| File name: | marketing-report (1).doc |
| Full analysis: | https://app.any.run/tasks/fd62cac2-3d64-4c59-b951-28f22f76865f |
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2022, 10:38:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | F22F3CC52489638AAB8C3F3AB8CD63FA |
| SHA1: | 21D1123EB9078DCD7EF1CD9196BBC2DC67DDAF2D |
| SHA256: | 3E11D7EF5C29498141FDC9664CFAEBCDAE5CC2711FF4A431C97AF9BFB040BA4E |
| SSDEEP: | 192:SEhMd9264wpf4Ghey7Z/c+8poF1d3jvvtlQb8P6rGxjPRwS4UU4fNt8h+:SqA92hwt4GA0cfa7pr1lQbLyxjPR4z4B |
MALICIOUS
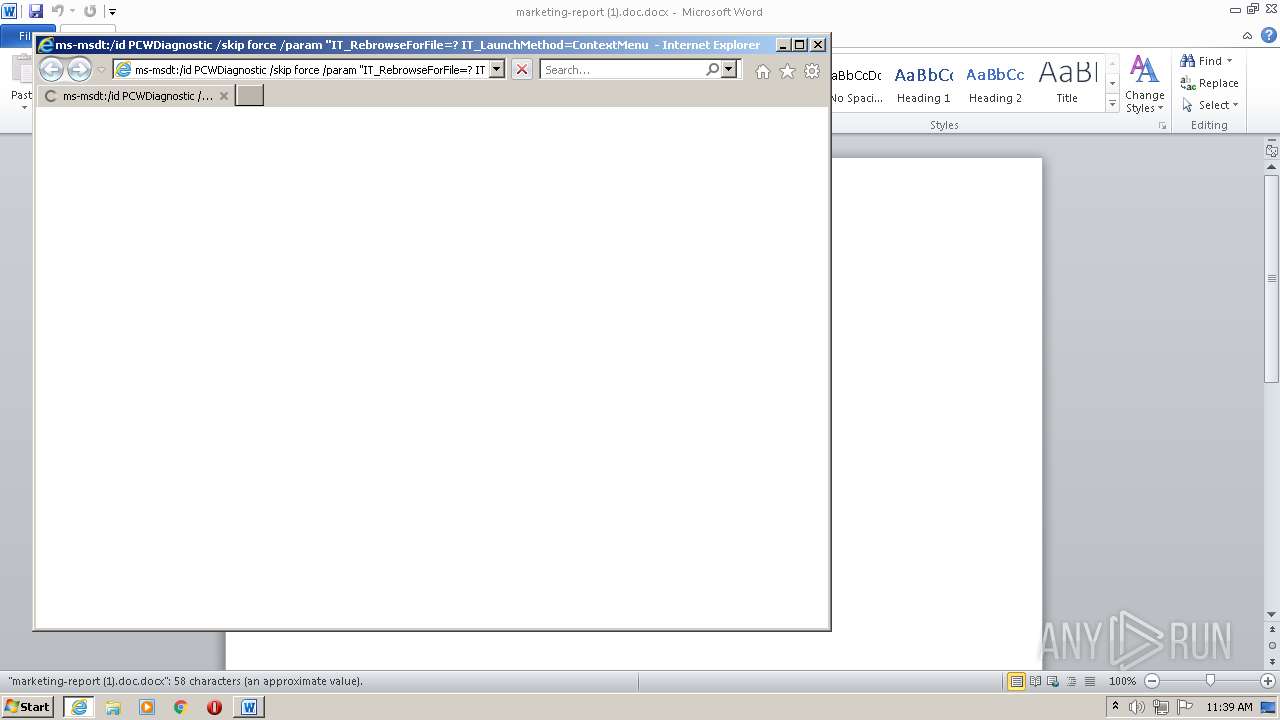
CVE-2022-30190 detected
- WINWORD.EXE (PID: 2840)
SUSPICIOUS
Executed via COM
- iexplore.exe (PID: 4072)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3664)
- iexplore.exe (PID: 3732)
INFO
Checks supported languages
- WINWORD.EXE (PID: 2840)
- iexplore.exe (PID: 4072)
- iexplore.exe (PID: 3664)
- iexplore.exe (PID: 3732)
Creates files in the user directory
- WINWORD.EXE (PID: 2840)
Reads internet explorer settings
- WINWORD.EXE (PID: 2840)
- iexplore.exe (PID: 3732)
Reads the computer name
- WINWORD.EXE (PID: 2840)
- iexplore.exe (PID: 3732)
- iexplore.exe (PID: 4072)
- iexplore.exe (PID: 3664)
Application launched itself
- iexplore.exe (PID: 4072)
Reads Microsoft Outlook installation path
- WINWORD.EXE (PID: 2840)
Changes internet zones settings
- iexplore.exe (PID: 4072)
Checks Windows Trust Settings
- iexplore.exe (PID: 4072)
Reads settings of System Certificates
- iexplore.exe (PID: 4072)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2840)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docx | | | Word Microsoft Office Open XML Format document (52.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (38.8) |
| .zip | | | ZIP compressed archive (8.8) |
EXIF
XML
| AppVersion: | 16 |
|---|---|
| HyperlinksChanged: | No |
| SharedDoc: | No |
| CharactersWithSpaces: | - |
| LinksUpToDate: | No |
| Company: | - |
| ScaleCrop: | No |
| Paragraphs: | - |
| Lines: | - |
| DocSecurity: | None |
| Application: | Microsoft Office Word |
| Characters: | - |
| Words: | - |
| Pages: | 1 |
| TotalEditTime: | - |
| Template: | Normal |
| ModifyDate: | 2022:05:25 13:14:00Z |
| CreateDate: | 2022:05:25 13:14:00Z |
| RevisionNumber: | 3 |
| LastModifiedBy: | KIS2 |
| Keywords: | - |
XMP
| Description: | - |
|---|---|
| Creator: | KIS2 |
| Subject: | - |
| Title: | - |
ZIP
| ZipFileName: | _rels/ |
|---|---|
| ZipUncompressedSize: | - |
| ZipCompressedSize: | - |
| ZipCRC: | 0x00000000 |
| ZipModifyDate: | 2022:06:12 15:44:00 |
| ZipCompression: | None |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 20 |
Total processes
39
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2840 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\marketing-report (1).doc.docx" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3664 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4072 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3732 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4072 CREDAT:3544328 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 4072 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
10 804
Read events
9 957
Write events
717
Delete events
130
Modification events
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | <s; |
Value: 3C733B00180B0000010000000000000000000000 | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
14
Text files
8
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR4F1C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\{66B37CB0-1DE8-4892-B64C-BB1458C8AA55} | binary | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$rketing-report (1).doc.docx | pgc | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\FSD-CNRY.FSD | binary | |
MD5:— | SHA256:— | |||
| 4072 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFC2CCF9F8CF8B87A4.TMP | gmc | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\C41A5E4B.htm | html | |
MD5:— | SHA256:— | |||
| 4072 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 4072 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 4072 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{5AF8BB87-F605-11EC-8C9F-1203334A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
| 4072 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
19
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
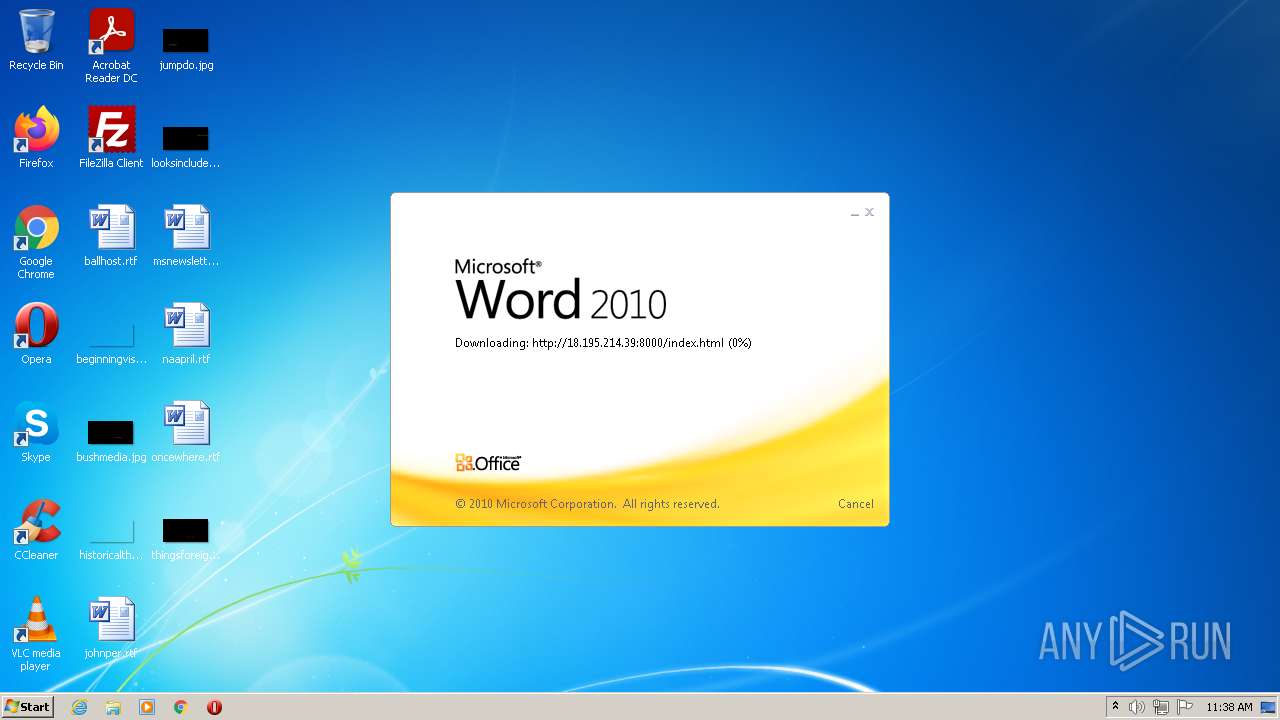
2840 | WINWORD.EXE | HEAD | 200 | 18.195.214.39:8000 | http://18.195.214.39:8000/index.html | DE | — | — | unknown |
2840 | WINWORD.EXE | HEAD | 200 | 18.195.214.39:8000 | http://18.195.214.39:8000/index.html | DE | — | — | unknown |
2840 | WINWORD.EXE | HEAD | 200 | 18.195.214.39:8000 | http://18.195.214.39:8000/index.html | DE | — | — | unknown |
2840 | WINWORD.EXE | GET | 304 | 18.195.214.39:8000 | http://18.195.214.39:8000/index.html | DE | — | — | unknown |
2840 | WINWORD.EXE | HEAD | 200 | 18.195.214.39:8000 | http://18.195.214.39:8000/index.html | DE | — | — | unknown |
2840 | WINWORD.EXE | HEAD | 200 | 18.195.214.39:8000 | http://18.195.214.39:8000/index.html | DE | — | — | unknown |
4072 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
836 | svchost.exe | OPTIONS | 501 | 18.195.214.39:8000 | http://18.195.214.39:8000/ | DE | html | 500 b | unknown |
2840 | WINWORD.EXE | OPTIONS | 501 | 18.195.214.39:8000 | http://18.195.214.39:8000/ | DE | html | 500 b | unknown |
4072 | iexplore.exe | GET | 200 | 41.63.96.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?39c98eec54dbf7e5 | ZA | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 18.195.214.39:8000 | — | Amazon.com, Inc. | DE | unknown |
2840 | WINWORD.EXE | 18.195.214.39:8000 | — | Amazon.com, Inc. | DE | unknown |
4072 | iexplore.exe | 41.63.96.128:80 | ctldl.windowsupdate.com | Limelight Networks, Inc. | ZA | suspicious |
4072 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
4072 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4072 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4072 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |