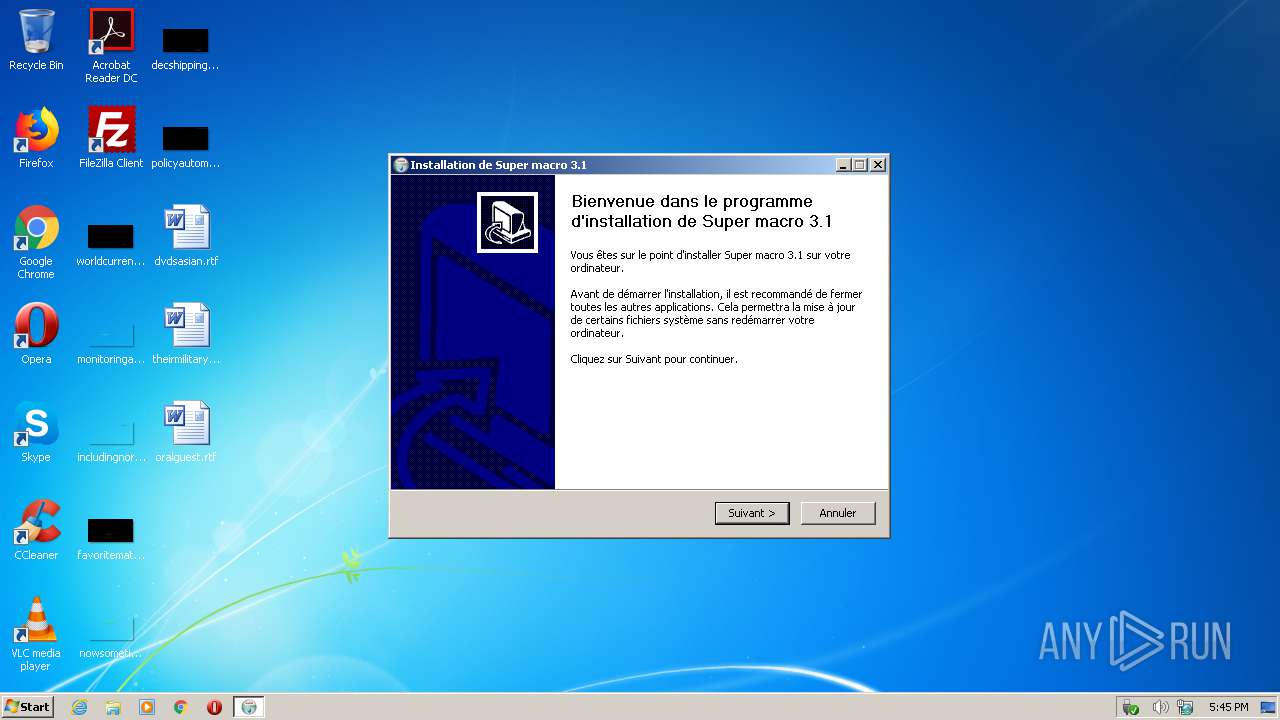
| File name: | SuperMacro_install.exe |
| Full analysis: | https://app.any.run/tasks/7cb2356c-24d1-4a5e-8781-4732dd5a8851 |
| Verdict: | Malicious activity |
| Analysis date: | November 25, 2020, 17:45:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | D982926D7FFD8F3C85BAB9AFEE07B35A |
| SHA1: | F46AE4CB62C4E7575C445D320E8AA94A842A81FC |
| SHA256: | 3E06465B4208EE727919A2EEAF3AECDCD238539618F89B8492259597F3E6FE20 |
| SSDEEP: | 98304:rAPe+sXQFZR4ftMyH6+H1DgvwSW4xYUCsgZC9xbLjEH7lv24fw:cPFswZR+Kc1cvV+dZefEblvRfw |
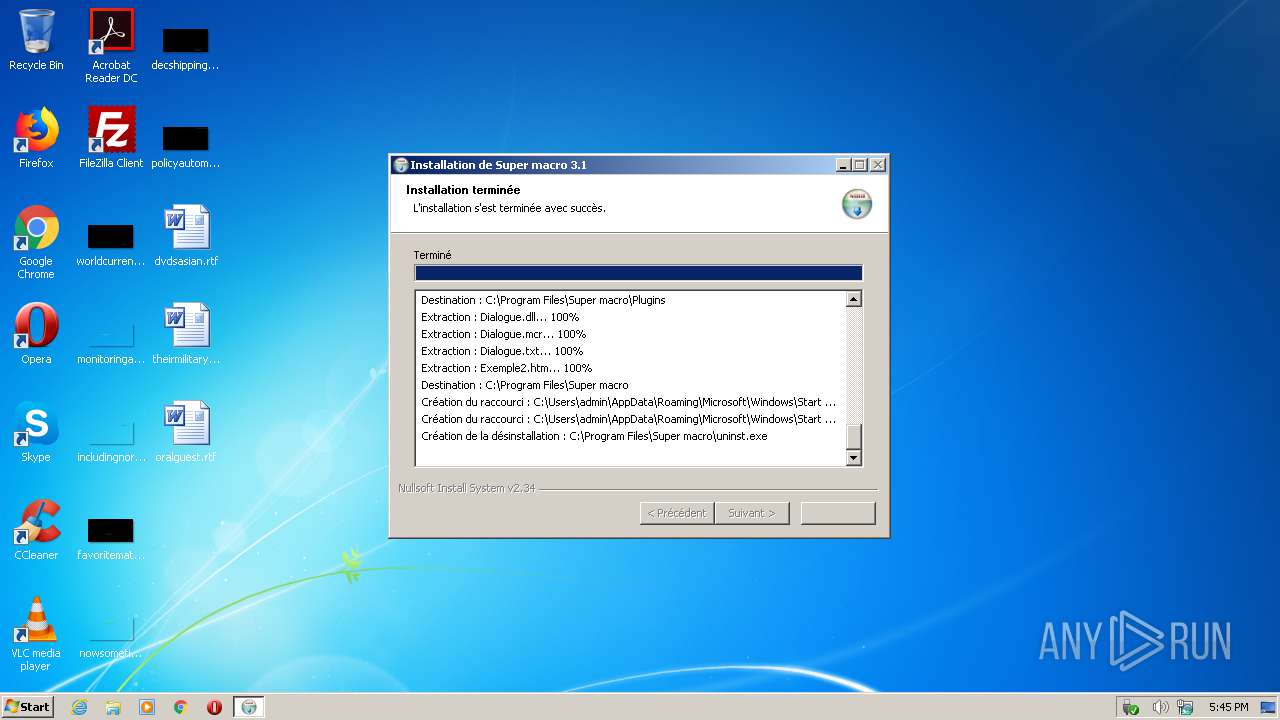
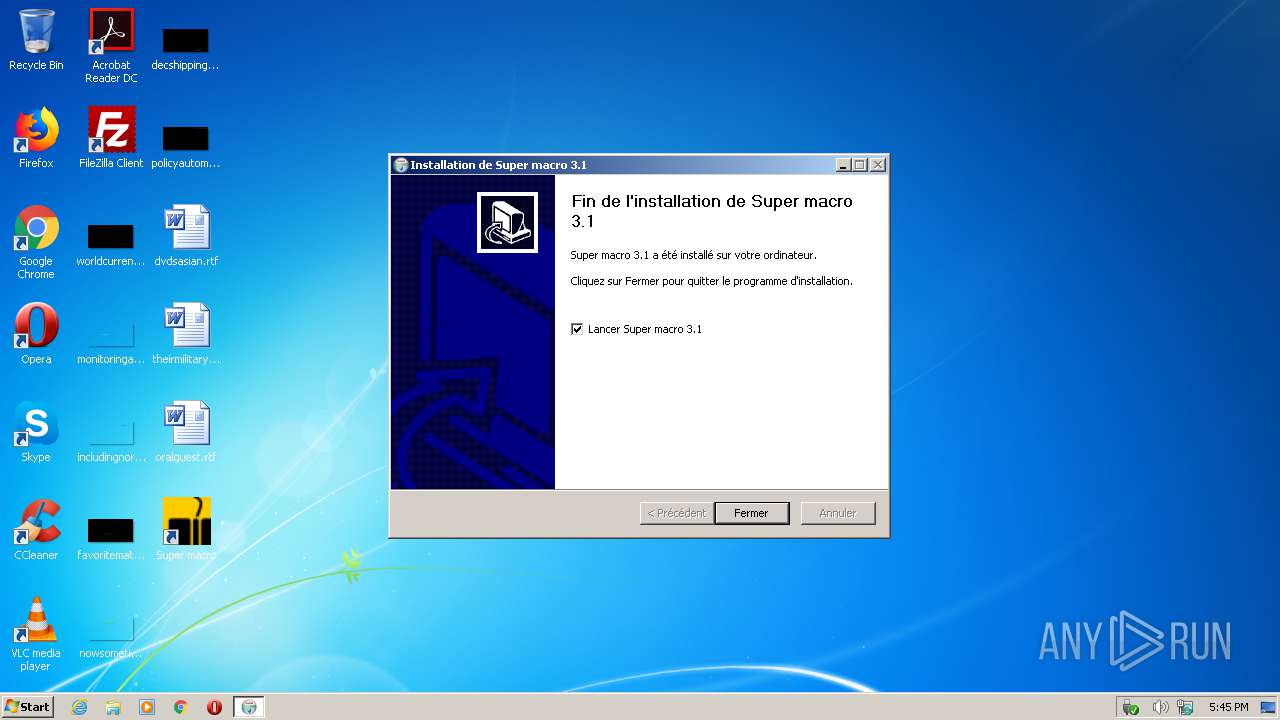
MALICIOUS
Drops executable file immediately after starts
- SuperMacro_install.exe (PID: 3760)
Loads dropped or rewritten executable
- SuperMacro_install.exe (PID: 3760)
Application was dropped or rewritten from another process
- super_macro.exe (PID: 3060)
SUSPICIOUS
Executable content was dropped or overwritten
- SuperMacro_install.exe (PID: 3760)
Reads the computer name
- SuperMacro_install.exe (PID: 3760)
- super_macro.exe (PID: 3060)
Checks supported languages
- SuperMacro_install.exe (PID: 3760)
- super_macro.exe (PID: 3060)
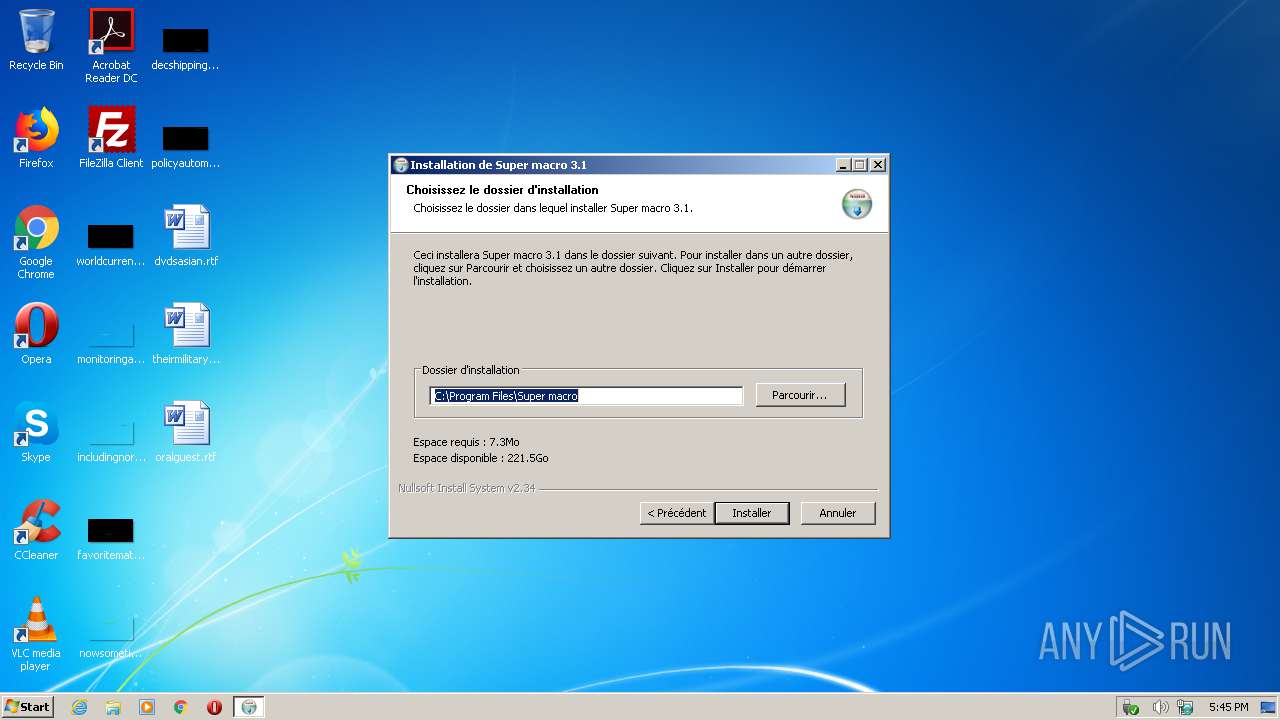
Creates a directory in Program Files
- SuperMacro_install.exe (PID: 3760)
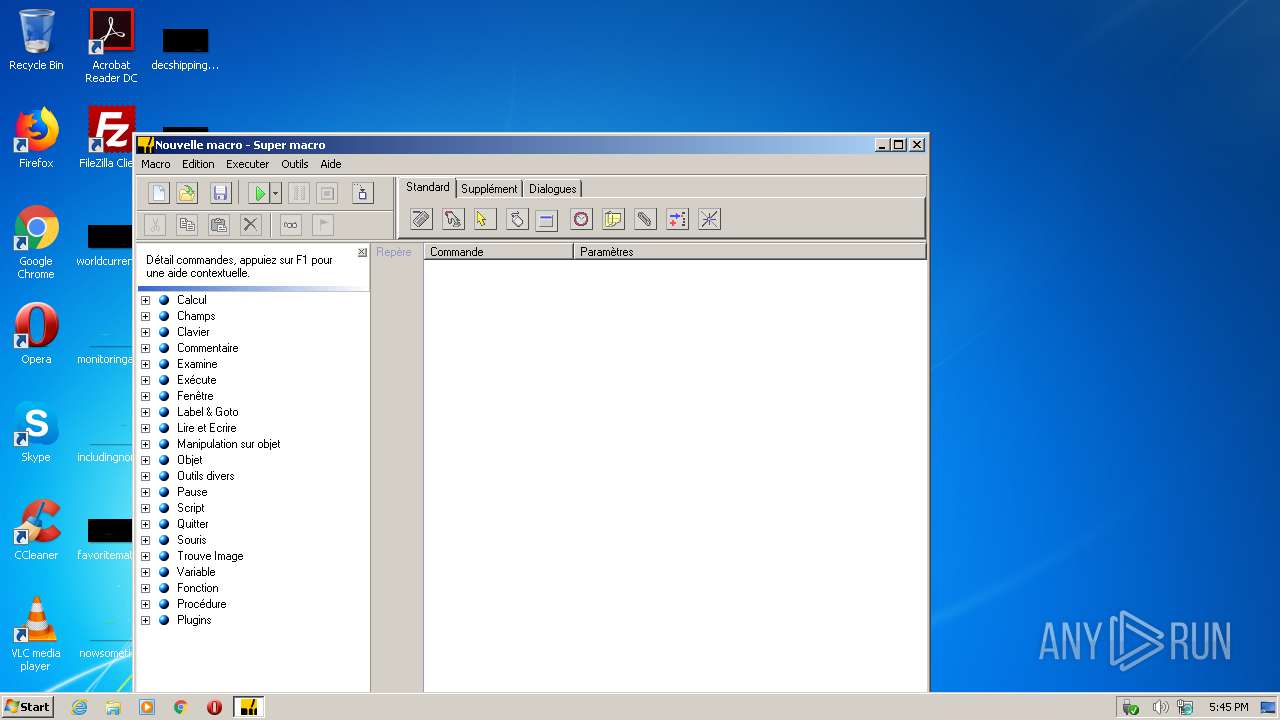
Creates files in the program directory
- SuperMacro_install.exe (PID: 3760)
- super_macro.exe (PID: 3060)
Drops a file with too old compile date
- SuperMacro_install.exe (PID: 3760)
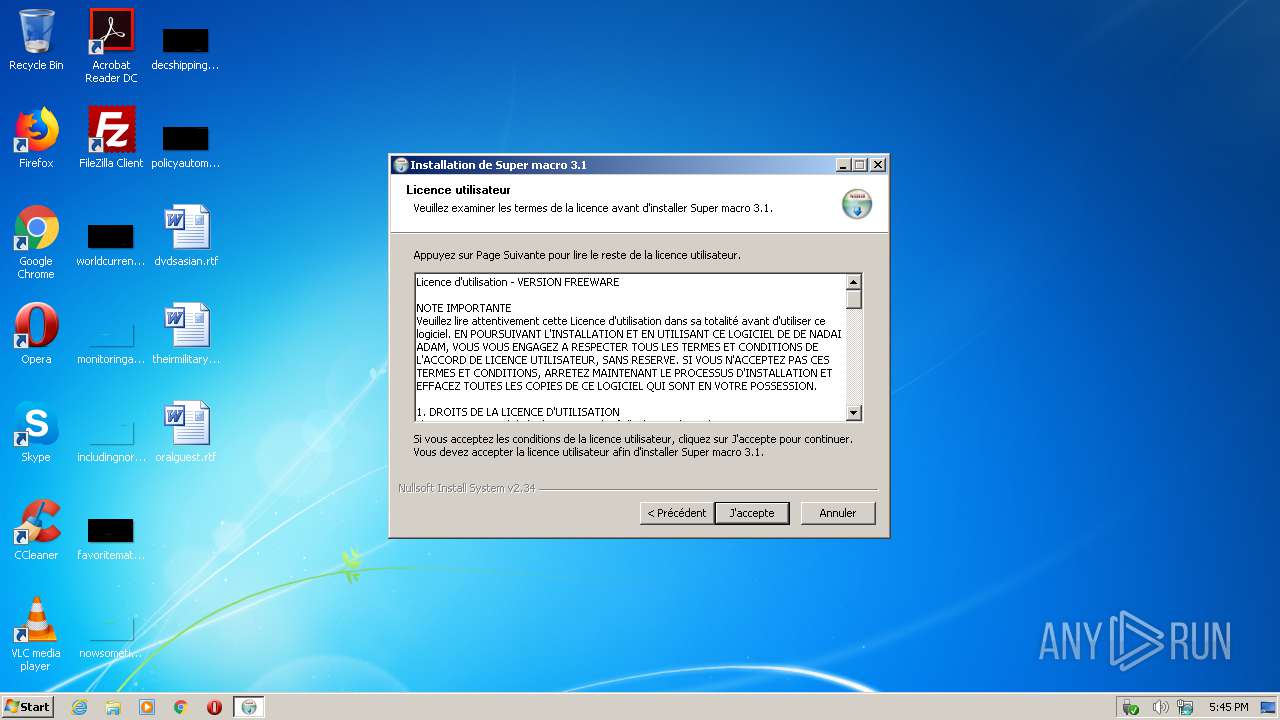
Creates a software uninstall entry
- SuperMacro_install.exe (PID: 3760)
Modifies the open verb of a shell class
- SuperMacro_install.exe (PID: 3760)
INFO
Dropped object may contain Bitcoin addresses
- SuperMacro_install.exe (PID: 3760)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (91.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.3) |
| .exe | | | Win64 Executable (generic) (3) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:12:24 22:04:29+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 164864 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x30ed |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Dec-2007 21:04:29 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 24-Dec-2007 21:04:29 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005B30 | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.47321 |
.rdata | 0x00007000 | 0x0000129C | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04904 |
.data | 0x00009000 | 0x00025CB8 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.1277 |
.ndata | 0x0002F000 | 0x00009000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00038000 | 0x00004130 | 0x00004200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.85855 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.10609 | 533 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.9993 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 6.24459 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 5.01502 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 6.16057 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 3.34146 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 3.04232 | 296 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.6691 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
44
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2940 | "C:\Users\admin\AppData\Local\Temp\SuperMacro_install.exe" | C:\Users\admin\AppData\Local\Temp\SuperMacro_install.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3060 | "C:\Program Files\Super macro\super_macro.exe" | C:\Program Files\Super macro\super_macro.exe | — | SuperMacro_install.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Editeur Macro Windows Exit code: 0 Version: 3.1.0.46 Modules
| |||||||||||||||
| 3760 | "C:\Users\admin\AppData\Local\Temp\SuperMacro_install.exe" | C:\Users\admin\AppData\Local\Temp\SuperMacro_install.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
1 242
Read events
1 232
Write events
10
Delete events
0
Modification events
| (PID) Process: | (3760) SuperMacro_install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\mcr_auto_file\shell\Open\command |
| Operation: | write | Name: | (default) |
Value: C:\Program Files\Super macro\super_macro.exe "%1" | |||
| (PID) Process: | (3760) SuperMacro_install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\mcr_auto_file\shell\Edition\command |
| Operation: | write | Name: | (default) |
Value: C:\Program Files\Super macro\super_macro.exe "%1" /edt | |||
| (PID) Process: | (3760) SuperMacro_install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\mcr_auto_file\DefaultIcon |
| Operation: | write | Name: | (default) |
Value: C:\Program Files\Super macro\K7.ico | |||
| (PID) Process: | (3760) SuperMacro_install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.mcr |
| Operation: | write | Name: | (default) |
Value: mcr_auto_file | |||
| (PID) Process: | (3760) SuperMacro_install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Super macro |
| Operation: | write | Name: | URLInfoAbout |
Value: http://adam.denadai.free.fr | |||
| (PID) Process: | (3760) SuperMacro_install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Super macro |
| Operation: | write | Name: | DisplayVersion |
Value: 3.1 | |||
| (PID) Process: | (3760) SuperMacro_install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Super macro |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\Super macro\MdlAE.exe | |||
