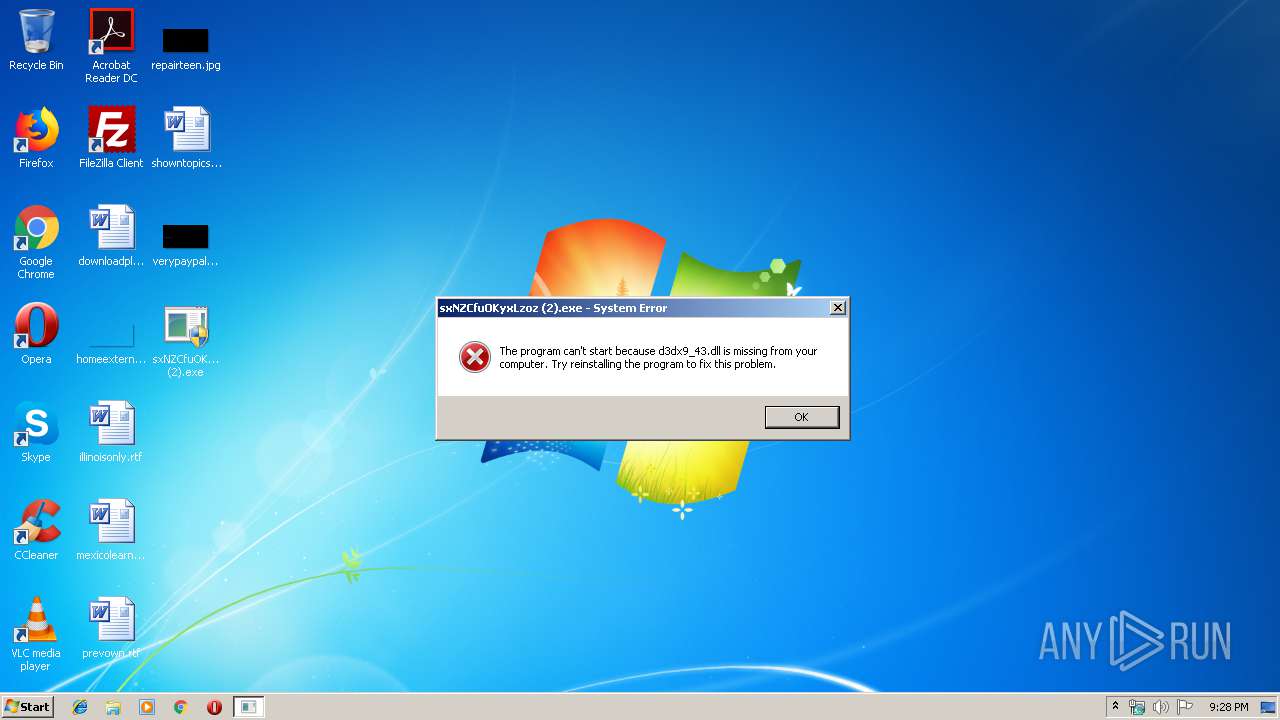
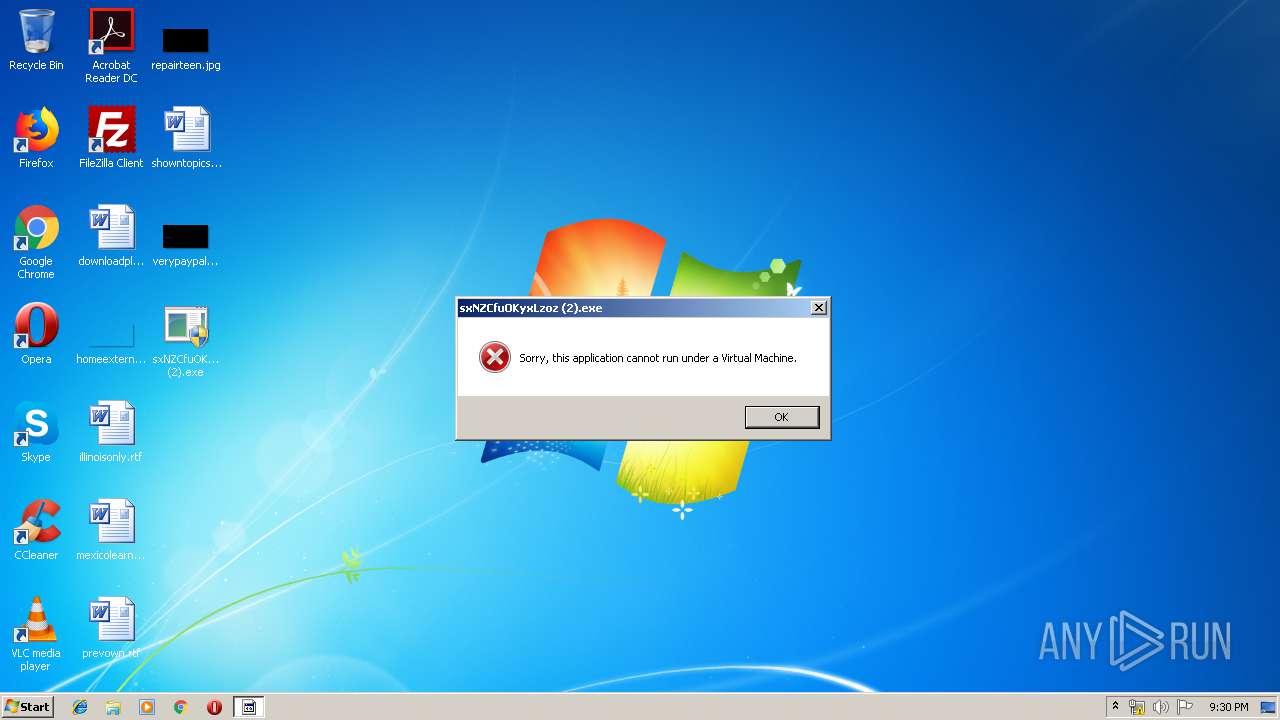
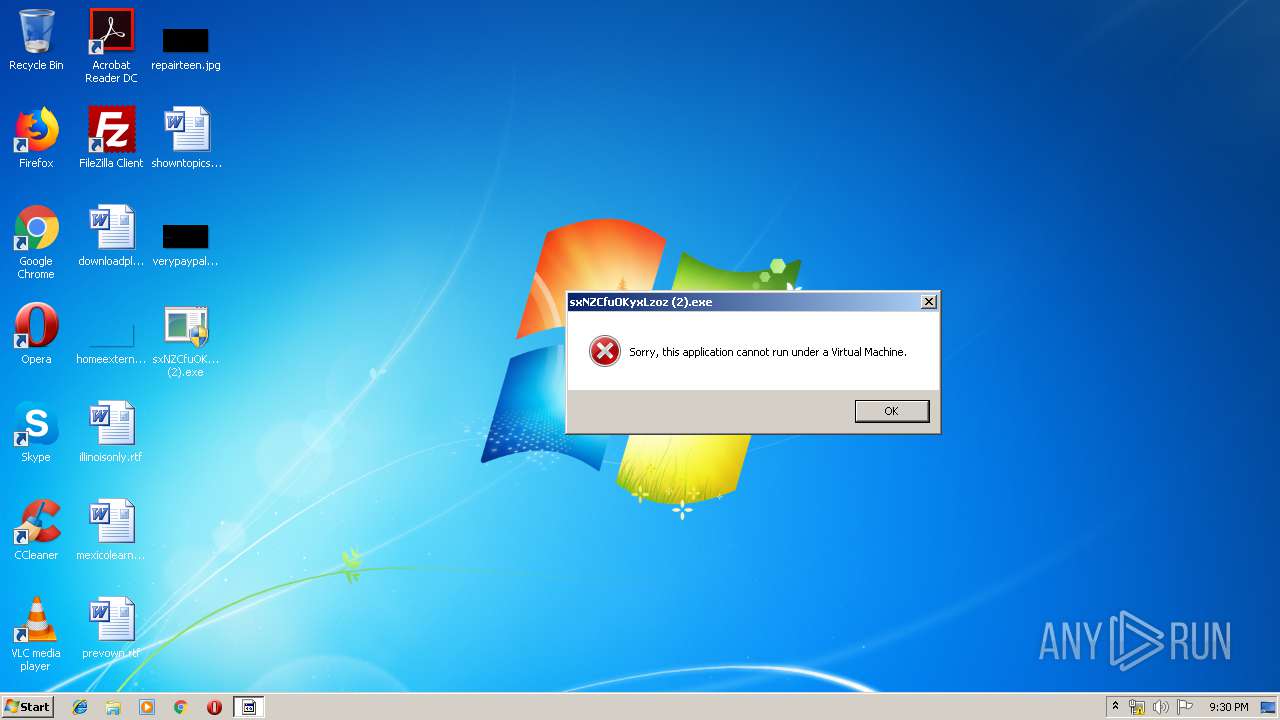
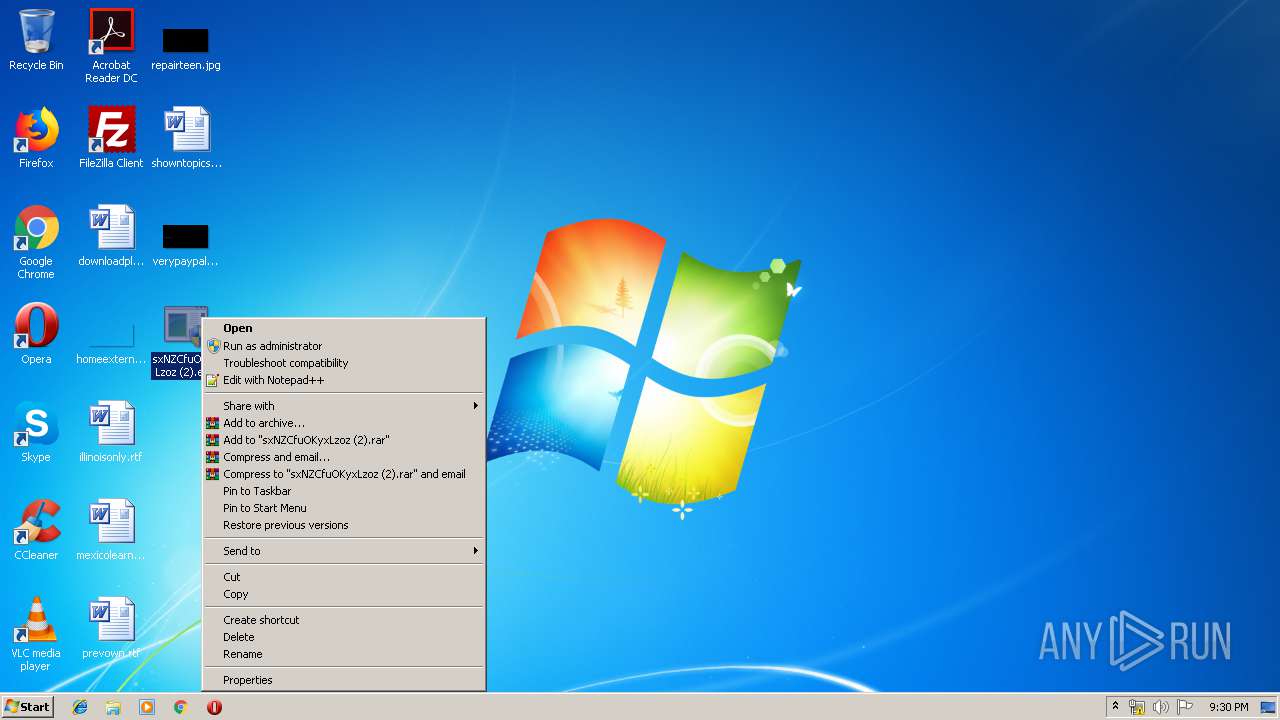
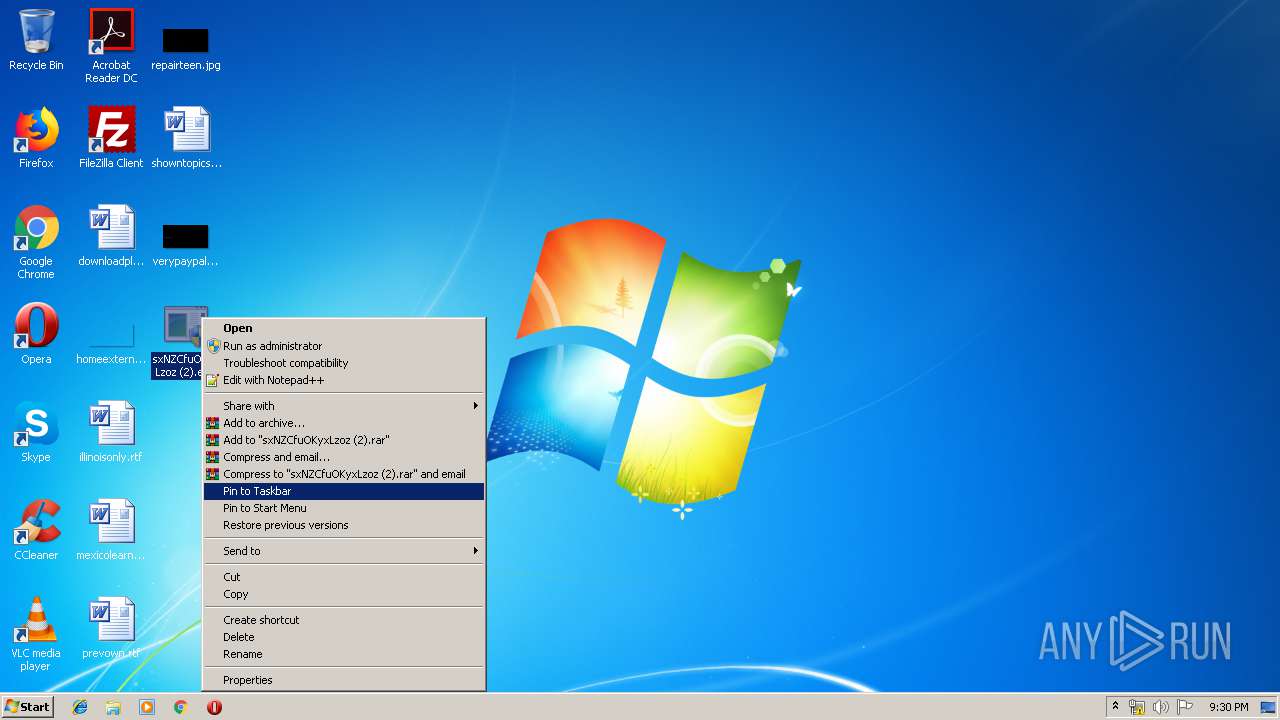
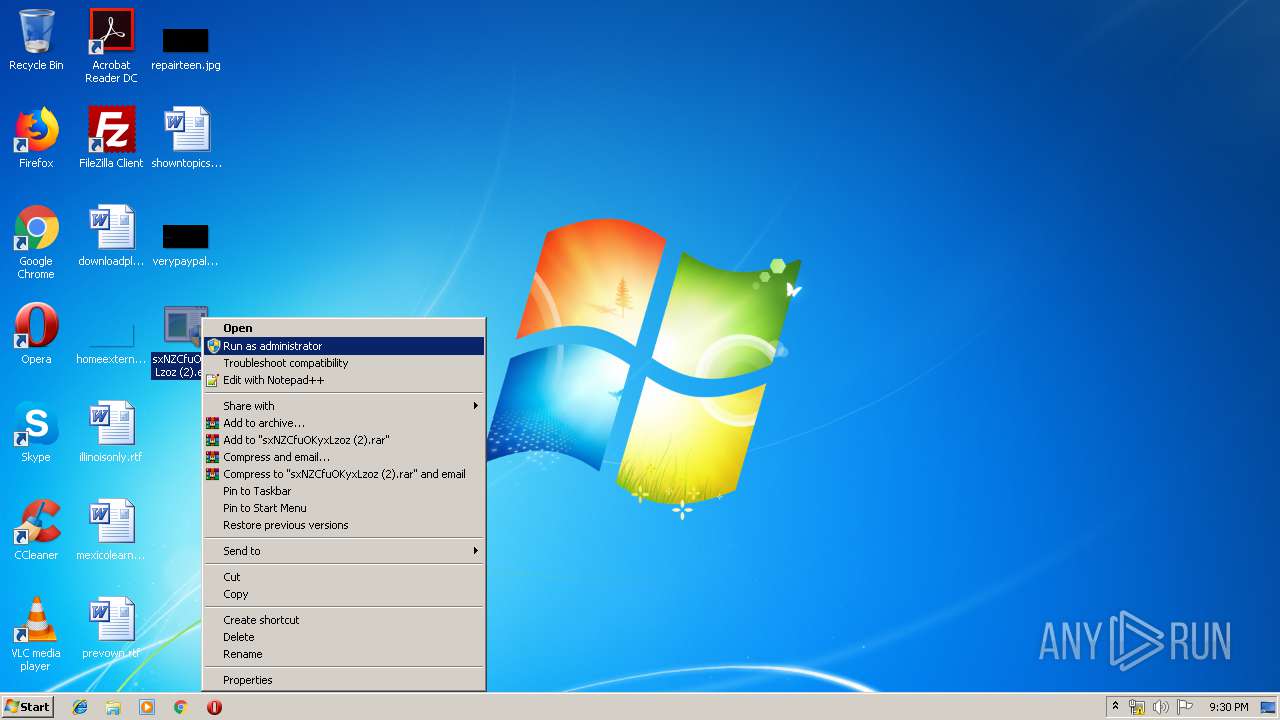
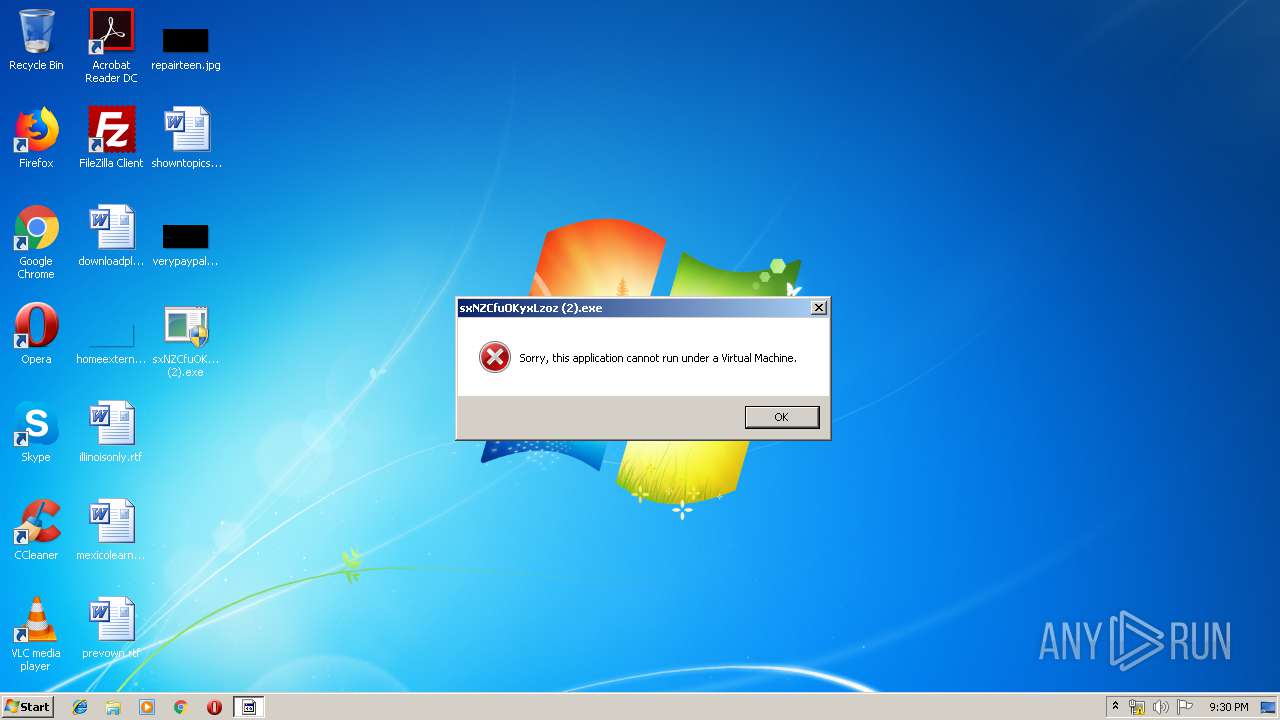
| File name: | sxNZCfuOKyxLzoz (2).exe |
| Full analysis: | https://app.any.run/tasks/08b901a4-b0f6-409d-bc1a-340318cbe33d |
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2019, 21:28:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 45807ECE76EE92229E19C58CA93CF4CF |
| SHA1: | F8A863EA6769B7193A9F400718B9A90D31DBDE75 |
| SHA256: | 3DC7EAE909B998D422FAEB900FB55D4AF4FCD5B64FADDDB2B48BB9AE1593F3D3 |
| SSDEEP: | 98304:zu6+L/RyxwCAJiOaWfxFORt3RfKHctxo4v6R0Ztt04nN0KsII3iMvz8+6TdK45Jq:a6+0xwn5aU+4Hcvov0rt04nN6X5gLpBB |
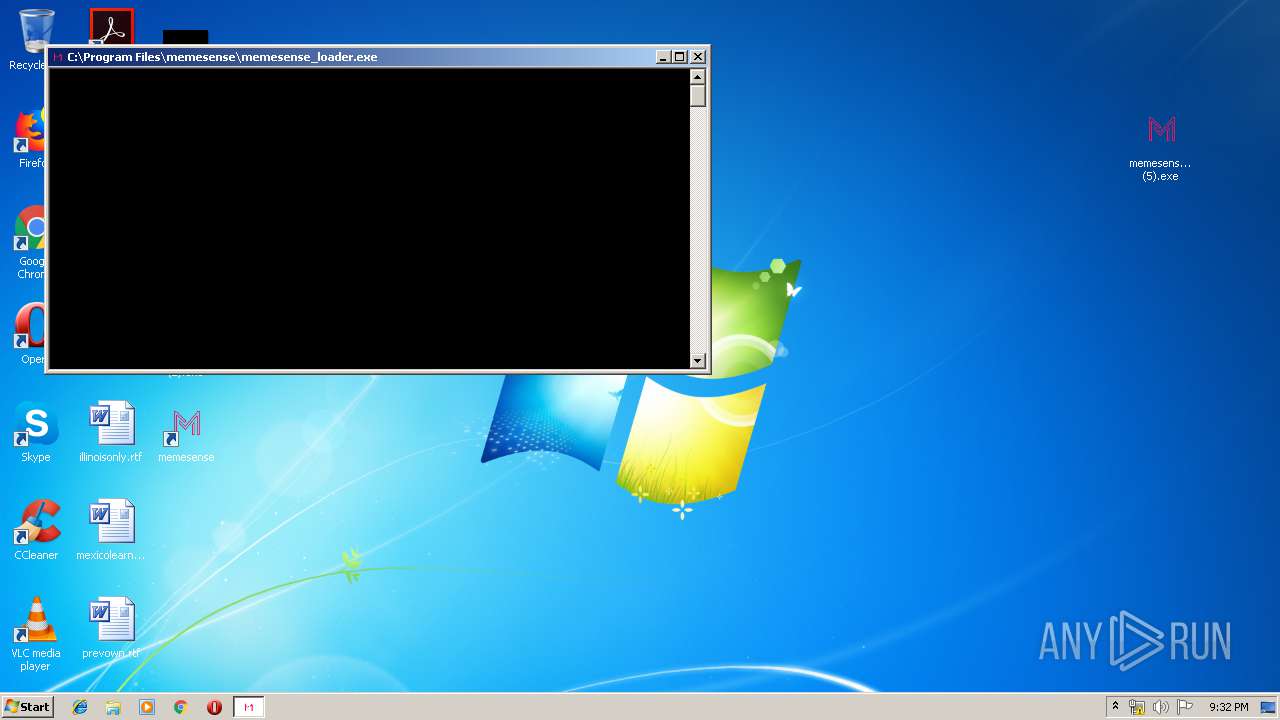
MALICIOUS
Changes the autorun value in the registry
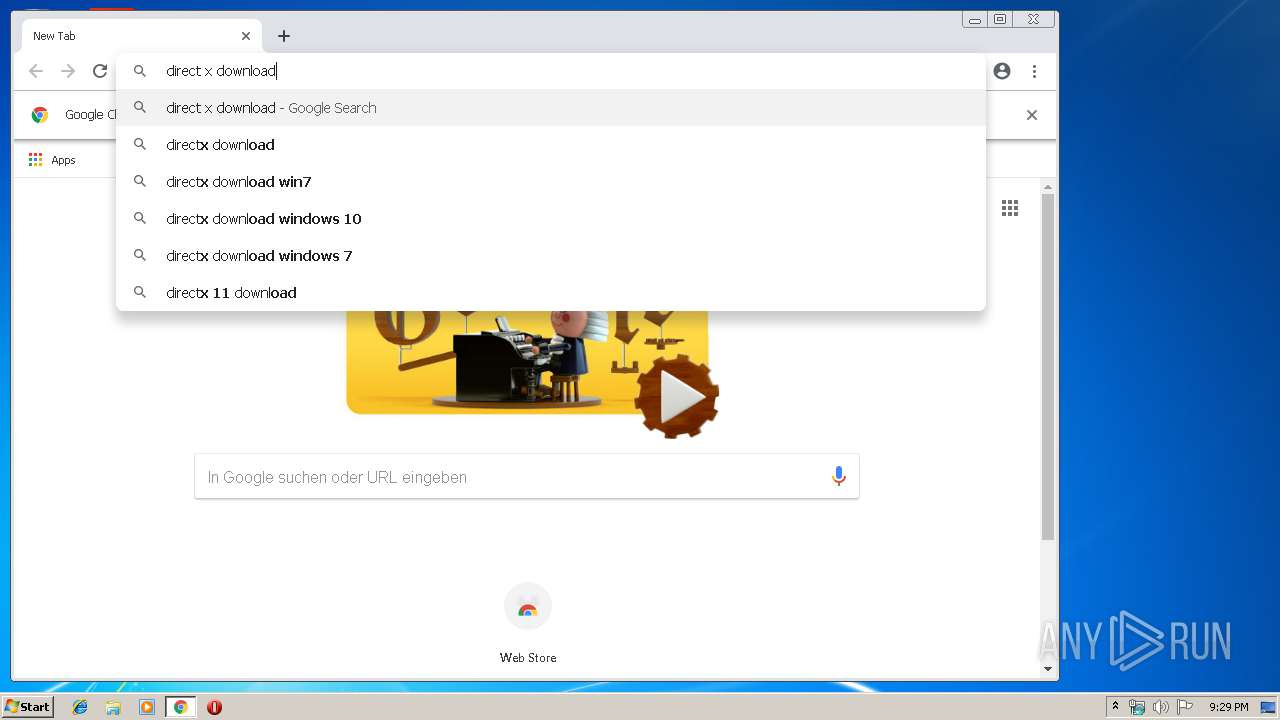
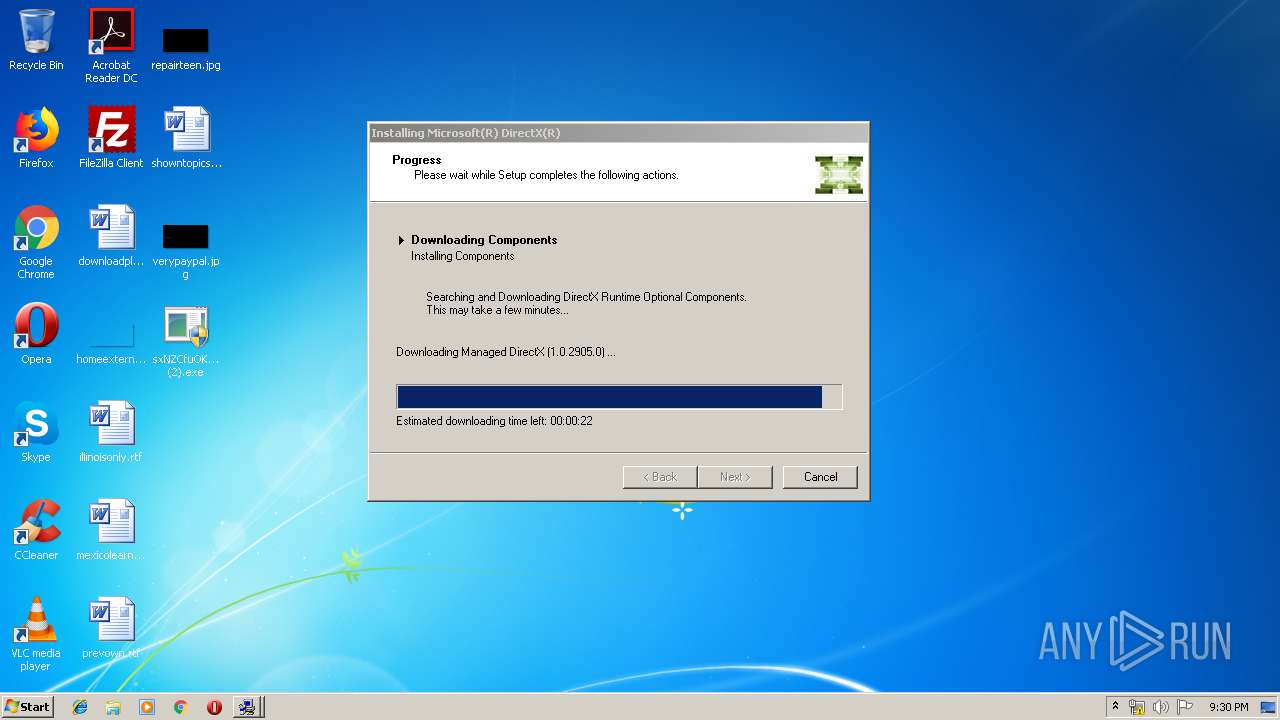
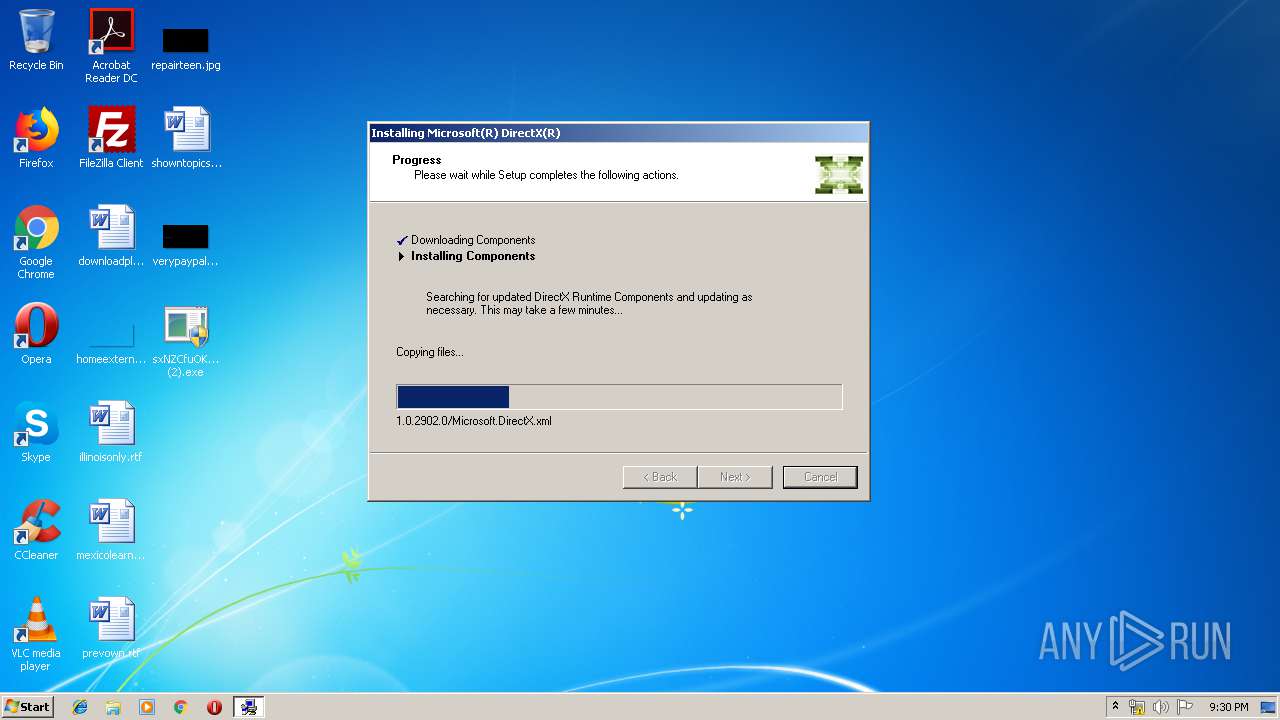
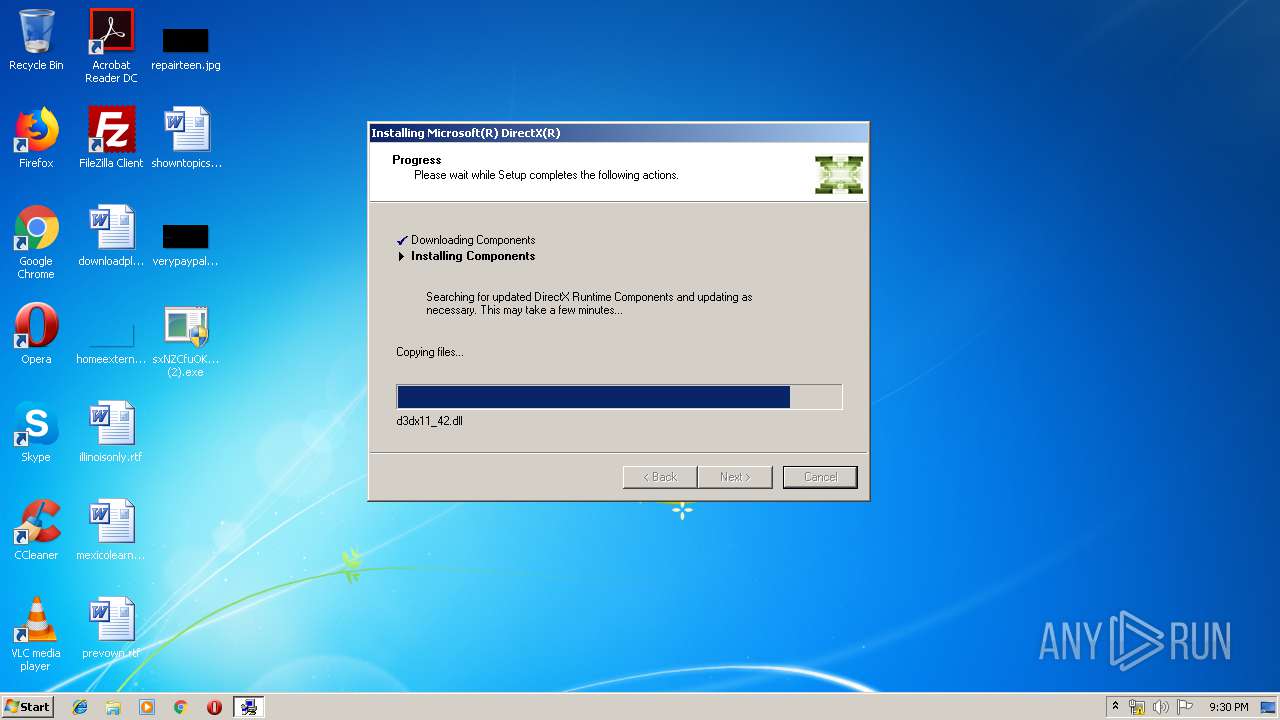
- dxwebsetup.exe (PID: 720)
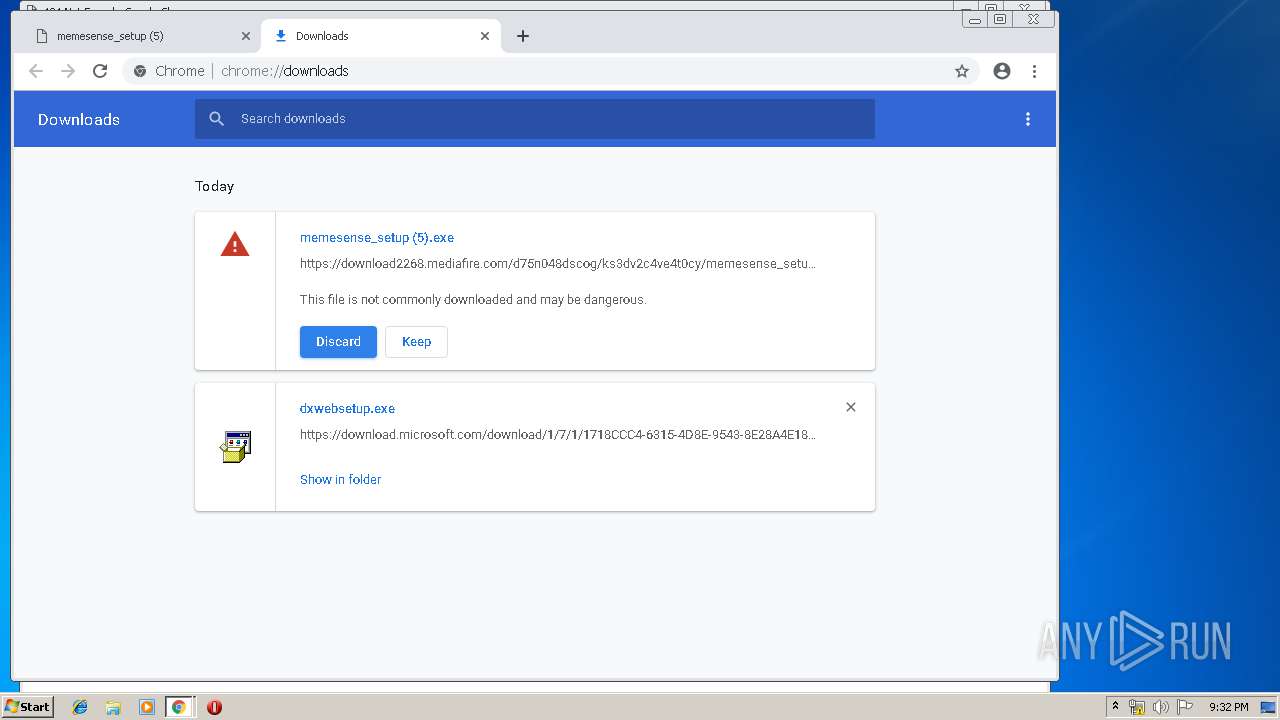
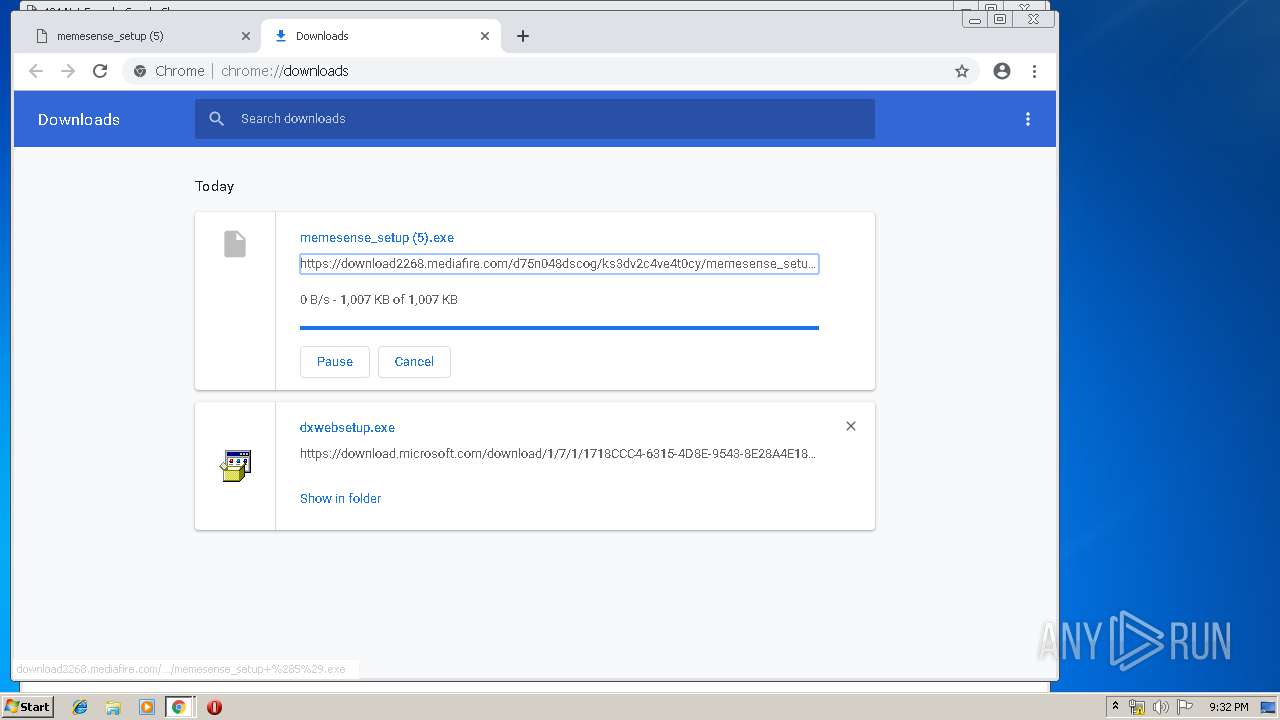
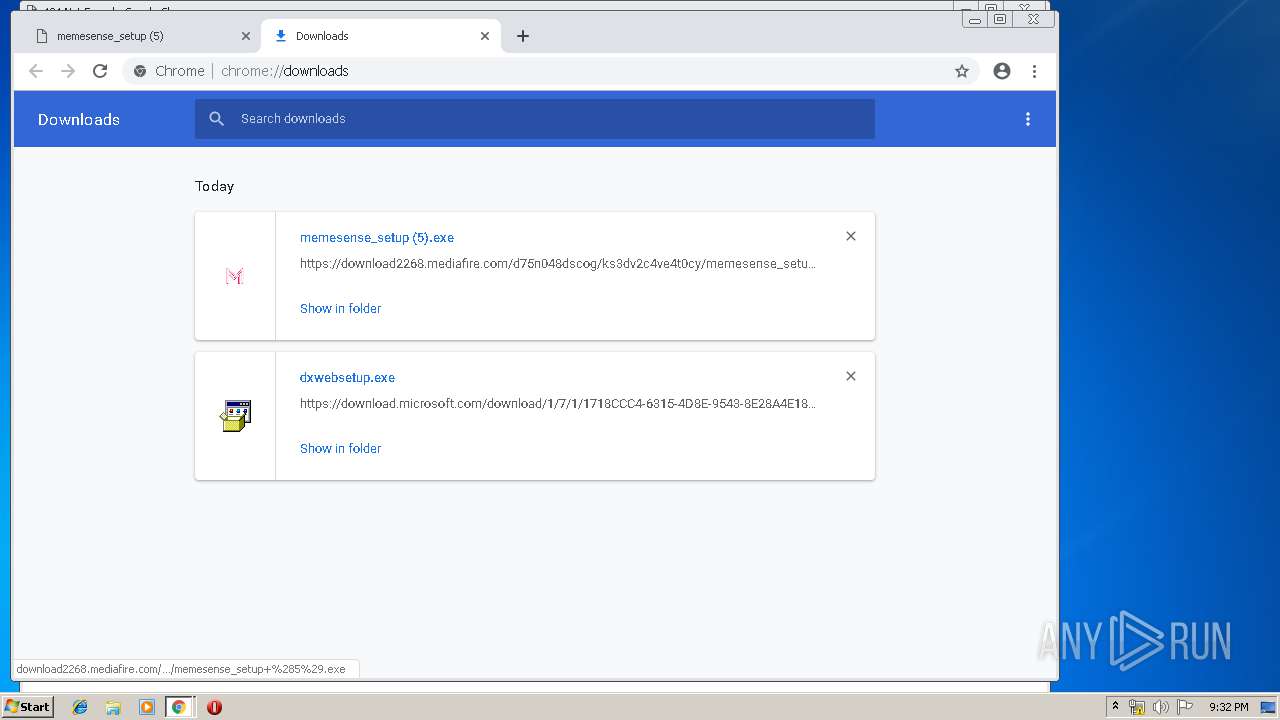
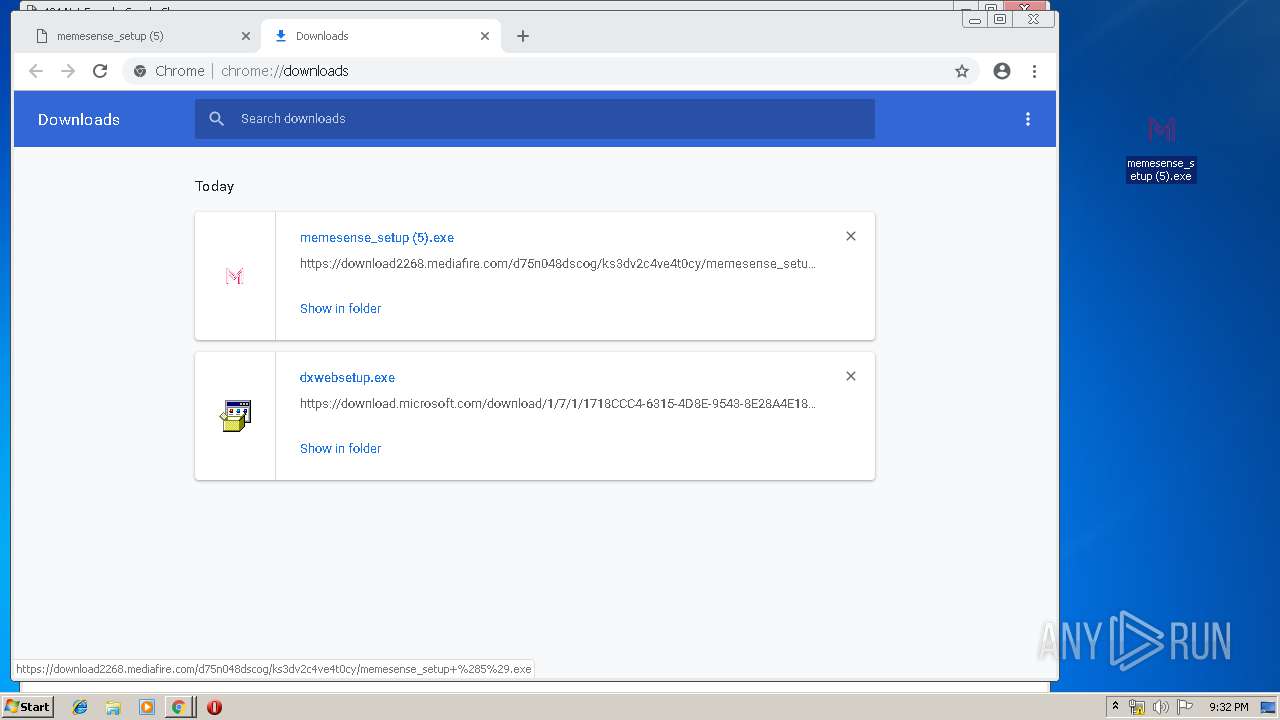
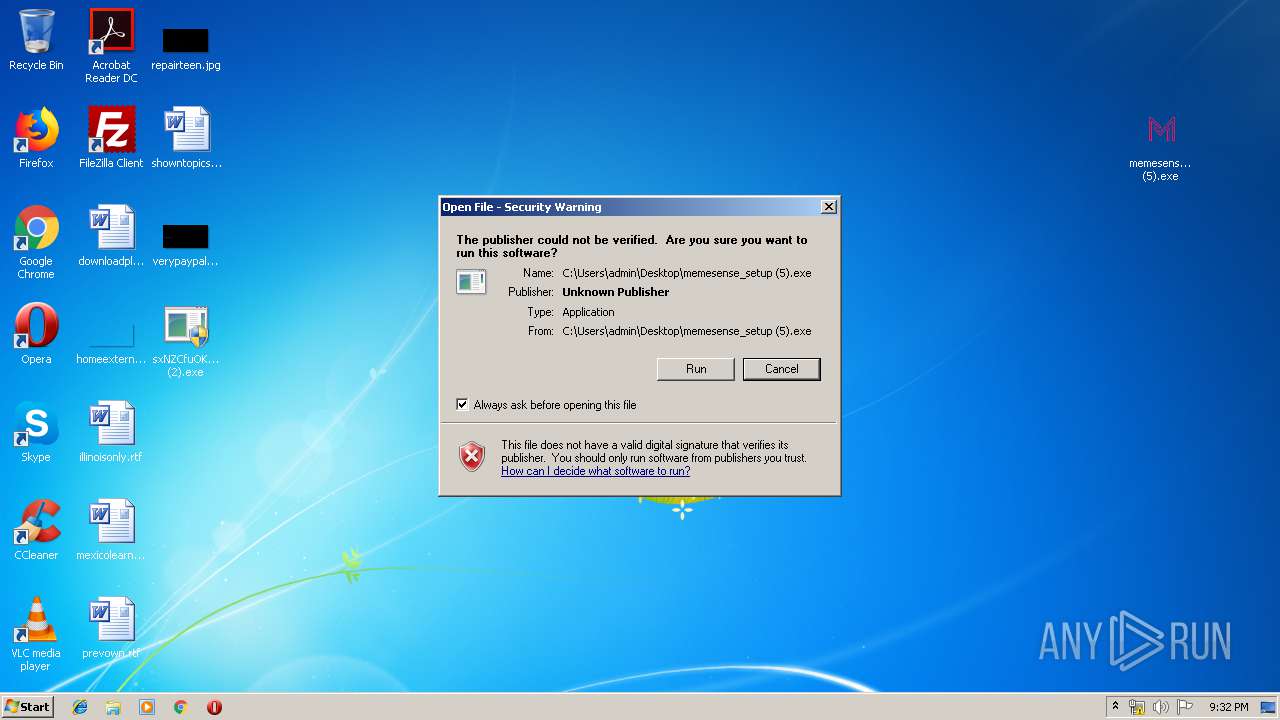
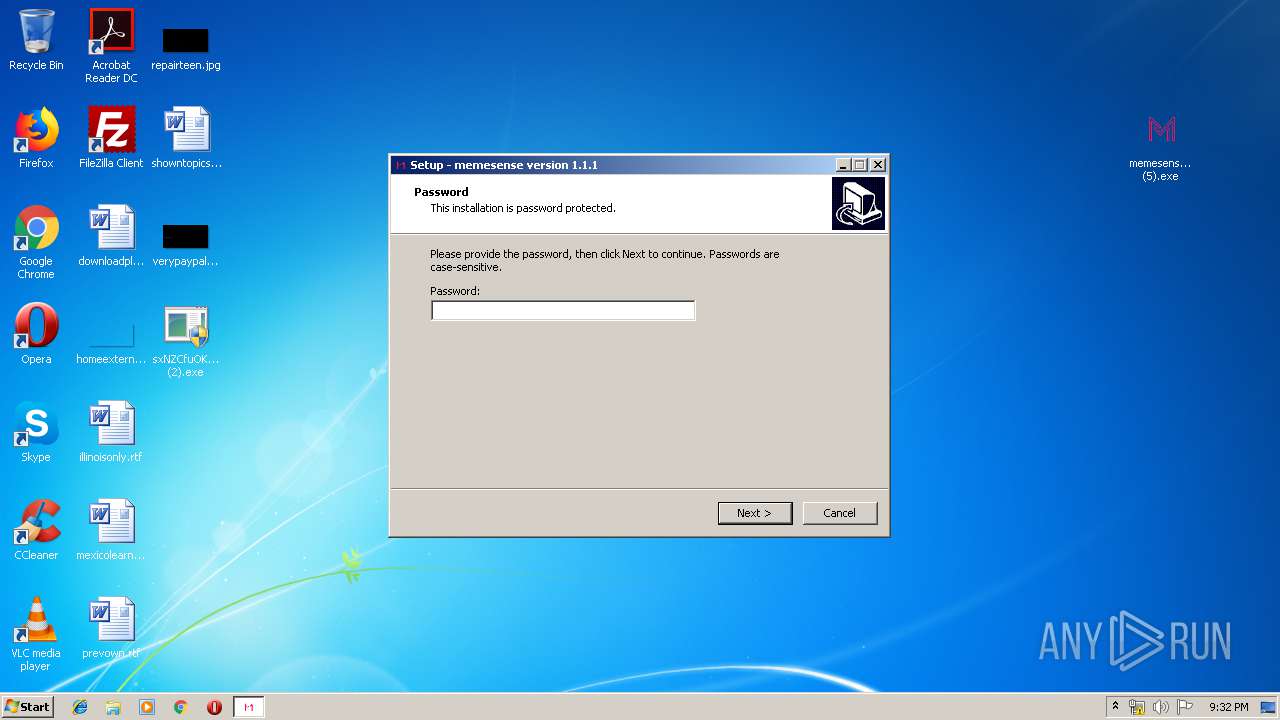
Application was dropped or rewritten from another process
- dxwsetup.exe (PID: 2092)
- dxwebsetup.exe (PID: 2932)
- dxwebsetup.exe (PID: 720)
