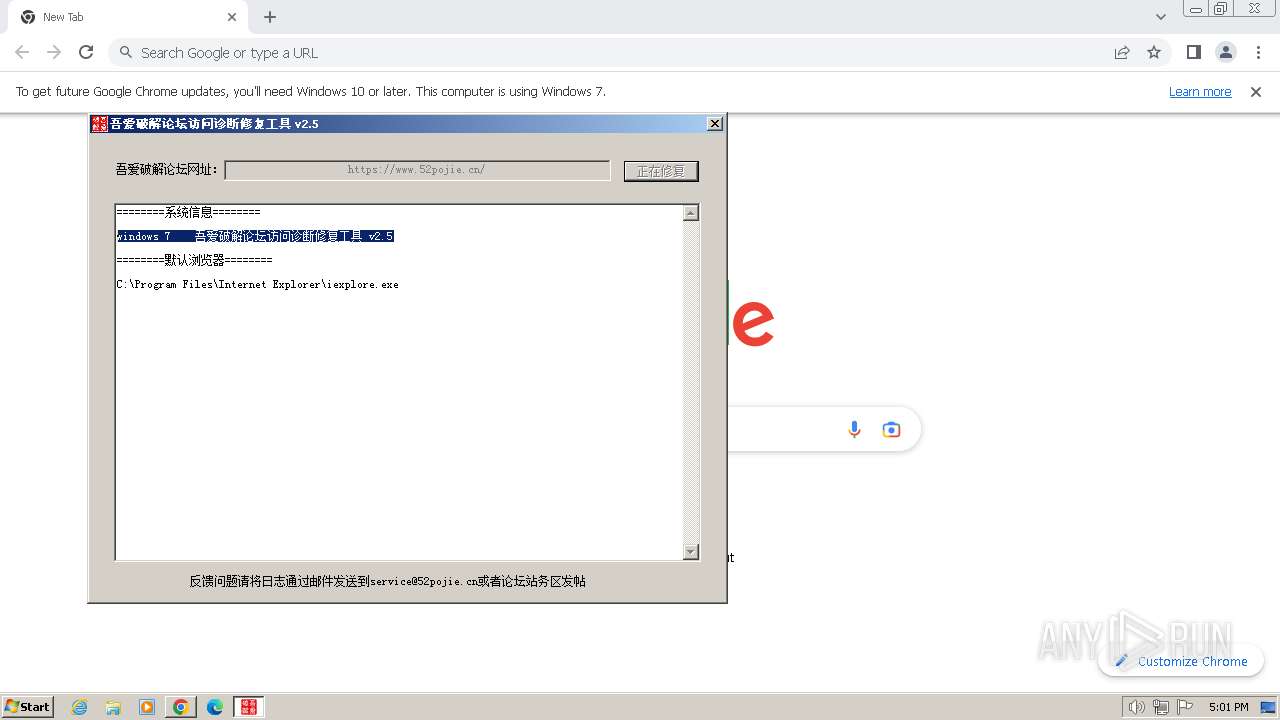
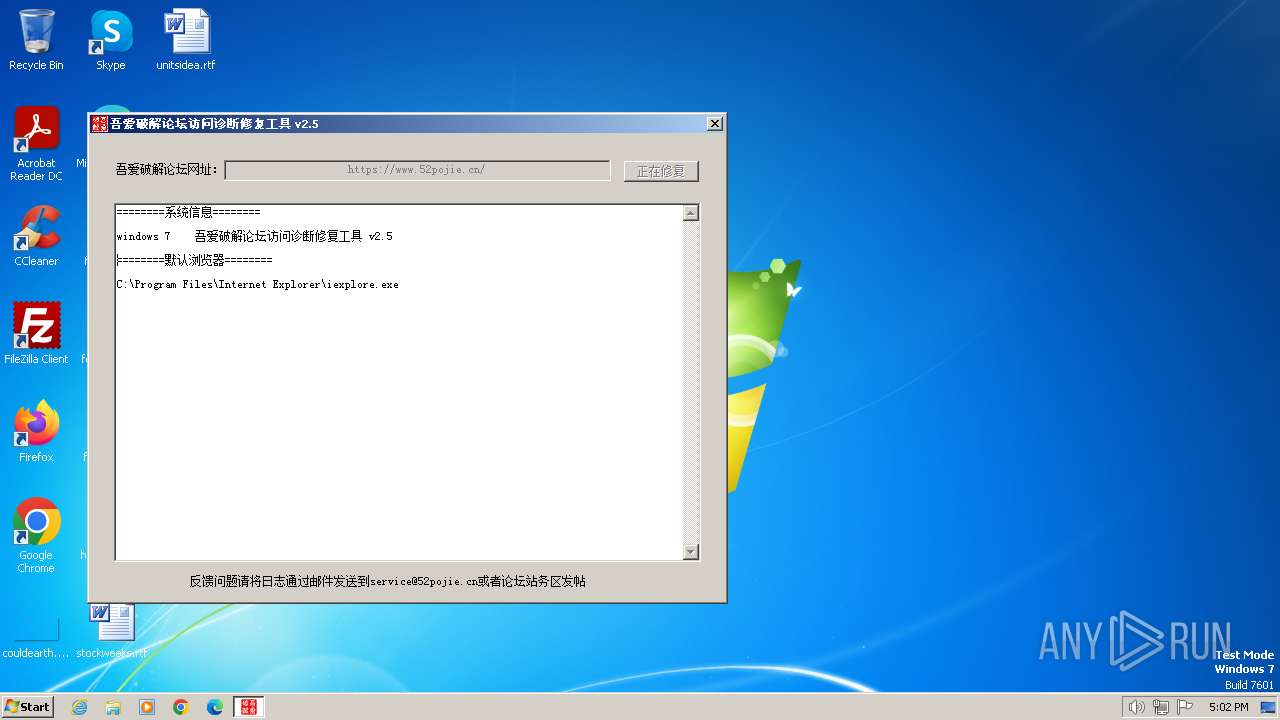
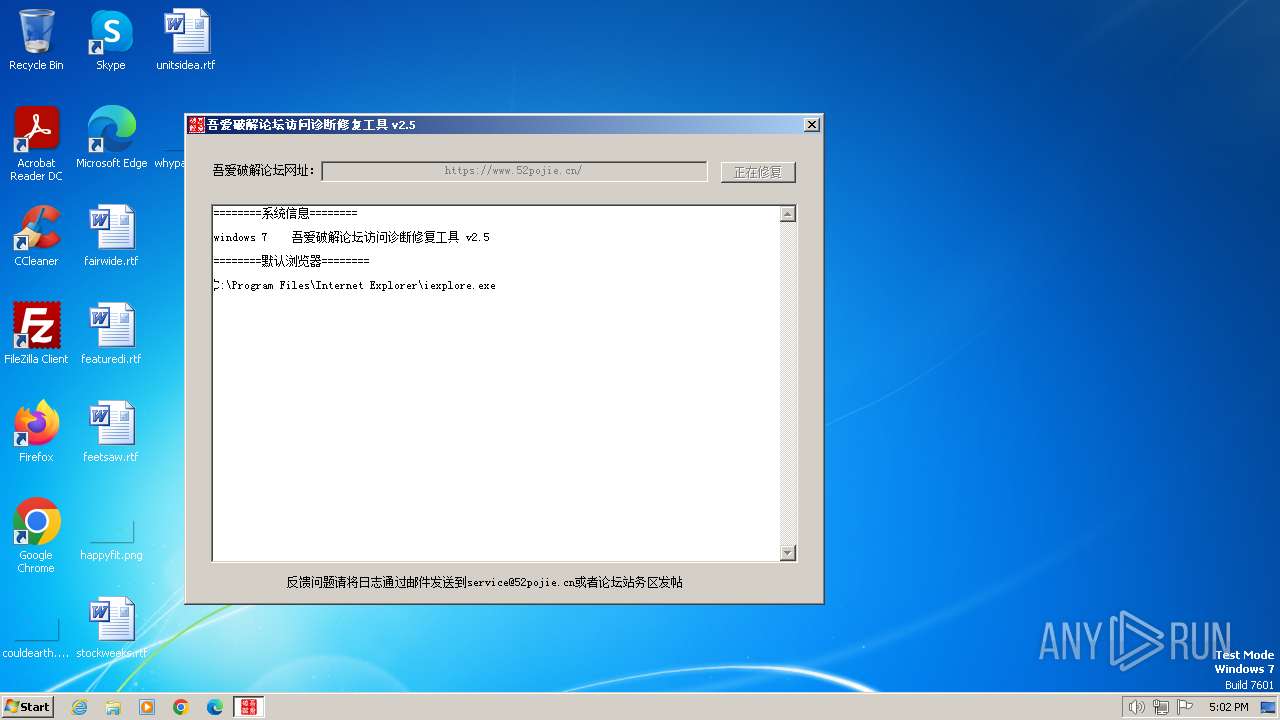
| File name: | 吾爱破解论坛网络诊断修复工具 v2.5.exe |
| Full analysis: | https://app.any.run/tasks/1dea4089-7373-4b6c-9b61-4d675cd5869b |
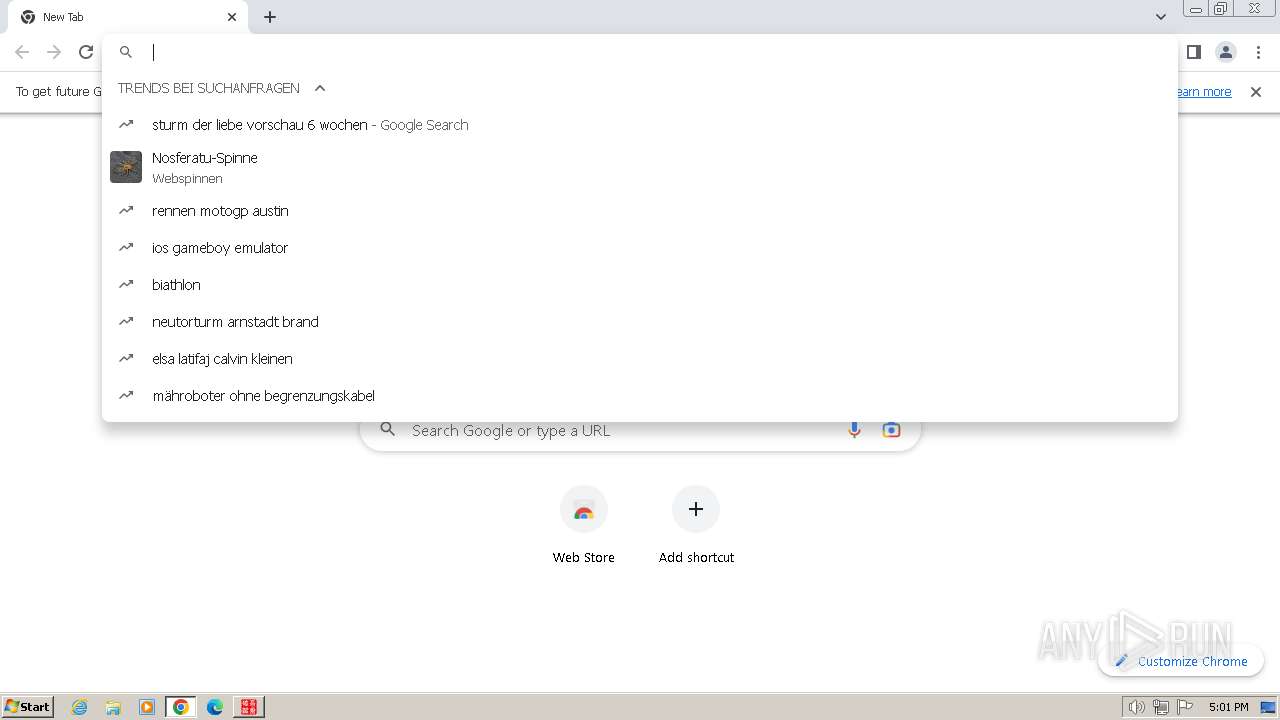
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2024, 16:00:13 |
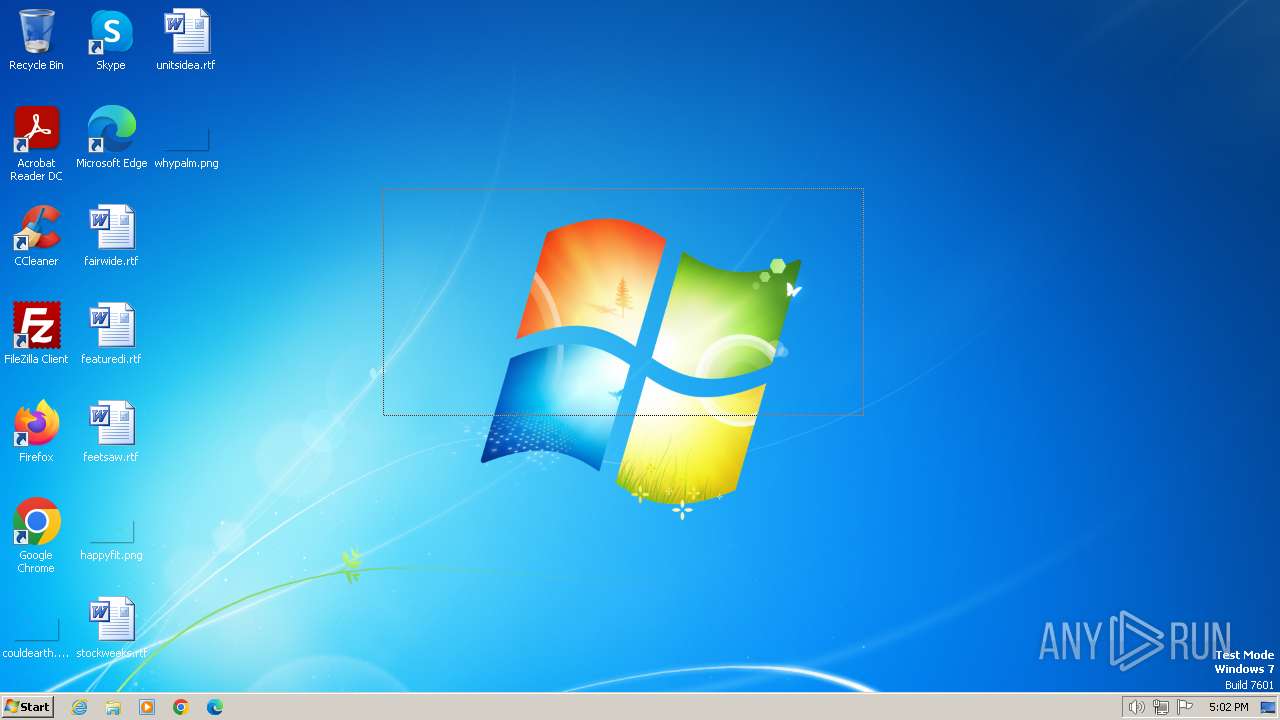
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A3E1393D3E12EB5613BAB7D620D2C838 |
| SHA1: | 0FE184AEE957D2BB4018DFA969564BA7CDC1F3DB |
| SHA256: | 3DF1584E856712D8B277EEDA341AFB9A95C01F19E7F508340AEB489BD9155A6E |
| SSDEEP: | 98304:/3hZ3AbOfOWYSepTKxS+Etd1/tAYVW0yfunZ0mAmJkqdFe3vtLj8tOQR+wRiYIsj:bAv1e0N9b0 |
MALICIOUS
Drops the executable file immediately after the start
- 吾爱破解论坛网络诊断修复工具 v2.5.exe (PID: 4064)
SUSPICIOUS
Reads the Internet Settings
- 吾爱破解论坛网络诊断修复工具 v2.5.exe (PID: 4064)
Reads security settings of Internet Explorer
- 吾爱破解论坛网络诊断修复工具 v2.5.exe (PID: 4064)
INFO
Reads the computer name
- 吾爱破解论坛网络诊断修复工具 v2.5.exe (PID: 4064)
Checks proxy server information
- 吾爱破解论坛网络诊断修复工具 v2.5.exe (PID: 4064)
Checks supported languages
- 吾爱破解论坛网络诊断修复工具 v2.5.exe (PID: 4064)
Application launched itself
- chrome.exe (PID: 3236)
Manual execution by a user
- explorer.exe (PID: 2028)
- chrome.exe (PID: 3236)
Reads the machine GUID from the registry
- 吾爱破解论坛网络诊断修复工具 v2.5.exe (PID: 4064)
Creates files or folders in the user directory
- 吾爱破解论坛网络诊断修复工具 v2.5.exe (PID: 4064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:06:12 09:58:13+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 2637312 |
| InitializedDataSize: | 1690480 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa40fa7 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.5.0.0 |
| ProductVersionNumber: | 2.5.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
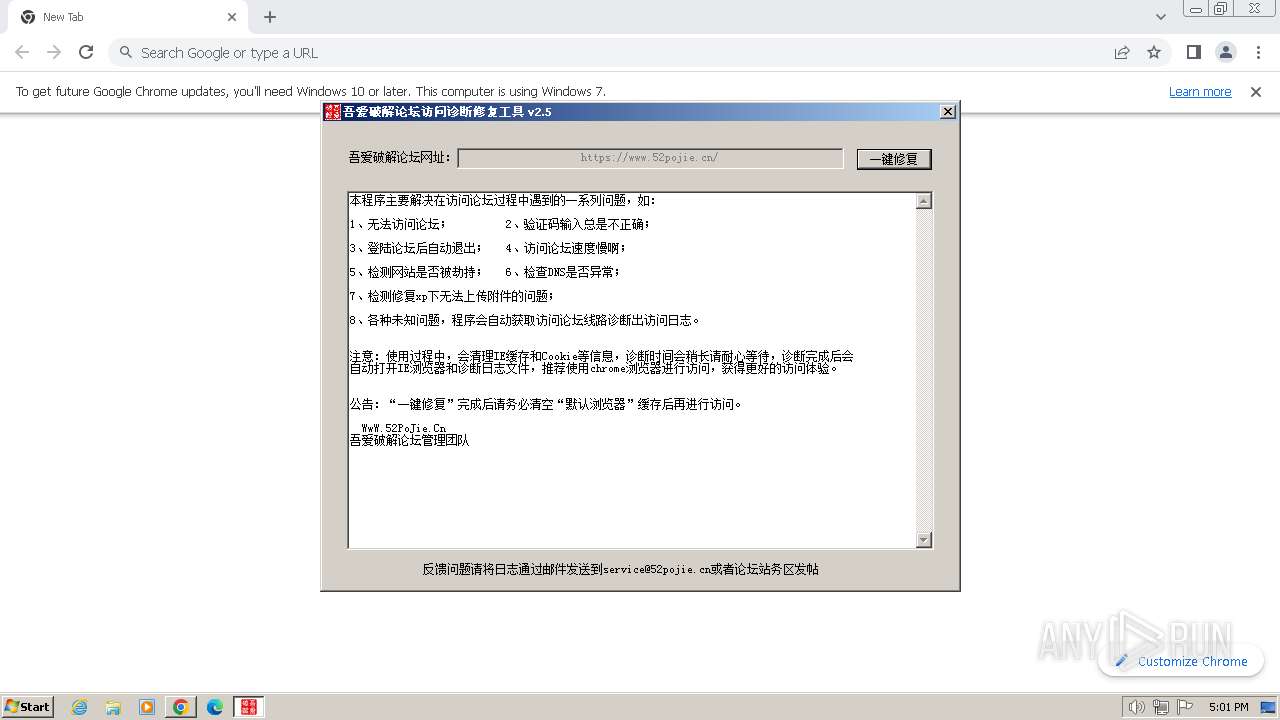
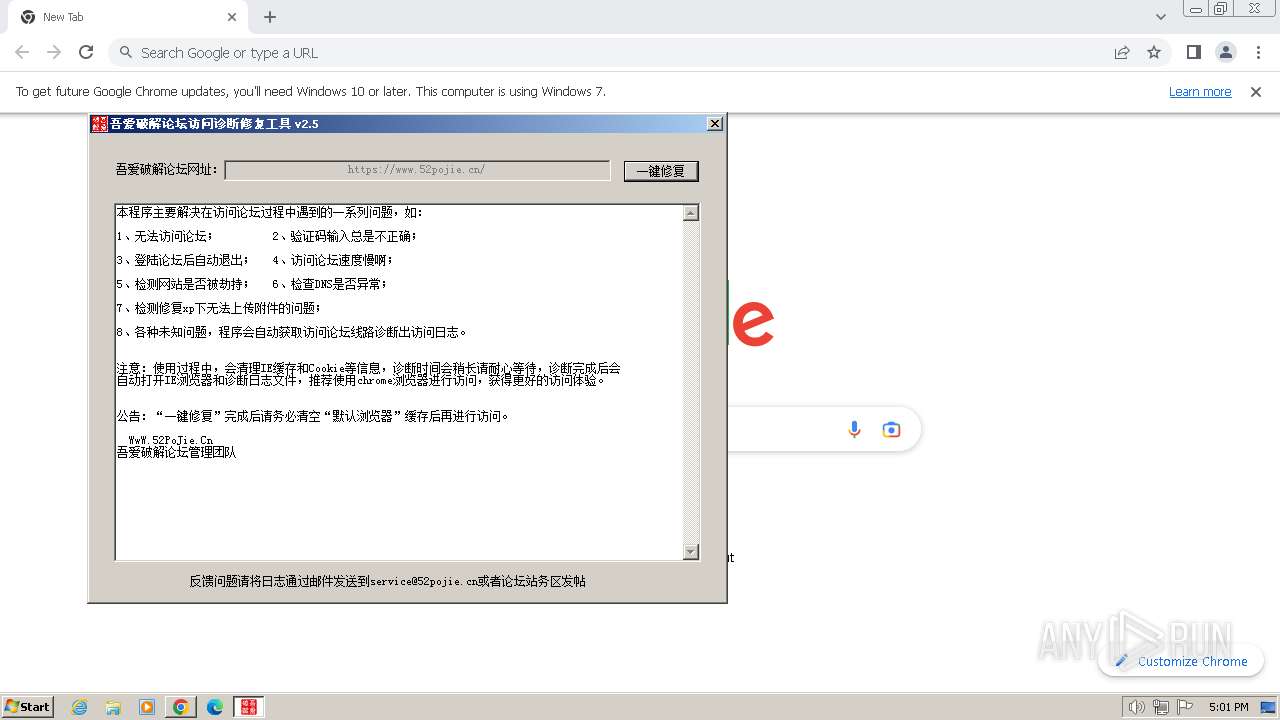
| CompanyName: | 吾爱破解论坛 |
| FileDescription: | <吾爱破解论坛访问诊断修复工具> |
| FileVersion: | 2.5.0.0 |
| InternalName: | 52Tool.exe |
| LegalCopyright: | (C) <吾爱破解论坛>。保留所有权利。 |
| OriginalFileName: | 52Tool.exe |
| ProductName: | <吾爱破解论坛访问诊断修复工具> |
| ProductVersion: | 2.5.0.0 |
Total processes
53
Monitored processes
14
Malicious processes
0
Suspicious processes
1
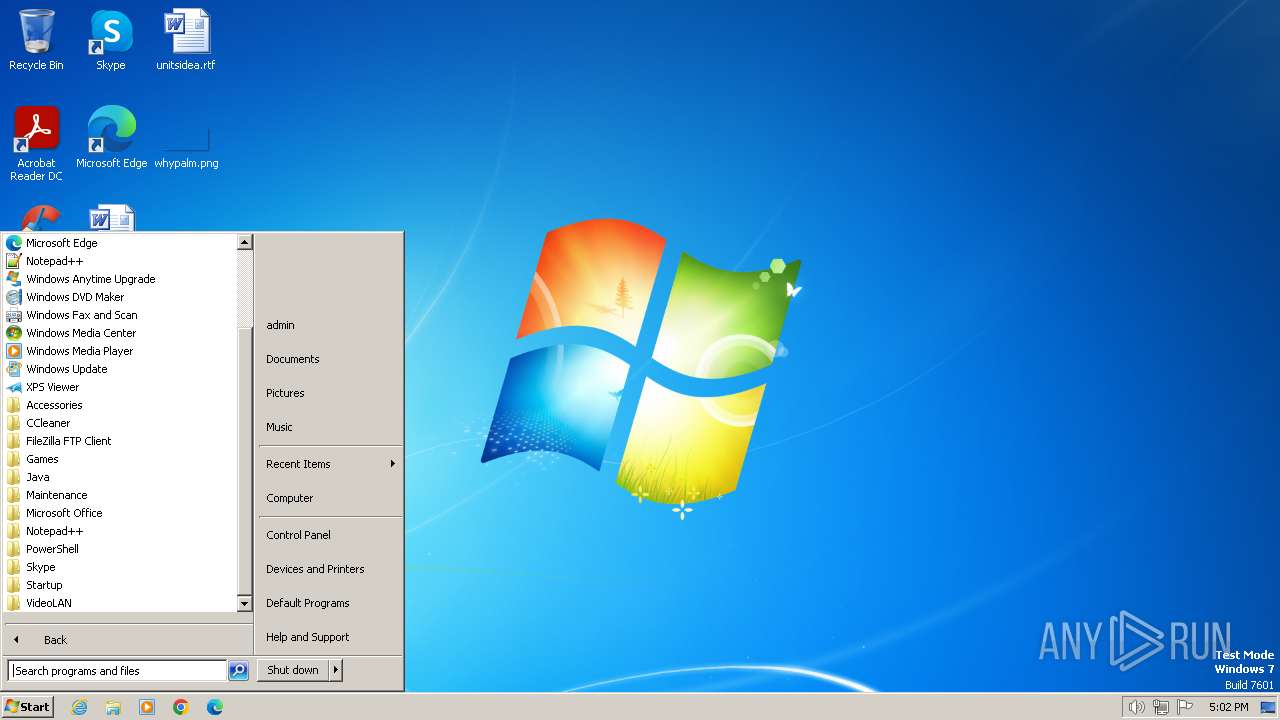
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2028 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=2264 --field-trial-handle=1156,i,10294320143769980022,17735441939265248103,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3104 --field-trial-handle=1156,i,10294320143769980022,17735441939265248103,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2424 | "C:\Users\admin\AppData\Local\Temp\吾爱破解论坛网络诊断修复工具 v2.5.exe" | C:\Users\admin\AppData\Local\Temp\吾爱破解论坛网络诊断修复工具 v2.5.exe | — | explorer.exe | |||||||||||
User: admin Company: 吾爱破解论坛 Integrity Level: MEDIUM Description: <吾爱破解论坛访问诊断修复工具> Exit code: 3221226540 Version: 2.5.0.0 Modules
| |||||||||||||||
| 2496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1104 --field-trial-handle=1156,i,10294320143769980022,17735441939265248103,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1612 --field-trial-handle=1156,i,10294320143769980022,17735441939265248103,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 3000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1456 --field-trial-handle=1156,i,10294320143769980022,17735441939265248103,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 3108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6a888b38,0x6a888b48,0x6a888b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 3236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "--disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 3320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2156 --field-trial-handle=1156,i,10294320143769980022,17735441939265248103,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
3 452
Read events
3 392
Write events
53
Delete events
7
Modification events
| (PID) Process: | (4064) 吾爱破解论坛网络诊断修复工具 v2.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (4064) 吾爱破解论坛网络诊断修复工具 v2.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyServer |
Value: | |||
| (PID) Process: | (4064) 吾爱破解论坛网络诊断修复工具 v2.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyOverride |
Value: | |||
| (PID) Process: | (4064) 吾爱破解论坛网络诊断修复工具 v2.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoConfigURL |
Value: | |||
| (PID) Process: | (4064) 吾爱破解论坛网络诊断修复工具 v2.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoDetect |
Value: | |||
