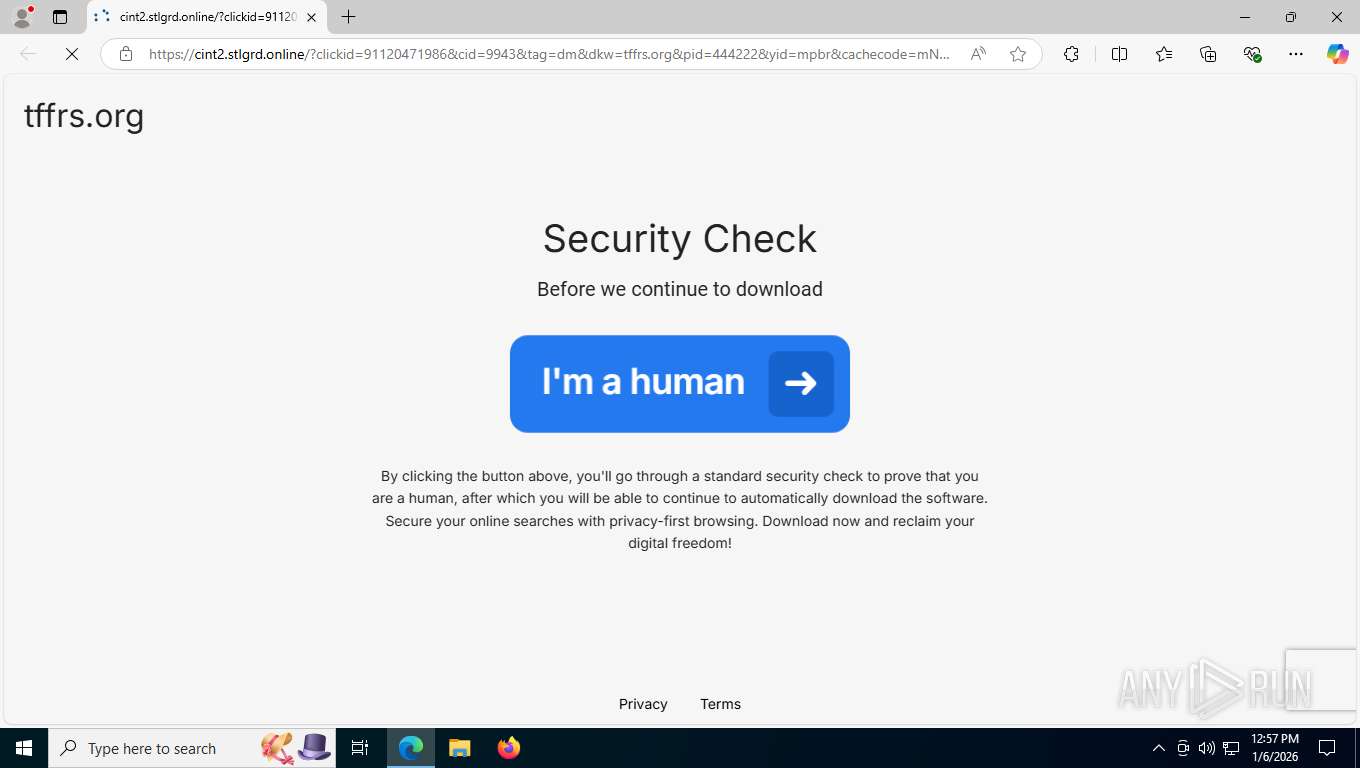
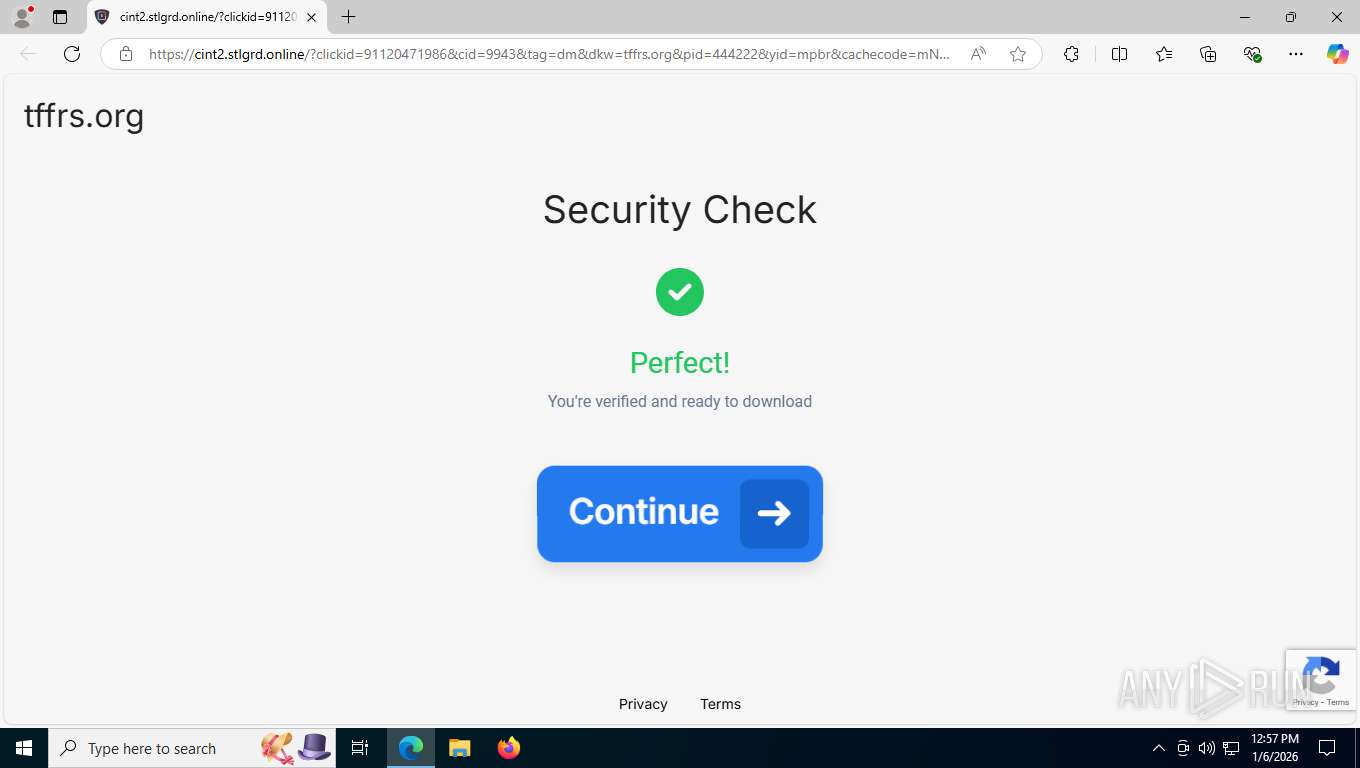
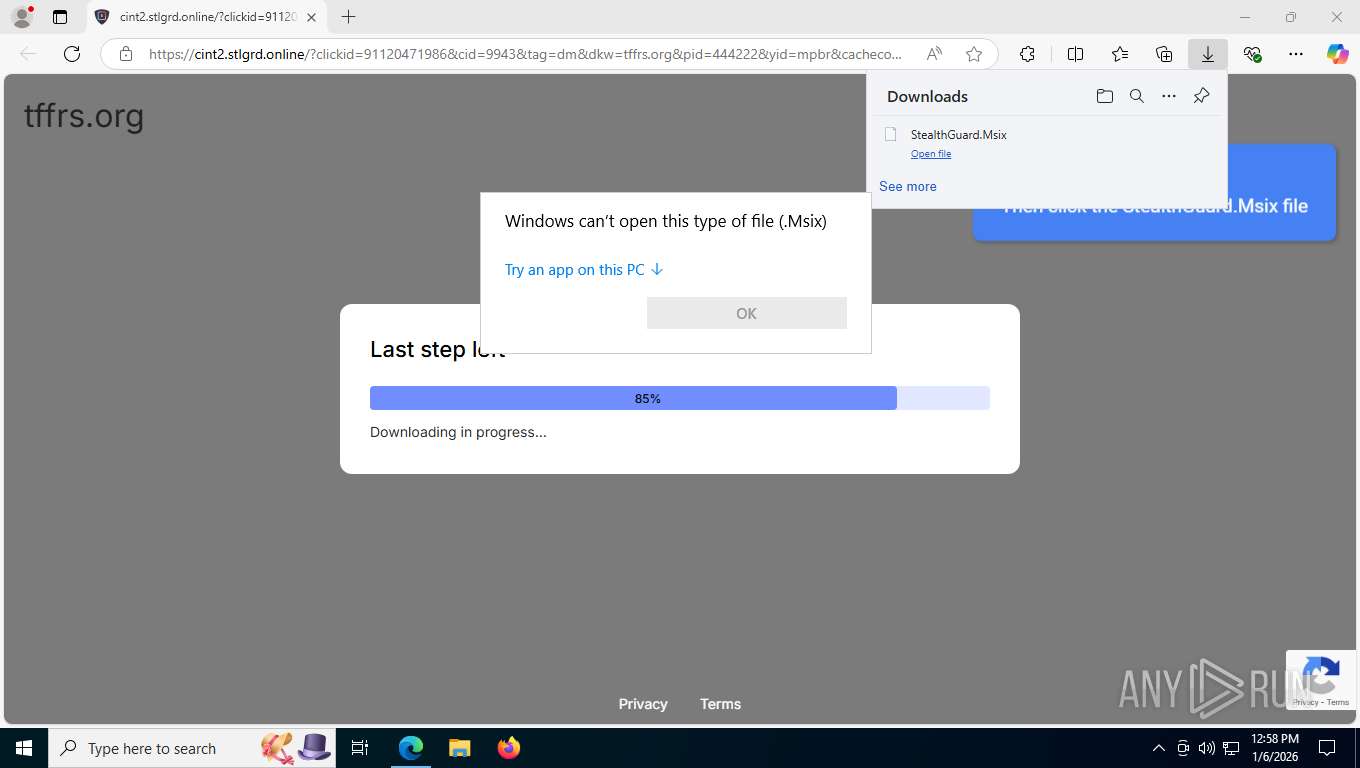
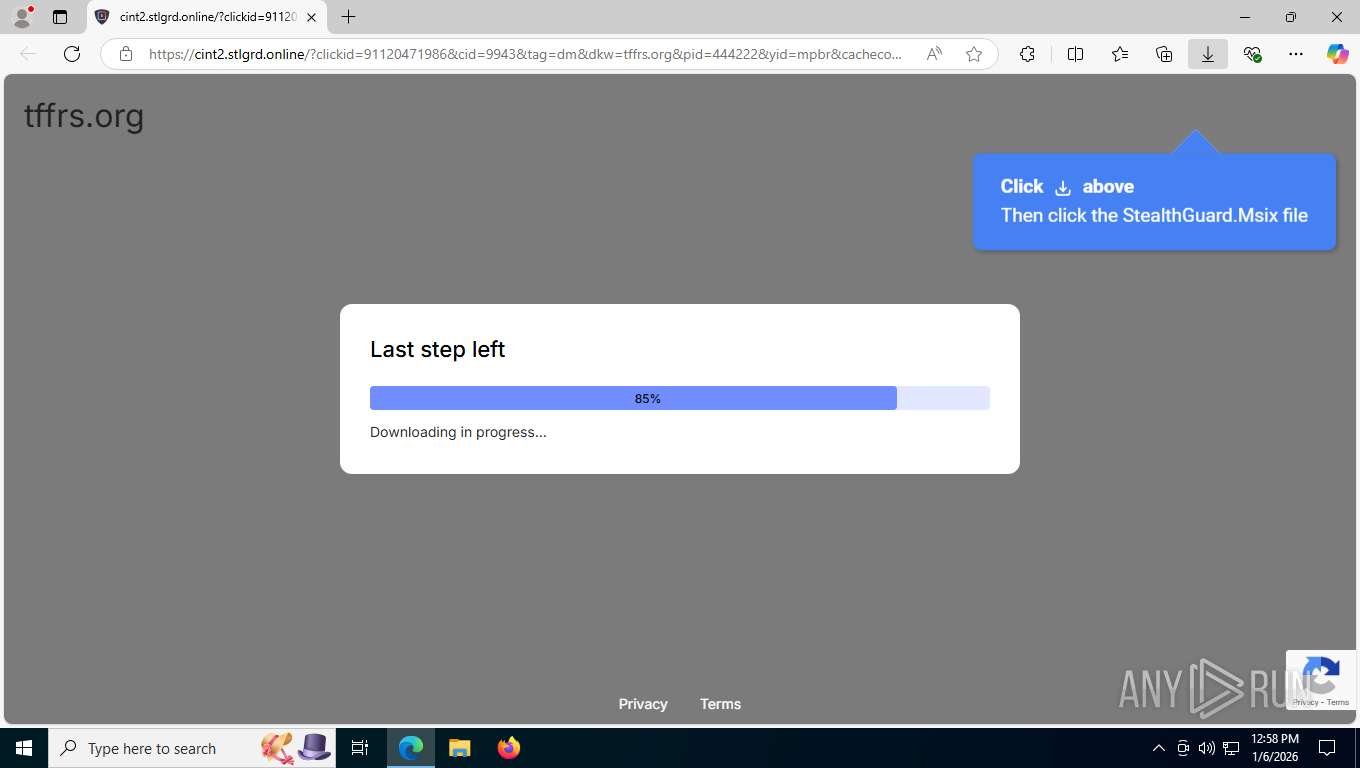
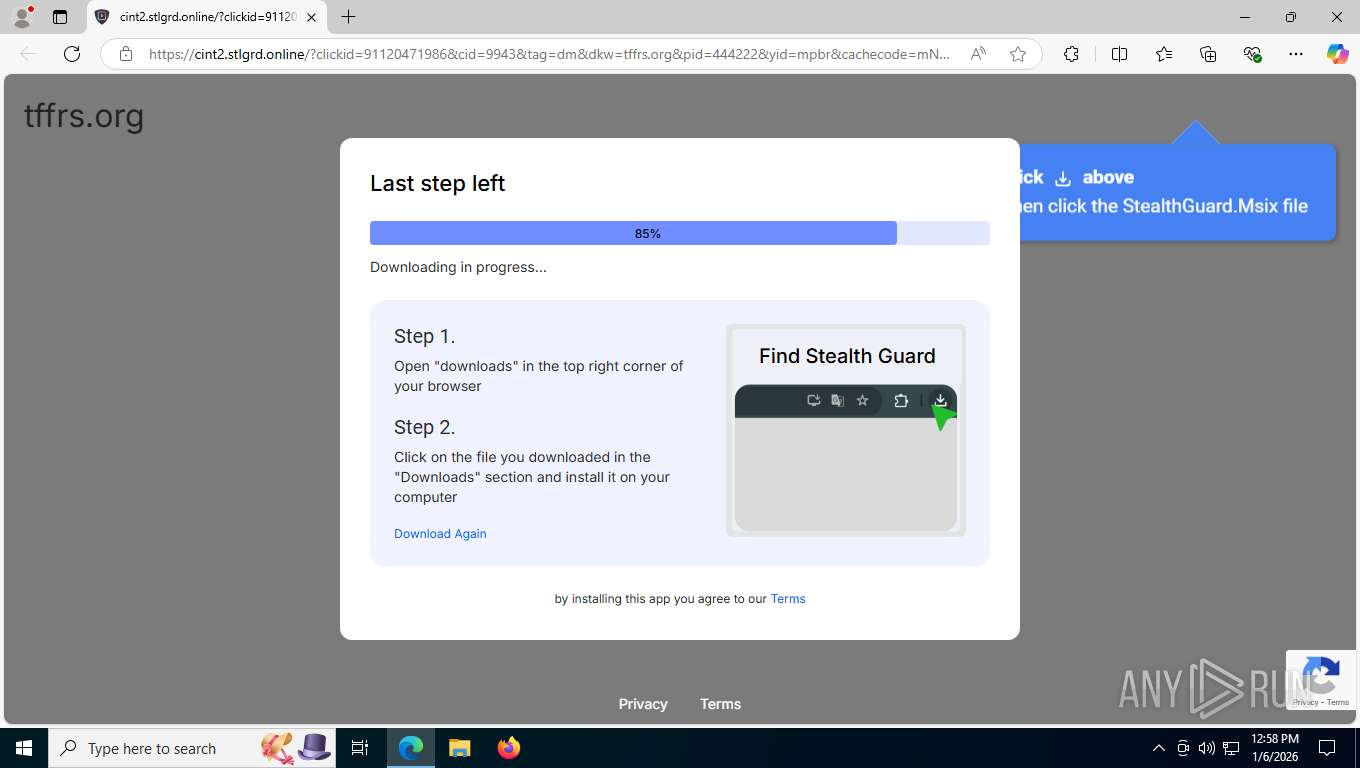
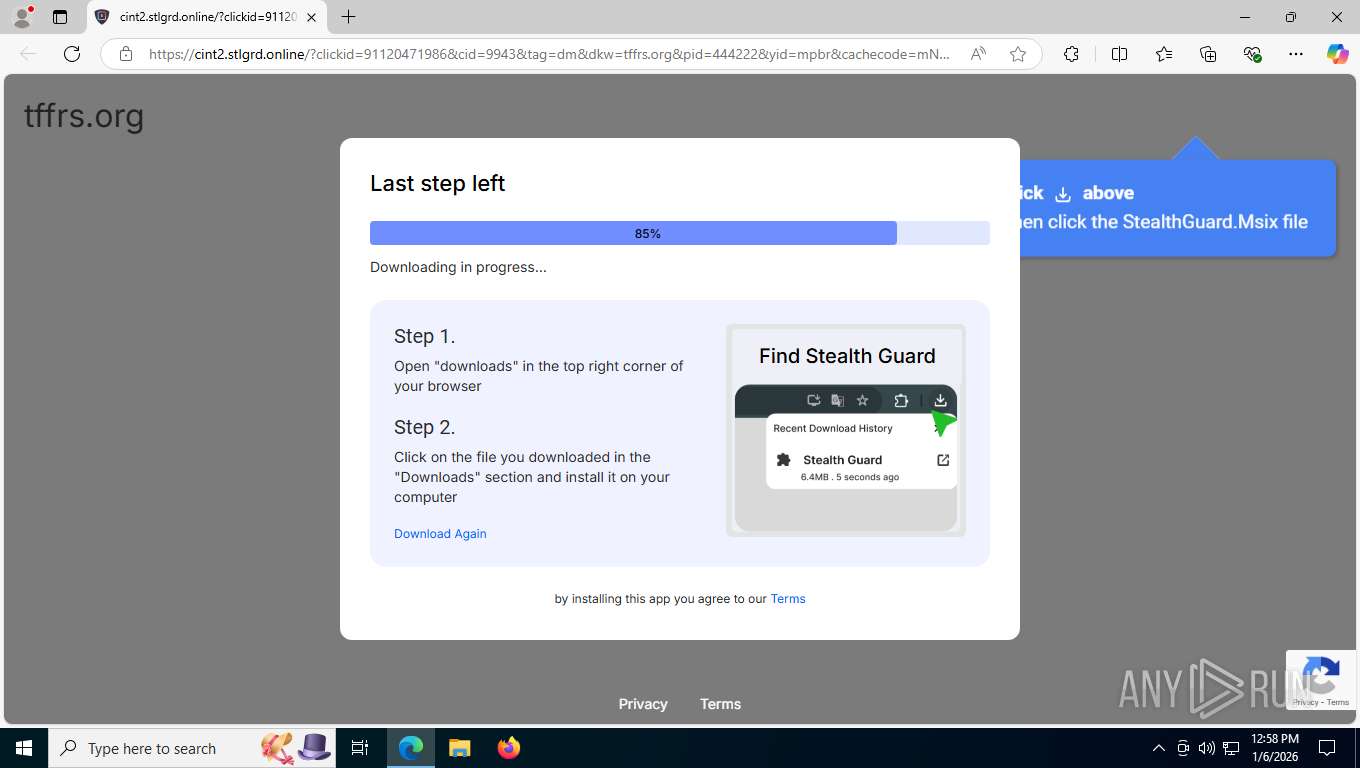
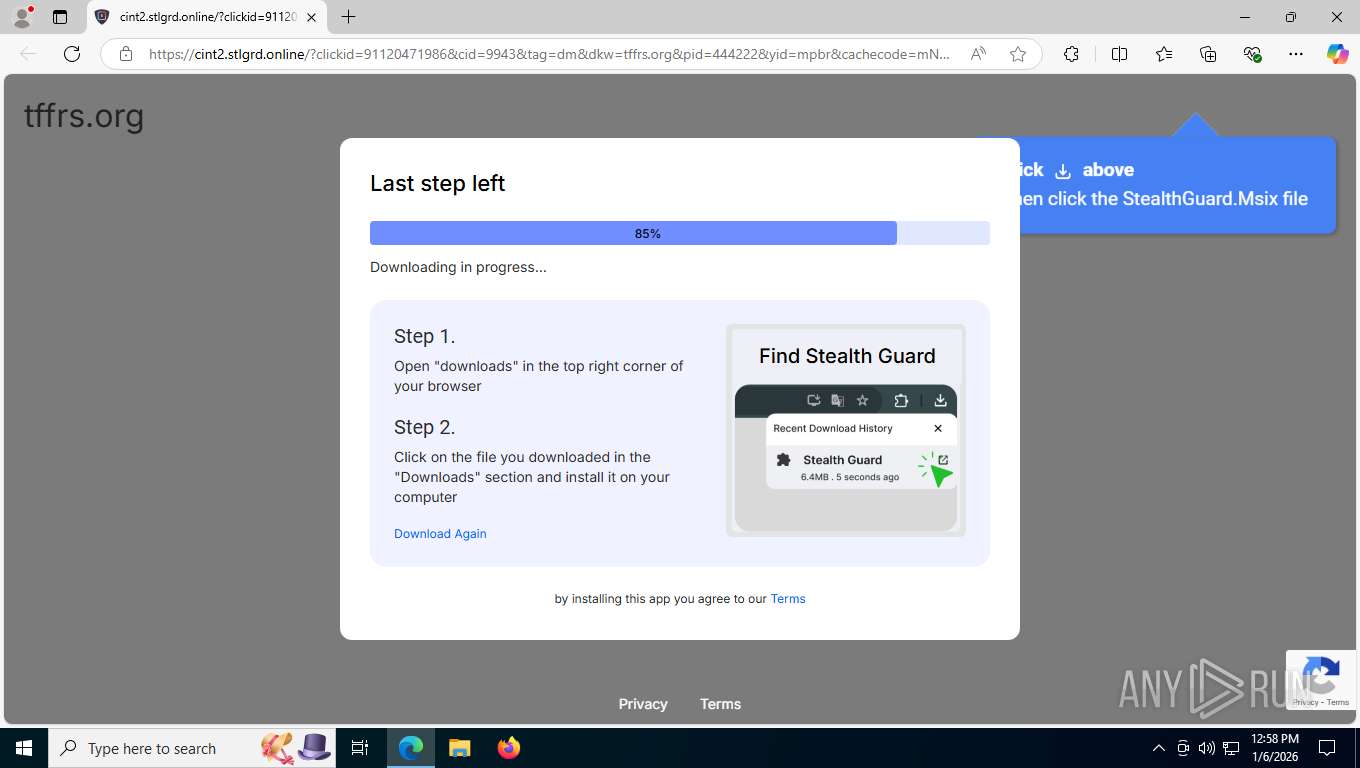
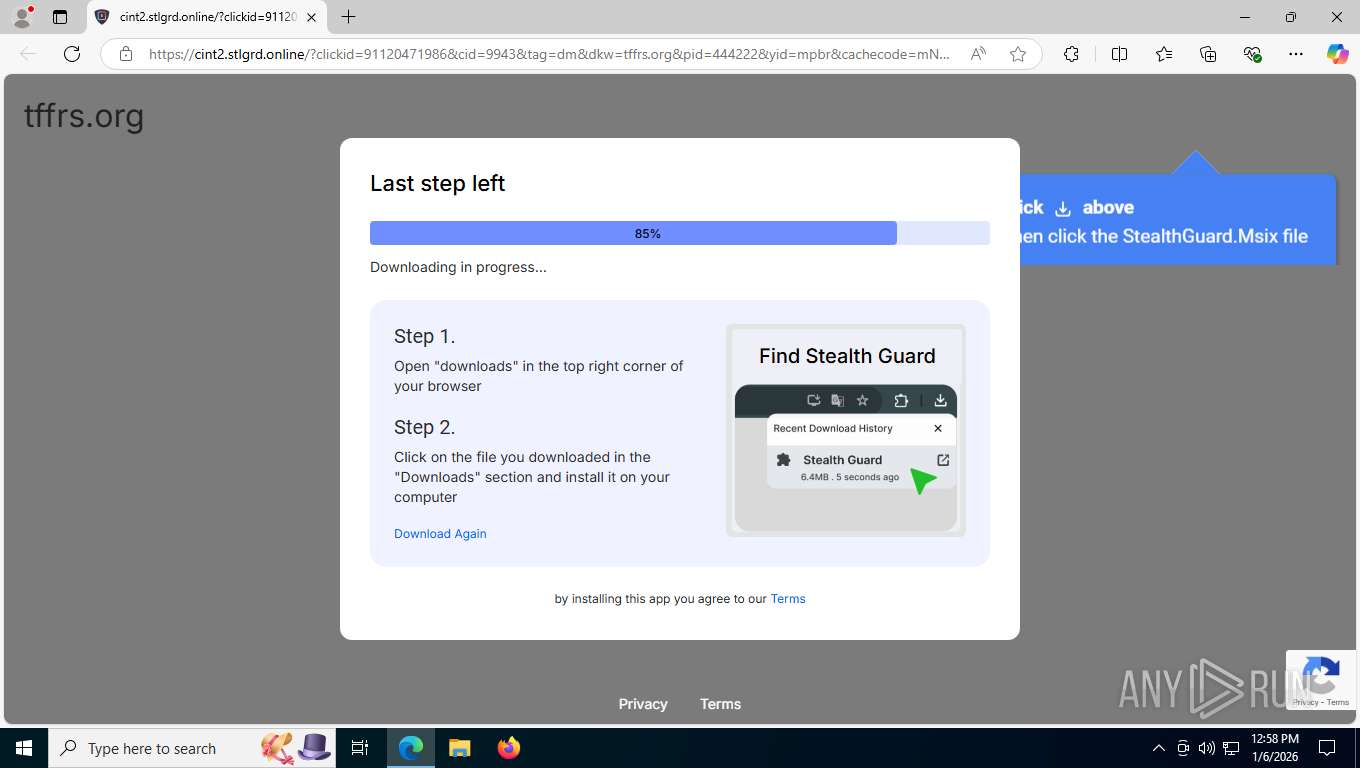
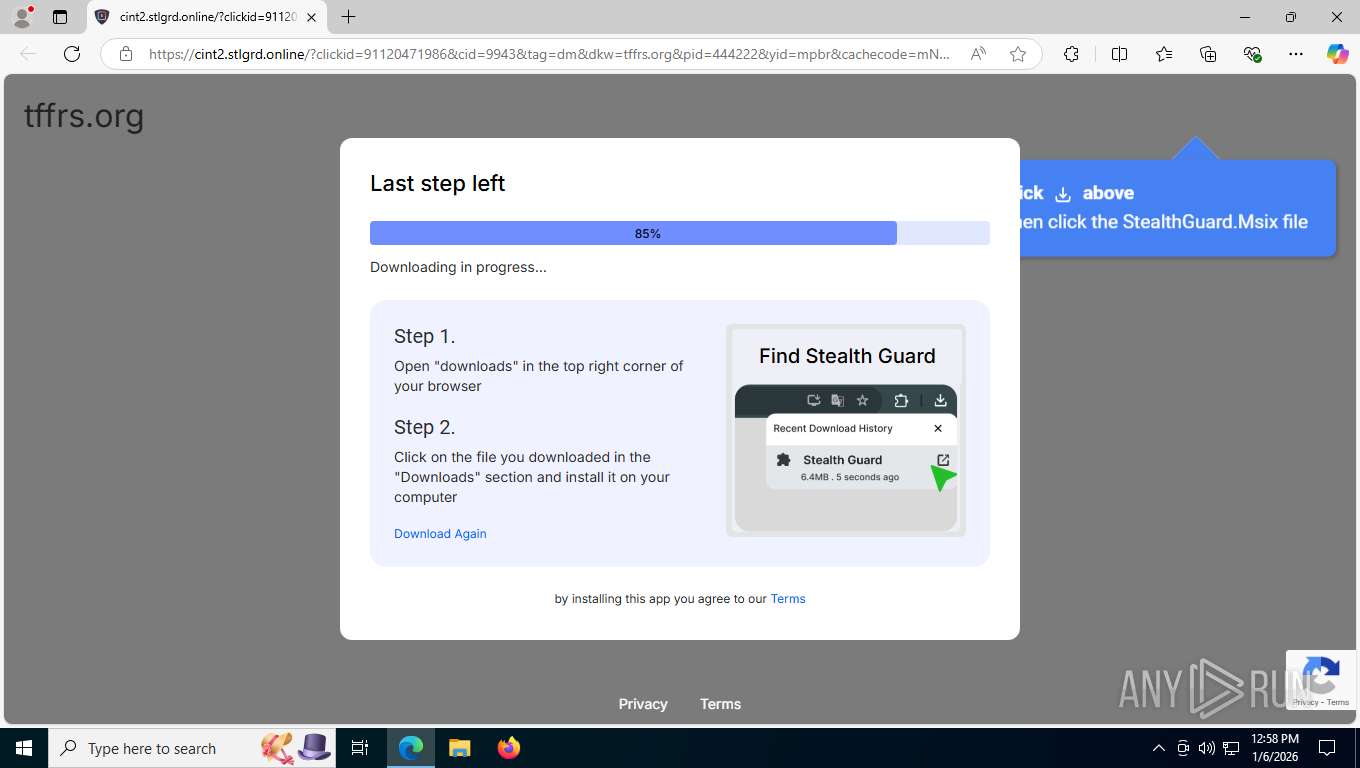
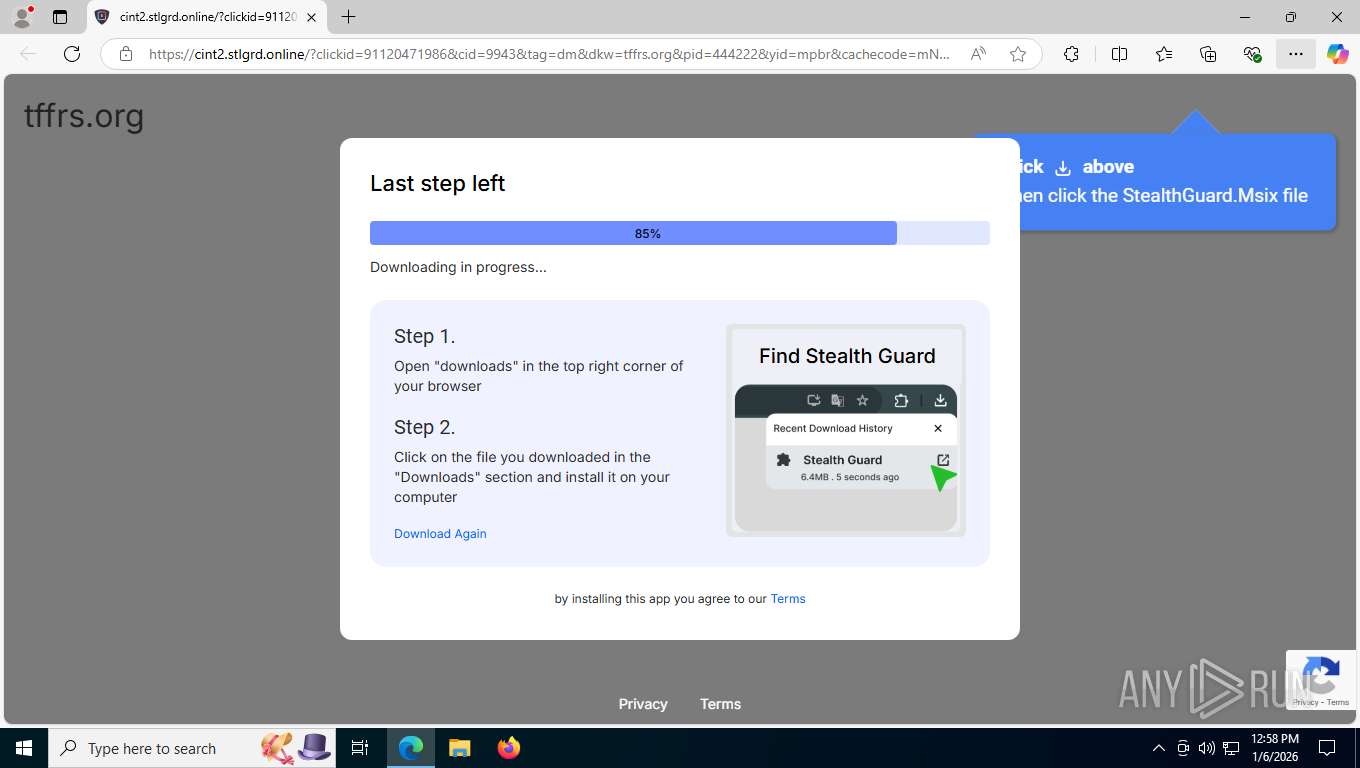
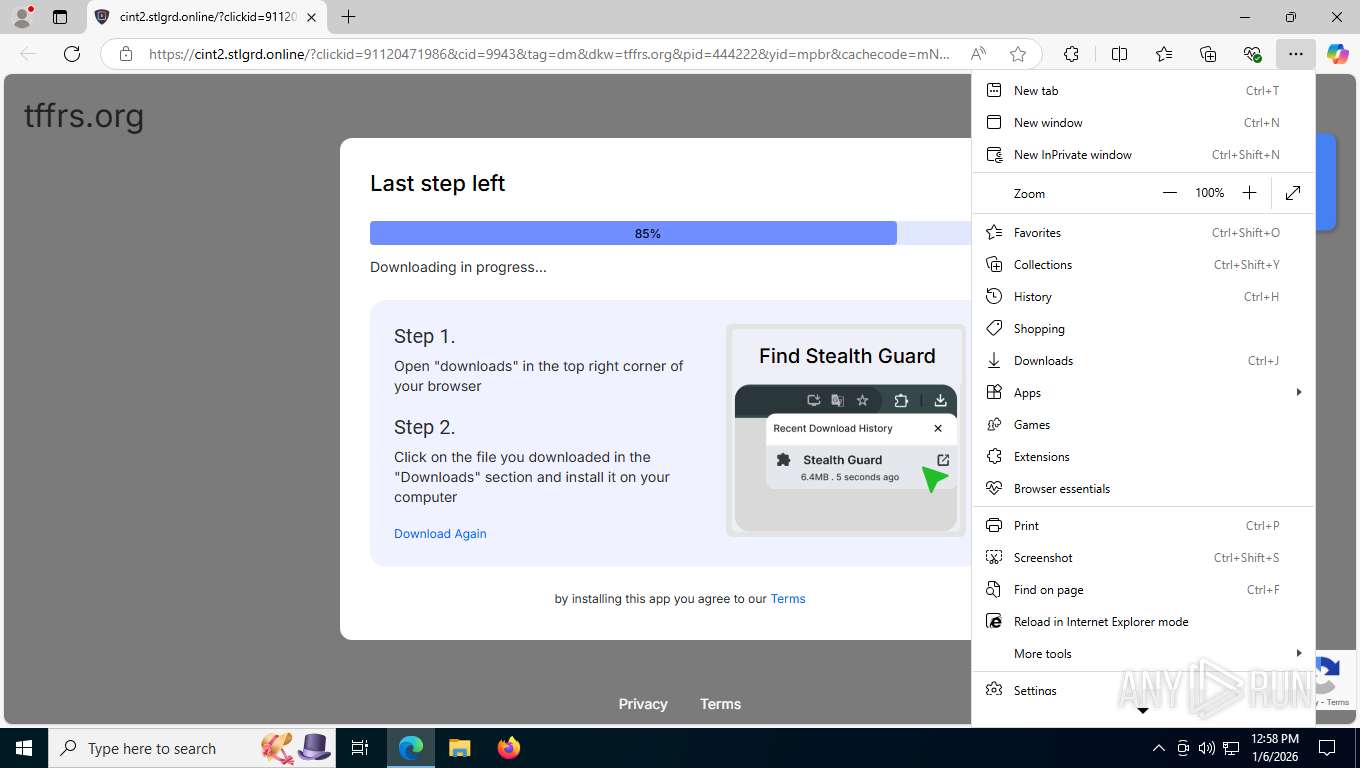
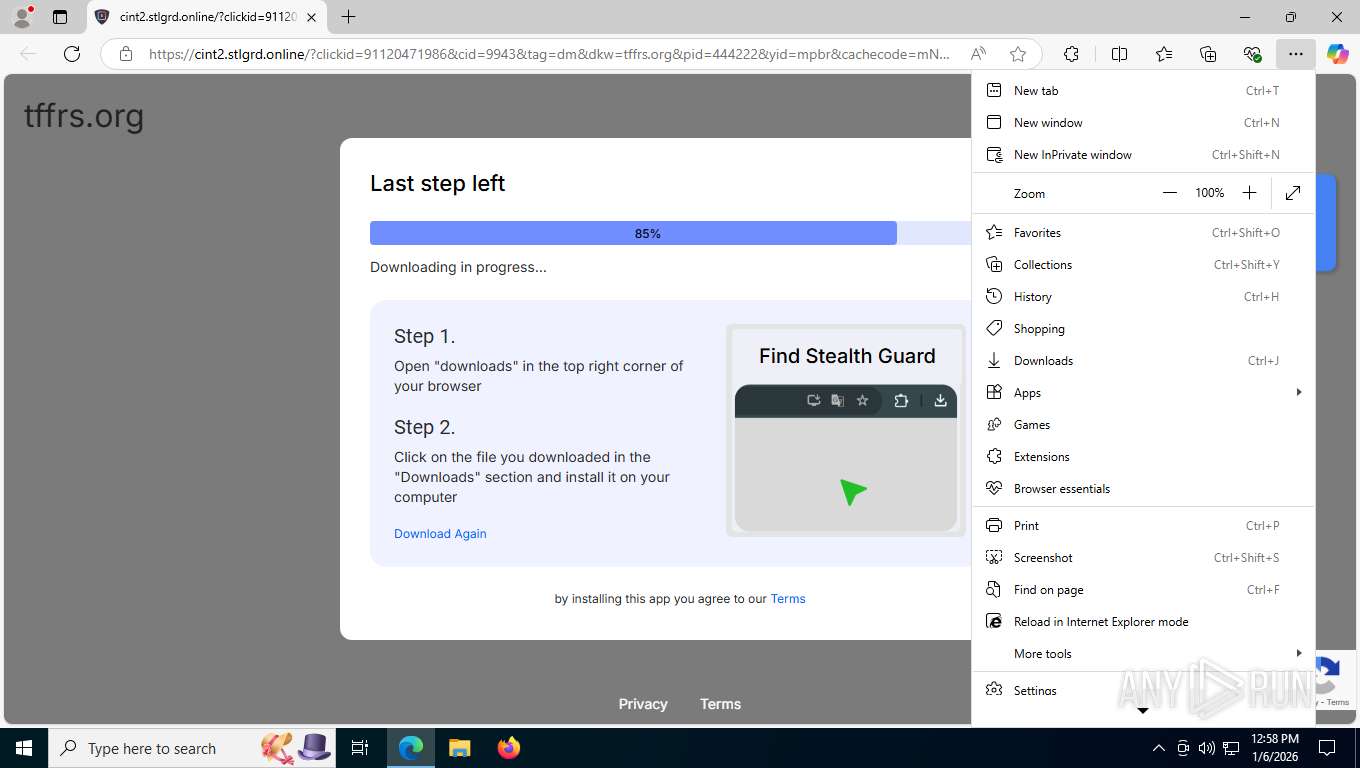
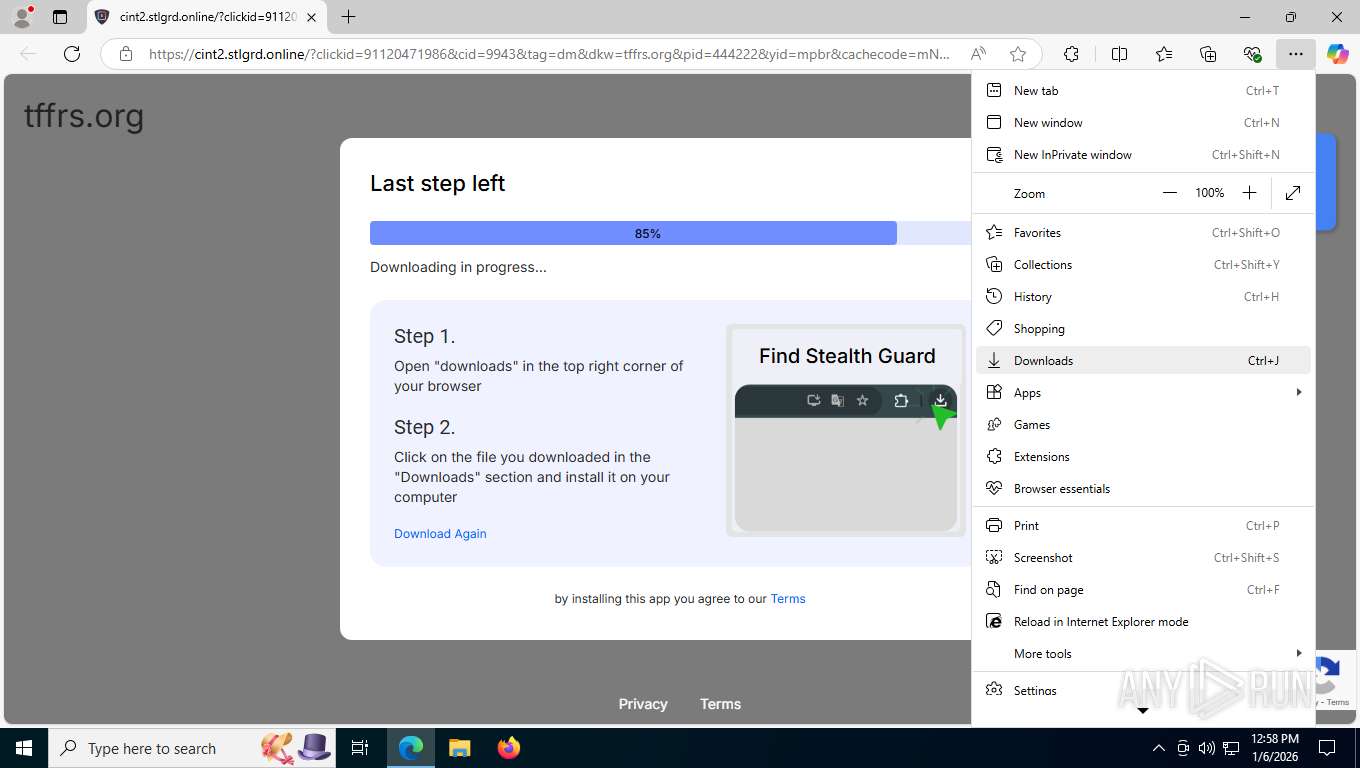
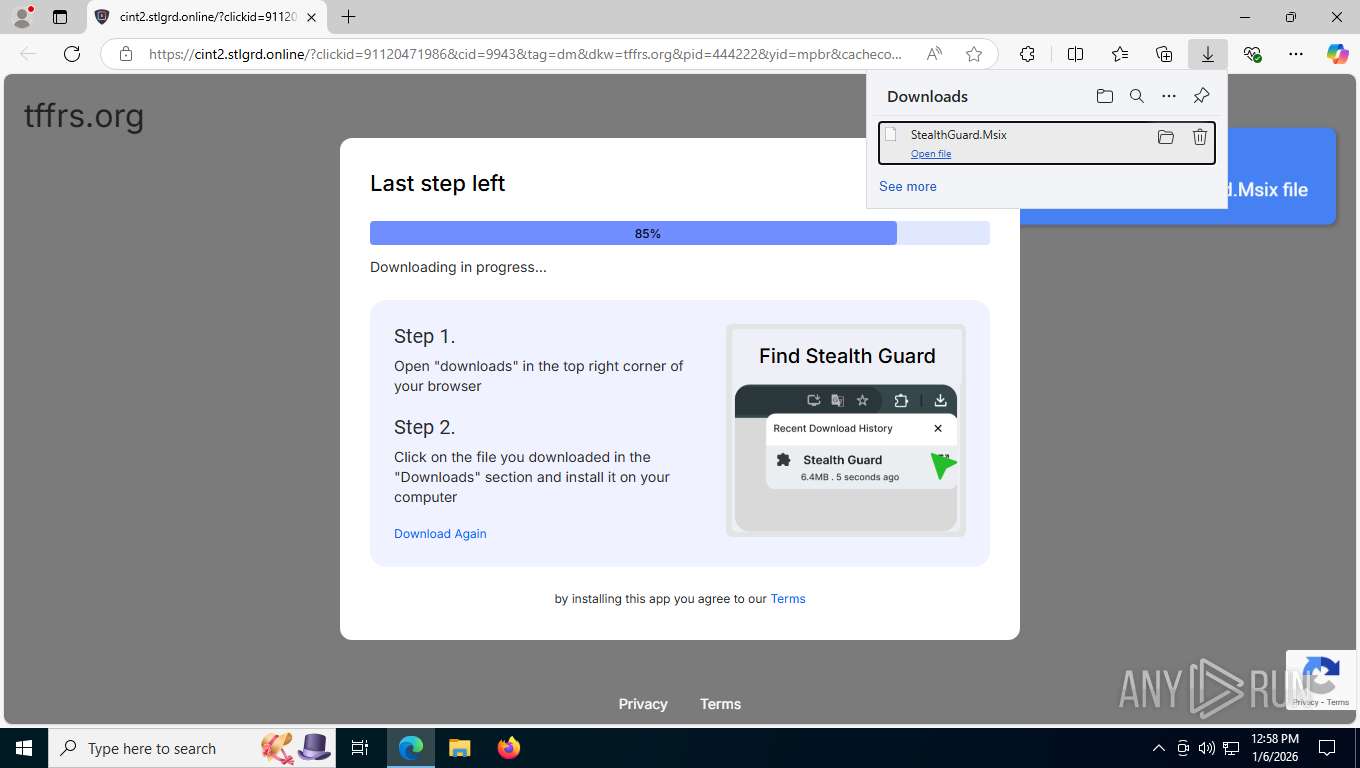
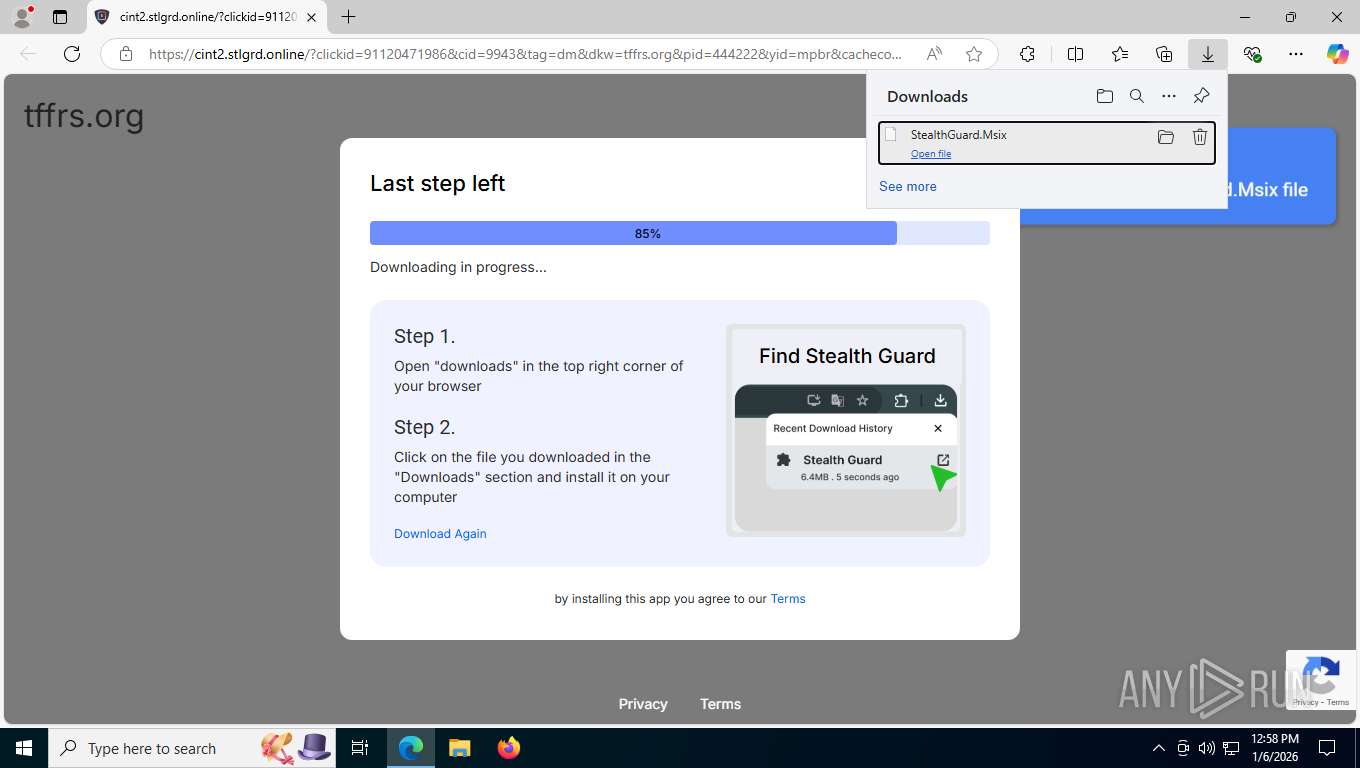
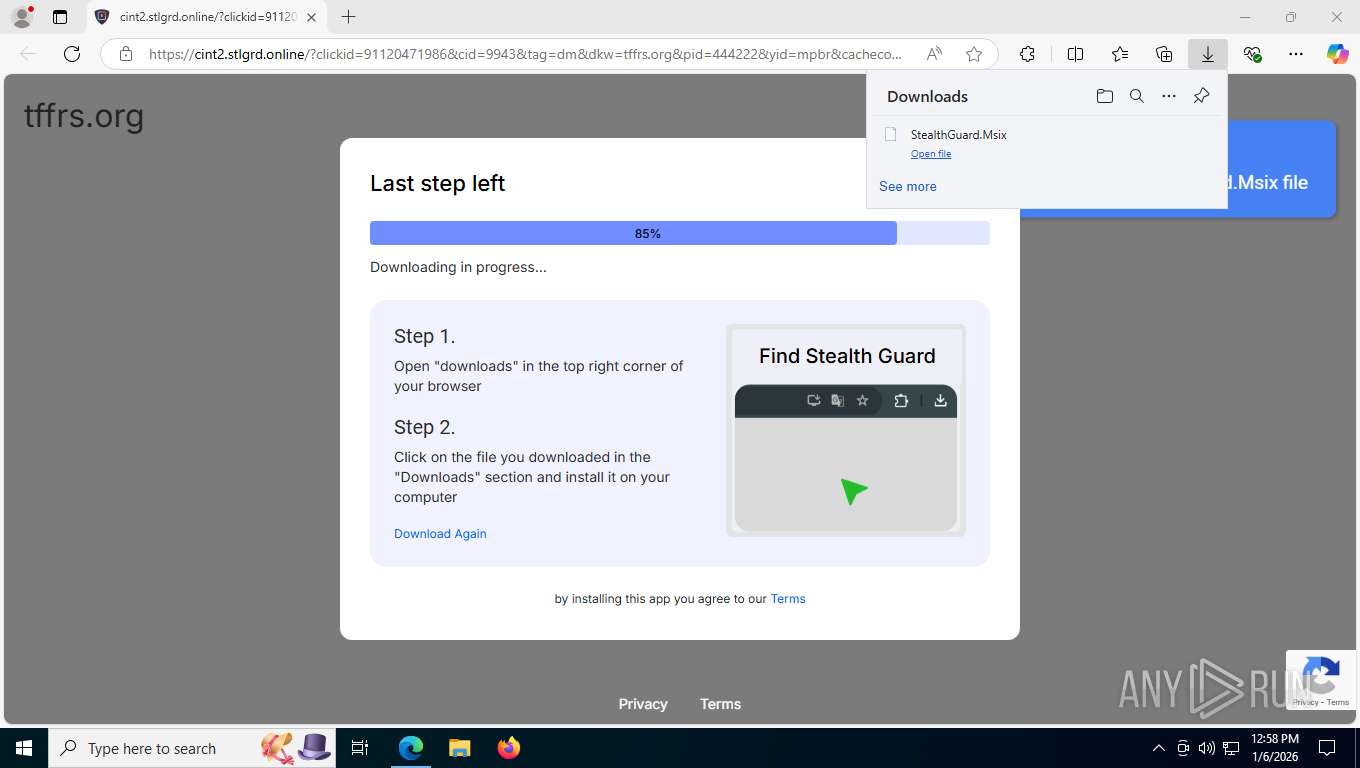
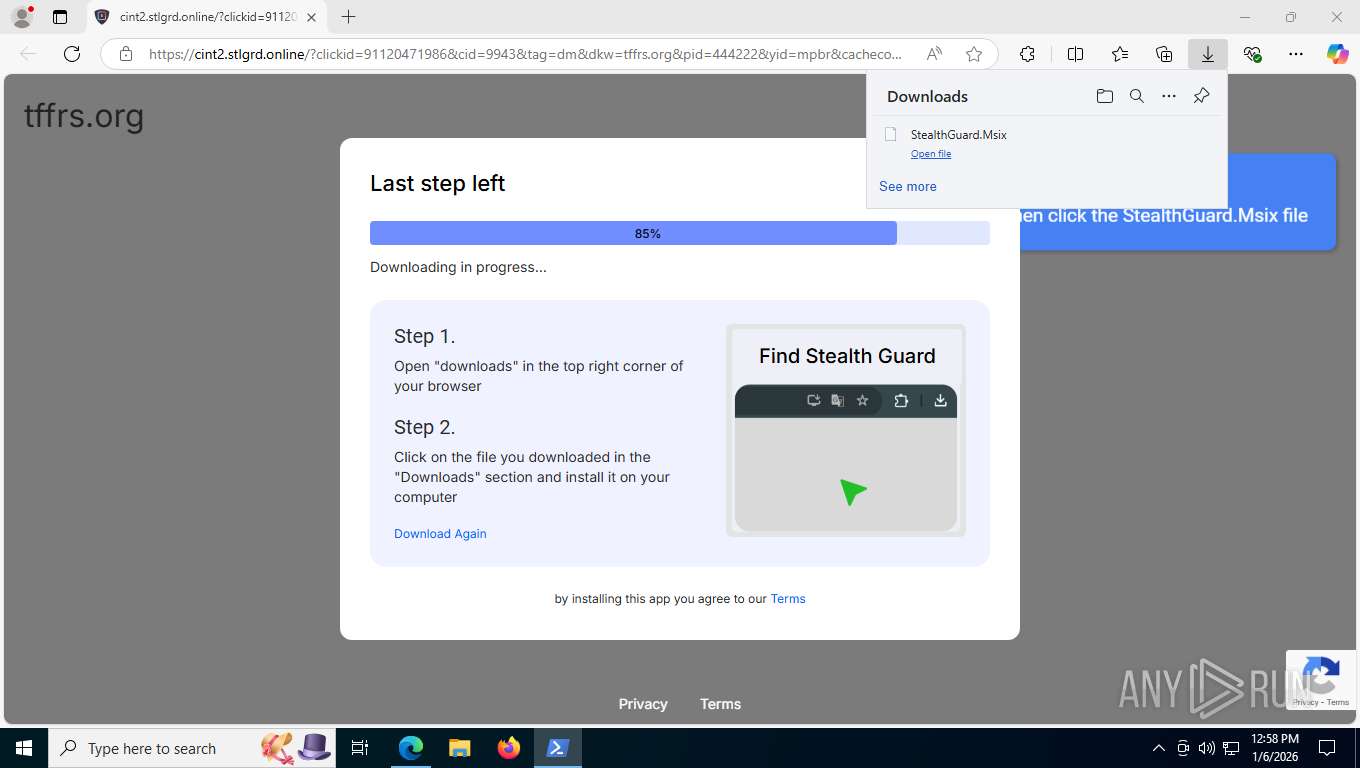
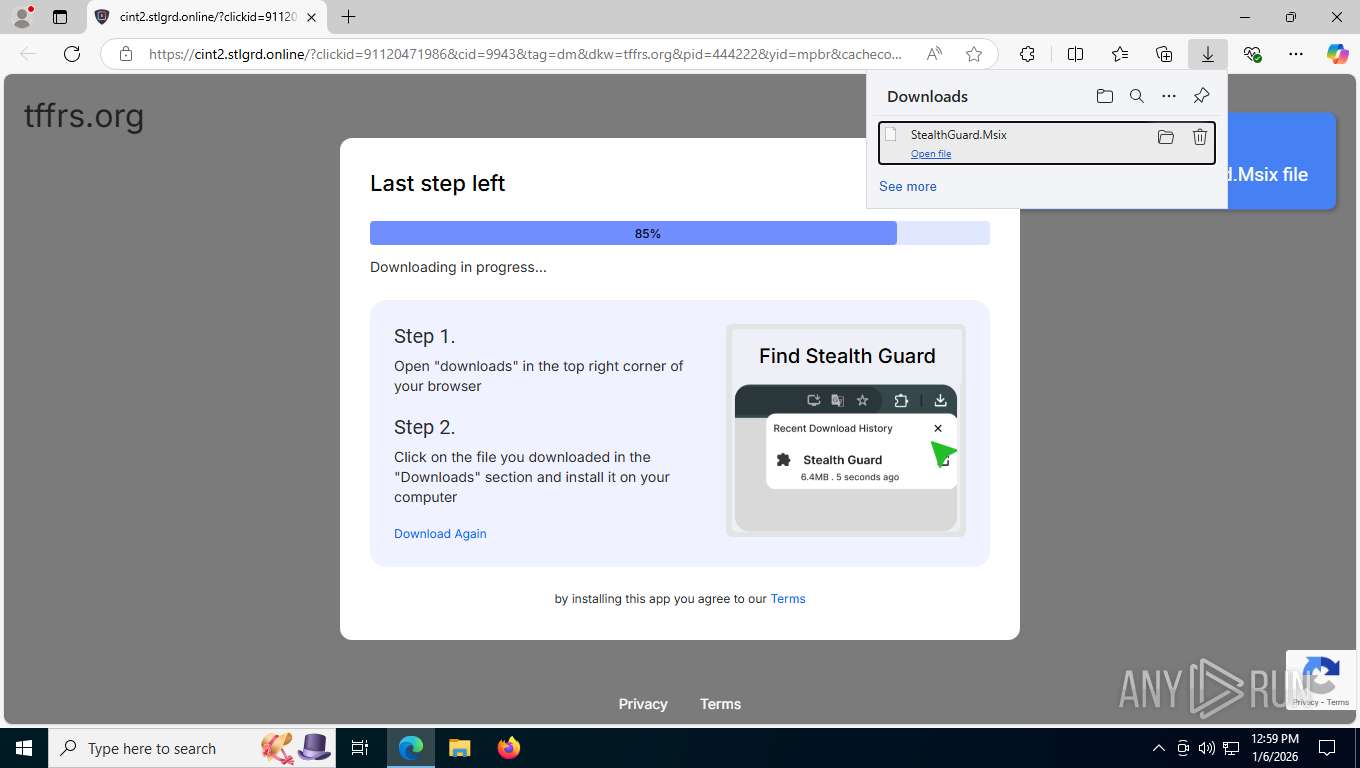
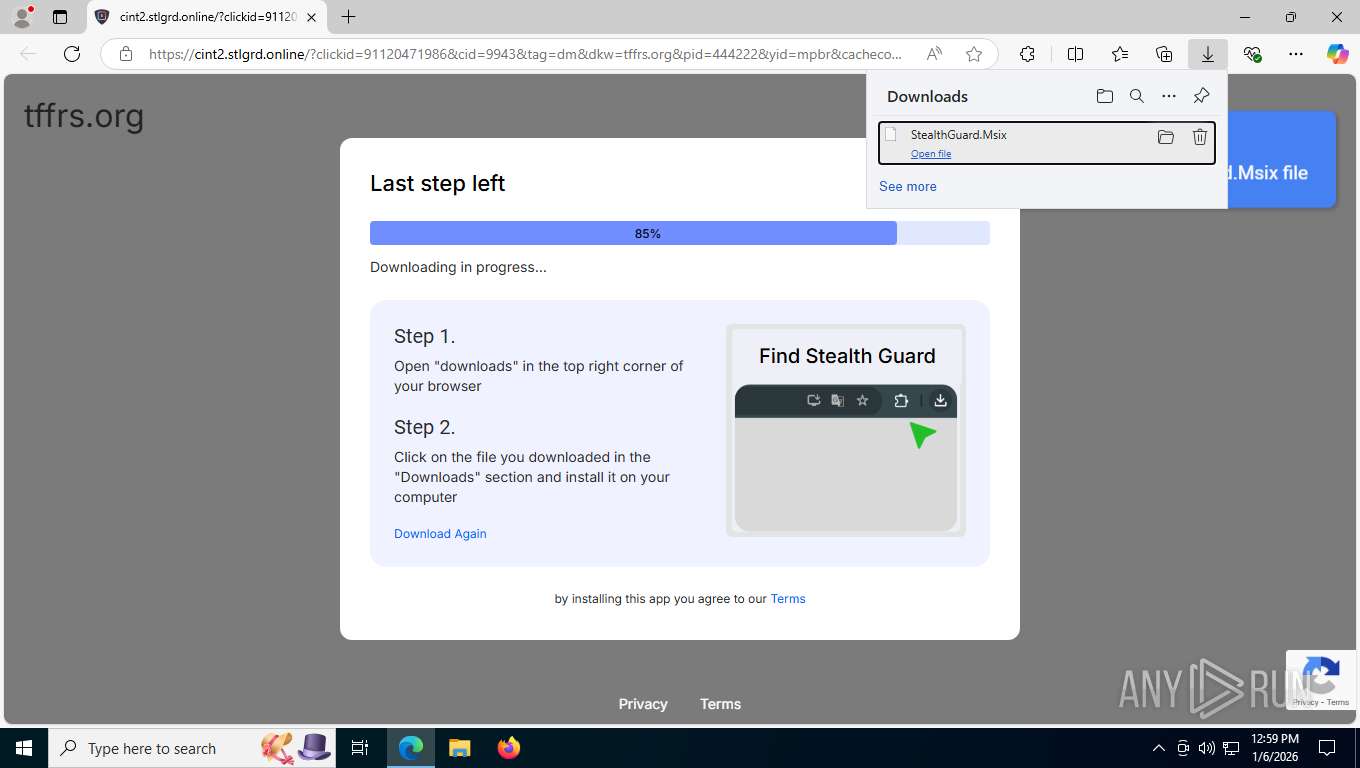
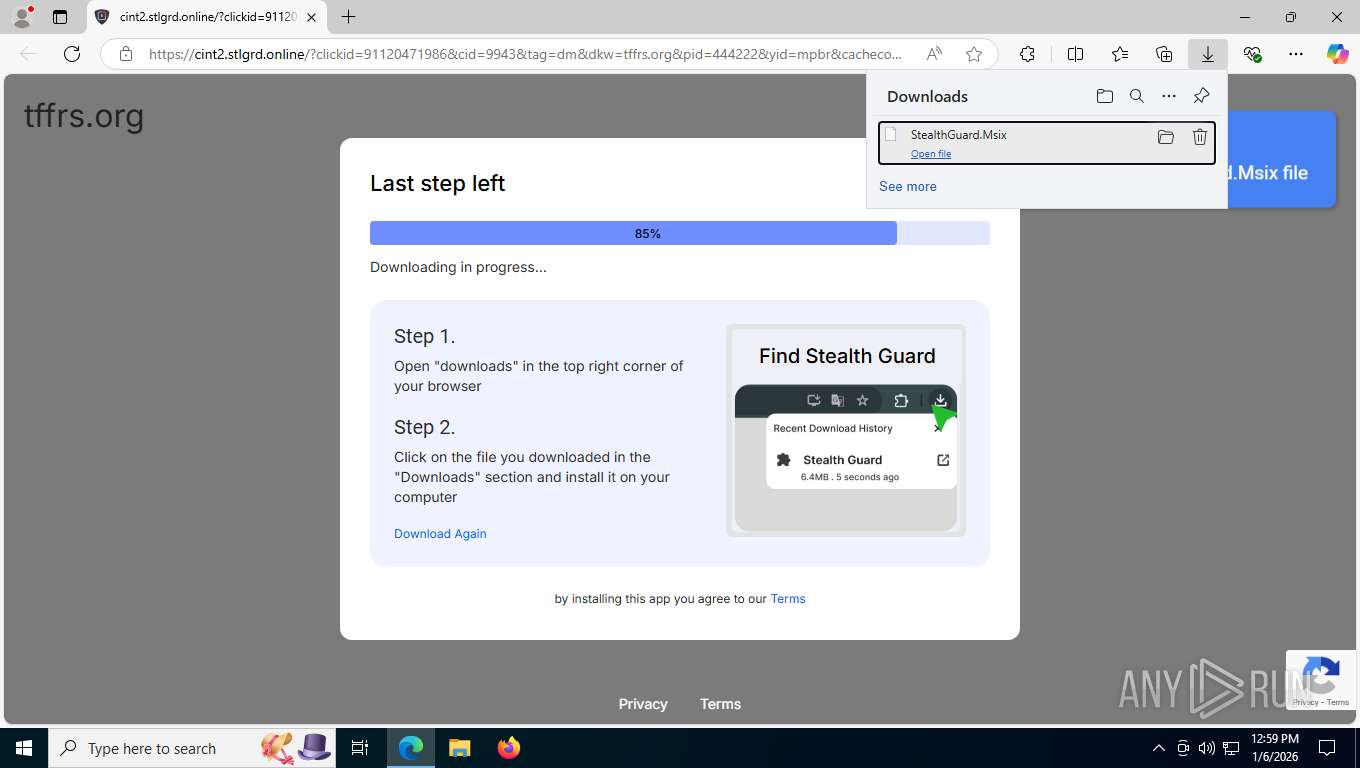
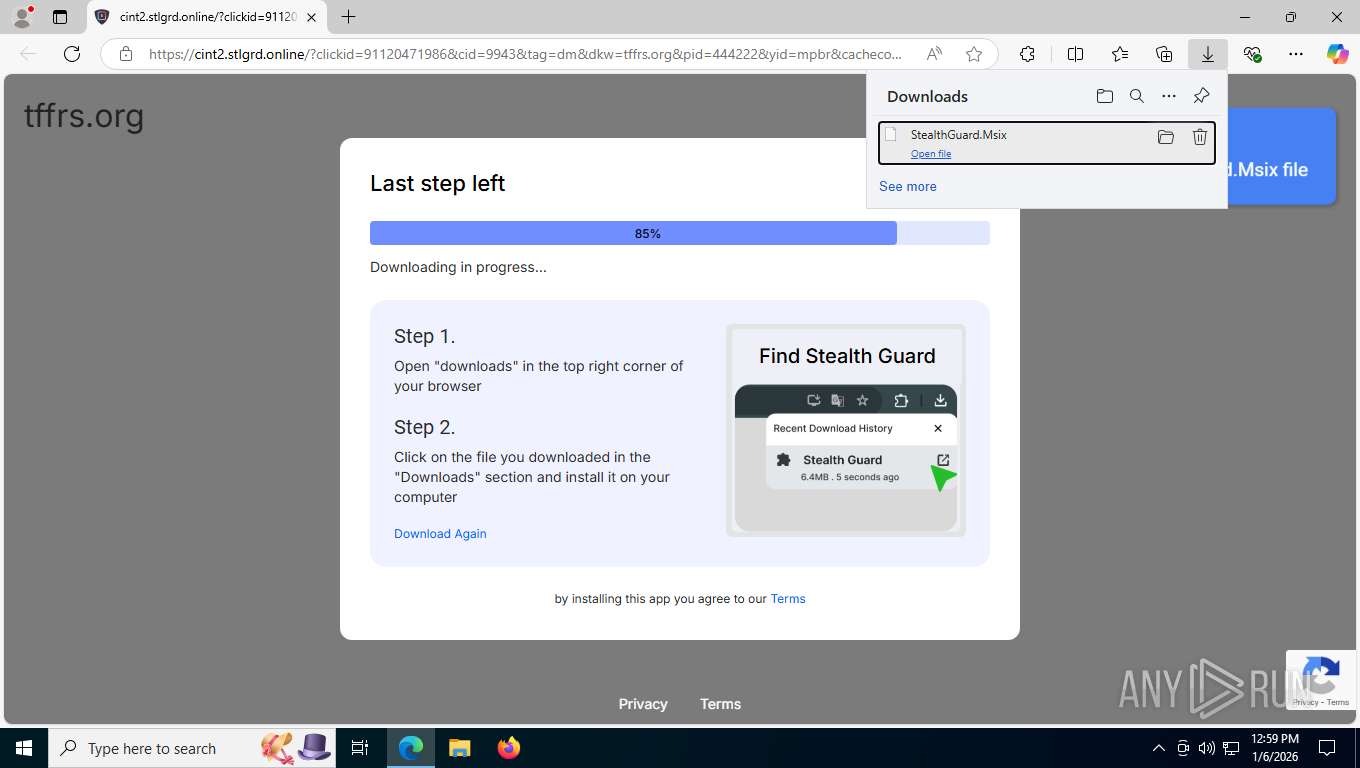
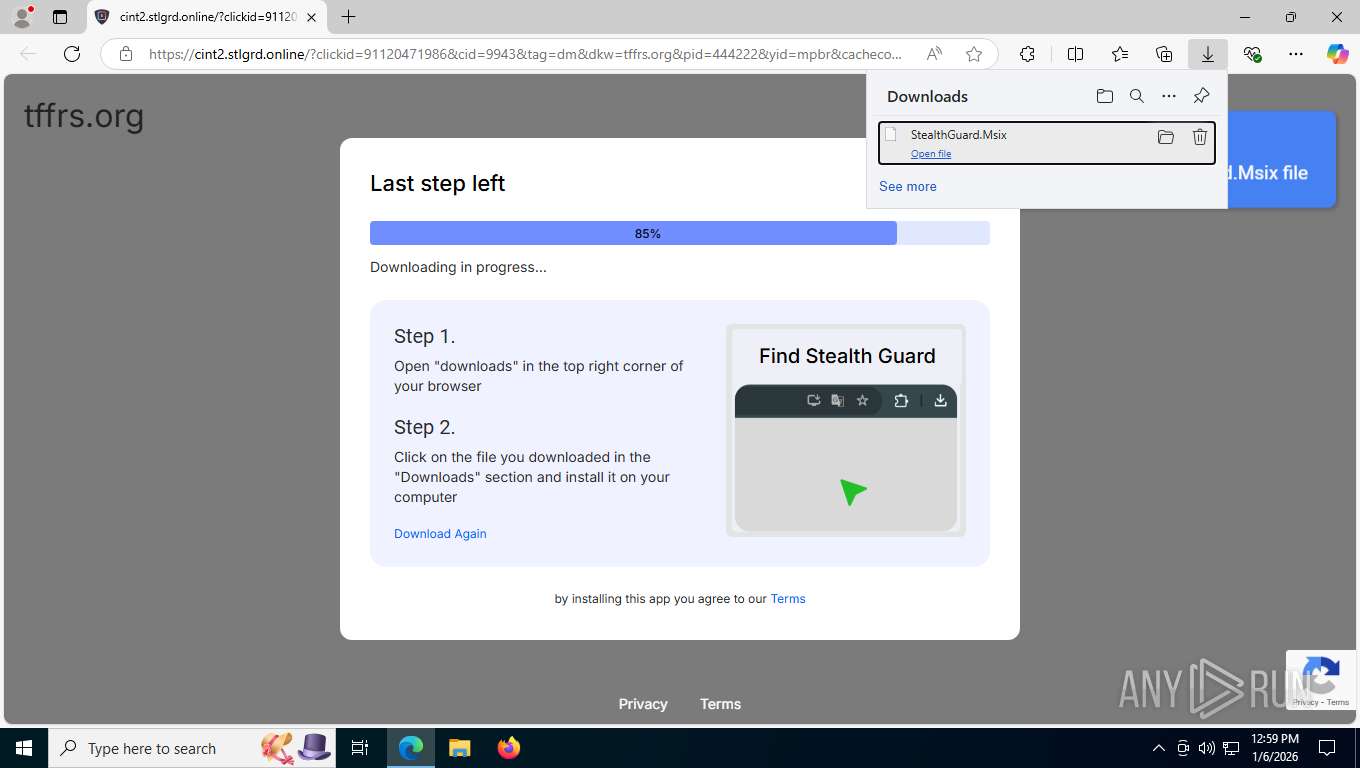
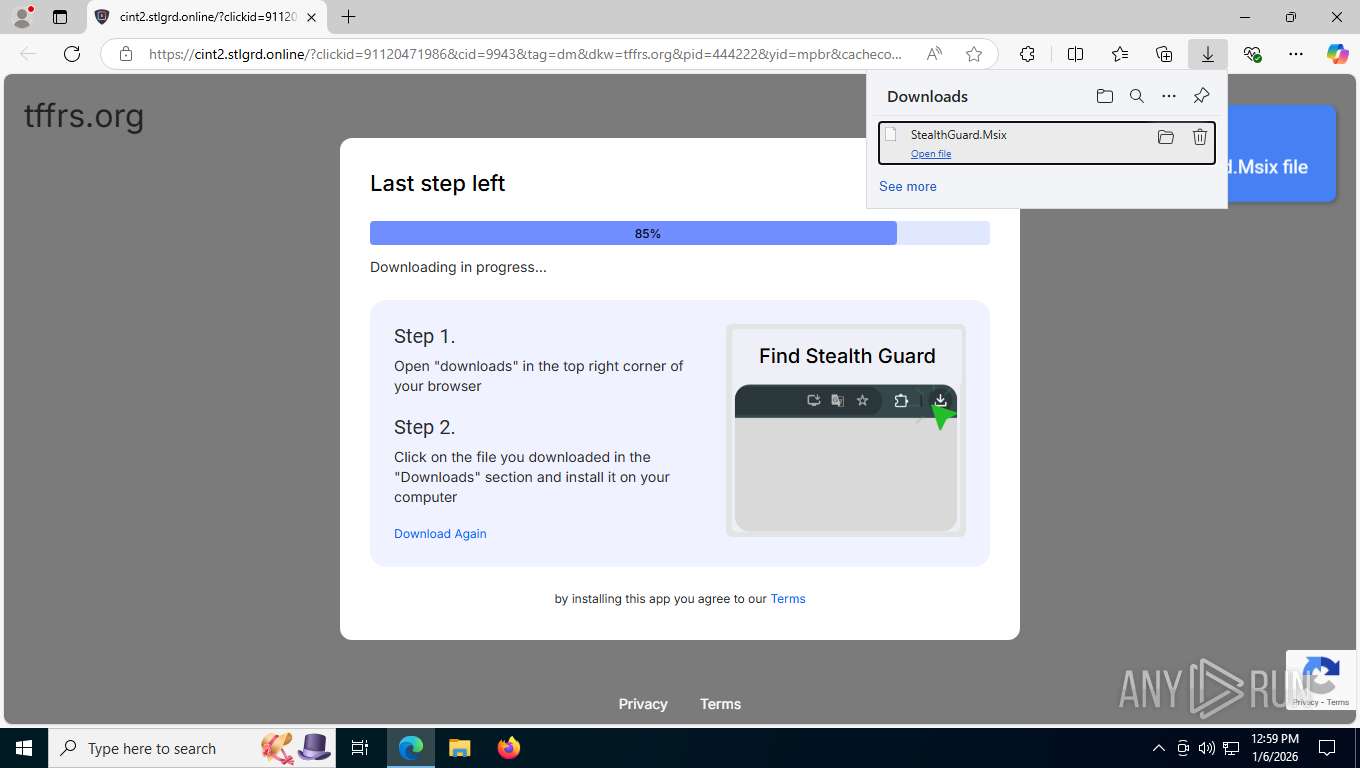
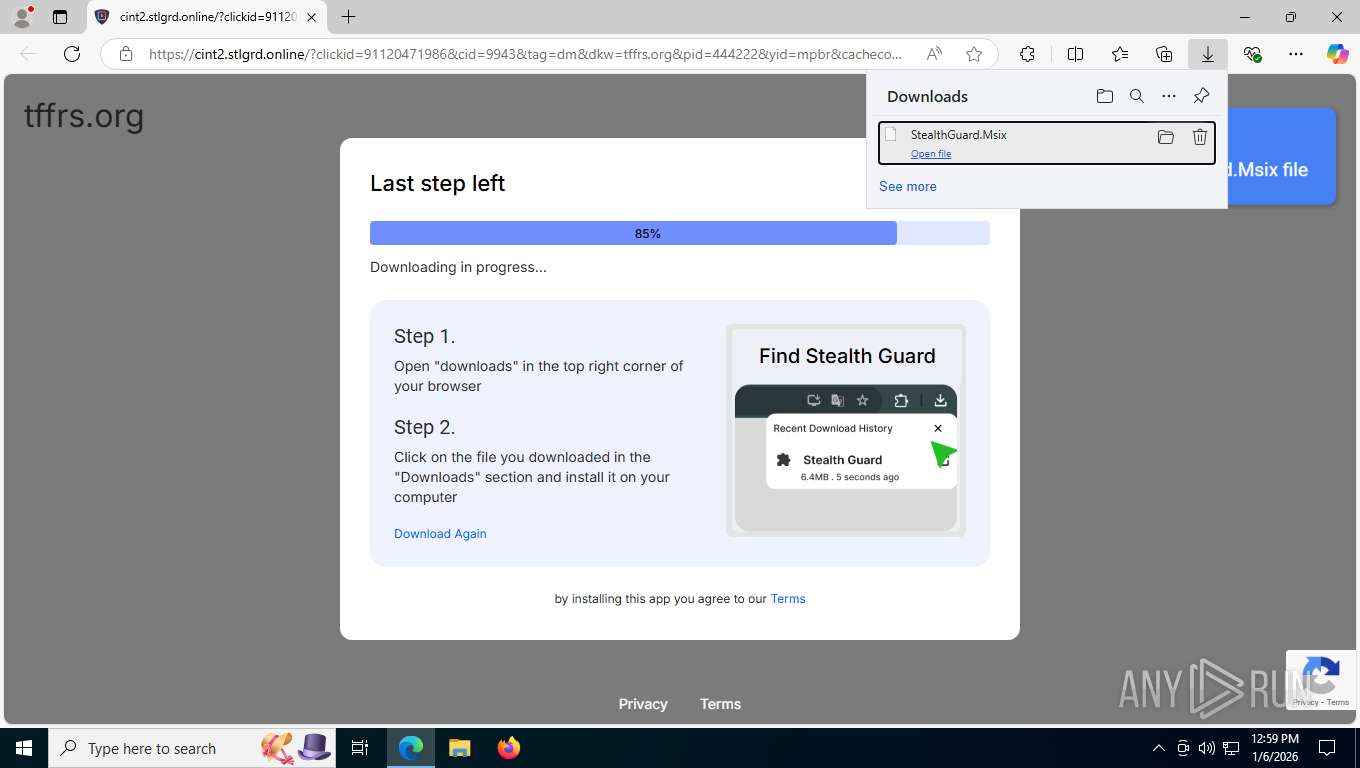
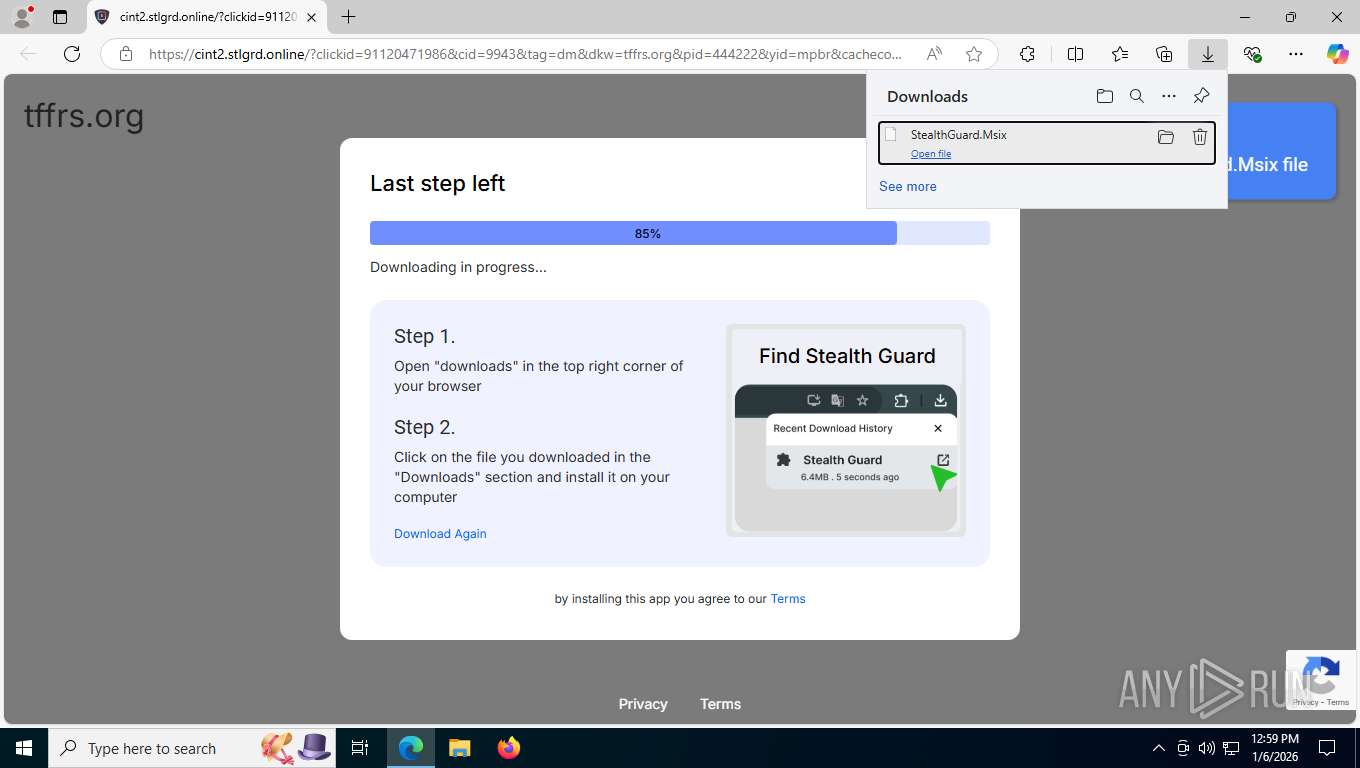
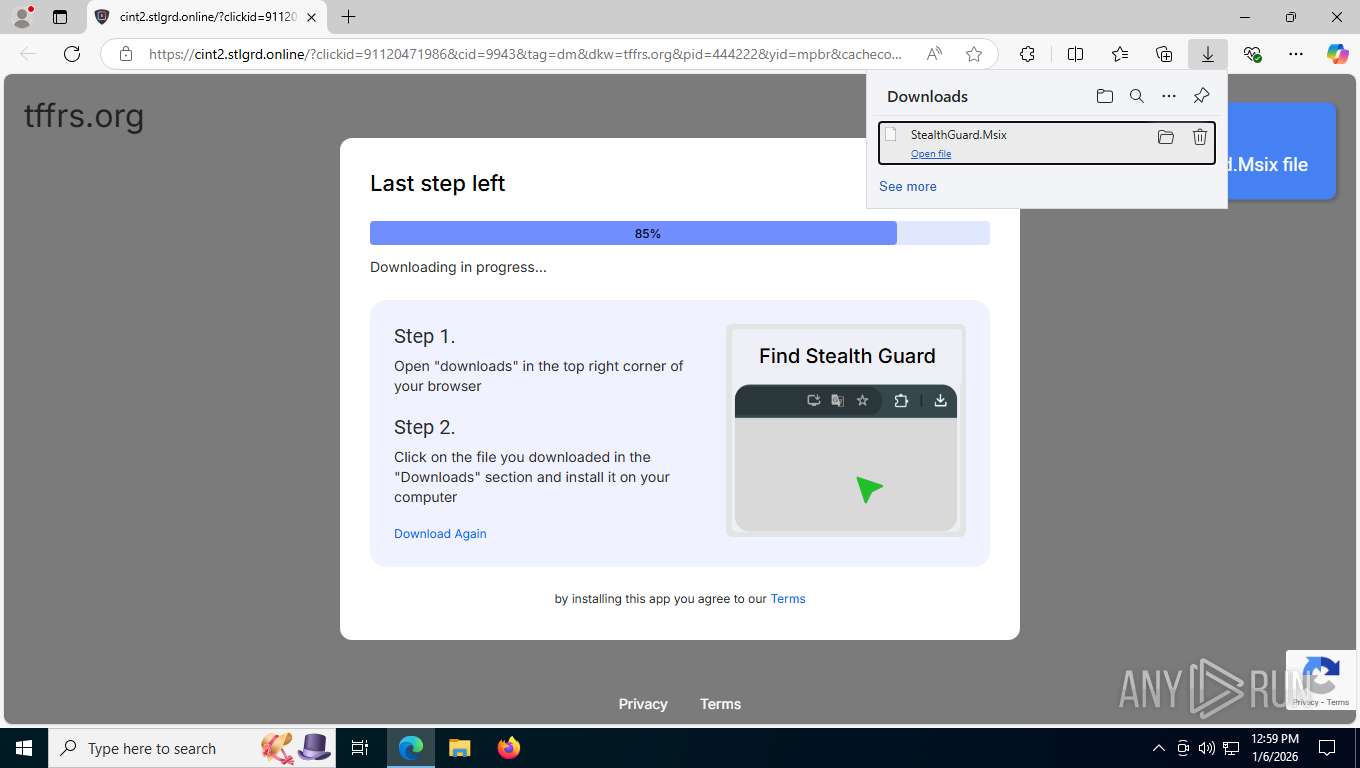
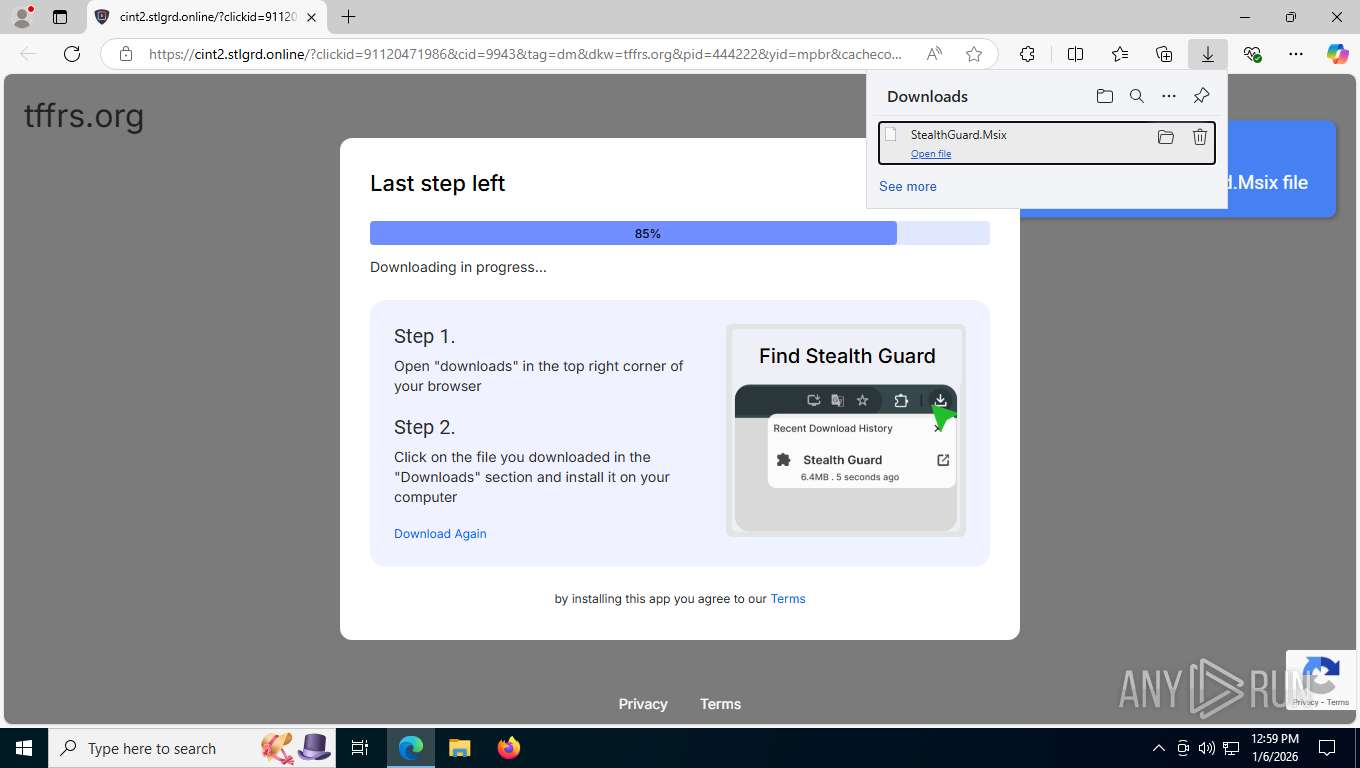
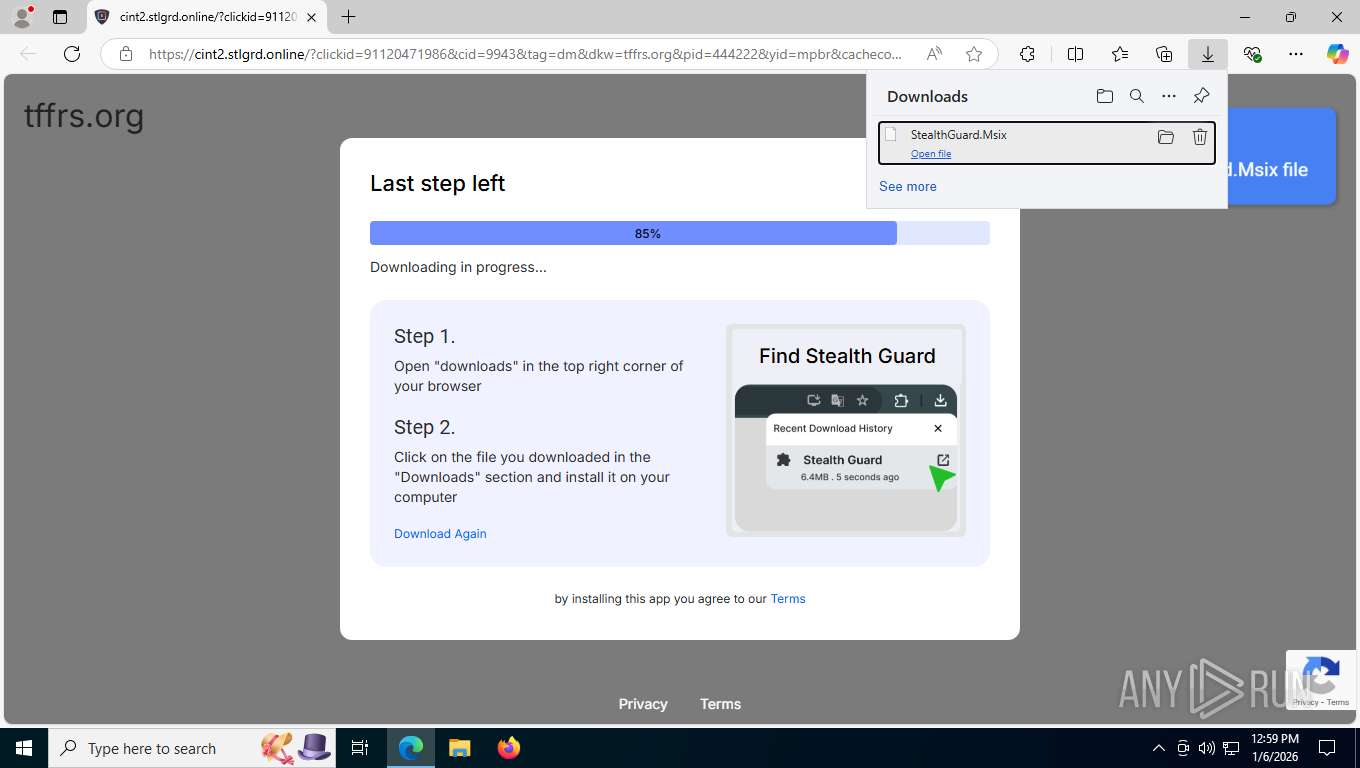
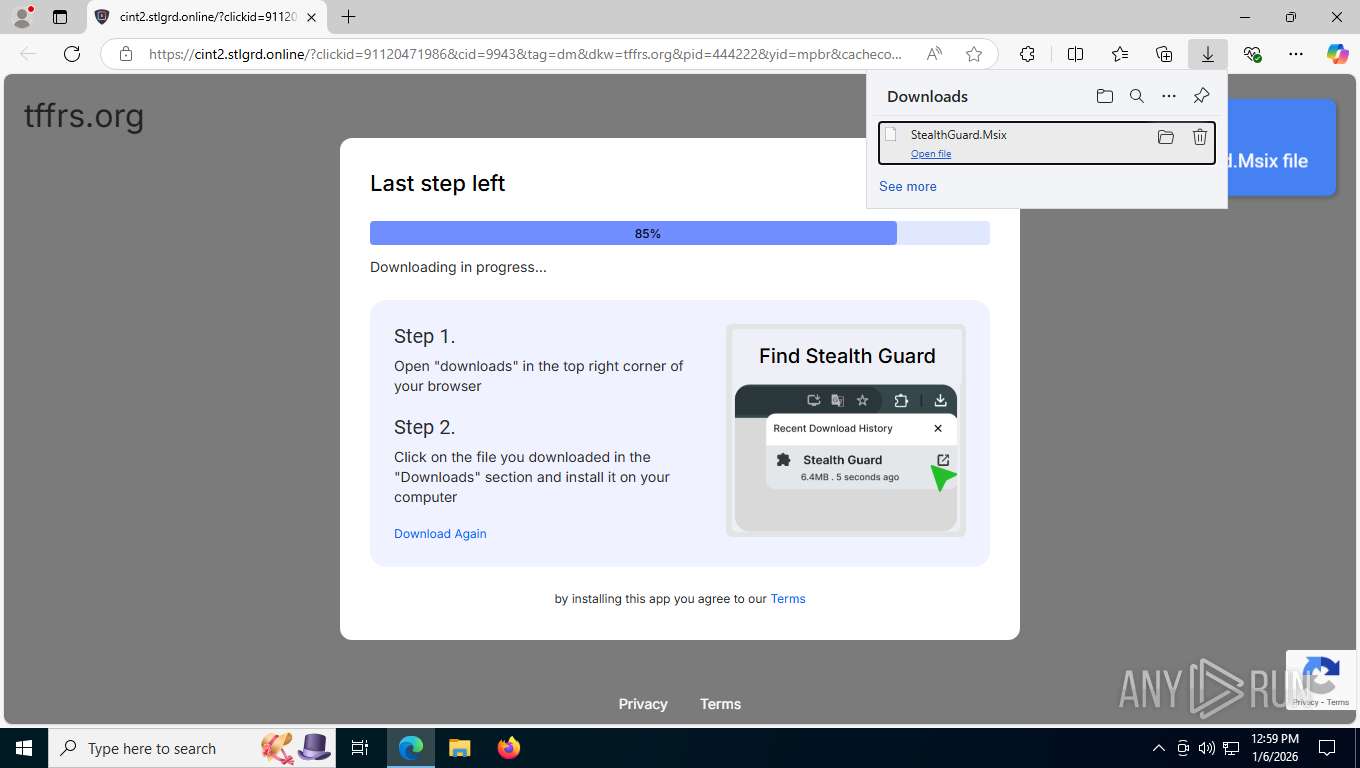
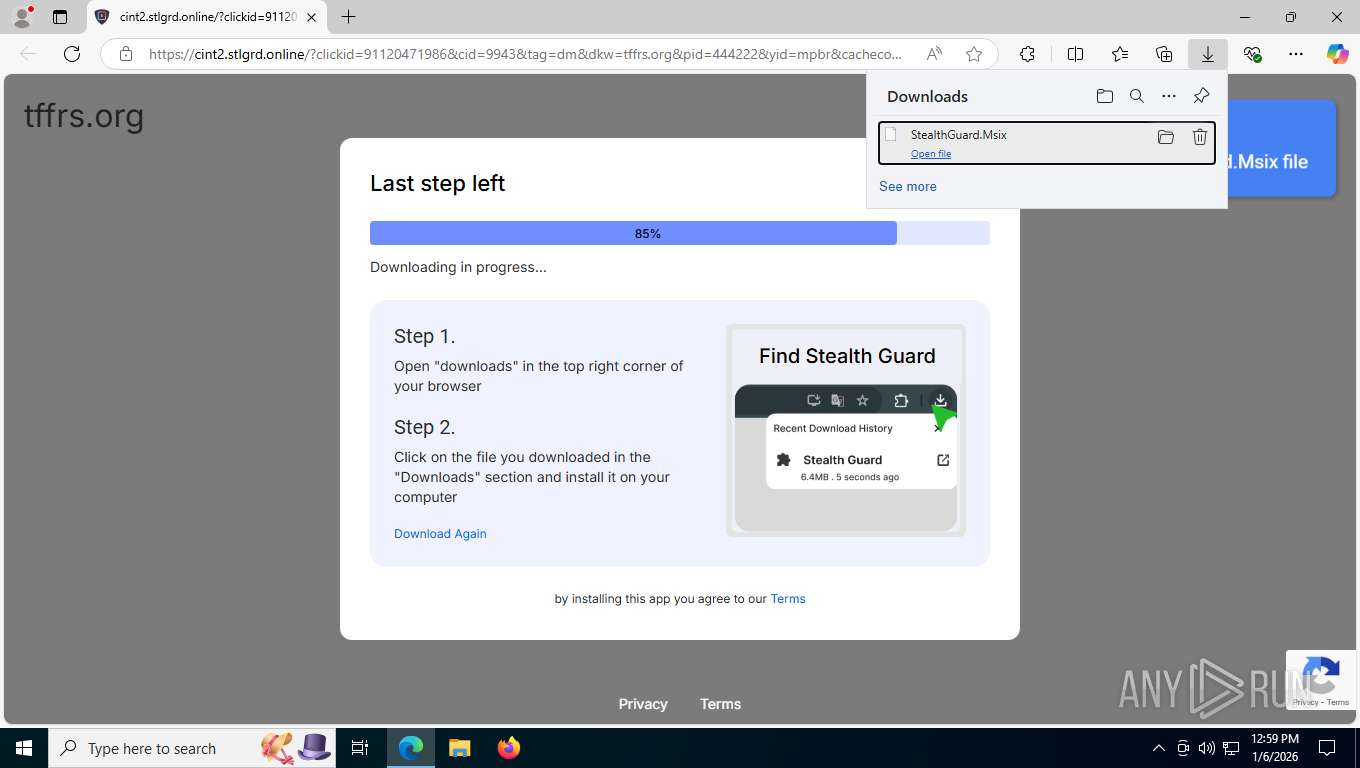
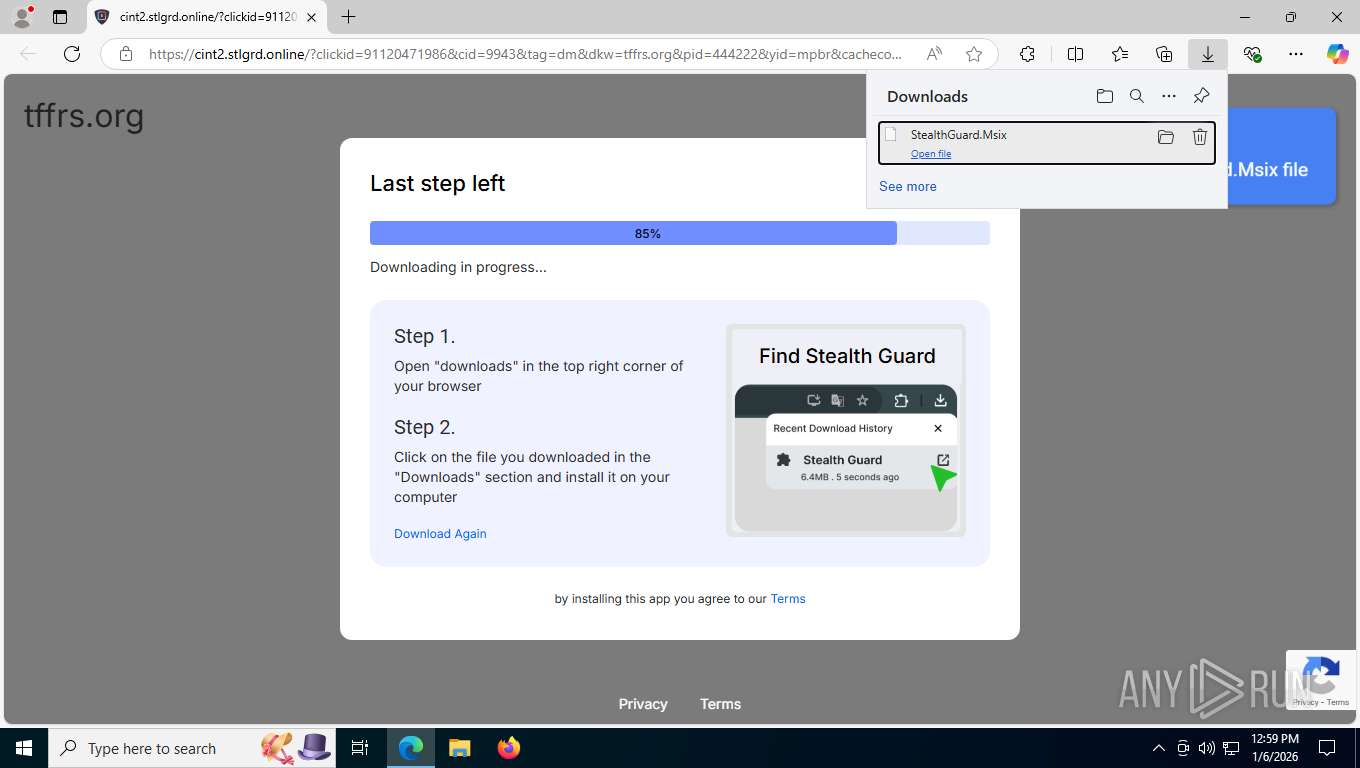
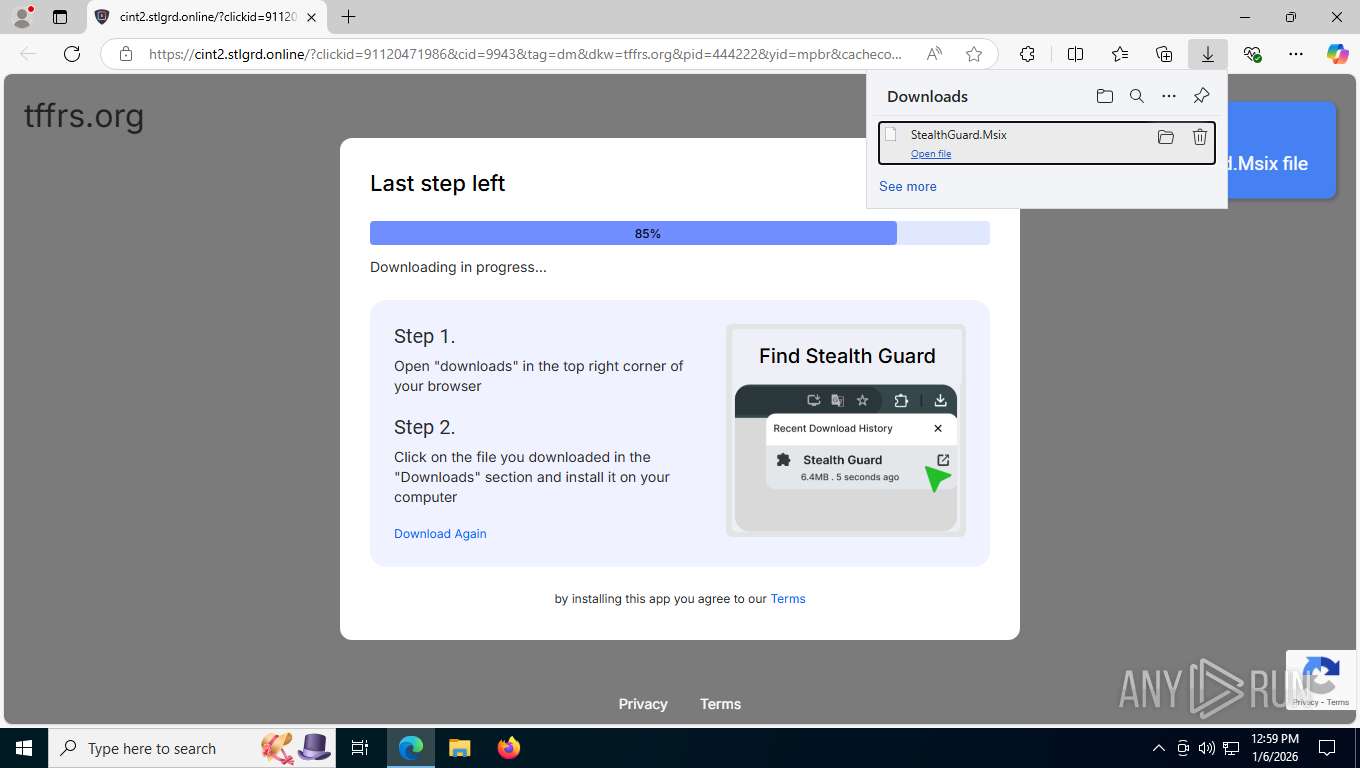
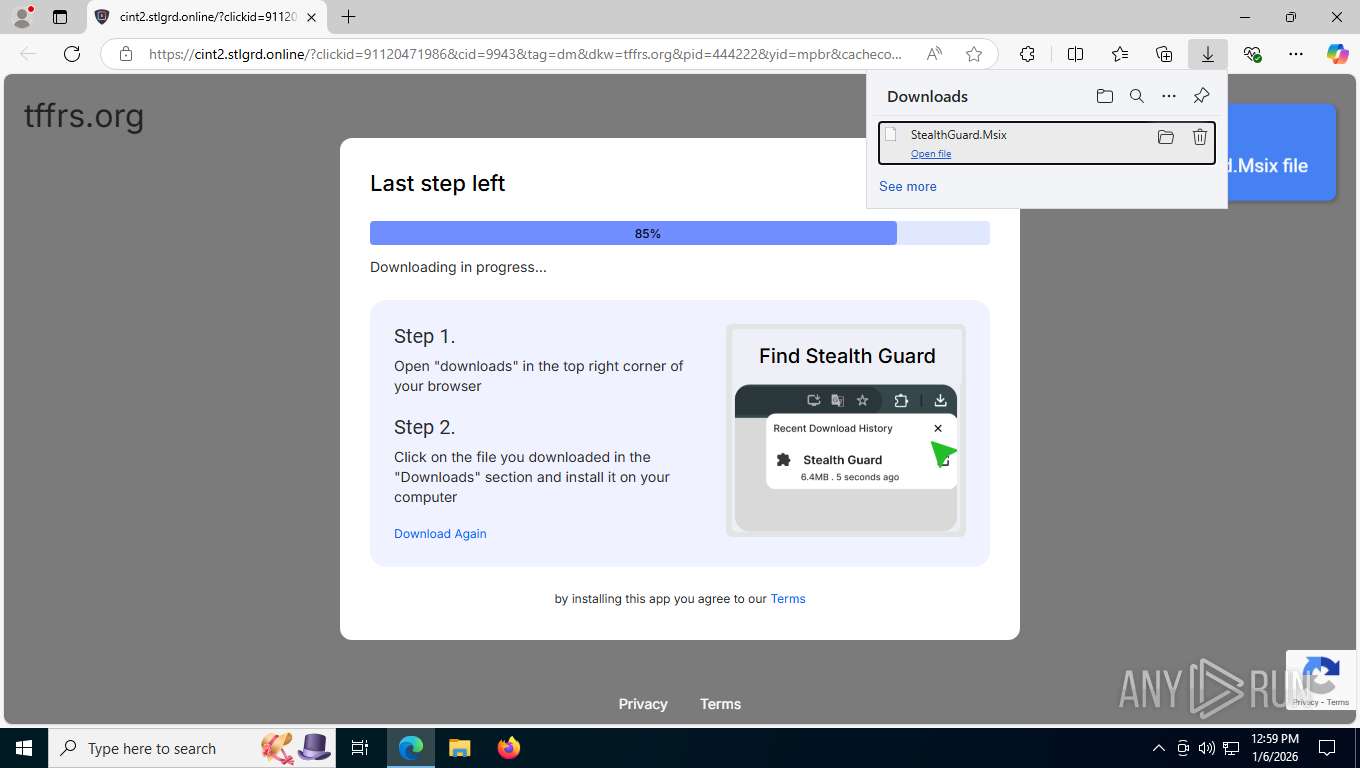
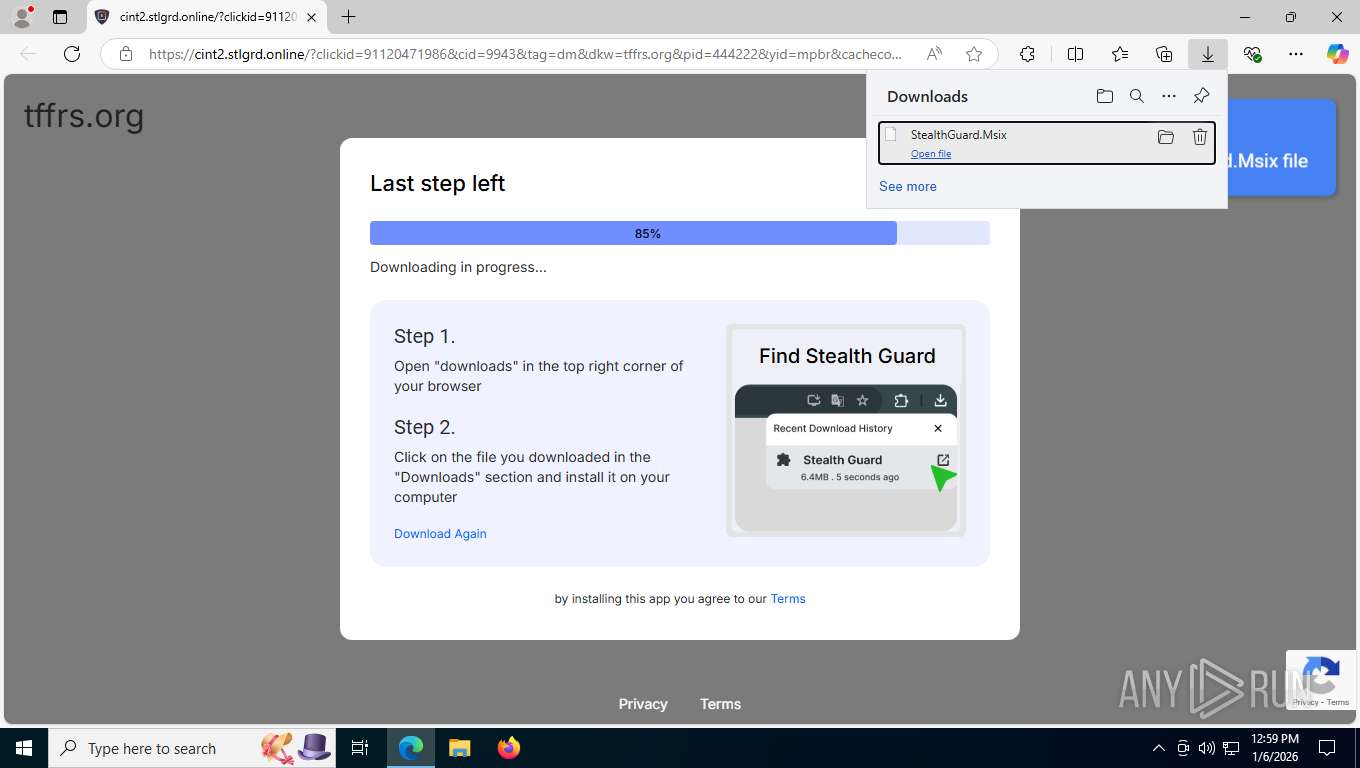
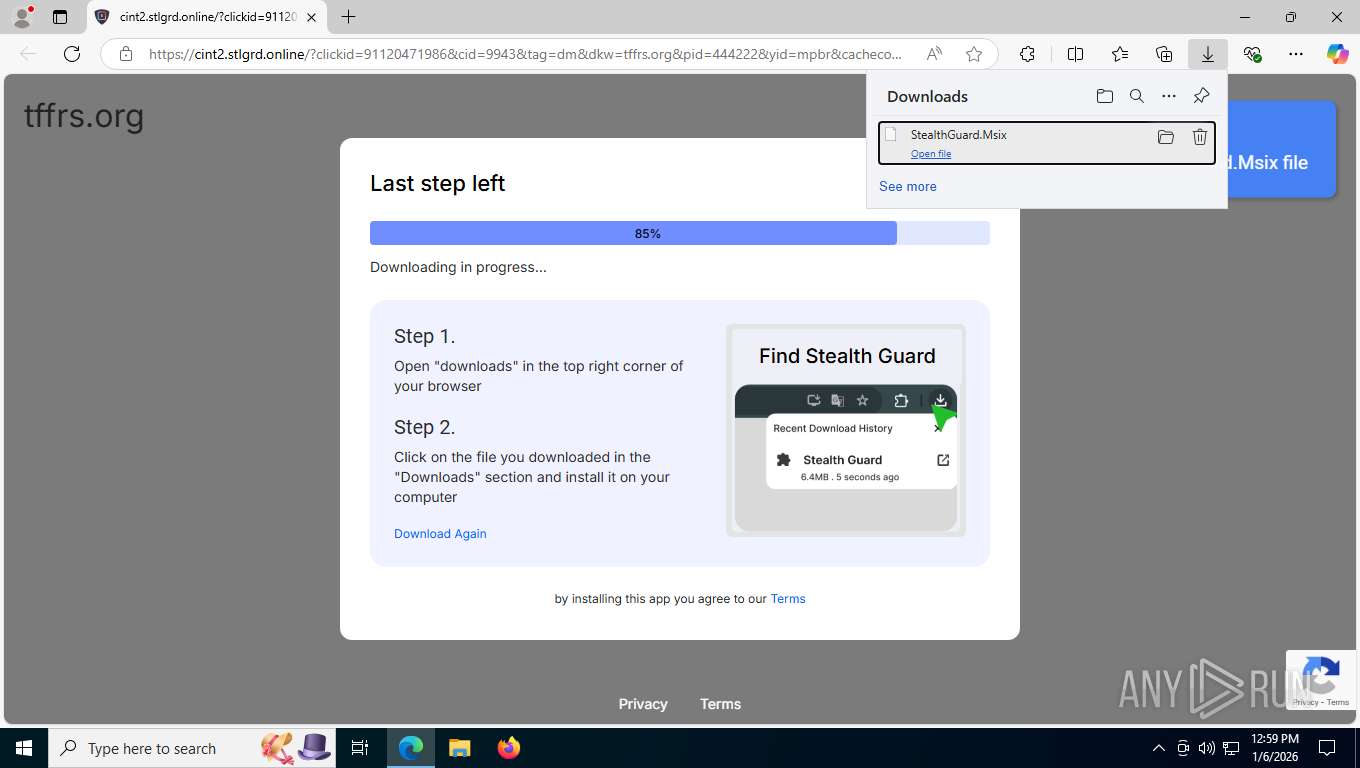
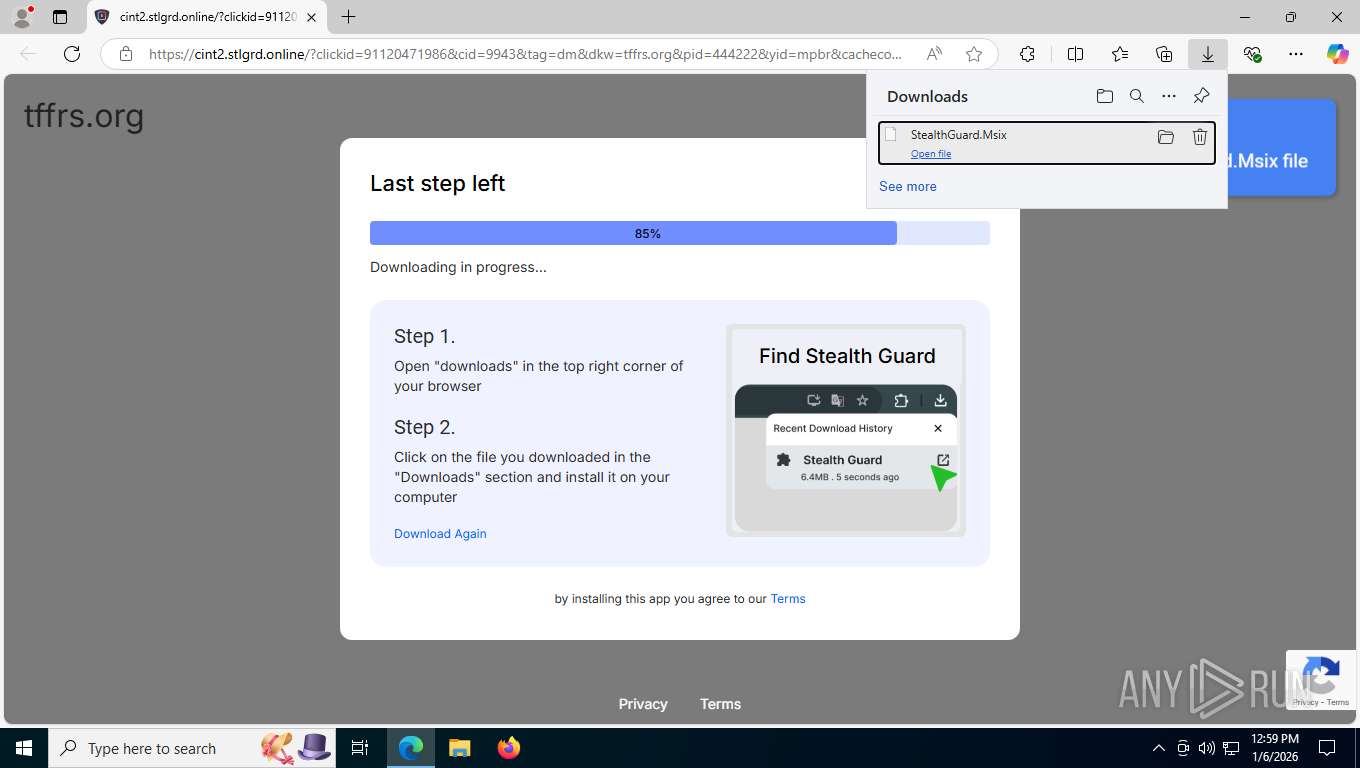
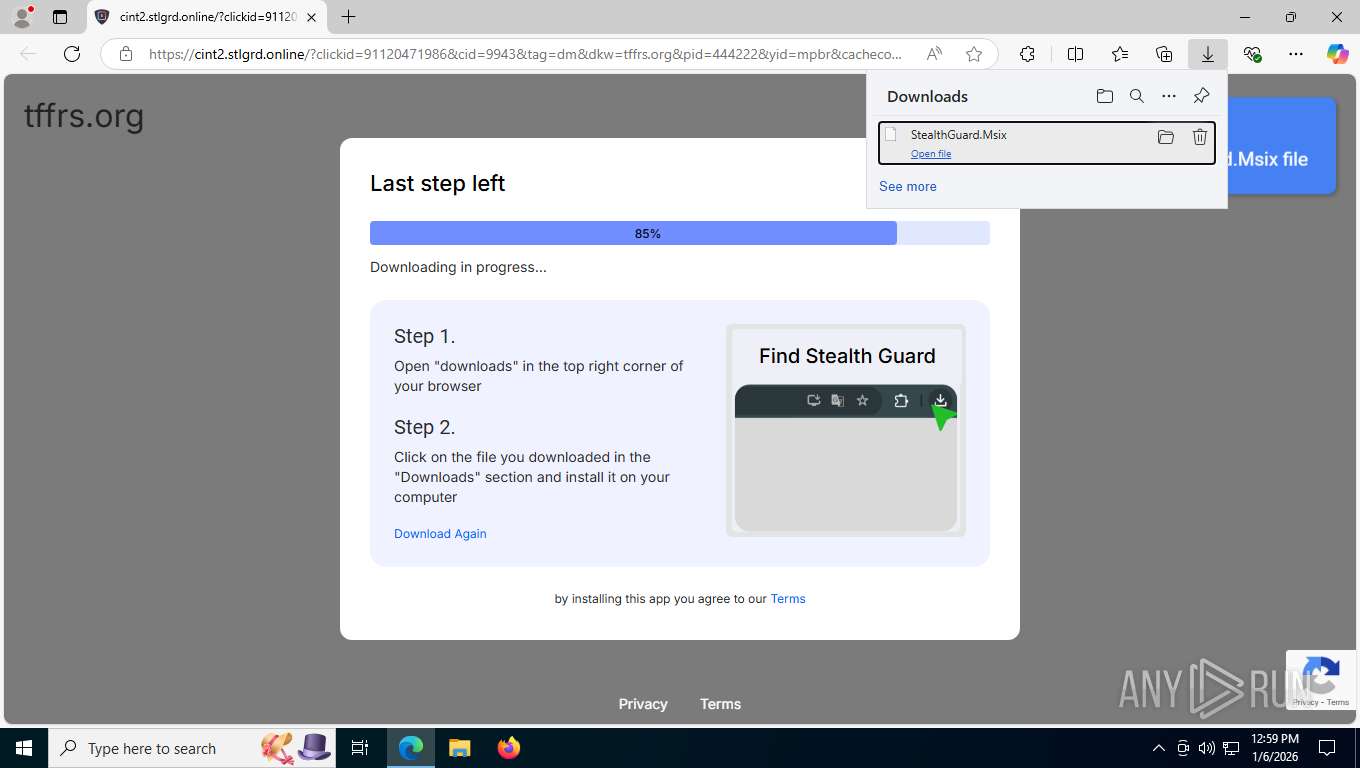
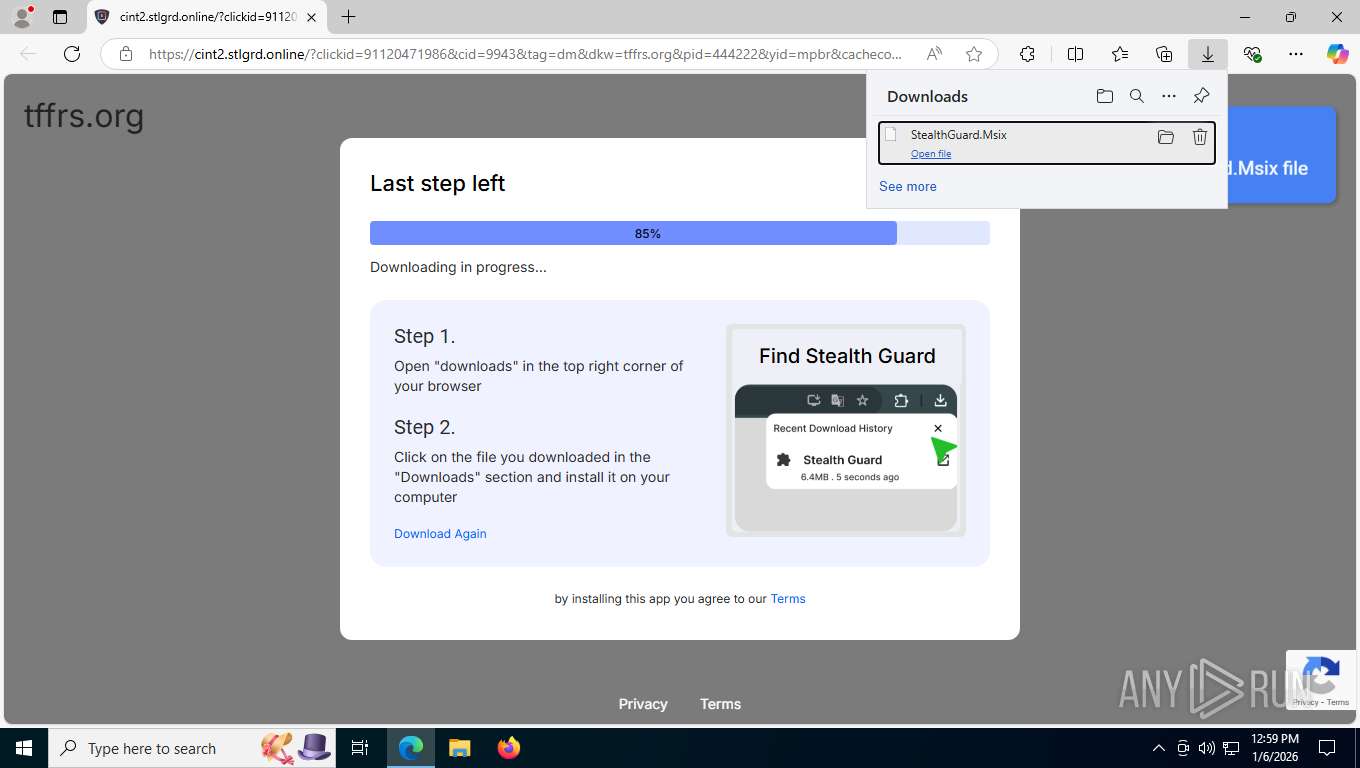
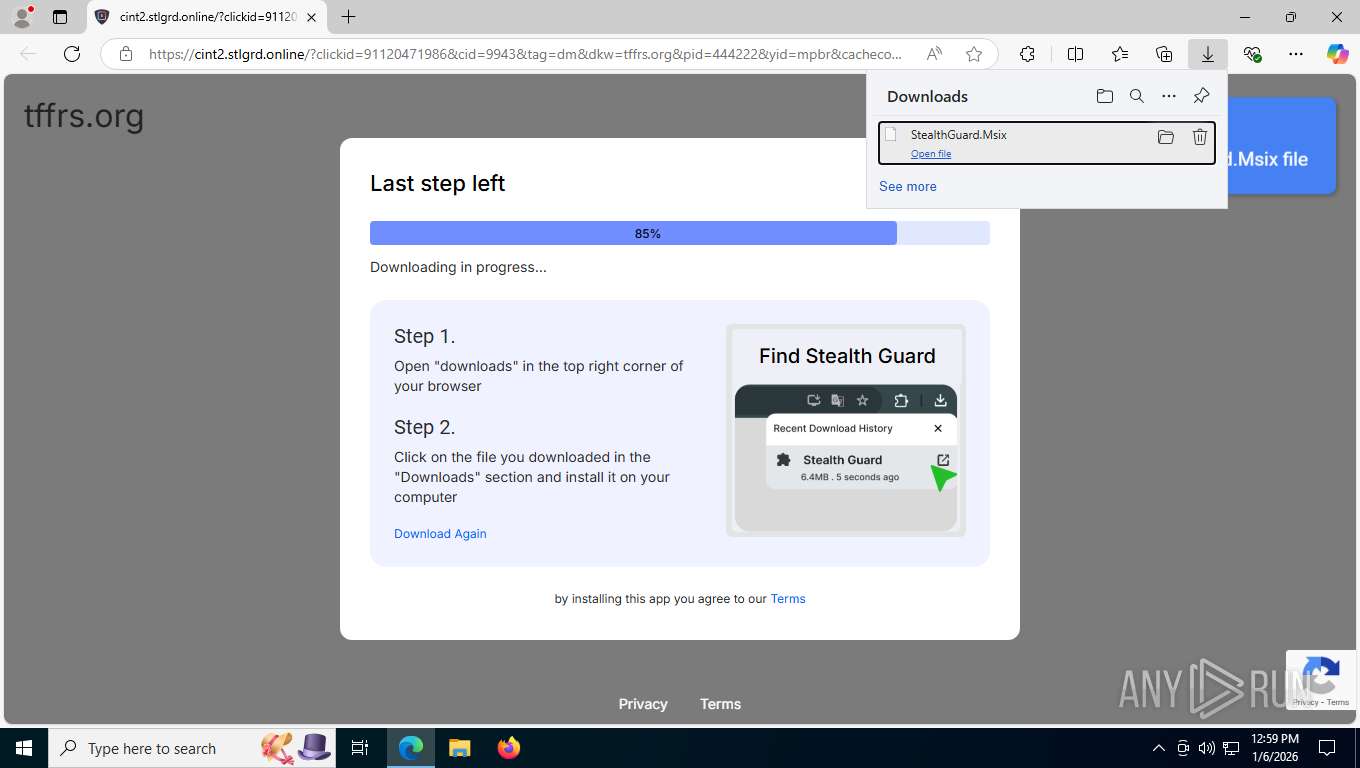
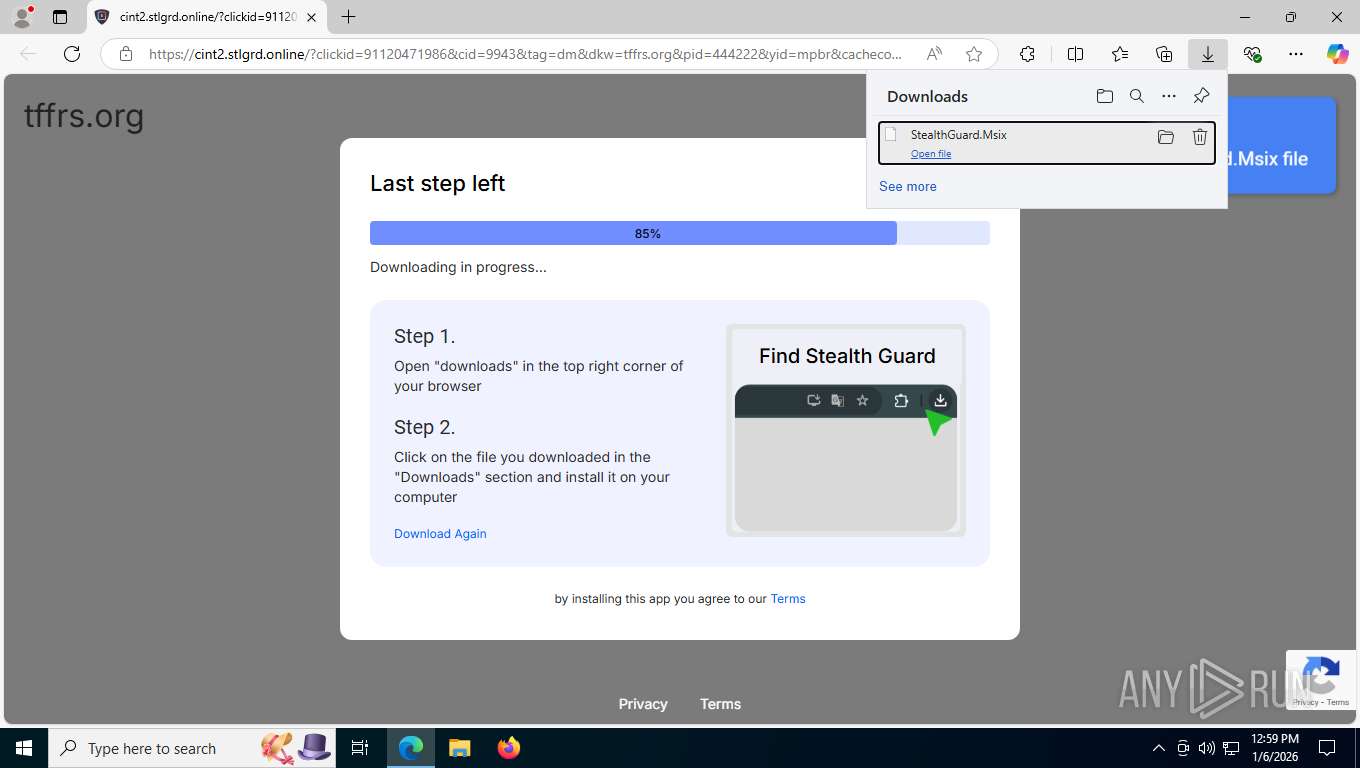
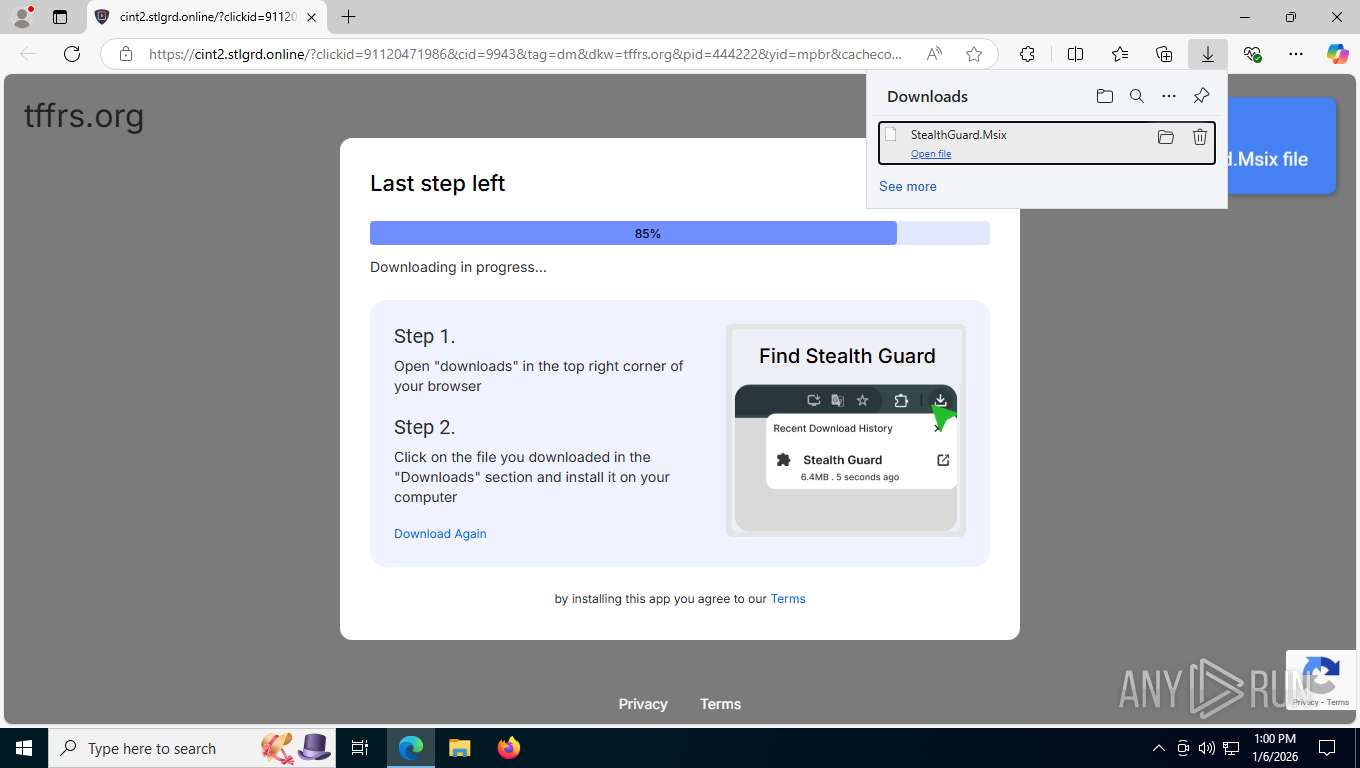
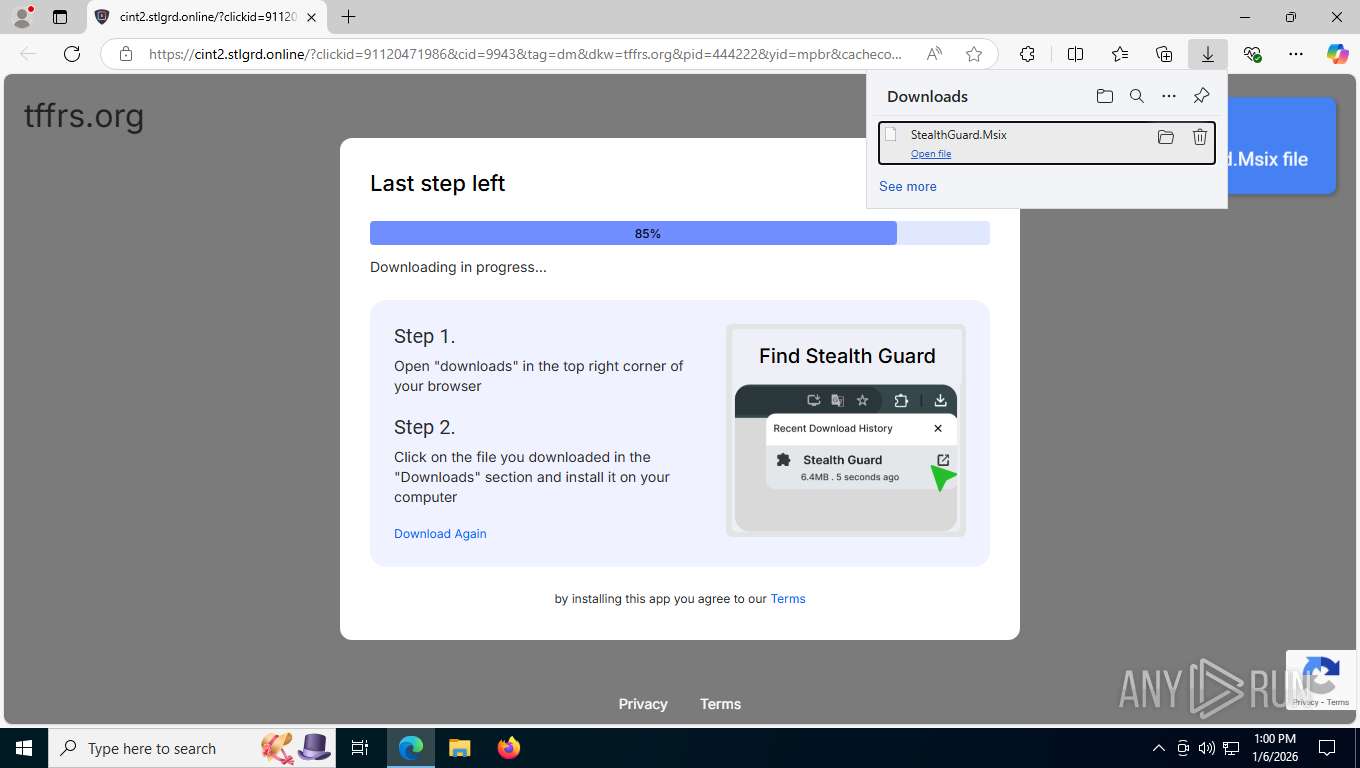
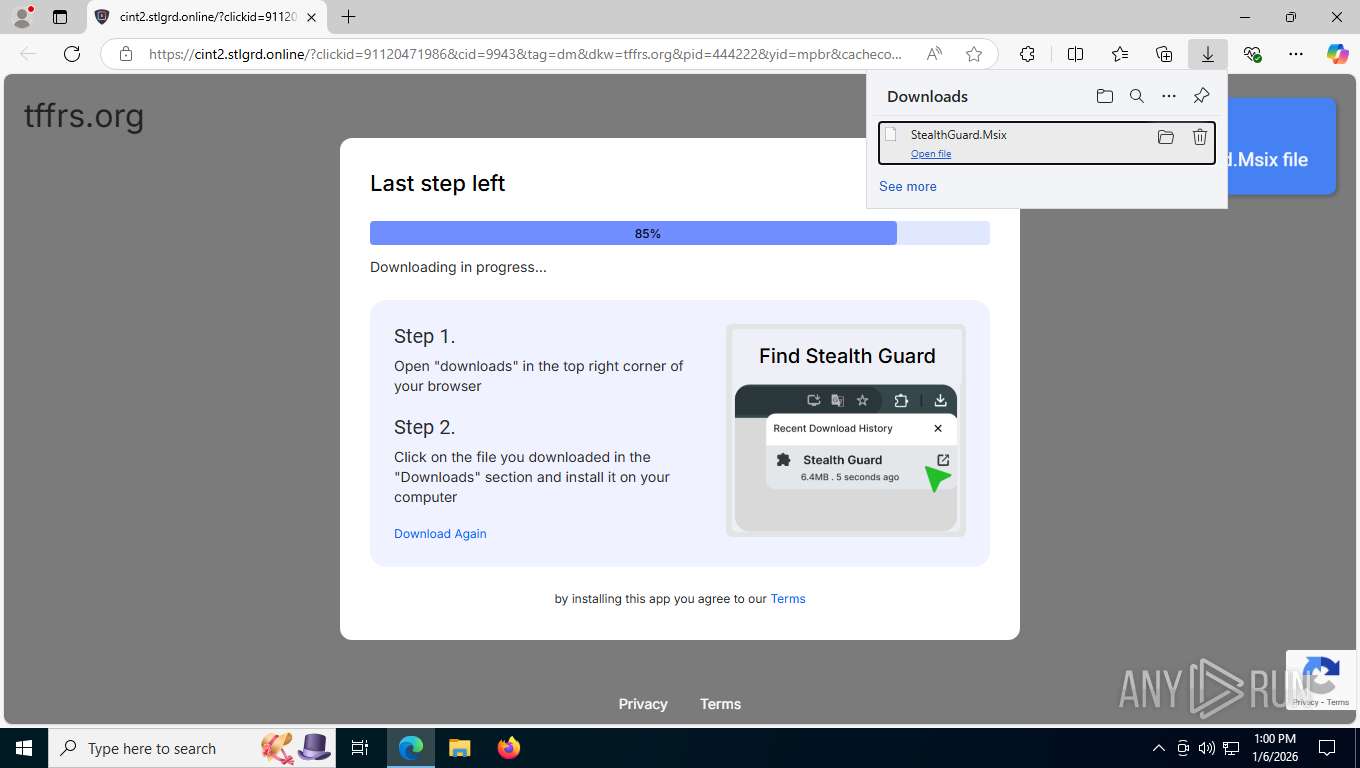
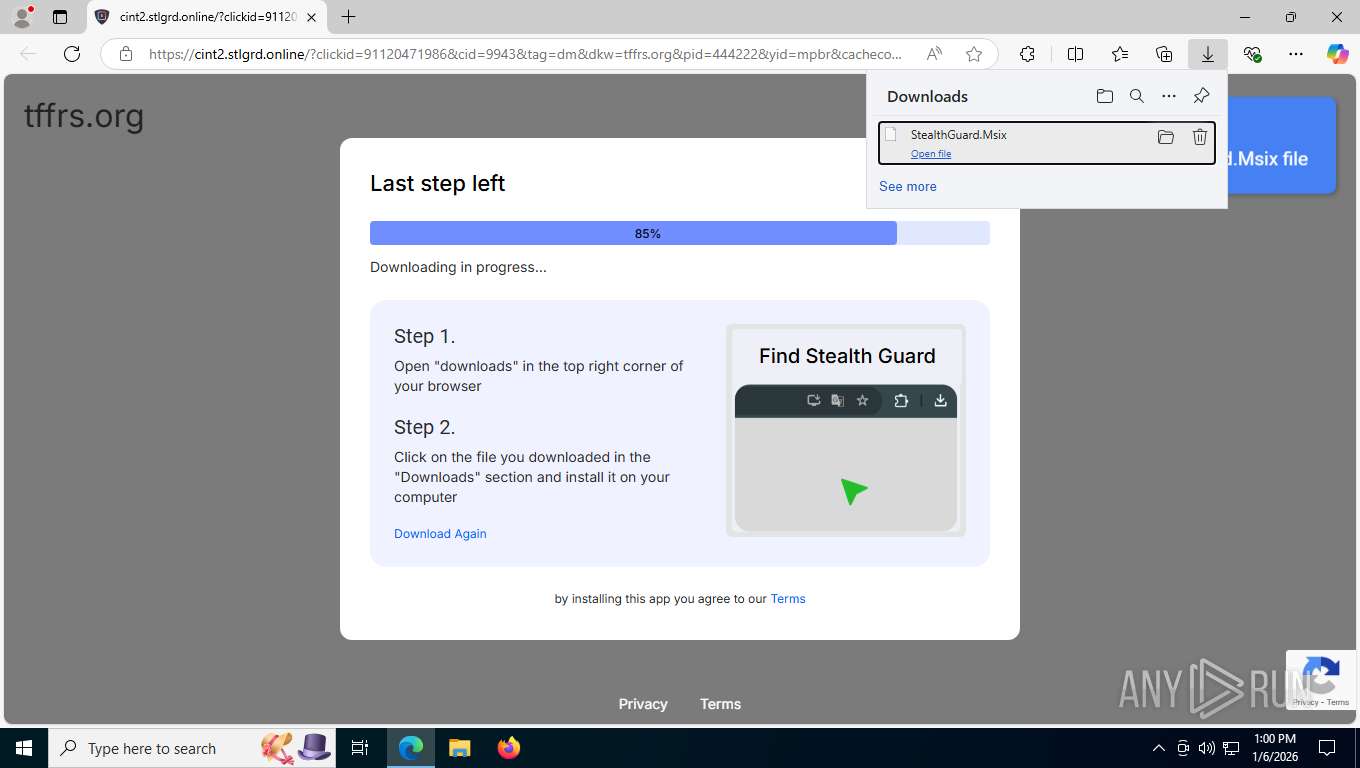
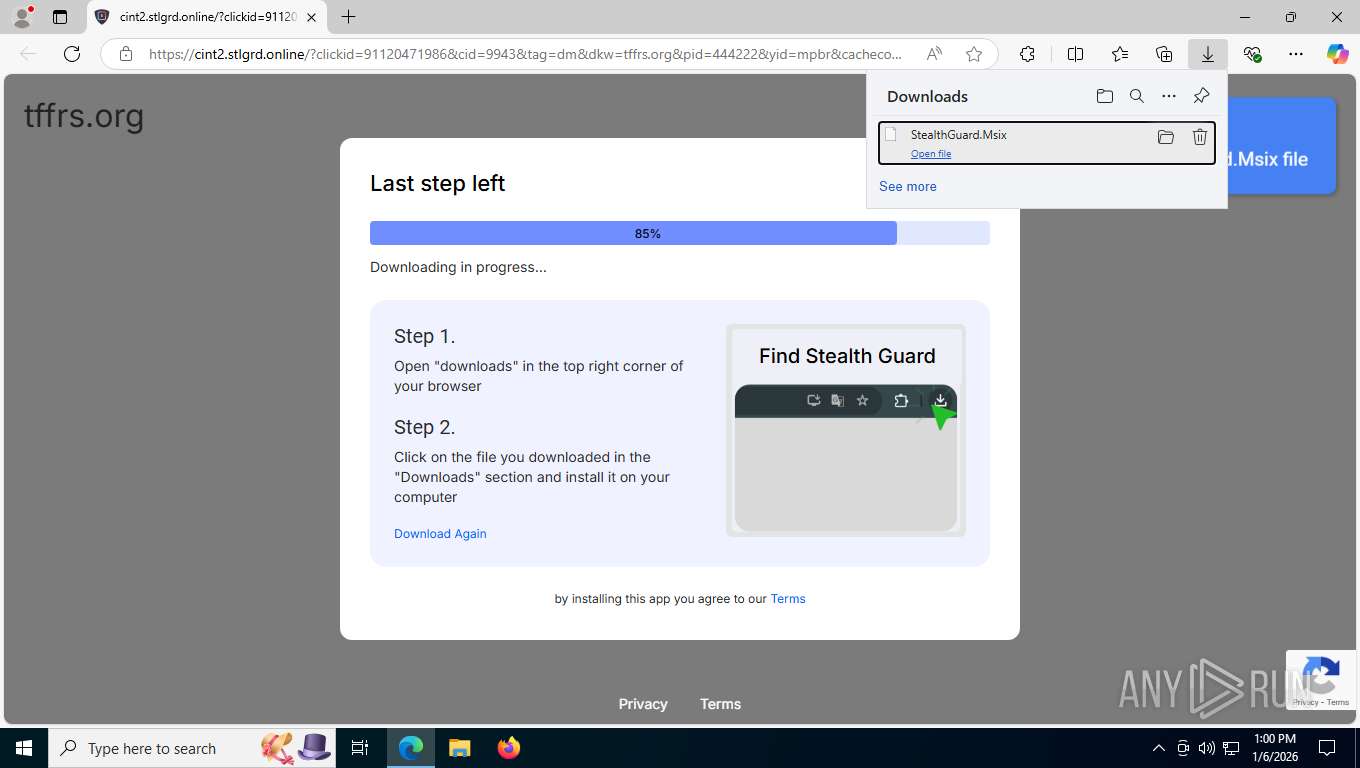
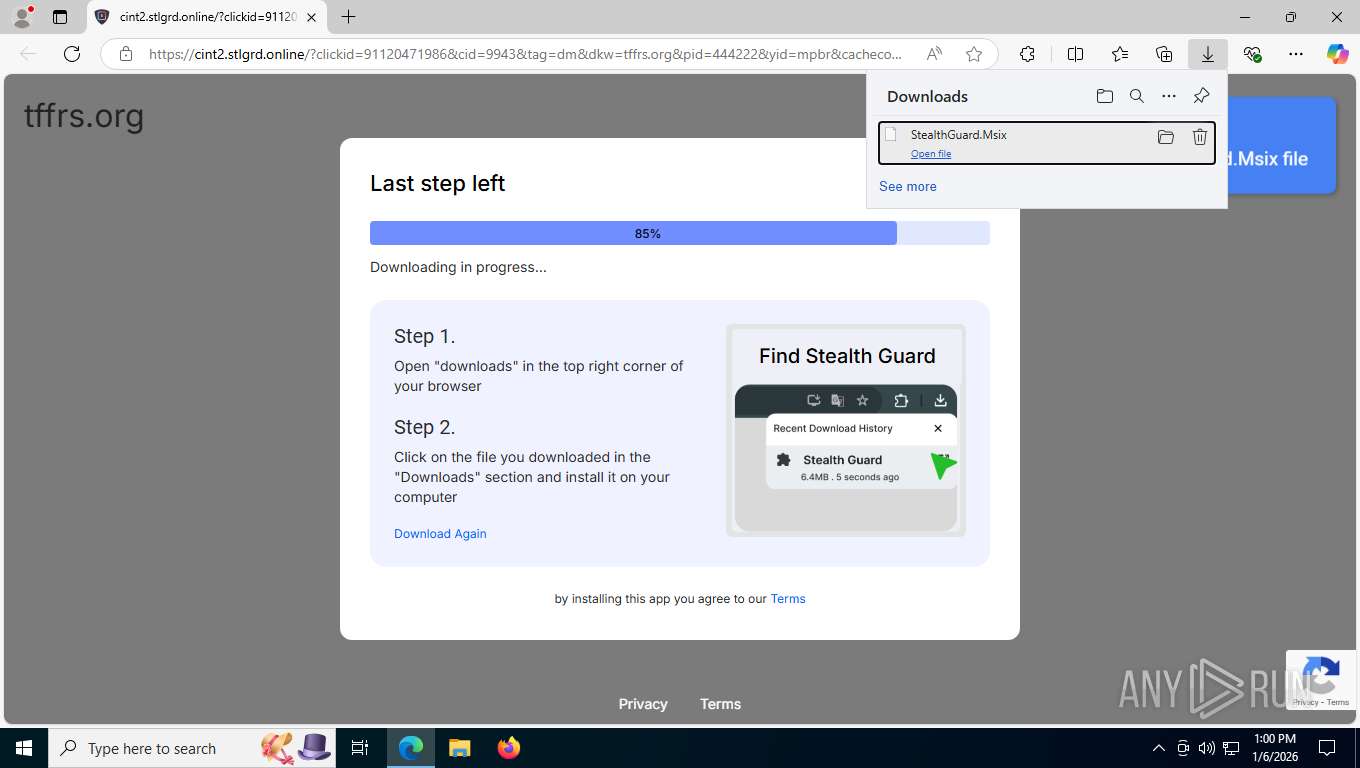
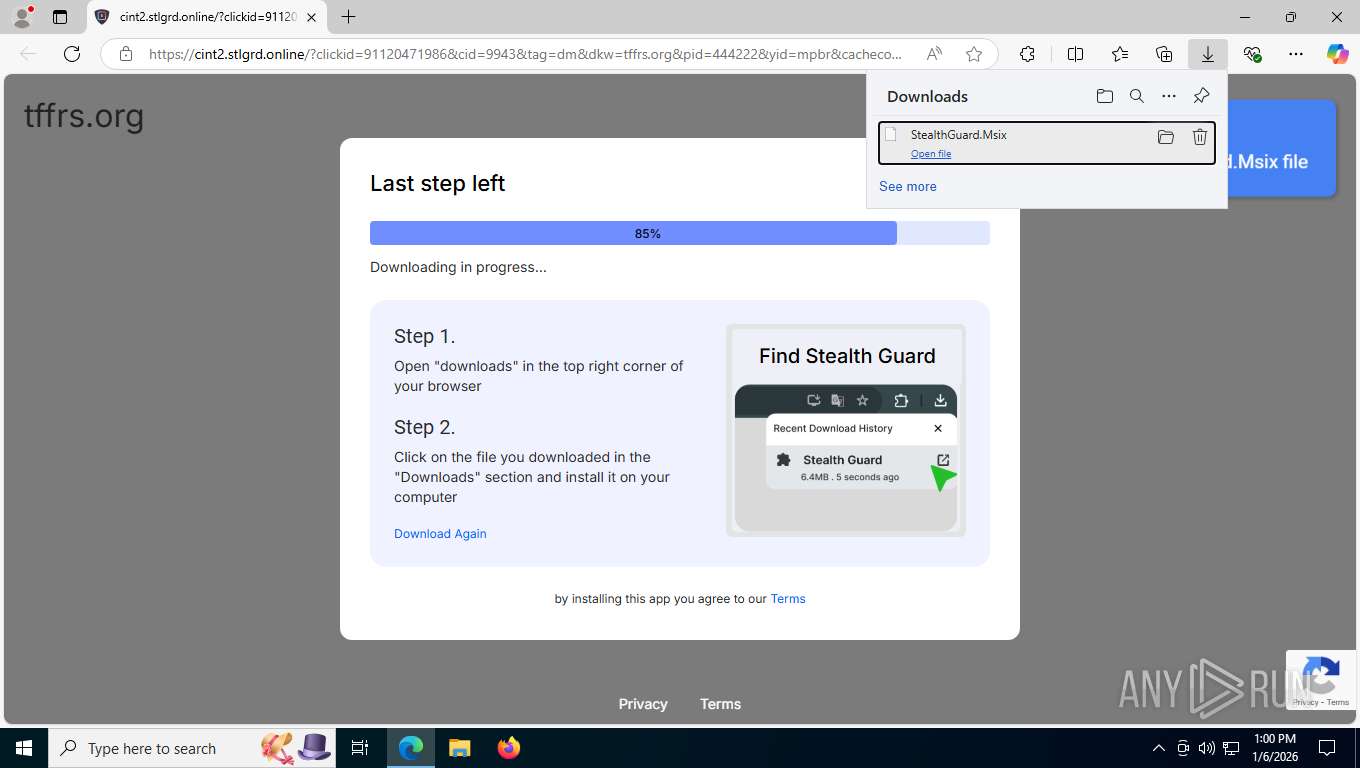
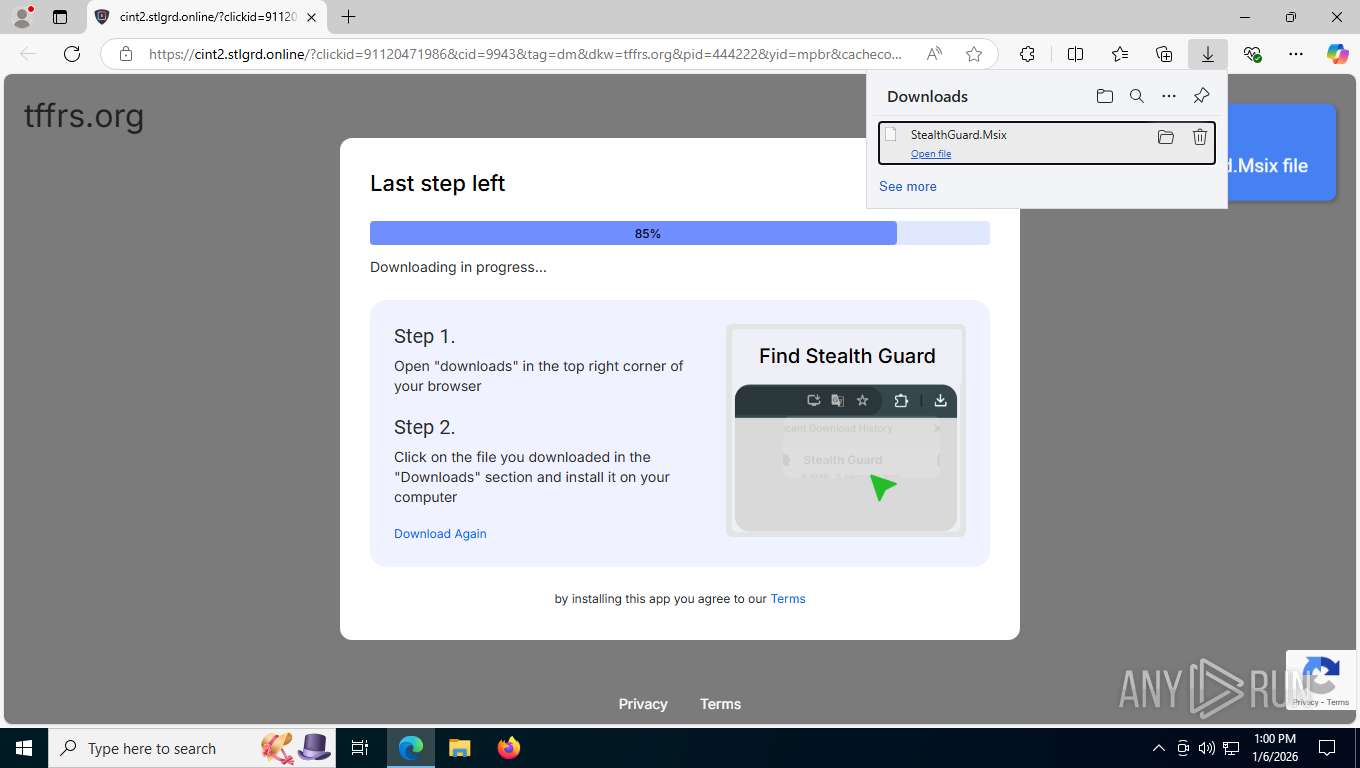
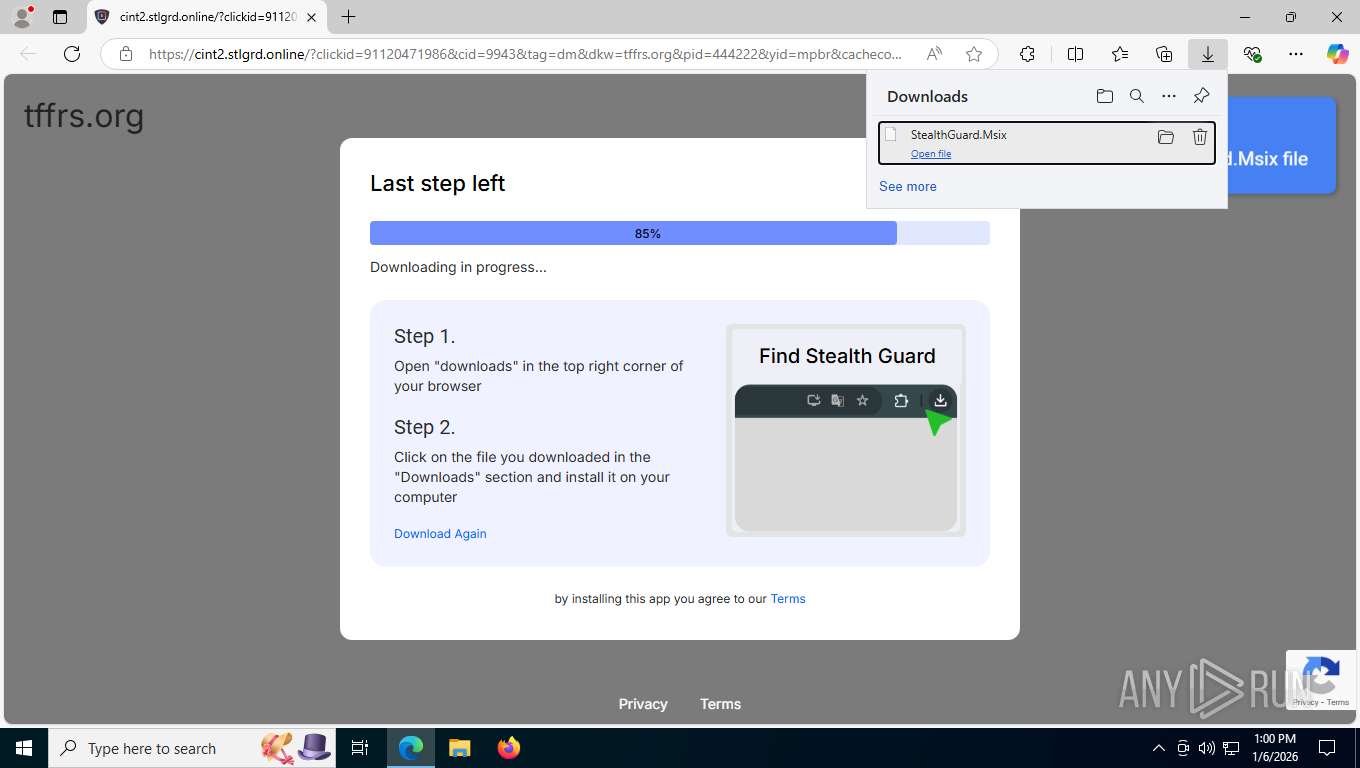
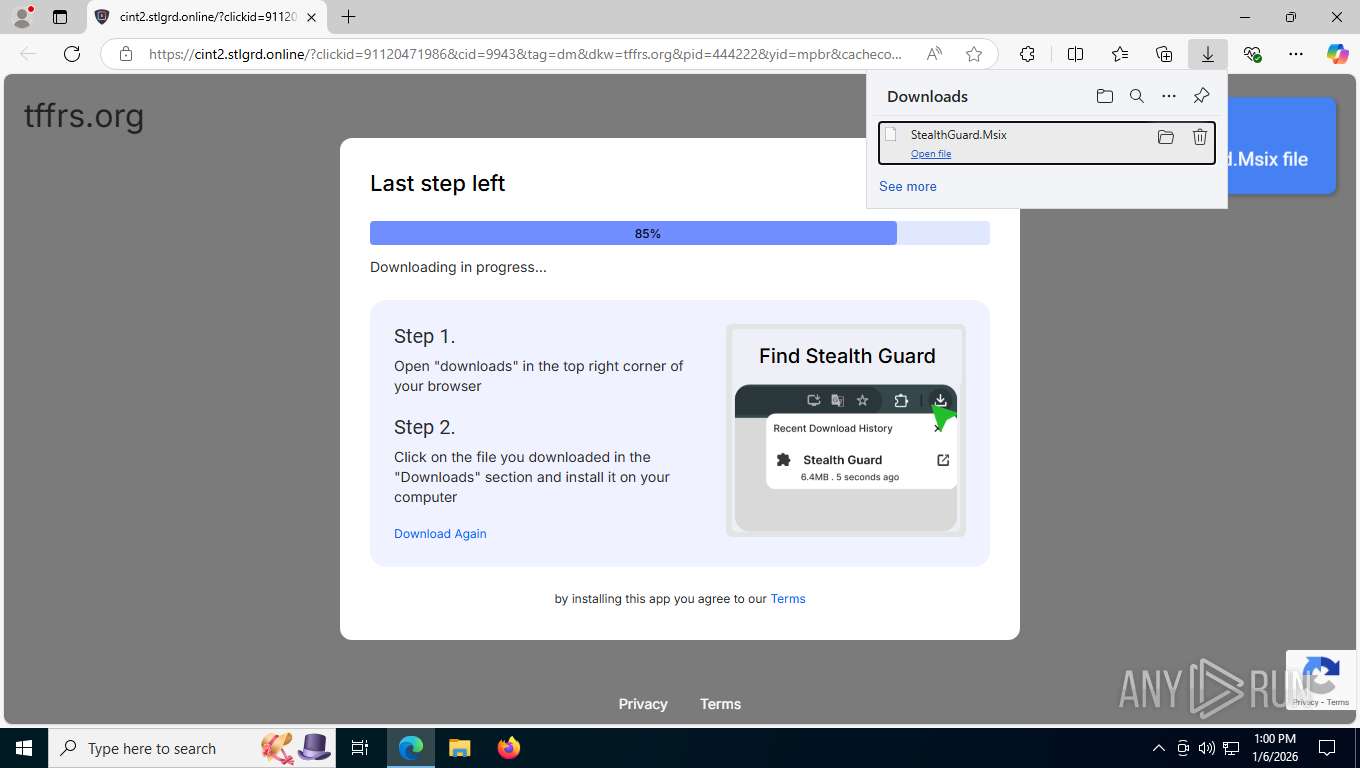
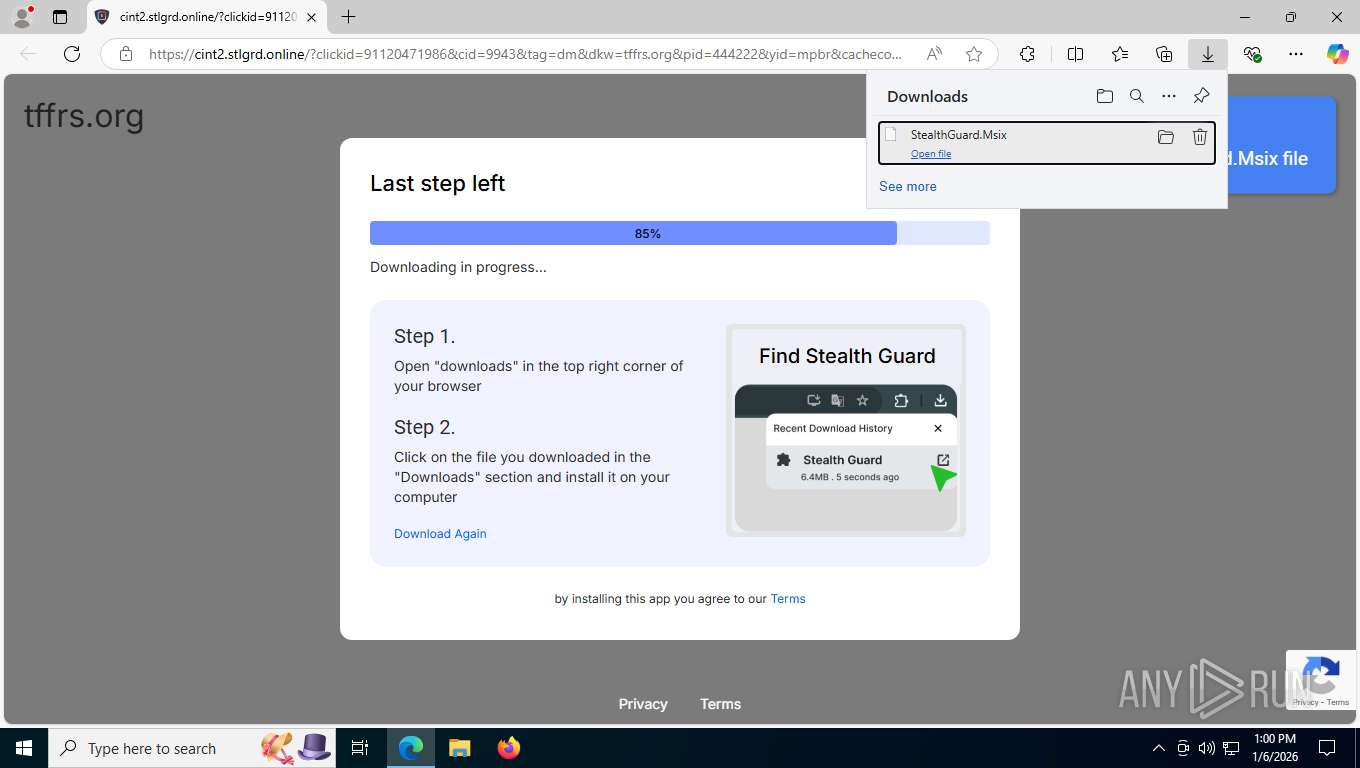
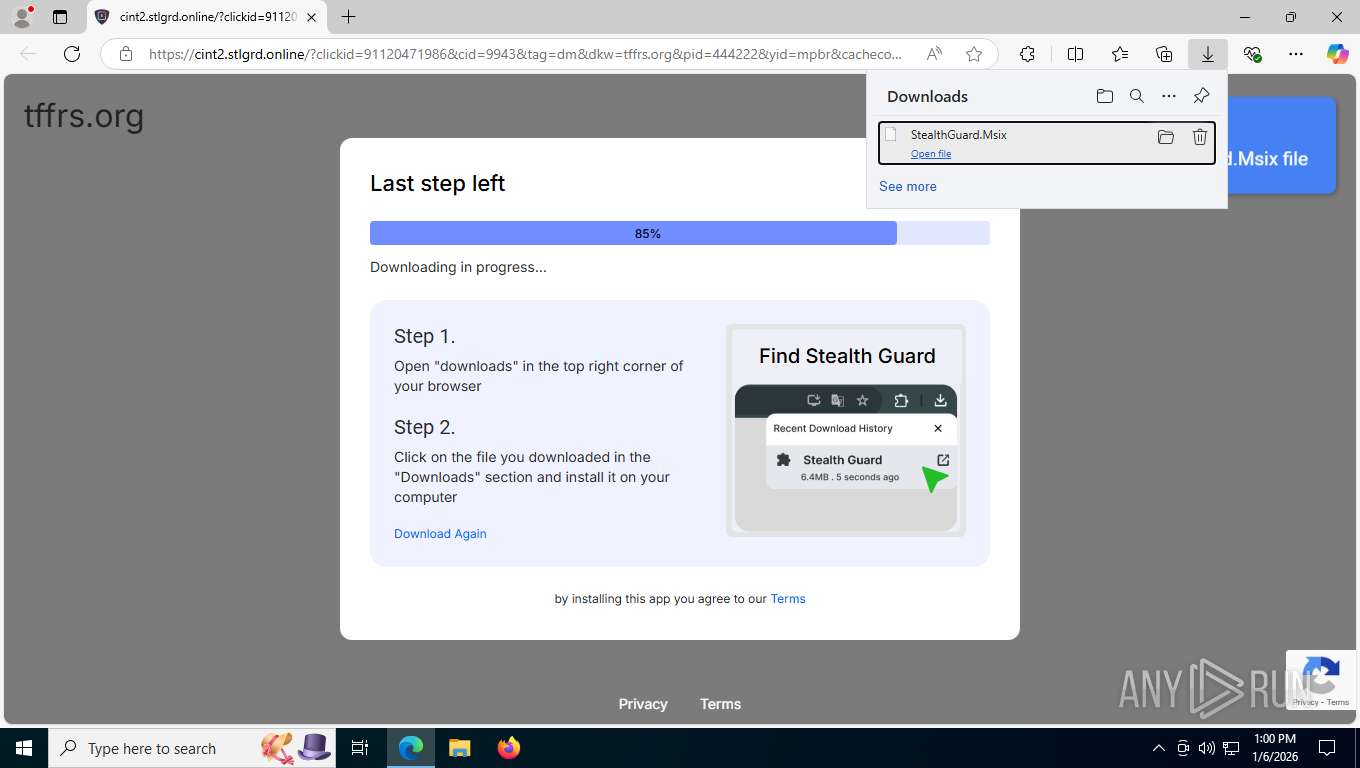
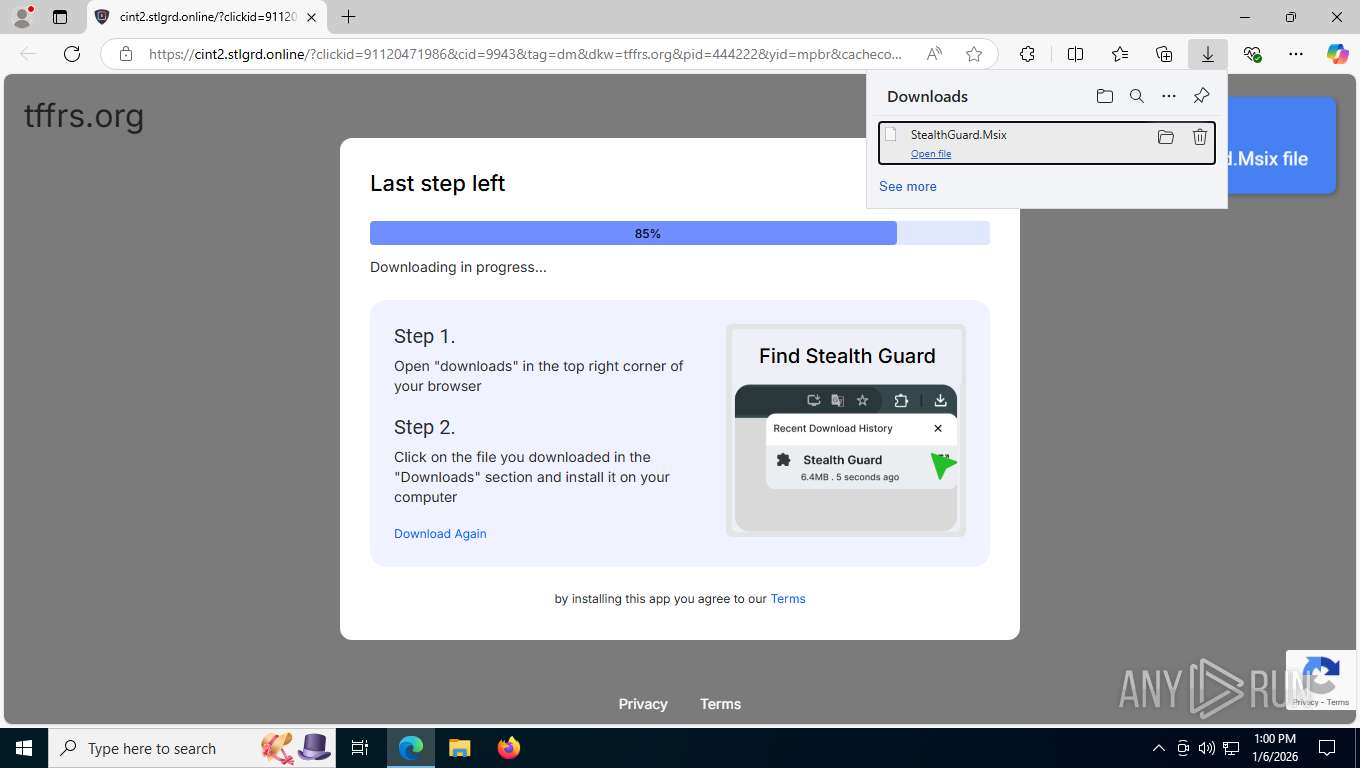
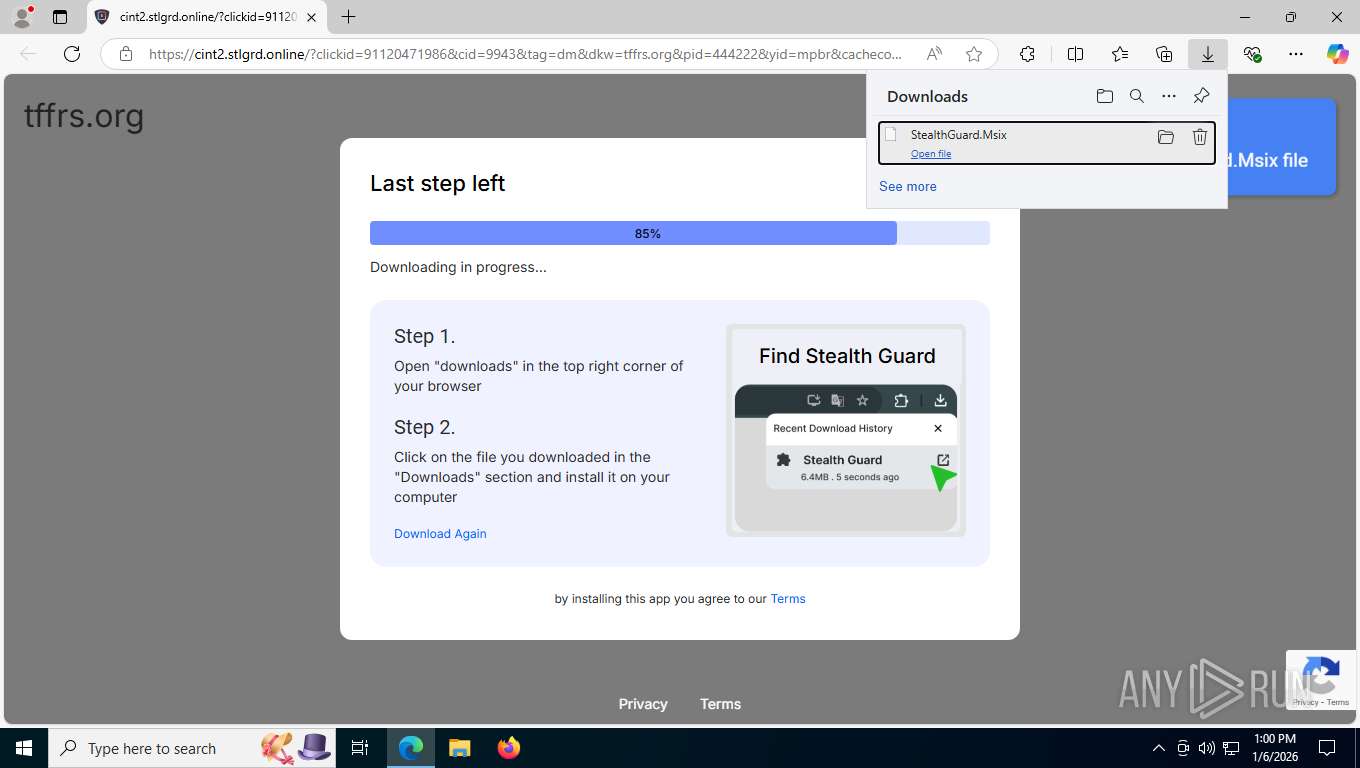
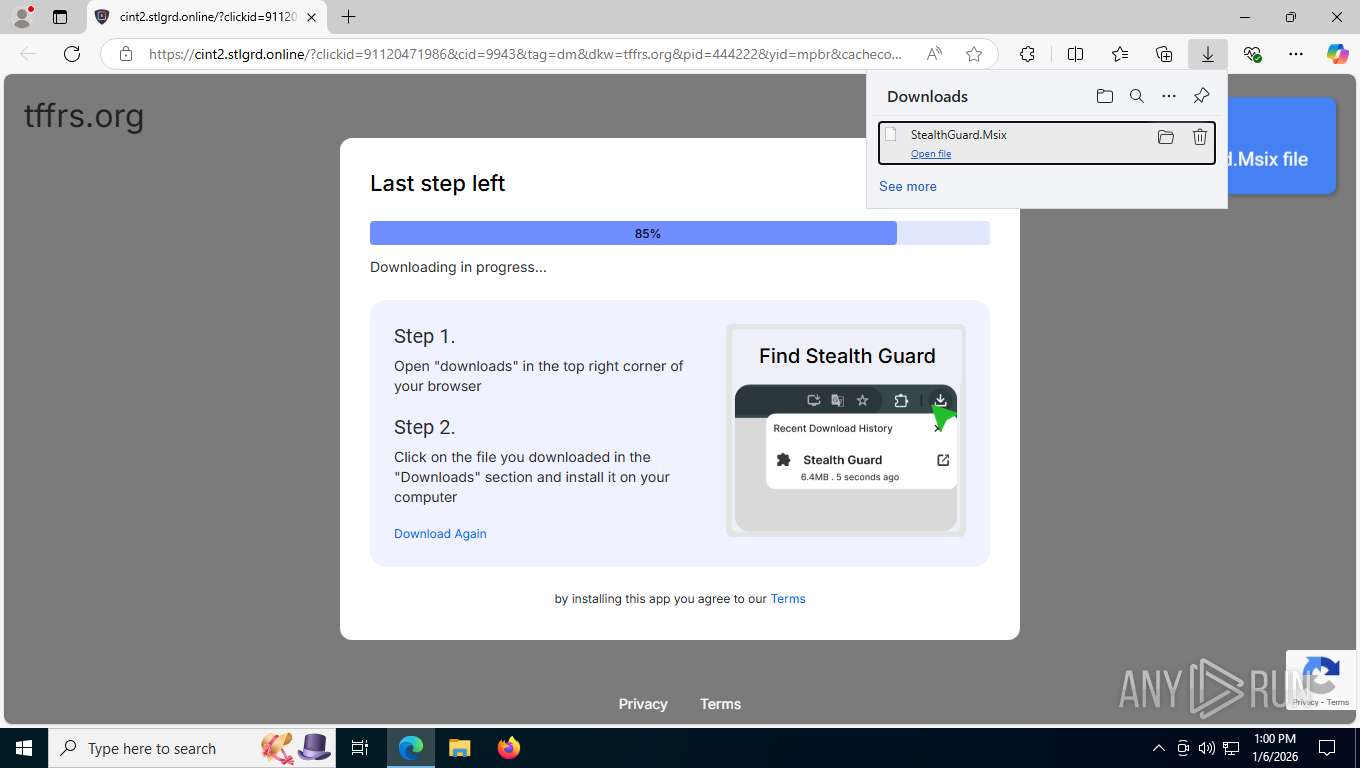
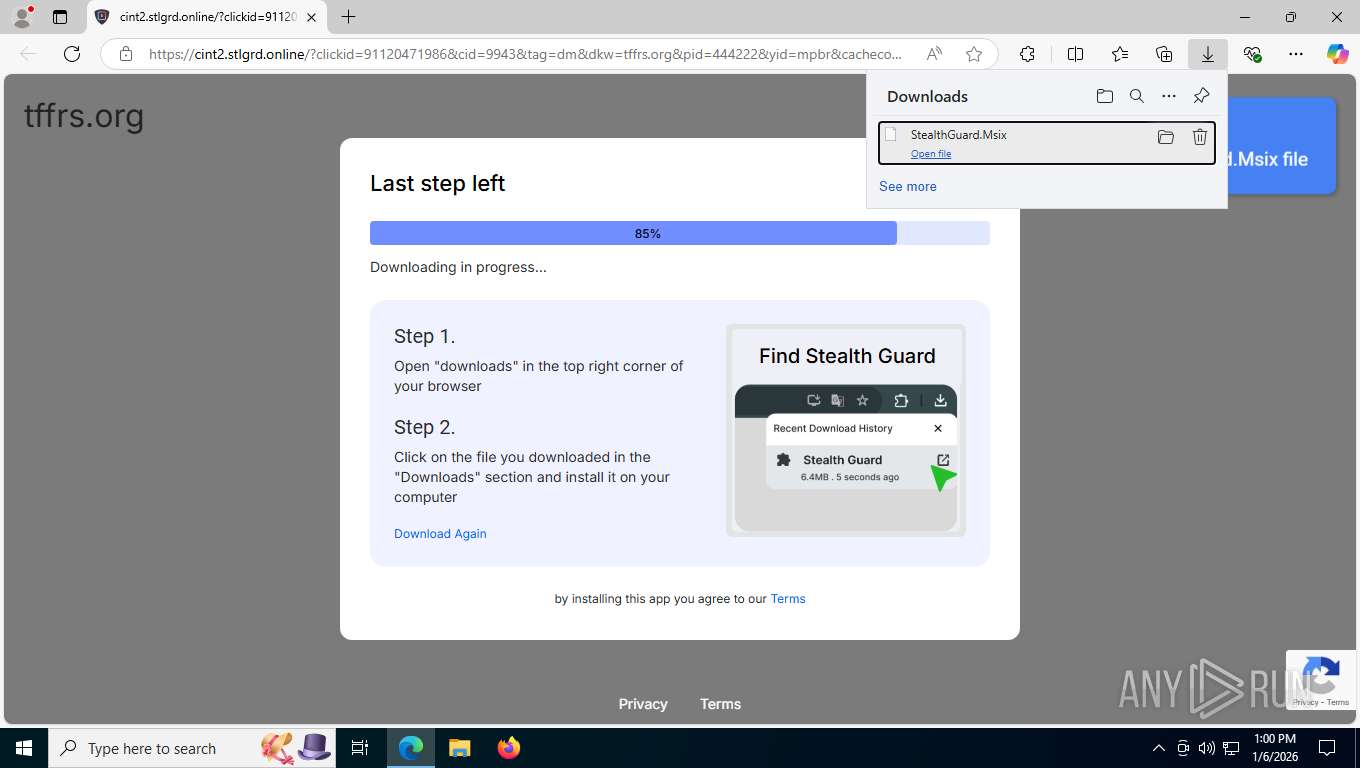
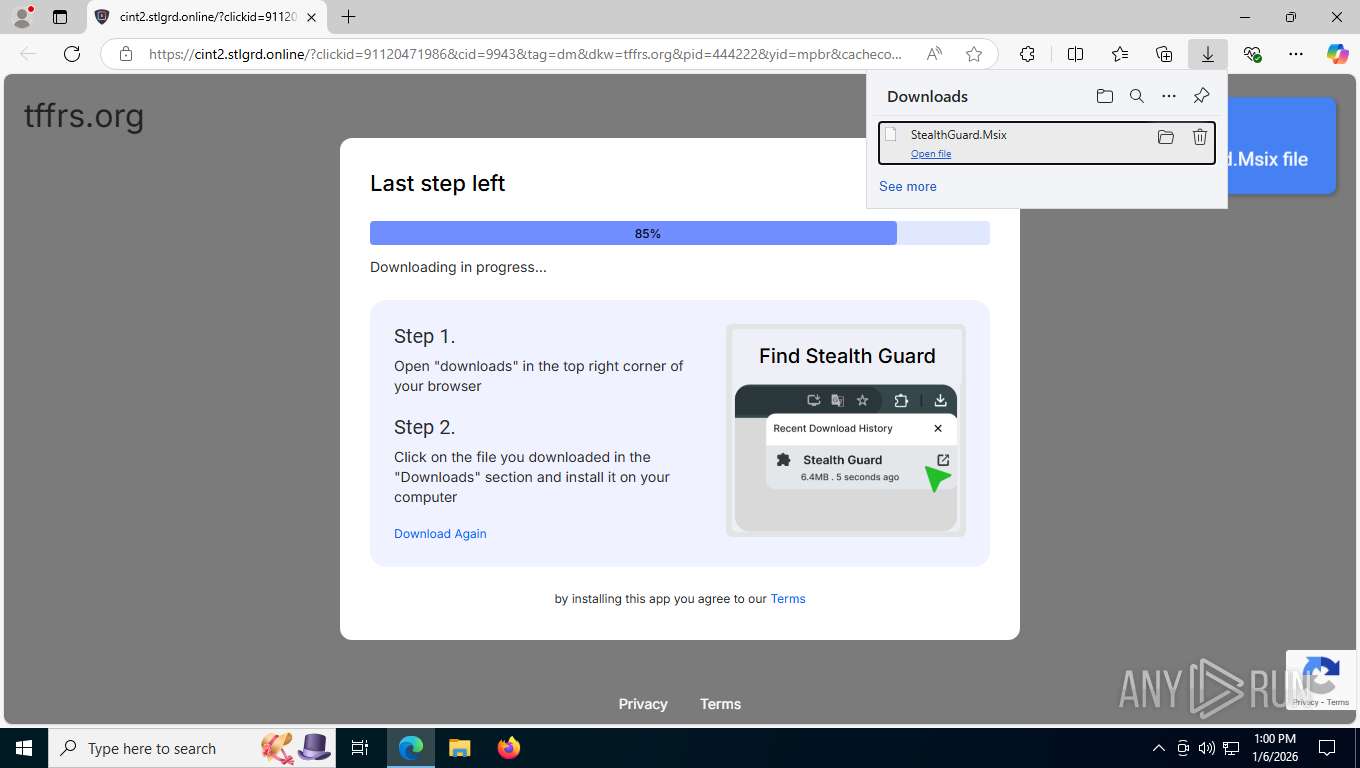
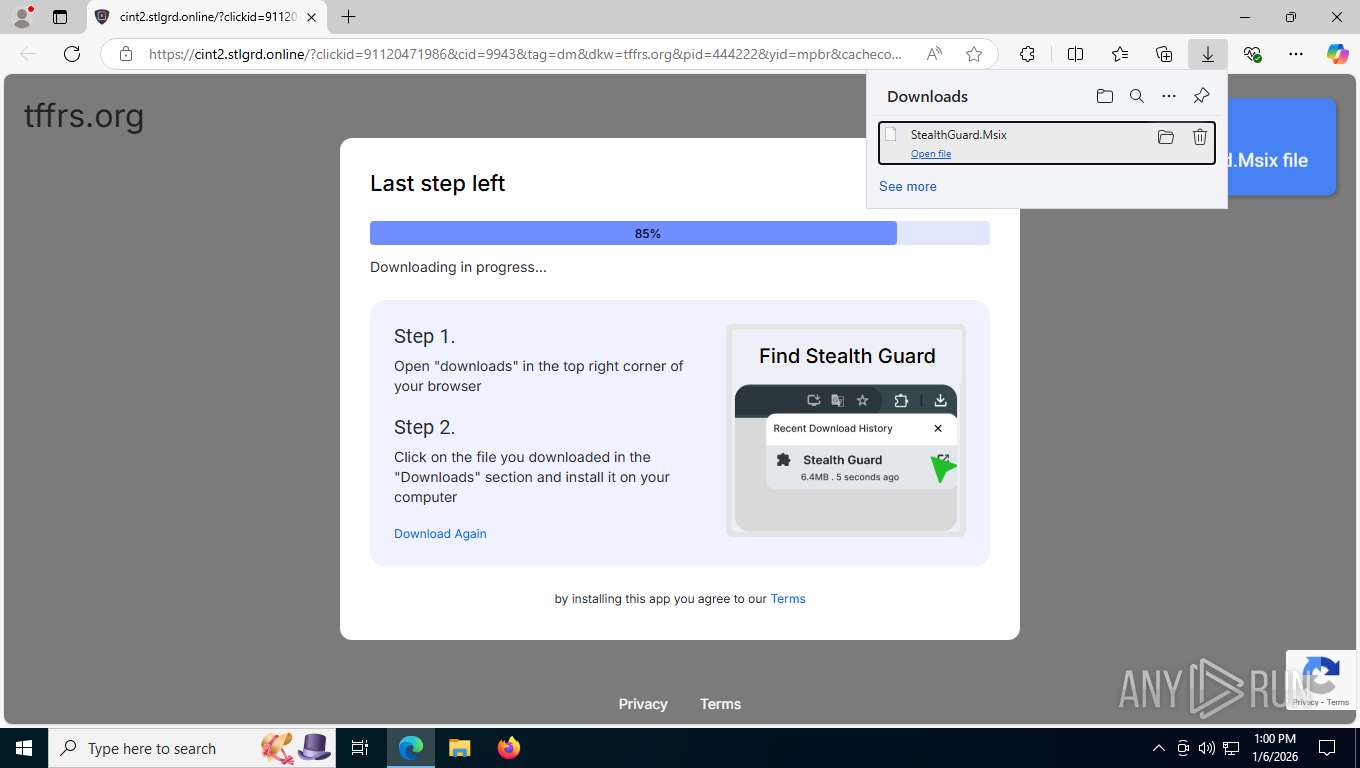
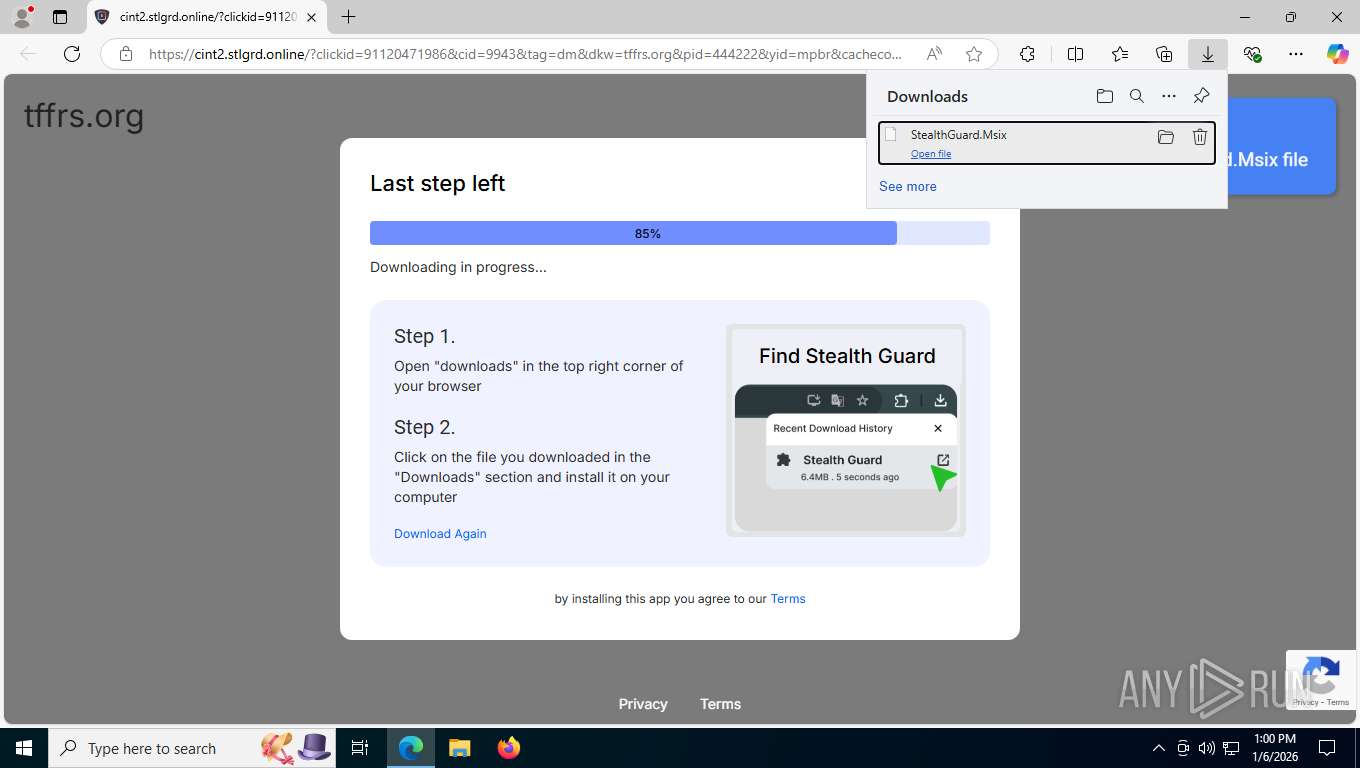
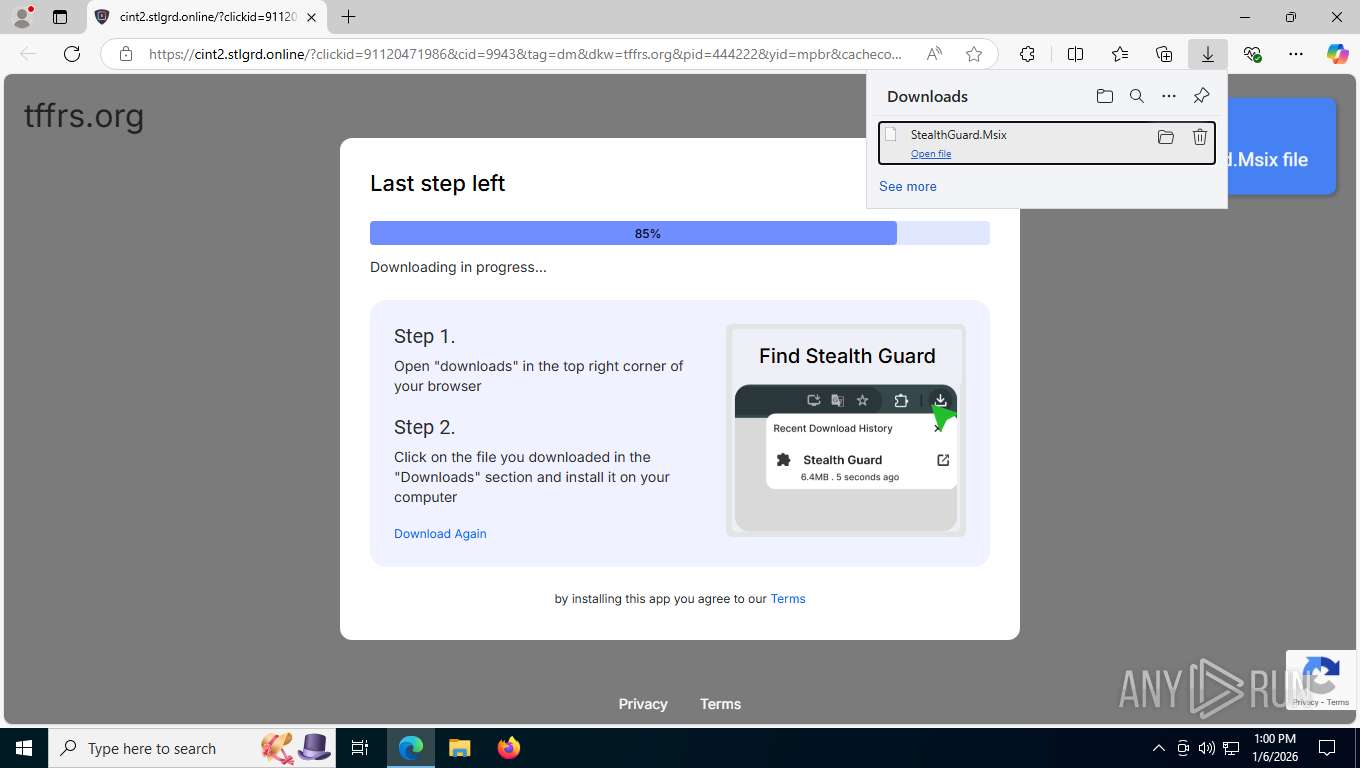
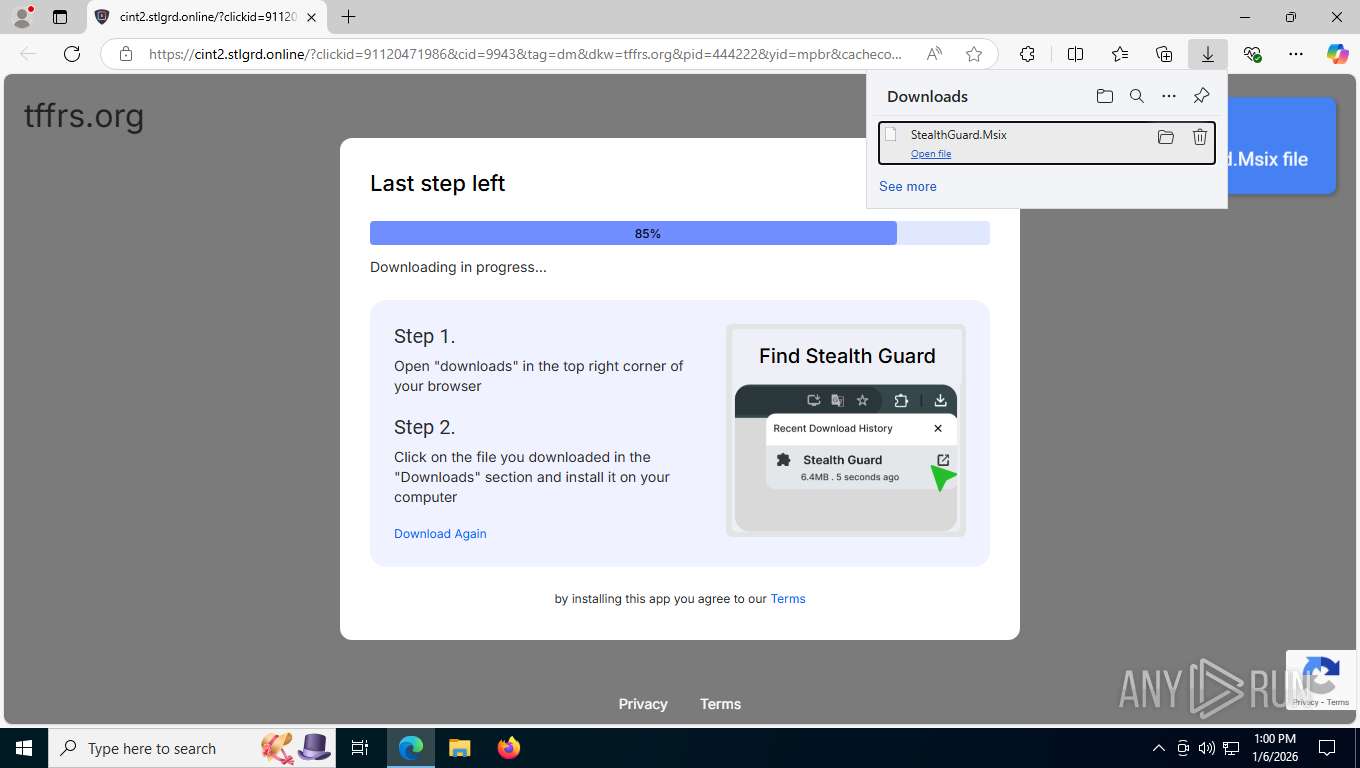
| URL: | https://cint2.stlgrd.online/?clickid=91120471986&cid=9943&tag=dm&dkw=tffrs.org&pid=444222&yid=mpbr&cachecode=mNZded5Ps9Sg%2BsevvWfzUA%3D%3D&rhi=b2747df0-772a-4f00-ad31-3e6f2a26c3cb |
| Full analysis: | https://app.any.run/tasks/4ef9612c-ca40-4b07-b018-bf4234c0b5b8 |
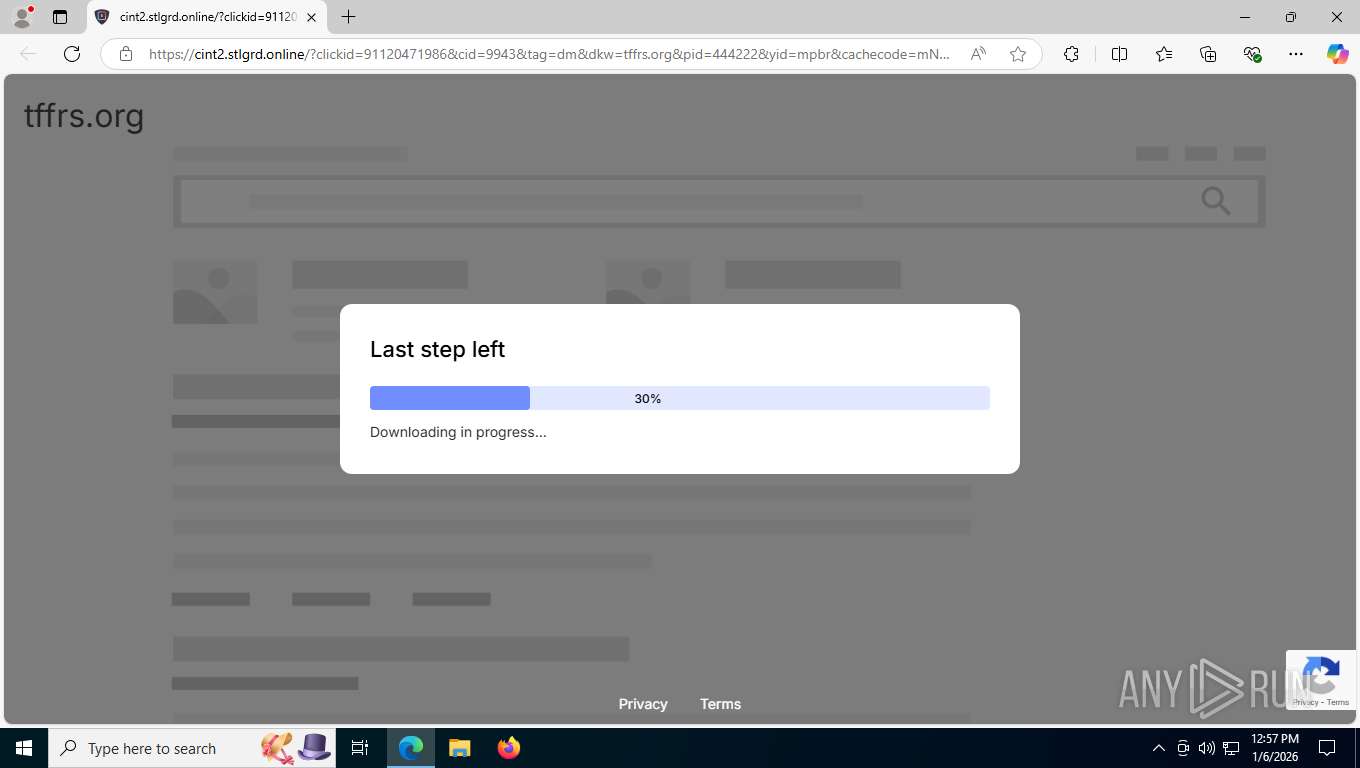
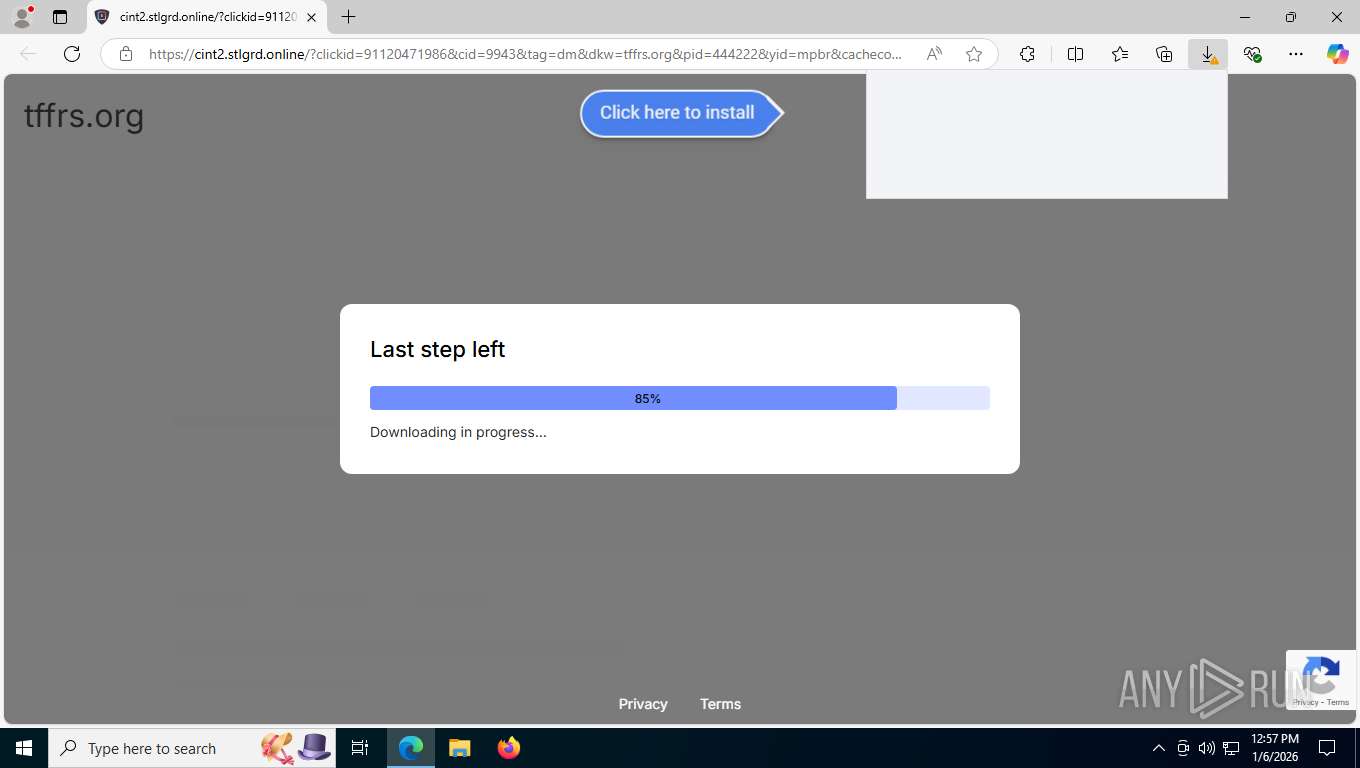
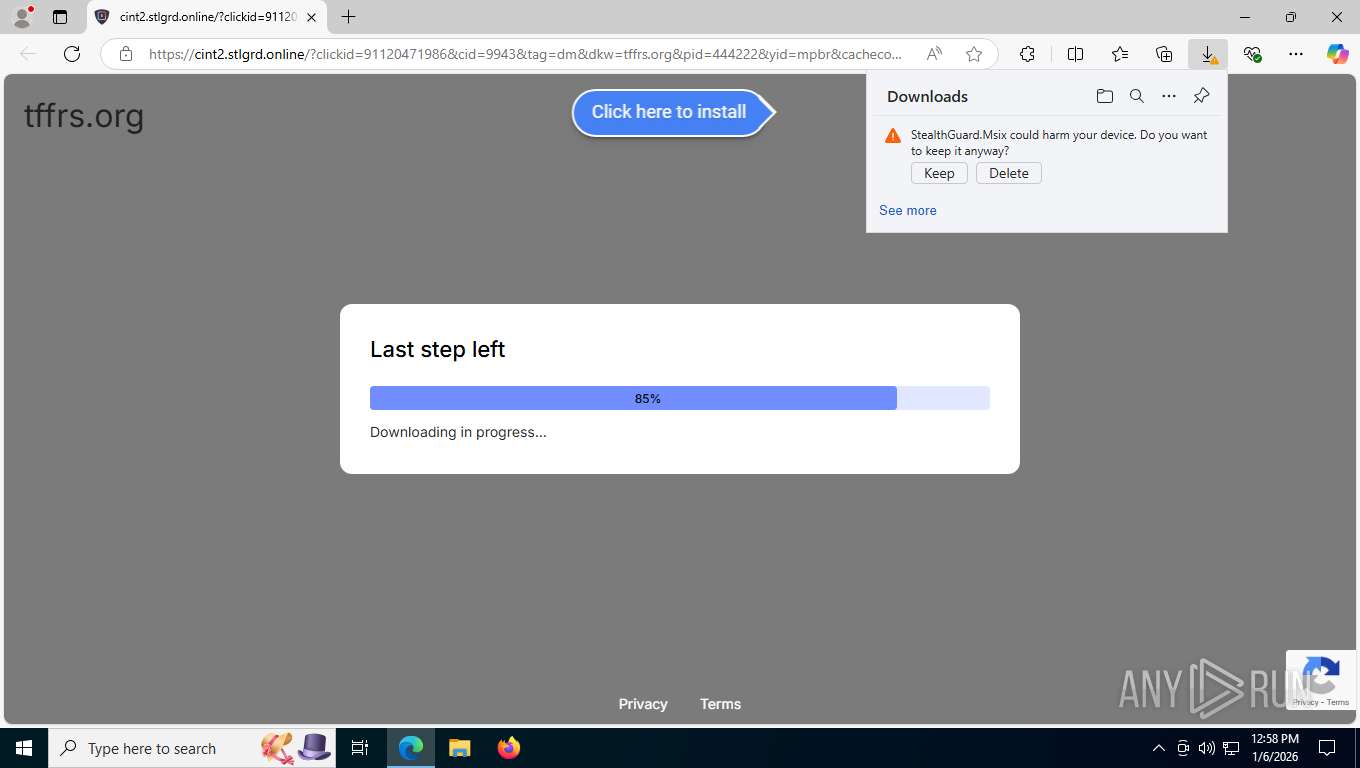
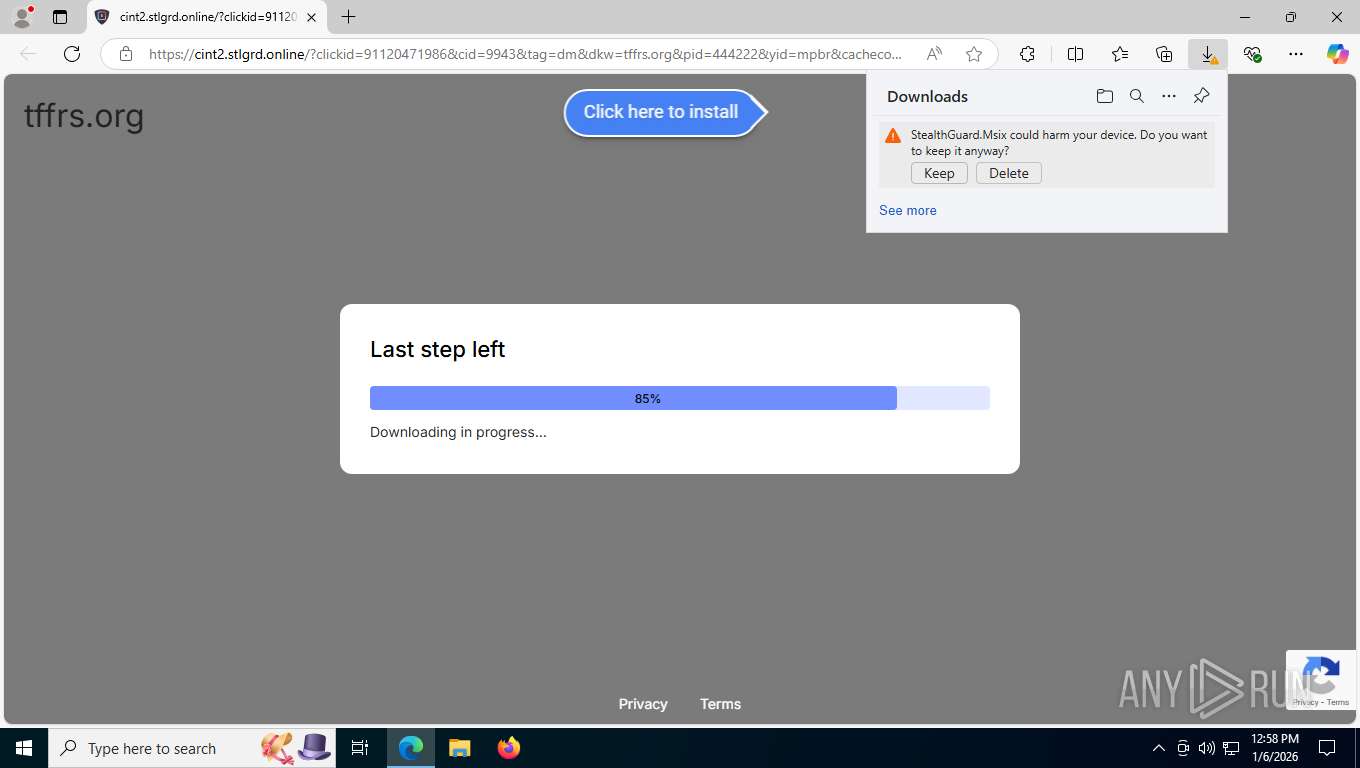
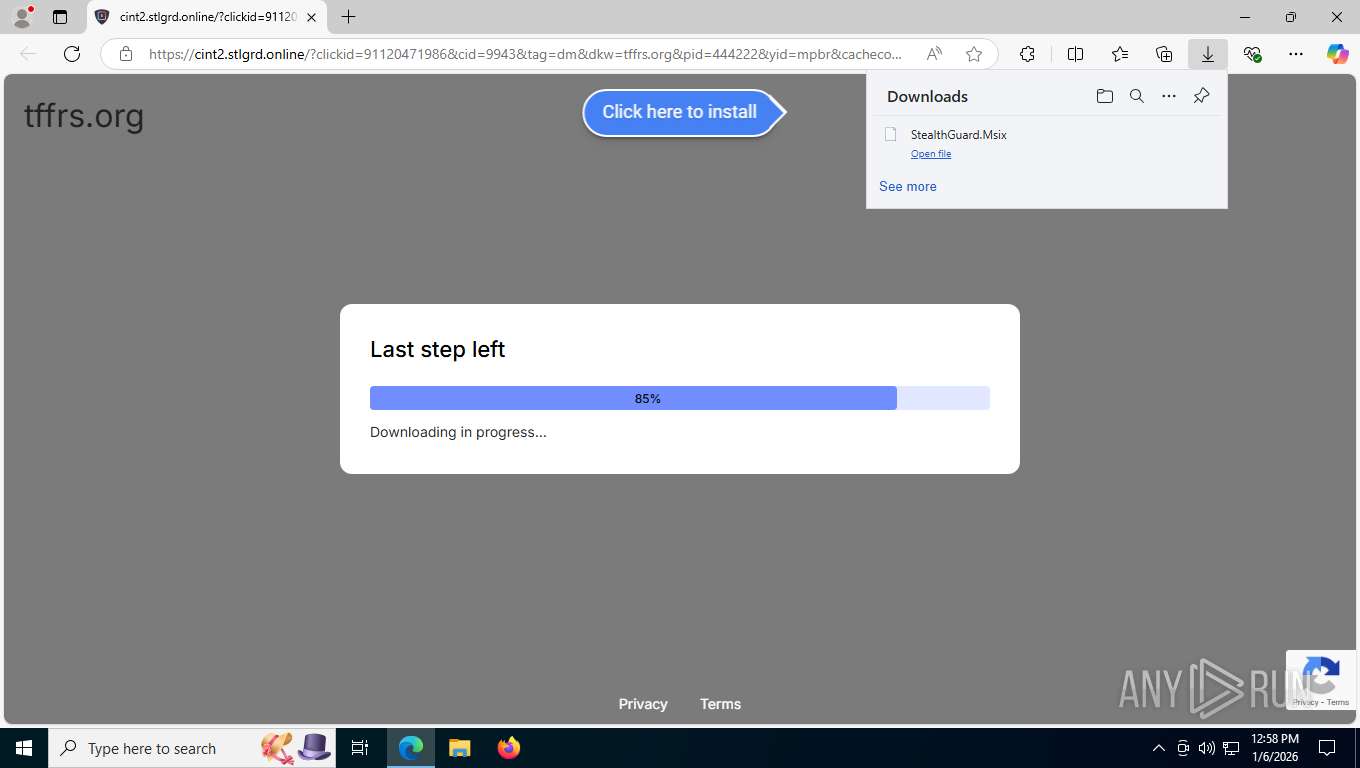
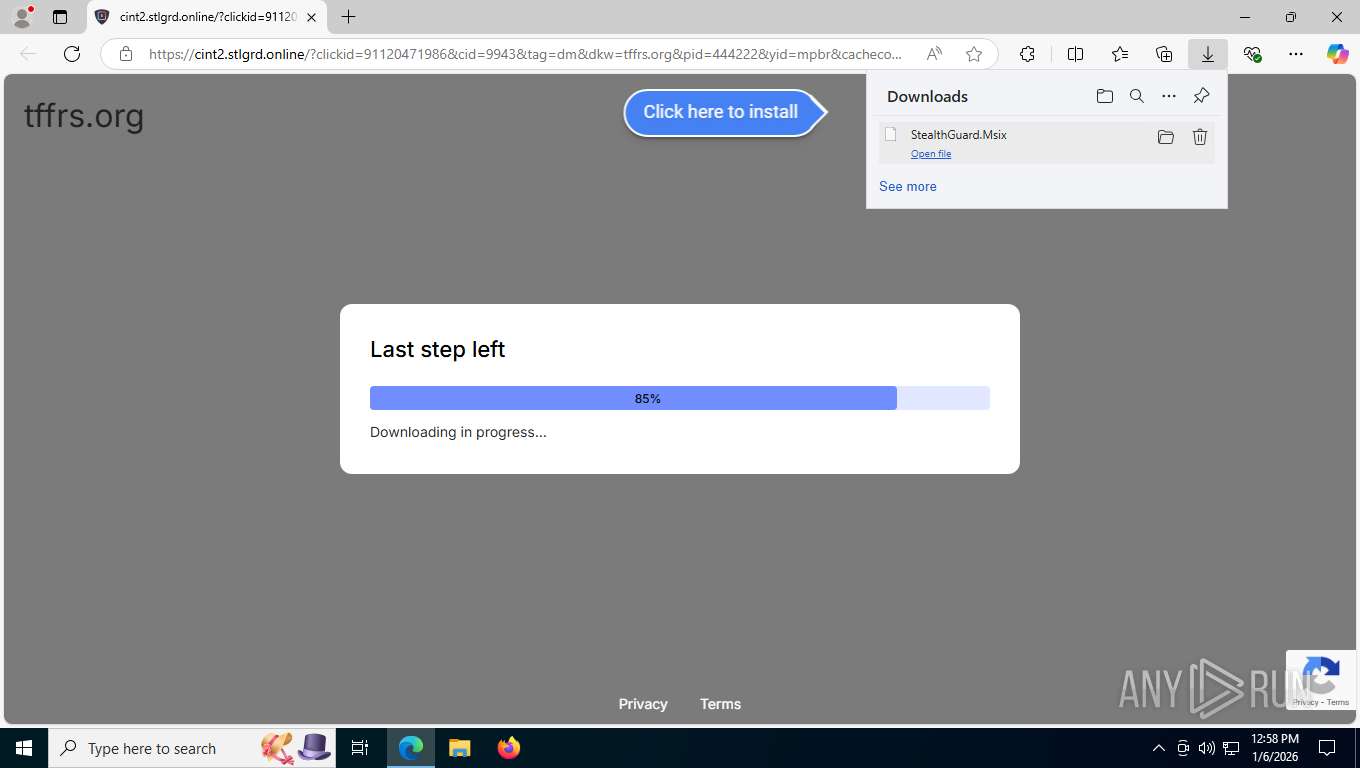
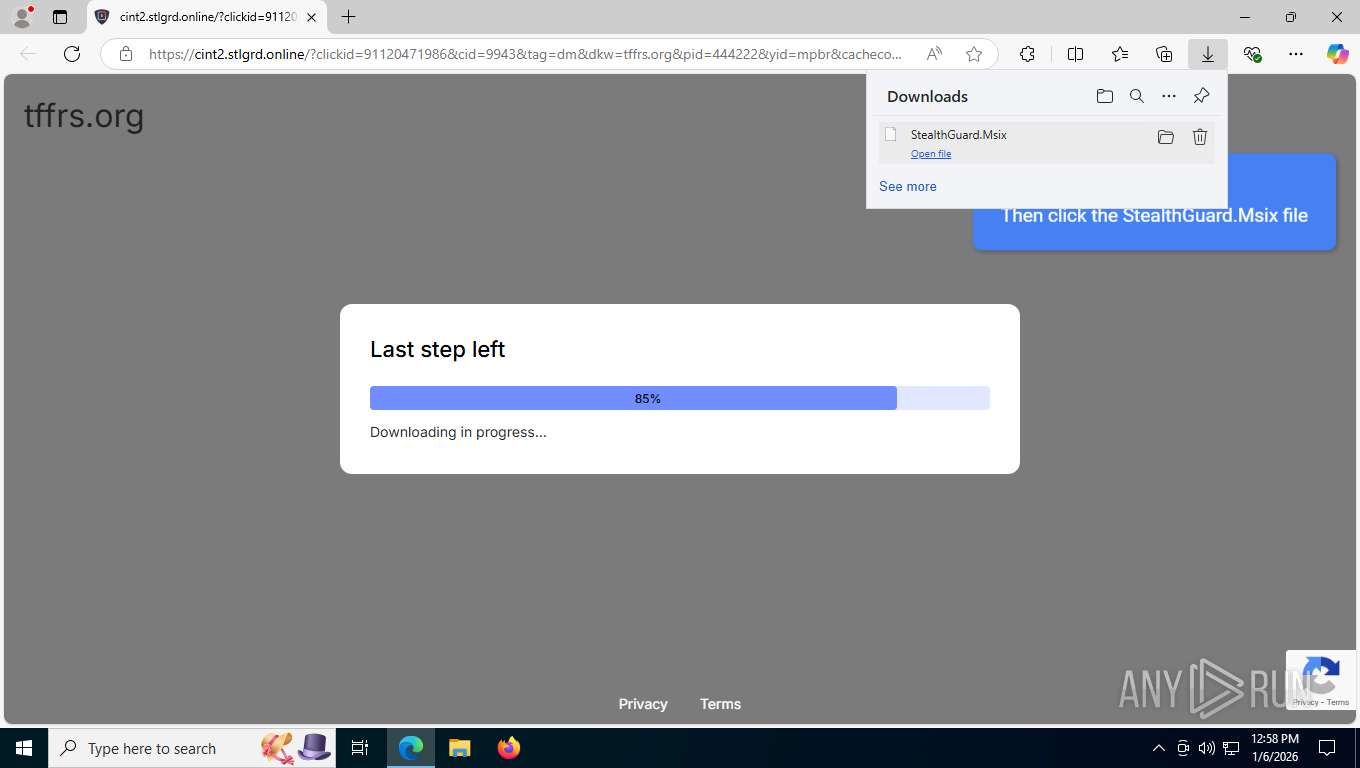
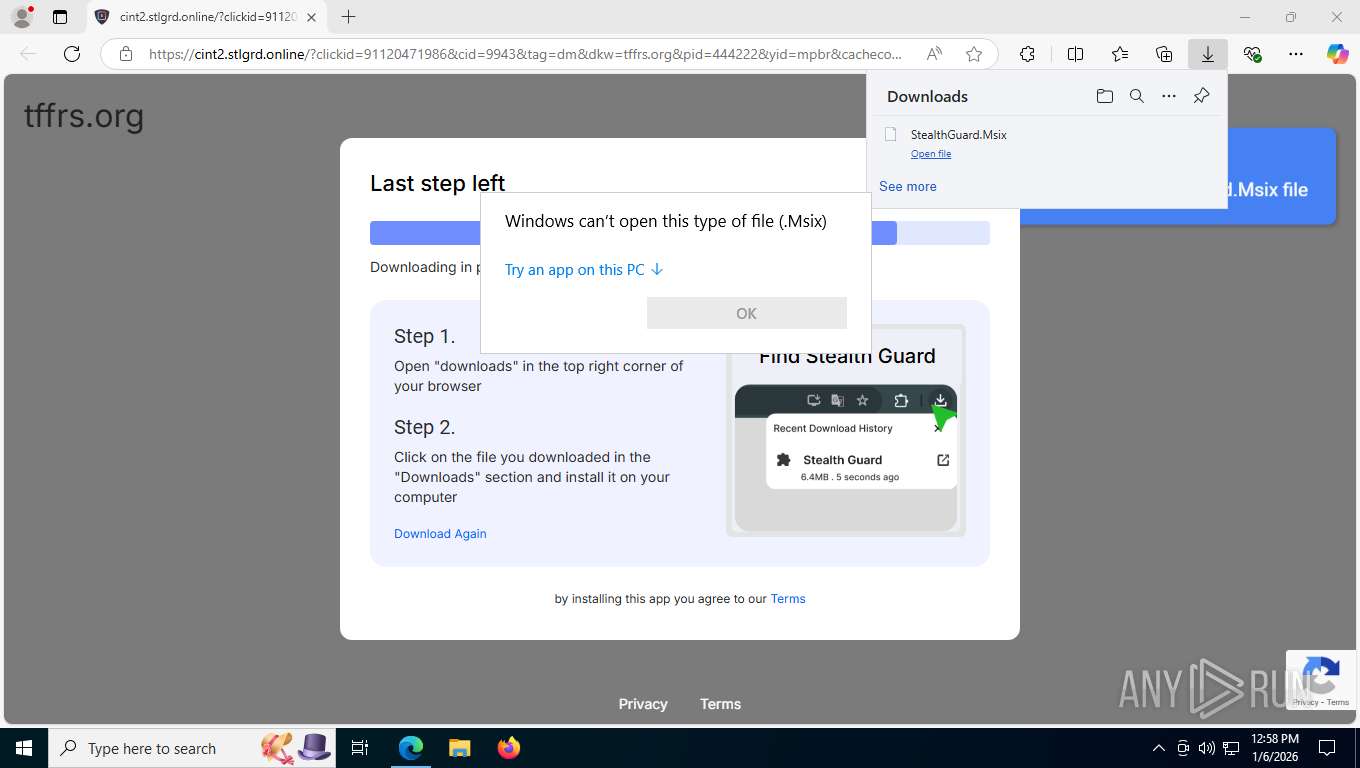
| Verdict: | Malicious activity |
| Analysis date: | January 06, 2026, 17:57:26 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D77C2C2D69BC1DC6461BD4A91EEF0B62 |
| SHA1: | A61C60F8528ADE523708C833CAC2AE6F39C1E7CA |
| SHA256: | 3DD3E01C5E6239B0D3C0880240649B428184CD643FF288EE597E734E3078C79F |
| SSDEEP: | 3:N8RLd0JM0BKjBYcNrS+MBYtBIDwlDG+SbxAyG7UrzMA3WhDdMY3S0fISkhlVVIoy:2j8HBa8wlXSp8Ur93CJmSoVfIT1 |
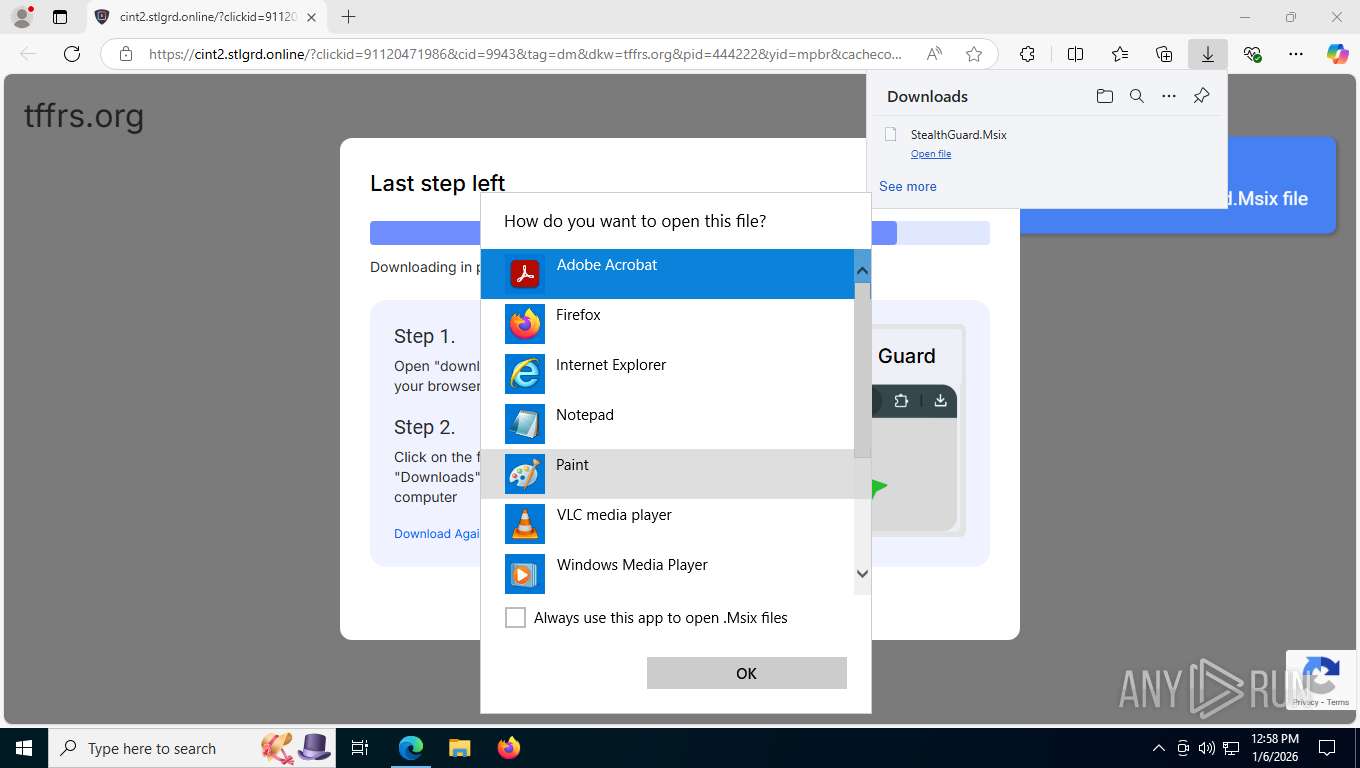
MALICIOUS
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 7908)
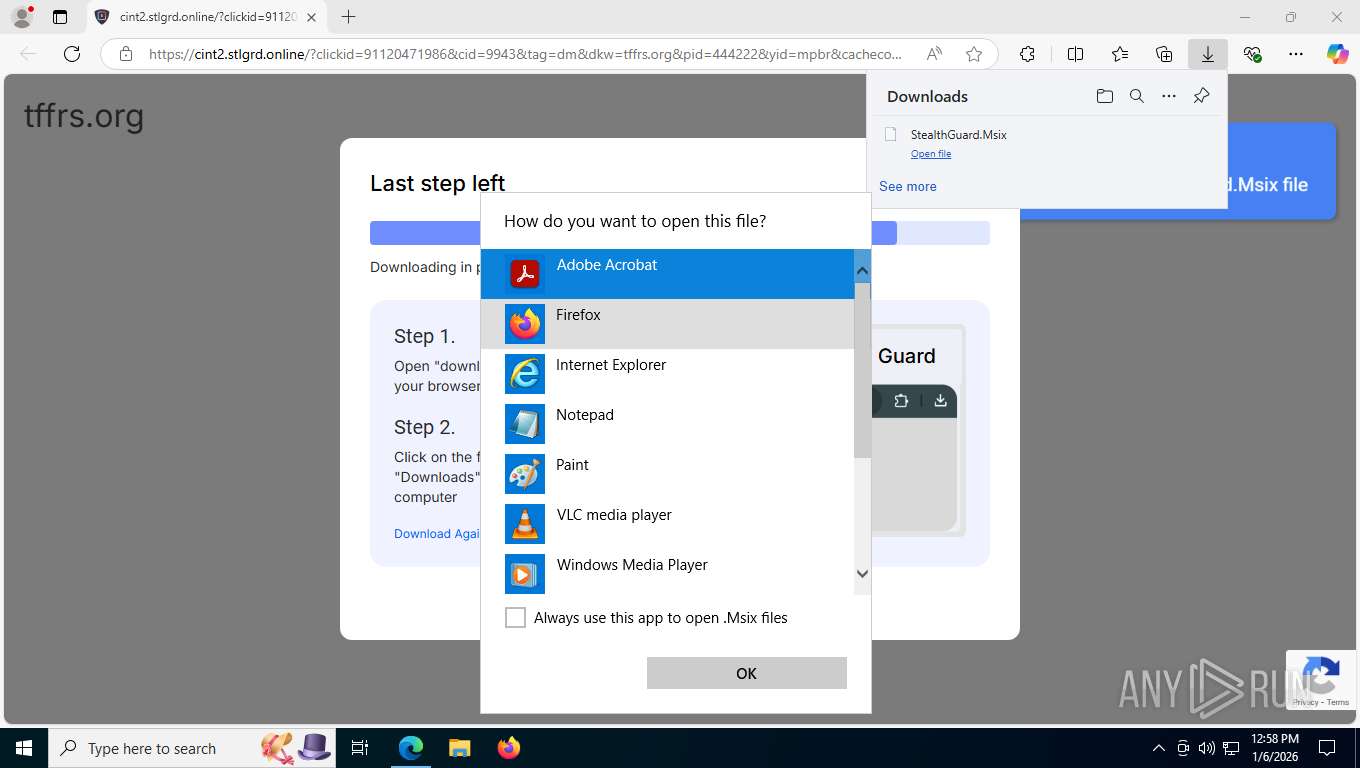
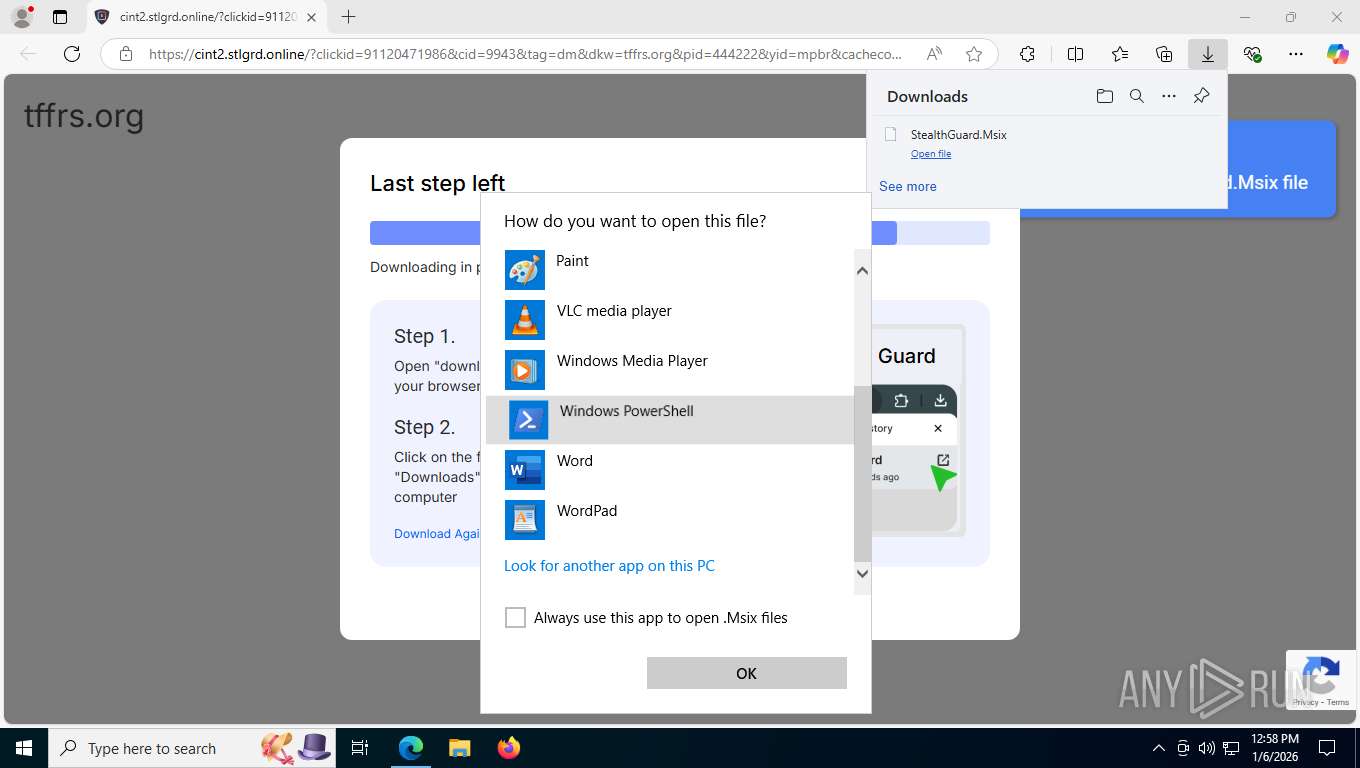
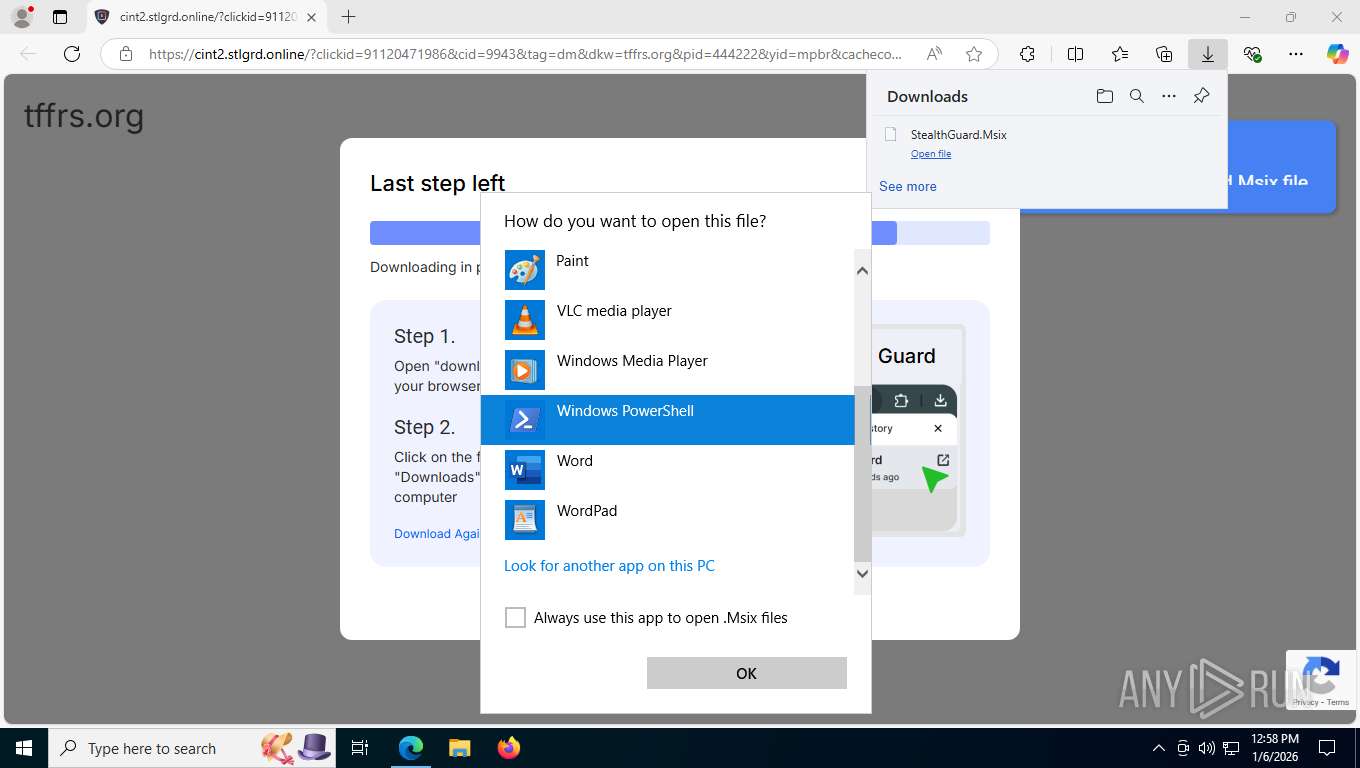
SUSPICIOUS
Application launched itself
- powershell.exe (PID: 2364)
- powershell.exe (PID: 9164)
- powershell.exe (PID: 2348)
- powershell.exe (PID: 7268)
- powershell.exe (PID: 7280)
- powershell.exe (PID: 2196)
- powershell.exe (PID: 7956)
- powershell.exe (PID: 8892)
- powershell.exe (PID: 4504)
- powershell.exe (PID: 8904)
- powershell.exe (PID: 5696)
- powershell.exe (PID: 2752)
- powershell.exe (PID: 6792)
- powershell.exe (PID: 7392)
- powershell.exe (PID: 8216)
- powershell.exe (PID: 2688)
- powershell.exe (PID: 7208)
- powershell.exe (PID: 7228)
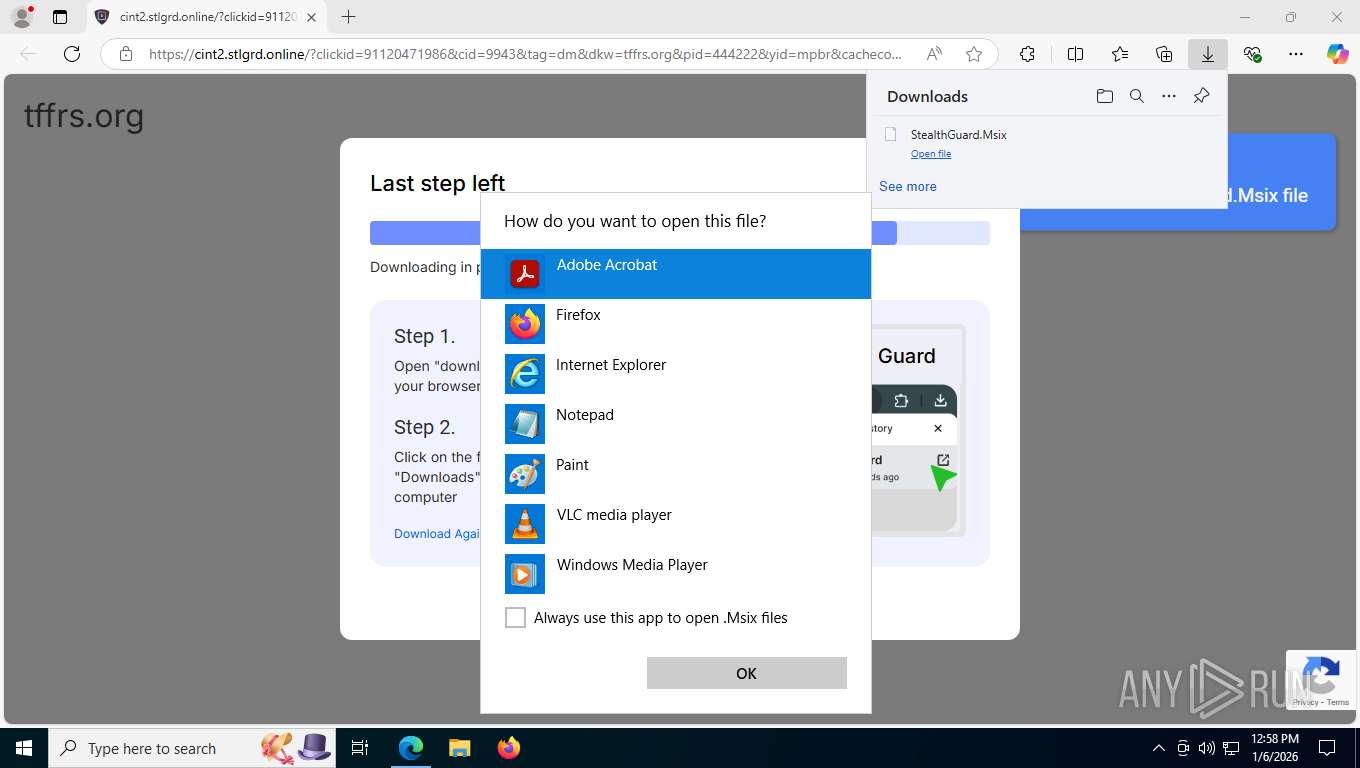
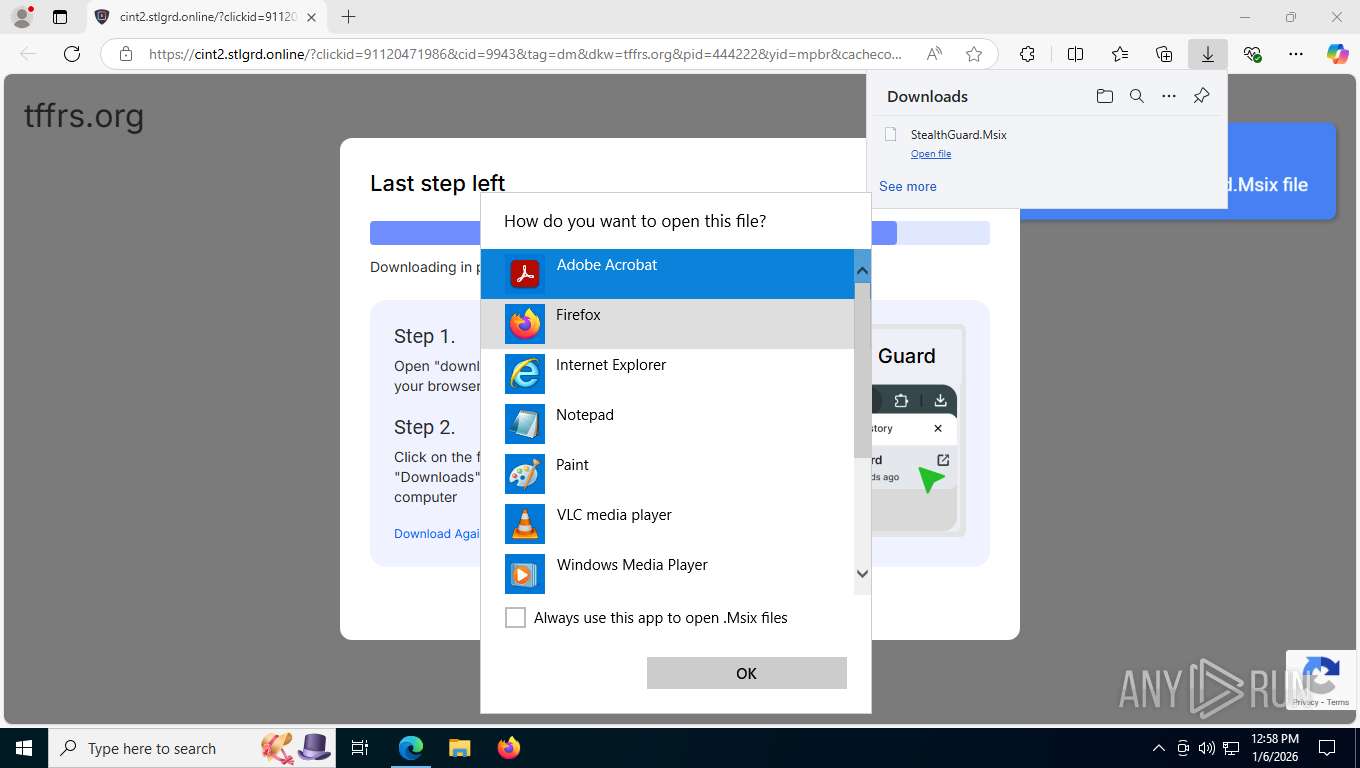
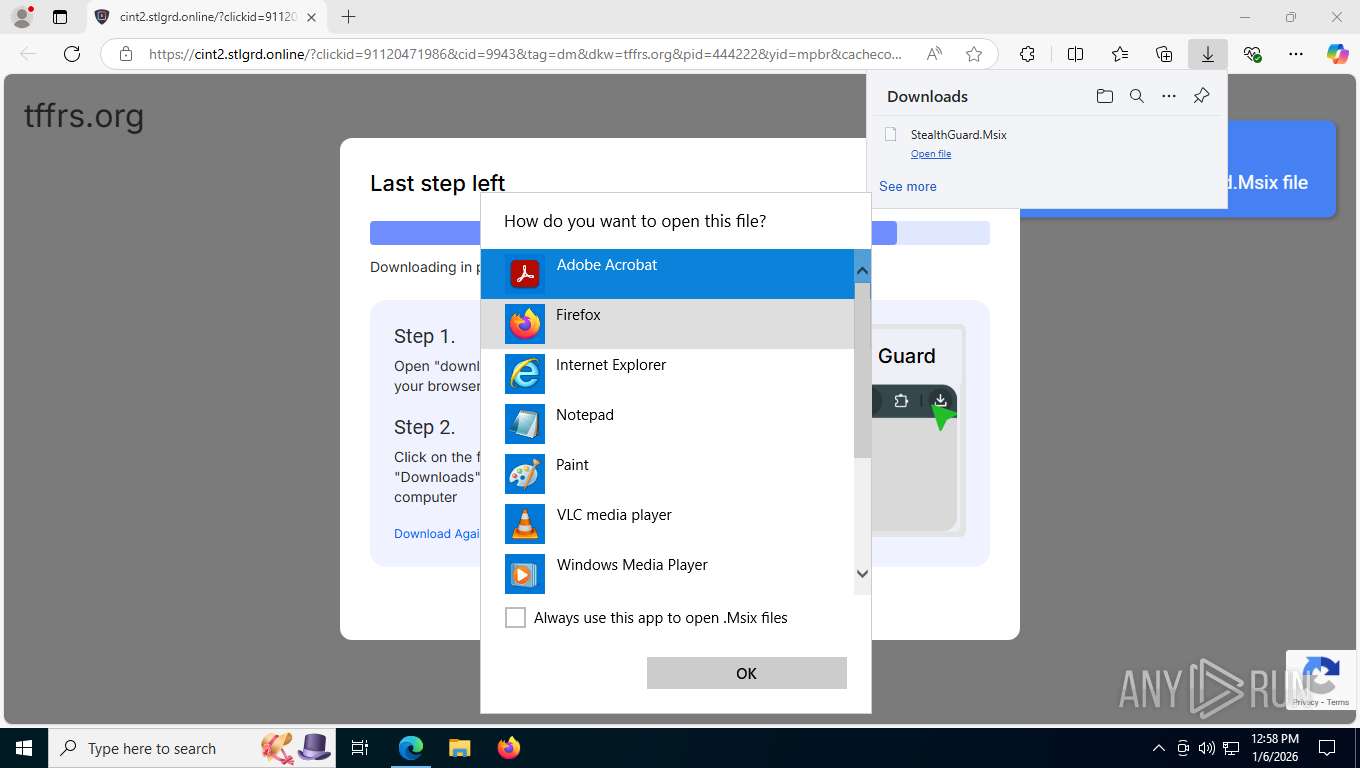
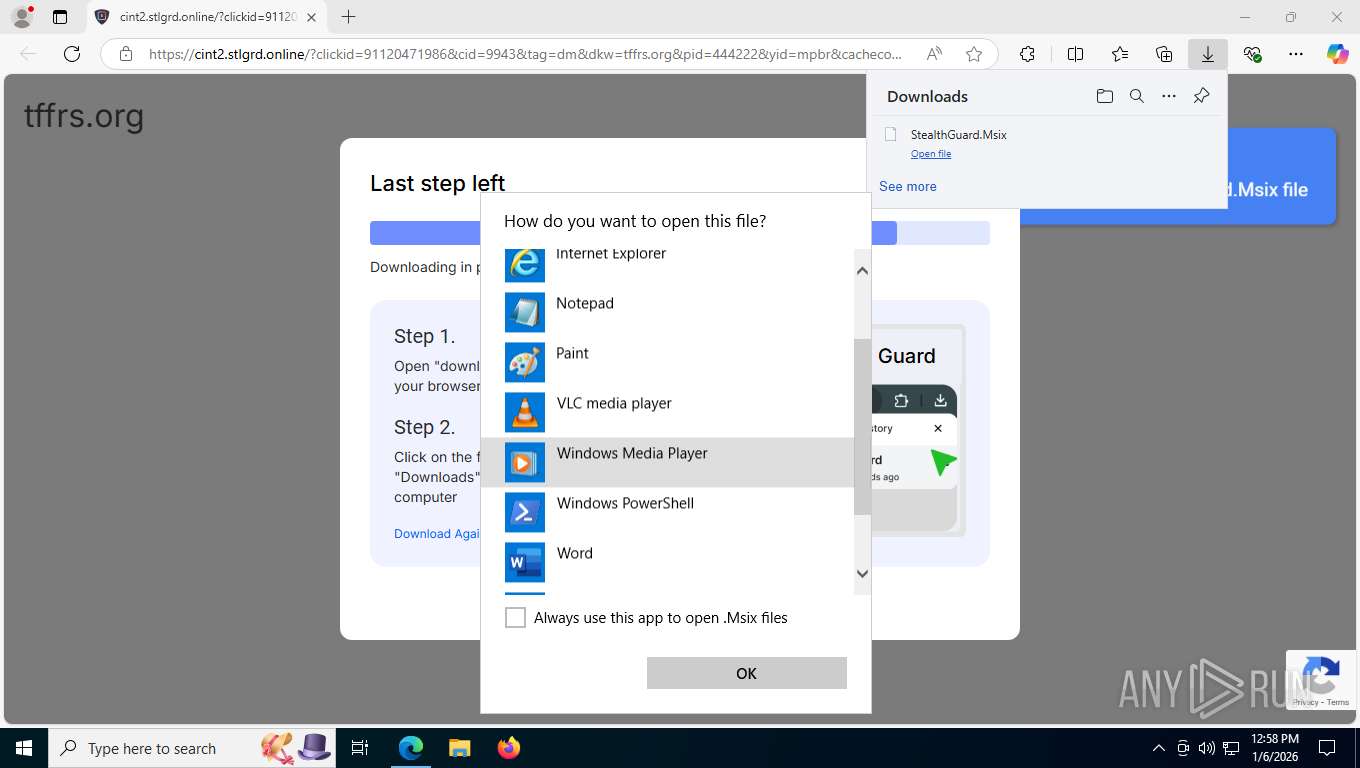
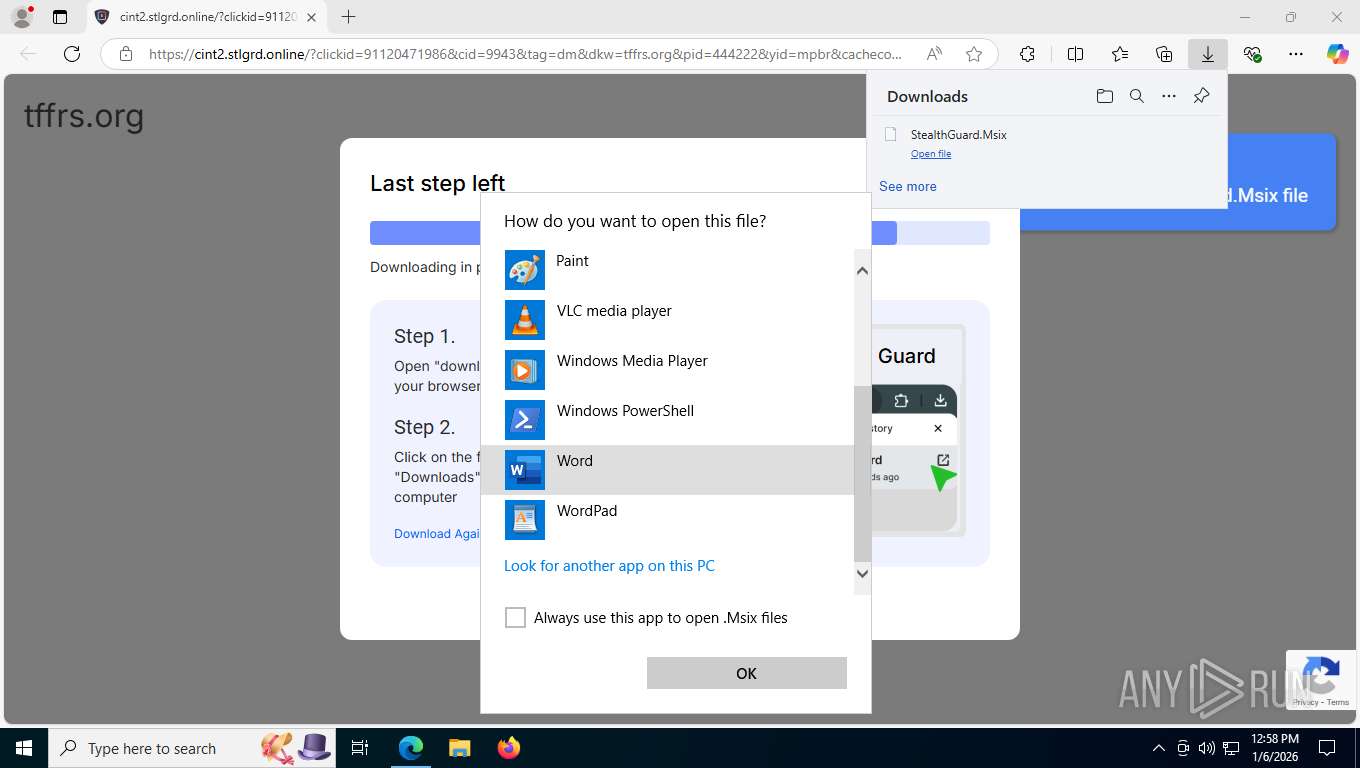
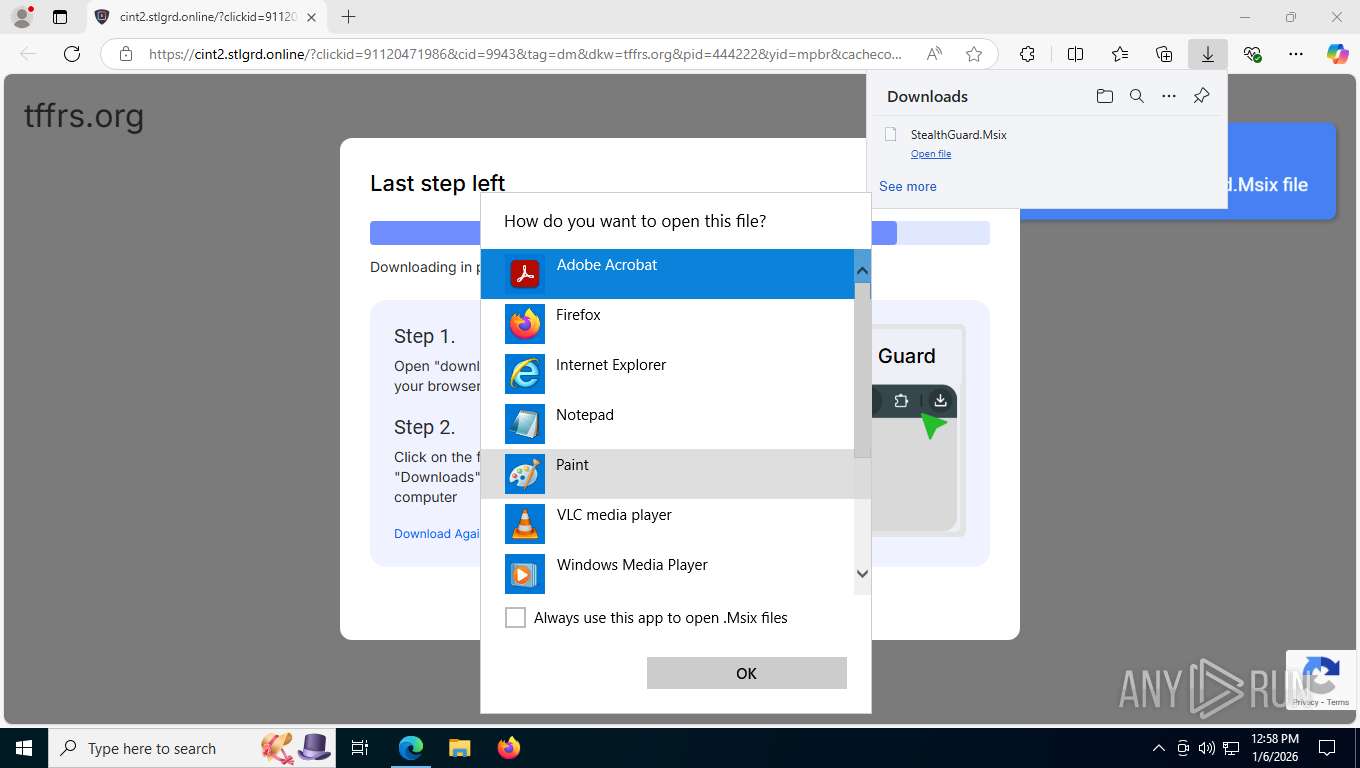
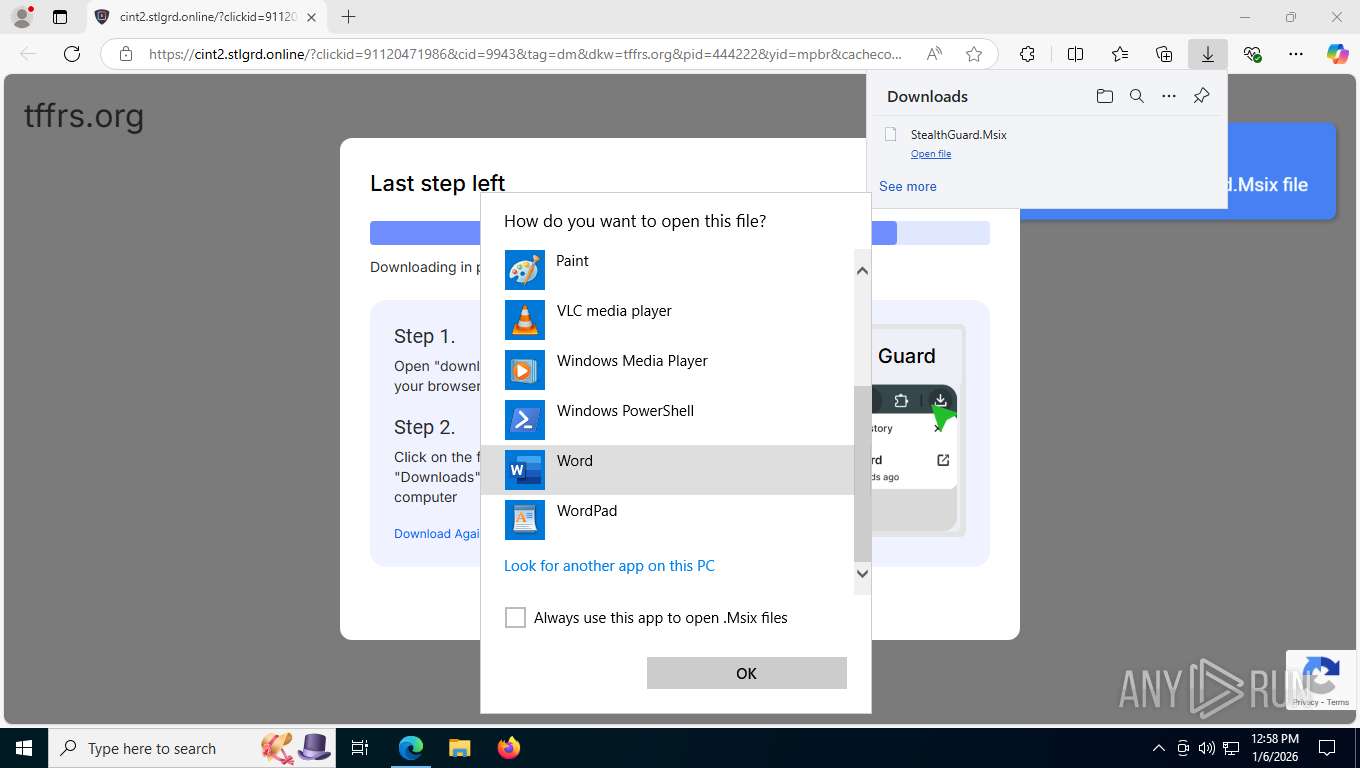
Starts POWERSHELL.EXE for commands execution
- OpenWith.exe (PID: 8736)
- powershell.exe (PID: 8892)
- powershell.exe (PID: 9164)
- powershell.exe (PID: 2348)
- powershell.exe (PID: 2364)
- powershell.exe (PID: 7280)
- powershell.exe (PID: 2196)
- powershell.exe (PID: 7268)
- powershell.exe (PID: 7956)
- powershell.exe (PID: 7228)
- powershell.exe (PID: 4504)
- powershell.exe (PID: 7392)
- powershell.exe (PID: 5696)
- powershell.exe (PID: 6792)
- powershell.exe (PID: 8216)
- powershell.exe (PID: 7208)
- powershell.exe (PID: 2752)
- powershell.exe (PID: 2688)
- powershell.exe (PID: 8904)
INFO
Reads Environment values
- identity_helper.exe (PID: 6300)
- identity_helper.exe (PID: 8284)
Application launched itself
- msedge.exe (PID: 7580)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 1420)
- OpenWith.exe (PID: 8736)
Checks supported languages
- identity_helper.exe (PID: 6300)
- identity_helper.exe (PID: 8284)
Reads the computer name
- identity_helper.exe (PID: 6300)
- identity_helper.exe (PID: 8284)
Reads security settings of Internet Explorer
- OpenWith.exe (PID: 8736)
Checks proxy server information
- slui.exe (PID: 4968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
225
Monitored processes
78
Malicious processes
1
Suspicious processes
12
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 356 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4332,i,14886012018743636288,16794267142948166491,262144 --variations-seed-version --mojo-platform-channel-handle=3972 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1232 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7424,i,14886012018743636288,16794267142948166491,262144 --variations-seed-version --mojo-platform-channel-handle=7368 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1412 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
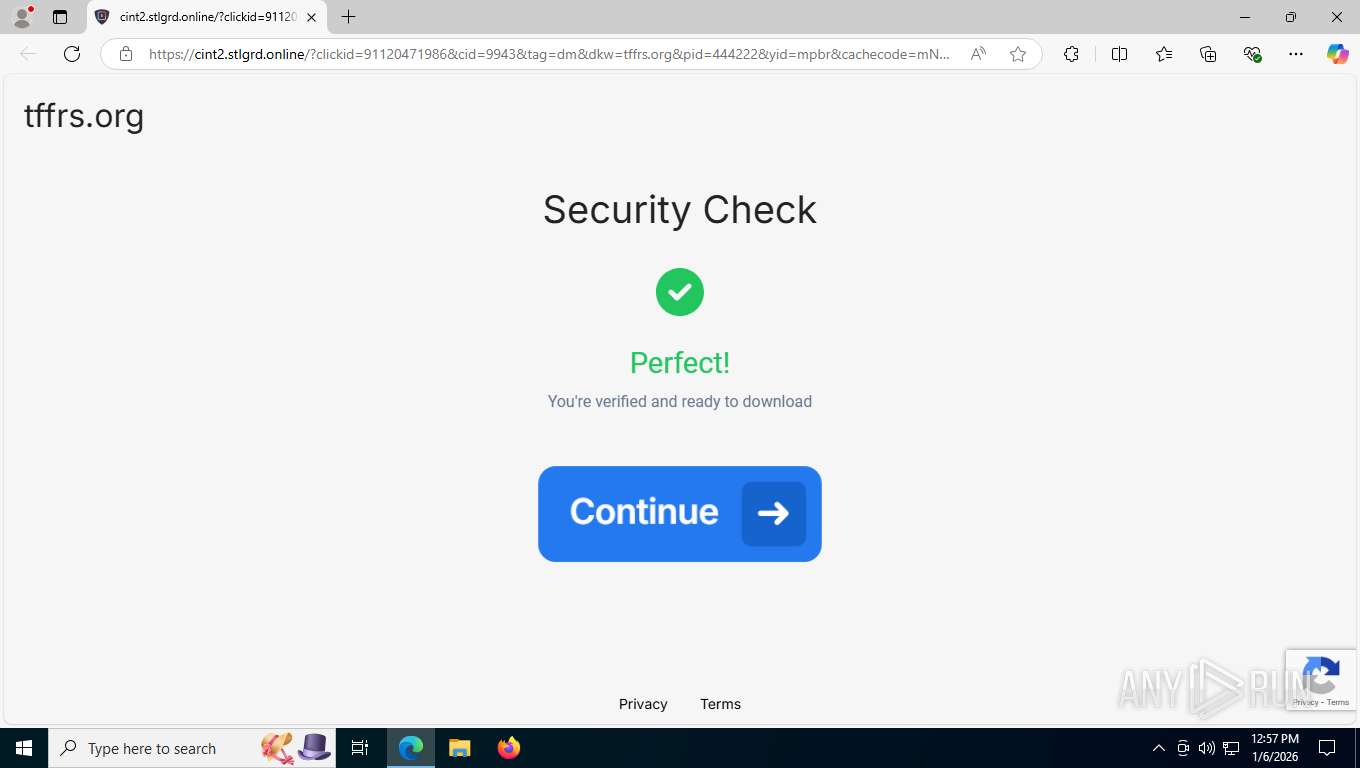
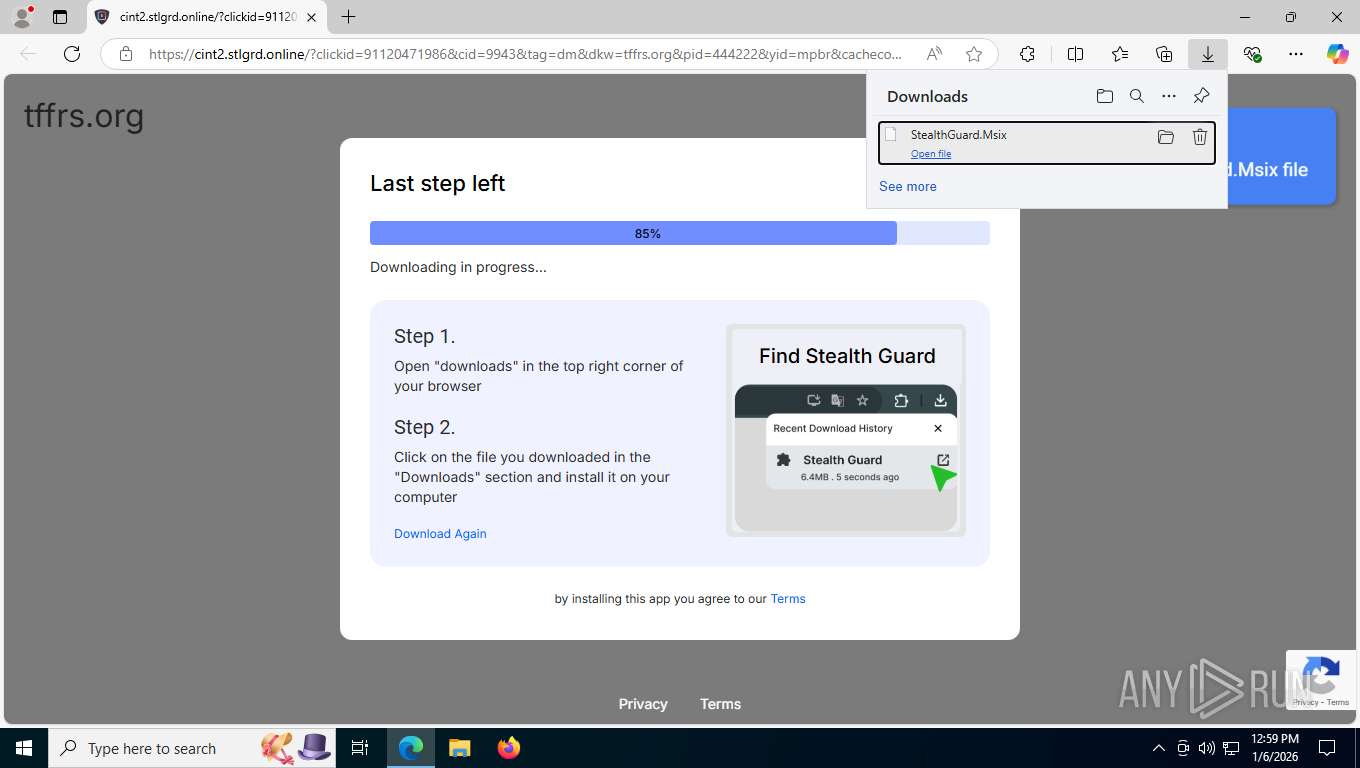
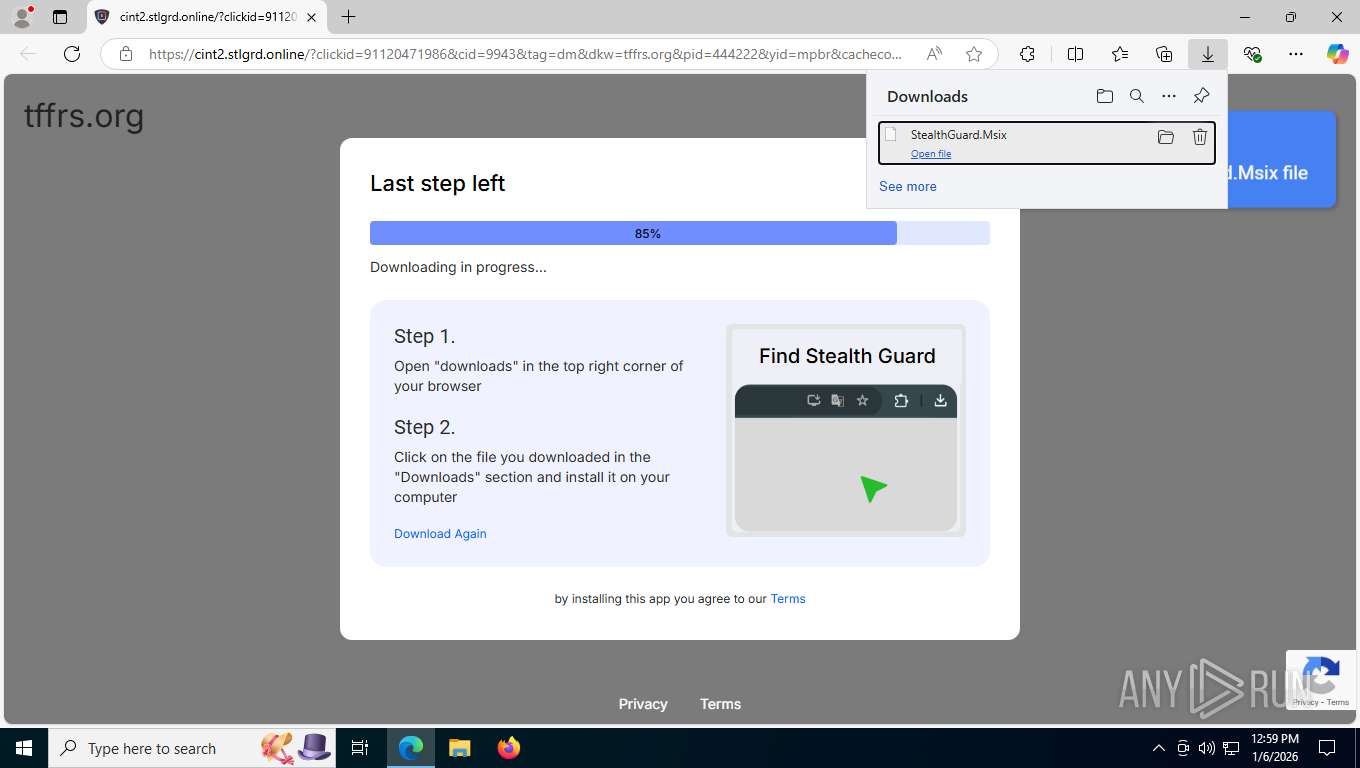
| 1412 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "C:\Users\admin\Downloads\StealthGuard.Msix" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
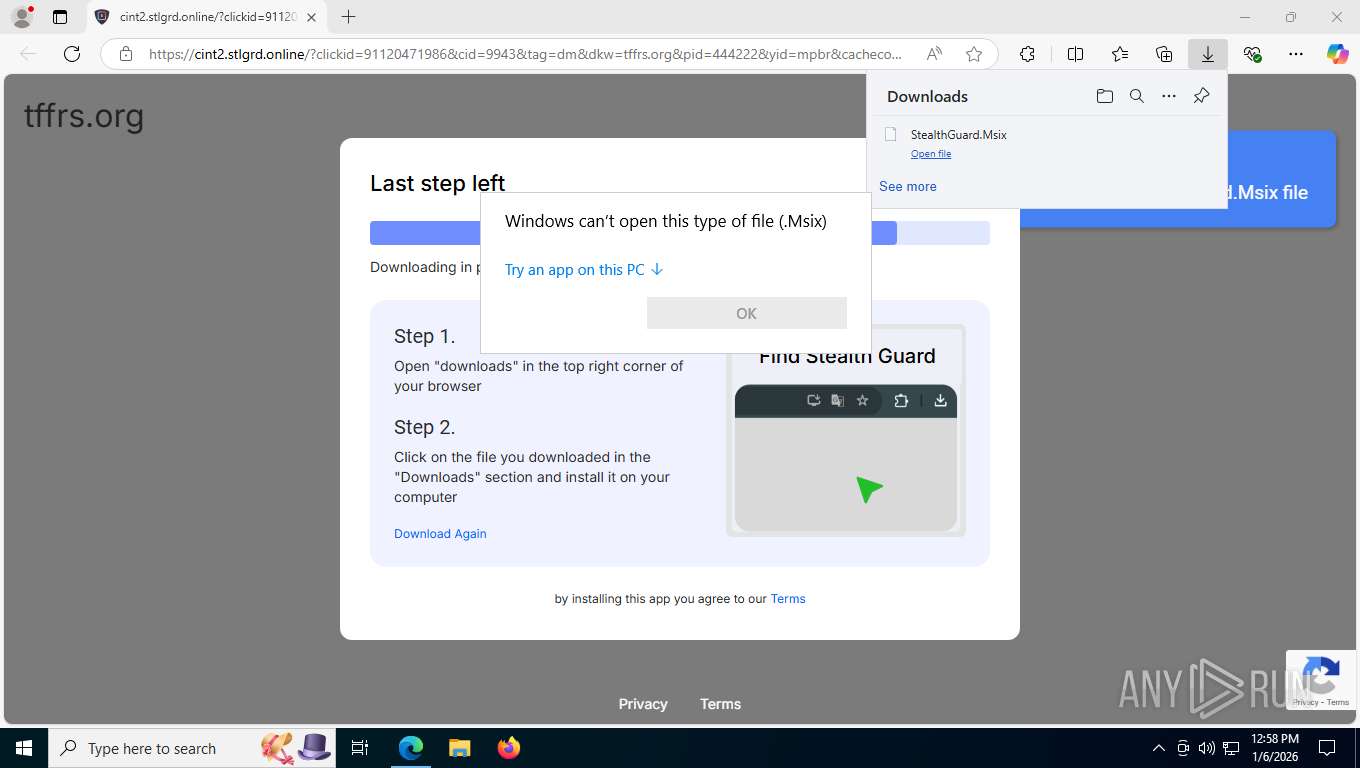
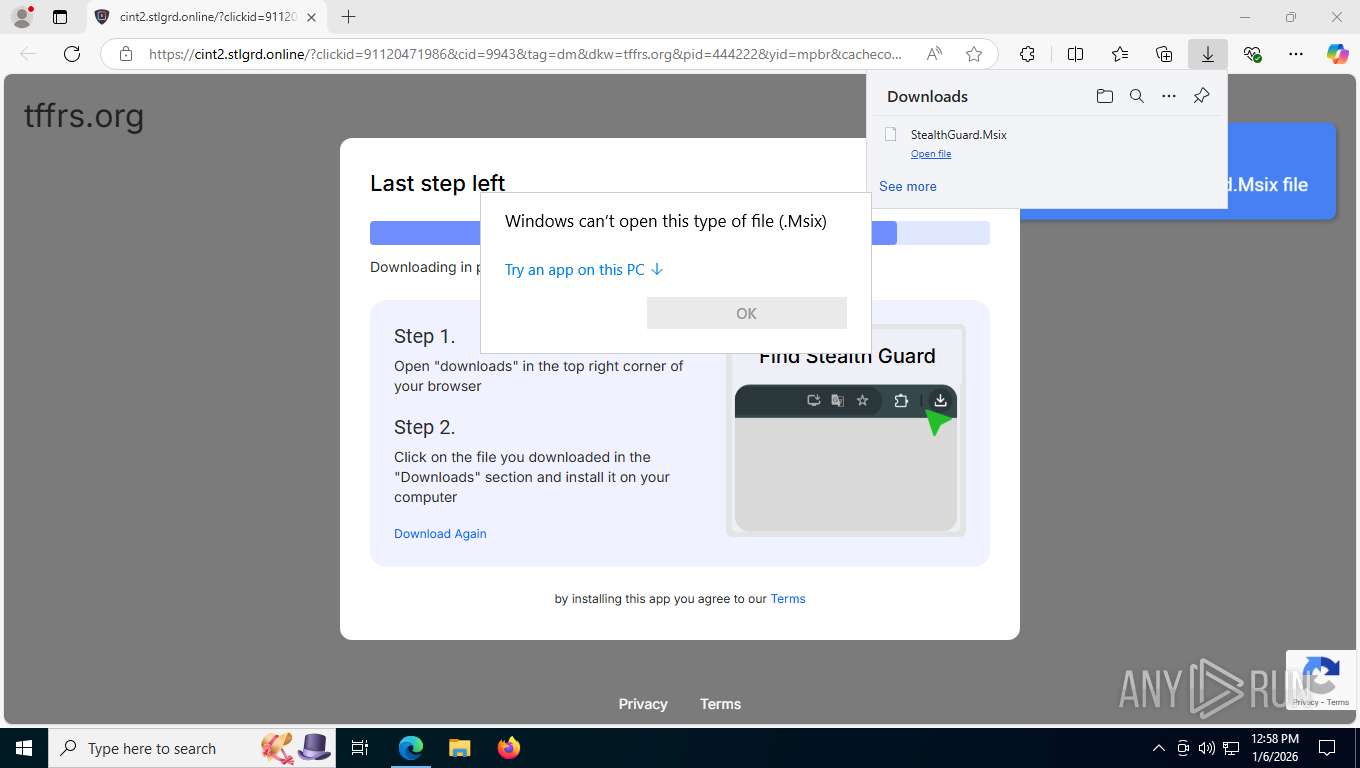
| 1420 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "C:\Users\admin\Downloads\StealthGuard.Msix" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2240 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=1680,i,14886012018743636288,16794267142948166491,262144 --variations-seed-version --mojo-platform-channel-handle=7788 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2252 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2348 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "C:\Users\admin\Downloads\StealthGuard.Msix" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2364 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "C:\Users\admin\Downloads\StealthGuard.Msix" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
94 042
Read events
94 014
Write events
28
Delete events
0
Modification events
| (PID) Process: | (8736) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.Msix\UserChoice |
| Operation: | write | Name: | ProgId |
Value: Applications\powershell.exe | |||
| (PID) Process: | (8736) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.Msix\UserChoice |
| Operation: | write | Name: | Hash |
Value: 7nB0QBWh55A= | |||
| (PID) Process: | (8736) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.Msix\OpenWithProgids |
| Operation: | write | Name: | Msix_auto_file |
Value: | |||
| (PID) Process: | (8736) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.Msix\OpenWithList |
| Operation: | write | Name: | a |
Value: powershell.exe | |||
| (PID) Process: | (8736) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.Msix\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
| (PID) Process: | (8736) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 138 | |||
| (PID) Process: | (8892) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.Msix\OpenWithProgids |
| Operation: | write | Name: | Msix_auto_file |
Value: | |||
| (PID) Process: | (9164) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.Msix\OpenWithProgids |
| Operation: | write | Name: | Msix_auto_file |
Value: | |||
| (PID) Process: | (2348) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.Msix\OpenWithProgids |
| Operation: | write | Name: | Msix_auto_file |
Value: | |||
| (PID) Process: | (2364) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.Msix\OpenWithProgids |
| Operation: | write | Name: | Msix_auto_file |
Value: | |||
Executable files
1
Suspicious files
120
Text files
349
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7580 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RFfdece.TMP | — | |
MD5:— | SHA256:— | |||
| 7580 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7580 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFfdeed.TMP | — | |
MD5:— | SHA256:— | |||
| 7580 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFfdefd.TMP | — | |
MD5:— | SHA256:— | |||
| 7580 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7580 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFfdefd.TMP | — | |
MD5:— | SHA256:— | |||
| 7580 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFfdf0c.TMP | — | |
MD5:— | SHA256:— | |||
| 7580 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7580 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFfdf0c.TMP | — | |
MD5:— | SHA256:— | |||
| 7580 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
160
TCP/UDP connections
106
DNS requests
112
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7908 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:DXej9qxQjVOVSXjxN-b34qCSwNFhgO-1qwxAvCr2eXc&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
7908 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=EdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=65&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1741678270&lafgdate=0 | unknown | text | 768 b | whitelisted |
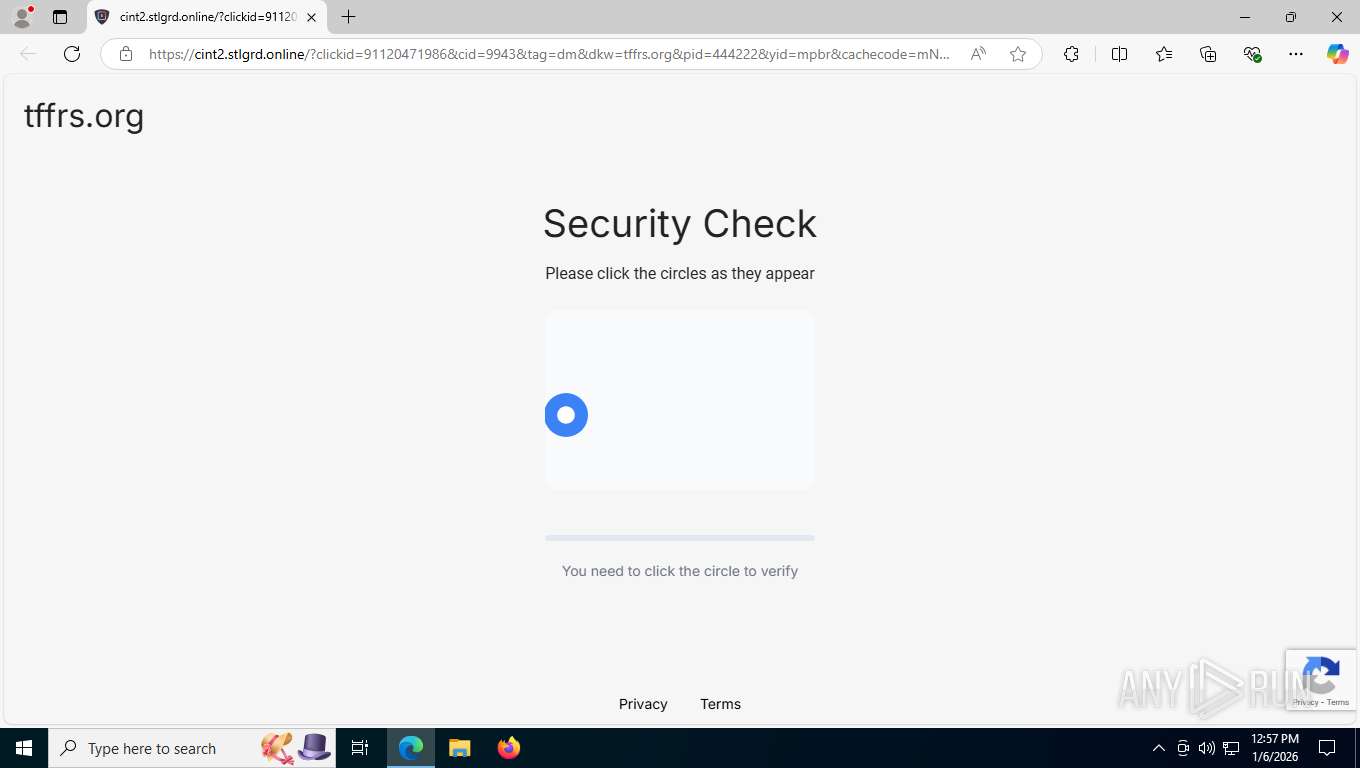
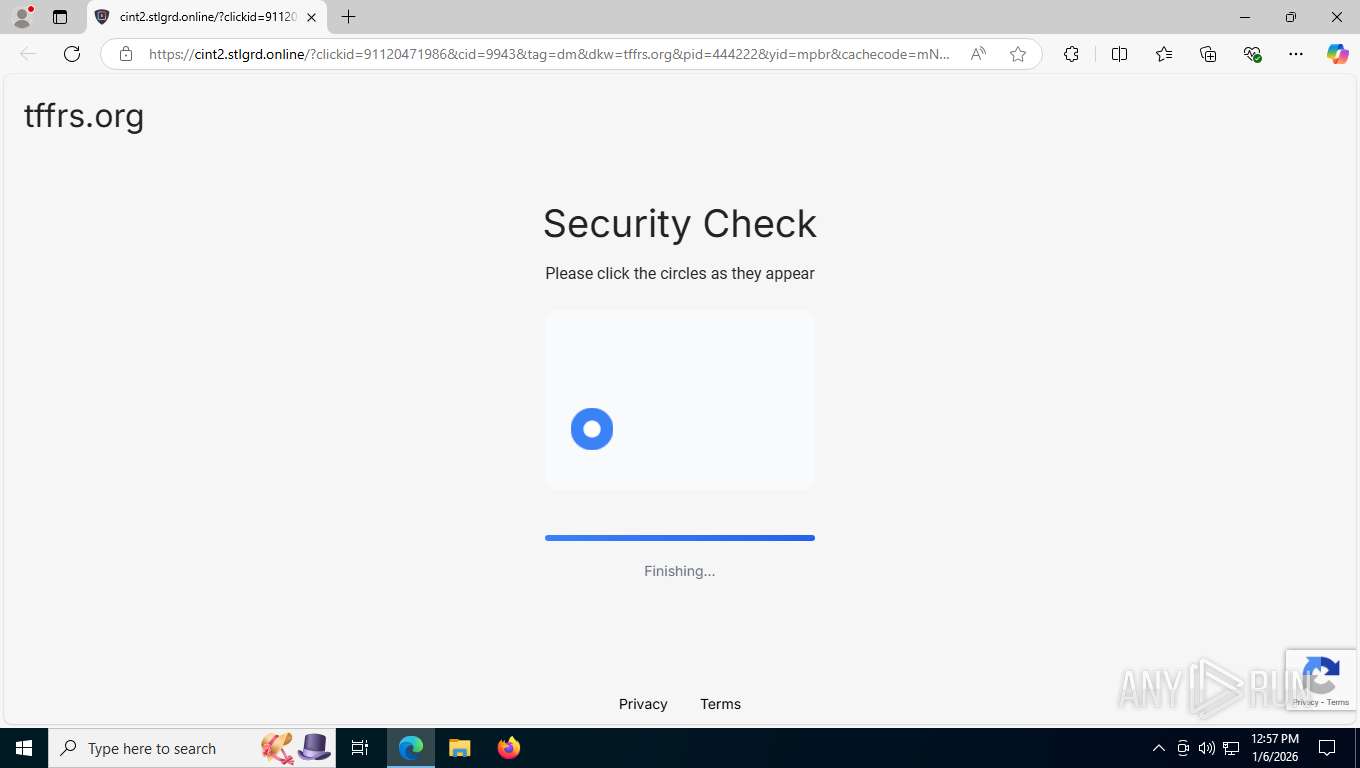
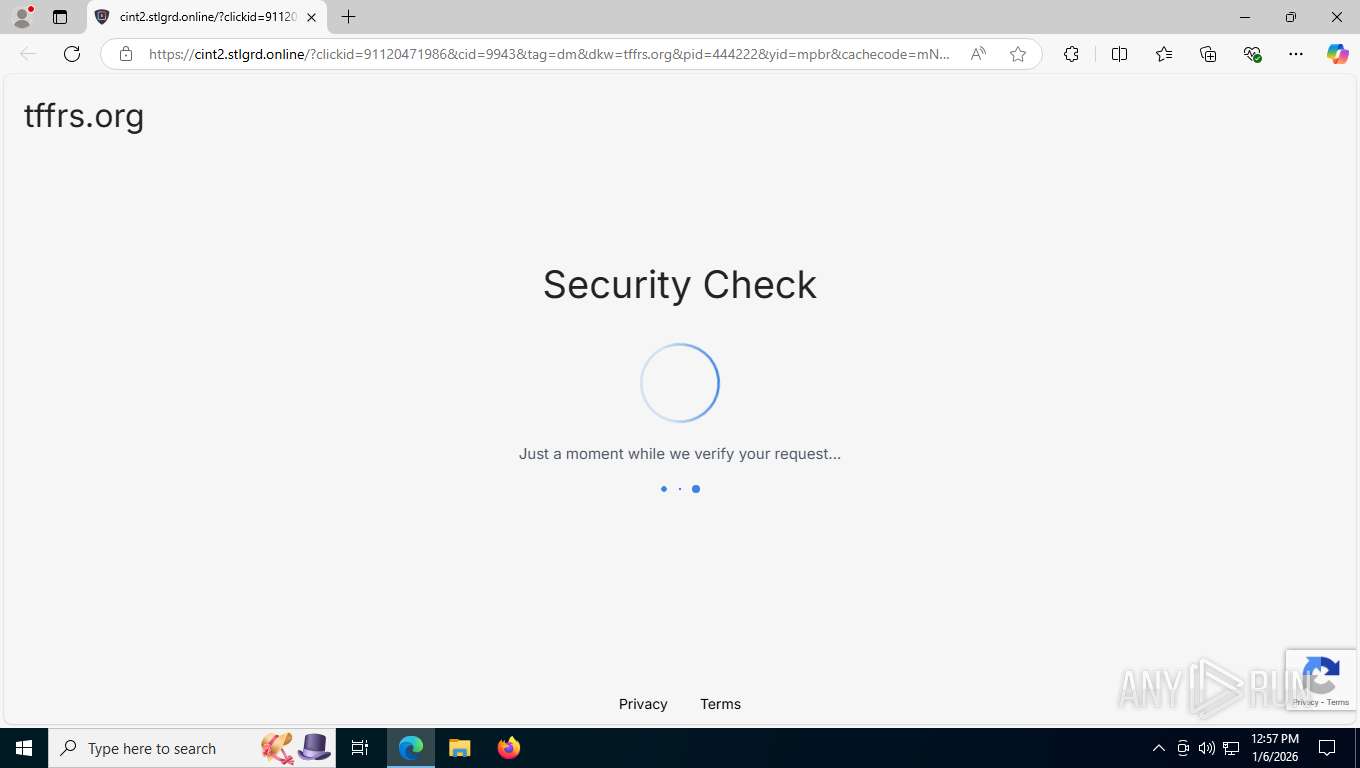
7908 | msedge.exe | GET | 200 | 188.114.97.3:443 | https://cint2.stlgrd.online/lps/security-check/styles/styles.css?v=17 | unknown | text | 7.94 Kb | unknown |
7908 | msedge.exe | GET | 200 | 150.171.28.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | unknown | text | 295 b | whitelisted |
7908 | msedge.exe | GET | 200 | 188.114.97.3:443 | https://cint2.stlgrd.online/?clickid=91120471986&cid=9943&tag=dm&dkw=tffrs.org&pid=444222&yid=mpbr&cachecode=mNZded5Ps9Sg%2BsevvWfzUA%3D%3D&rhi=b2747df0-772a-4f00-ad31-3e6f2a26c3cb | unknown | html | 35.1 Kb | unknown |
7908 | msedge.exe | GET | 200 | 104.18.23.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | unknown | text | 25 b | whitelisted |
7908 | msedge.exe | GET | 200 | 188.114.97.3:443 | https://cint2.stlgrd.online/lps/security-check/styles/hint.css?v=17 | unknown | text | 14.6 Kb | unknown |
7908 | msedge.exe | GET | 200 | 188.114.97.3:443 | https://cint2.stlgrd.online/js/shared/protections.min.js | unknown | text | 72.5 Kb | unknown |
7908 | msedge.exe | GET | 206 | 188.114.97.3:443 | https://cint2.stlgrd.online/assets/videos/mpbr.mp4 | unknown | — | — | unknown |
7908 | msedge.exe | GET | 200 | 188.114.97.3:443 | https://cint2.stlgrd.online/lps/security-check/assets/images/download.svg | unknown | image | 671 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
1600 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
496 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7908 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7908 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7908 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7908 | msedge.exe | 188.114.97.3:443 | cint2.stlgrd.online | CLOUDFLARENET | US | whitelisted |
7908 | msedge.exe | 104.18.23.222:443 | copilot.microsoft.com | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
cint2.stlgrd.online |
| malicious |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7908 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain (stlgrd .online) |
7908 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7908 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7908 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7908 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7908 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7908 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |