexplore.exe | 216.58.205.227:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2764 | iexplore.exe | 23.37.43.27:80 | s.symcd.com | Akamai Technologies, Inc. | NL | whitelisted |
2764 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2764 | iexplore.exe | 192.124.249.24:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
2764 | iexplore.exe | 35.227.236.88:443 | api.parking.godaddy.com | — | US | suspicious |
2764 | iexplore.exe | 198.58.118.167:443 | postback.trafficmotor.com | Linode, LLC | US | malicious |
2764 | iexplore.exe | 2.16.186.35:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www6.benningmwr.com |
| whitelisted |
www.google.com |
| malicious |
d1hi41nc56pmug.cloudfront.net |
| whitelisted |
s.symcd.com |
| shared |
ocsp.pki.goog |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.aws.parking.godaddy.com |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
afs.googleusercontent.com |
| whitelisted |
api.parking.godaddy.com |
| whitelisted |