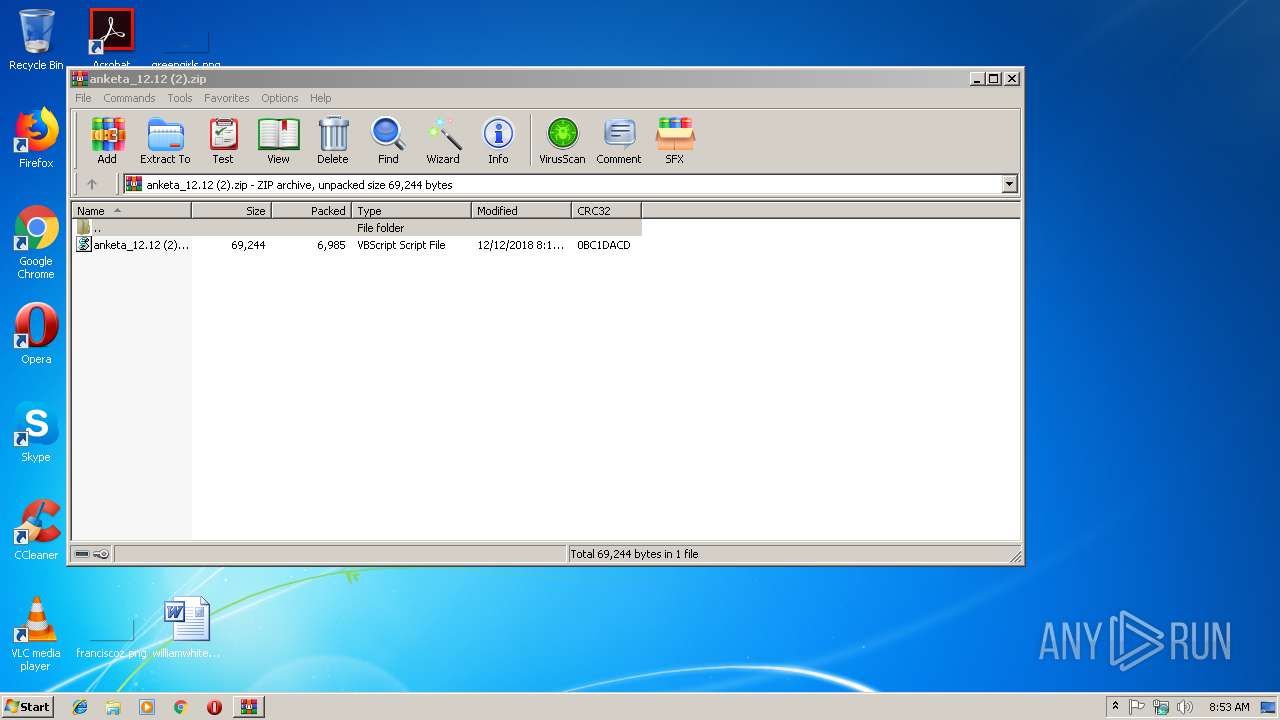
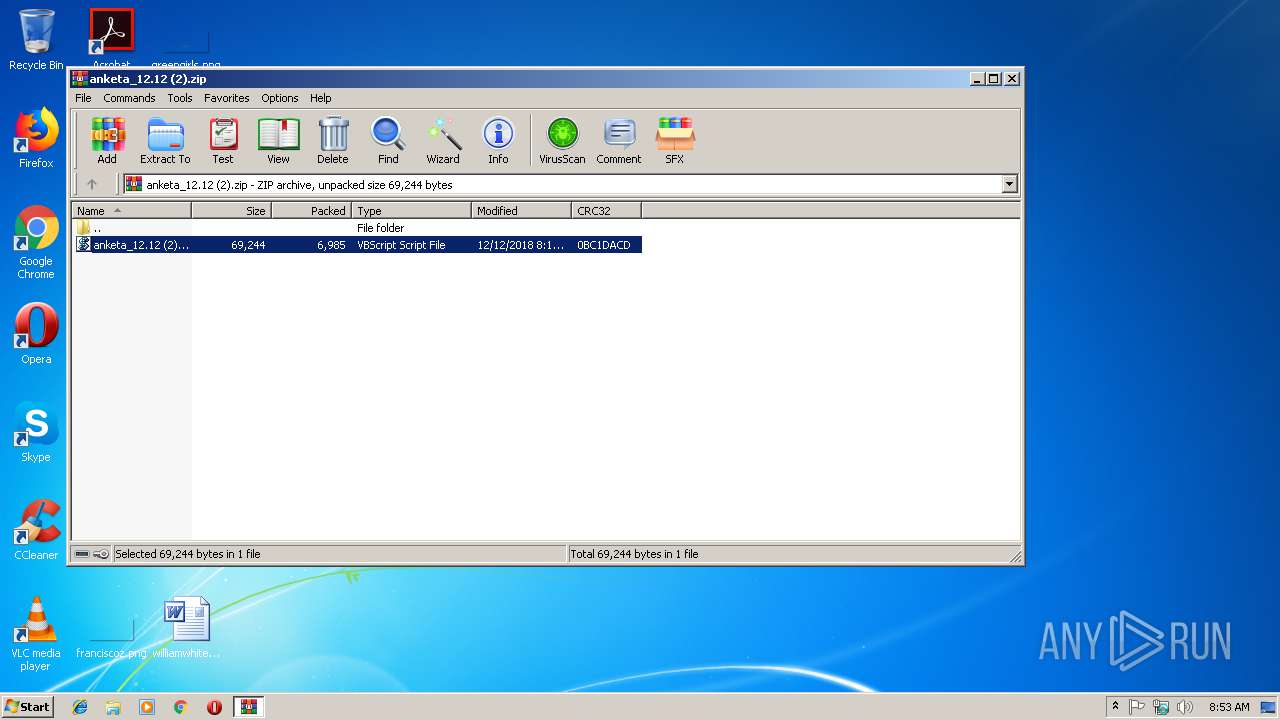
| File name: | anketa_12.12 (2).zip |
| Full analysis: | https://app.any.run/tasks/a010e565-4cfe-4300-8d52-24f6215d6e1e |
| Verdict: | Malicious activity |
| Analysis date: | February 11, 2019, 08:53:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | C0E90F403A68E7551B8B82B1E566CA80 |
| SHA1: | AC5E4D0A80404D1F9B50C1CF460C6DA7189C7C58 |
| SHA256: | 3E02E6C625D7266CC161CCB8AE192BAE6950ACC8C65EF1BFA1BA9D951C732FB0 |
| SSDEEP: | 192:DkPyN1VQFVhV7+z4Xzoo9IBSdYZKg/Uu+f:iJ7hVW4X0mkKYUN |
MALICIOUS
Changes the autorun value in the registry
- powershell.exe (PID: 3024)
SUSPICIOUS
Starts NET.EXE for network exploration
- cmd.exe (PID: 2220)
Creates files in the user directory
- powershell.exe (PID: 3024)
- WScript.exe (PID: 2624)
- powershell.exe (PID: 3576)
- powershell.exe (PID: 2844)
- powershell.exe (PID: 2916)
Starts CMD.EXE for commands execution
- WScript.exe (PID: 2624)
Uses SYSTEMINFO.EXE to read environment
- cmd.exe (PID: 3048)
Executes scripts
- WinRAR.exe (PID: 2964)
Executes PowerShell scripts
- WScript.exe (PID: 2624)
INFO
Reads settings of System Certificates
- WScript.exe (PID: 2624)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:12:12 11:12:27 |
| ZipCRC: | 0x0bc1dacd |
| ZipCompressedSize: | 6985 |
| ZipUncompressedSize: | 69244 |
| ZipFileName: | anketa_12.12 (2).VBS |
Total processes
51
Monitored processes
12
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2220 | "C:\Windows\System32\cmd.exe" /C net view> ~tmp_nv.txt | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2476 | "C:\Windows\System32\cmd.exe" /C nslookup e > ~tmp_ns.txt | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2624 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa2964.22978\anketa_12.12 (2).VBS" | C:\Windows\System32\WScript.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2768 | net view | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2844 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep unrestricted -file "C:\Users\admin\AppData\Roaming\X93J0FOK5170C5CWTOV0VUAJU.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2916 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -command New-ItemProperty -Path HKLM:\SOFTWARE\Microsoft\Windows\CurrentVersion\Run -Name ARSv5 -PropertyType String -Value C:\Users\admin\AppData\Roaming\MVajjQxnkYFmZwjbyqWBEjpWE.vbs | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2964 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\anketa_12.12 (2).zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2984 | nslookup e | C:\Windows\system32\nslookup.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3024 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -command New-ItemProperty -Path HKCU:\SOFTWARE\Microsoft\Windows\CurrentVersion\Run -Name ARSv5 -PropertyType String -Value C:\Users\admin\AppData\Roaming\MVajjQxnkYFmZwjbyqWBEjpWE.vbs | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3048 | "C:\Windows\System32\cmd.exe" /C systeminfo > ~tmp_si.txt | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 564
Read events
1 294
Write events
270
Delete events
0
Modification events
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\anketa_12.12 (2).zip | |||
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\wshext.dll,-4802 |
Value: VBScript Script File | |||
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
8
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3576 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\1DEC520R35QDD3B2EG6C.temp | — | |
MD5:— | SHA256:— | |||
| 2220 | cmd.exe | C:\Users\admin\AppData\Local\Temp\~tmp_nv.txt | — | |
MD5:— | SHA256:— | |||
| 2844 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\WXT9OGW79649LC9R4XWD.temp | — | |
MD5:— | SHA256:— | |||
| 3024 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\XM069C6YXJTCUU9MYLTR.temp | — | |
MD5:— | SHA256:— | |||
| 2916 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\Q0Z98LDAM9VPC3RXAY9B.temp | — | |
MD5:— | SHA256:— | |||
| 3576 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF212d0a.TMP | binary | |
MD5:— | SHA256:— | |||
| 3048 | cmd.exe | C:\Users\admin\AppData\Local\Temp\~tmp_si.txt | text | |
MD5:— | SHA256:— | |||
| 2844 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF215812.TMP | binary | |
MD5:— | SHA256:— | |||
| 2844 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2624 | WScript.exe | C:\Users\admin\AppData\Roaming\X93J0FOK5170C5CWTOV0VUAJU.ps1 | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
4
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2624 | WScript.exe | 185.180.197.79:443 | real-estate-news.host | Hosting Solution Ltd. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
real-estate-news.host |
| suspicious |
e |
| unknown |
dream-domains-news.club |
| unknown |