| File name: | Procmon64.exe |
| Full analysis: | https://app.any.run/tasks/49623ed9-34e9-411c-97d4-43e5ff7245ed |
| Verdict: | Malicious activity |
| Analysis date: | July 07, 2024, 12:28:54 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows |
| MD5: | 223B222CE387A7F446D49A1EE9B572BB |
| SHA1: | 8ED888A02861142E5EB576385568C2BA0DDD8589 |
| SHA256: | 3E15995894F38B2EEAD95F7FF714585471F34F3AF3D8F50A7F83344781502468 |
| SSDEEP: | 49152:X+i33dwHZTYitAQ8pyH+Cw+upl/HTttdVcPSX4eYNp0ko/NSHHcIo9q:NdwWNpIbsplPTttdVQou89q |
MALICIOUS
Drops the executable file immediately after the start
- Procmon64.exe (PID: 5332)
- Procmon64.exe (PID: 2928)
Creates a writable file in the system directory
- Procmon64.exe (PID: 2928)
SUSPICIOUS
Reads security settings of Internet Explorer
- Procmon64.exe (PID: 5332)
Reads the date of Windows installation
- Procmon64.exe (PID: 5332)
Application launched itself
- Procmon64.exe (PID: 5332)
Creates or modifies Windows services
- Procmon64.exe (PID: 2928)
Drops a system driver (possible attempt to evade defenses)
- Procmon64.exe (PID: 2928)
Executable content was dropped or overwritten
- Procmon64.exe (PID: 2928)
Creates files in the driver directory
- Procmon64.exe (PID: 2928)
INFO
Reads product name
- Procmon64.exe (PID: 5332)
Process checks whether UAC notifications are on
- Procmon64.exe (PID: 5332)
Reads the computer name
- Procmon64.exe (PID: 5332)
- Procmon64.exe (PID: 2928)
Checks supported languages
- Procmon64.exe (PID: 5332)
- Procmon64.exe (PID: 2928)
Process checks computer location settings
- Procmon64.exe (PID: 5332)
Reads Environment values
- Procmon64.exe (PID: 5332)
Reads the time zone
- Procmon64.exe (PID: 2928)
Reads CPU info
- Procmon64.exe (PID: 2928)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:06:20 16:50:00+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.39 |
| CodeSize: | 979456 |
| InitializedDataSize: | 1231872 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xba150 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.1.0.0 |
| ProductVersionNumber: | 4.1.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Sysinternals - www.sysinternals.com |
| FileDescription: | Process Monitor |
| FileVersion: | 4.01 |
| InternalName: | Process Monitor |
| LegalCopyright: | Copyright © 1996-2024 Mark Russinovich |
| OriginalFileName: | Process Monitor |
| ProductName: | Sysinternals Procmon |
| ProductVersion: | 4.01 |
Total processes
143
Monitored processes
2
Malicious processes
2
Suspicious processes
0
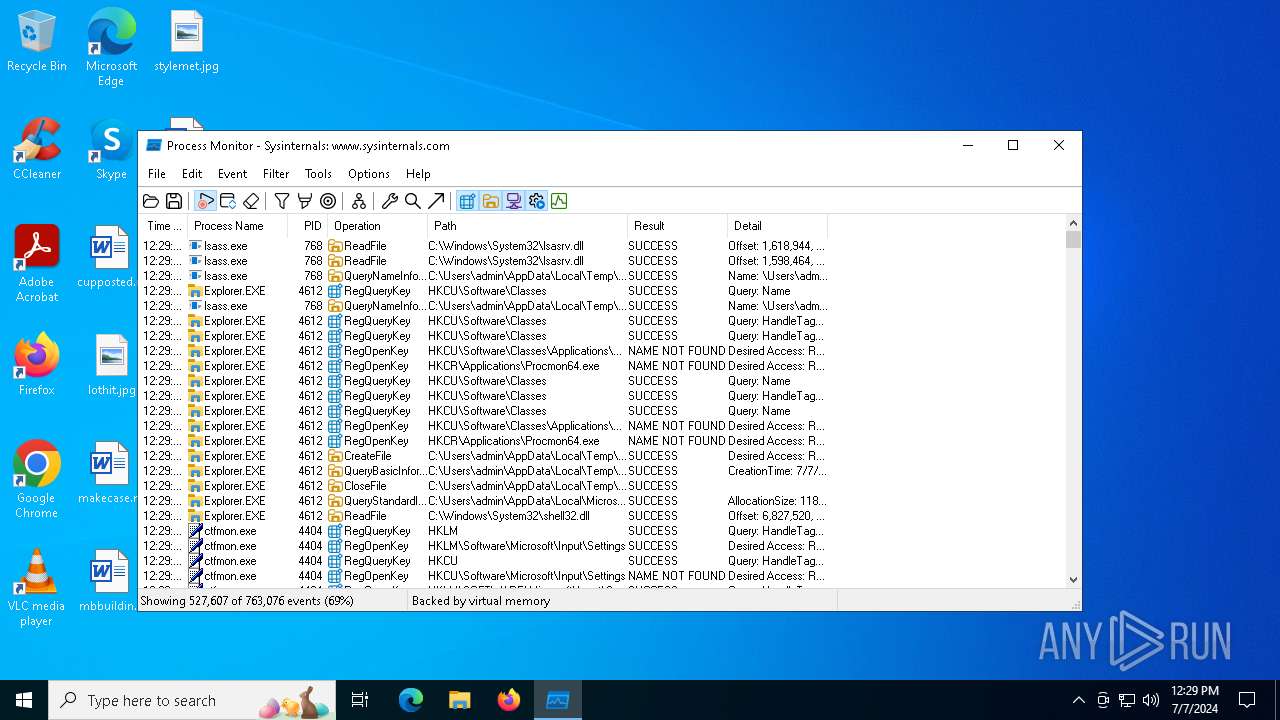
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2928 | "C:\Users\admin\AppData\Local\Temp\Procmon64.exe" | C:\Users\admin\AppData\Local\Temp\Procmon64.exe | Procmon64.exe | ||||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: HIGH Description: Process Monitor Version: 4.01 Modules
| |||||||||||||||
| 5332 | "C:\Users\admin\AppData\Local\Temp\Procmon64.exe" | C:\Users\admin\AppData\Local\Temp\Procmon64.exe | — | explorer.exe | |||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: MEDIUM Description: Process Monitor Version: 4.01 Modules
| |||||||||||||||
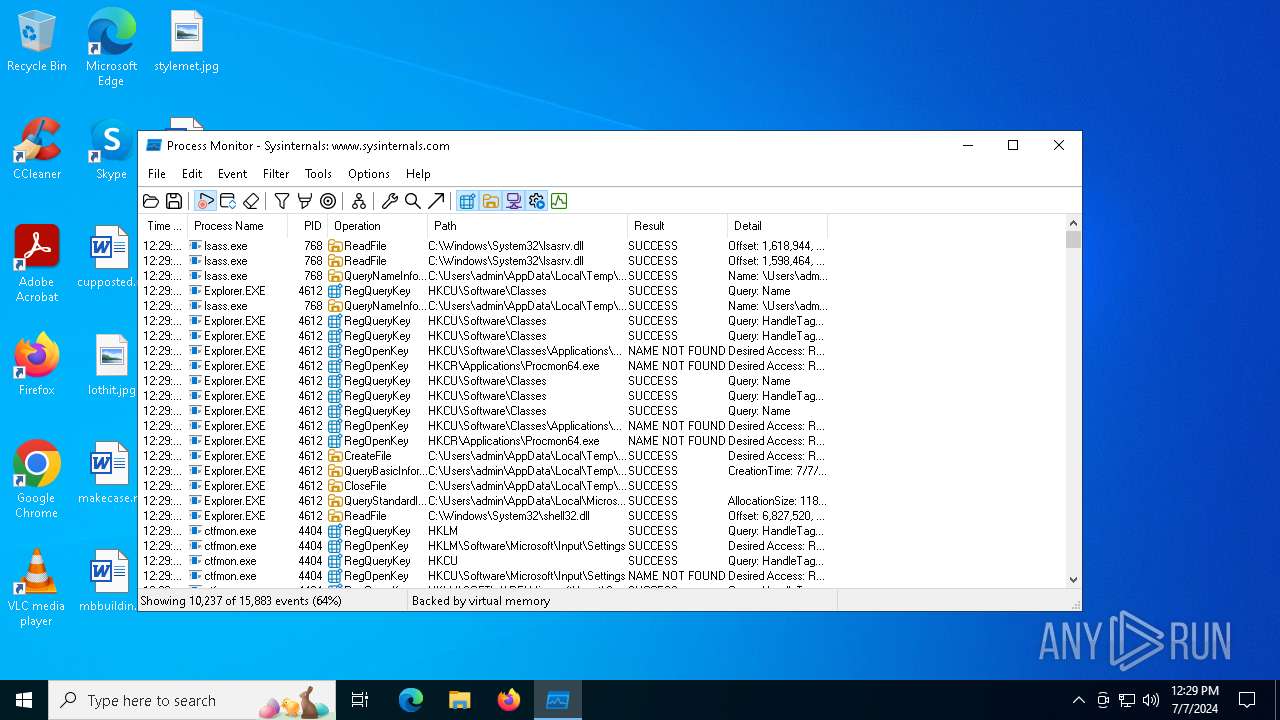
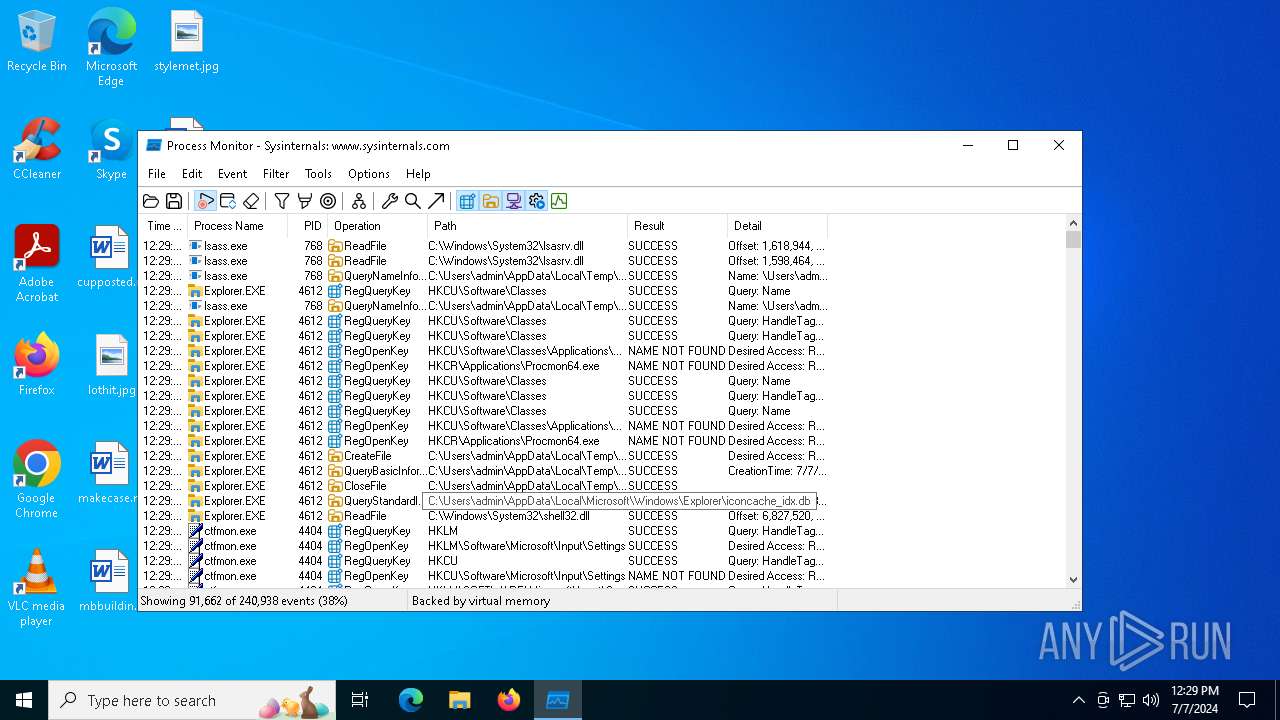
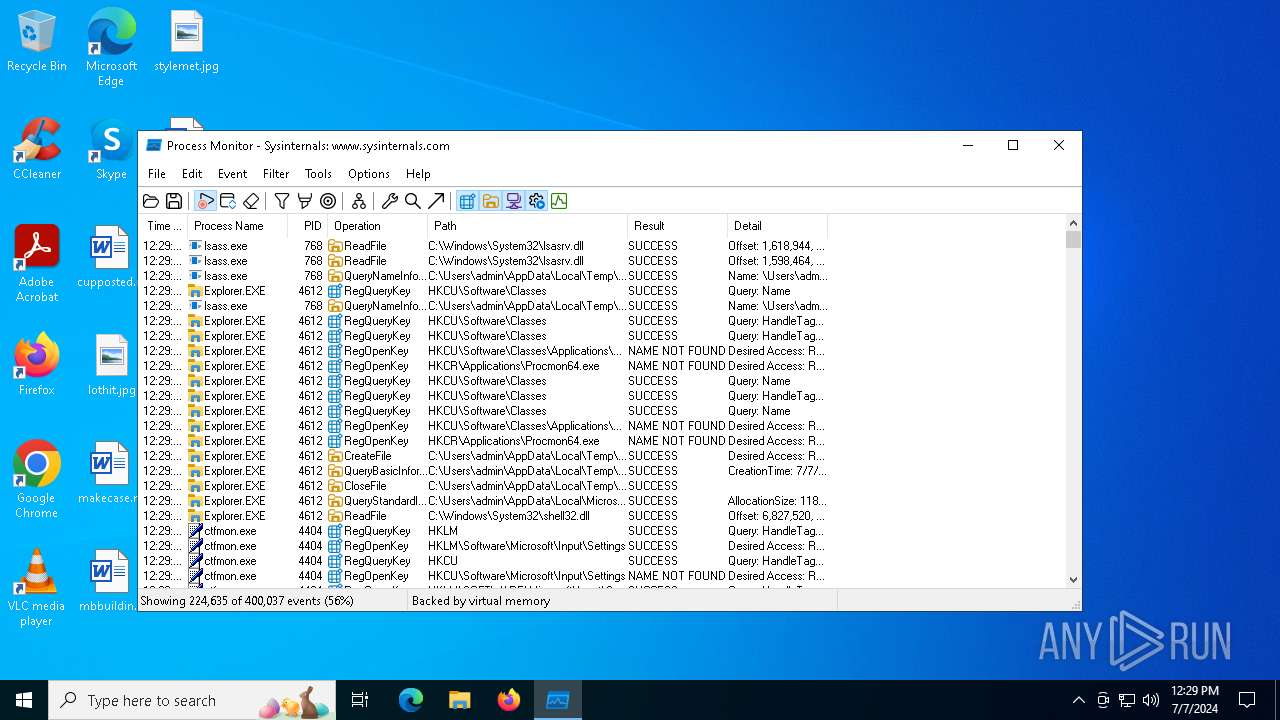
Total events
4 279
Read events
4 256
Write events
19
Delete events
4
Modification events
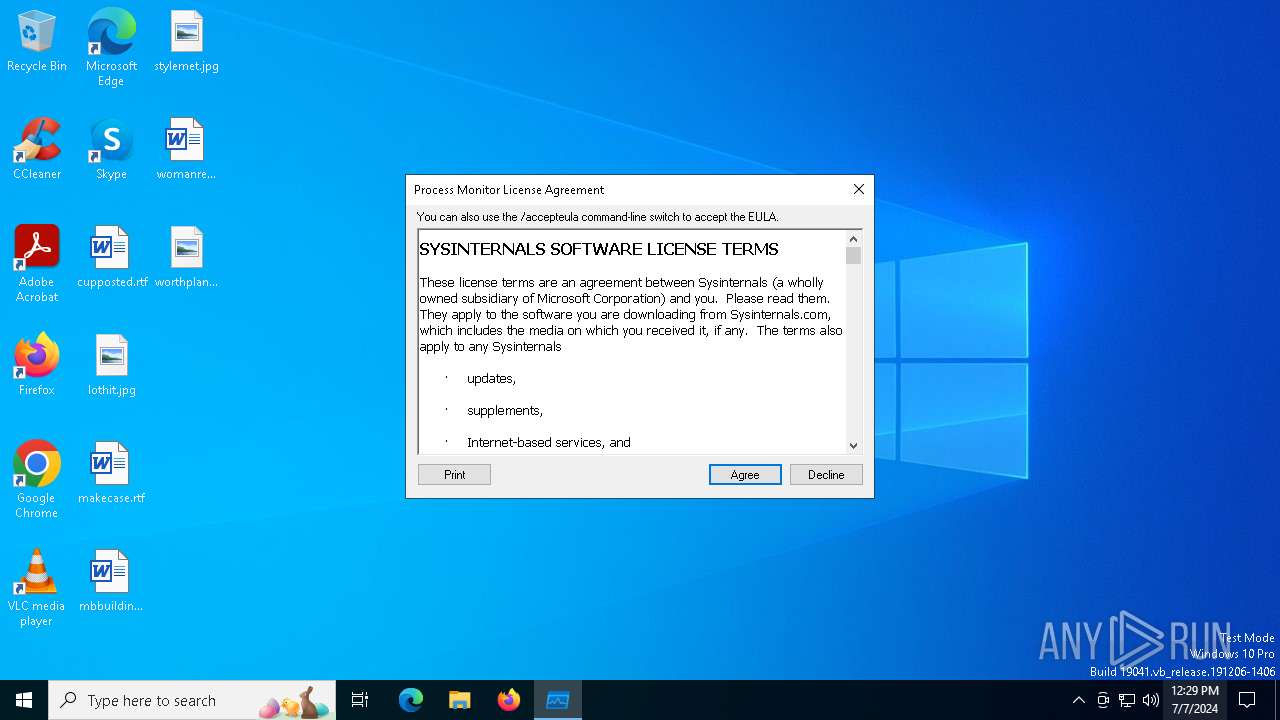
| (PID) Process: | (5332) Procmon64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Sysinternals\Process Monitor |
| Operation: | write | Name: | EulaAccepted |
Value: 1 | |||
| (PID) Process: | (5332) Procmon64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (5332) Procmon64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (5332) Procmon64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (5332) Procmon64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2928) Procmon64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Sysinternals\Process Monitor |
| Operation: | write | Name: | EulaAccepted |
Value: 1 | |||
| (PID) Process: | (2928) Procmon64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 17 | |||
| (PID) Process: | (2928) Procmon64.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\PROCMON24 |
| Operation: | write | Name: | Type |
Value: 2 | |||
| (PID) Process: | (2928) Procmon64.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\PROCMON24 |
| Operation: | write | Name: | ErrorControl |
Value: 1 | |||
| (PID) Process: | (2928) Procmon64.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\PROCMON24 |
| Operation: | write | Name: | Start |
Value: 3 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2928 | Procmon64.exe | C:\WINDOWS\system32\Drivers\PROCMON24.SYS | executable | |
MD5:03480D56A090F0CD397677251F747929 | SHA256:2A5A61BDA7B7B5D6E69B588FFBF625A1534D5A94F39801F6E0376774AA103DD9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
72
DNS requests
36
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4452 | svchost.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
4636 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
4656 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | unknown |
4452 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
6716 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
6716 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
2328 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
3516 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4452 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2476 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2248 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2168 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4452 | svchost.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
4452 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.2:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
255.100.168.192.in-addr.arpa |
| unknown |
250.255.255.239.in-addr.arpa |
| unknown |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
158.240.127.40.in-addr.arpa |
| unknown |
2.100.168.192.in-addr.arpa |
| unknown |
3.0.0.0.1.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.2.0.f.f.ip6.arpa |
| unknown |
252.0.0.224.in-addr.arpa |
| unknown |
12.241.16.2.in-addr.arpa |
| unknown |