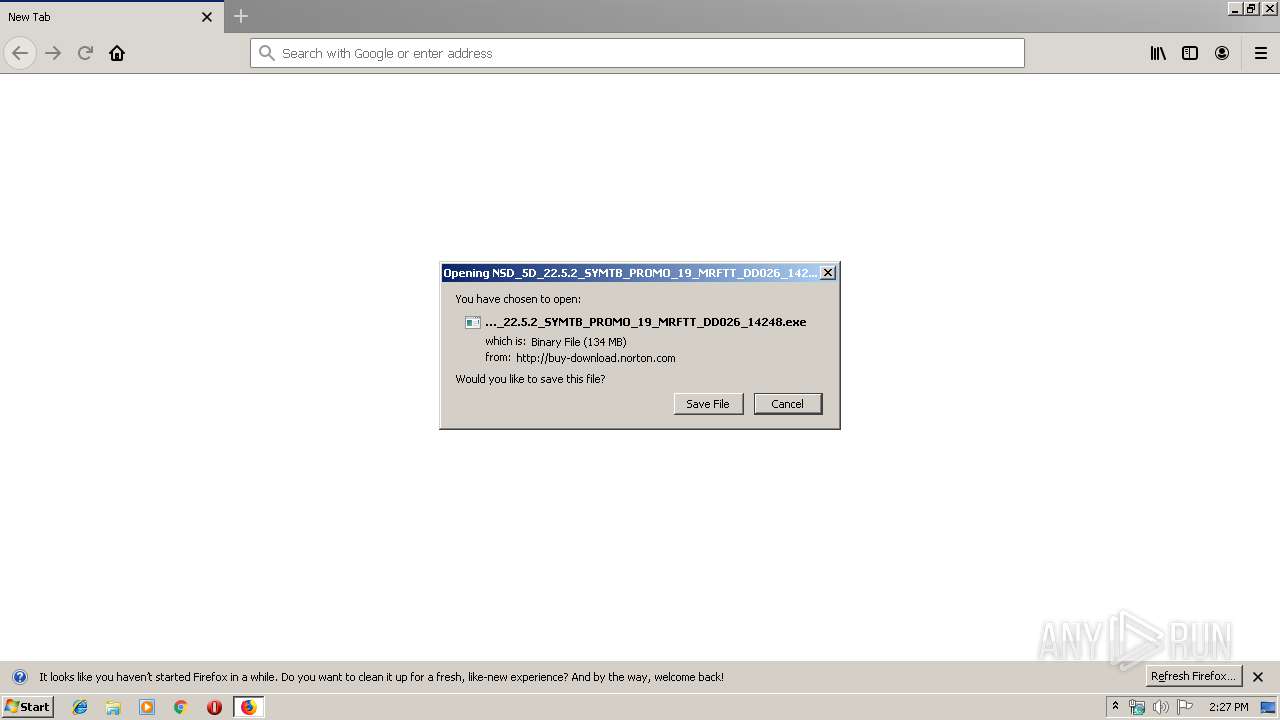
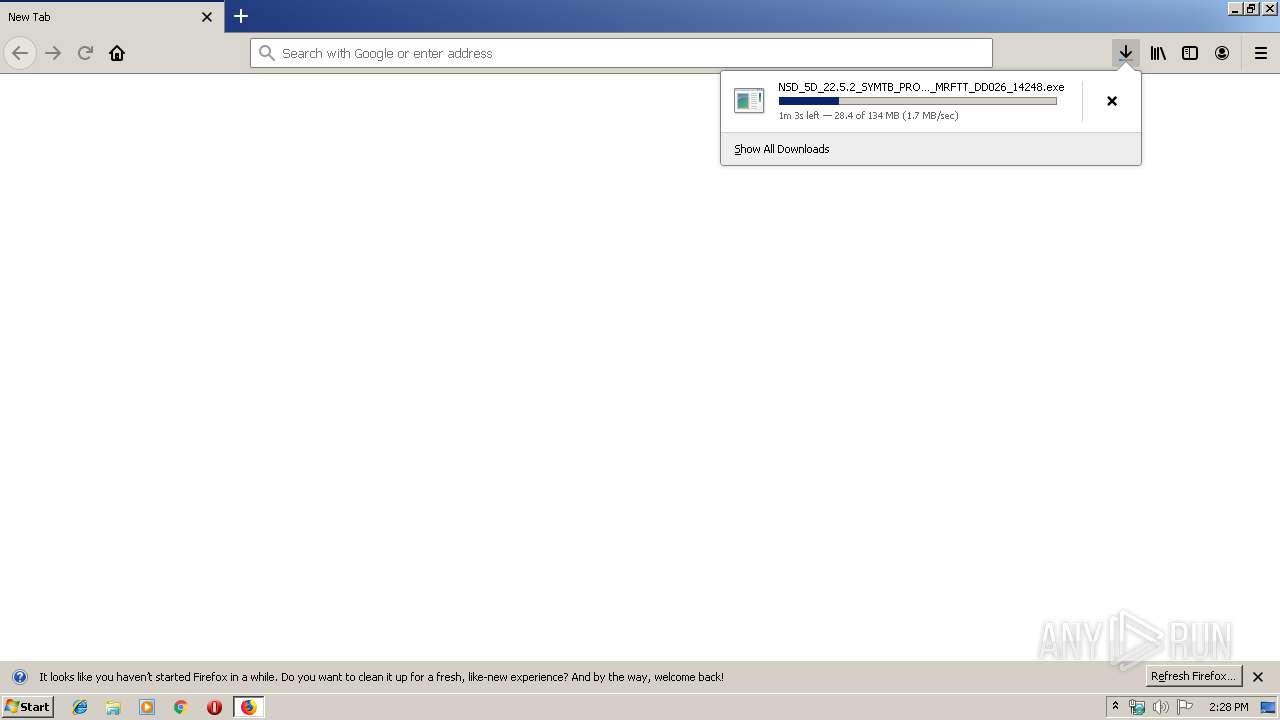
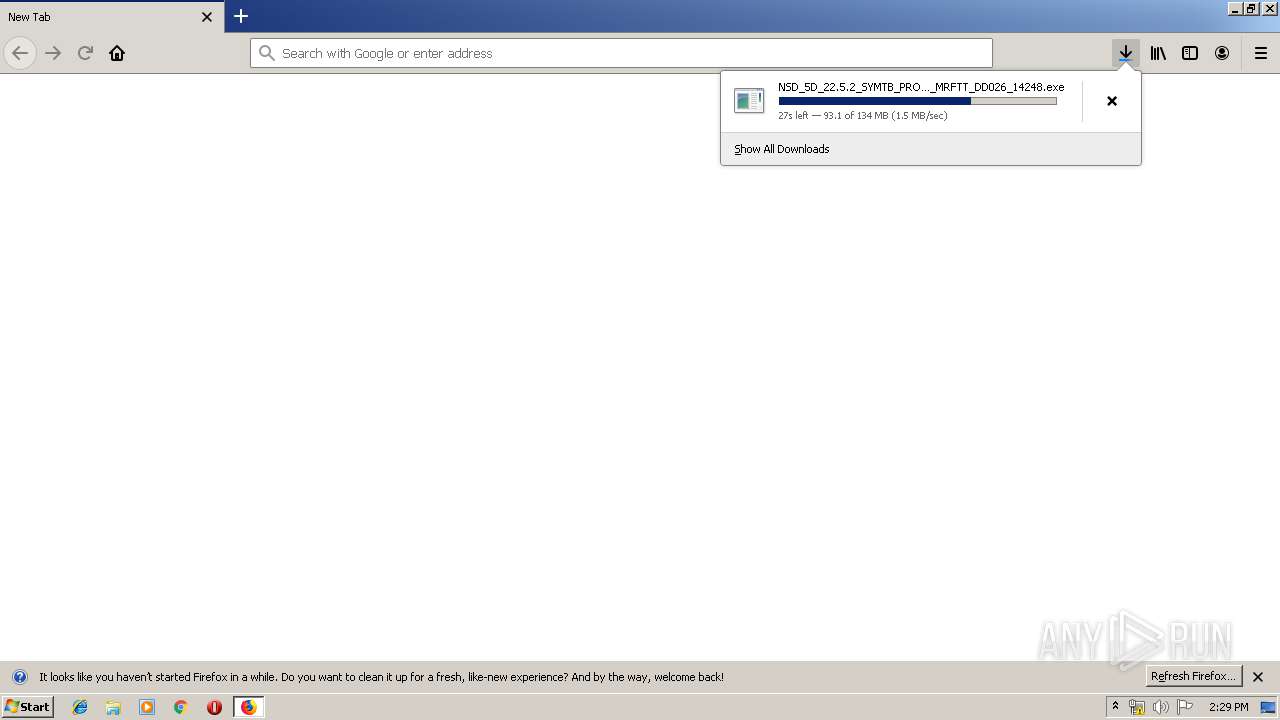
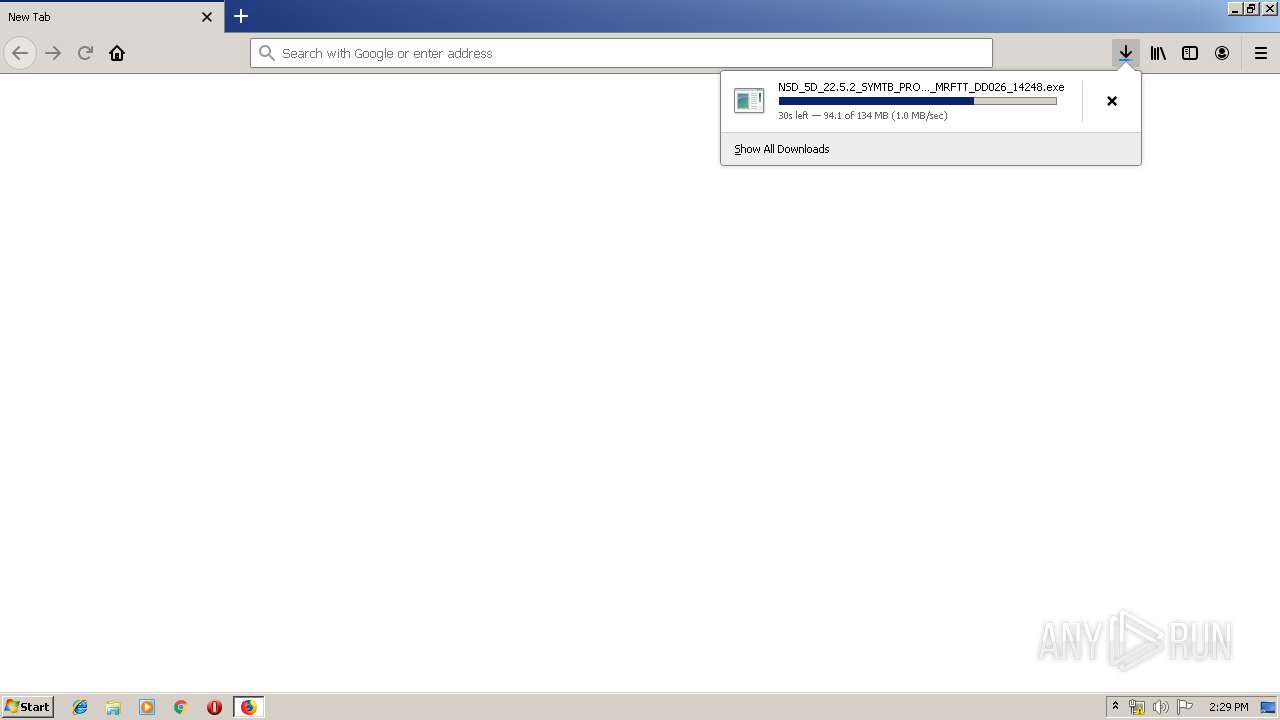
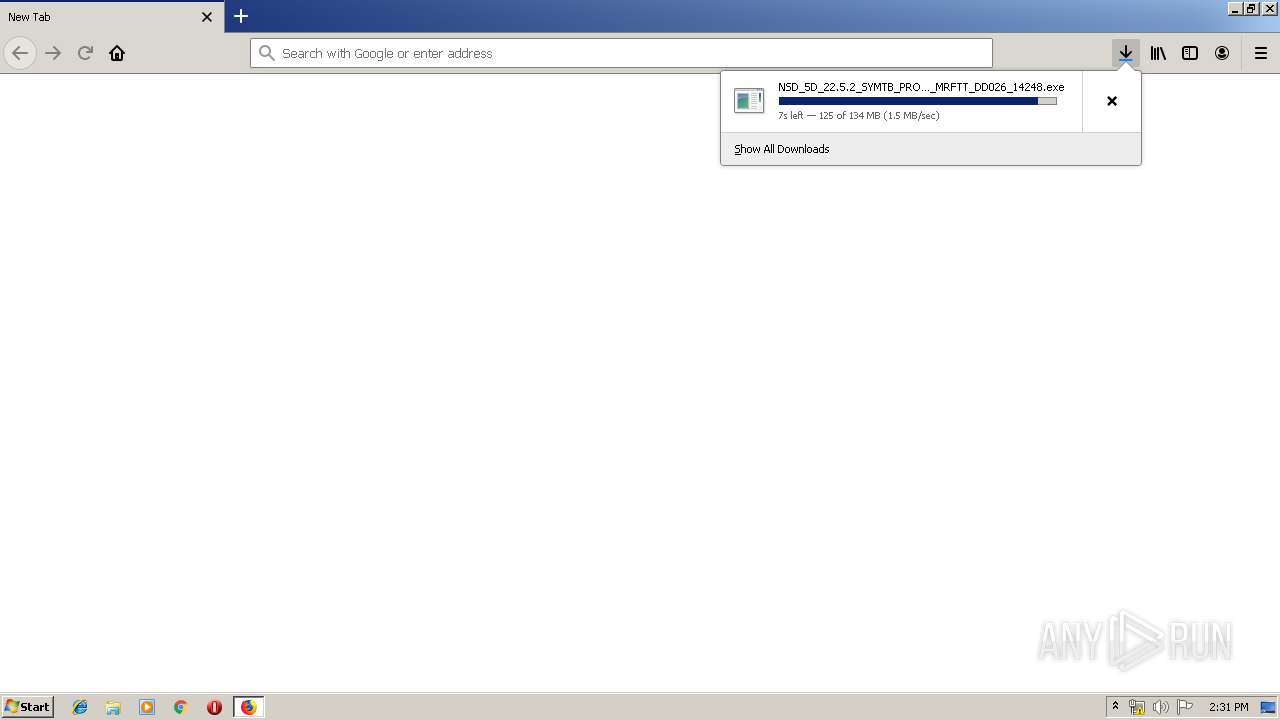
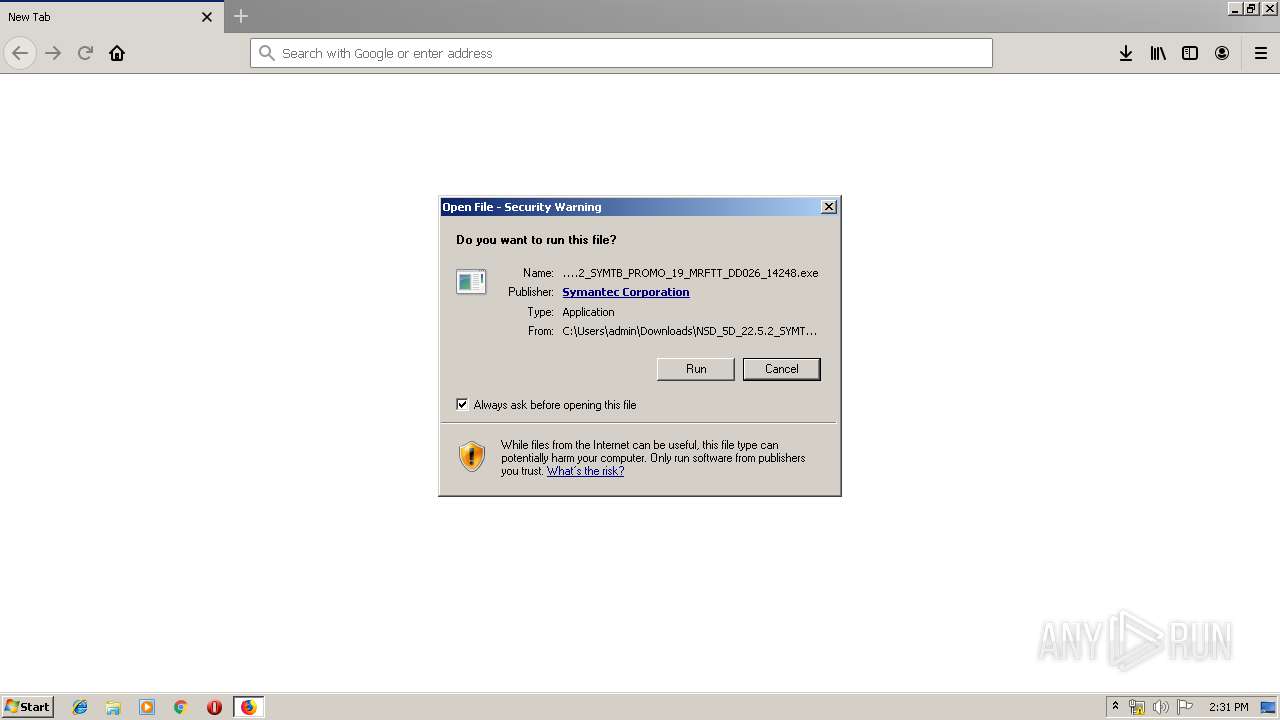
| URL: | http://buy-download.norton.com/downloads/OEM/22.5.2/NSD/5D/NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe |
| Full analysis: | https://app.any.run/tasks/3ff05b3d-c0c7-49cc-b4a7-9a9b2ed49972 |
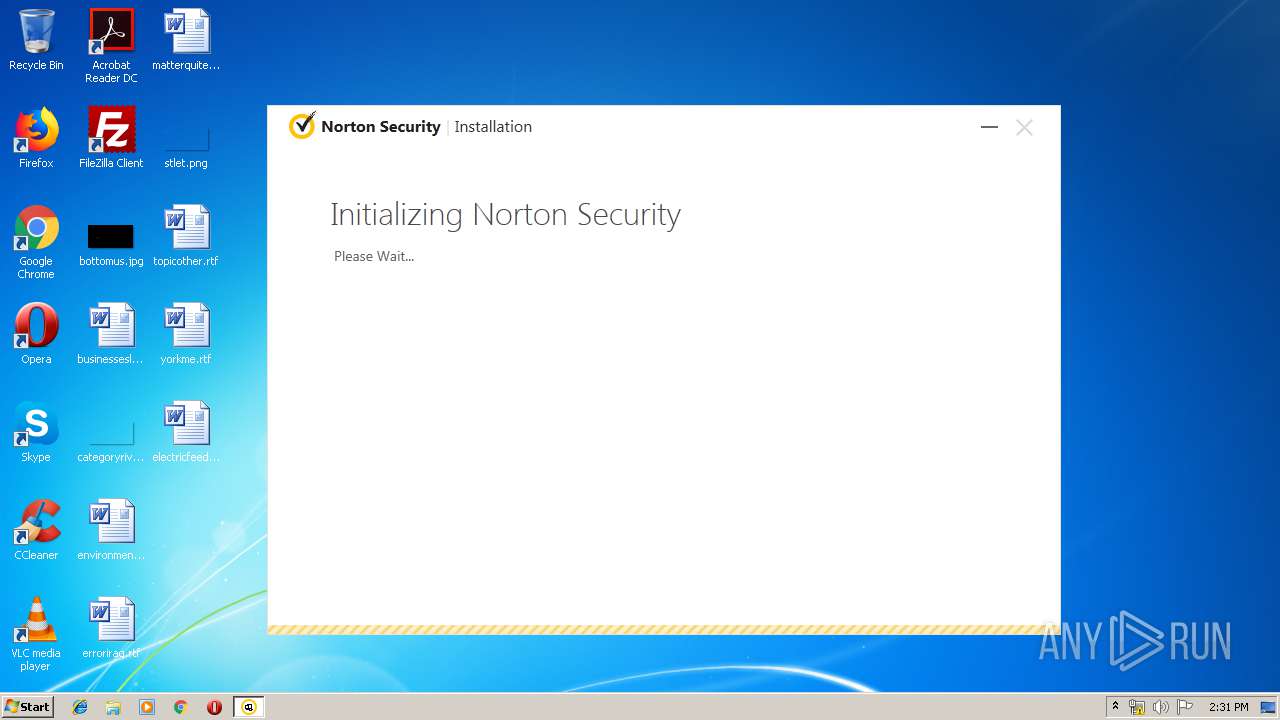
| Verdict: | Malicious activity |
| Analysis date: | November 12, 2019, 14:27:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7A641955F783DCE0563A3127EFECC282 |
| SHA1: | A45676EF090193835D37E70C58EA32A087B36064 |
| SHA256: | 3E12C157CFAF378BBACD7DBFA053F8B6000A48951F6B462341AC1B9C02BC821B |
| SSDEEP: | 3:N1KcJI84Jl+BQyWKXKbHEKrSat4+sne3LD3CD6URfACn:CcJI3/majXPrXXCD6IfACn |
MALICIOUS
Application was dropped or rewritten from another process
- NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe (PID: 392)
- NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe (PID: 3772)
- EFAInst.exe (PID: 3948)
- BHCA.exe (PID: 3028)
- coInst.exe (PID: 3060)
- coInst.exe (PID: 1712)
- buIH.exe (PID: 2728)
- Sevinst.exe (PID: 3092)
- InstCA.exe (PID: 2128)
- NS.exe (PID: 1012)
- cltLMH.exe (PID: 2088)
- NS.exe (PID: 3376)
Loads dropped or rewritten executable
- NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe (PID: 3772)
- explorer.exe (PID: 352)
- SearchProtocolHost.exe (PID: 784)
- buIH.exe (PID: 2728)
- coInst.exe (PID: 3060)
- coInst.exe (PID: 1712)
- EFAInst.exe (PID: 3948)
- SymIMIns.exe (PID: 3780)
- RuleUp.exe (PID: 1764)
- tuIH.exe (PID: 328)
- InstCA.exe (PID: 2128)
- NS.exe (PID: 1012)
- cltLMH.exe (PID: 2088)
- NS.exe (PID: 3376)
Changes the autorun value in the registry
- NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe (PID: 3772)
Loads the Task Scheduler COM API
- tuIH.exe (PID: 328)
- InstCA.exe (PID: 2128)
- NS.exe (PID: 1012)
SUSPICIOUS
Creates files in the driver directory
- NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe (PID: 3772)
- Sevinst.exe (PID: 3092)
Creates a software uninstall entry
- NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe (PID: 3772)
- Sevinst.exe (PID: 3092)
Creates files in the Windows directory
- NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe (PID: 3772)
- Sevinst.exe (PID: 3092)
- NS.exe (PID: 1012)
Creates COM task schedule object
- NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe (PID: 3772)
Executable content was dropped or overwritten
- firefox.exe (PID: 3744)
- Sevinst.exe (PID: 3092)
- NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe (PID: 3772)
- NS.exe (PID: 1012)
Creates files in the program directory
- firefox.exe (PID: 3744)
- buIH.exe (PID: 2728)
- BHCA.exe (PID: 3028)
- EFAInst.exe (PID: 3948)
- Sevinst.exe (PID: 3092)
- SymIMIns.exe (PID: 3780)
- RuleUp.exe (PID: 1764)
- tuIH.exe (PID: 328)
- InstCA.exe (PID: 2128)
- NS.exe (PID: 1012)
- NS.exe (PID: 3376)
- NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe (PID: 3772)
Cleans NTFS data-stream (Zone Identifier)
- firefox.exe (PID: 3744)
Application launched itself
- NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe (PID: 392)
- NS.exe (PID: 1012)
Creates or modifies windows services
- NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe (PID: 3772)
Writes to a desktop.ini file (may be used to cloak folders)
- NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe (PID: 3772)
Executed as Windows Service
- NS.exe (PID: 1012)
INFO
Reads CPU info
- firefox.exe (PID: 3744)
Application launched itself
- firefox.exe (PID: 1448)
- firefox.exe (PID: 3744)
Reads settings of System Certificates
- firefox.exe (PID: 3744)
- explorer.exe (PID: 352)
- NS.exe (PID: 1012)
Creates files in the user directory
- firefox.exe (PID: 3744)
Reads the hosts file
- NS.exe (PID: 1012)
Reads Microsoft Office registry keys
- NS.exe (PID: 3376)
Dropped object may contain Bitcoin addresses
- NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe (PID: 3772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
67
Monitored processes
24
Malicious processes
10
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 328 | "C:\Program Files\Norton Security\Engine\22.5.4.24\tuIH.exe" /install | C:\Program Files\Norton Security\Engine\22.5.4.24\tuIH.exe | NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe | ||||||||||||
User: admin Company: Symantec Corporation Integrity Level: HIGH Description: Tuneup Install Helper Exit code: 0 Version: 10.0.0.67 Modules
| |||||||||||||||
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 392 | "C:\Users\admin\Downloads\NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe" | C:\Users\admin\Downloads\NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe | — | firefox.exe | |||||||||||
User: admin Company: Symantec Corporation Integrity Level: MEDIUM Description: Norton Security Exit code: 0 Version: 22.5.4.24 Modules
| |||||||||||||||
| 640 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3744.20.1462799792\1399540073" -childID 3 -isForBrowser -prefsHandle 3912 -prefMapHandle 3916 -prefsLen 7195 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3744 "\\.\pipe\gecko-crash-server-pipe.3744" 3928 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 784 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe3_ Global\UsGthrCtrlFltPipeMssGthrPipe3 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Norton Security\Engine\22.5.4.24\NS.exe" /s "NS" /m "C:\Program Files\Norton Security\Engine\22.5.4.24\diMaster.dll" /prefetch:1 | C:\Program Files\Norton Security\Engine\22.5.4.24\NS.exe | services.exe | ||||||||||||
User: SYSTEM Company: Symantec Corporation Integrity Level: SYSTEM Description: Norton Security Exit code: 0 Version: 13.0.2.6 Modules
| |||||||||||||||
| 1448 | "C:\Program Files\Mozilla Firefox\firefox.exe" "http://buy-download.norton.com/downloads/OEM/22.5.2/NSD/5D/NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1712 | "C:\Program Files\Norton Security\Engine\22.5.4.24\coInst.exe" /install | C:\Program Files\Norton Security\Engine\22.5.4.24\coInst.exe | — | NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe | |||||||||||
User: admin Company: Symantec Corporation Integrity Level: HIGH Description: coCustomAction Exit code: 0 Version: 2015.5.4.10 Modules
| |||||||||||||||
| 1764 | "C:\Program Files\Norton Security\Engine\22.5.4.24\RuleUp.exe" /install | C:\Program Files\Norton Security\Engine\22.5.4.24\RuleUp.exe | NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe | ||||||||||||
User: admin Company: Symantec Corporation Integrity Level: HIGH Description: Rule database upgrader Executable Exit code: 0 Version: 15.1.0.70 Modules
| |||||||||||||||
| 2088 | scan:b-f+ onlinedefs:0 boot:"*"- file:"%SYSTEMDRIVE%\*"+"%TEMP%"-"%TMP%"- container:"*"+"dxsndb"- containerdepth:8 dataexchange:"%APPDATA%\cltLMH.dxsndb" | C:\PROGRAM FILES\NORTON SECURITY\ENGINE\22.5.4.24\cltLMH.exe | — | NS.exe | |||||||||||
User: SYSTEM Company: Symantec Corporation Integrity Level: SYSTEM Description: Symantec Shared Component Exit code: 0 Version: 15.5.5.4 Modules
| |||||||||||||||
Total events
6 286
Read events
4 646
Write events
1 615
Delete events
25
Modification events
| (PID) Process: | (3744) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: A78A041803000000 | |||
| (PID) Process: | (1448) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: CC80001803000000 | |||
| (PID) Process: | (3744) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (3744) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3744) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | 308046O0NS4N39PO |
Value: 00000000090000000D000000CC190500000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF605D425CD146D50100000000 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000003200000037000000E2DB1200090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000E101CD944A76CC90FF0188E5E101408CFF012DAC977714E3E700408CFF01D8E4E700EDE064777D401800FEFFFFFF8B8D6877108B687701000000010000000000000004E5E700CCE4E700E8E4E7006C878875010000000000000004E5E7007F878875CDBDE5E3000000006CEAE70002000000410037004400320037007D00000000000000D172ACE4E7007800650050E9E70065E18975ADDE8A96FEFFFFFF7F878875F36B8875E186887545B0E5E36CEAE70010000000ED0003003C003E006CEAE70080E9E700000000000000000000000000000008023CE7E7000000080234E5E700000000000000D172040D0000200200000000000060E5E700000000000700000078E5E700140000000000000000002800E82A00070000000010D61A0408D51A047CE5E7003DA96C7600000000FBFFFF7FA0E5E700987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF0000000000000000000000000B391107253911070B391107000000000000000000000000080000002E006C00E72F687711000000B8452B00B0452B0000002800140000000500000054E600007291E1E304E6E70082916C7654E6E70008E6E70027956C76000000008C00FD0330E6E700CD946C768C00FD03DCE6E70000FCFC03E1946C760000000000FCFC03DCE6E70038E6E700090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000E101CD944A76CC90FF0188E5E101408CFF012DAC977714E3E700408CFF01D8E4E700EDE064777D401800FEFFFFFF8B8D6877108B687701000000010000000000000004E5E700CCE4E700E8E4E7006C878875010000000000000004E5E7007F878875CDBDE5E3000000006CEAE70002000000410037004400320037007D00000000000000D172ACE4E7007800650050E9E70065E18975ADDE8A96FEFFFFFF7F878875F36B8875E186887545B0E5E36CEAE70010000000ED0003003C003E006CEAE70080E9E700000000000000000000000000000008023CE7E7000000080234E5E700000000000000D172040D0000200200000000000060E5E700000000000700000078E5E700140000000000000000002800E82A00070000000010D61A0408D51A047CE5E7003DA96C7600000000FBFFFF7FA0E5E700987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF0000000000000000000000000B391107253911070B391107000000000000000000000000080000002E006C00E72F687711000000B8452B00B0452B0000002800140000000500000054E600007291E1E304E6E70082916C7654E6E70008E6E70027956C76000000008C00FD0330E6E700CD946C768C00FD03DCE6E70000FCFC03E1946C760000000000FCFC03DCE6E70038E6E700090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000E101CD944A76CC90FF0188E5E101408CFF012DAC977714E3E700408CFF01D8E4E700EDE064777D401800FEFFFFFF8B8D6877108B687701000000010000000000000004E5E700CCE4E700E8E4E7006C878875010000000000000004E5E7007F878875CDBDE5E3000000006CEAE70002000000410037004400320037007D00000000000000D172ACE4E7007800650050E9E70065E18975ADDE8A96FEFFFFFF7F878875F36B8875E186887545B0E5E36CEAE70010000000ED0003003C003E006CEAE70080E9E700000000000000000000000000000008023CE7E7000000080234E5E700000000000000D172040D0000200200000000000060E5E700000000000700000078E5E700140000000000000000002800E82A00070000000010D61A0408D51A047CE5E7003DA96C7600000000FBFFFF7FA0E5E700987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF0000000000000000000000000B391107253911070B391107000000000000000000000000080000002E006C00E72F687711000000B8452B00B0452B0000002800140000000500000054E600007291E1E304E6E70082916C7654E6E70008E6E70027956C76000000008C00FD0330E6E700CD946C768C00FD03DCE6E70000FCFC03E1946C760000000000FCFC03DCE6E70038E6E700 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000003200000037000000E2DB1200090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000E101CD944A76CC90FF0188E5E101408CFF012DAC977714E3E700408CFF01D8E4E700EDE064777D401800FEFFFFFF8B8D6877108B687701000000010000000000000004E5E700CCE4E700E8E4E7006C878875010000000000000004E5E7007F878875CDBDE5E3000000006CEAE70002000000410037004400320037007D00000000000000D172ACE4E7007800650050E9E70065E18975ADDE8A96FEFFFFFF7F878875F36B8875E186887545B0E5E36CEAE700100000000F0104003C003E006CEAE70080E9E700000000000000000000000000000008023CE7E7000000080234E5E700000000000000D172040D0000200200000000000060E5E700000000000700000078E5E700140000000000000000002800E82A00070000000010D61A0408D51A047CE5E7003DA96C7600000000FBFFFF7FA0E5E700987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF0000000000000000000000000B391107253911070B391107000000000000000000000000080000002E006C00E72F687711000000B8452B00B0452B0000002800140000000500000054E600007291E1E304E6E70082916C7654E6E70008E6E70027956C76000000008C00FD0330E6E700CD946C768C00FD03DCE6E70000FCFC03E1946C760000000000FCFC03DCE6E70038E6E700090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000E101CD944A76CC90FF0188E5E101408CFF012DAC977714E3E700408CFF01D8E4E700EDE064777D401800FEFFFFFF8B8D6877108B687701000000010000000000000004E5E700CCE4E700E8E4E7006C878875010000000000000004E5E7007F878875CDBDE5E3000000006CEAE70002000000410037004400320037007D00000000000000D172ACE4E7007800650050E9E70065E18975ADDE8A96FEFFFFFF7F878875F36B8875E186887545B0E5E36CEAE700100000000F0104003C003E006CEAE70080E9E700000000000000000000000000000008023CE7E7000000080234E5E700000000000000D172040D0000200200000000000060E5E700000000000700000078E5E700140000000000000000002800E82A00070000000010D61A0408D51A047CE5E7003DA96C7600000000FBFFFF7FA0E5E700987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF0000000000000000000000000B391107253911070B391107000000000000000000000000080000002E006C00E72F687711000000B8452B00B0452B0000002800140000000500000054E600007291E1E304E6E70082916C7654E6E70008E6E70027956C76000000008C00FD0330E6E700CD946C768C00FD03DCE6E70000FCFC03E1946C760000000000FCFC03DCE6E70038E6E700090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000E101CD944A76CC90FF0188E5E101408CFF012DAC977714E3E700408CFF01D8E4E700EDE064777D401800FEFFFFFF8B8D6877108B687701000000010000000000000004E5E700CCE4E700E8E4E7006C878875010000000000000004E5E7007F878875CDBDE5E3000000006CEAE70002000000410037004400320037007D00000000000000D172ACE4E7007800650050E9E70065E18975ADDE8A96FEFFFFFF7F878875F36B8875E186887545B0E5E36CEAE700100000000F0104003C003E006CEAE70080E9E700000000000000000000000000000008023CE7E7000000080234E5E700000000000000D172040D0000200200000000000060E5E700000000000700000078E5E700140000000000000000002800E82A00070000000010D61A0408D51A047CE5E7003DA96C7600000000FBFFFF7FA0E5E700987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF0000000000000000000000000B391107253911070B391107000000000000000000000000080000002E006C00E72F687711000000B8452B00B0452B0000002800140000000500000054E600007291E1E304E6E70082916C7654E6E70008E6E70027956C76000000008C00FD0330E6E700CD946C768C00FD03DCE6E70000FCFC03E1946C760000000000FCFC03DCE6E70038E6E700 | |||
| (PID) Process: | (3744) firefox.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
998
Suspicious files
387
Text files
233
Unknown types
80
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3744 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 3744 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 3744 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 3744 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3744 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3744 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3744 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-child-current.bin | binary | |
MD5:— | SHA256:— | |||
| 3744 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:— | SHA256:— | |||
| 3744 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
| 3744 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\base-track-digest256.sbstore | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
28
DNS requests
67
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3744 | firefox.exe | GET | — | 2.20.20.197:80 | http://buy-download.norton.com/downloads/OEM/22.5.2/NSD/5D/NSD_5D_22.5.2_SYMTB_PROMO_19_MRFTT_DD026_14248.exe | unknown | — | — | whitelisted |
3744 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3744 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3744 | firefox.exe | POST | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
3744 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3744 | firefox.exe | 2.20.20.197:80 | buy-download.norton.com | Akamai International B.V. | — | whitelisted |
3744 | firefox.exe | 2.16.106.209:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
3744 | firefox.exe | 35.164.109.147:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3744 | firefox.exe | 143.204.214.95:443 | snippets.cdn.mozilla.net | — | US | suspicious |
3744 | firefox.exe | 35.160.158.154:443 | push.services.mozilla.com | Amazon.com, Inc. | US | malicious |
3744 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3744 | firefox.exe | 172.217.23.106:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3744 | firefox.exe | 35.161.239.106:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3744 | firefox.exe | 172.217.22.35:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3744 | firefox.exe | 99.86.243.30:443 | content-signature-2.cdn.mozilla.net | AT&T Services, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
buy-download.norton.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
e859.g.akamaiedge.net |
| suspicious |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
d228z91au11ukj.cloudfront.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3744 | firefox.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
BHCA.exe | 2019-11-12-14-32-09-128 : BHCA : 0x0BD4 : 0x0F60 : Information : wWinMain(93) : BHCA starting...
|
BHCA.exe | 2019-11-12-14-32-09-128 : BHCA : 0x0BD4 : 0x0F60 : Information : wWinMain(98) : BHCA Version 5.0.0.24
|
BHCA.exe | 2019-11-12-14-32-09-128 : BHCA : 0x0BD4 : 0x0F60 : Information : ccVerifyTrust::CVerifyTrustImpl::Create(75) : bLoadTrustPolicy = 0
|
BHCA.exe | 2019-11-12-14-32-09-143 : BHCA : 0x0BD4 : 0x0F60 : Information : ccVerifyTrust::CVerifyFile::Create(131) : WTPF_TRUSTTEST flag is not set.
|
BHCA.exe | 2019-11-12-14-32-09-143 : BHCA : 0x0BD4 : 0x0F60 : Information : ccVerifyTrust::CVerifyFile::Create(132) : WTPF_TESTCANBEVALID flag is not set.
|
BHCA.exe | 2019-11-12-14-32-09-143 : BHCA : 0x0BD4 : 0x0F60 : Information : ccVerifyTrust::CVerifyFile::Create(133) : WTPF_IGNOREEXPIRATION flag is not set.
|
BHCA.exe | 2019-11-12-14-32-09-143 : BHCA : 0x0BD4 : 0x0F60 : Information : ccVerifyTrust::CVerifyFile::Create(134) : WTPF_IGNOREREVOKATION flag is set.
|
BHCA.exe | 2019-11-12-14-32-09-143 : BHCA : 0x0BD4 : 0x0F60 : Information : ccVerifyTrust::CVerifyFile::Create(135) : WTPF_OFFLINEOK_COM flag is set.
|
BHCA.exe | 2019-11-12-14-32-09-143 : BHCA : 0x0BD4 : 0x0F60 : Information : ccVerifyTrust::CVerifyFile::Create(136) : WTPF_OFFLINEOKNBU_IND flag is set.
|
BHCA.exe | 2019-11-12-14-32-09-143 : BHCA : 0x0BD4 : 0x0F60 : Information : ccVerifyTrust::CVerifyFile::Create(137) : WTPF_OFFLINEOKNBU_COM flag is set.
|