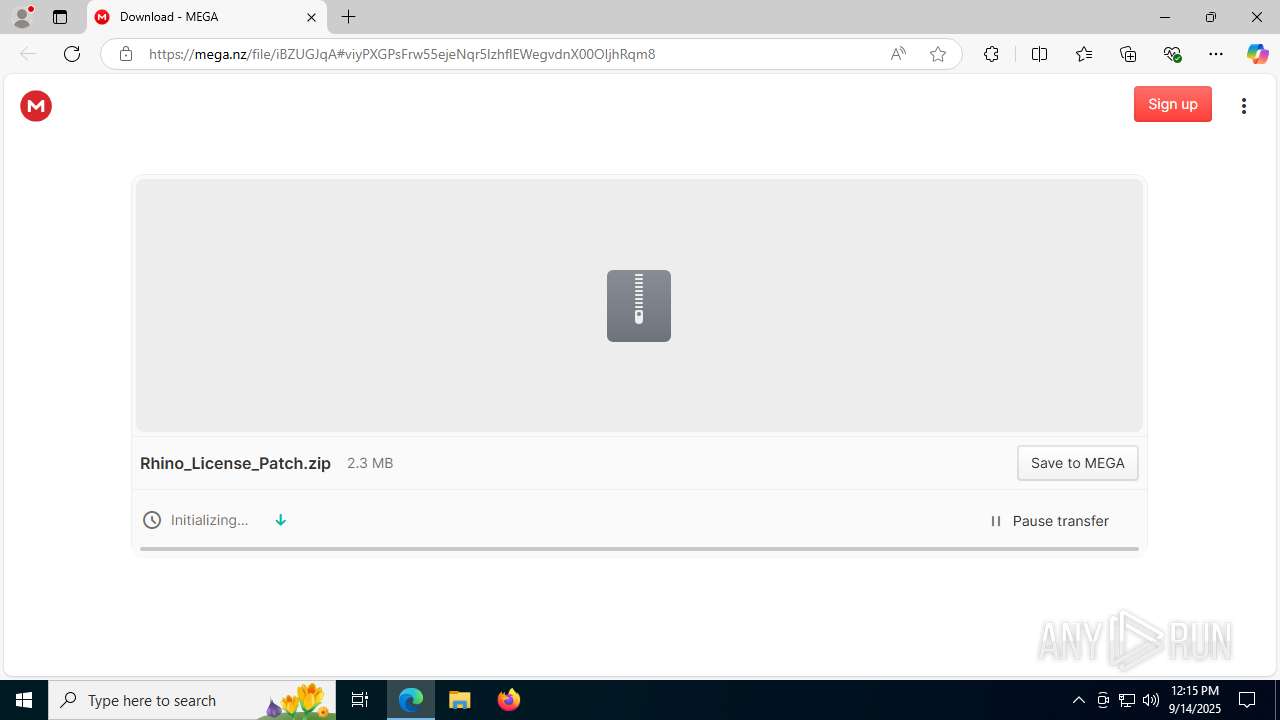
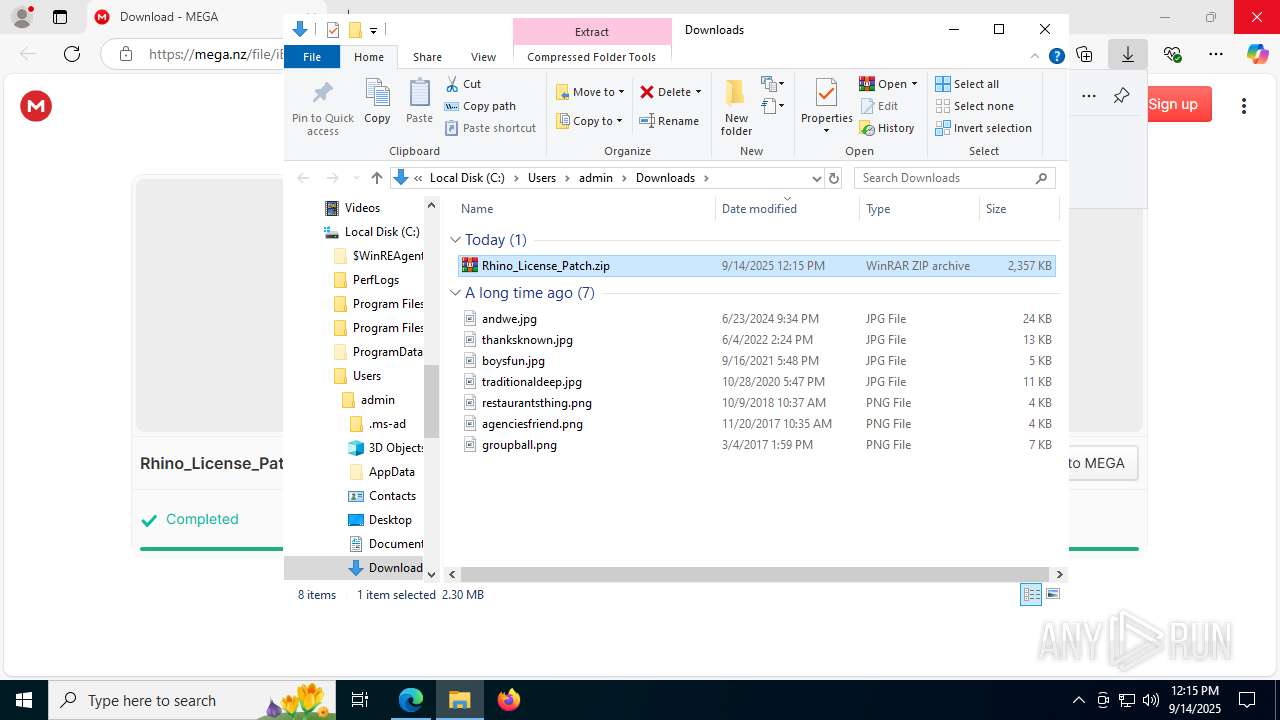
| URL: | https://mega.nz/file/iBZUGJqA#viyPXGPsFrw55ejeNqr5lzhflEWegvdnX00OIjhRqm8 |
| Full analysis: | https://app.any.run/tasks/549e37b6-b4e4-4300-9466-2ec123b62dd1 |
| Verdict: | Malicious activity |
| Analysis date: | September 14, 2025, 12:15:10 |
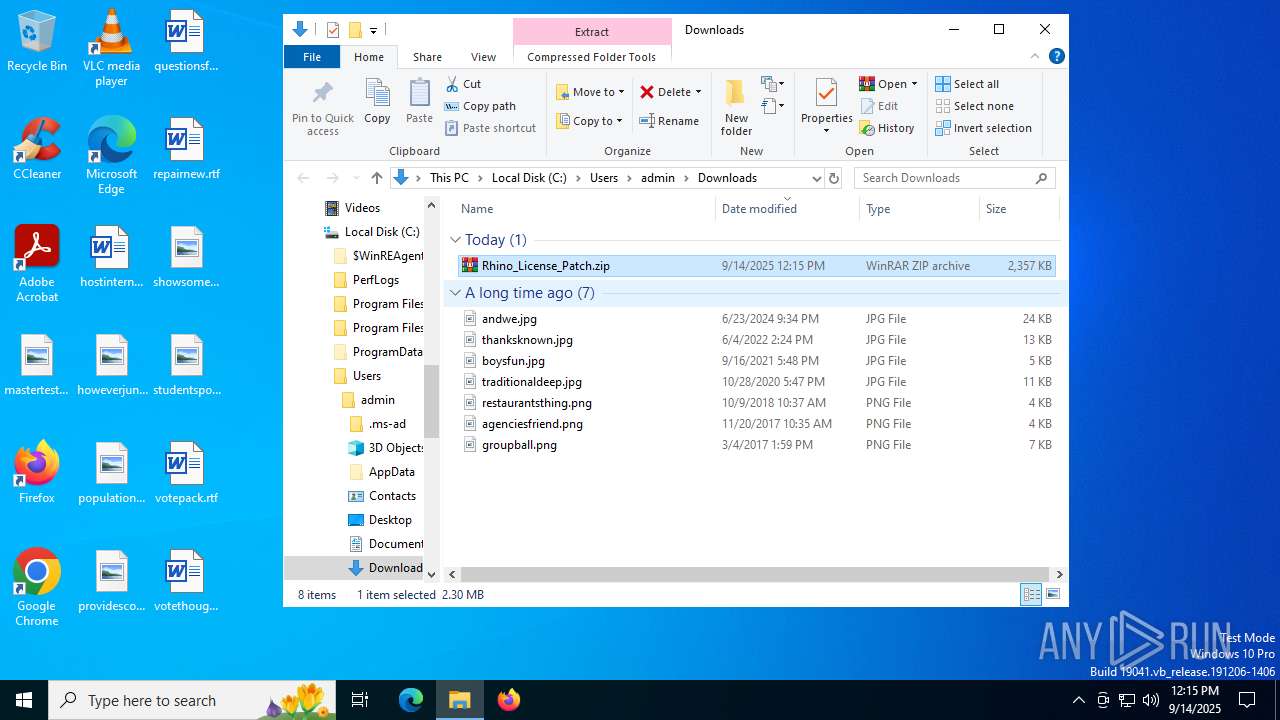
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E8176D391C2E59EDE6184C6C4400D9D5 |
| SHA1: | 460F163DC5D757909E73689C056603F8D848CECF |
| SHA256: | 3DF0CF1D1ADDA4972A716AB3CA9E849A7FD1AE7840A7A536A6146F8A092DCA57 |
| SSDEEP: | 3:N8X/inei1NQQ7r/Rvw6Vmg:28dF7r/ZZn |
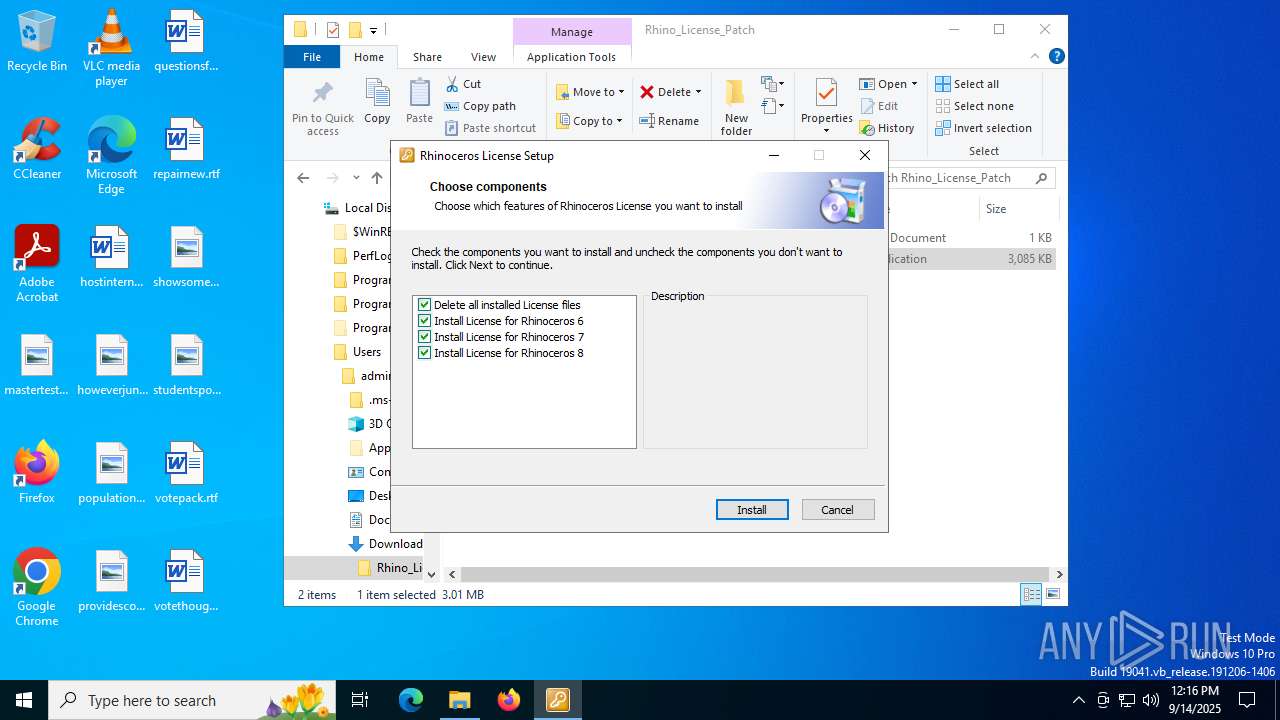
MALICIOUS
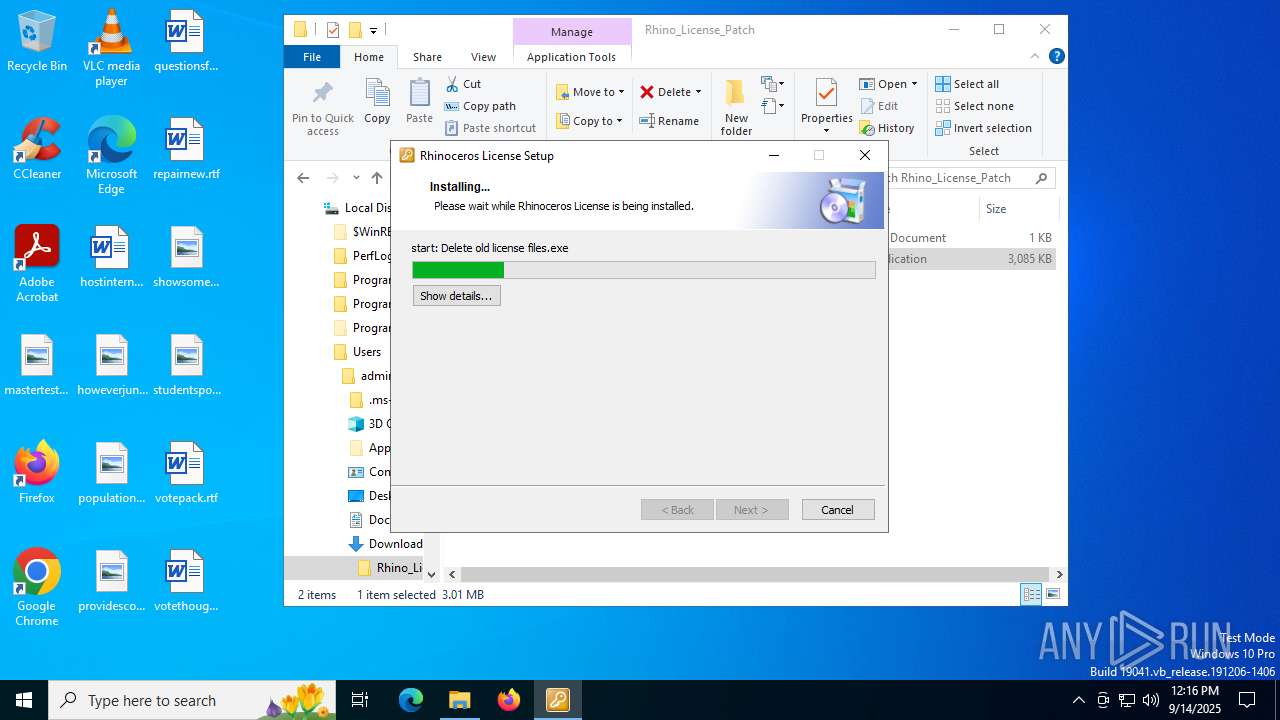
Changes powershell execution policy (Bypass)
- Delete old license files.exe (PID: 4692)
- Adding entries to hosts file.exe (PID: 8064)
- Adding entries to hosts file.exe (PID: 7192)
Bypass execution policy to execute commands
- powershell.exe (PID: 7244)
- powershell.exe (PID: 2288)
- powershell.exe (PID: 4412)
SUSPICIOUS
The process executes Powershell scripts
- Delete old license files.exe (PID: 4692)
- Adding entries to hosts file.exe (PID: 8064)
- Adding entries to hosts file.exe (PID: 7192)
Reads security settings of Internet Explorer
- Delete old license files.exe (PID: 4692)