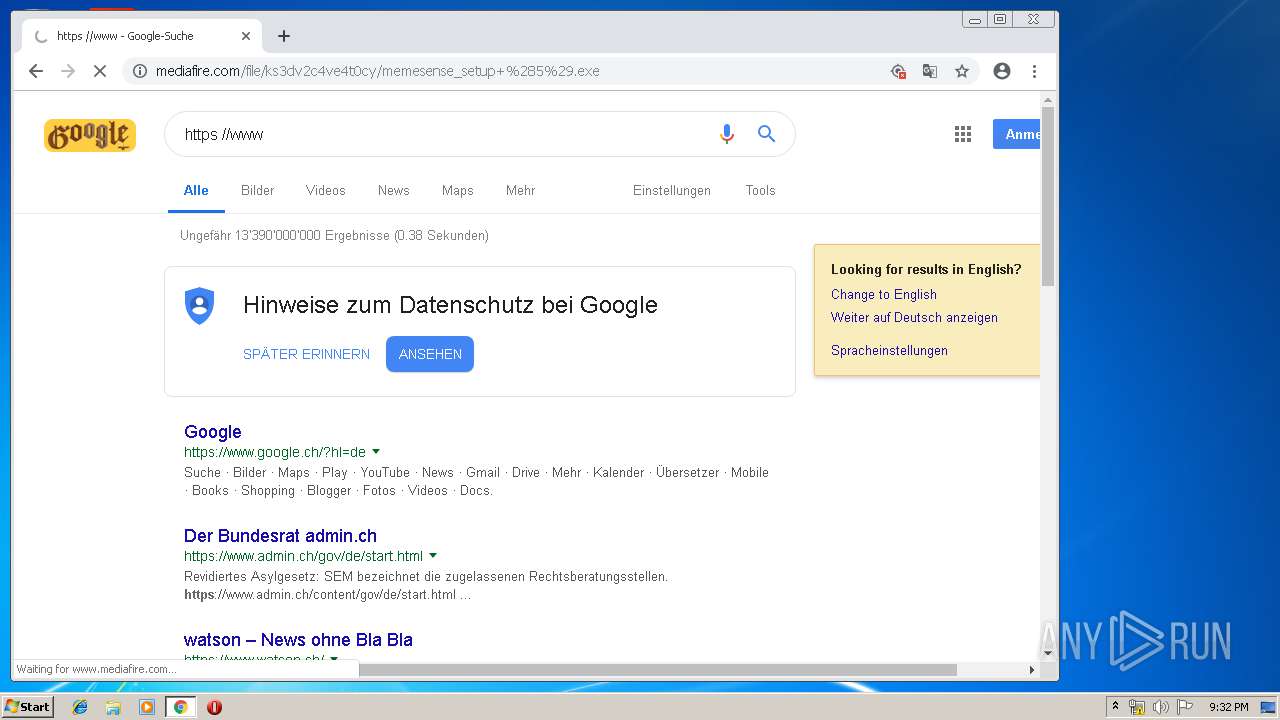
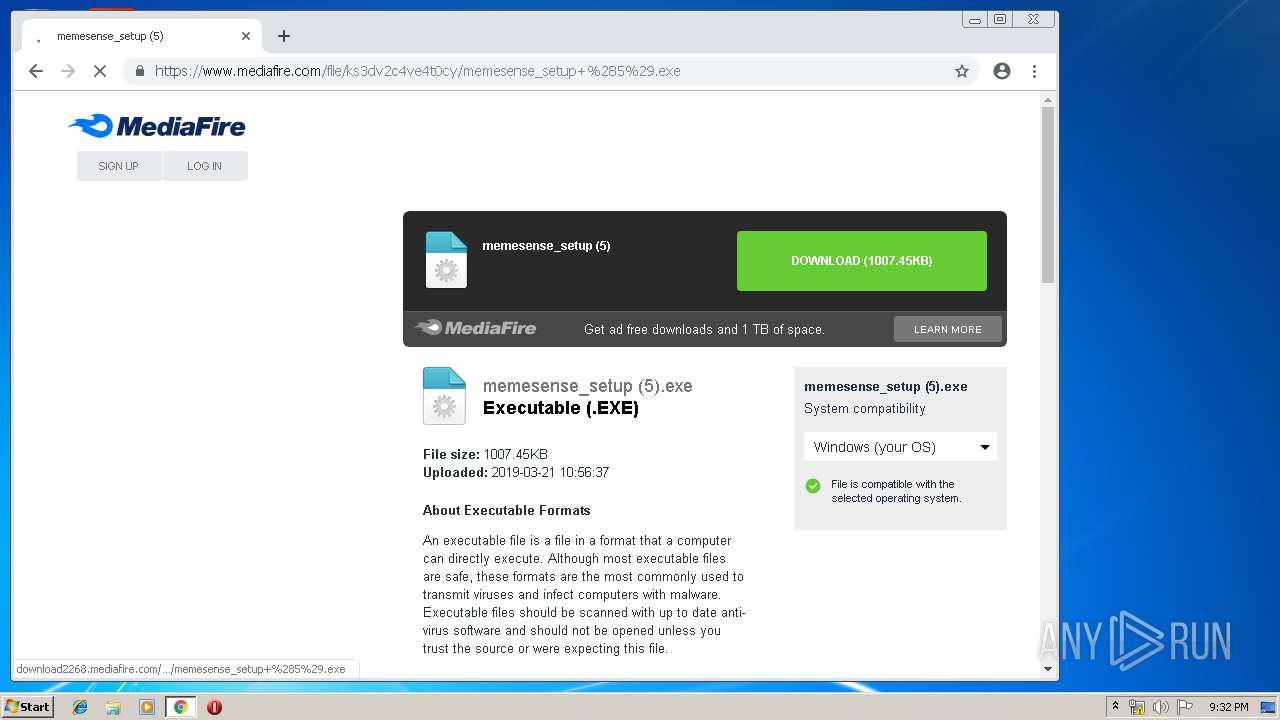
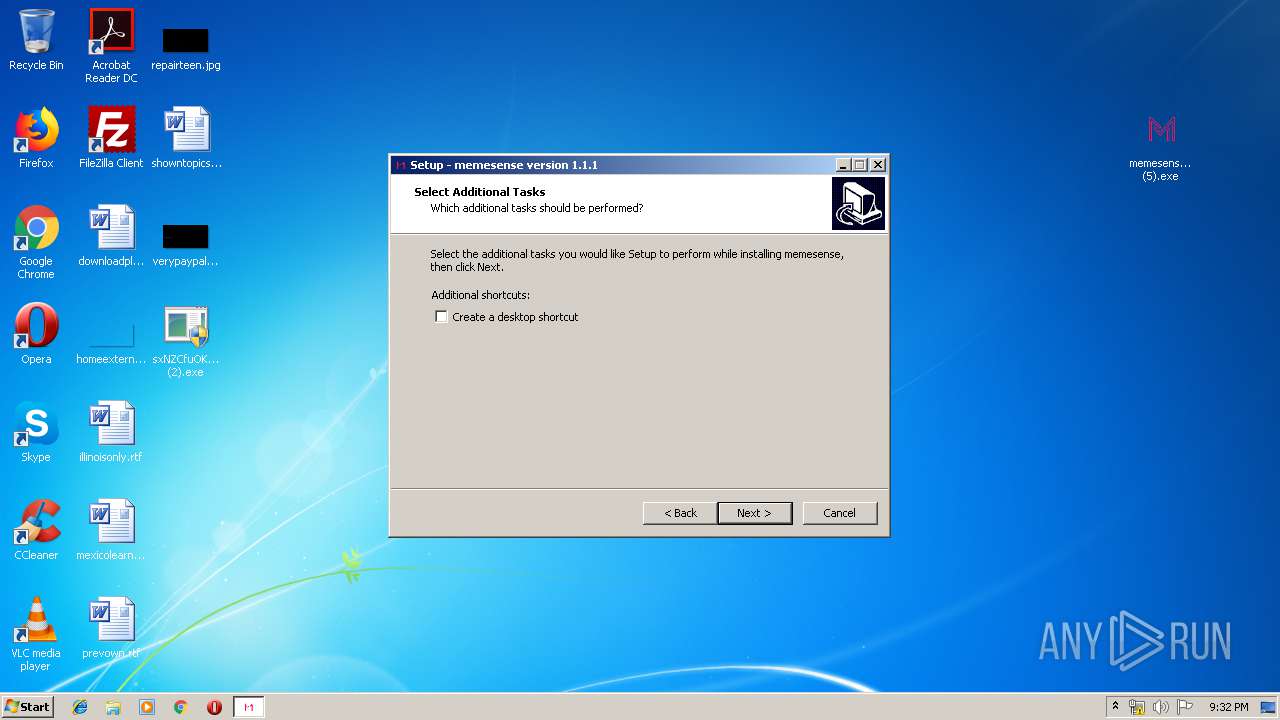
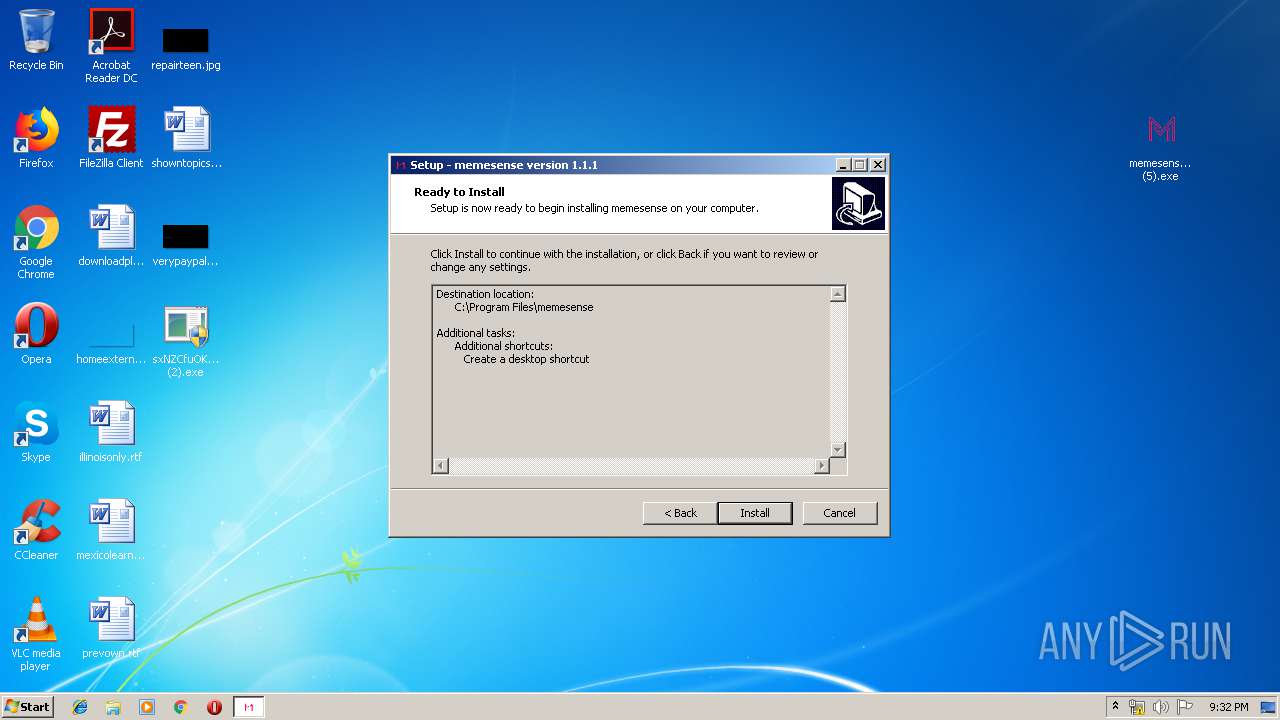
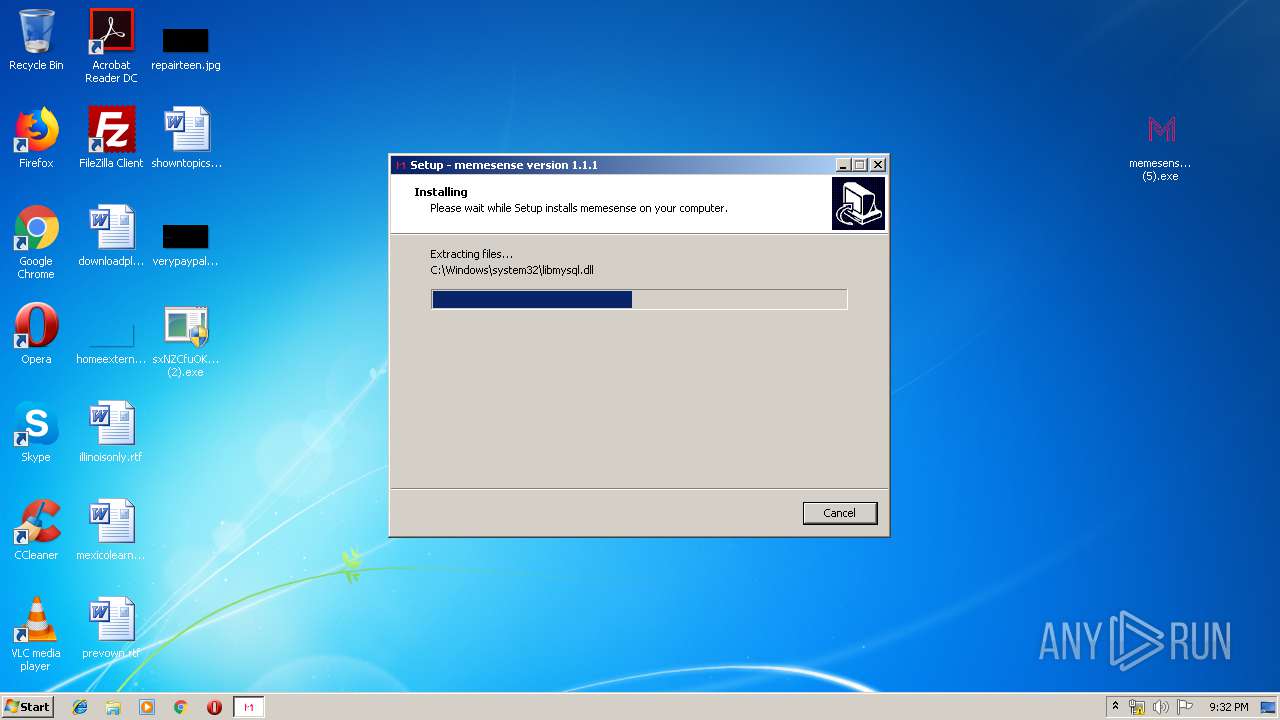
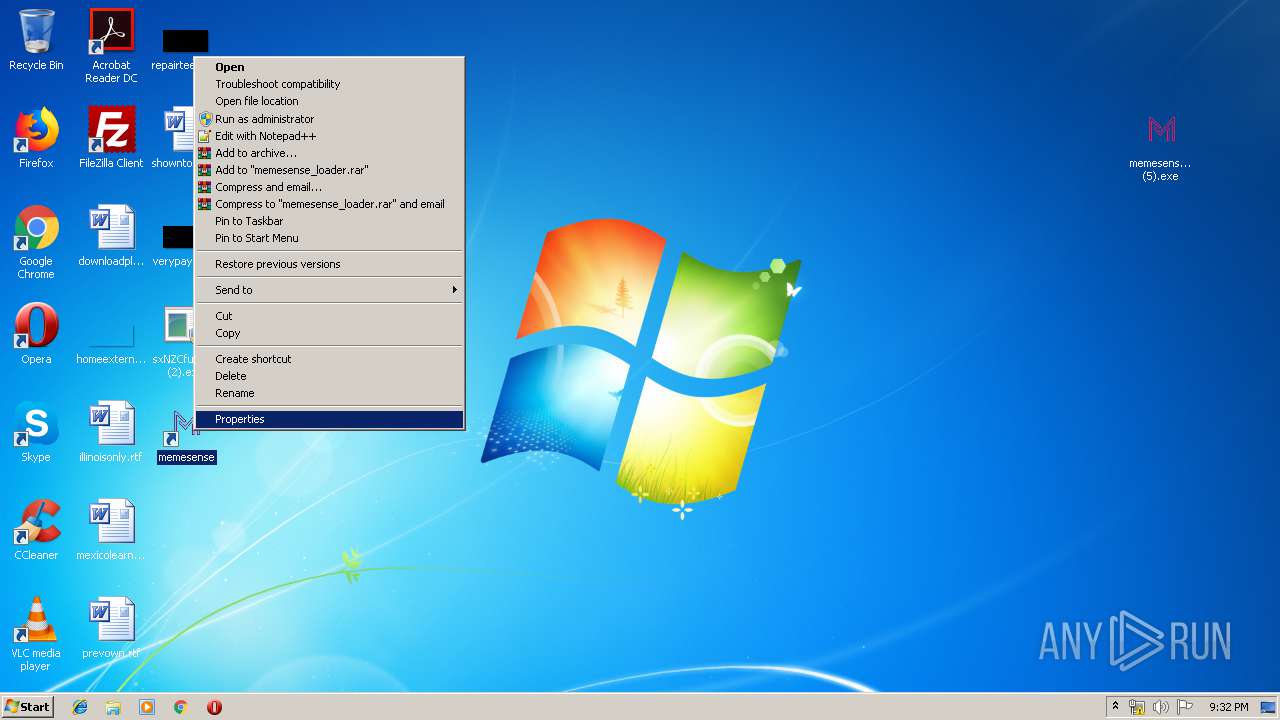
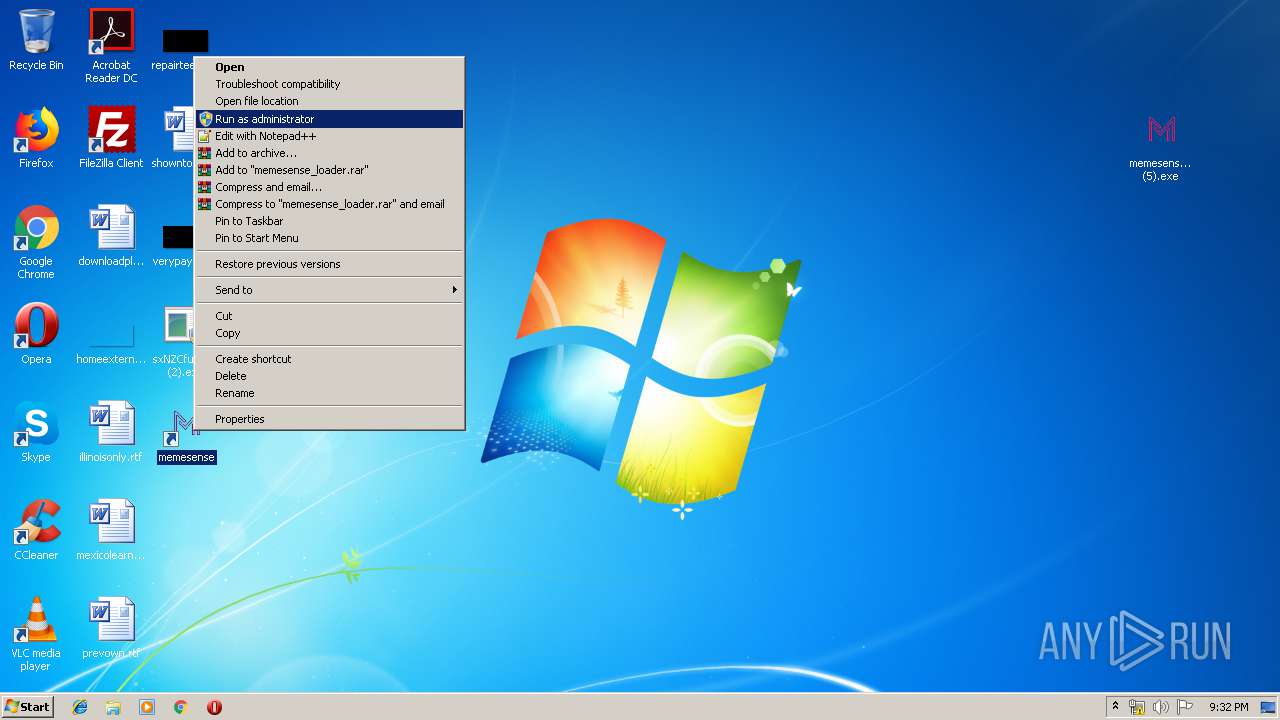
- memesense_setup (5).exe (PID: 2708)
- memesense_setup (5).exe (PID: 3392)
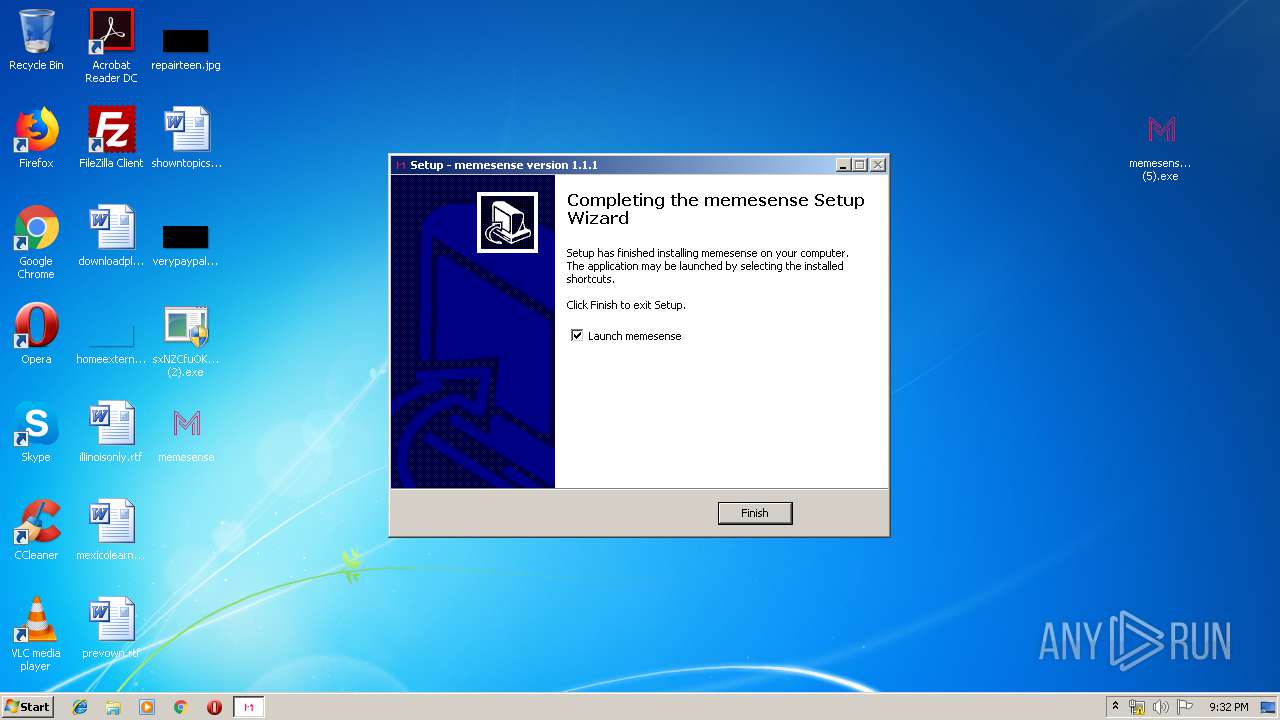
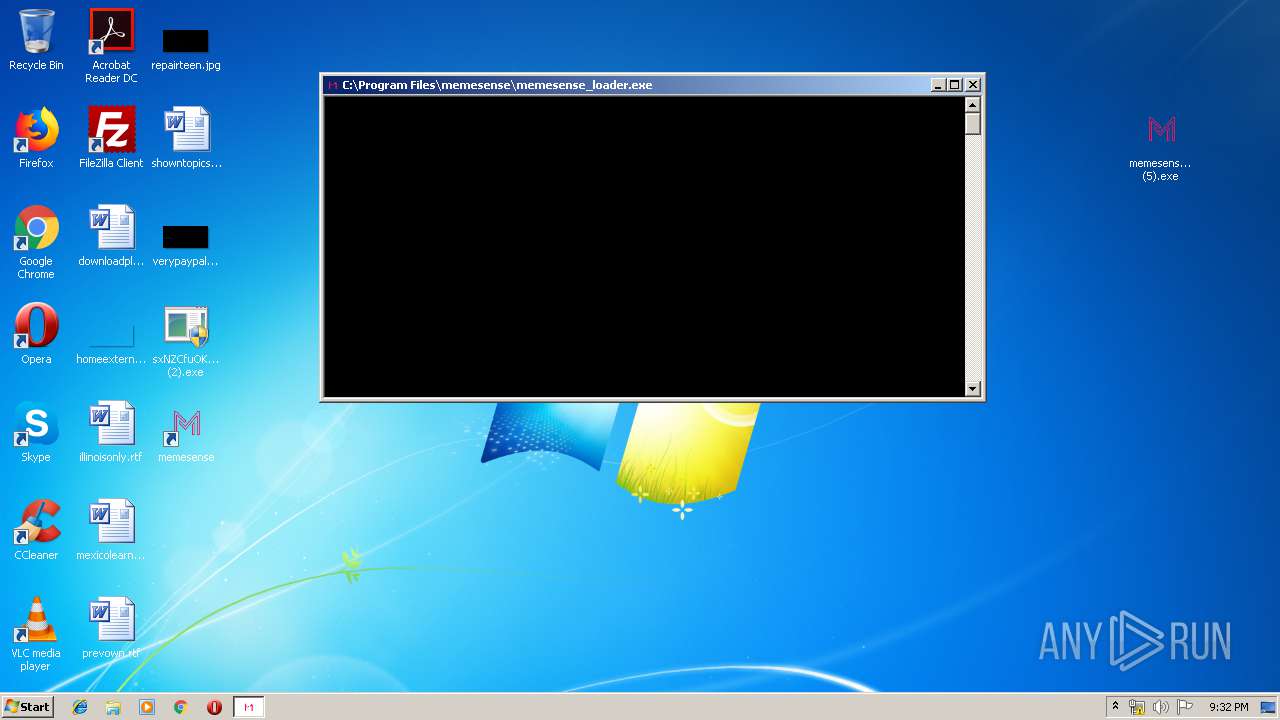
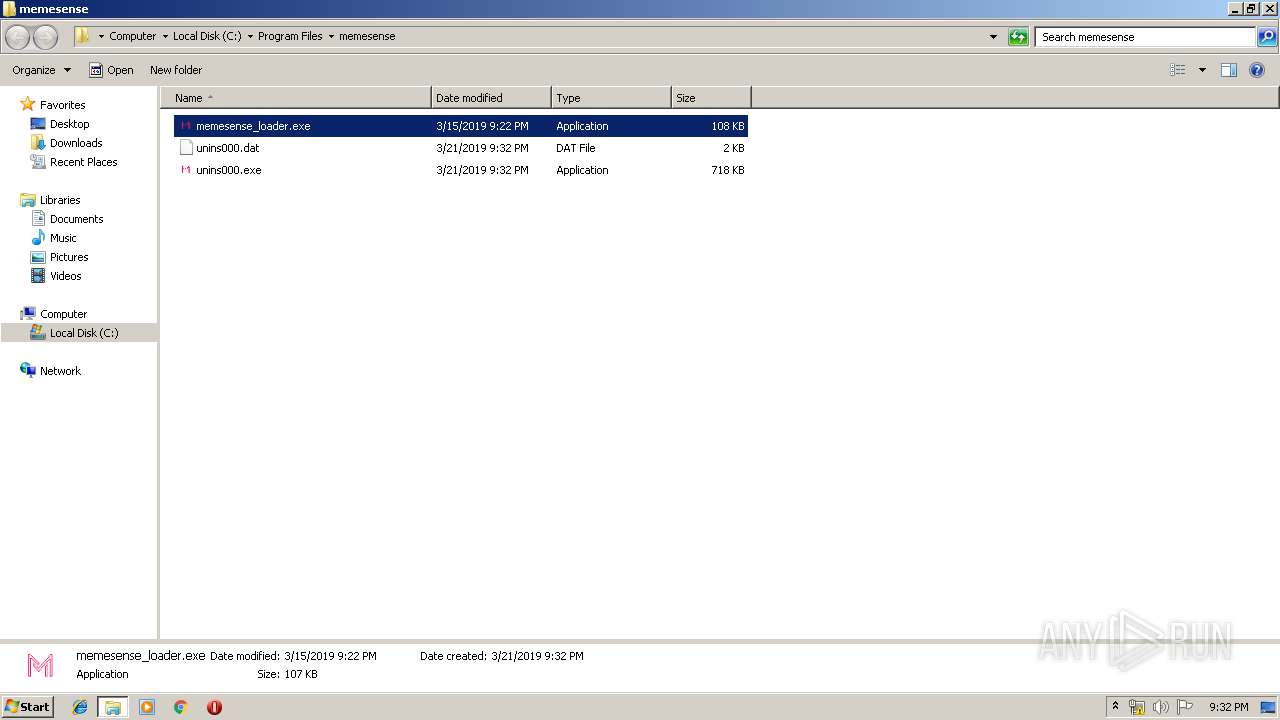
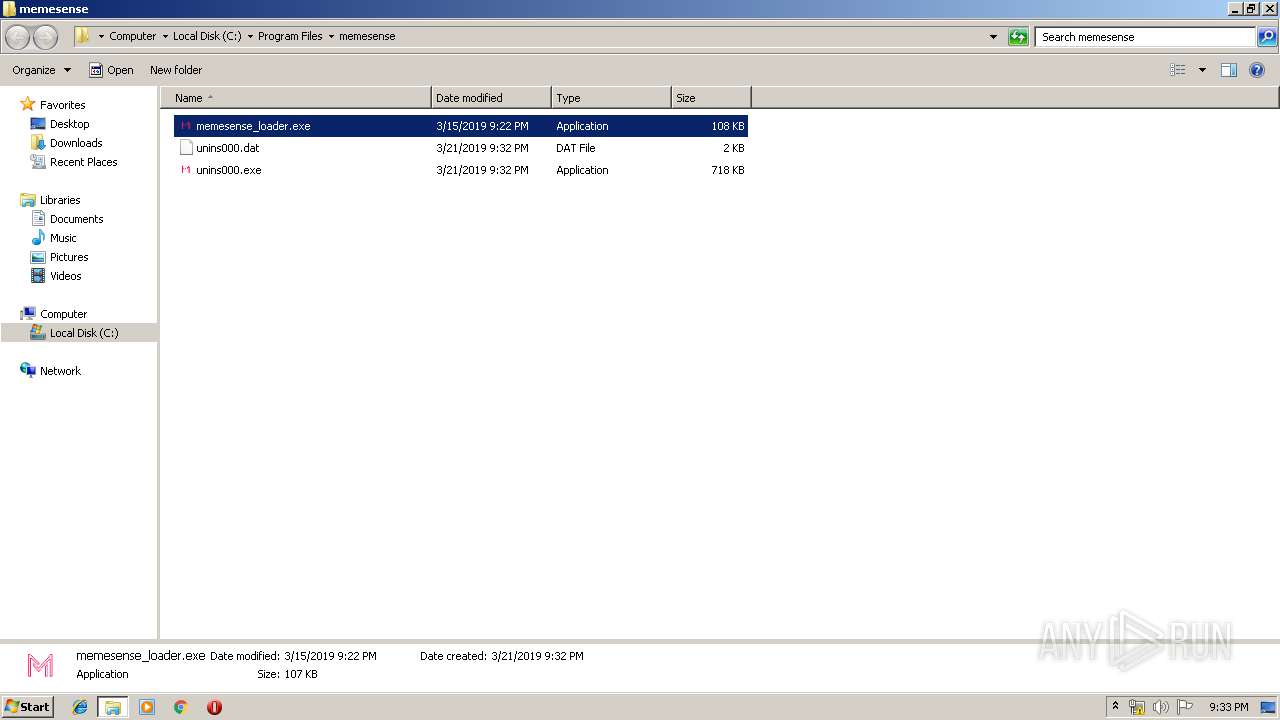
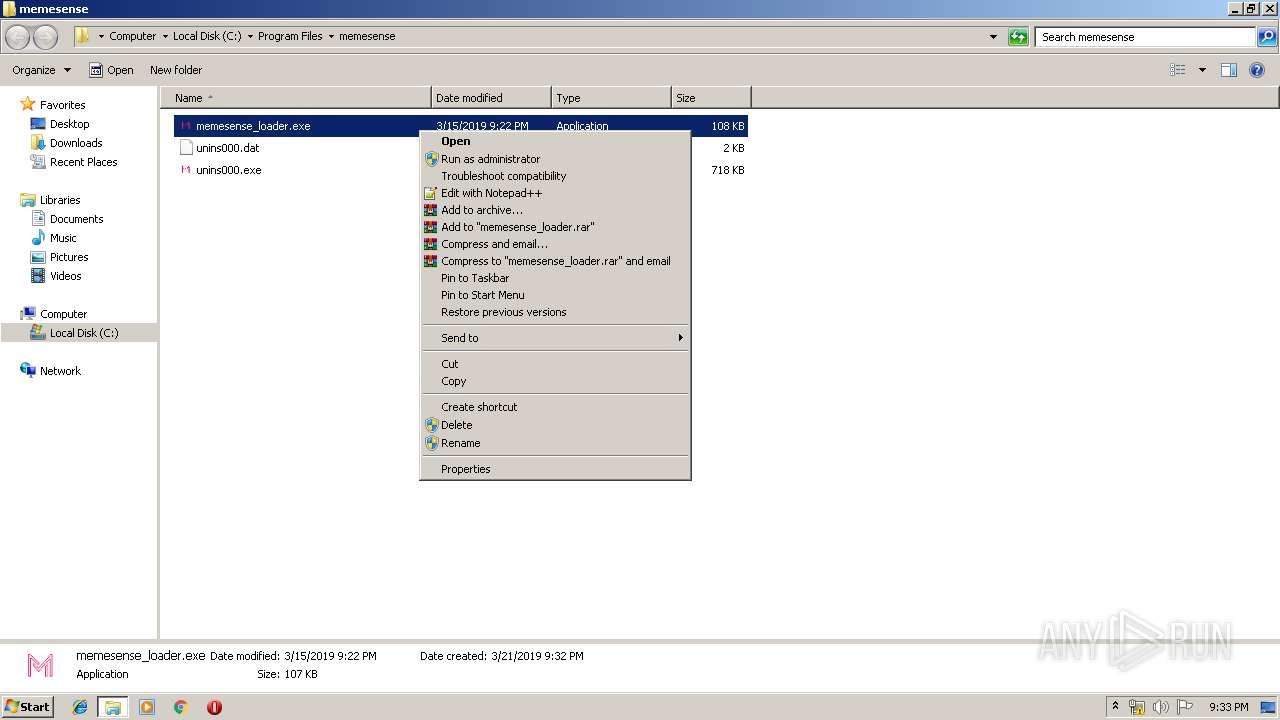
- memesense_loader.exe (PID: 1220)
- memesense_loader.exe (PID: 2304)
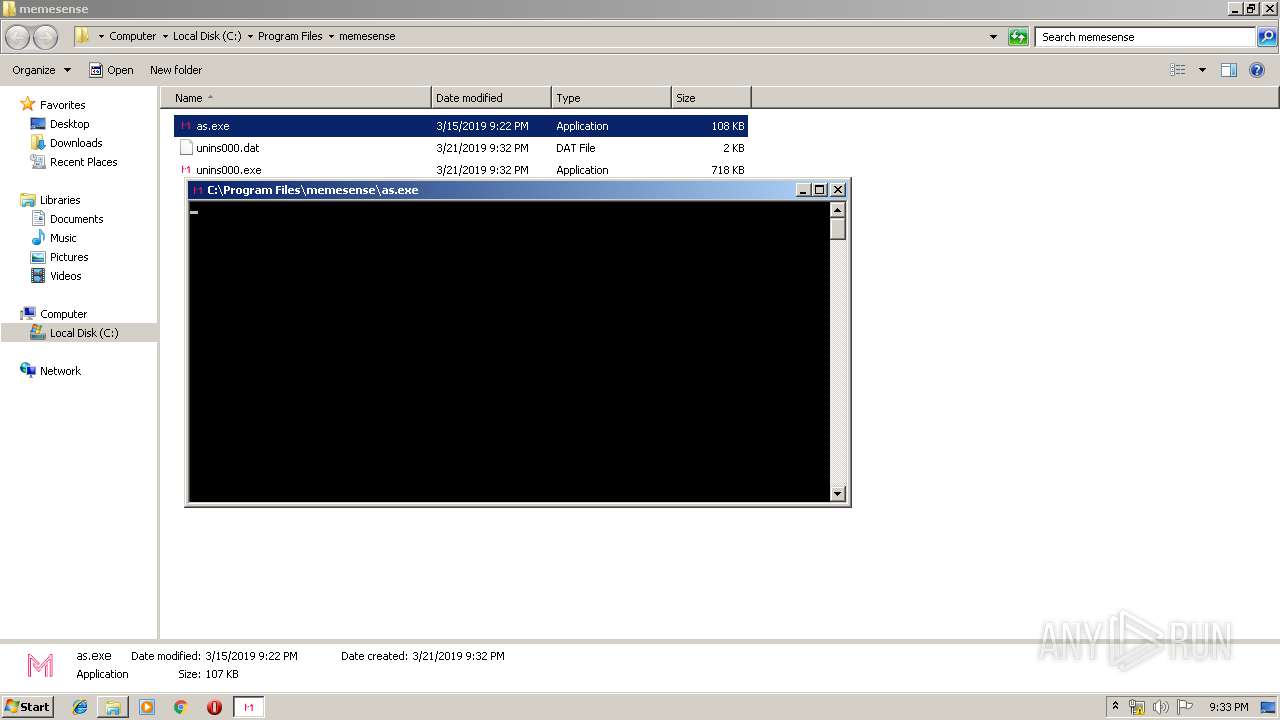
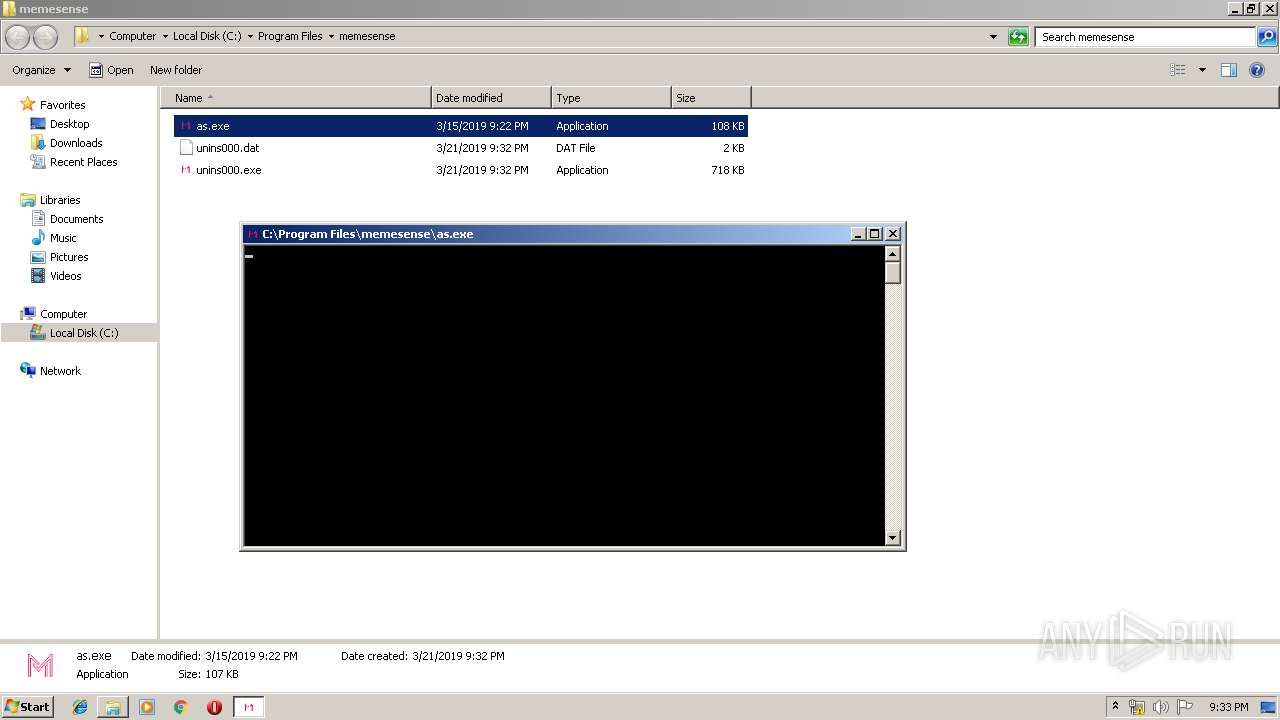
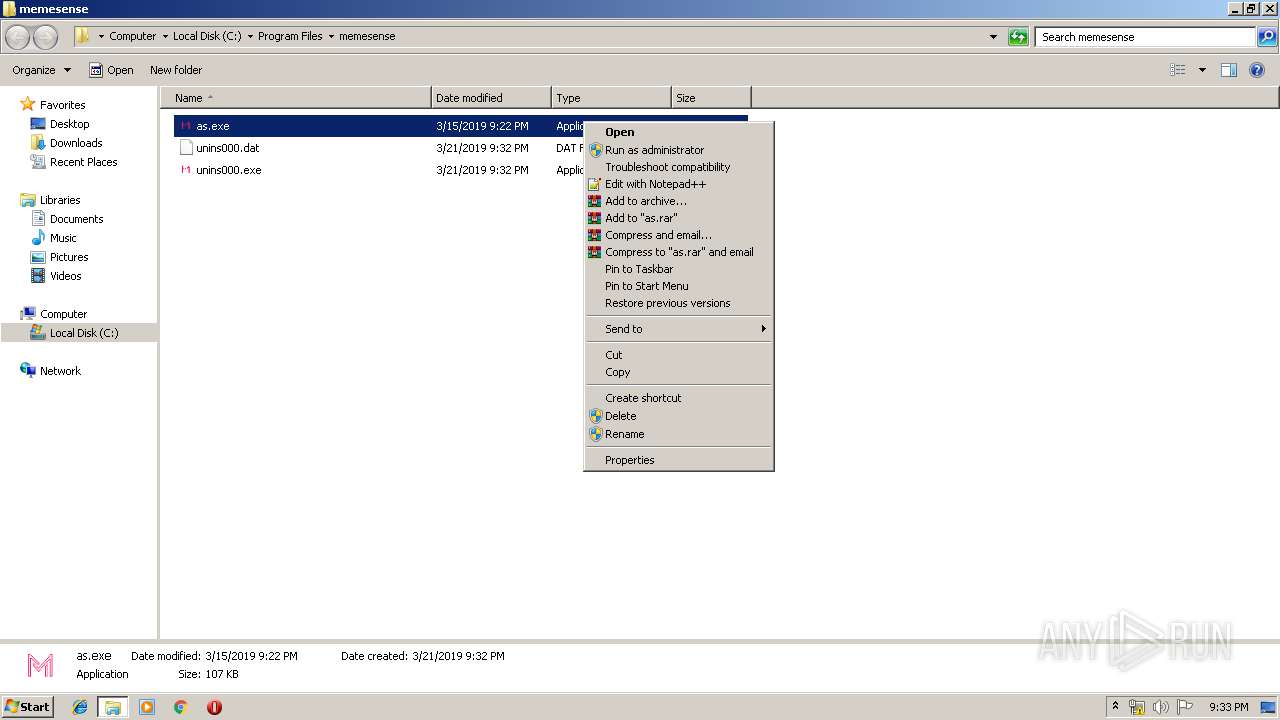
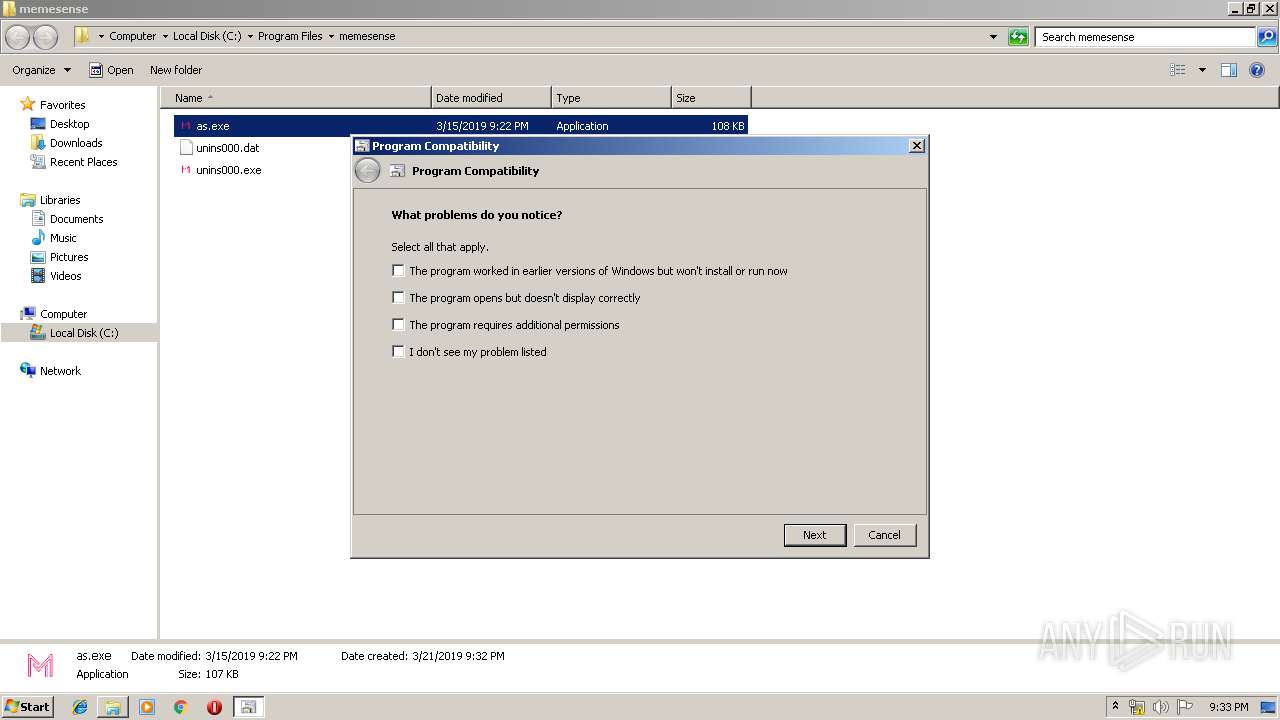
- as.exe (PID: 2464)
- as.exe (PID: 3120)
- as.exe (PID: 2316)
Changes settings of System certificates
- dxwsetup.exe (PID: 2092)
Loads dropped or rewritten executable
- dxwsetup.exe (PID: 2092)
- sxNZCfuOKyxLzoz (2).exe (PID: 3792)
- sxNZCfuOKyxLzoz (2).exe (PID: 2432)
- memesense_loader.exe (PID: 2304)
- memesense_loader.exe (PID: 1220)
- as.exe (PID: 2464)
- as.exe (PID: 2316)
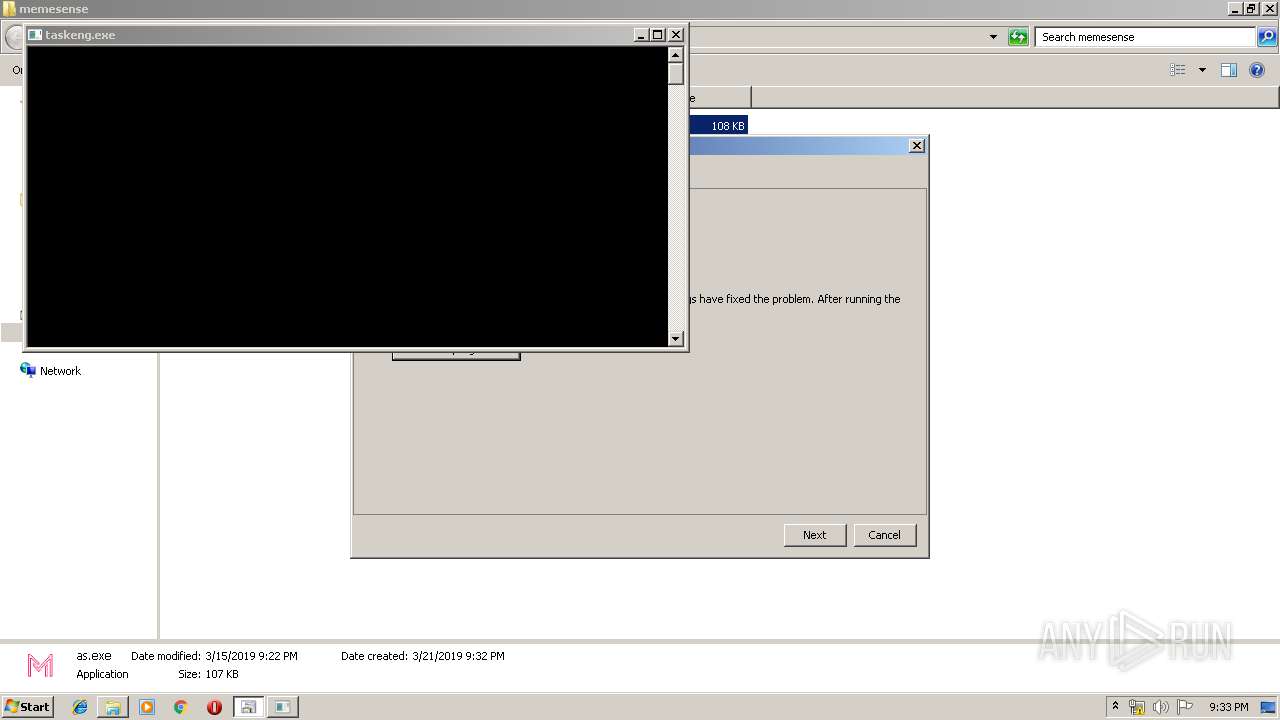
Loads the Task Scheduler COM API
- rundll32.exe (PID: 2068)
SUSPICIOUS
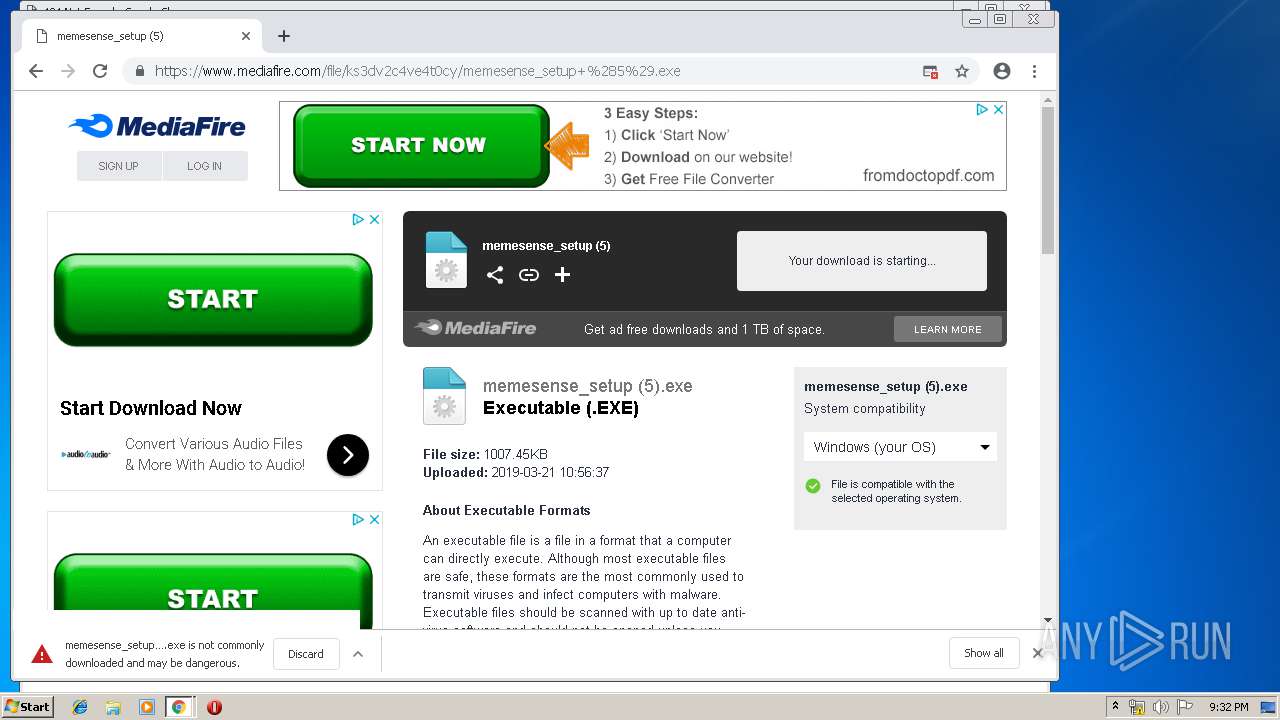
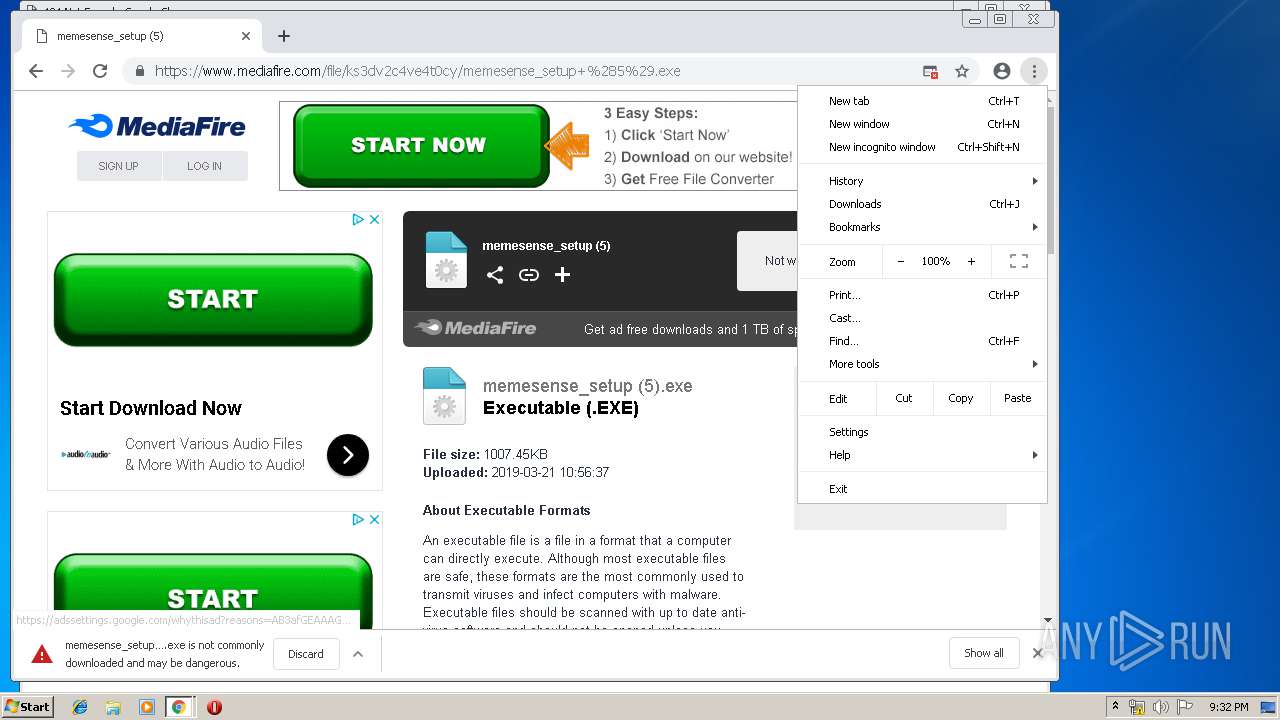
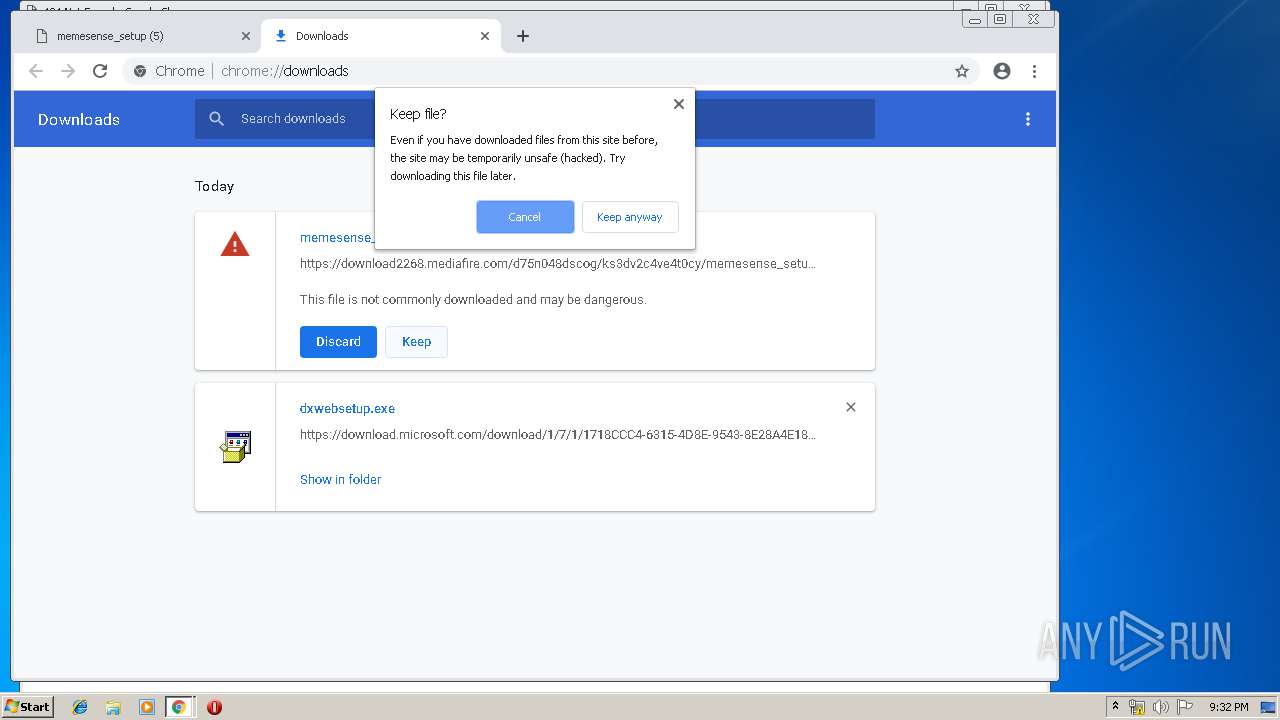
Executable content was dropped or overwritten
- chrome.exe (PID: 1684)
- chrome.exe (PID: 2260)
- dxwebsetup.exe (PID: 720)
- chrome.exe (PID: 3904)
- memesense_setup (5).exe (PID: 3392)
- dxwsetup.exe (PID: 2092)
- memesense_setup (5).exe (PID: 2708)
- memesense_setup (5).tmp (PID: 2508)
- DllHost.exe (PID: 3620)
- msdt.exe (PID: 2728)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1684)
Searches for installed software
- dxwsetup.exe (PID: 2092)
- DllHost.exe (PID: 1756)
Adds / modifies Windows certificates
- dxwsetup.exe (PID: 2092)
Creates COM task schedule object
- dxwsetup.exe (PID: 2092)
Creates files in the Windows directory
- memesense_setup (5).tmp (PID: 2508)
- dxwsetup.exe (PID: 2092)
Removes files from Windows directory
- dxwsetup.exe (PID: 2092)
Uses RUNDLL32.EXE to load library
- msdt.exe (PID: 2728)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 2260)
- dxwsetup.exe (PID: 2092)
Application launched itself
- chrome.exe (PID: 1684)
- chrome.exe (PID: 3904)
Low-level read access rights to disk partition
- vssvc.exe (PID: 1480)
Changes settings of System certificates
- chrome.exe (PID: 1524)
Creates files in the user directory
- chrome.exe (PID: 3904)
Creates files in the program directory
- memesense_setup (5).tmp (PID: 2508)
Application was dropped or rewritten from another process
- memesense_setup (5).tmp (PID: 2508)
- memesense_setup (5).tmp (PID: 1868)
Creates a software uninstall entry
- memesense_setup (5).tmp (PID: 2508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:03:20 23:02:20+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 1347072 |
| InitializedDataSize: | 763904 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x756233 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
140
Monitored processes
78
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESC1FC.tmp" "c:\Users\admin\AppData\Local\Temp\CSCC1FB.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
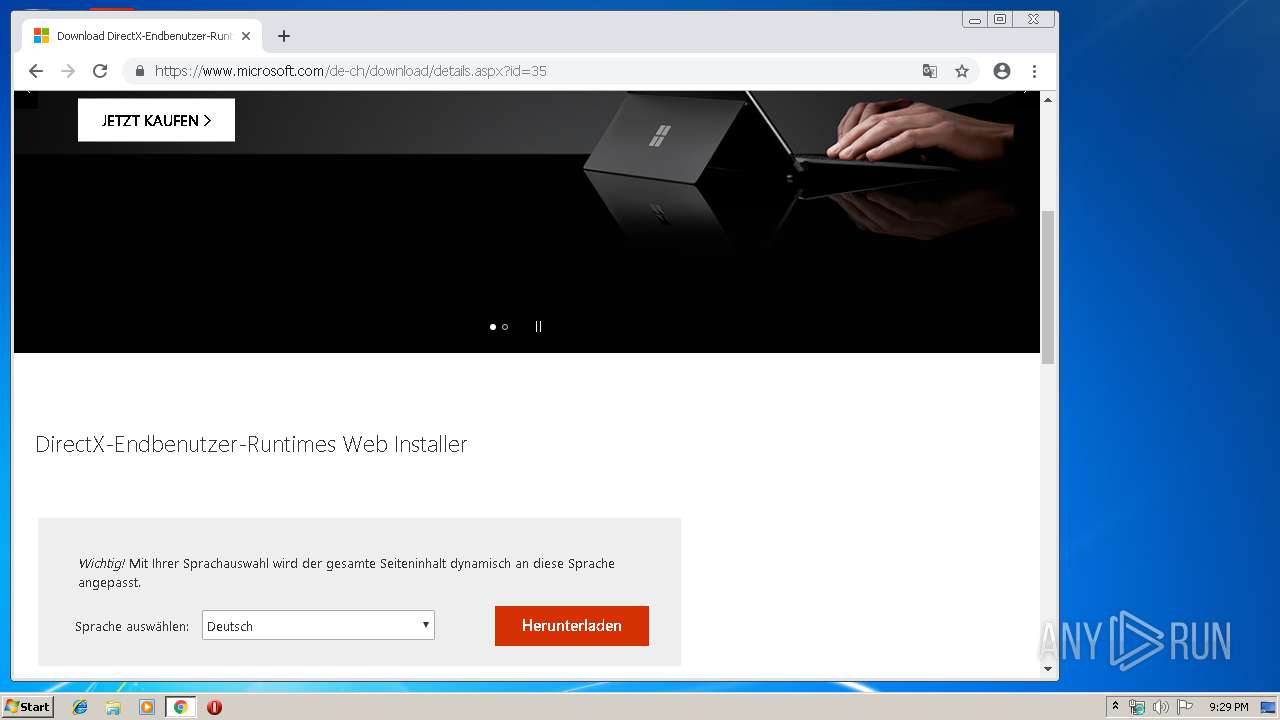
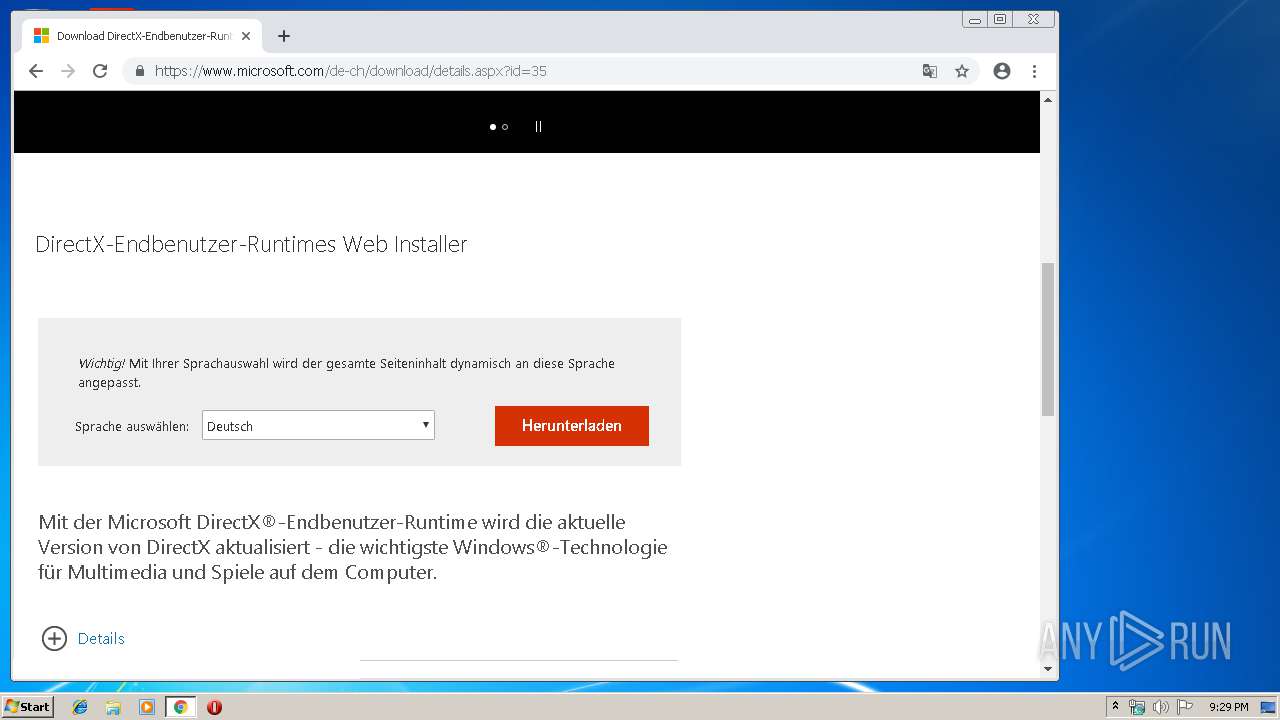
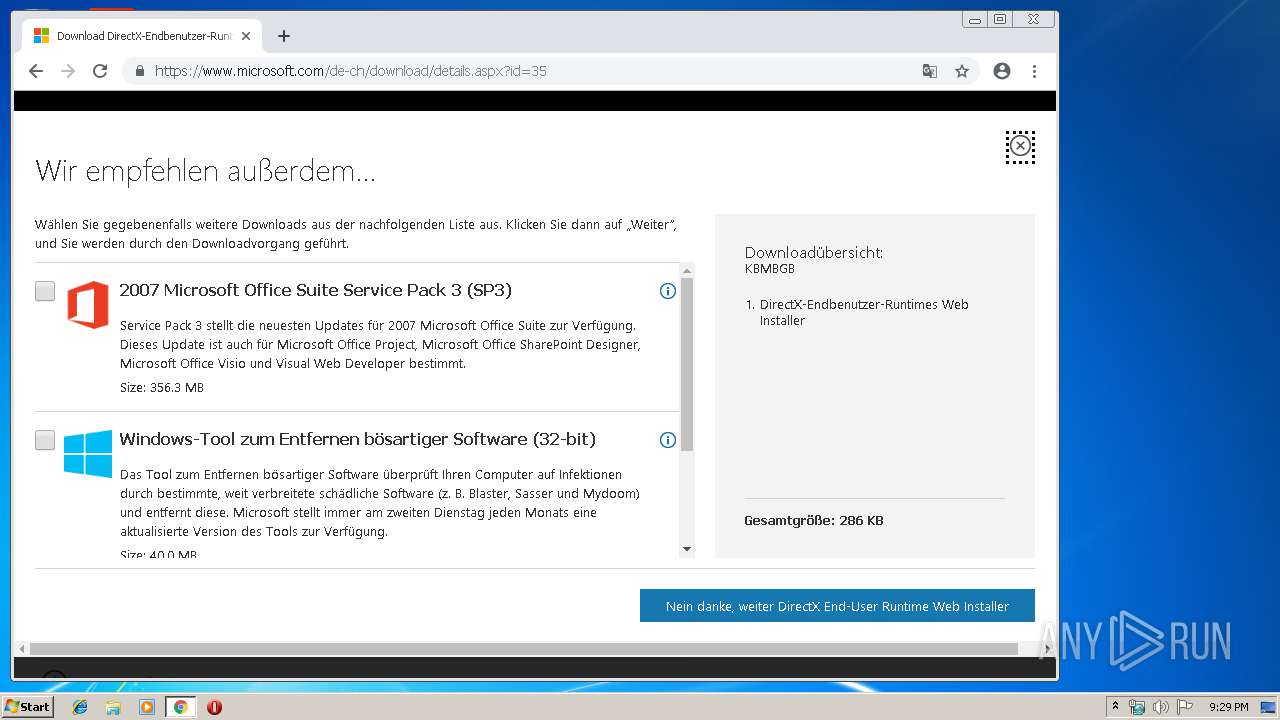
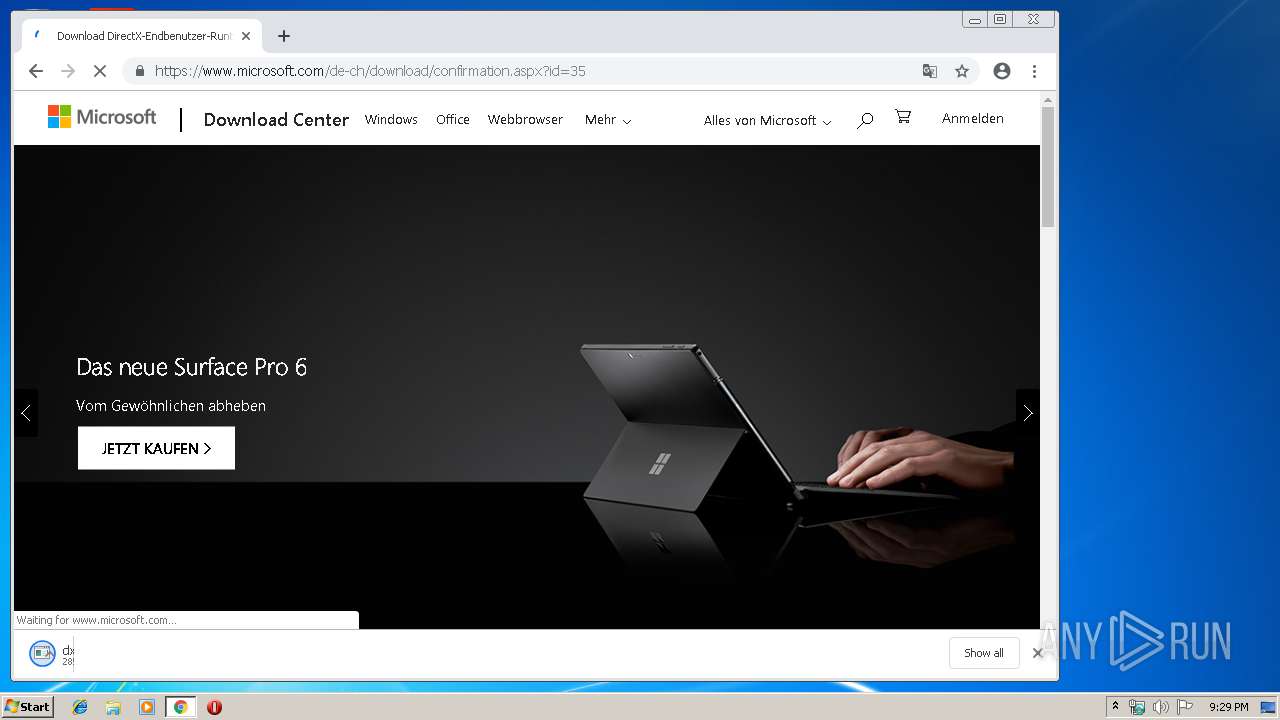
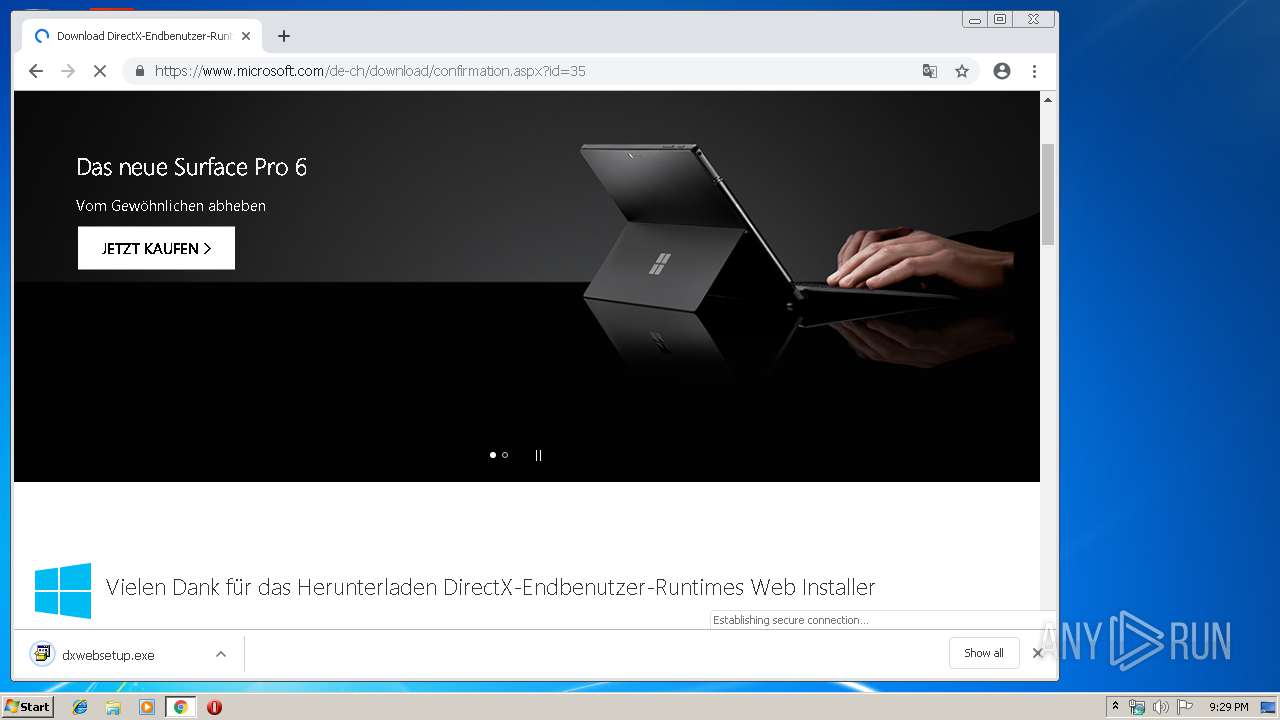
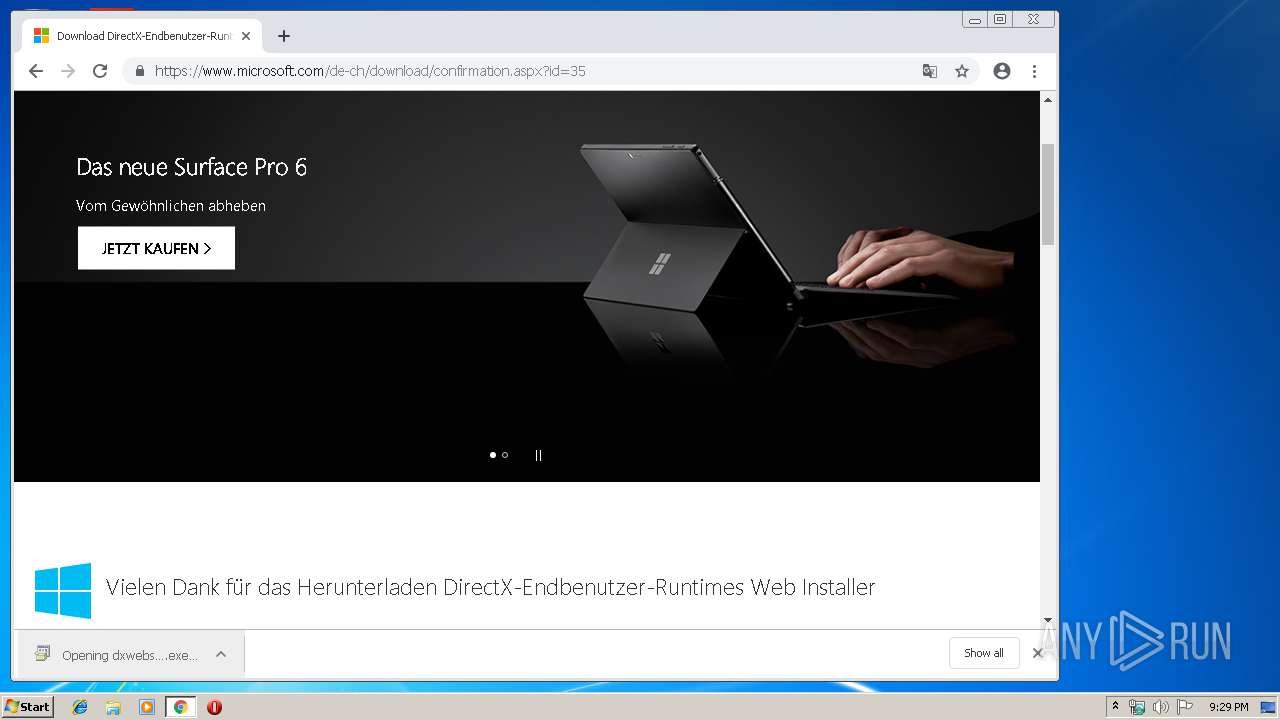
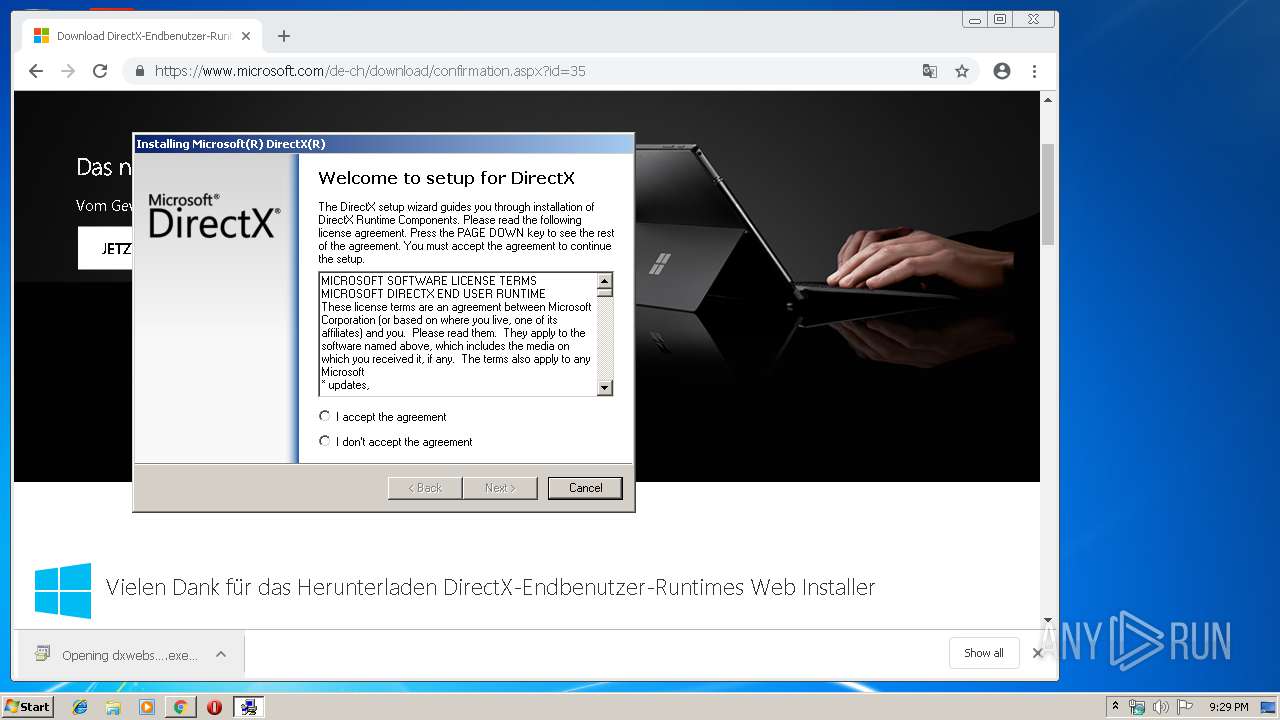
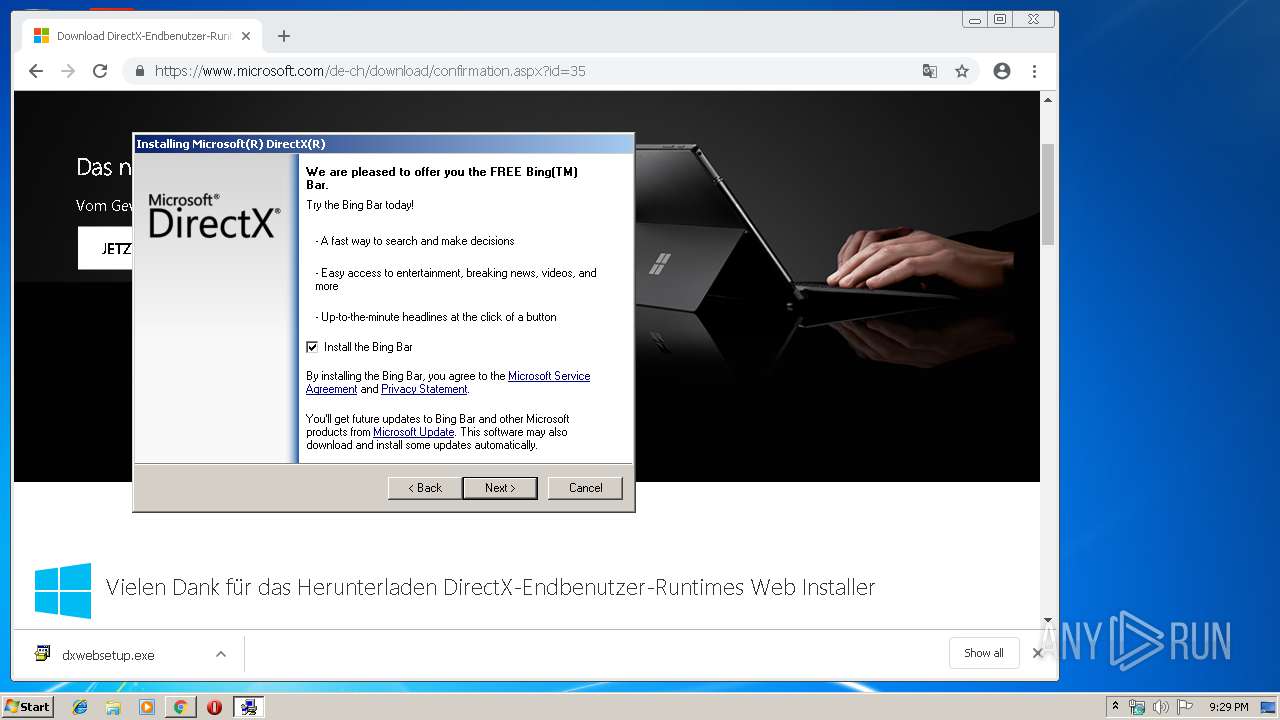
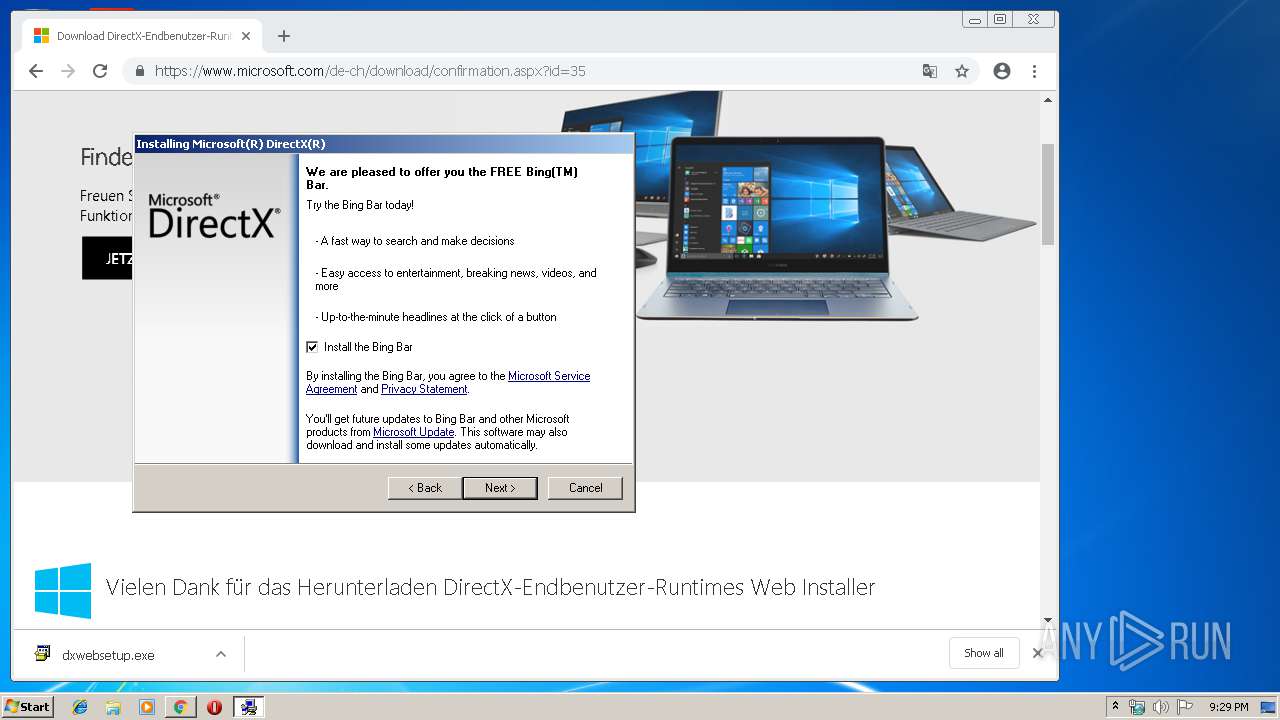
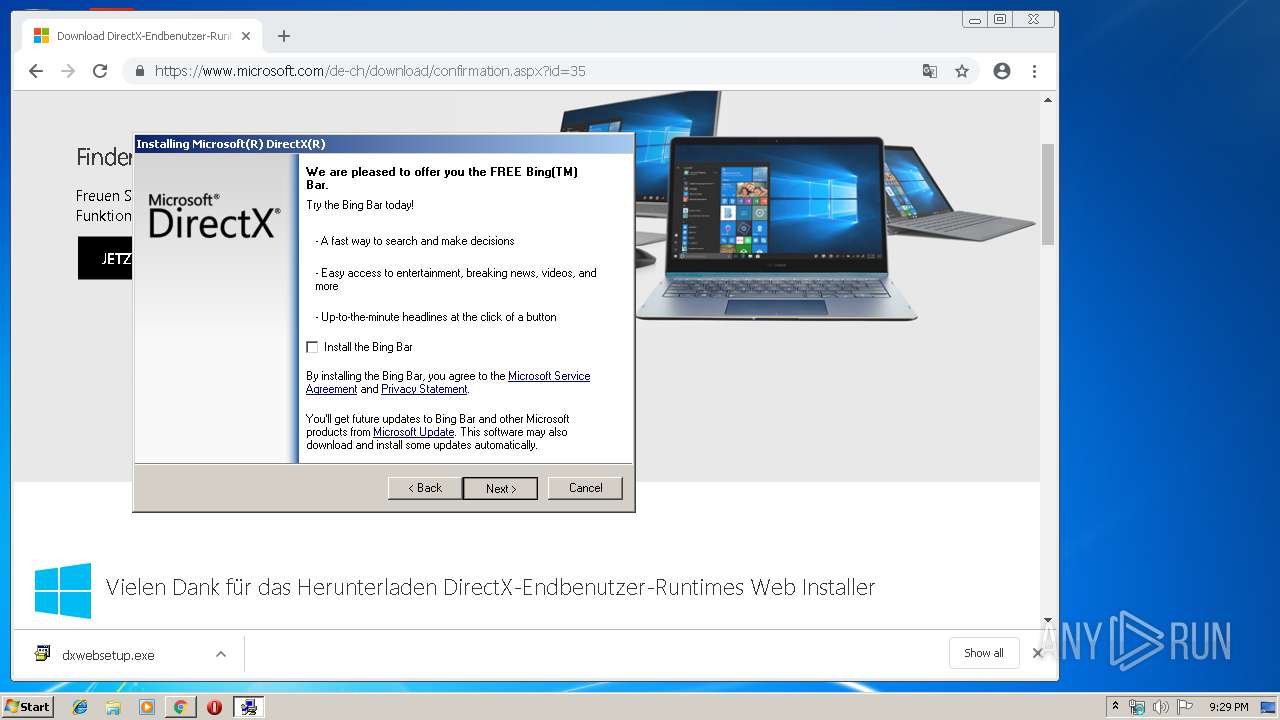
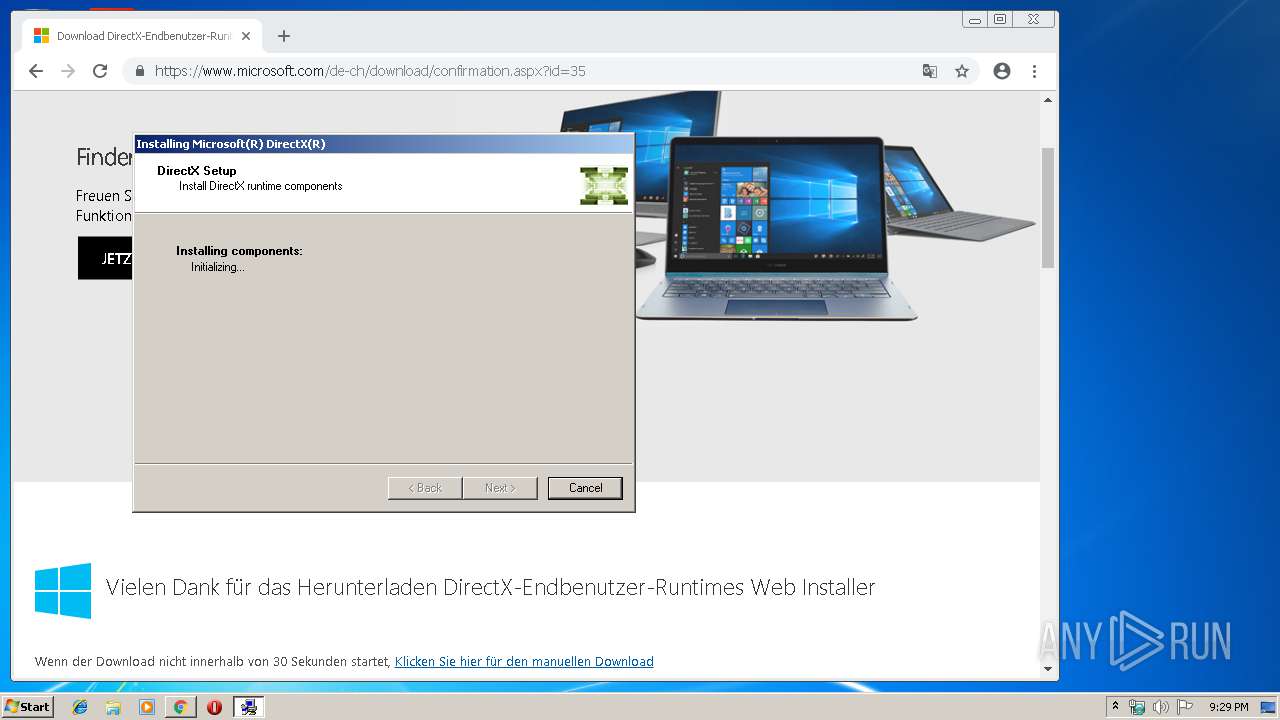
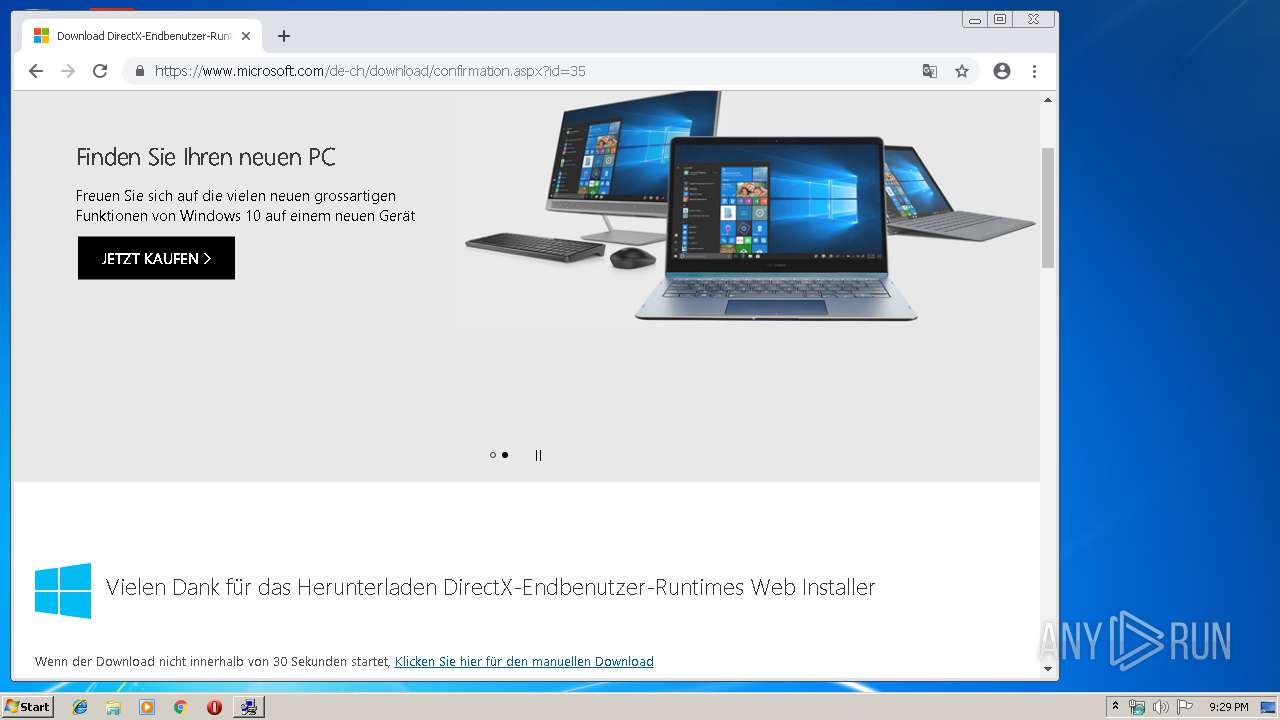
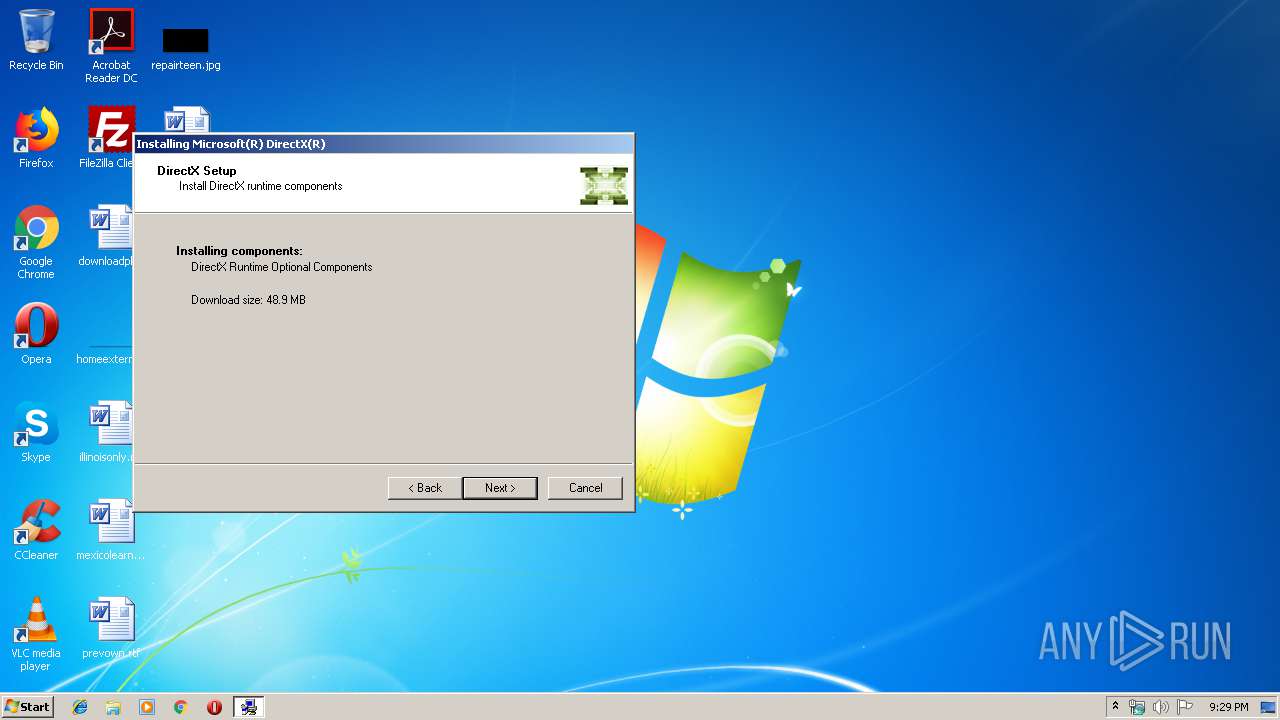
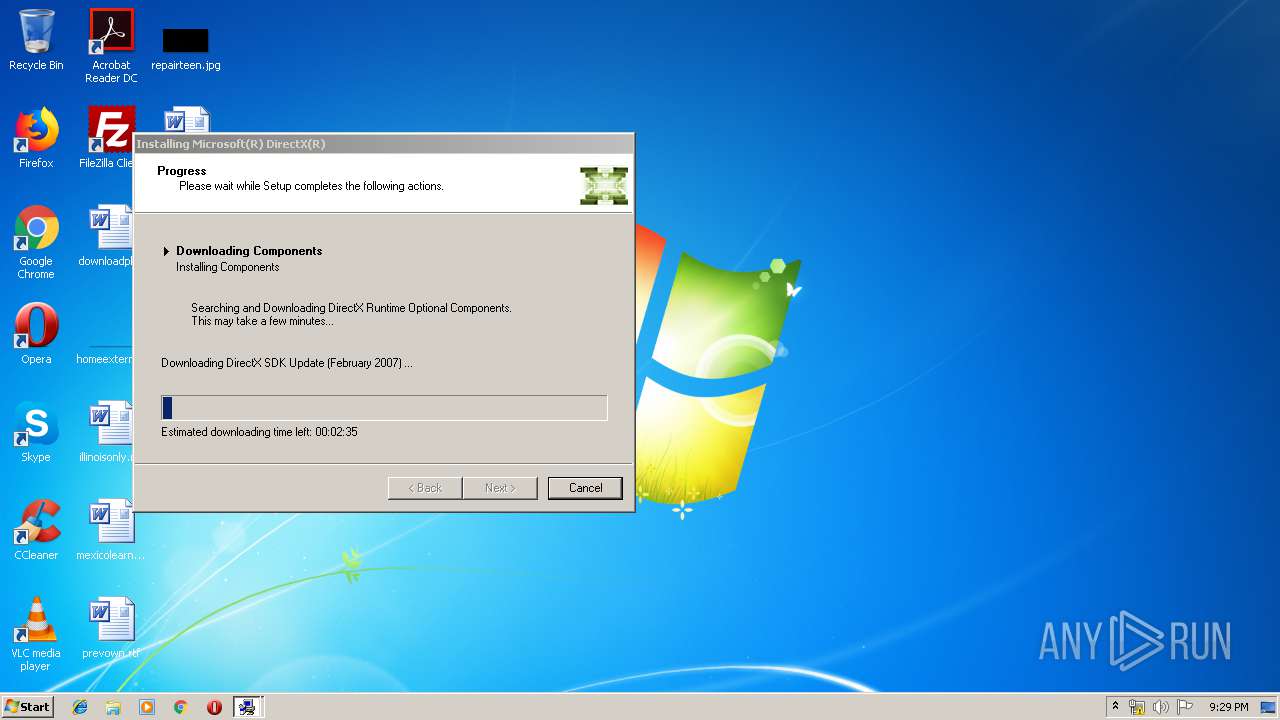
| 720 | "C:\Users\admin\Downloads\dxwebsetup.exe" | C:\Users\admin\Downloads\dxwebsetup.exe | chrome.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DirectX 9.0 Web setup Exit code: 2852126720 Version: 9.29.1974.0 Modules
| |||||||||||||||
| 908 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\-hngx3qb.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,9535763313075790965,13948685128655607372,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=12155567273667336300 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12155567273667336300 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=888 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
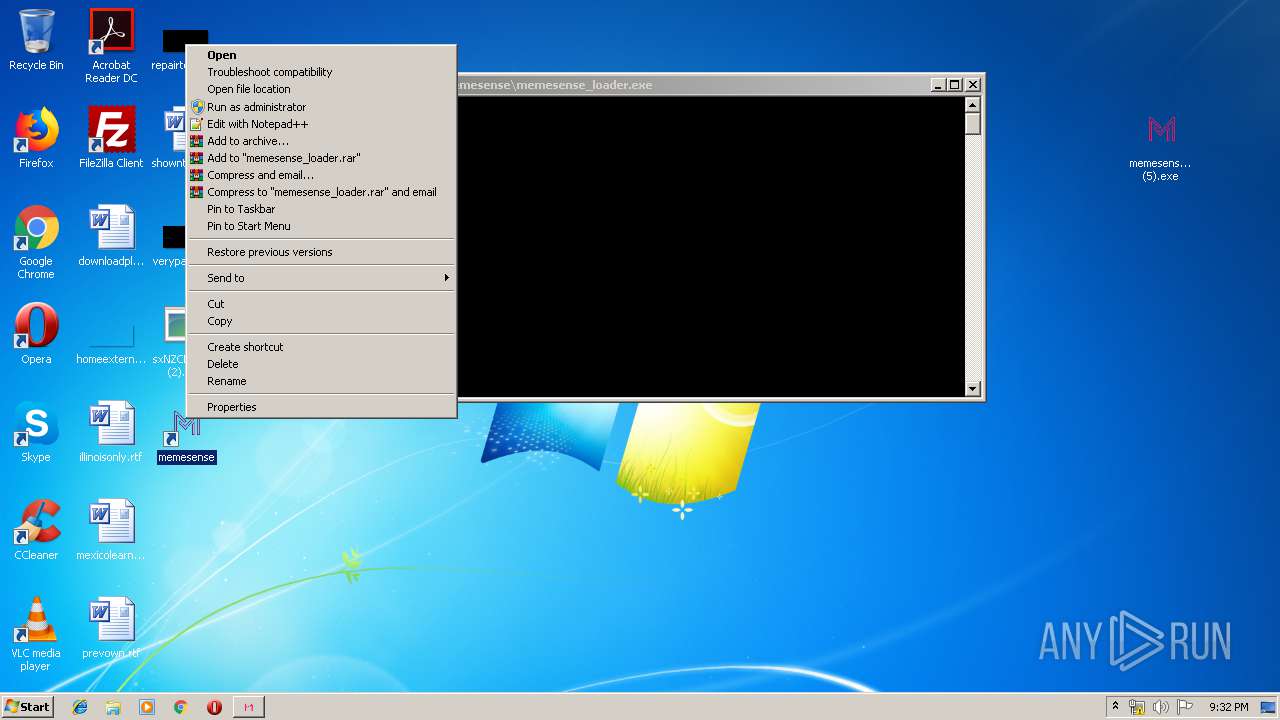
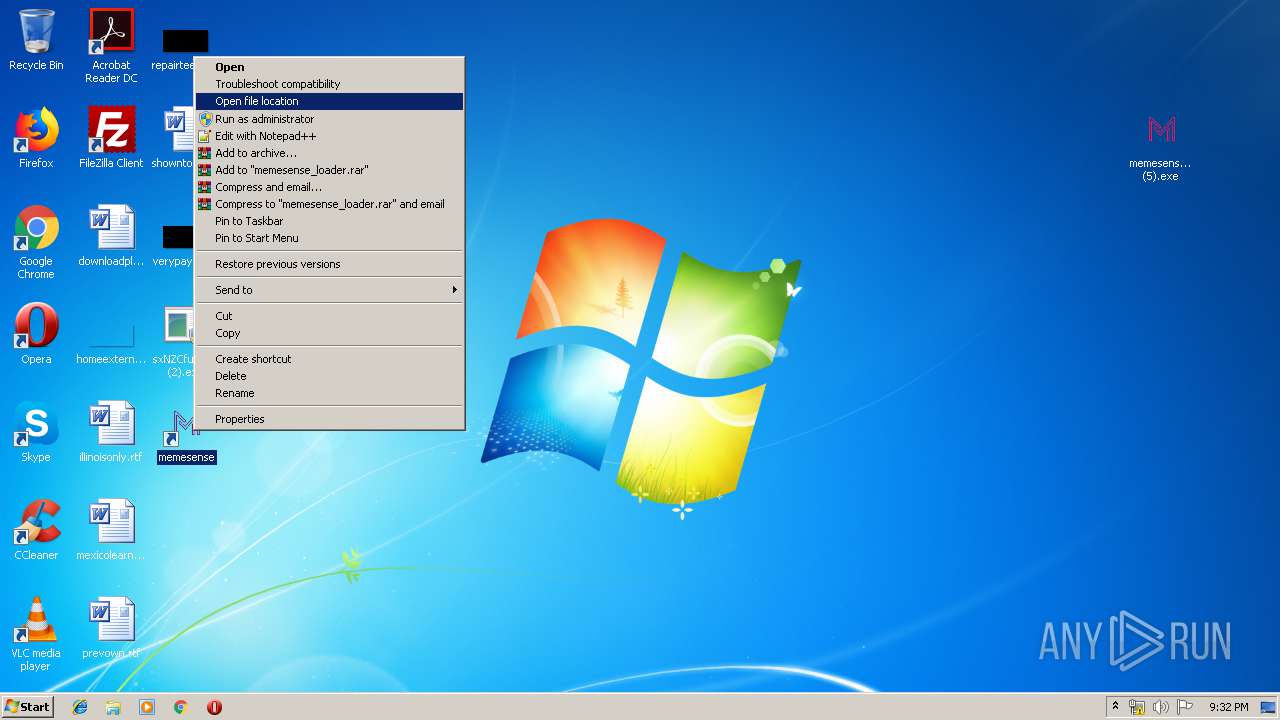
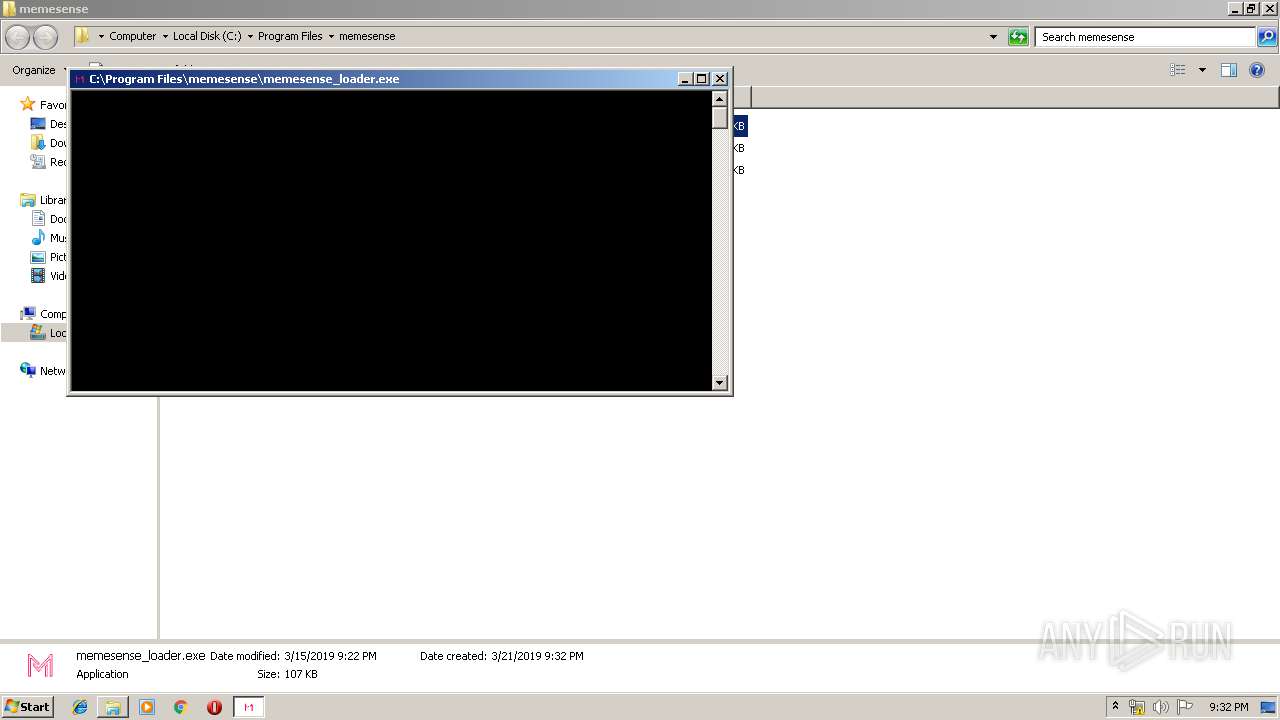
| 1220 | "C:\Program Files\memesense\memesense_loader.exe" | C:\Program Files\memesense\memesense_loader.exe | — | memesense_setup (5).tmp | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225786 Modules
| |||||||||||||||
| 1348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,9535763313075790965,13948685128655607372,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=12414455642310638799 --mojo-platform-channel-handle=944 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
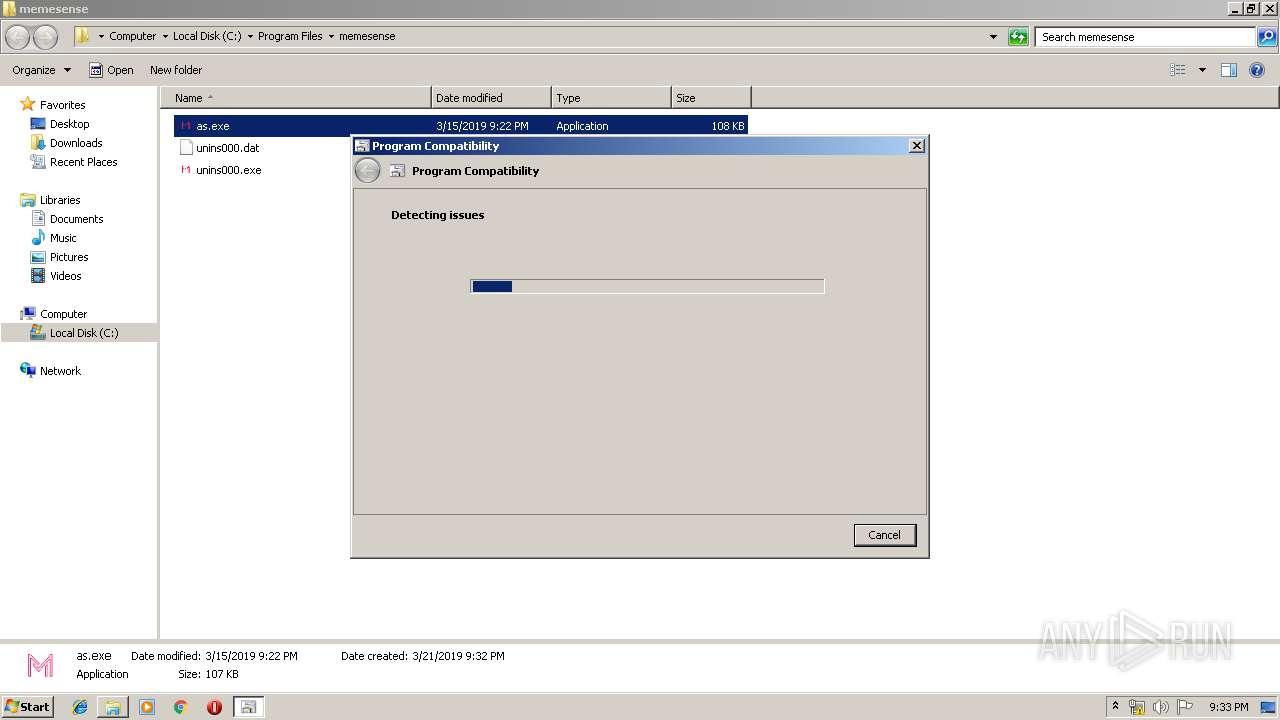
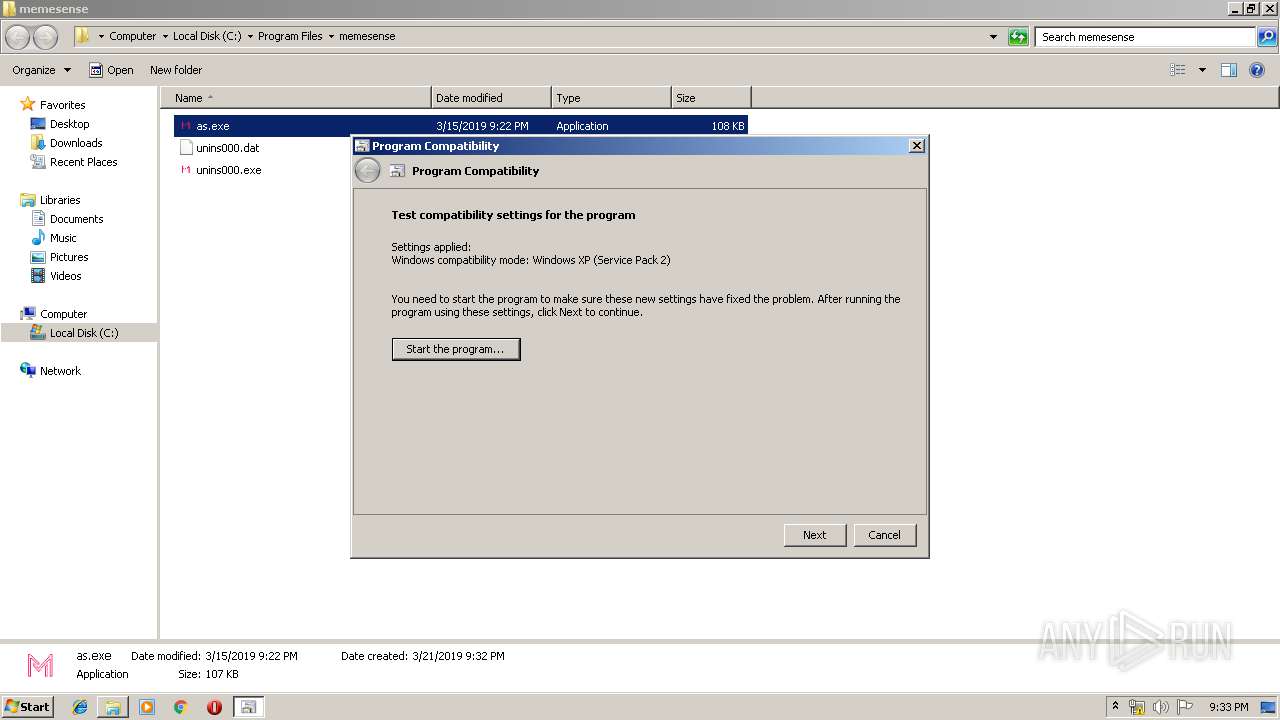
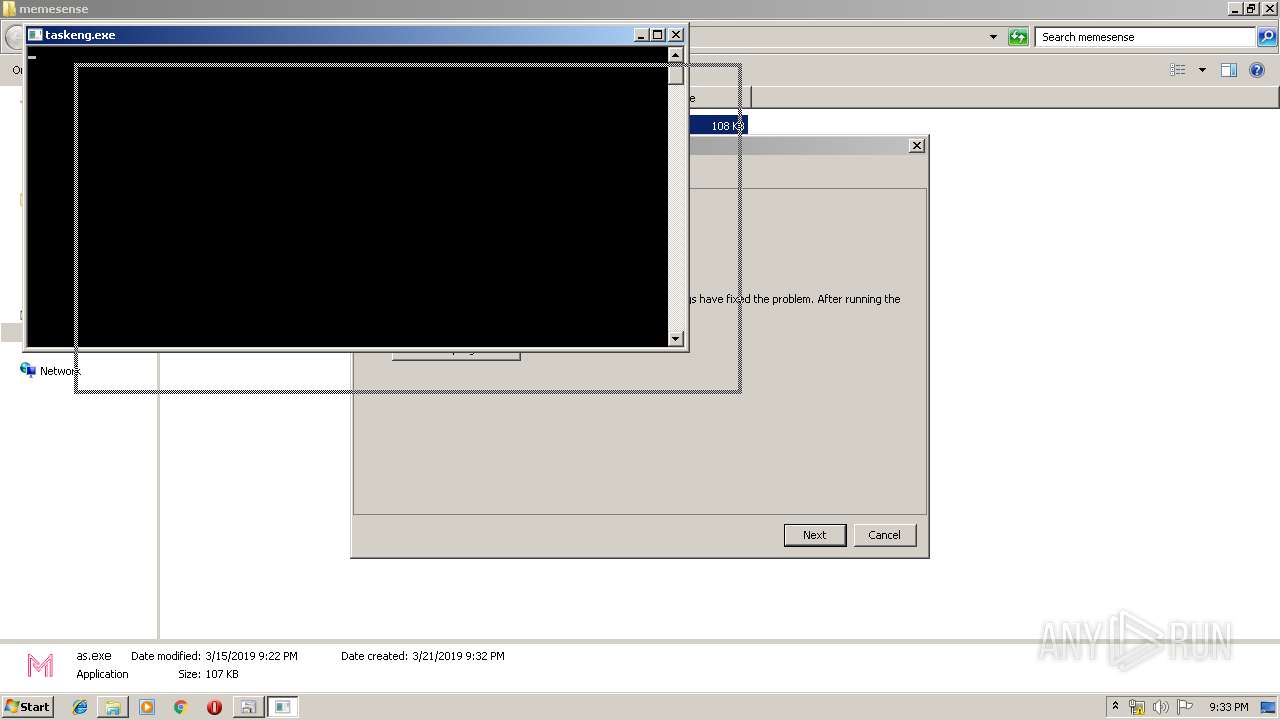
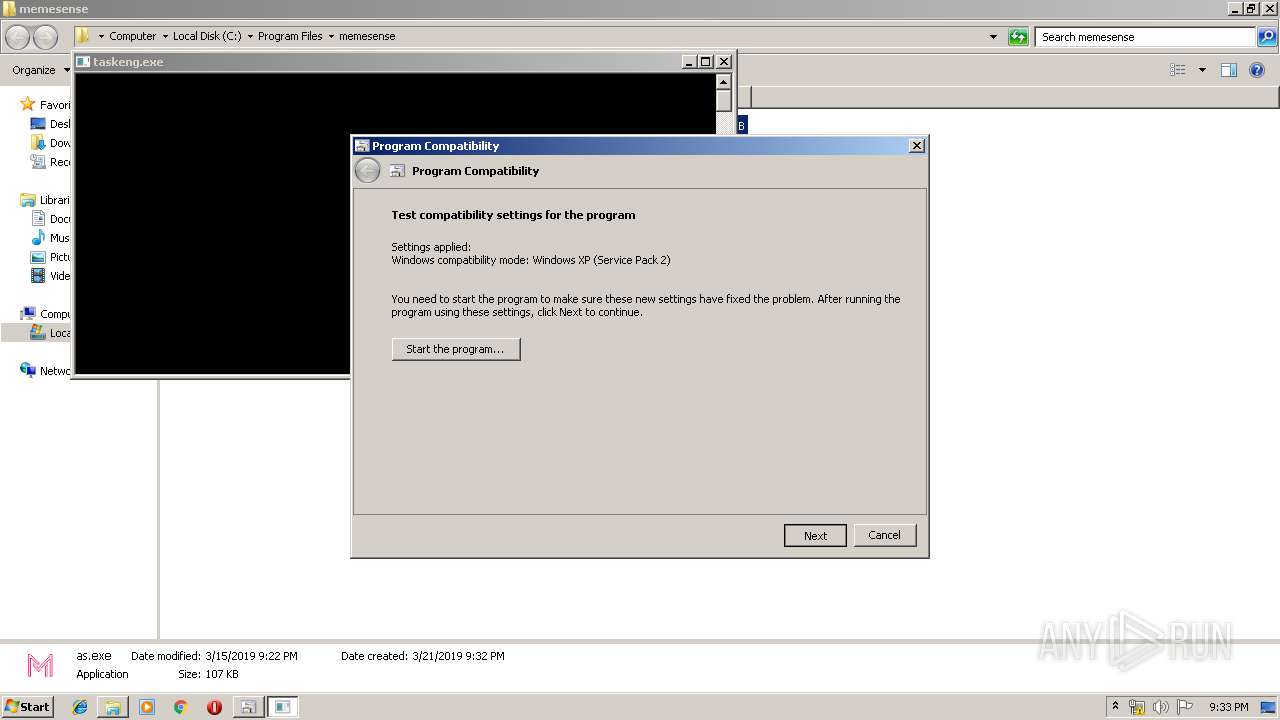
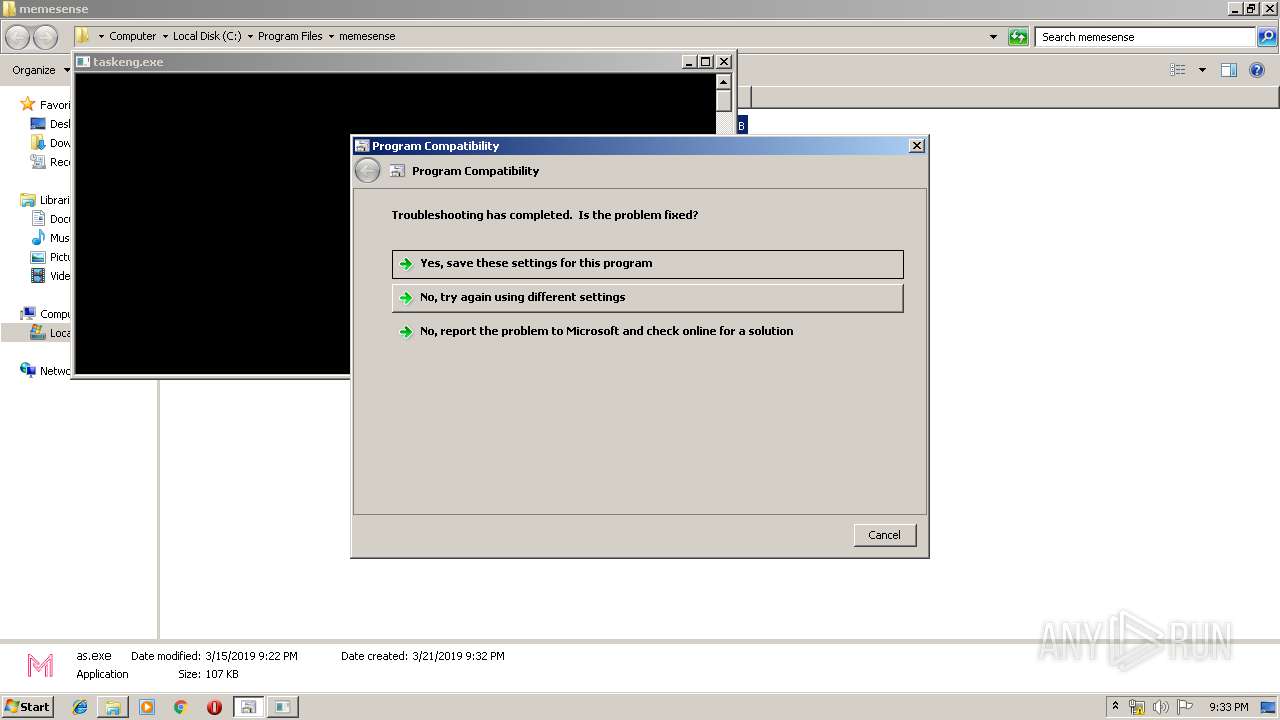
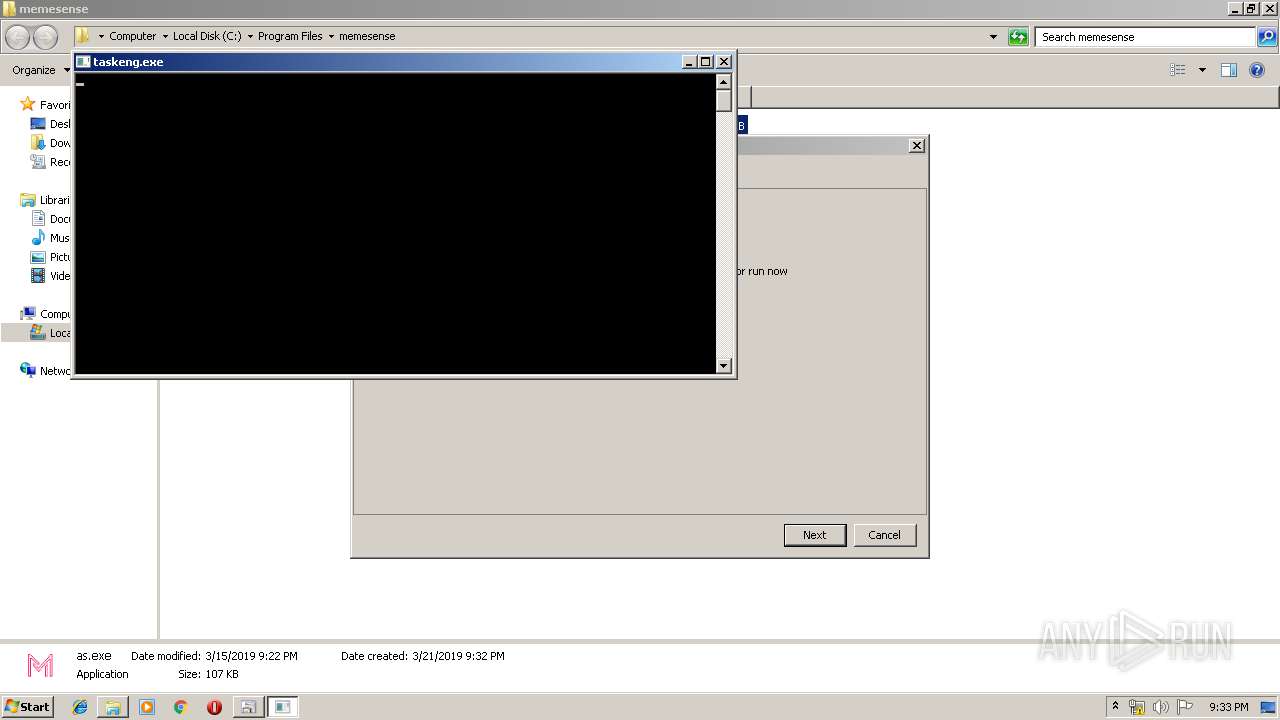
| 1472 | C:\Windows\system32\pcwrun.exe "C:\Program Files\memesense\as.exe" | C:\Windows\system32\pcwrun.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Program Compatibility Troubleshooter Invoker Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1480 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,9535763313075790965,13948685128655607372,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=10566554096798958936 --mojo-platform-channel-handle=1516 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=968,9535763313075790965,13948685128655607372,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7159091141021446793 --mojo-platform-channel-handle=3424 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
2 693
Read events
1 982
Write events
694
Delete events
17
Modification events
| (PID) Process: | (1684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (1684) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1684-13197677337075375 |
Value: 259 | |||
Executable files
132
Suspicious files
347
Text files
1 495
Unknown types
105
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 1684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 1684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\01137bab-ba93-4d3e-ad16-235561cc4fe2.tmp | — | |
MD5:— | SHA256:— | |||
| 1684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
98
TCP/UDP connections
174
DNS requests
117
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2260 | chrome.exe | GET | 200 | 217.146.165.205:80 | http://r2---sn-oun-1gie.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=136.0.0.150&mm=28&mn=sn-oun-1gie&ms=nvh&mt=1553203220&mv=u&pl=20&shardbypass=yes | CH | crx | 842 Kb | whitelisted |
2092 | dxwsetup.exe | GET | 200 | 2.18.233.19:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/Apr2006_xact_x86.cab | unknown | compressed | 130 Kb | whitelisted |
2092 | dxwsetup.exe | GET | 200 | 2.18.233.19:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/Apr2006_xinput_x86.cab | unknown | compressed | 45.9 Kb | whitelisted |
2092 | dxwsetup.exe | GET | 200 | 2.18.233.19:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/dxupdate.cab | unknown | compressed | 94.8 Kb | whitelisted |
2092 | dxwsetup.exe | GET | 200 | 2.18.233.19:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/Oct2006_xact_x86.cab | unknown | compressed | 135 Kb | whitelisted |
2092 | dxwsetup.exe | GET | 200 | 2.18.233.19:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/Jun2006_xact_x86.cab | unknown | compressed | 131 Kb | whitelisted |
2092 | dxwsetup.exe | GET | 200 | 2.18.233.19:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/Dec2006_xact_x86.cab | unknown | compressed | 142 Kb | whitelisted |
2092 | dxwsetup.exe | GET | 200 | 2.18.233.19:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/Feb2007_xact_x86.cab | unknown | compressed | 145 Kb | whitelisted |
2092 | dxwsetup.exe | GET | 200 | 2.18.233.19:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/Aug2006_xact_x86.cab | unknown | compressed | 135 Kb | whitelisted |
2092 | dxwsetup.exe | GET | 200 | 2.18.233.19:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/Feb2006_xact_x86.cab | unknown | compressed | 130 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
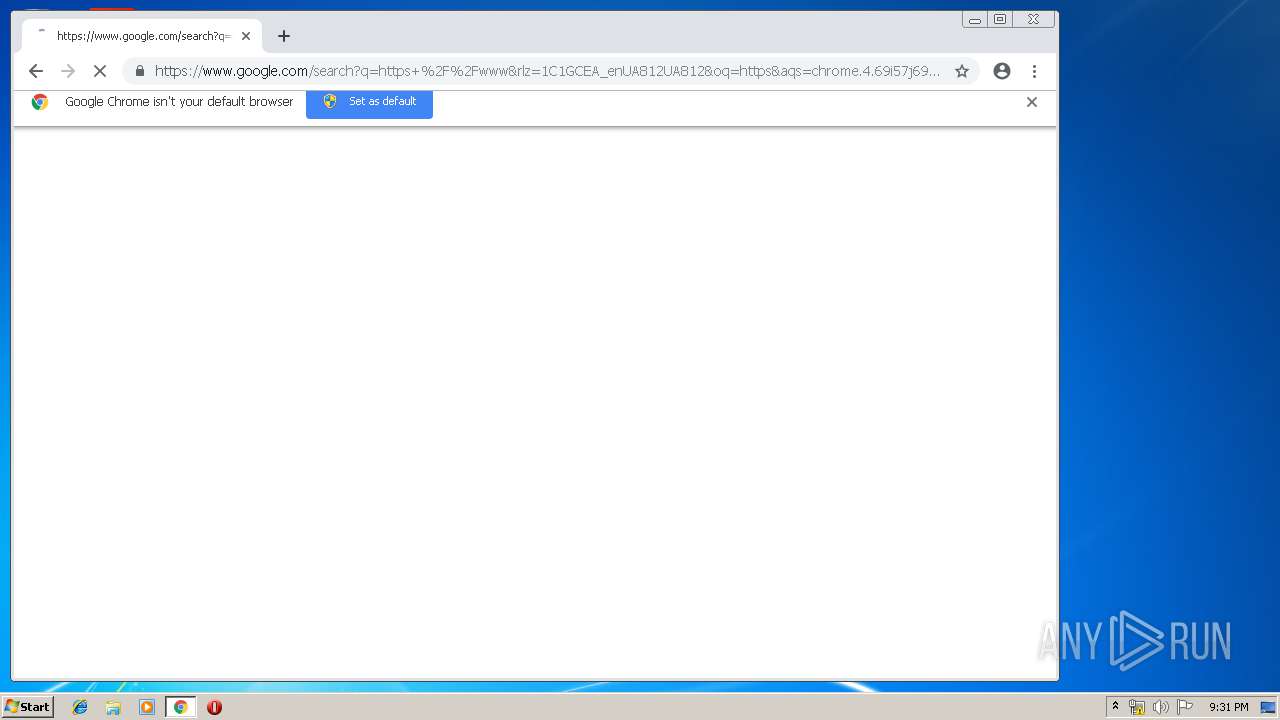
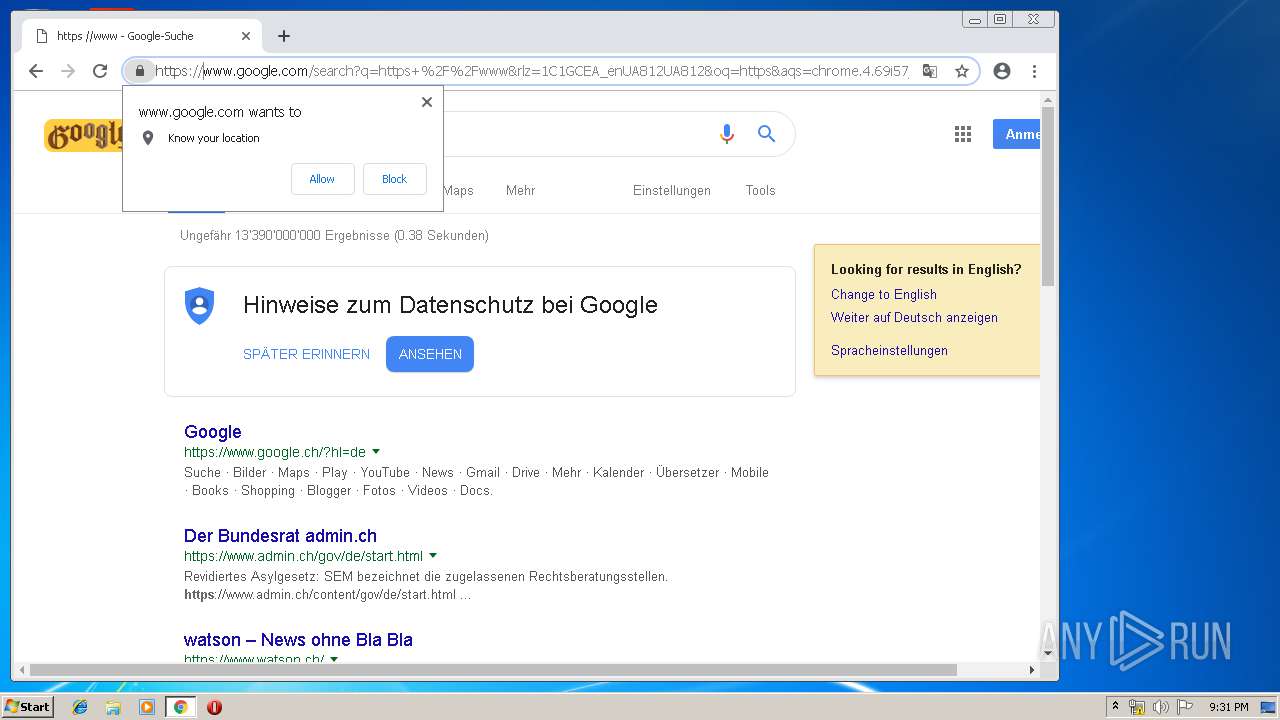
2260 | chrome.exe | 172.217.22.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2260 | chrome.exe | 172.217.22.4:443 | www.google.com | Google Inc. | US | whitelisted |
2260 | chrome.exe | 172.217.22.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
2260 | chrome.exe | 216.58.205.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2260 | chrome.exe | 216.58.210.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2260 | chrome.exe | 172.217.18.174:443 | apis.google.com | Google Inc. | US | whitelisted |
2260 | chrome.exe | 216.58.210.10:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2260 | chrome.exe | 216.58.207.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2260 | chrome.exe | 216.58.205.234:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2260 | chrome.exe | 172.217.23.142:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
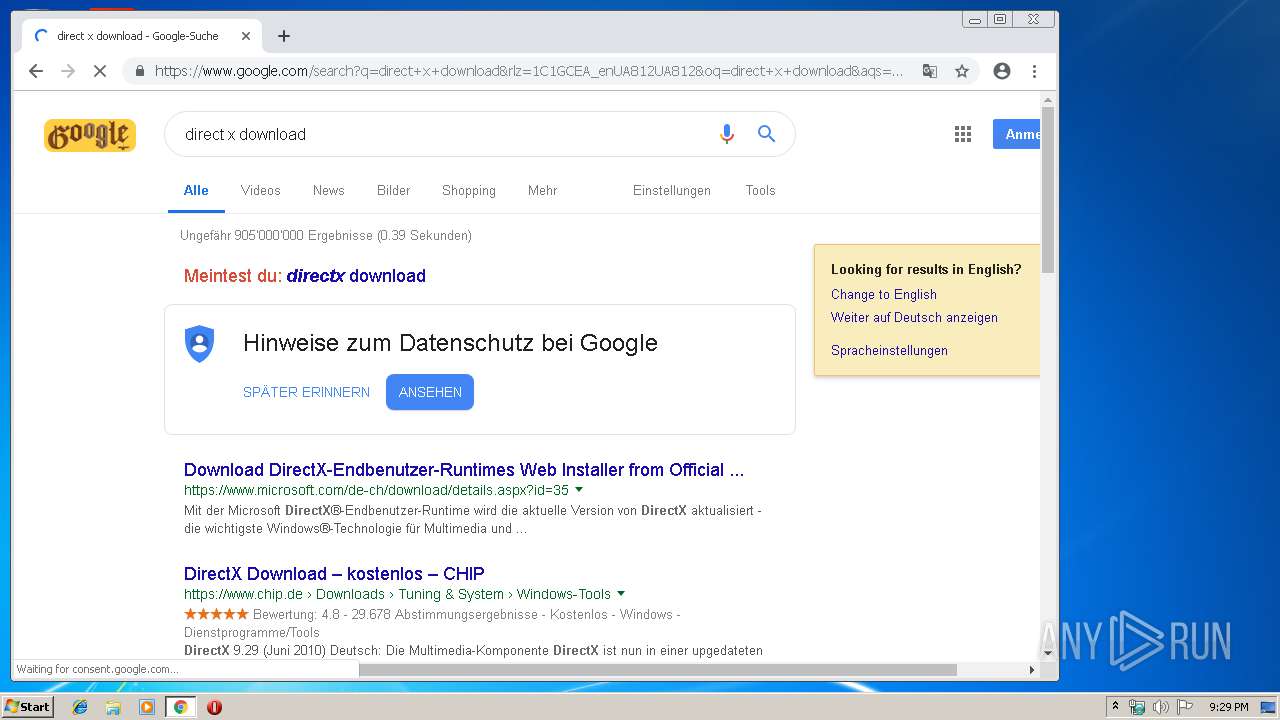
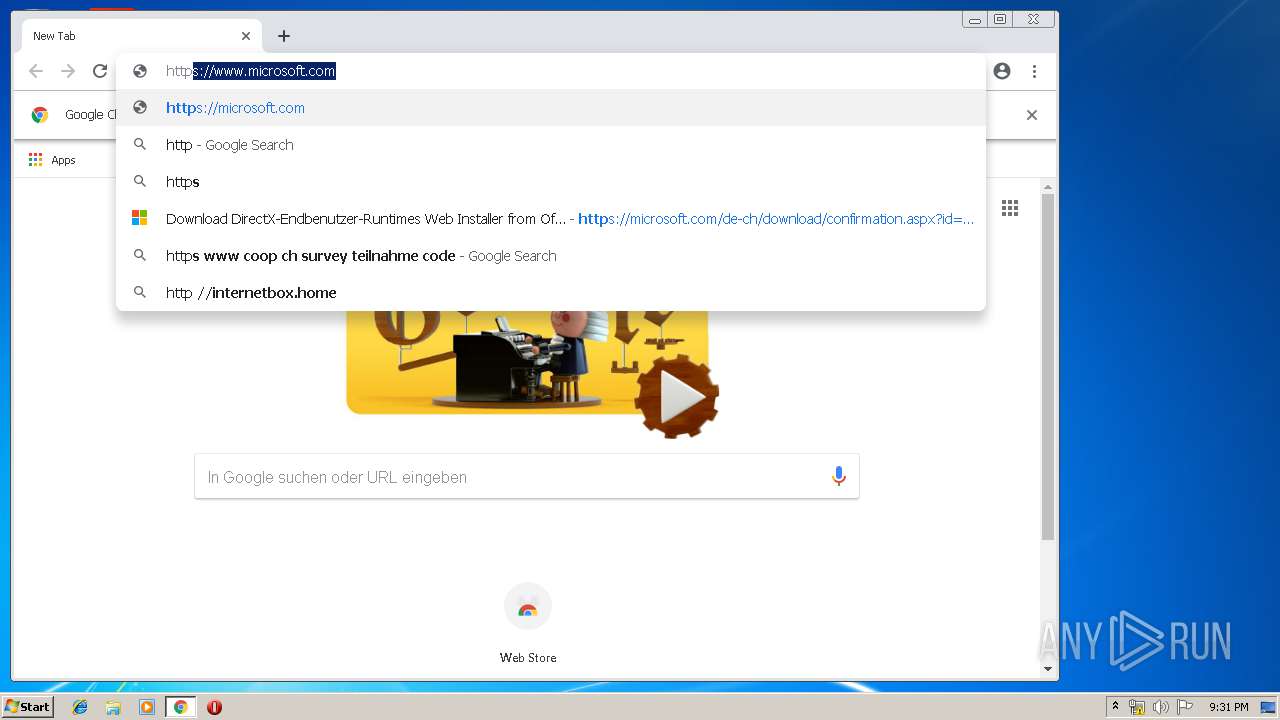
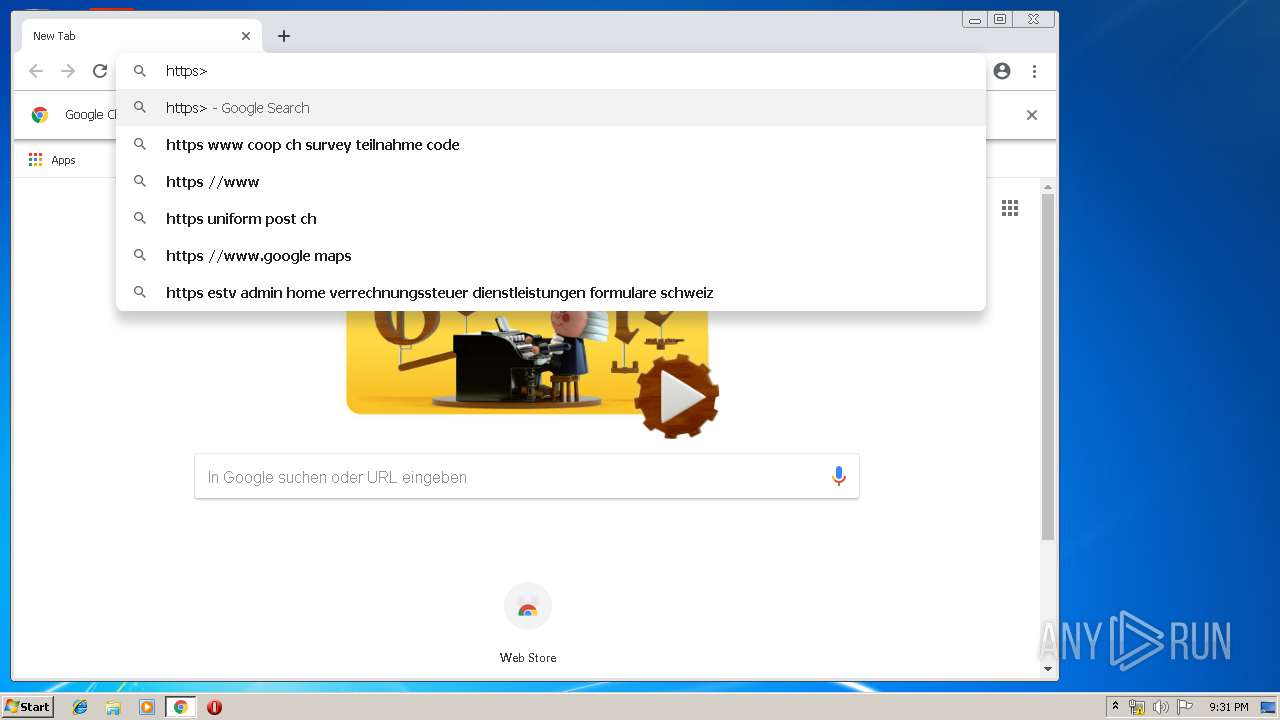
www.google.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2260 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
2092 | dxwsetup.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
Process | Message |
|---|---|
dxwsetup.exe | DLL_PROCESS_ATTACH |
dxwsetup.exe | DLL_PROCESS_ATTACH |
dxwsetup.exe | Invalid parameter passed to C runtime function.
|
dxwsetup.exe | Invalid parameter passed to C runtime function.
|
dxwsetup.exe | DLL_PROCESS_DETACH |
dxwsetup.exe | DLL_PROCESS_DETACH |
dxwsetup.exe | DLL_PROCESS_ATTACH |
dxwsetup.exe | DLL_PROCESS_ATTACH |
dxwsetup.exe | DLL_PROCESS_DETACH |
dxwsetup.exe | DLL_PROCESS_DETACH |