| File name: | InvColPC.exe |
| Full analysis: | https://app.any.run/tasks/6933424d-d2a1-427a-adea-eb123ff39fd1 |
| Verdict: | Malicious activity |
| Analysis date: | April 06, 2021, 15:20:20 |
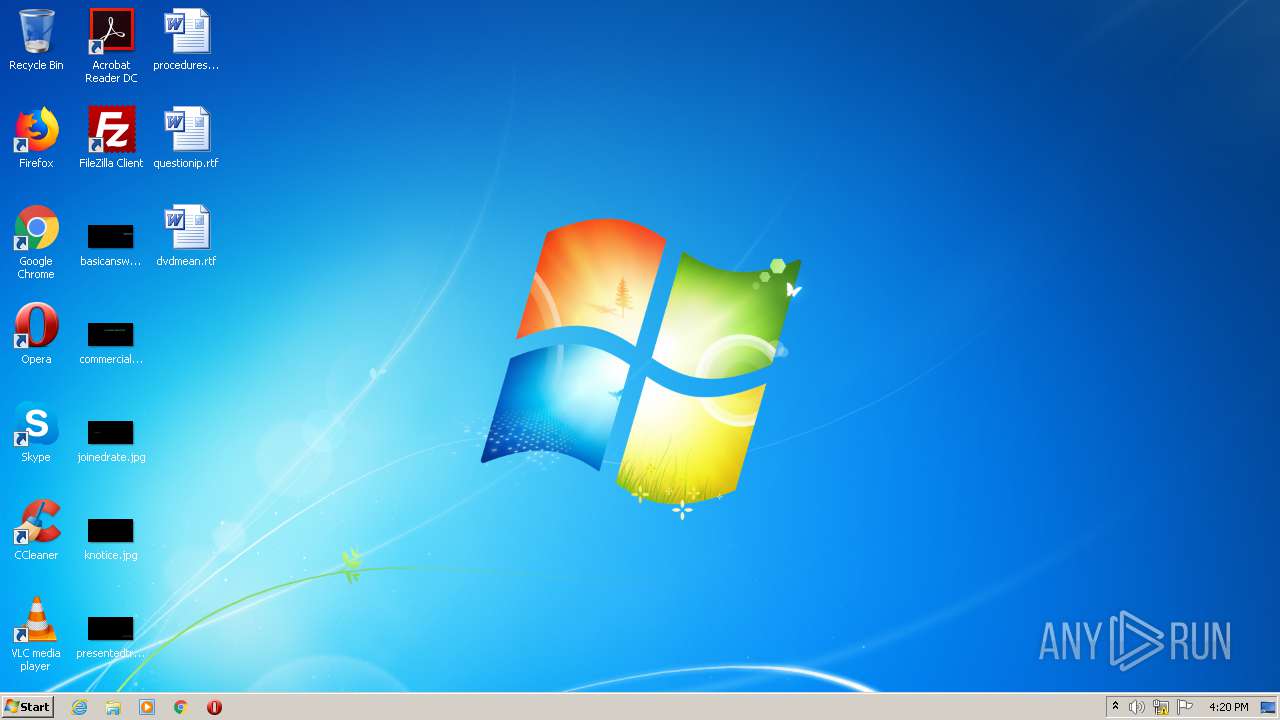
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 46CE00C4F8E034373D23F7D598987E31 |
| SHA1: | 65F97217E4E20BE5E50E597DA025881CA9D8F69C |
| SHA256: | 3DDB25BC9584E311575FAB1FEB2575F2A6995B71EEC4A48463E220B216ABFB9E |
| SSDEEP: | 98304:Qjb5ENHjM500l7y2k8b25DjVwOwPuOAIrqnwhQ+FzNYIDlWQqmLgpOaZAESobEuR:O9tgQsyOwPuOfqwPzNYoUQpLZU+m9P |
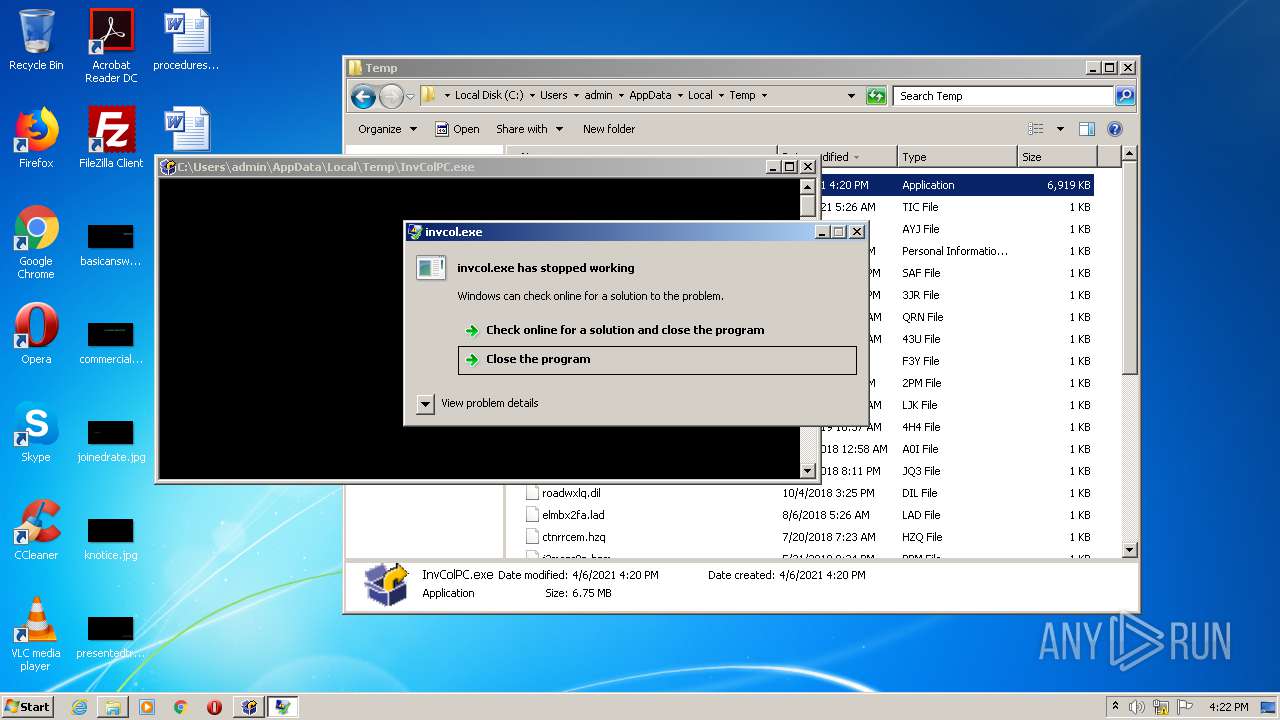
MALICIOUS
Loads dropped or rewritten executable
- invcol.exe (PID: 1544)
- WerFault.exe (PID: 3984)
Application was dropped or rewritten from another process
- invcol.exe (PID: 1544)
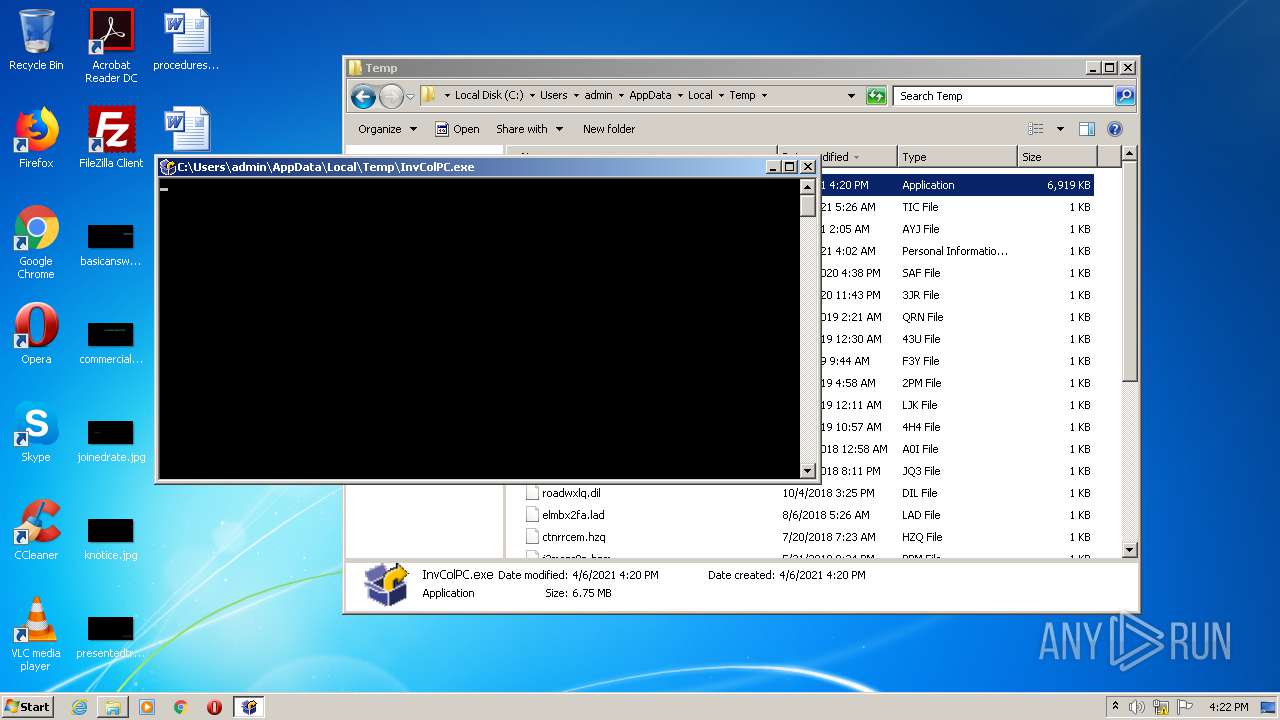
Drops executable file immediately after starts
- InvColPC.exe (PID: 2088)
SUSPICIOUS
Creates files in the program directory
- InvColPC.exe (PID: 2088)
- WerFault.exe (PID: 3984)
Drops a file that was compiled in debug mode
- InvColPC.exe (PID: 2088)
Executable content was dropped or overwritten
- InvColPC.exe (PID: 2088)
Drops a file with a compile date too recent
- InvColPC.exe (PID: 2088)
INFO
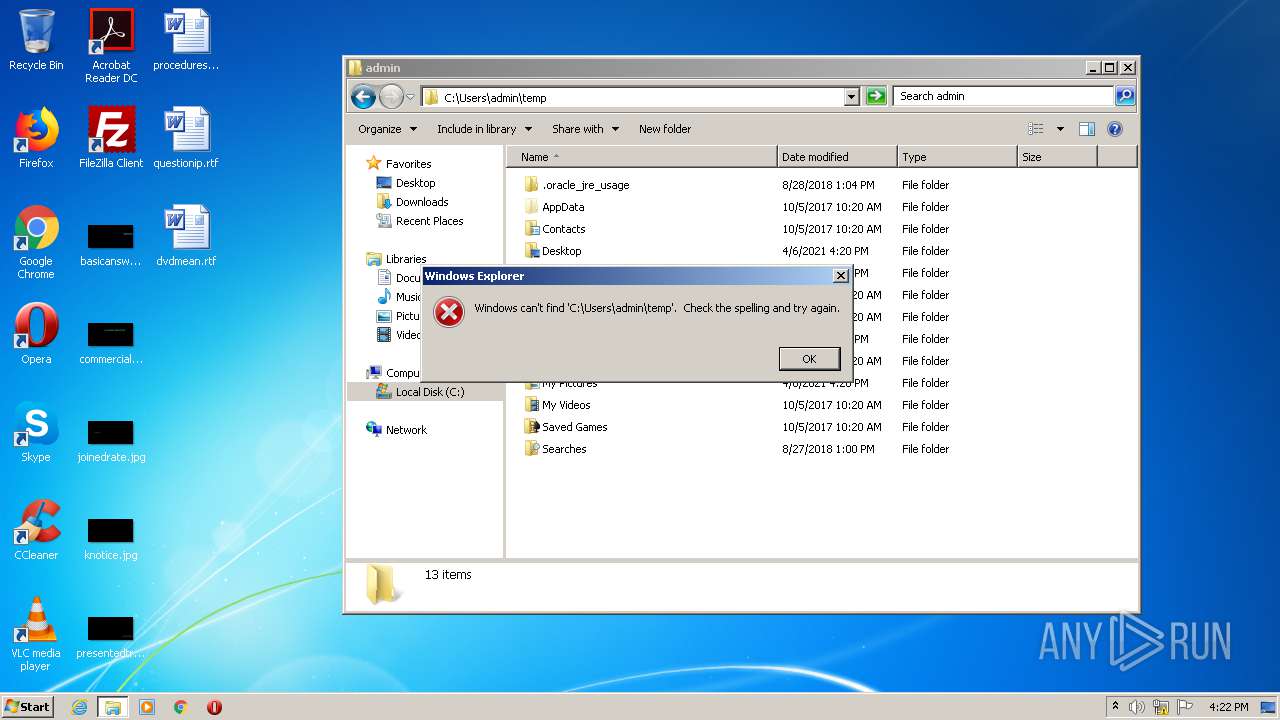
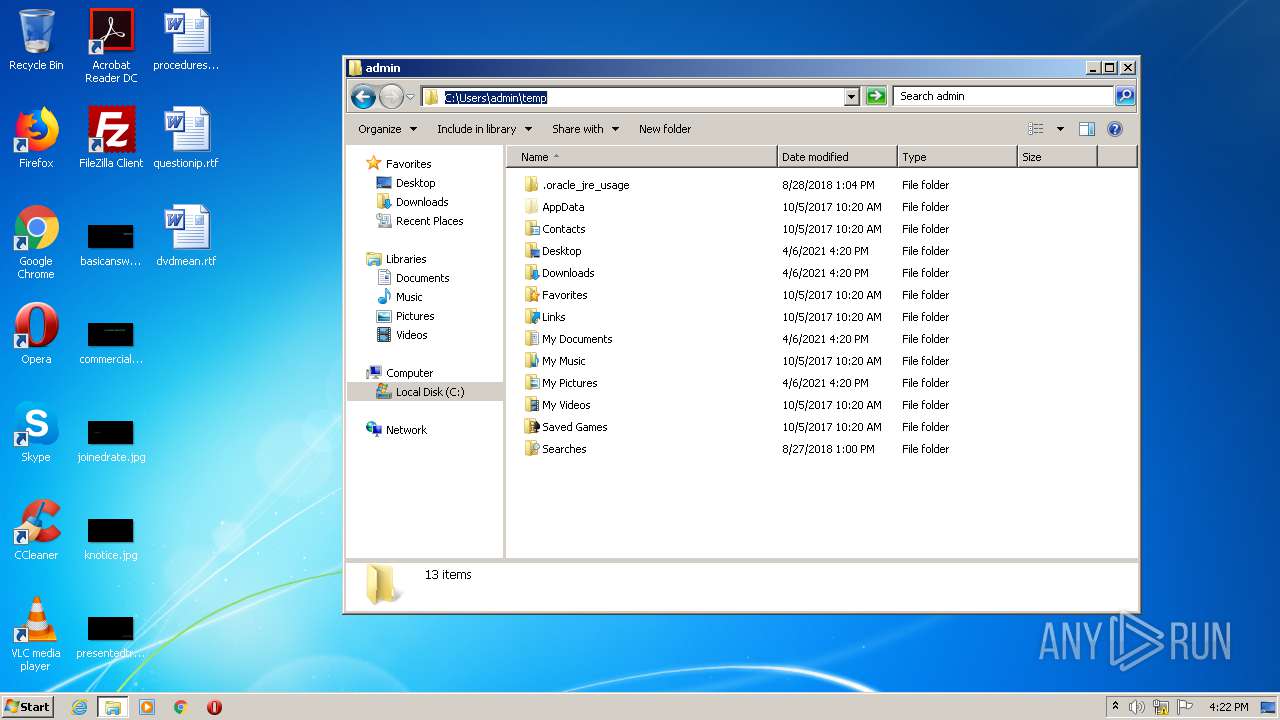
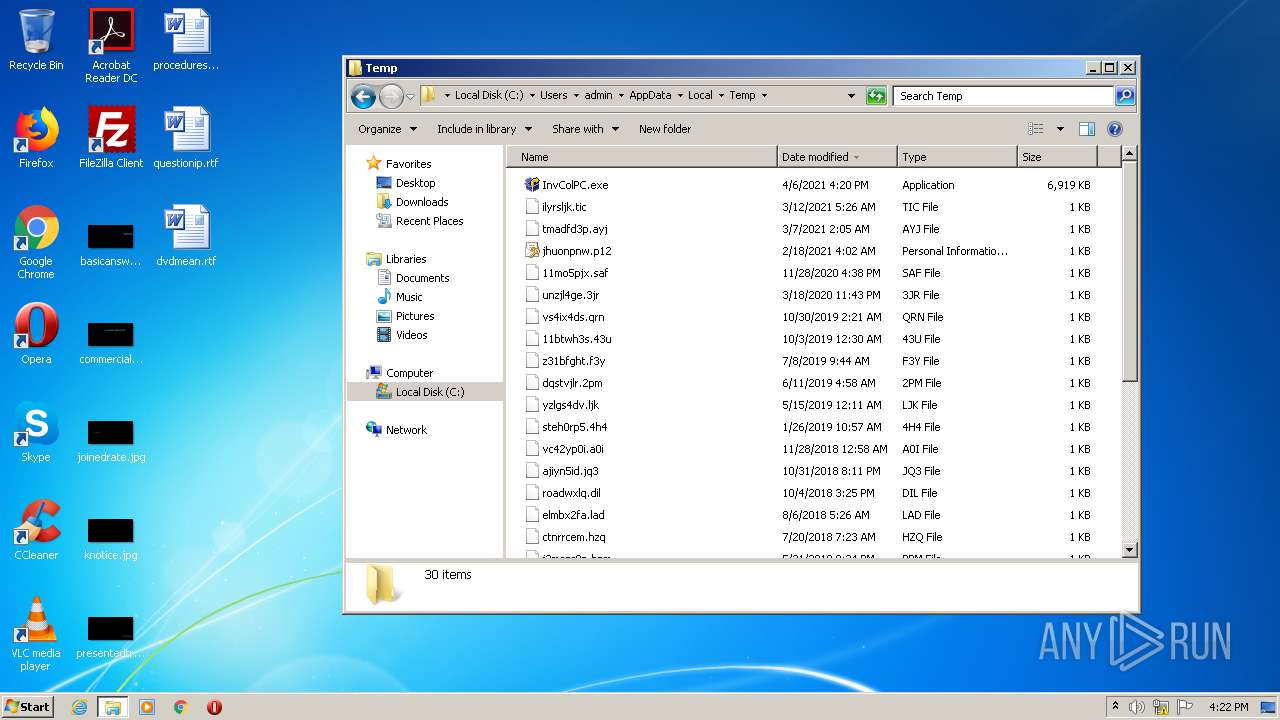
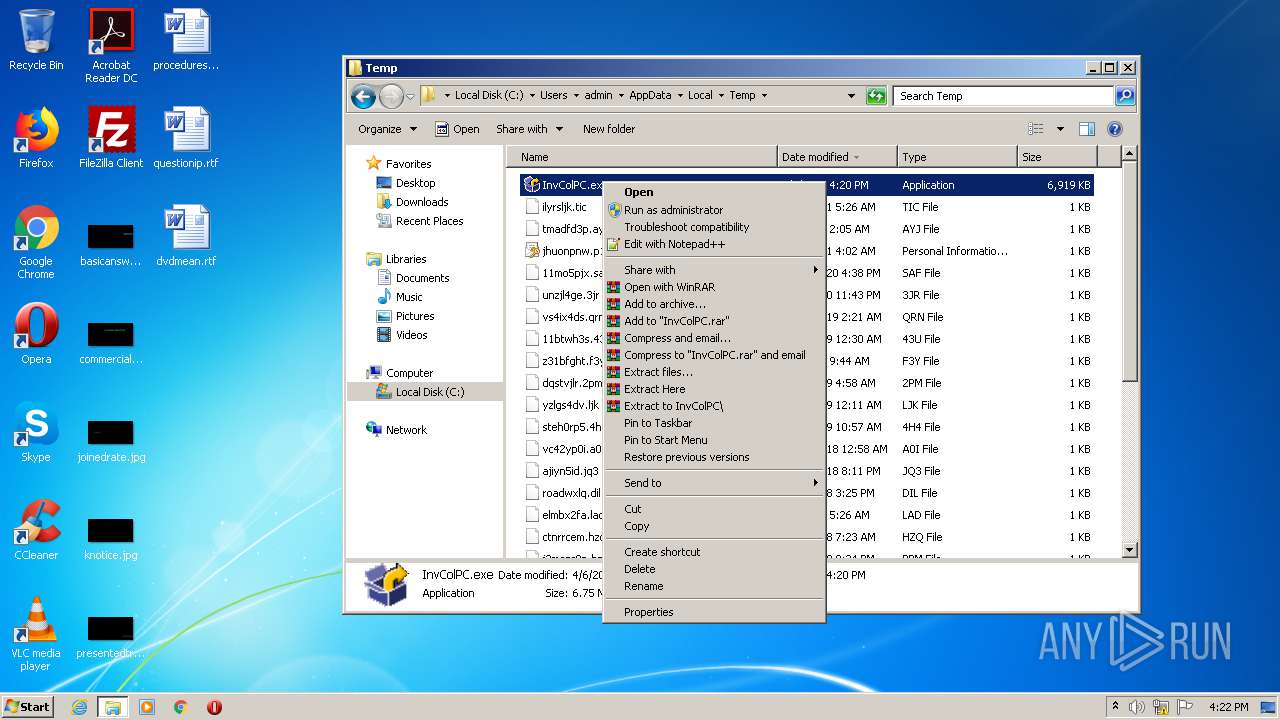
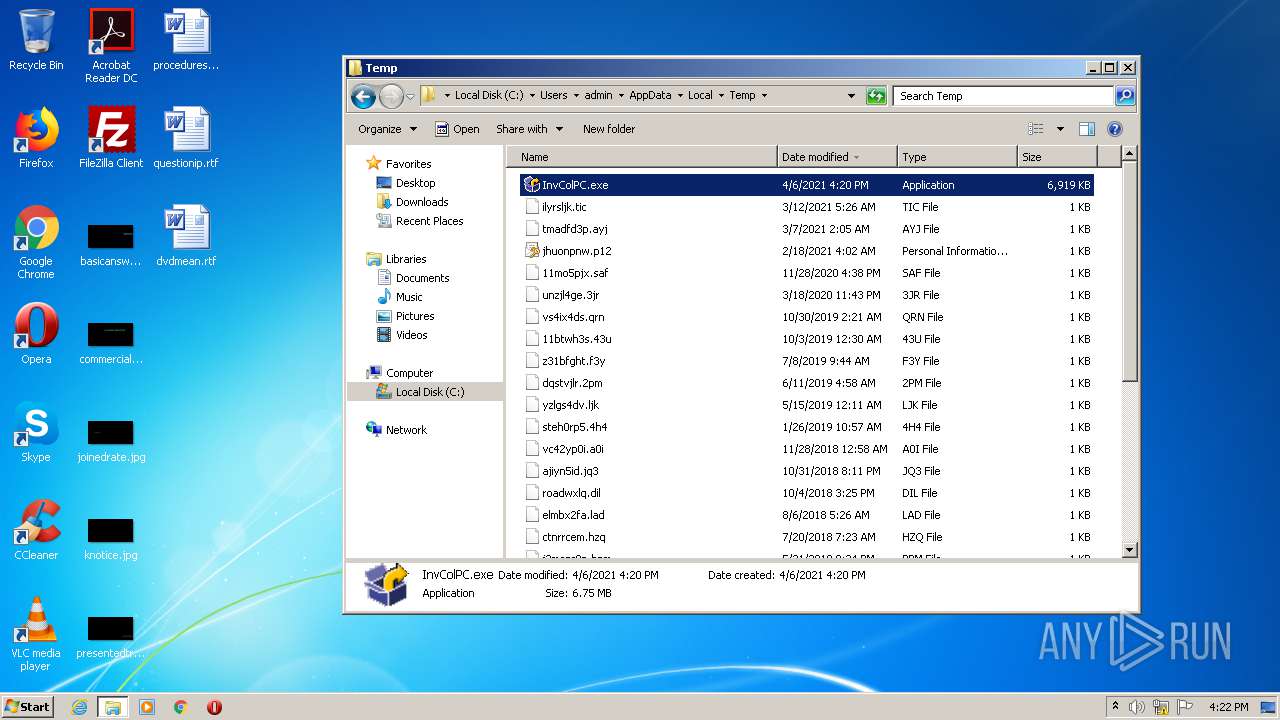
Manual execution by user
- explorer.exe (PID: 3344)
- InvColPC.exe (PID: 2088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:04:04 16:42:53+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 332288 |
| InitializedDataSize: | 70144 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xd53d |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 9.5.1.1 |
| ProductVersionNumber: | 9.5.1.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Dell Inc. |
| FileDescription: | Dell Inventory Utility |
| FileVersion: | 9.5.1 |
| InternalName: | InvCol.exe |
| LegalCopyright: | Copyright (C) Dell Inc. 1995-2013. All rights reserved. |
| OriginalFileName: | InvCol.exe |
| ProductName: | Inventory Collector |
| ProductVersion: | 9.5.1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 04-Apr-2021 14:42:53 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Dell Inc. |
| FileDescription: | Dell Inventory Utility |
| FileVersion: | 9.5.1 |
| InternalName: | InvCol.exe |
| LegalCopyright: | Copyright (C) Dell Inc. 1995-2013. All rights reserved. |
| OriginalFilename: | InvCol.exe |
| ProductName: | Inventory Collector |
| ProductVersion: | 9.5.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 04-Apr-2021 14:42:53 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000510B4 | 0x00051200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.58103 |
.rdata | 0x00053000 | 0x0000B326 | 0x0000B400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.30037 |
.data | 0x0005F000 | 0x000023F8 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.30749 |
.gfids | 0x00062000 | 0x0000019C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.63482 |
.rsrc | 0x00063000 | 0x00004F7C | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.53369 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.68066 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.68472 | 872 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.81898 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 3.3339 | 3240 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 2.03832 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 2.76813 | 392 | Latin 1 / Western European | English - United States | RT_ICON |
122 | 0 | 1 | Latin 1 / Western European | English - United States | PADDING_ENABLED |
BIN_LEN | 3.2728 | 21 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
CAPTION | 3.67531 | 23 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
52
Monitored processes
5
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
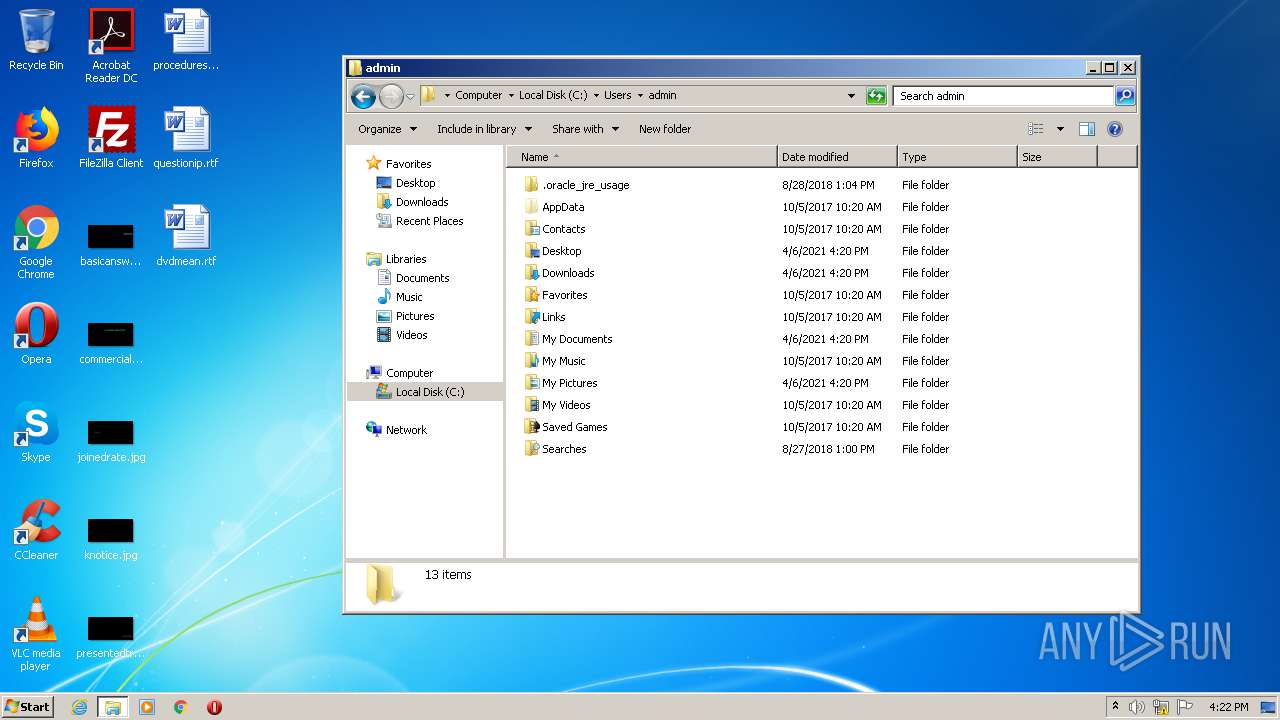
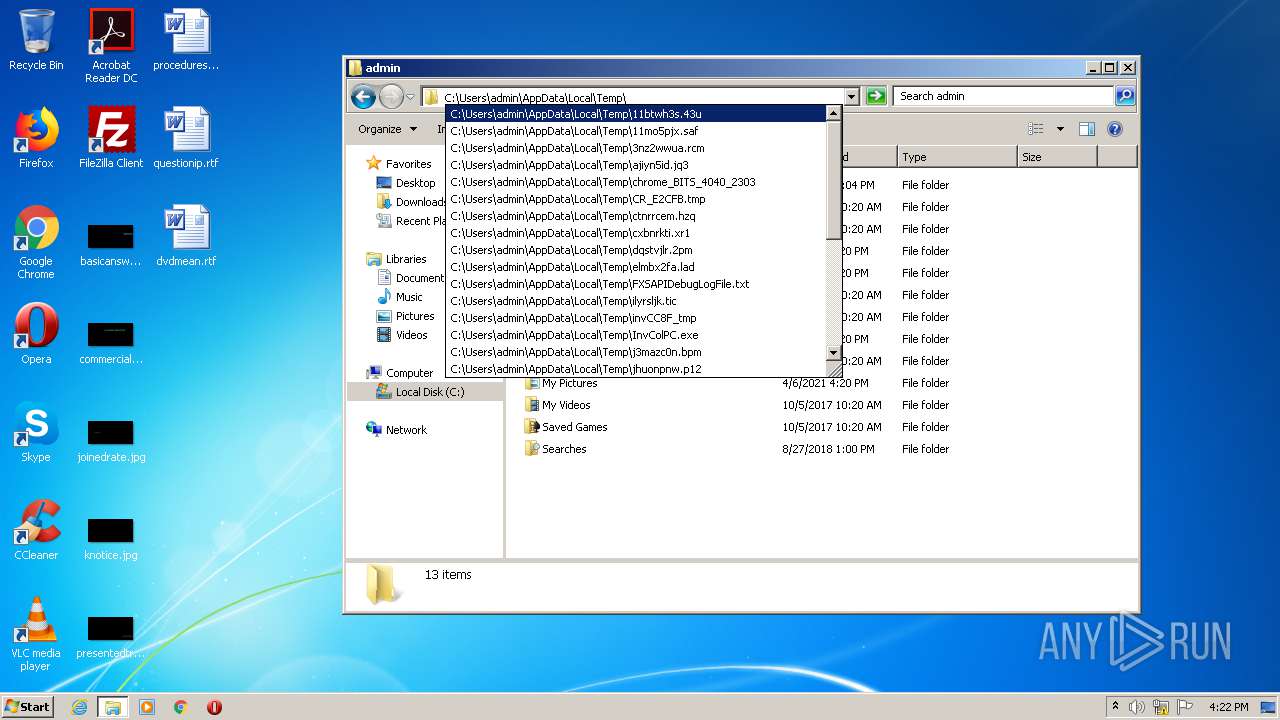
| 1544 | C:\Users\admin\AppData\Local\Temp\inv8B08_tmp\.\invcol.exe -bdir="C:\Users\admin\AppData\Local\Temp" | C:\Users\admin\AppData\Local\Temp\inv8B08_tmp\invcol.exe | InvColPC.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225477 Modules
| |||||||||||||||
| 2088 | "C:\Users\admin\AppData\Local\Temp\InvColPC.exe" | C:\Users\admin\AppData\Local\Temp\InvColPC.exe | explorer.exe | ||||||||||||
User: admin Company: Dell Inc. Integrity Level: HIGH Description: Dell Inventory Utility Exit code: 3221225477 Version: 9.5.1 Modules
| |||||||||||||||
| 2864 | "C:\Users\admin\AppData\Local\Temp\InvColPC.exe" | C:\Users\admin\AppData\Local\Temp\InvColPC.exe | — | explorer.exe | |||||||||||
User: admin Company: Dell Inc. Integrity Level: MEDIUM Description: Dell Inventory Utility Exit code: 4294966286 Version: 9.5.1 Modules
| |||||||||||||||
| 3344 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3984 | C:\Windows\system32\WerFault.exe -u -p 1544 -s 352 | C:\Windows\system32\WerFault.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
41
Read events
38
Write events
3
Delete events
0
Modification events
| (PID) Process: | (3984) WerFault.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Windows Error Reporting\Debug |
| Operation: | write | Name: | ExceptionRecord |
Value: 050000C000000000000000001A152F0002000000000000004D004D007F0001000000000000000000000000000000000000000000000000007F02000000000000FFFF0000000000000000000000000000 | |||
| (PID) Process: | (3984) WerFault.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\Windows Error Reporting\Debug\UIHandles |
| Operation: | write | Name: | FirstLevelConsentDialog |
Value: D201030000000000 | |||
| (PID) Process: | (3984) WerFault.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Windows Error Reporting\Debug\UIHandles |
| Operation: | write | Name: | FirstLevelConsentDialog |
Value: D201030000000000 | |||
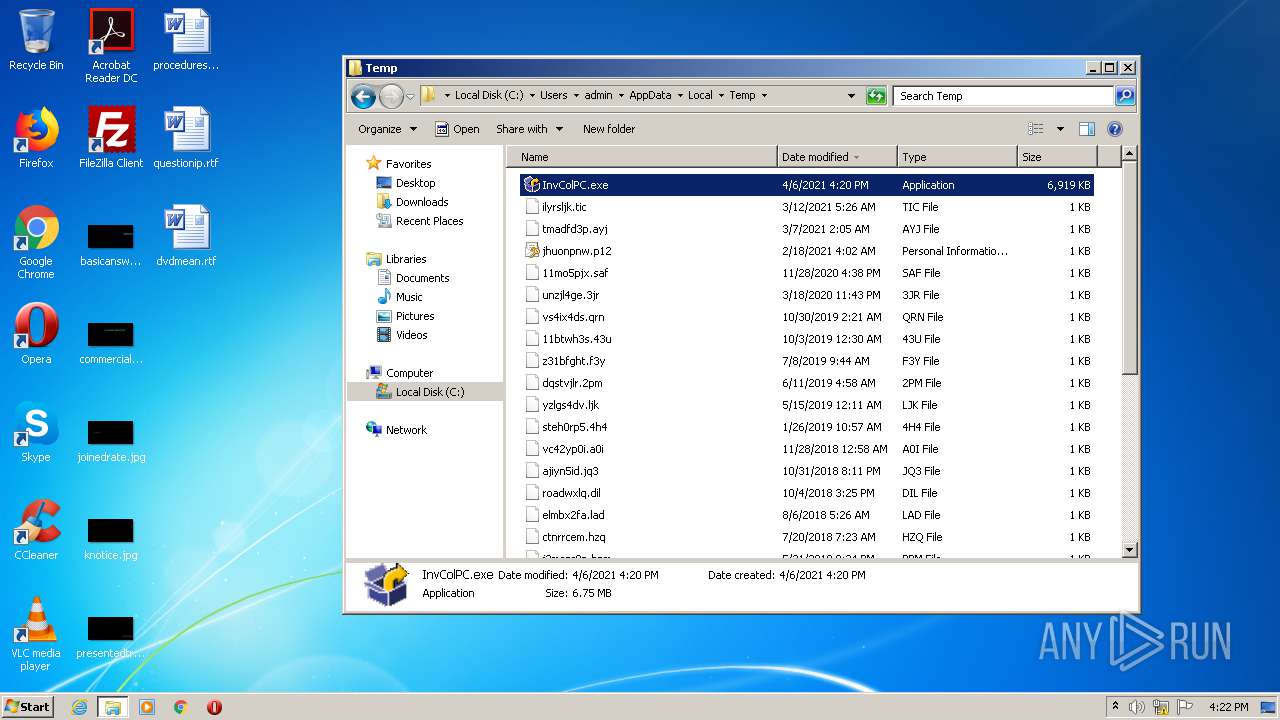
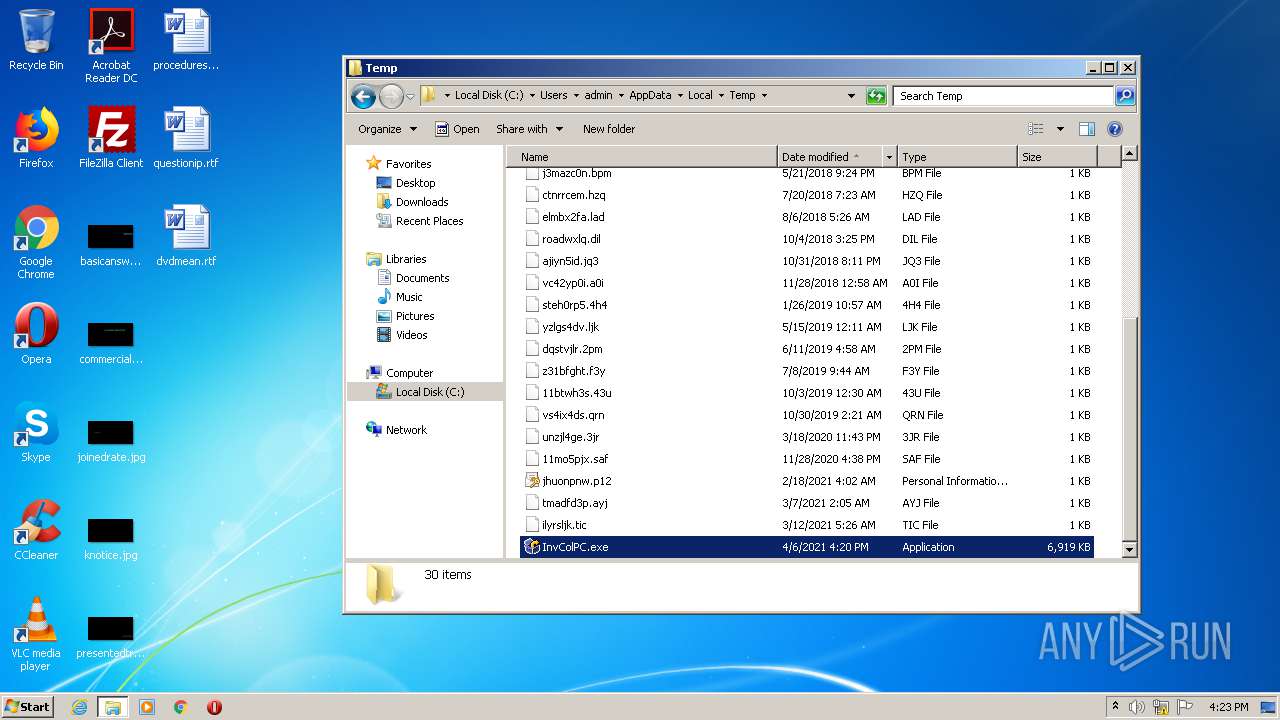
Executable files
35
Suspicious files
1
Text files
108
Unknown types
1
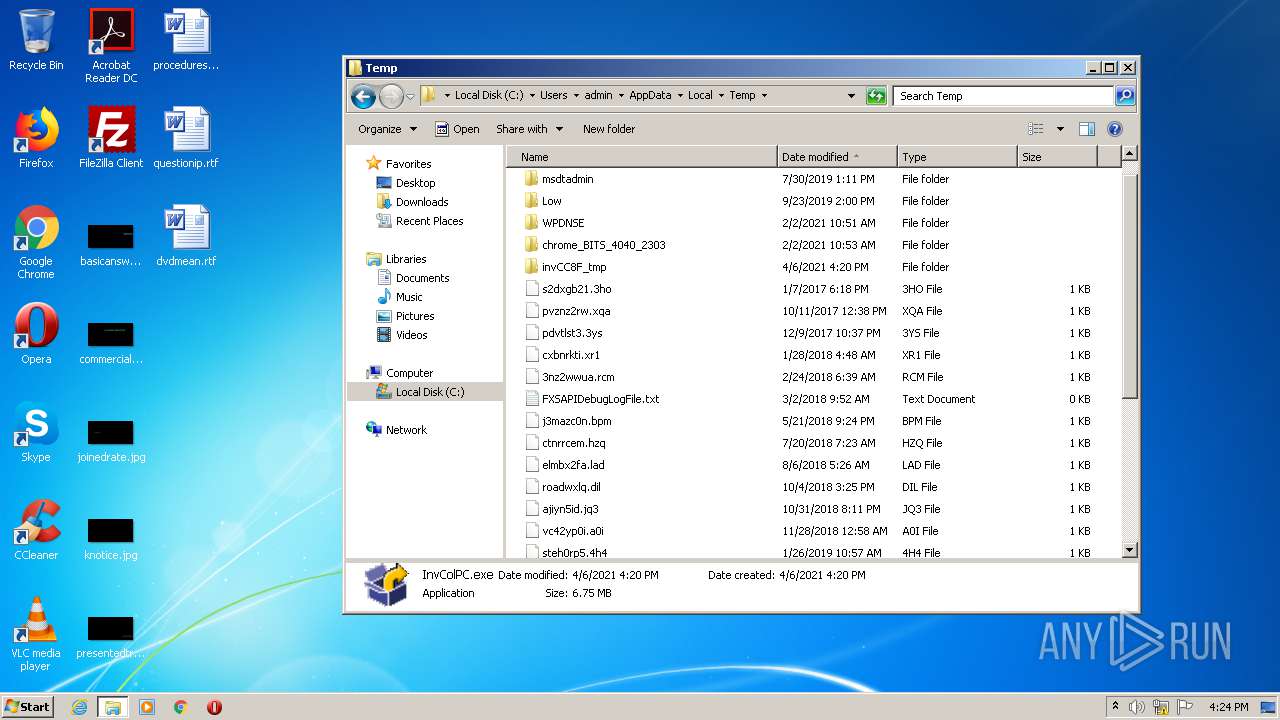
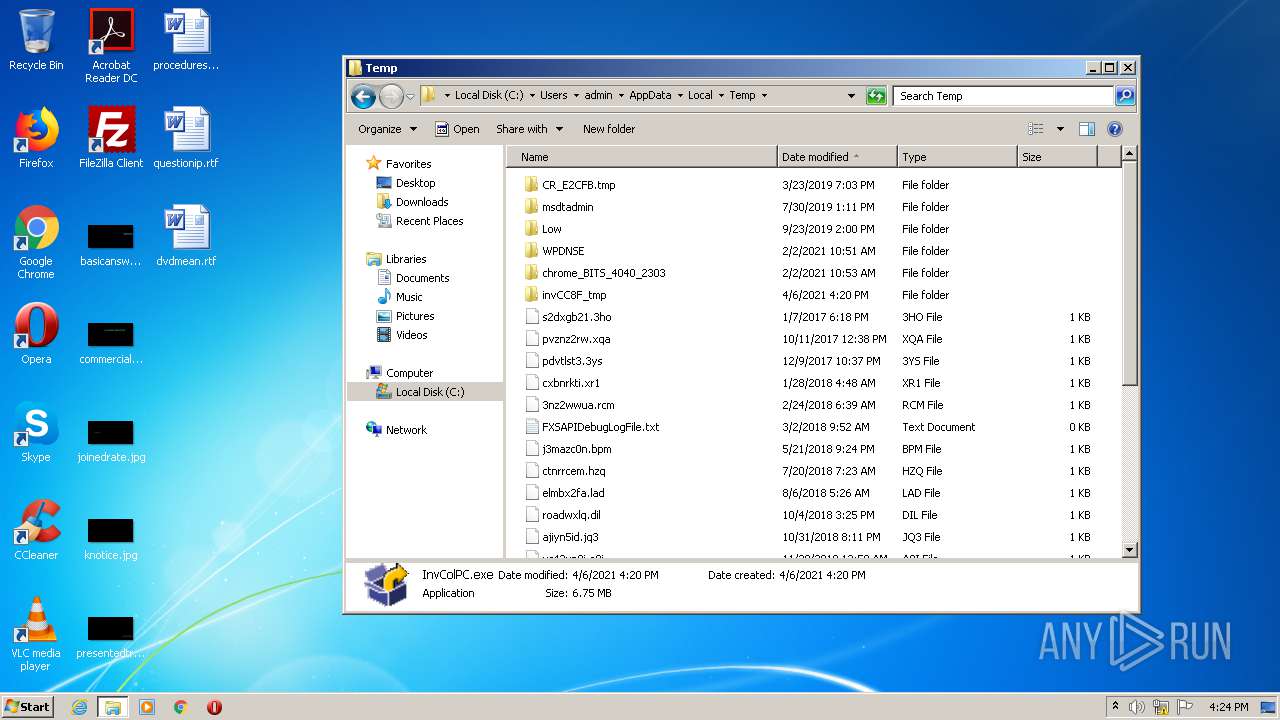
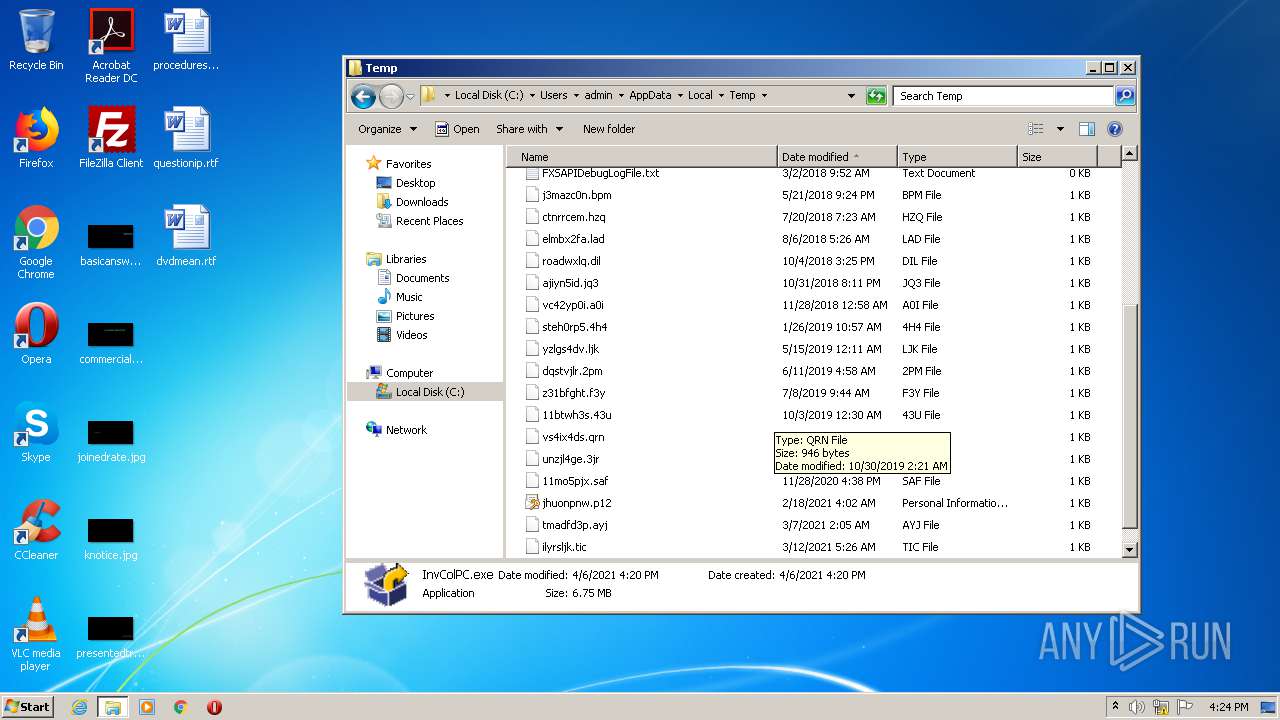
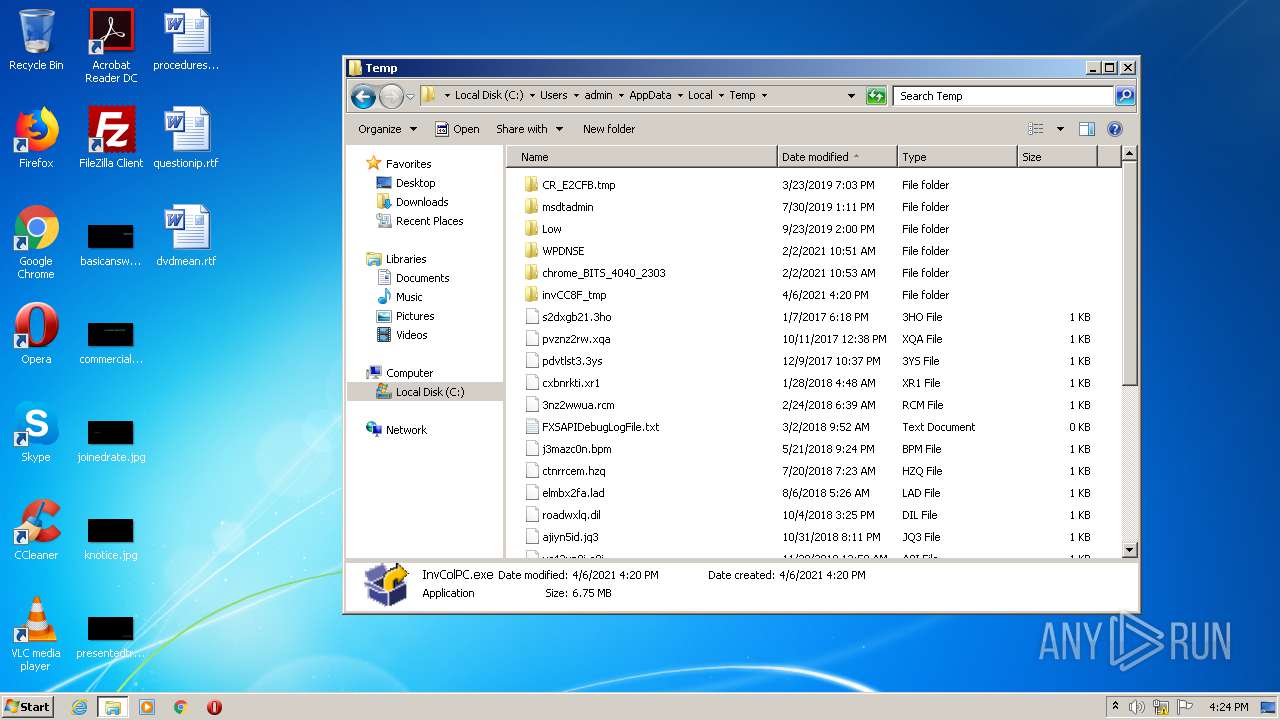
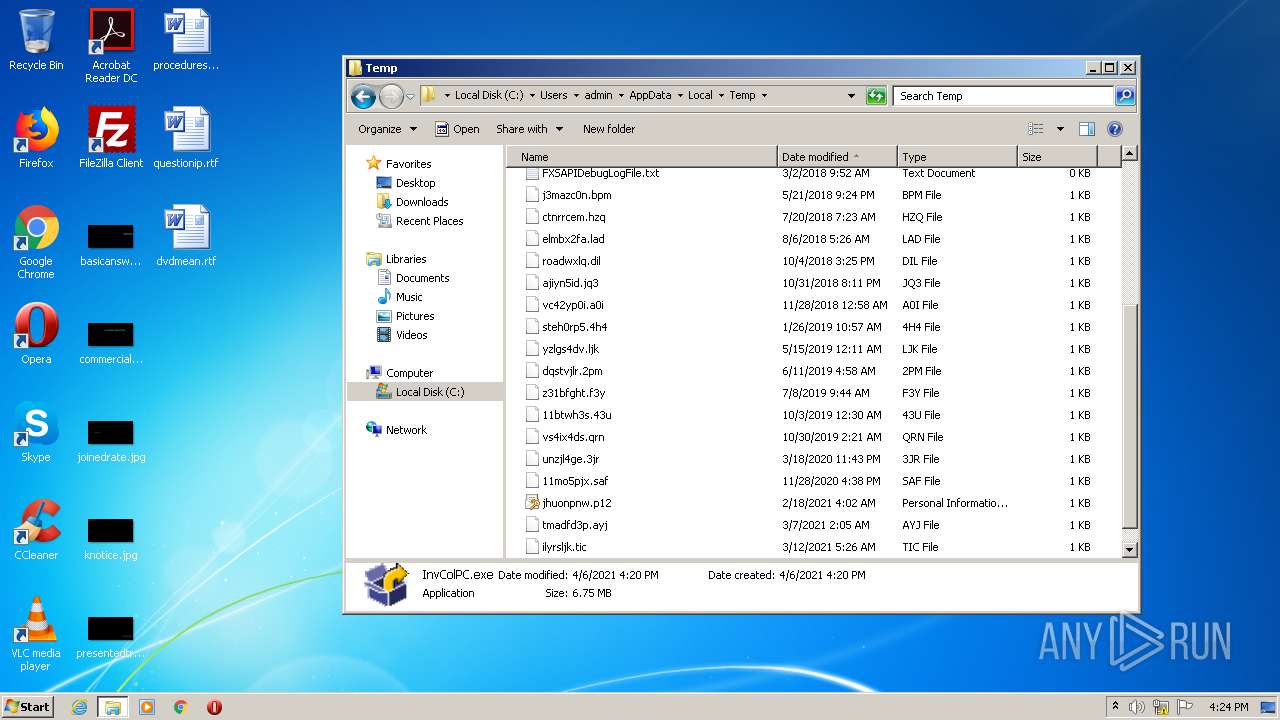
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2088 | InvColPC.exe | C:\Users\admin\AppData\Local\Temp\inv8B08_tmp\AppxInventory\APPXInventory.exe | executable | |
MD5:31365CD159180A9057B6227AFB715A7C | SHA256:D2A5277CD3EB21BFAEA921D2479070CA14B2410B2CA184663D5F327AC200AE90 | |||
| 2088 | InvColPC.exe | C:\Users\admin\AppData\Local\Temp\inv8B08_tmp\AppxInventory\APPXMapping.ini | text | |
MD5:4EA3E15D85ED61FAC9C20292AA5646BB | SHA256:BBA7B44ACE6314E397C084DE95529C8A906C46D53E364DEEA095316B7AAB565B | |||
| 2088 | InvColPC.exe | C:\Users\admin\AppData\Local\Temp\inv8B08_tmp\DCH_CompID_Mapping.ini | text | |
MD5:215D6E154E243EAF50F847C8BE713909 | SHA256:42BF30F9A7631AA71A6F589FAE77220D274CBA566CC3089C900F740A124EB20A | |||
| 2088 | InvColPC.exe | C:\Users\admin\AppData\Local\Temp\inv8B08_tmp\Broadcom_BT\DrvCfg32.ini | text | |
MD5:4CE27CB33711A46749DE053AE386EDB6 | SHA256:4886EB41EC8AB65A23BF8CB22CAAB691A020E9D31EE654D32A60E5A5EB989393 | |||
| 2088 | InvColPC.exe | C:\Users\admin\AppData\Local\Temp\inv8B08_tmp\AppxInventory\vccorlib140.dll | executable | |
MD5:60F11A76E35FD4A9CD2455EA3EFF3224 | SHA256:F3BCC4A3AE6CD03E08EC48411B6927A0A163AF6F92384279C1DD7AFCB7F52293 | |||
| 2088 | InvColPC.exe | C:\Users\admin\AppData\Local\Temp\inv8B08_tmp\APP_18260_WIGIG\PIEConfig.xml | text | |
MD5:54BFE695F971A7FEA12F6C03FCC252A8 | SHA256:F5E71F263F0CFFE305FA085FA27030ED4E652E8A363E8BEAF04673A6D19A3215 | |||
| 2088 | InvColPC.exe | C:\Users\admin\AppData\Local\Temp\inv8B08_tmp\CompID_Mapping.ini | text | |
MD5:D404B3ABA5CCCF7057EDBFA40FCADE84 | SHA256:BC756C01B4D38D2011C995414319A342F8B5A64494E6CC05FCD93C7B61C492E8 | |||
| 2088 | InvColPC.exe | C:\Users\admin\AppData\Local\Temp\inv8B08_tmp\APP_18260_WIGIG\DrvCfg64.ini | ini | |
MD5:3A11050AE2368DCA54F77C8A74C180CD | SHA256:2EEB4DCF7B05313B254B3C5BC935227823A582AF4EEAD4EB0405CF3A9CB15733 | |||
| 2088 | InvColPC.exe | C:\Users\admin\AppData\Local\Temp\inv8B08_tmp\APP_18260_WIGIG\DrvCfg32.ini | ini | |
MD5:3A11050AE2368DCA54F77C8A74C180CD | SHA256:2EEB4DCF7B05313B254B3C5BC935227823A582AF4EEAD4EB0405CF3A9CB15733 | |||
| 2088 | InvColPC.exe | C:\Users\admin\AppData\Local\Temp\inv8B08_tmp\Broadcom_BT\PIEInfo.txt | text | |
MD5:309382D03A5668B46A6A99EF235C8380 | SHA256:0FB9216ED2D3331177A4353F45A553B27B590EA86F16AFFDE510B4D9955F0CA9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report