- Rhinoceros Universal License Patch.exe (PID: 7748)
- Adding entries to hosts file.exe (PID: 8064)
- Installing License for Rhinoceros 8.exe (PID: 7836)
- Adding entries to hosts file.exe (PID: 7192)
Reads the date of Windows installation
- Delete old license files.exe (PID: 4692)
- Adding entries to hosts file.exe (PID: 8064)
- Adding entries to hosts file.exe (PID: 7192)
Starts POWERSHELL.EXE for commands execution
- Delete old license files.exe (PID: 4692)
- Adding entries to hosts file.exe (PID: 8064)
- Adding entries to hosts file.exe (PID: 7192)
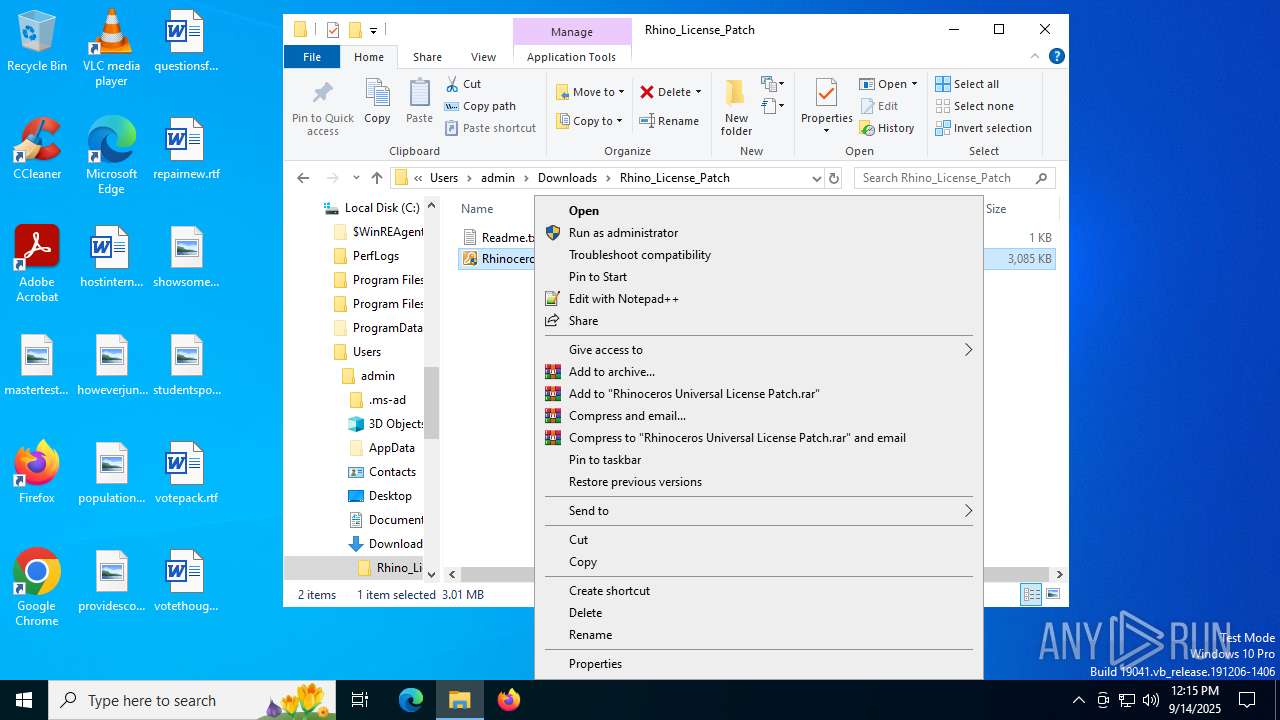
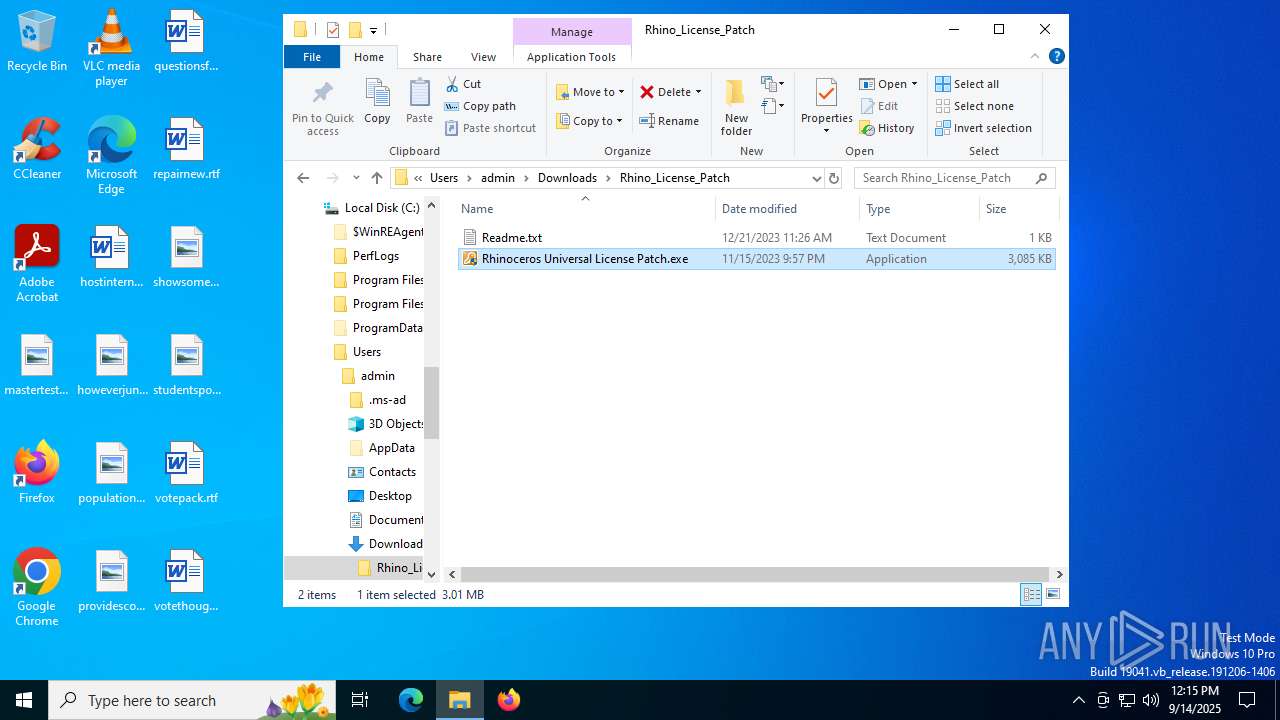
Executable content was dropped or overwritten
- Rhinoceros Universal License Patch.exe (PID: 7748)
- Installing License for Rhinoceros 8.exe (PID: 7836)
Windows service management via SC.EXE
- sc.exe (PID: 2400)
Modifies hosts file to alter network resolution
- powershell.exe (PID: 2288)
There is functionality for taking screenshot (YARA)
- Rhinoceros Universal License Patch.exe (PID: 7748)
Executing commands from ".cmd" file
- Rhinoceros Universal License Patch.exe (PID: 7748)
Starts CMD.EXE for commands execution
- Rhinoceros Universal License Patch.exe (PID: 7748)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 8112)
Stops a currently running service
- sc.exe (PID: 5928)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- cmd.exe (PID: 8112)
Starts itself from another location
- Rhinoceros Universal License Patch.exe (PID: 7748)
INFO
Application launched itself
- msedge.exe (PID: 6680)
- msedge.exe (PID: 7624)
Reads the computer name
- identity_helper.exe (PID: 7528)
- identity_helper.exe (PID: 7336)
- Rhinoceros Universal License Patch.exe (PID: 7748)
- Delete old license files.exe (PID: 4692)
- Adding entries to hosts file.exe (PID: 8064)
- Adding entries to hosts file.exe (PID: 7192)
- Installing License for Rhinoceros 8.exe (PID: 7836)
The sample compiled with english language support
- msedge.exe (PID: 6680)
- WinRAR.exe (PID: 3788)
- Rhinoceros Universal License Patch.exe (PID: 7748)
Reads Environment values
- identity_helper.exe (PID: 7528)
- identity_helper.exe (PID: 7336)
Checks supported languages
- identity_helper.exe (PID: 7528)
- identity_helper.exe (PID: 7336)
- Rhinoceros Universal License Patch.exe (PID: 7748)
- Delete old license files.exe (PID: 4692)
- Adding entries to hosts file.exe (PID: 8064)
- Adding entries to hosts file.exe (PID: 7192)
- Installing License for Rhinoceros 8.exe (PID: 7836)
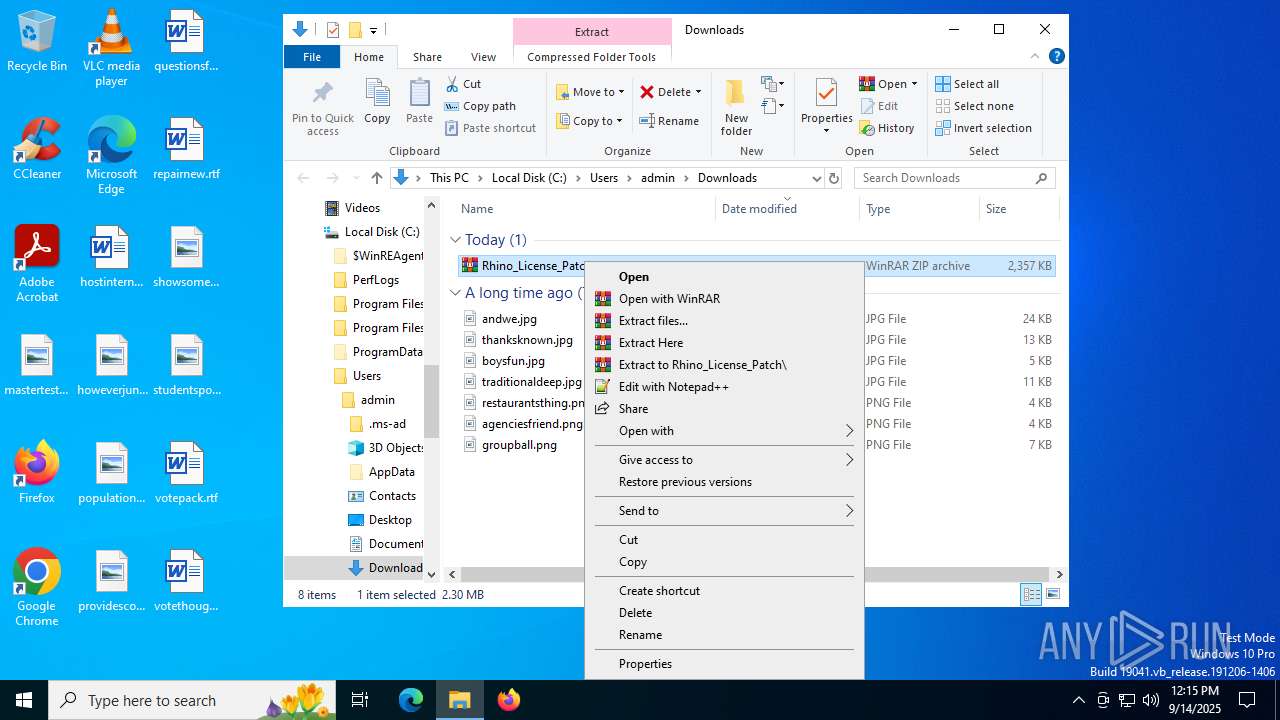
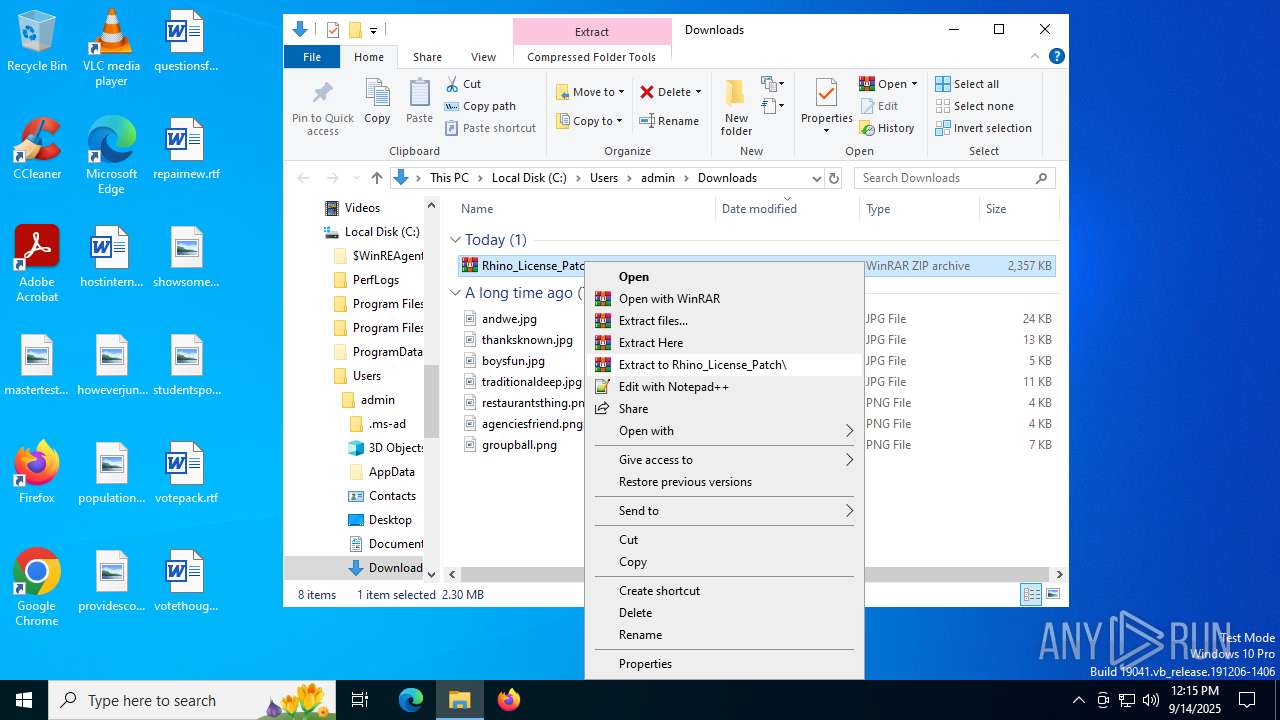
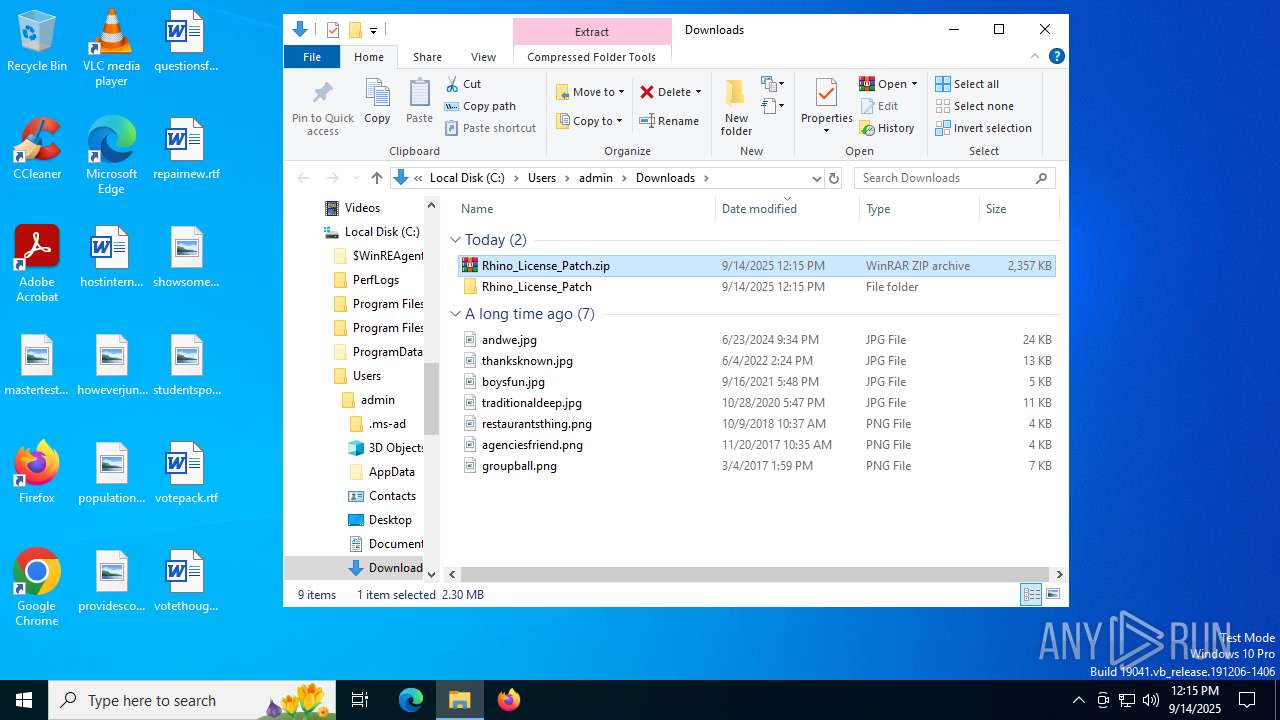
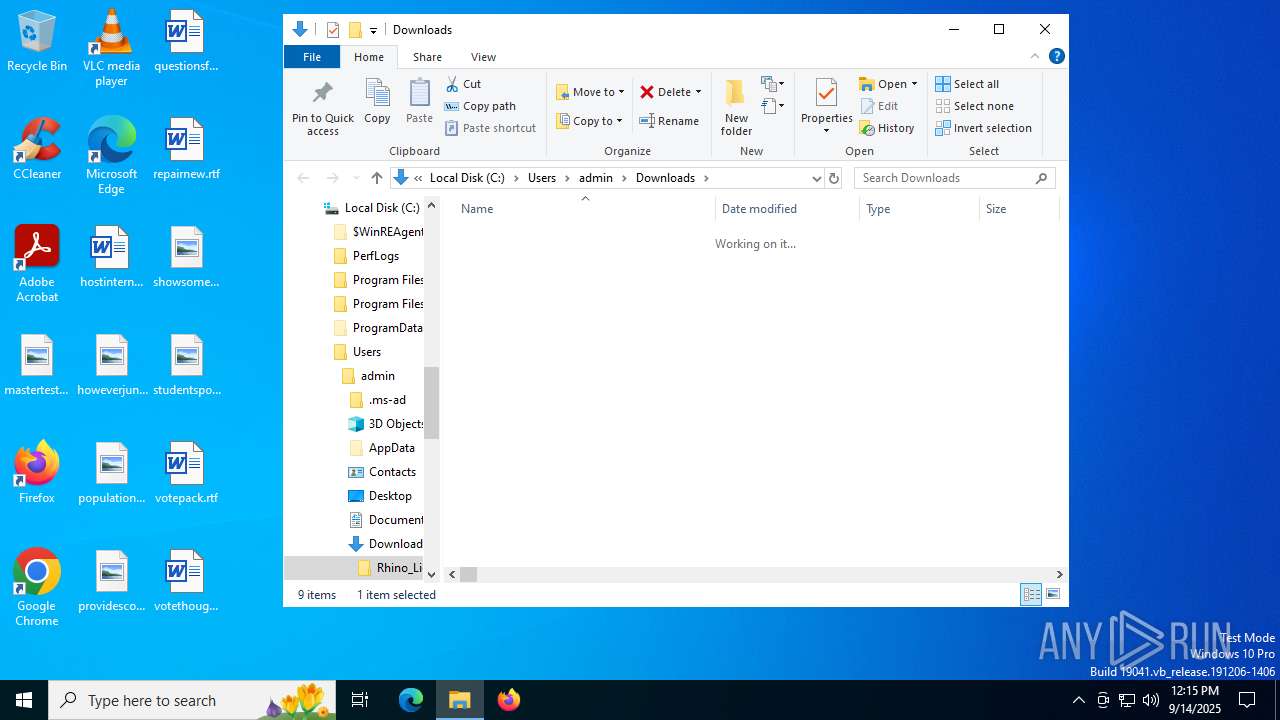
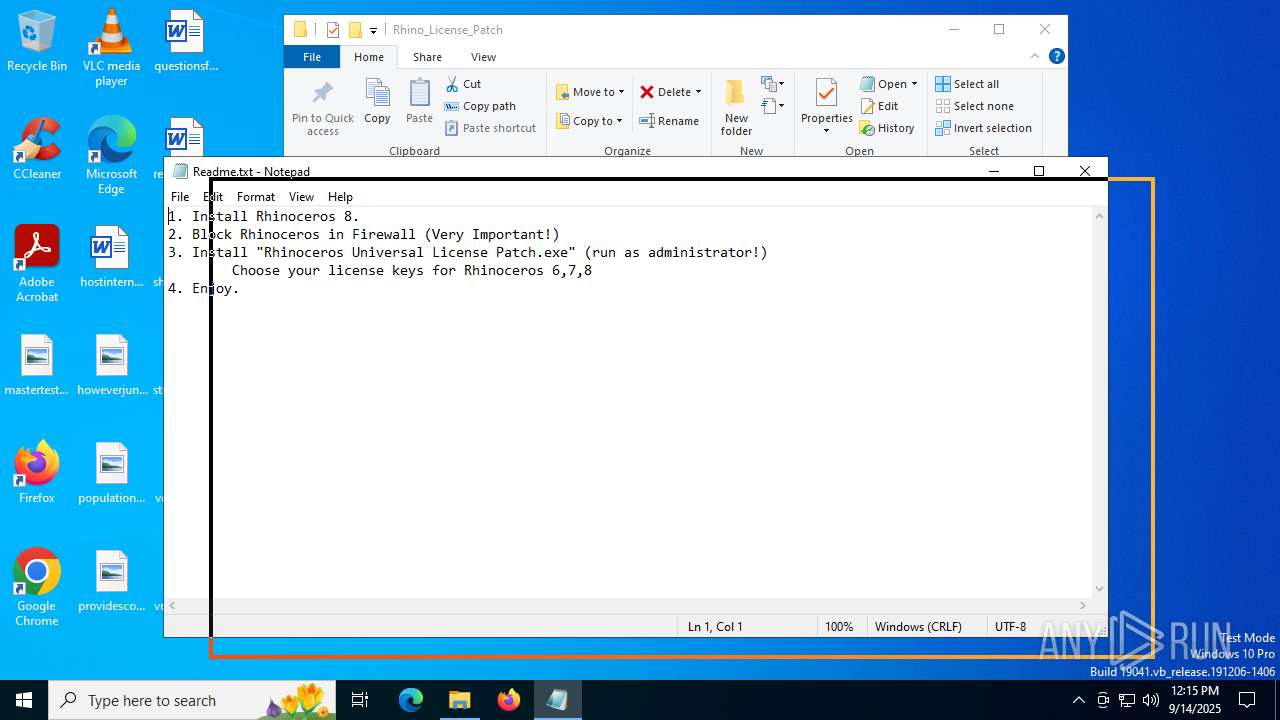
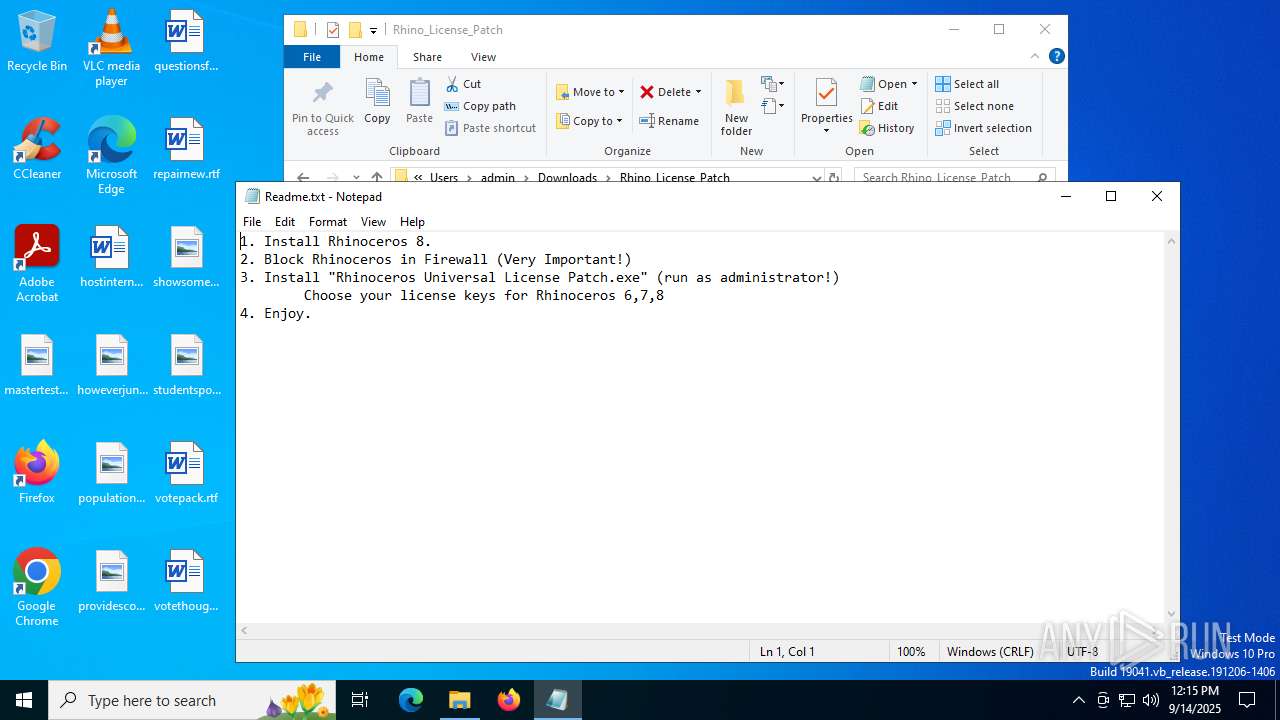
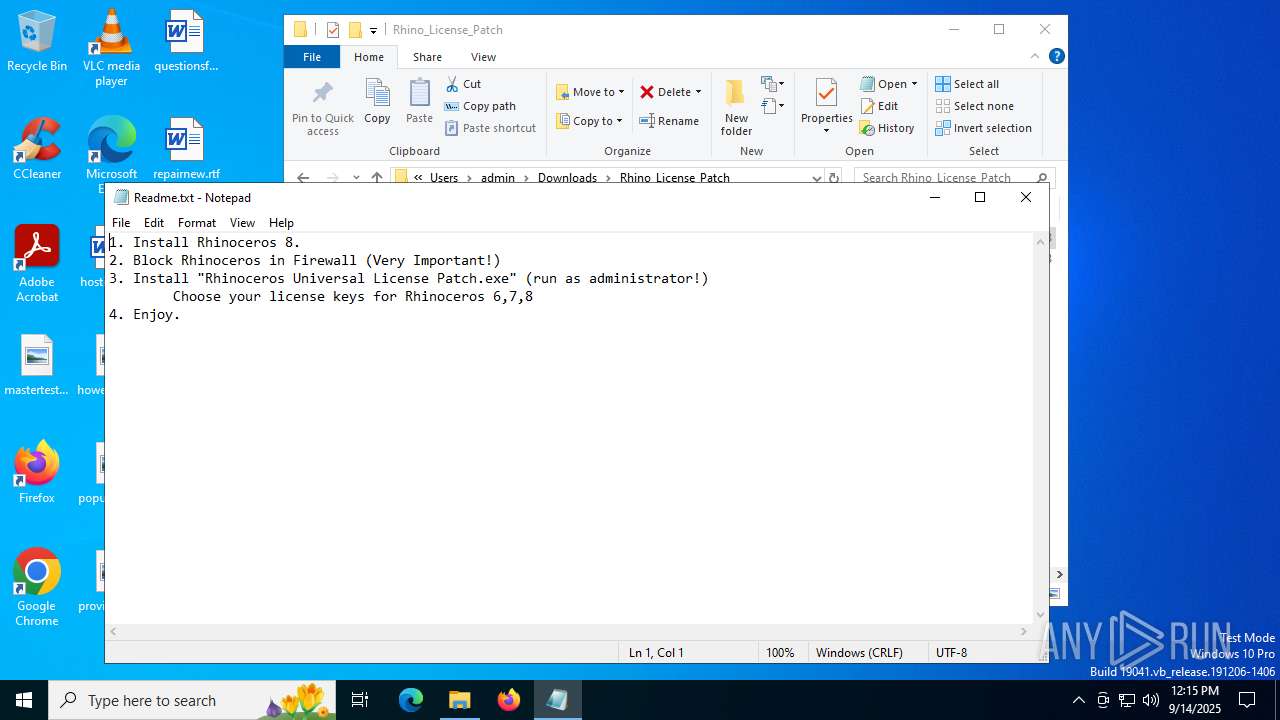
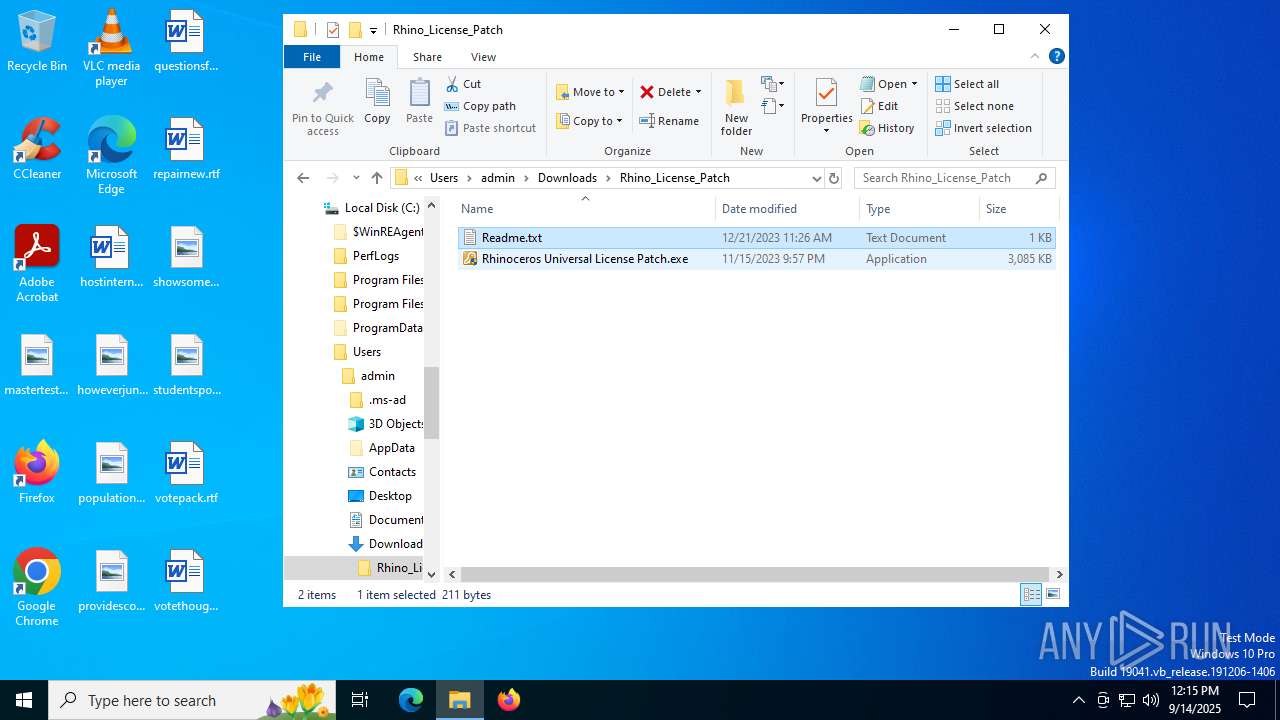
Manual execution by a user
- WinRAR.exe (PID: 3788)
- notepad.exe (PID: 6180)
- Rhinoceros Universal License Patch.exe (PID: 7748)
Reads security settings of Internet Explorer
- notepad.exe (PID: 6180)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3788)
Process checks computer location settings
- Delete old license files.exe (PID: 4692)
- Adding entries to hosts file.exe (PID: 8064)
- Adding entries to hosts file.exe (PID: 7192)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7244)
Create files in a temporary directory
- Delete old license files.exe (PID: 4692)
- Adding entries to hosts file.exe (PID: 8064)
- Rhinoceros Universal License Patch.exe (PID: 7748)
- Installing License for Rhinoceros 8.exe (PID: 7836)
- Adding entries to hosts file.exe (PID: 7192)
Reads the machine GUID from the registry
- Rhinoceros Universal License Patch.exe (PID: 7748)
- Installing License for Rhinoceros 8.exe (PID: 7836)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
217
Monitored processes
81
Malicious processes
2
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2804,i,9721811601133463341,16715921624299310735,262144 --variations-seed-version --mojo-platform-channel-handle=2792 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1040 | netsh advfirewall firewall delete rule name=all program="C:\Program Files\Rhinoceros 5 (64-bit)\System\Rhino.exe" | C:\Windows\SysWOW64\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1160 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=5072,i,8241911656378561600,8071103427956246826,262144 --variations-seed-version --mojo-platform-channel-handle=5088 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1332 | netsh advfirewall firewall add rule name="Rhino 6 Yak" dir=out program="C:\Program Files\Rhino 6\System\Yak.exe" profile=any action=block | C:\Windows\SysWOW64\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1336 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1568 | netsh advfirewall firewall add rule name="Rhino 6 Yak" dir=in program="C:\Program Files\Rhino 6\System\Yak.exe" profile=any action=block | C:\Windows\SysWOW64\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1728 | netsh advfirewall firewall delete rule name=all program="C:\Program Files\Rhinoceros 5 (64-bit)\System\RmaErrorReporting.exe" | C:\Windows\SysWOW64\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2032 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x304,0x308,0x30c,0x2fc,0x314,0x7ffc443cf208,0x7ffc443cf214,0x7ffc443cf220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2032 | netsh advfirewall firewall add rule name="Rhino 5 RmaErrorReporting" dir=out program="C:\Program Files\Rhinoceros 5 (64-bit)\System\RmaErrorReporting.exe" profile=any action=block | C:\Windows\SysWOW64\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2112 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x29c,0x2a0,0x2a4,0x294,0x1e0,0x7ffc443cf208,0x7ffc443cf214,0x7ffc443cf220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
29 812
Read events
29 777
Write events
35
Delete events
0
Modification events
| (PID) Process: | (6680) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6680) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6680) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6680) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6680) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: FF819E1F589D2F00 | |||
| (PID) Process: | (6680) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590370 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {697A492C-1065-4456-877E-072EA0E24696} | |||
| (PID) Process: | (6680) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590370 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {766B6817-97A9-45AD-AE5B-8645D7A79E5A} | |||
| (PID) Process: | (6680) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 15E6C51F589D2F00 | |||
| (PID) Process: | (6680) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (6680) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
19
Suspicious files
189
Text files
107
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF18da4e.TMP | — | |
MD5:— | SHA256:— | |||
| 6680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF18da5d.TMP | — | |
MD5:— | SHA256:— | |||
| 6680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF18da5d.TMP | — | |
MD5:— | SHA256:— | |||
| 6680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF18da6d.TMP | — | |
MD5:— | SHA256:— | |||
| 6680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF18da8c.TMP | — | |
MD5:— | SHA256:— | |||
| 6680 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
98
DNS requests
70
Threats
32
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6408 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:K6QR76cfSQRTIJvxESiAMCEPj3imsrs40bl1UZDURXc&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
4060 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.32.238.112:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8028 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8028 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
8028 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8028 | SIHClient.exe | GET | 200 | 23.32.238.112:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
8028 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | unknown | — | — | whitelisted |
8028 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1976 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6408 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6408 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6408 | msedge.exe | 31.216.144.5:443 | mega.nz | Datacenter Luxembourg S.A. | LU | whitelisted |
6408 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6408 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
mega.nz |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
eu.static.mega.co.nz |
| whitelisted |
xpaywalletcdn.azureedge.net |
| whitelisted |
g.api.mega.co.nz |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6408 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
6408 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
6408 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
6408 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
6408 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
6408 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
6408 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
6408 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
6408 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
6408 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |