| File name: | malware.bin |
| Full analysis: | https://app.any.run/tasks/a5879556-86c7-40fa-88f8-a0920a41d356 |
| Verdict: | Malicious activity |
| Analysis date: | June 13, 2019, 10:53:26 |
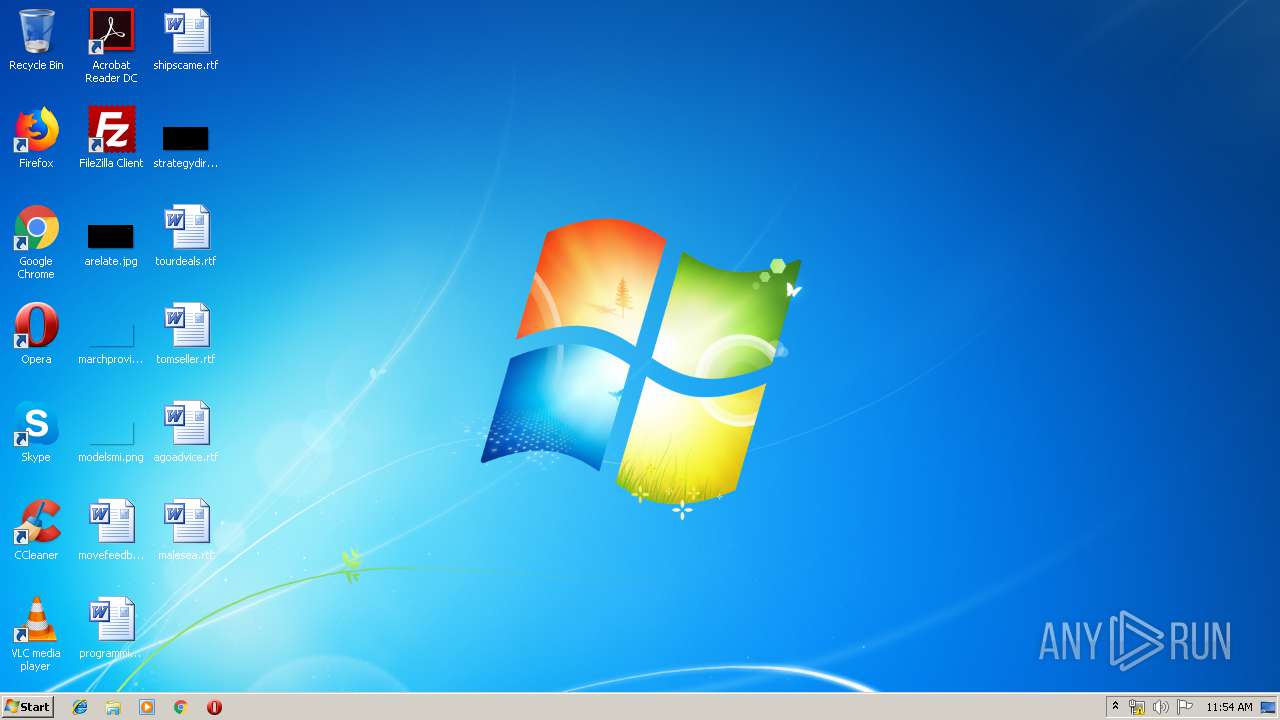
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7B44B67425CB3B8EF7D420DE2FF3DB37 |
| SHA1: | 2AF8AE87ECBA695A68E60F63DF14D2C843A52DF9 |
| SHA256: | 3DE9285180D464E7C1E6331C7BF43BC3941E0F665F66B855103C6BEE8E4C038E |
| SSDEEP: | 12288:92Ka2pRmH6ysvWsmYDMtNhkxh3dfhg4OQYZeVHgMkakT/xdV+hoJ/R:9fvlmYDMt0ZuZeVeT/xX+hoJ |
MALICIOUS
Application was dropped or rewritten from another process
- TurboMeeting.exe (PID: 2684)
- TurboMeeting.exe (PID: 3396)
- TMLauncher.exe (PID: 3580)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 2080)
- TurboMeeting.exe (PID: 2684)
- TurboMeeting.exe (PID: 3396)
SUSPICIOUS
Executable content was dropped or overwritten
- malware.bin.exe (PID: 3660)
- TMLauncher.exe (PID: 3580)
- TurboMeeting.exe (PID: 2684)
Modifies the open verb of a shell class
- TMLauncher.exe (PID: 3580)
Creates files in the program directory
- TurboMeeting.exe (PID: 2684)
Creates a software uninstall entry
- TurboMeeting.exe (PID: 2684)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:01:18 09:01:58+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 395776 |
| InitializedDataSize: | 294400 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3a36e |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | RHUB Communications, Inc. |
| FileDescription: | MeetingStarter |
| FileVersion: | 1 |
| InternalName: | MeetingStarter.exe |
| LegalCopyright: | Copyright (c) 2003-2013 |
| OriginalFileName: | MeetingStarter.exe |
| ProductName: | Meeting Starter |
| ProductVersion: | 1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Jan-2018 08:01:58 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | RHUB Communications, Inc. |
| FileDescription: | MeetingStarter |
| FileVersion: | 1.0 |
| InternalName: | MeetingStarter.exe |
| LegalCopyright: | Copyright (c) 2003-2013 |
| OriginalFilename: | MeetingStarter.exe |
| ProductName: | Meeting Starter |
| ProductVersion: | 1.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 18-Jan-2018 08:01:58 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000608B1 | 0x00060A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.6298 |
.rdata | 0x00062000 | 0x0001E054 | 0x0001E200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.4667 |
.data | 0x00081000 | 0x000148E0 | 0x00008A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.33615 |
.rsrc | 0x00096000 | 0x0000E228 | 0x0000E400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.18414 |
.reloc | 0x000A5000 | 0x00006C98 | 0x00006E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.61315 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.1126 | 977 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 1.06208 | 2216 | UNKNOWN | English - United States | RT_ICON |
3 | 1.32583 | 5672 | UNKNOWN | English - United States | RT_ICON |
4 | 4.91149 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 3.15425 | 9640 | UNKNOWN | English - United States | RT_ICON |
6 | 3.51059 | 9640 | UNKNOWN | English - United States | RT_ICON |
7 | 3.94107 | 1128 | UNKNOWN | English - United States | RT_ICON |
8 | 3.02695 | 308 | UNKNOWN | English - United States | RT_CURSOR |
9 | 2.74274 | 180 | UNKNOWN | English - United States | RT_CURSOR |
10 | 2.34038 | 308 | UNKNOWN | English - United States | RT_CURSOR |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEACC.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
WININET.dll |
Total processes
39
Monitored processes
5
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2080 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe5_ Global\UsGthrCtrlFltPipeMssGthrPipe5 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2684 | "C:\Users\Public\MXmeeting\TurboMeeting\TurboMeeting.exe" --program C:\Users\Public\MXmeeting\TurboMeeting\rsp1024hcmd.txt | C:\Users\Public\MXmeeting\TurboMeeting\TurboMeeting.exe | TMLauncher.exe | ||||||||||||
User: admin Company: RHUB Communications, Inc. Integrity Level: HIGH Description: TurboMeeting Exit code: 0 Version: 7.0.0.0 Modules
| |||||||||||||||
| 3396 | TurboMeeting.exe --VSEDetect | C:\Users\Public\MXmeeting\TurboMeeting\TurboMeeting.exe | — | TurboMeeting.exe | |||||||||||
User: admin Company: RHUB Communications, Inc. Integrity Level: HIGH Description: TurboMeeting Exit code: 0 Version: 7.0.0.0 Modules
| |||||||||||||||
| 3580 | "C:\Users\admin\AppData\Local\Temp\tm_starter_dir\TMLauncher.exe" | C:\Users\admin\AppData\Local\Temp\tm_starter_dir\TMLauncher.exe | malware.bin.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3660 | "C:\Users\admin\AppData\Local\Temp\malware.bin.exe" | C:\Users\admin\AppData\Local\Temp\malware.bin.exe | explorer.exe | ||||||||||||
User: admin Company: RHUB Communications, Inc. Integrity Level: MEDIUM Description: MeetingStarter Exit code: 2 Version: 1.0 Modules
| |||||||||||||||
Total events
967
Read events
933
Write events
34
Delete events
0
Modification events
| (PID) Process: | (3660) malware.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\malware_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3660) malware.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\malware_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3660) malware.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\malware_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3660) malware.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\malware_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3660) malware.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\malware_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3660) malware.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\malware_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3660) malware.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\malware_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3660) malware.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\malware_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3660) malware.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\malware_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3660) malware.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\malware_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
37
Suspicious files
0
Text files
189
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3660 | malware.bin.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\get_client_size[1].htm | — | |
MD5:— | SHA256:— | |||
| 3660 | malware.bin.exe | C:\Users\admin\AppData\Local\Temp\PCClient.zip | — | |
MD5:— | SHA256:— | |||
| 3660 | malware.bin.exe | C:\Users\admin\AppData\Local\Temp\tm_starter_dir\dictionary_client_CHIT.tmd | text | |
MD5:— | SHA256:— | |||
| 3660 | malware.bin.exe | C:\Users\admin\AppData\Local\Temp\tm_starter_dir\dictionary_client_ENG.tmd | text | |
MD5:— | SHA256:— | |||
| 3660 | malware.bin.exe | C:\Users\admin\AppData\Local\Temp\tm_starter_dir\dictionary_client_DTH.tmd | text | |
MD5:— | SHA256:— | |||
| 3660 | malware.bin.exe | C:\Users\admin\AppData\Local\Temp\tm_starter_dir\dictionary_client_GER.tmd | text | |
MD5:— | SHA256:— | |||
| 3660 | malware.bin.exe | C:\Users\admin\AppData\Local\Temp\tm_starter_dir\dictionary_client_SPA.tmd | text | |
MD5:— | SHA256:— | |||
| 3660 | malware.bin.exe | C:\Users\admin\AppData\Local\Temp\tm_starter_dir\dictionary_client_JPN.tmd | text | |
MD5:— | SHA256:— | |||
| 3660 | malware.bin.exe | C:\Users\admin\AppData\Local\Temp\tm_starter_dir\dictionary_client_CHI.tmd | text | |
MD5:— | SHA256:— | |||
| 3660 | malware.bin.exe | C:\Users\admin\AppData\Local\Temp\tm_starter_dir\dictionary_client_PRT.tmd | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
1
DNS requests
2
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
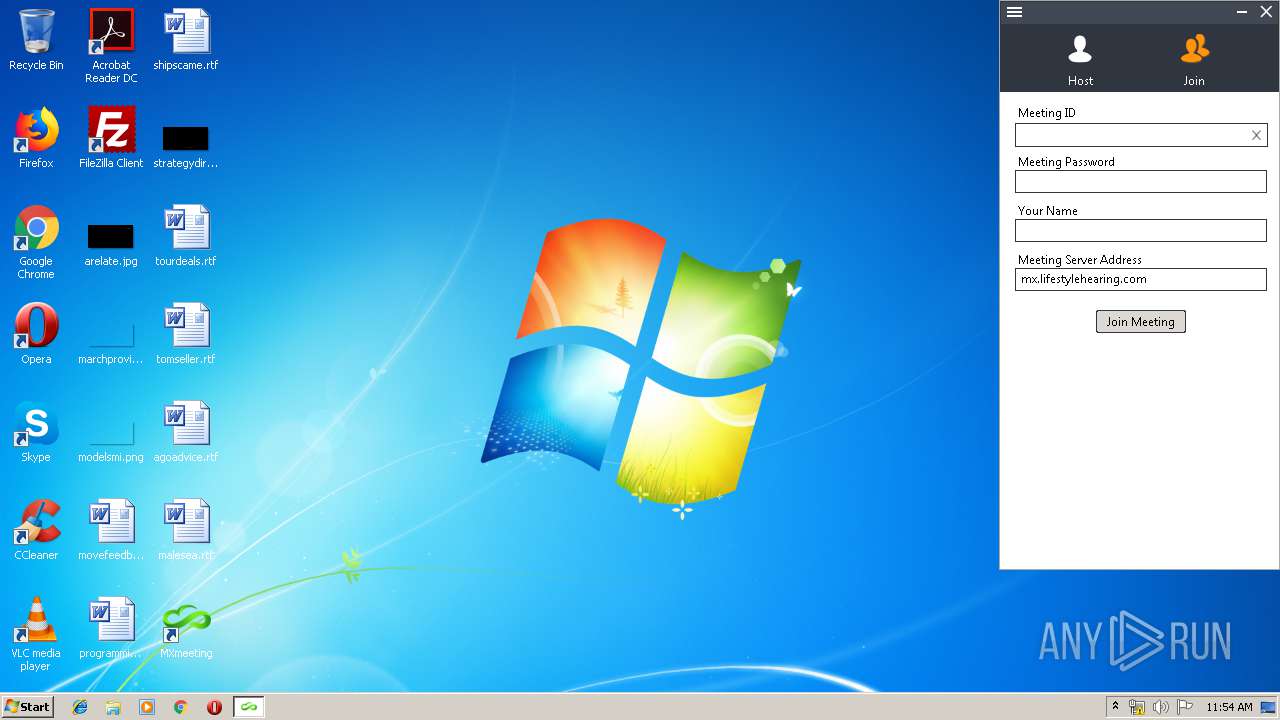
3660 | malware.bin.exe | GET | 200 | 208.72.179.221:80 | http://mx.lifestylehearing.com/as/wapi/get_client_size?client_type=0&xml_format=Y&client=pc&myrand11262017=jVZVTiLeVawvKIGIfpWHWPxafI8347283&rdm=1560423228 | CA | html | 85 b | suspicious |
3660 | malware.bin.exe | GET | 200 | 208.72.179.221:80 | http://mx.lifestylehearing.com/as/wapi/get_client?client_type=0&client=pc&myrand11262017=lotvkwLSFKWEE3dU6aLGynhMTTI347284&rdm=1560423230 | CA | binary | 9.11 Mb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3660 | malware.bin.exe | 208.72.179.221:80 | mx.lifestylehearing.com | CALGAH Computer Systems and Management Ltd | CA | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mx.lifestylehearing.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3660 | malware.bin.exe | A Network Trojan was detected | ET USER_AGENTS Suspicious User Agent (Microsoft Internet Explorer) |
3660 | malware.bin.exe | A Network Trojan was detected | ET USER_AGENTS Suspicious User Agent (Microsoft Internet Explorer) |