| (PID) Process: | (4064) 吾爱破解论坛网络诊断修复工具 v2.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005C010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4064) 吾爱破解论坛网络诊断修复工具 v2.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4064) 吾爱破解论坛网络诊断修复工具 v2.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4064) 吾爱破解论坛网络诊断修复工具 v2.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4064) 吾爱破解论坛网络诊断修复工具 v2.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
25
Text files
38
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3236 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:— | SHA256:— | |||
| 3236 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:— | SHA256:— | |||
| 3236 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3236 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF197f67.TMP | — | |
MD5:— | SHA256:— | |||
| 3236 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3236 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF197f77.TMP | text | |
MD5:— | SHA256:— | |||
| 3236 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3236 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF197f77.TMP | text | |
MD5:— | SHA256:— | |||
| 3236 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3236 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0cff615a-2b78-4fe8-9085-e68d503ab1b4.tmp | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
14
DNS requests
18
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4064 | 吾爱破解论坛网络诊断修复工具 v2.5.exe | GET | — | 172.67.22.102:80 | http://clientapi.ipip.net/free/ip?ip=&lang=CN | unknown | — | — | unknown |
4064 | 吾爱破解论坛网络诊断修复工具 v2.5.exe | GET | 200 | 220.181.168.203:80 | http://52pojie.sinaapp.com/52pojie.txt | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4064 | 吾爱破解论坛网络诊断修复工具 v2.5.exe | 220.181.168.203:80 | 52pojie.sinaapp.com | IDC, China Telecommunications Corporation | CN | unknown |
3236 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
3000 | chrome.exe | 142.250.185.99:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
3000 | chrome.exe | 74.125.133.84:443 | accounts.google.com | GOOGLE | US | unknown |
3000 | chrome.exe | 142.250.185.164:443 | www.google.com | GOOGLE | US | whitelisted |
3000 | chrome.exe | 216.58.206.35:443 | update.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |
52pojie.sinaapp.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
update.googleapis.com |
| unknown |
www.googleapis.com |
| whitelisted |
clientapi.ipip.net |
| unknown |
whois.pconline.com.cn |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Check Domain in DNS Lookup (whois .pconline .com .cn) |
— | — | Device Retrieving External IP Address Detected | ET INFO External IP Check Domain in DNS Lookup (whois .pconline .com .cn) |