| File name: | Malware_3db0e385eb53a32d61a5a35908a99317868b571e4cf7079db67fd68604da662c.exe |
| Full analysis: | https://app.any.run/tasks/30d8235a-0973-478e-858d-f7f337f183e1 |
| Verdict: | Malicious activity |
| Analysis date: | October 05, 2022, 07:04:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 56AC9E72644A8DAE8C1968D63A26E58A |
| SHA1: | D0349D04F33400541898426438D9E036D21DECC5 |
| SHA256: | 3DB0E385EB53A32D61A5A35908A99317868B571E4CF7079DB67FD68604DA662C |
| SSDEEP: | 24576:mq5TfcdHj4fmbi2q+0MmV0VMXeyrtoT1GokHTQoCwsC+Y:mUTsamOx9RoBVoCwT |
MALICIOUS
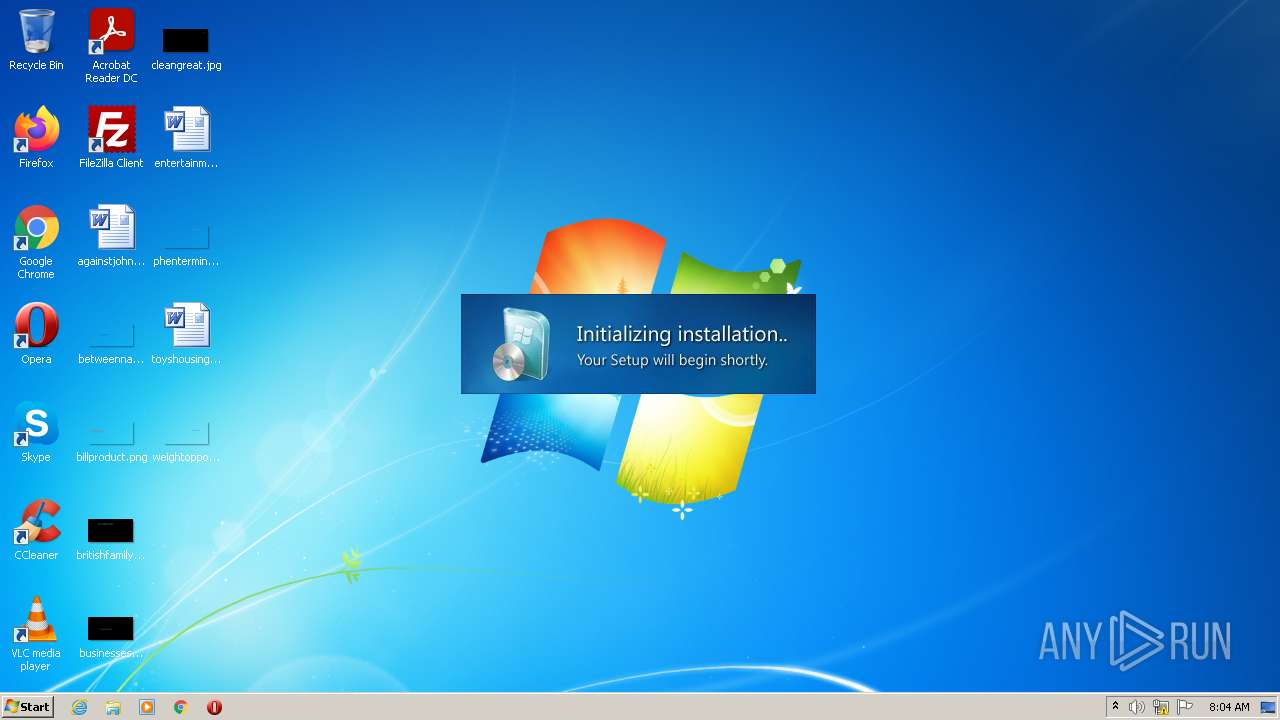
Drops the executable file immediately after the start
- Malware_3db0e385eb53a32d61a5a35908a99317868b571e4cf7079db67fd68604da662c.exe (PID: 3652)
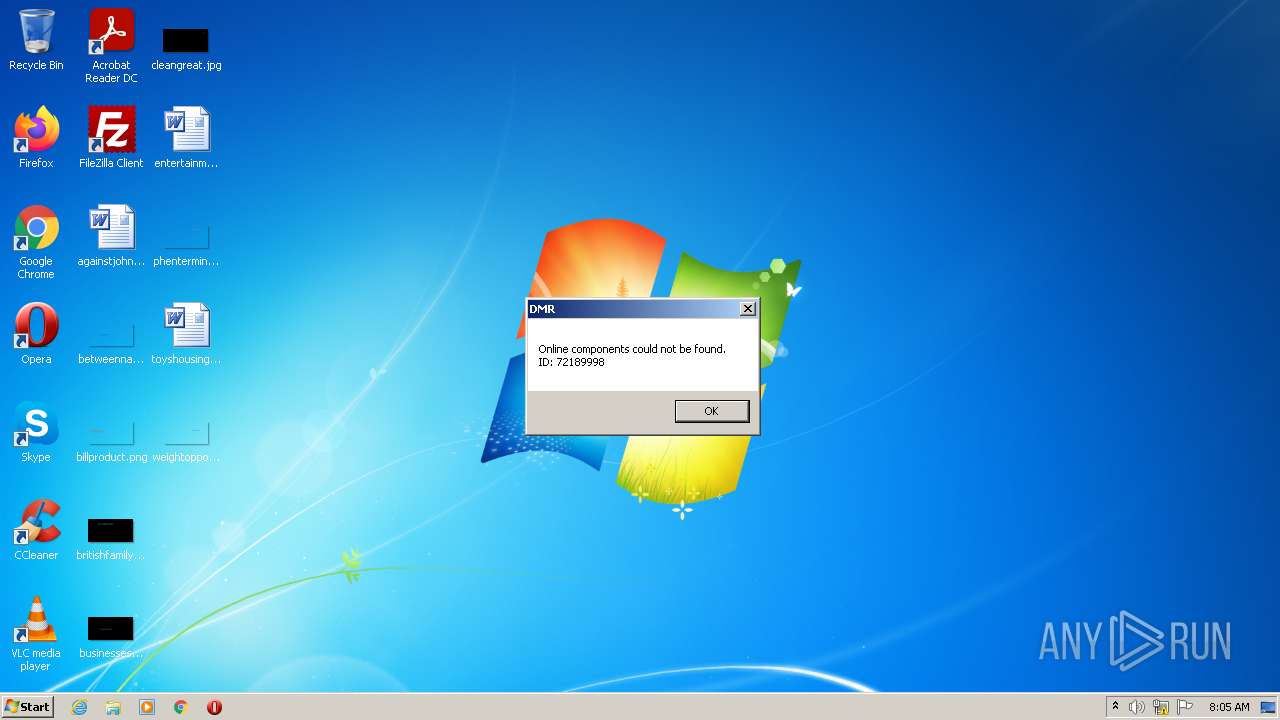
Application was dropped or rewritten from another process
- dmr_72.exe (PID: 3148)
SUSPICIOUS
Executable content was dropped or overwritten
- Malware_3db0e385eb53a32d61a5a35908a99317868b571e4cf7079db67fd68604da662c.exe (PID: 3652)
Reads Internet Settings
- Malware_3db0e385eb53a32d61a5a35908a99317868b571e4cf7079db67fd68604da662c.exe (PID: 3652)
- dmr_72.exe (PID: 3148)
Reads the machine GUID from the registry
- dmr_72.exe (PID: 3148)
INFO
Reads mouse settings
- Malware_3db0e385eb53a32d61a5a35908a99317868b571e4cf7079db67fd68604da662c.exe (PID: 3652)
Checks supported languages
- Malware_3db0e385eb53a32d61a5a35908a99317868b571e4cf7079db67fd68604da662c.exe (PID: 3652)
- dmr_72.exe (PID: 3148)
Checks Windows language
- Malware_3db0e385eb53a32d61a5a35908a99317868b571e4cf7079db67fd68604da662c.exe (PID: 3652)
Process checks LSA protection
- Malware_3db0e385eb53a32d61a5a35908a99317868b571e4cf7079db67fd68604da662c.exe (PID: 3652)
- dmr_72.exe (PID: 3148)
Creates a file in a temporary directory
- Malware_3db0e385eb53a32d61a5a35908a99317868b571e4cf7079db67fd68604da662c.exe (PID: 3652)
Reads the computer name
- Malware_3db0e385eb53a32d61a5a35908a99317868b571e4cf7079db67fd68604da662c.exe (PID: 3652)
- dmr_72.exe (PID: 3148)
Reads Environment values
- dmr_72.exe (PID: 3148)
Manual execution by user
- firefox.exe (PID: 2240)
Application launched itself
- firefox.exe (PID: 2240)
- firefox.exe (PID: 2076)
Dropped object may contain TOR URL's
- firefox.exe (PID: 2076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (30.7) |
|---|---|---|
| .exe | | | UPX compressed Win32 Executable (30.1) |
| .exe | | | Win32 EXE Yoda's Crypter (29.5) |
| .exe | | | Win32 Executable (generic) (5) |
| .exe | | | Generic Win/DOS Executable (2.2) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 2015-Jul-22 13:51:55 |
| Detected languages: |
|
| FileVersion: | 1.0.7.4 |
| Comments: | CHIP Secured Installer |
| FileDescription: | CHIP Secured Installer |
| ProductVersion: | 1.0.7.4 |
| LegalCopyright: | Copyright © 2015 Chip Digital GmbH |
DOS Header
| e_magic: | MZ |
|---|---|
| e_cblp: | 144 |
| e_cp: | 3 |
| e_crlc: | - |
| e_cparhdr: | 4 |
| e_minalloc: | - |
| e_maxalloc: | 65535 |
| e_ss: | - |
| e_sp: | 184 |
| e_csum: | - |
| e_ip: | - |
| e_cs: | - |
| e_ovno: | - |
| e_oemid: | - |
| e_oeminfo: | - |
| e_lfanew: | 264 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| NumberofSections: | 3 |
| TimeDateStamp: | 2015-Jul-22 13:51:55 |
| PointerToSymbolTable: | - |
| NumberOfSymbols: | - |
| SizeOfOptionalHeader: | 224 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 4096 | 1380352 | 0 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | |
UPX1 | 1384448 | 344064 | 343040 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.93591 |
.rsrc | 1728512 | 851968 | 850944 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.34589 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.34174 | 588 | Latin 1 / Western European | German - Germany | RT_VERSION |
4 | 3.75291 | 9640 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
7 | 3.34702 | 1428 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
8 | 3.2817 | 1674 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
9 | 3.28849 | 1168 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
10 | 3.28373 | 1532 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
11 | 3.26322 | 1628 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
12 | 3.25812 | 1126 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
99 | 2.0815 | 20 | Latin 1 / Western European | English - United Kingdom | RT_GROUP_ICON |
166 | 2.68292 | 80 | Latin 1 / Western European | English - United Kingdom | RT_MENU |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.DLL |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
Total processes
46
Monitored processes
10
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2076.0.945350448\315375849" -parentBuildID 20201112153044 -prefsHandle 988 -prefMapHandle 1008 -prefsLen 1 -prefMapSize 238726 -appdir "C:\Program Files\Mozilla Firefox\browser" - 2076 "\\.\pipe\gecko-crash-server-pipe.2076" 1192 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 1180 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2076.6.759711757\2064147820" -childID 1 -isForBrowser -prefsHandle 2960 -prefMapHandle 2956 -prefsLen 245 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 2076 "\\.\pipe\gecko-crash-server-pipe.2076" 2972 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 2076 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 2208 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2076.21.976449032\869481600" -childID 4 -isForBrowser -prefsHandle 3248 -prefMapHandle 3512 -prefsLen 7399 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 2076 "\\.\pipe\gecko-crash-server-pipe.2076" 3560 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 2240 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 2272 | "C:\Users\admin\AppData\Local\Temp\Malware_3db0e385eb53a32d61a5a35908a99317868b571e4cf7079db67fd68604da662c.exe" | C:\Users\admin\AppData\Local\Temp\Malware_3db0e385eb53a32d61a5a35908a99317868b571e4cf7079db67fd68604da662c.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: CHIP Secured Installer Exit code: 3221226540 Version: 1.0.7.4 Modules
| |||||||||||||||
| 2568 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2076.20.1468574424\822854906" -childID 3 -isForBrowser -prefsHandle 3488 -prefMapHandle 3484 -prefsLen 7399 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 2076 "\\.\pipe\gecko-crash-server-pipe.2076" 3508 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 3148 | "C:\Users\admin\AppData\Local\Temp\DMR\dmr_72.exe" -install -72189998 -chipde -e37278fe332e42d1af33e4480ad52248 - -BLUB2 -sliyoffjkooorudw -3652 | C:\Users\admin\AppData\Local\Temp\DMR\dmr_72.exe | Malware_3db0e385eb53a32d61a5a35908a99317868b571e4cf7079db67fd68604da662c.exe | ||||||||||||
User: admin Company: Chip Digital GmbH Integrity Level: HIGH Description: DMR Exit code: 0 Version: 1.0.7.4 Modules
| |||||||||||||||
| 3652 | "C:\Users\admin\AppData\Local\Temp\Malware_3db0e385eb53a32d61a5a35908a99317868b571e4cf7079db67fd68604da662c.exe" | C:\Users\admin\AppData\Local\Temp\Malware_3db0e385eb53a32d61a5a35908a99317868b571e4cf7079db67fd68604da662c.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Description: CHIP Secured Installer Exit code: 0 Version: 1.0.7.4 Modules
| |||||||||||||||
| 3776 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2076.13.1031020715\454178639" -childID 2 -isForBrowser -prefsHandle 3148 -prefMapHandle 1816 -prefsLen 6644 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 2076 "\\.\pipe\gecko-crash-server-pipe.2076" 3160 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
Total events
8 181
Read events
8 134
Write events
47
Delete events
0
Modification events
| (PID) Process: | (3652) Malware_3db0e385eb53a32d61a5a35908a99317868b571e4cf7079db67fd68604da662c.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3652) Malware_3db0e385eb53a32d61a5a35908a99317868b571e4cf7079db67fd68604da662c.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3652) Malware_3db0e385eb53a32d61a5a35908a99317868b571e4cf7079db67fd68604da662c.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3652) Malware_3db0e385eb53a32d61a5a35908a99317868b571e4cf7079db67fd68604da662c.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3148) dmr_72.exe | Key: | HKEY_CURRENT_USER\Software\OCS |
| Operation: | write | Name: | CID |
Value: 081ec1bf-e0e4-40cf-96e4-0dd7d3b5eb94 | |||
| (PID) Process: | (3148) dmr_72.exe | Key: | HKEY_CURRENT_USER\Software\OCS |
| Operation: | write | Name: | PID |
Value: chipde | |||
| (PID) Process: | (3148) dmr_72.exe | Key: | HKEY_CURRENT_USER\Software\OCS |
| Operation: | write | Name: | lastPID |
Value: chipde | |||
| (PID) Process: | (3148) dmr_72.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dmr_72_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3148) dmr_72.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dmr_72_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3148) dmr_72.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dmr_72_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
Executable files
1
Suspicious files
28
Text files
21
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2076 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2076 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 2076 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-wal | binary | |
MD5:— | SHA256:— | |||
| 2076 | firefox.exe | C:\Users\admin\AppData\Local\Temp\mz_etilqs_rwUt3ETeniFCRry | binary | |
MD5:— | SHA256:— | |||
| 3652 | Malware_3db0e385eb53a32d61a5a35908a99317868b571e4cf7079db67fd68604da662c.exe | C:\Users\admin\AppData\Local\Temp\DMR\sliyoffjkooorudw.dat | text | |
MD5:8C934B48A05955C6CC934925F4C01E7D | SHA256:51BE55DD44A7D2C782EF432971878A64040AEC99C5EC0B53AC92D72BB2645992 | |||
| 2076 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:299A2B747C11E4BDA194E563FEA4A699 | SHA256:94EE461F62E8B4A0A65471A41E10C8C56722B73C0A019D76ACA7F5BAF109813E | |||
| 2076 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 2076 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2076 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:994A33896BB41A278A315D0D796422B6 | SHA256:54EC50A20FFF8CC016710E49437CF6A11D3FE5EE7B28C185E4A9AAFEE2908B63 | |||
| 2076 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
18
DNS requests
84
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3148 | dmr_72.exe | GET | 200 | 116.203.169.158:80 | http://api.chip-secured-download.de/geoip/geoip.php?ip=322e3234342e3130302e323535 | IN | text | 2 b | unknown |
3148 | dmr_72.exe | GET | 200 | 116.203.169.158:80 | http://api.chip-secured-download.de/dotnet/com | IN | text | 22 b | unknown |
3148 | dmr_72.exe | GET | 200 | 116.203.169.158:80 | http://api.chip-secured-download.de/dotnet/com | IN | text | 22 b | unknown |
2076 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt | US | text | 8 b | whitelisted |
— | — | POST | 200 | 172.217.17.99:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
2076 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2076 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | US | text | 8 b | whitelisted |
2076 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3148 | dmr_72.exe | 116.203.169.158:80 | api.chip-secured-download.de | Hetzner Online GmbH | DE | unknown |
3148 | dmr_72.exe | 116.203.169.152:80 | ocs1.chdi-server.de | Hetzner Online GmbH | DE | unknown |
2076 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
— | — | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
2076 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
2076 | firefox.exe | 18.66.147.5:443 | content-signature-2.cdn.mozilla.net | AMAZON-02 | US | unknown |
2076 | firefox.exe | 13.32.121.85:443 | snippets.cdn.mozilla.net | AMAZON-02 | US | suspicious |
2076 | firefox.exe | 172.217.17.99:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
2076 | firefox.exe | 18.66.248.38:443 | firefox.settings.services.mozilla.com | AMAZON-02 | US | suspicious |
2076 | firefox.exe | 34.218.159.206:443 | push.services.mozilla.com | AMAZON-02 | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.chip-secured-download.de |
| unknown |
ocs1.chdi-server.de |
| unknown |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
location.services.mozilla.com |
| whitelisted |
locprod2-elb-us-west-2.prod.mozaws.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2076 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
2076 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |