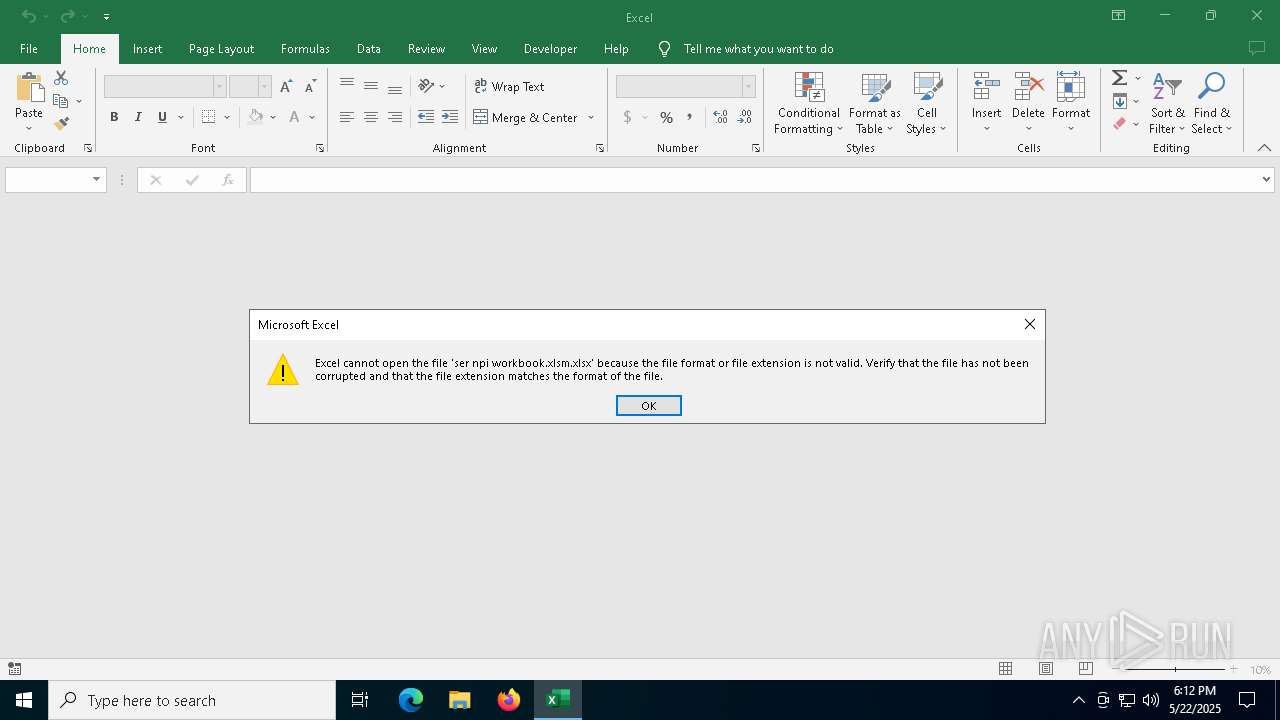
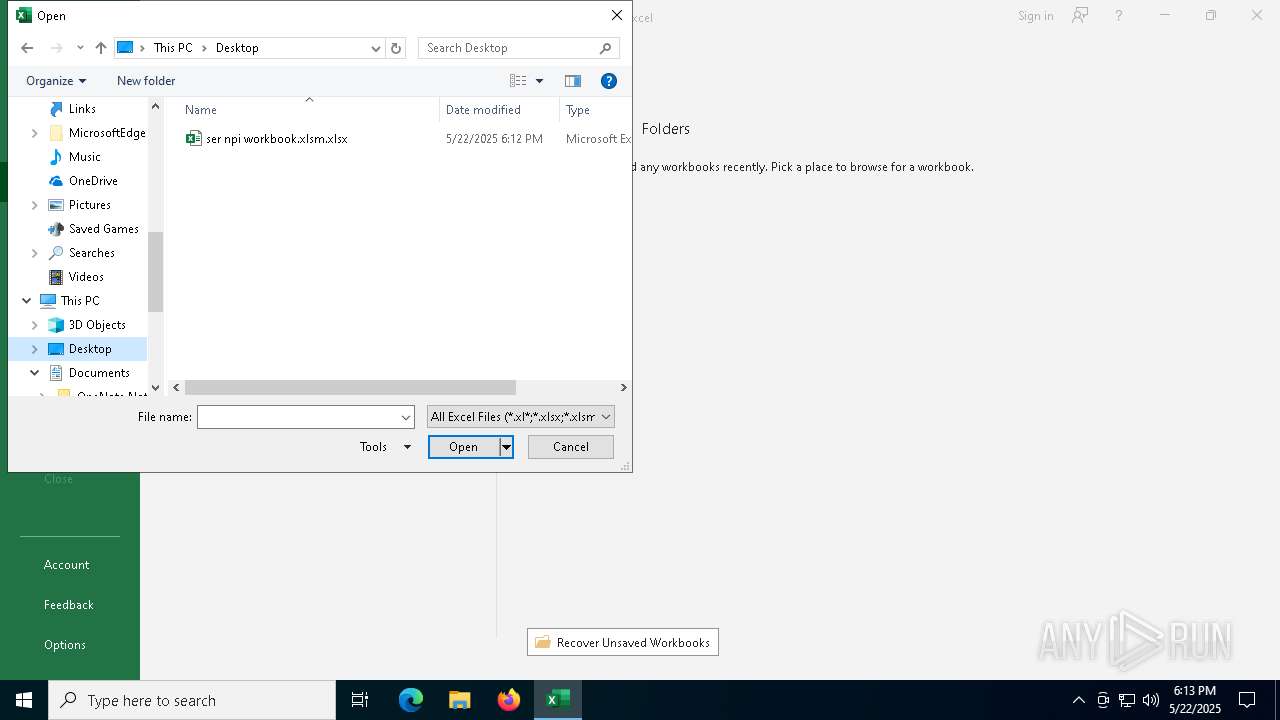
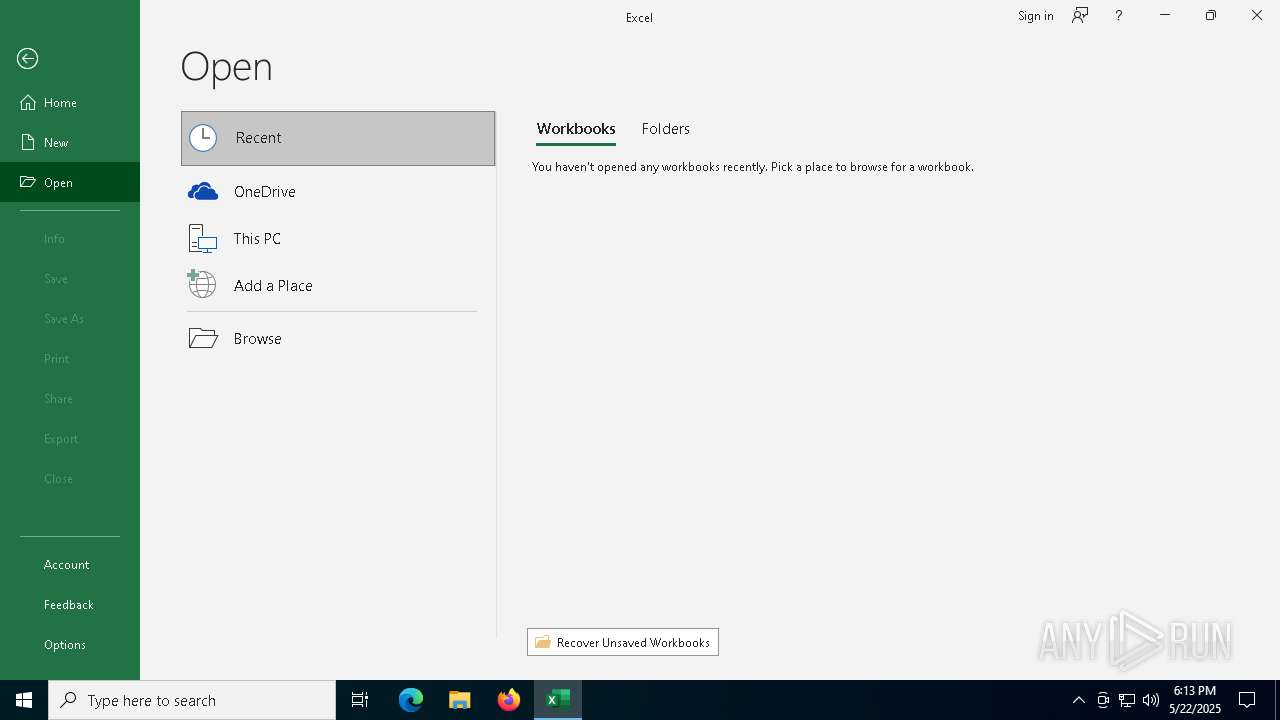
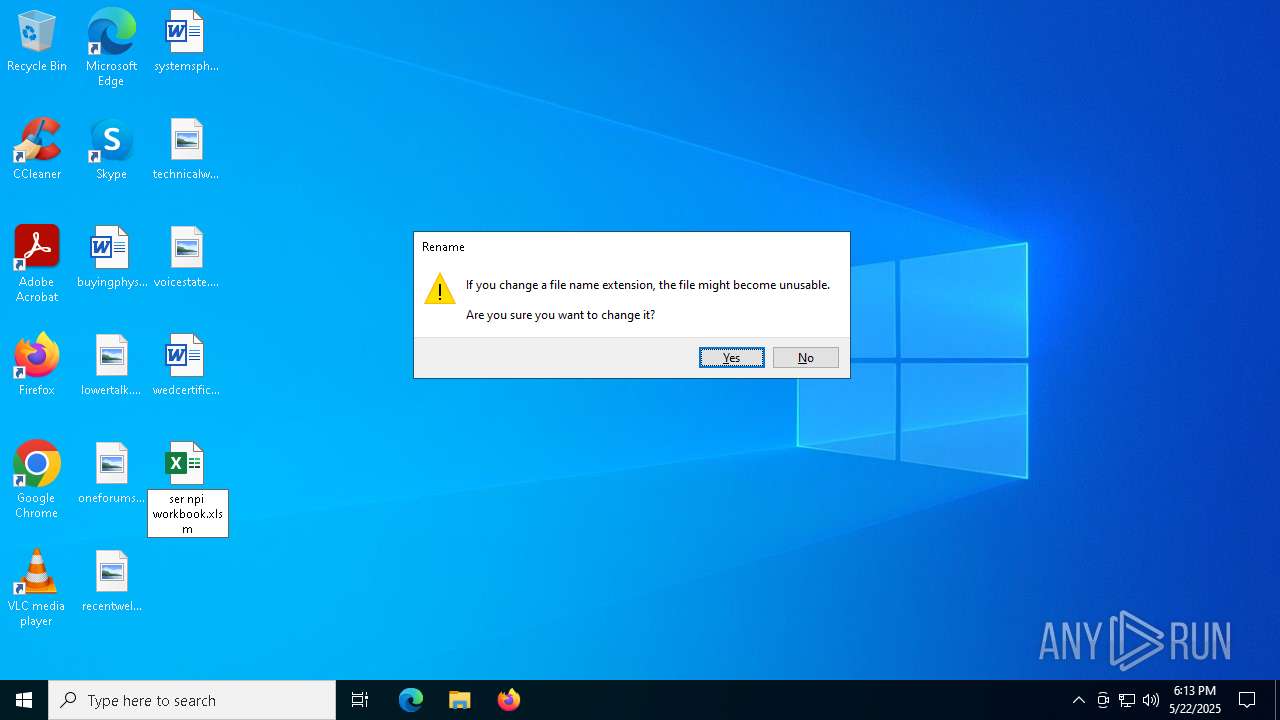
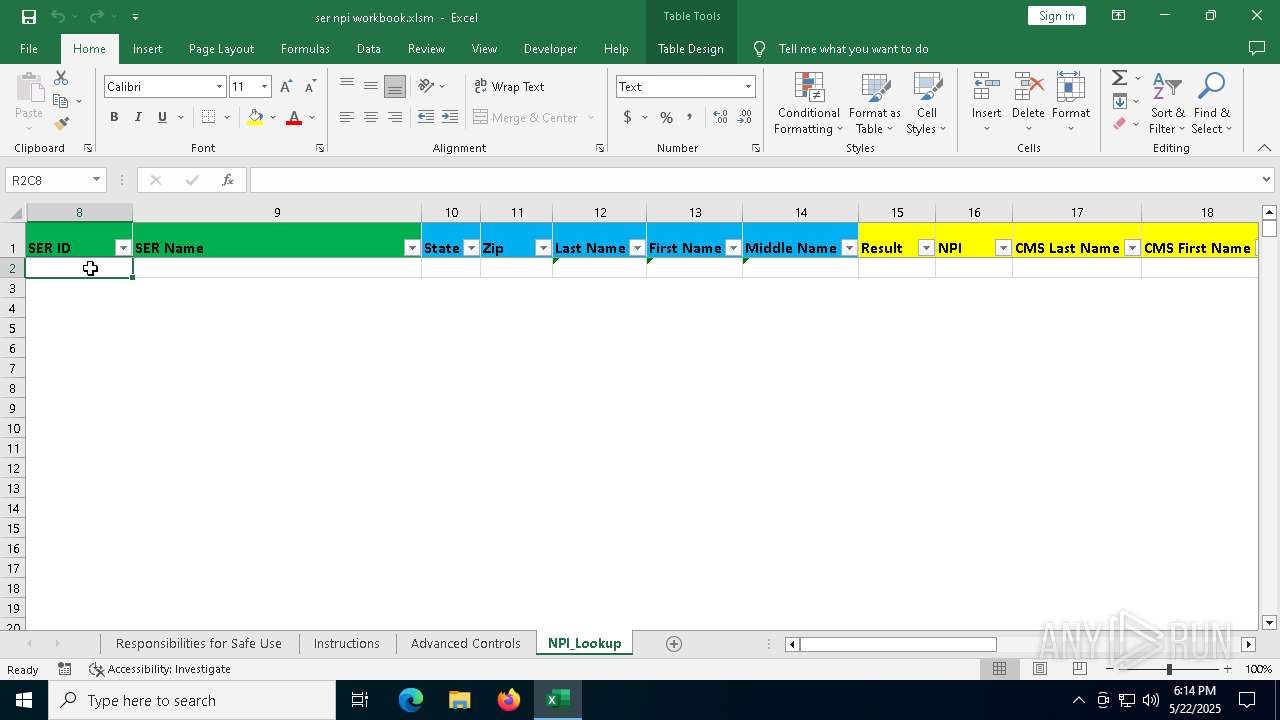
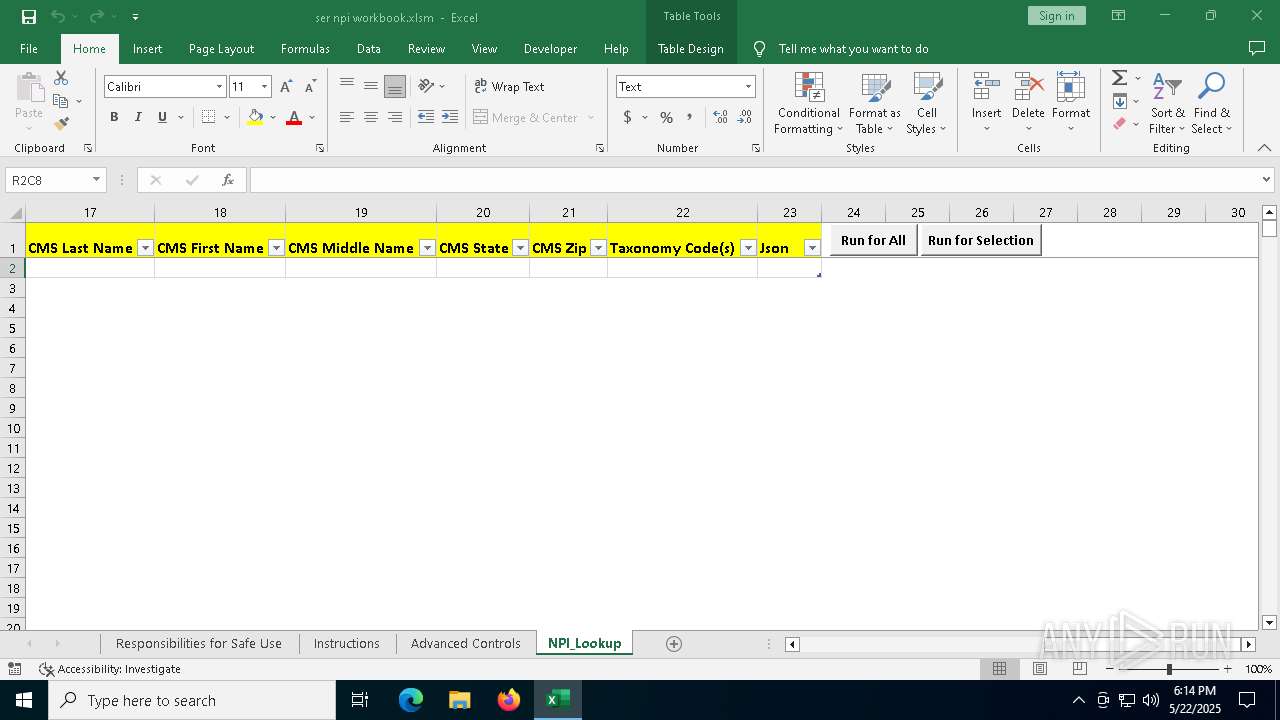
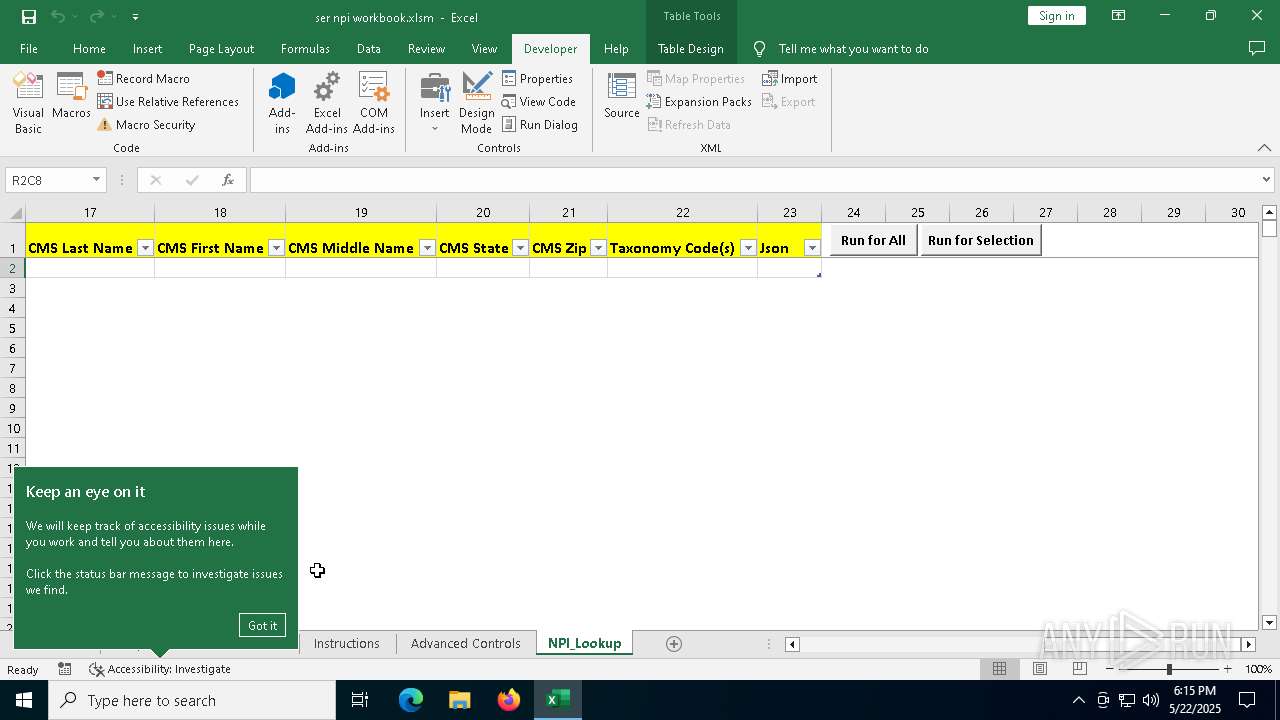
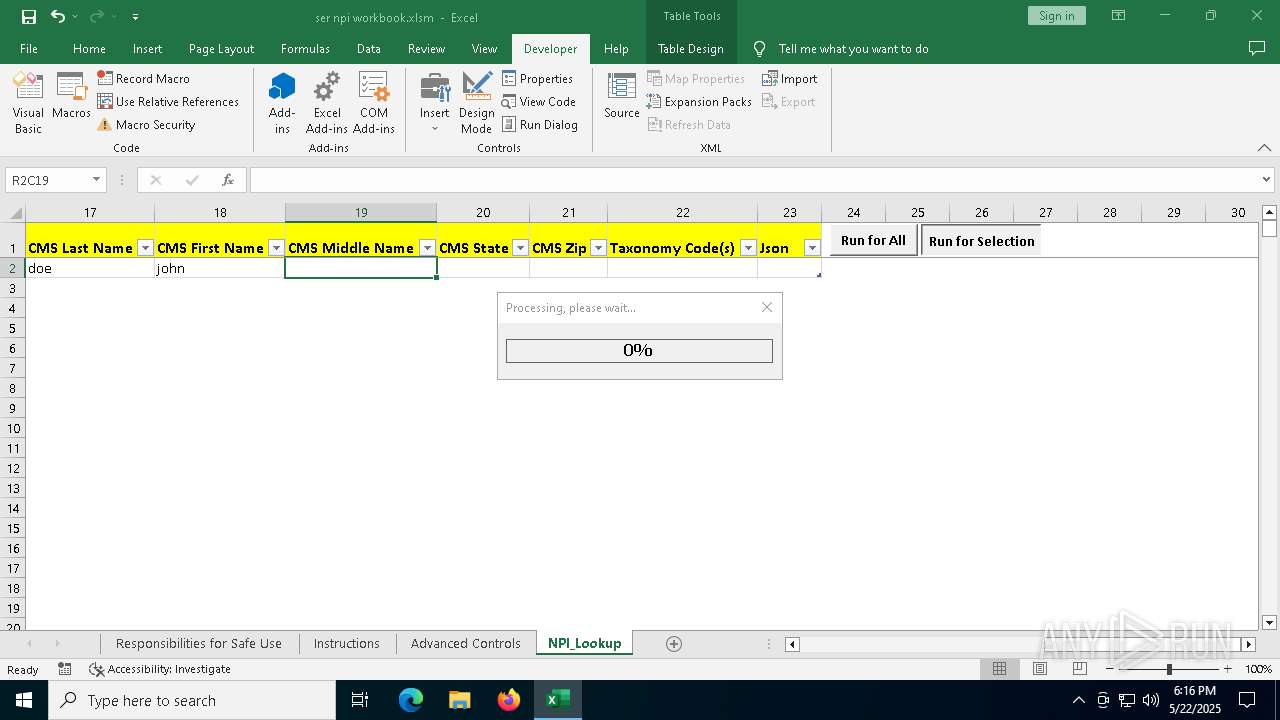
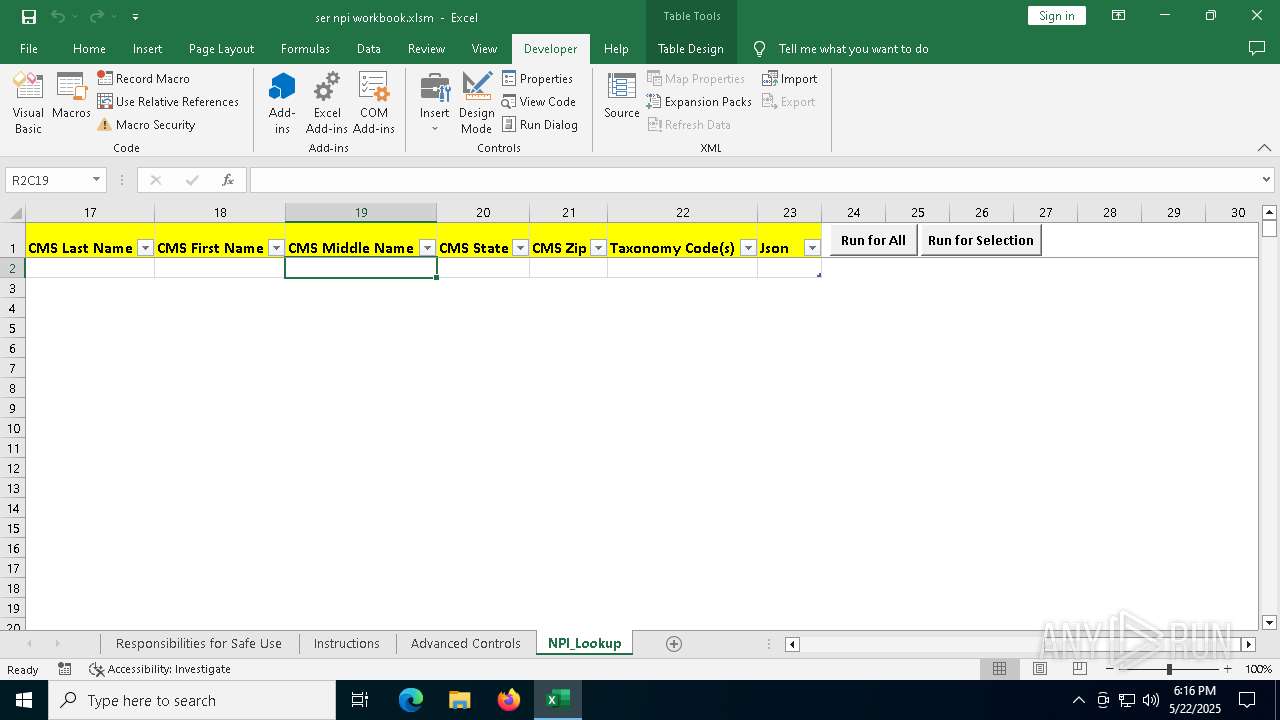
| File name: | ser npi workbook.xlsm |
| Full analysis: | https://app.any.run/tasks/bb79e355-0061-4acb-8ff5-259e010a837a |
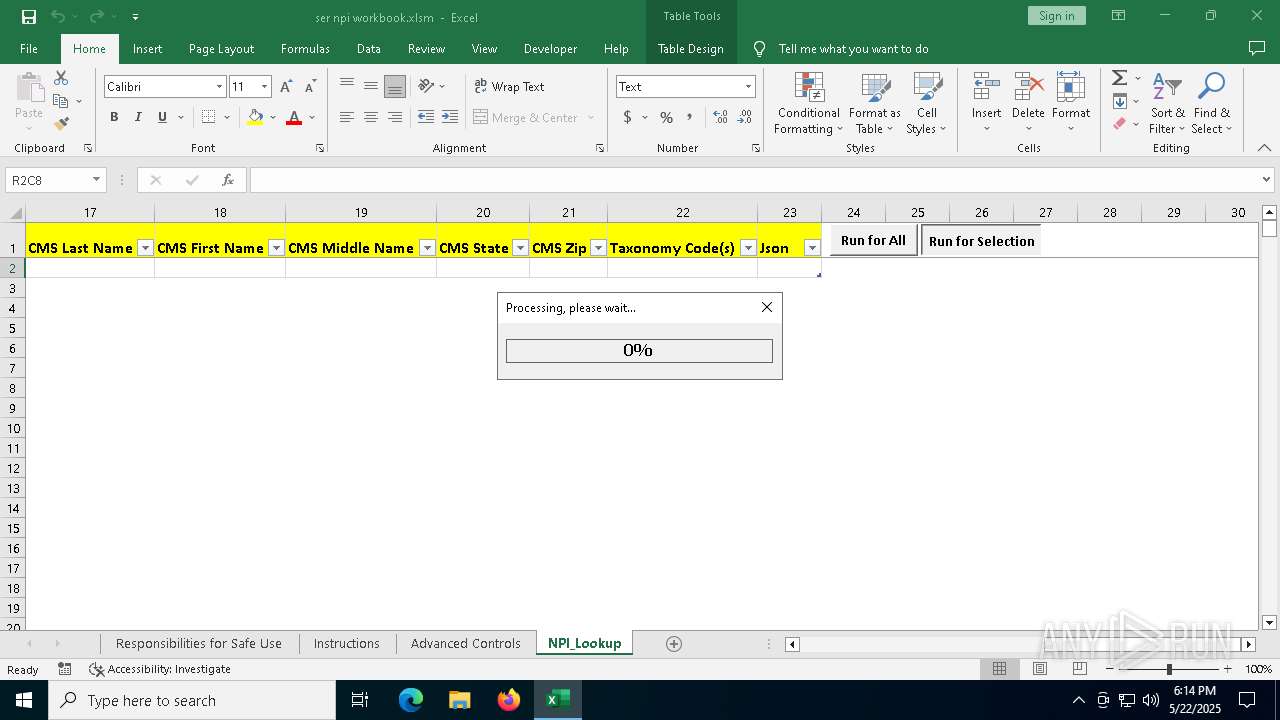
| Verdict: | Malicious activity |
| Analysis date: | May 22, 2025, 18:12:05 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.spreadsheetml.sheet |
| File info: | Microsoft Excel 2007+ |
| MD5: | 42E77C024B439F9820FF84E1866DA10B |
| SHA1: | CB1268FF36F8297664D2C6775C7A0F2B4CCF6B9D |
| SHA256: | 3E1B07B1C94C627F4E3511991A7F488A34A88F6409E1AC74437AE63AE8040A86 |
| SSDEEP: | 6144:Af/hhhhaRtihhu93HmthKcBdHHts5whVSgftCbg6SC1f8pCd9TvJKI1rw8asjLEO:wIhKsjYE9H |
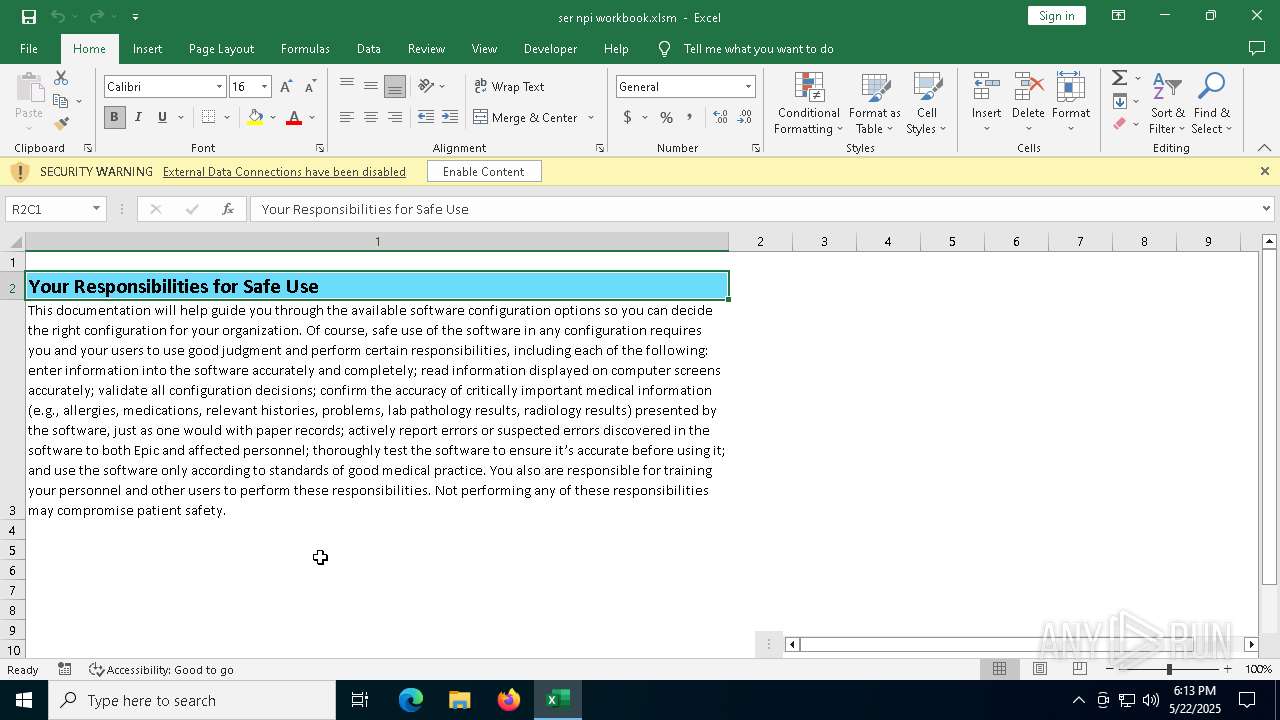
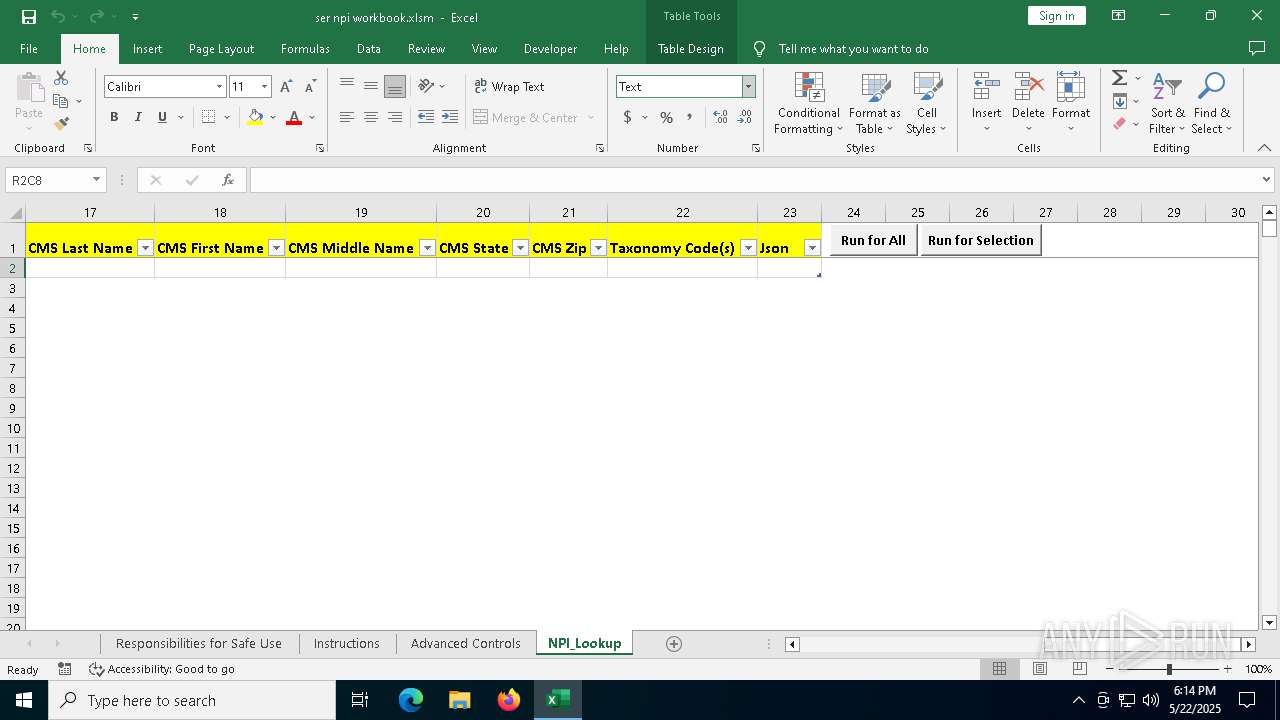
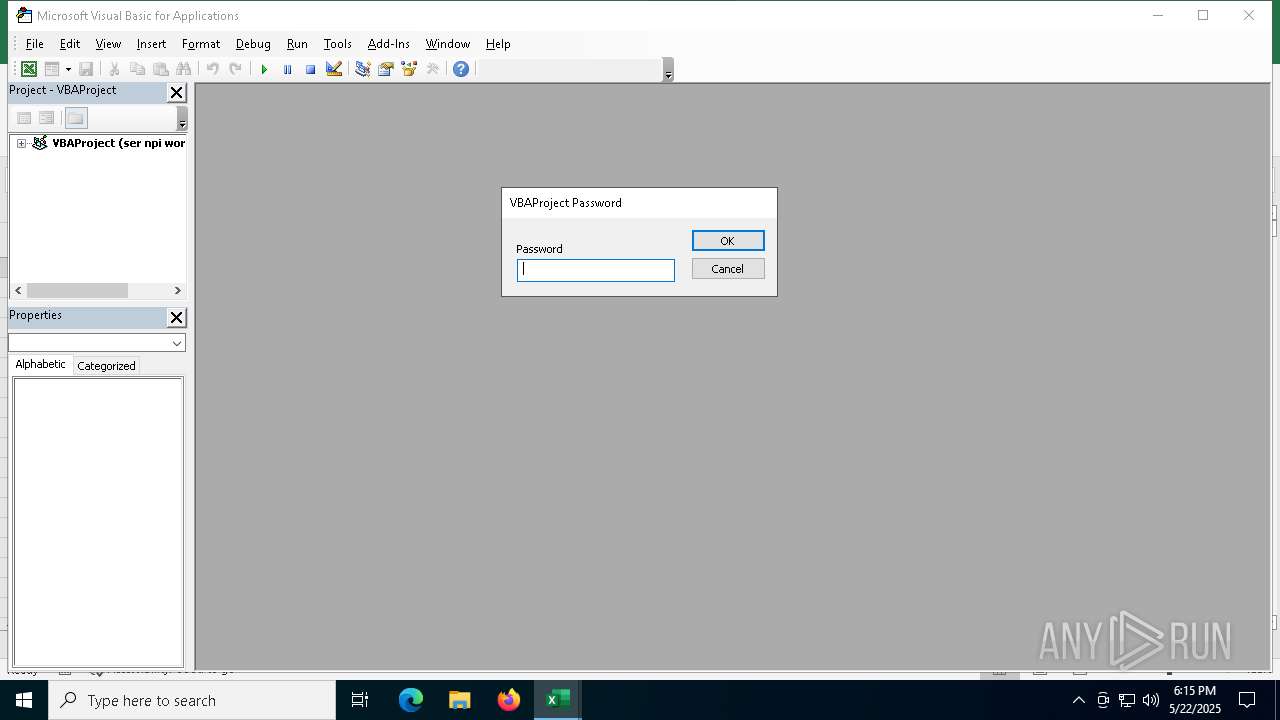
MALICIOUS
Unusual execution from MS Office
- EXCEL.EXE (PID: 5512)
Uses sleep, probably for evasion (MACROS)
- EXCEL.EXE (PID: 5512)
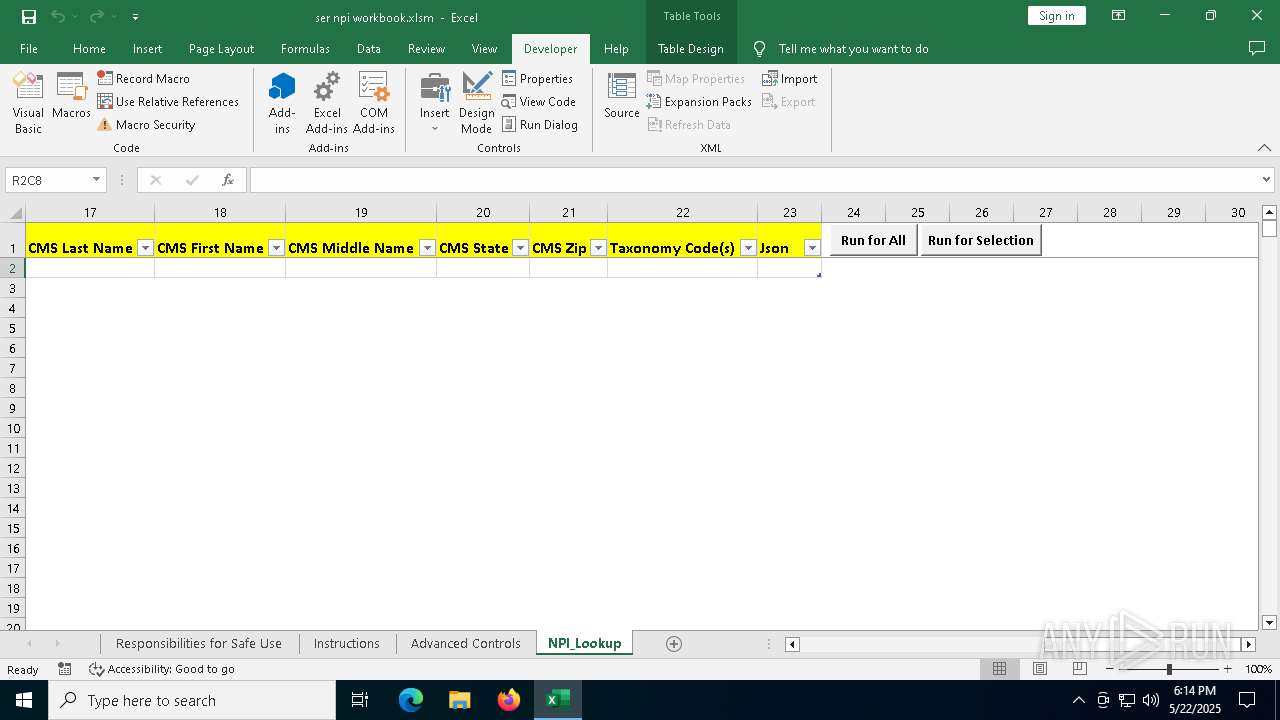
SUSPICIOUS
Runs shell command (SCRIPT)
- EXCEL.EXE (PID: 5512)
Sets XML DOM element text (SCRIPT)
- splwow64.exe (PID: 5740)
HTML script is executed
- EXCEL.EXE (PID: 5512)
INFO
Reads the software policy settings
- slui.exe (PID: 2960)
- slui.exe (PID: 3896)
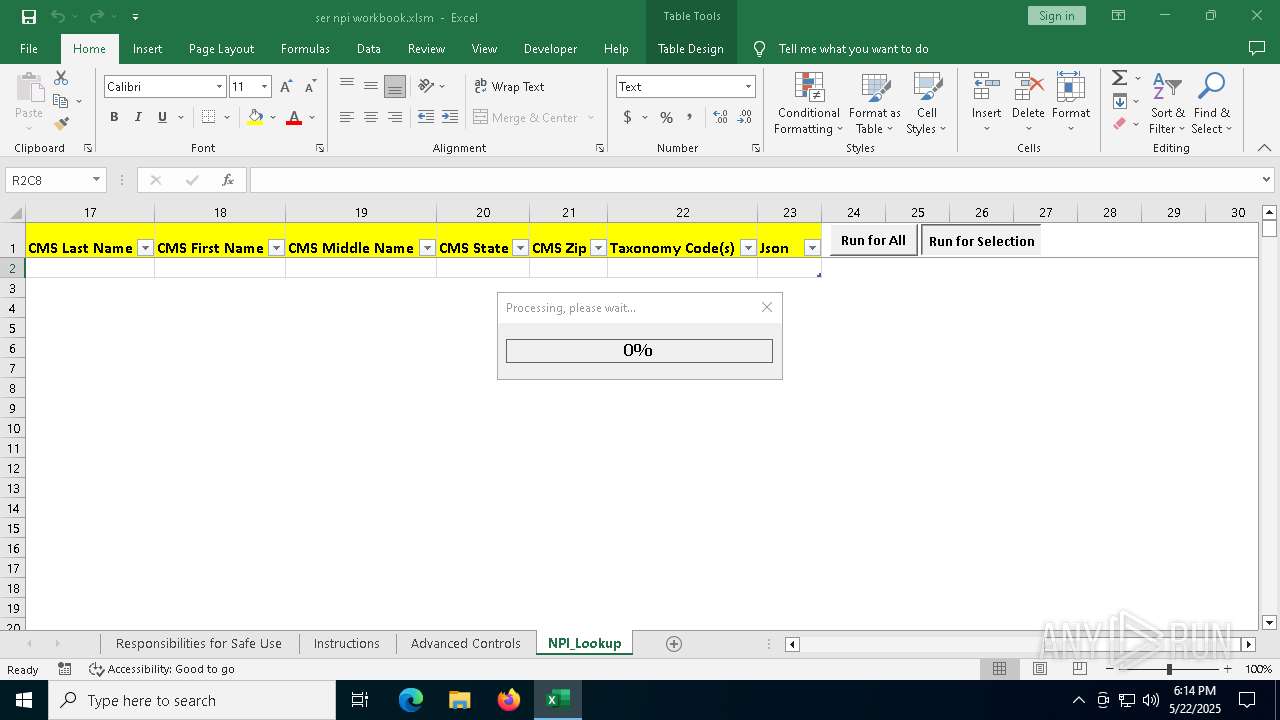
Manual execution by a user
- EXCEL.EXE (PID: 5512)
Checks proxy server information
- slui.exe (PID: 3896)
- mshta.exe (PID: 2236)
- mshta.exe (PID: 1764)
Reads Internet Explorer settings
- mshta.exe (PID: 1764)
- mshta.exe (PID: 2236)
Reads security settings of Internet Explorer
- splwow64.exe (PID: 5740)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xlam | | | Excel Macro-enabled Open XML add-in (42.4) |
|---|---|---|
| .xlsm | | | Excel Microsoft Office Open XML Format document (with Macro) (29.2) |
| .xlsx | | | Excel Microsoft Office Open XML Format document (17.3) |
| .zip | | | Open Packaging Conventions container (8.9) |
| .zip | | | ZIP compressed archive (2) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x4f36ce96 |
| ZipCompressedSize: | 544 |
| ZipUncompressedSize: | 3109 |
| ZipFileName: | [Content_Types].xml |
XML
| Application: | Microsoft Excel |
|---|---|
| DocSecurity: | None |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: |
|
| Company: | Epic |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16.03 |
| LastModifiedBy: | Ryan Muckel |
| LastPrinted: | 2015:11:11 21:20:41Z |
| CreateDate: | 2013:08:07 22:15:51Z |
| ModifyDate: | 2020:04:03 14:02:08Z |
| ContentStatus: | Release |
XMP
| Title: | SER_NPI_Workbook |
|---|---|
| Creator: | Epic |
Total processes
148
Monitored processes
11
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1244 | "C:\Program Files\Microsoft Office\Root\Office16\EXCEL.EXE" "C:\Users\admin\Desktop\ser npi workbook.xlsm.xlsx" | C:\Program Files\Microsoft Office\root\Office16\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 1764 | "C:\WINDOWS\syswow64\mshta.exe" about:"<head><script>moveTo(-32000,-32000);document.title='x86Host'</script><hta:application showintaskbar=no /><object id='shell' classid='clsid:8856F961-340A-11D0-A96B-00C04FD705A2'><param name=RegisterAsBrowser value=1></object><script>shell.putproperty('{86DAD60B-18E1-4178-B727-A4F4E21A3FAC}',document.parentWindow);</script></head>" | C:\Windows\SysWOW64\mshta.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2088 | "C:\WINDOWS\syswow64\mshta.exe" about:"<head><script>moveTo(-32000,-32000);document.title='x86Host'</script><hta:application showintaskbar=no /><object id='shell' classid='clsid:8856F961-340A-11D0-A96B-00C04FD705A2'><param name=RegisterAsBrowser value=1></object><script>shell.putproperty('{4B87C90F-D3C2-439D-A819-4F32E5AC6FF7}',document.parentWindow);</script></head>" | C:\Windows\SysWOW64\mshta.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2236 | "C:\WINDOWS\syswow64\mshta.exe" about:"<head><script>moveTo(-32000,-32000);document.title='x86Host'</script><hta:application showintaskbar=no /><object id='shell' classid='clsid:8856F961-340A-11D0-A96B-00C04FD705A2'><param name=RegisterAsBrowser value=1></object><script>shell.putproperty('{17E9B6CD-26D5-46B6-89C1-5CF8095FFA51}',document.parentWindow);</script></head>" | C:\Windows\SysWOW64\mshta.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2564 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2796 | "C:\WINDOWS\syswow64\mshta.exe" about:"<head><script>moveTo(-32000,-32000);document.title='x86Host'</script><hta:application showintaskbar=no /><object id='shell' classid='clsid:8856F961-340A-11D0-A96B-00C04FD705A2'><param name=RegisterAsBrowser value=1></object><script>shell.putproperty('{530706B4-7CF6-4356-884F-B87FCC29F45D}',document.parentWindow);</script></head>" | C:\Windows\SysWOW64\mshta.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2960 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3896 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4016 | "C:\WINDOWS\syswow64\mshta.exe" about:"<head><script>moveTo(-32000,-32000);document.title='x86Host'</script><hta:application showintaskbar=no /><object id='shell' classid='clsid:8856F961-340A-11D0-A96B-00C04FD705A2'><param name=RegisterAsBrowser value=1></object><script>shell.putproperty('{60EECB6F-F04D-4BD0-85CC-59DD6D9FE7C0}',document.parentWindow);</script></head>" | C:\Windows\SysWOW64\mshta.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5512 | "C:\Program Files\Microsoft Office\Root\Office16\EXCEL.EXE" "C:\Users\admin\Desktop\ser npi workbook.xlsm" | C:\Program Files\Microsoft Office\root\Office16\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Version: 16.0.16026.20146 Modules
| |||||||||||||||
Total events
26 236
Read events
24 563
Write events
1 528
Delete events
145
Modification events
| (PID) Process: | (1244) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\EXCEL\1244 |
| Operation: | write | Name: | 0 |
Value: 0B0E10489288955851EA48B4595B3DBFC730B5230046A08FE9F9D0E8F2ED016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DC2190000C91003783634C511DC09D2120965007800630065006C002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (1244) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (1244) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
| (PID) Process: | (1244) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 2 | |||
| (PID) Process: | (1244) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 2 | |||
| (PID) Process: | (1244) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | it-it |
Value: 2 | |||
| (PID) Process: | (1244) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ja-jp |
Value: 2 | |||
| (PID) Process: | (1244) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ko-kr |
Value: 2 | |||
| (PID) Process: | (1244) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | pt-br |
Value: 2 | |||
| (PID) Process: | (1244) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ru-ru |
Value: 2 | |||
Executable files
1
Suspicious files
37
Text files
66
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1244 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\FontCache\4\Catalog\ListAll.Json | binary | |
MD5:CFD54484BBCCD842CE5113068C419A8A | SHA256:4FEE36BCBAB47965FD07134DE0BC666ECE4041CD1495D0107B468630BF6ED571 | |||
| 1244 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\Personalization\Governance\Anonymous\floodgatecampaigns.json.tmp | binary | |
MD5:D0954EC2DCFF4C4FE7159ECEC2B6F15B | SHA256:14E3E1D6FDD6BE13D78BE033F038EECA49484866365C30CBCF3833B99F02D33D | |||
| 1244 | EXCEL.EXE | C:\Users\admin\Desktop\~$ser npi workbook.xlsm.xlsx | binary | |
MD5:21E5D64E6DD2C94C577A61B0A25DE7A4 | SHA256:657F0604A7C1F6CFDC4E8A224F59BD6E1900A4A4DD8B3F61A20F67DEBE41F209 | |||
| 1244 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\Personalization\Governance\Anonymous\floodgatecampaigns.json | binary | |
MD5:D0954EC2DCFF4C4FE7159ECEC2B6F15B | SHA256:14E3E1D6FDD6BE13D78BE033F038EECA49484866365C30CBCF3833B99F02D33D | |||
| 1244 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_363582827213C09529A76F35FB615187 | binary | |
MD5:BF631EEB89ECFEEDCD321BB33B7F3292 | SHA256:0AE02D8E5AF1EB8AFFD267C1C87AC60B287F65F94C0F21546F9F0A376CAD8B90 | |||
| 1244 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\excel.exe_Rules.xml | xml | |
MD5:13AF026BB17E87B1A24C00E8295447B0 | SHA256:4695B860F6568E9EDDC220E4C80C848D5B6BE780C9A4A31FAD4D878E098FF8DB | |||
| 1244 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\DTS\en-US{6237D7B6-51B3-4C18-BD8B-25D0C654C2F0}\{450A3B26-17F9-4E44-B5D6-A9984A2D2367}mt16400647.png | image | |
MD5:D3590428E83DC27B626978EC0867477A | SHA256:6B7382E1BF3F58C62F21300DA74F13C649C46BC0FC244188371BA55C56B6117D | |||
| 1244 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\DTS\en-US{6237D7B6-51B3-4C18-BD8B-25D0C654C2F0}\{41E9ECAB-4DE5-4E75-9F63-24EC57935028}mt67739505.png | image | |
MD5:FE238D4D994149381553BA0A5CD17B17 | SHA256:F25507CB3FAE7439117F05285EC6DE20A5A7356FAE74F5F935D31A63430598DA | |||
| 1244 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_363582827213C09529A76F35FB615187 | binary | |
MD5:EFE306A476DA27BCD3B203A60CEBB4E0 | SHA256:BC246245AF79B1D8FC564F31515705793905F9AD5EE99968AF6961A9344506F2 | |||
| 1244 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\56a61aeb75d8f5be186c26607f4bb213abe7c5ec.tbres | binary | |
MD5:632ABC8C3745DB17D99F7F30F57B2AFE | SHA256:1A4DE3529A6704212B5958DCDD424C85C5D3825E7092A13DF963D150FFD52B3C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
105
DNS requests
32
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6512 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5512 | EXCEL.EXE | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6512 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.169:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1244 | EXCEL.EXE | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.169:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
roaming.officeapps.live.com |
| whitelisted |