| (PID) Process: | (3760) SuperMacro_install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Super macro |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\Super macro\uninst.exe | |||
| (PID) Process: | (3760) SuperMacro_install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Super macro |
| Operation: | write | Name: | DisplayName |
Value: Super macro 3.1 | |||
| (PID) Process: | (3760) SuperMacro_install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\MdlAE.exe |
| Operation: | write | Name: | (default) |
Value: C:\Program Files\Super macro\MdlAE.exe | |||
Executable files
10
Suspicious files
10
Text files
25
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3760 | SuperMacro_install.exe | C:\Users\admin\Desktop\Super macro.lnk | lnk | |
MD5:800E5405D4A12331A07331CE1B1C962F | SHA256:DCF9B3F9A9BC8DD2ED0A30B771E913D40D4244F667DA3F31FD9FA3F03323294A | |||
| 3760 | SuperMacro_install.exe | C:\Program Files\Super macro\English.lng | text | |
MD5:7B6529DA04BF862FC713E7887EC75299 | SHA256:0D2D29BF332A0690DFCE98B4F36C5DFC9DB3C5914DCB20614BE8BA3EE5C2B9CF | |||
| 3760 | SuperMacro_install.exe | C:\Users\admin\AppData\Local\Temp\nst6300.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 3760 | SuperMacro_install.exe | C:\Users\Administrator\Desktop\Super macro.lnk | lnk | |
MD5:800E5405D4A12331A07331CE1B1C962F | SHA256:DCF9B3F9A9BC8DD2ED0A30B771E913D40D4244F667DA3F31FD9FA3F03323294A | |||
| 3760 | SuperMacro_install.exe | C:\Program Files\Super macro\Fran�ais.lng | text | |
MD5:6C3E1F70CB931FE90FFD2506FBD5A877 | SHA256:E69F8CFCD00F5822A6E9784E34B26723FCFDA48A0FD33B9D87A06E7D99885A71 | |||
| 3760 | SuperMacro_install.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Super macro\Help.lnk | lnk | |
MD5:6882623BF34A66DDF90D977BE193B93D | SHA256:D7903DBFFC3ABC739565A02FAAAC3D0A33535202B6FC161614B2C76CF5D7FD35 | |||
| 3760 | SuperMacro_install.exe | C:\Program Files\Super macro\k7.ico | image | |
MD5:81252BBBBCA13B42E7694FD4E3799870 | SHA256:70CC720FD114FBF26E86AEA9F38D4FF6595E8CA6C9A5CC4C63D3CDC2E0D8F172 | |||
| 3760 | SuperMacro_install.exe | C:\Program Files\Super macro\Souris_Hook.dll | executable | |
MD5:55098D707B919B336DF01C0C18D2EE39 | SHA256:61E82F7273760717AE1CAA95040E032304E389F5401121473DCDA507EF1D5E7B | |||
| 3760 | SuperMacro_install.exe | C:\Program Files\Super macro\Ressources.dll | executable | |
MD5:4FCDBC497AAD5C2738DA5D7F8E5E8086 | SHA256:8F63B39691FAF1ACCEAAFBE8FCFB732F2569F7C9948374195C07127944667D75 | |||
| 3760 | SuperMacro_install.exe | C:\Program Files\Super macro\Clavier_Hook.dll | executable | |
MD5:83AD298BA24F6AE86D19C91CE9ABFCDE | SHA256:6E7200BA5E00CB6B864DC0B4147C2FDAB9EFBF209867C52C4BEA8FC6015F0479 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report