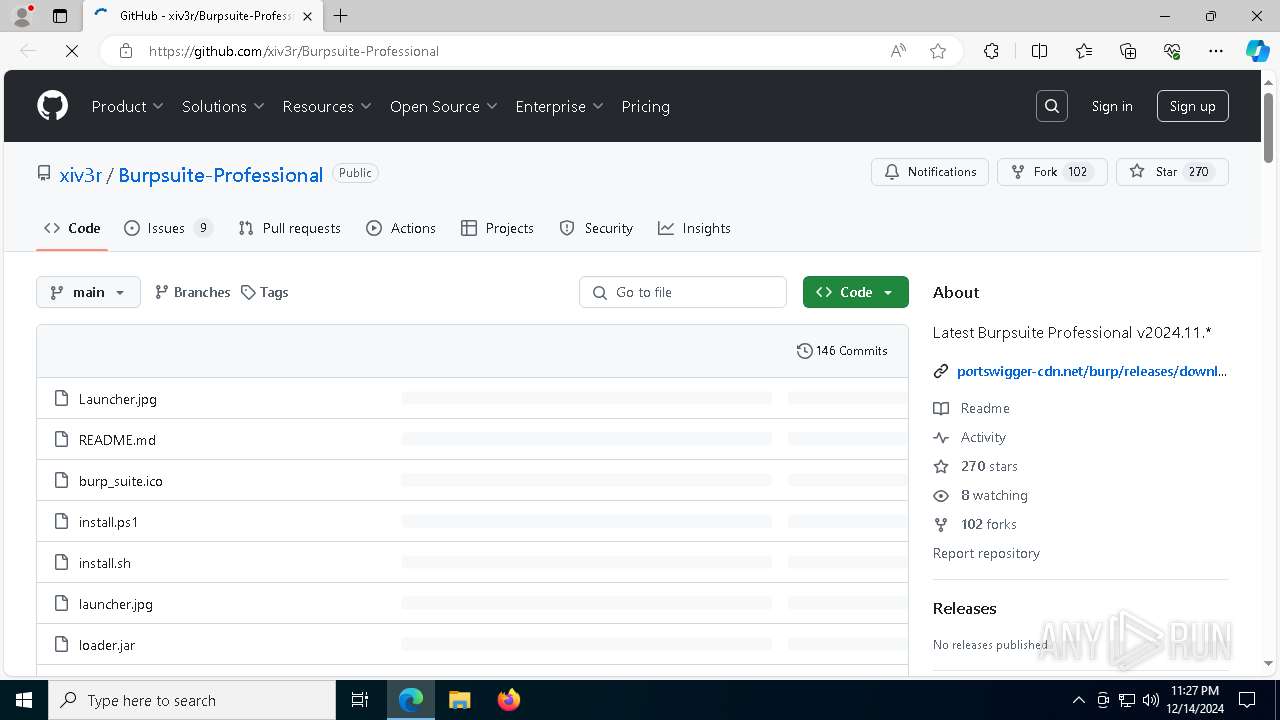
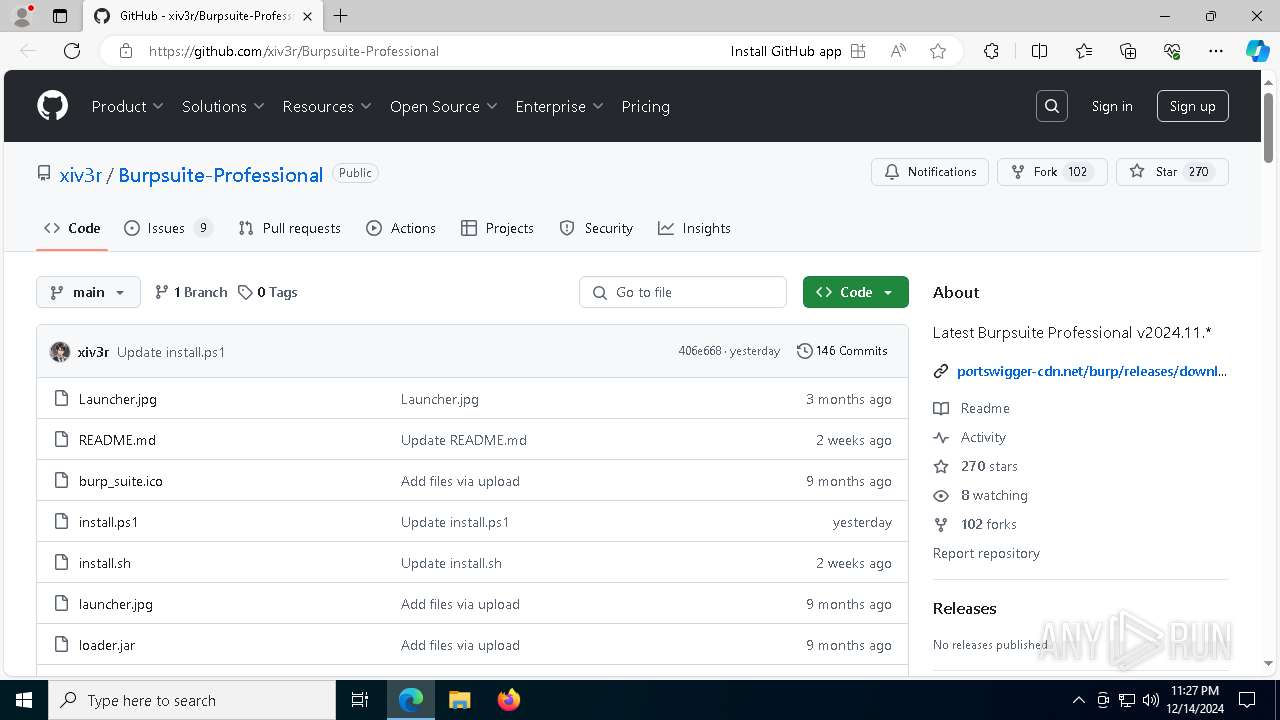
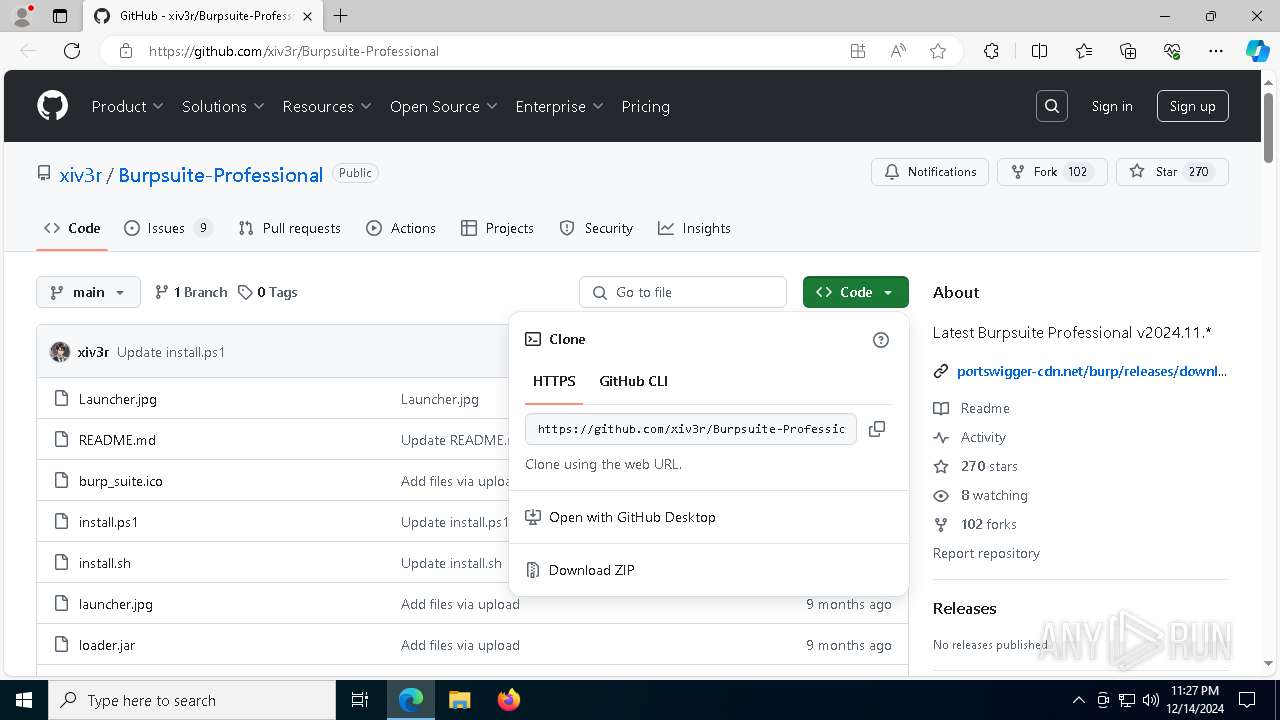
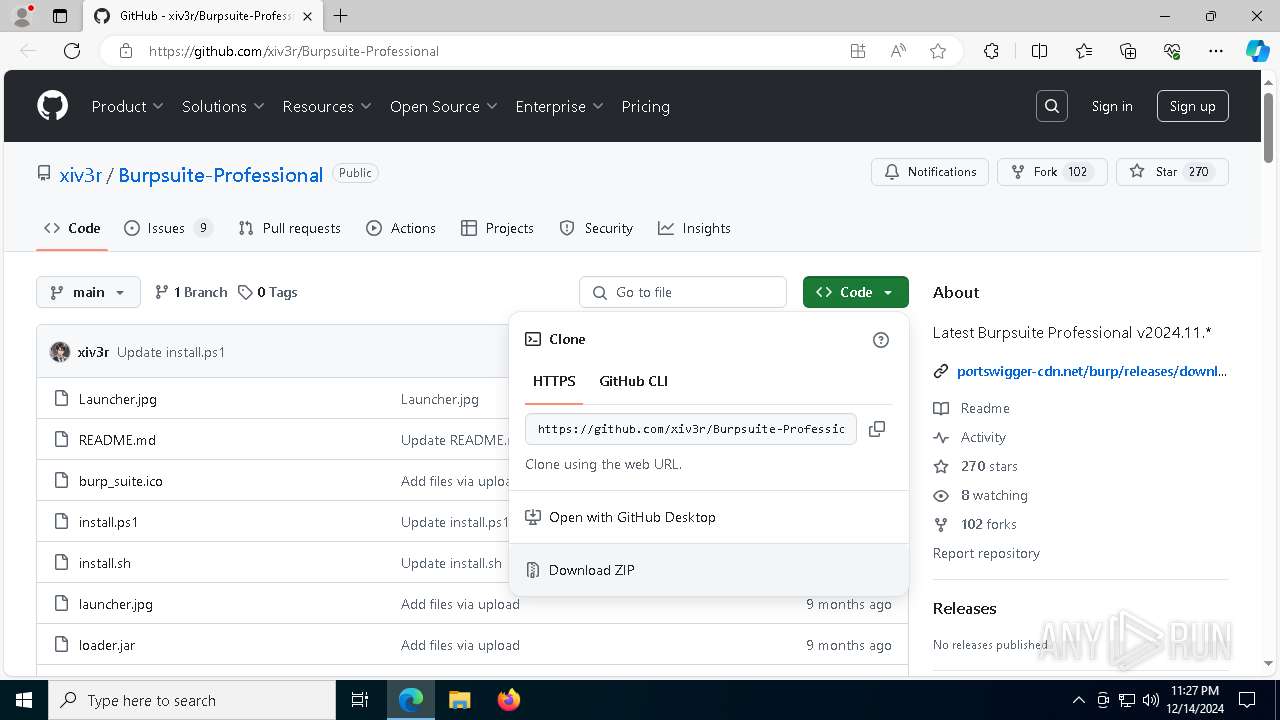
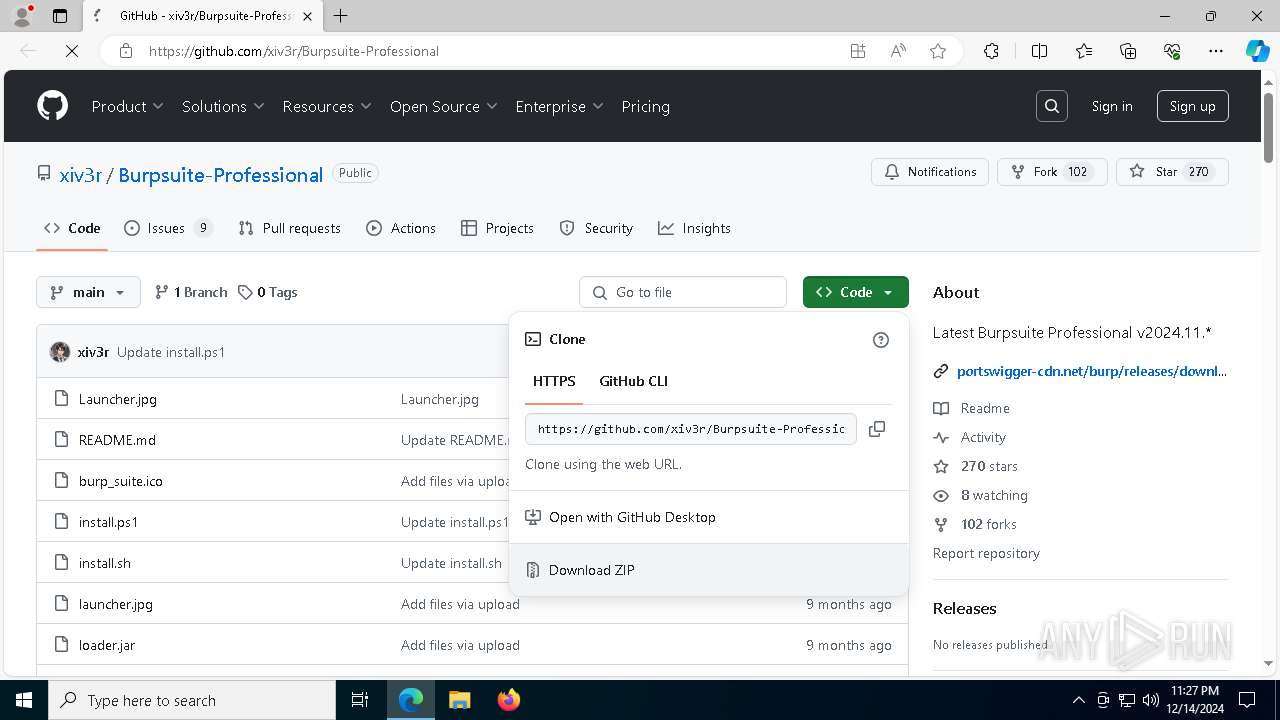
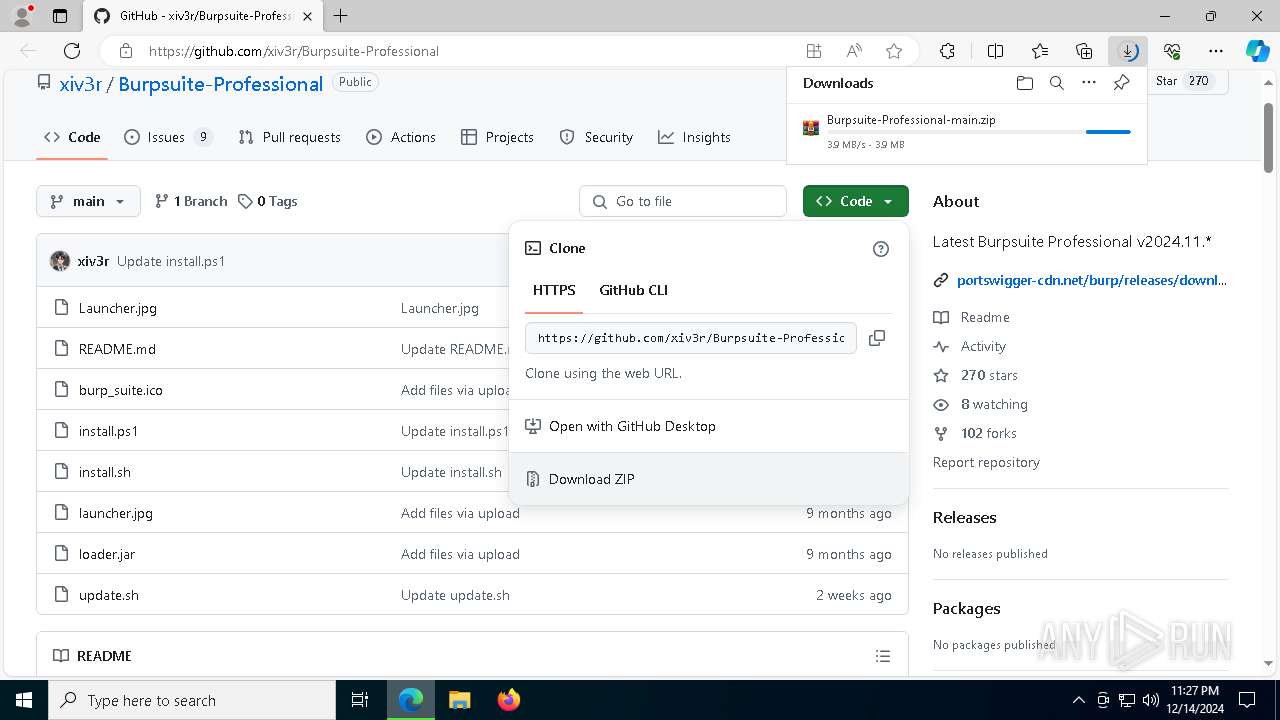
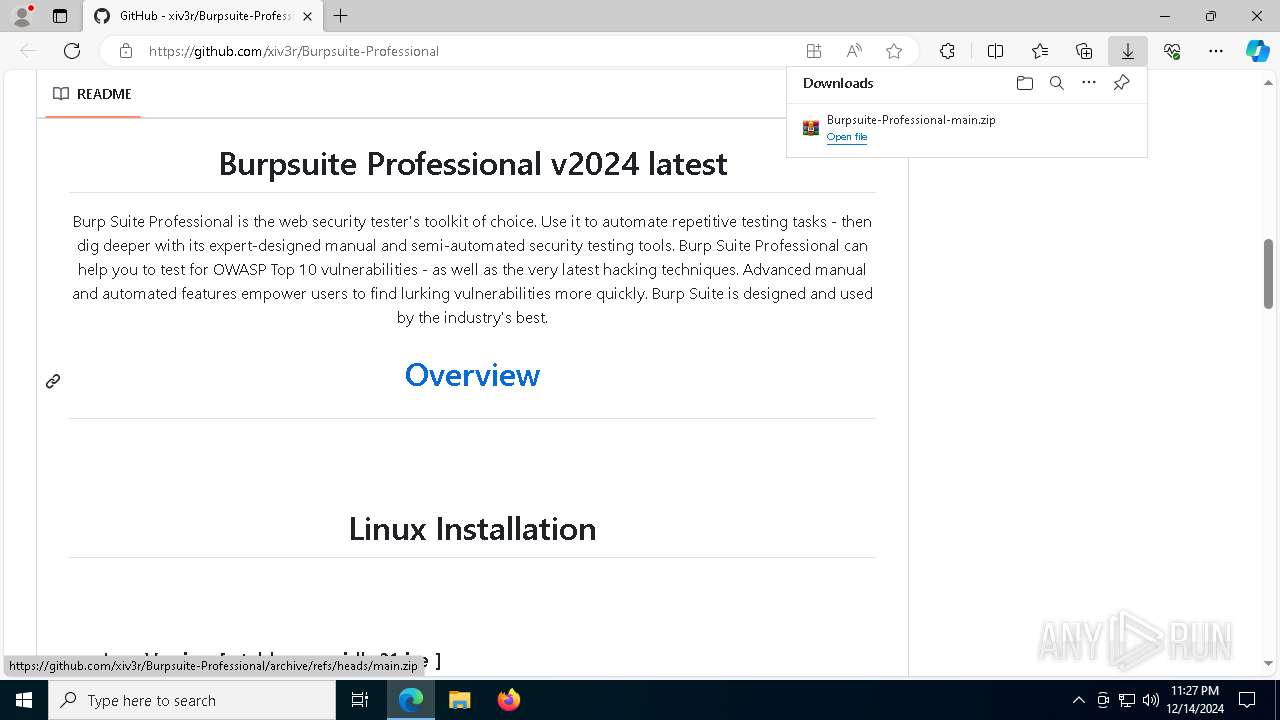
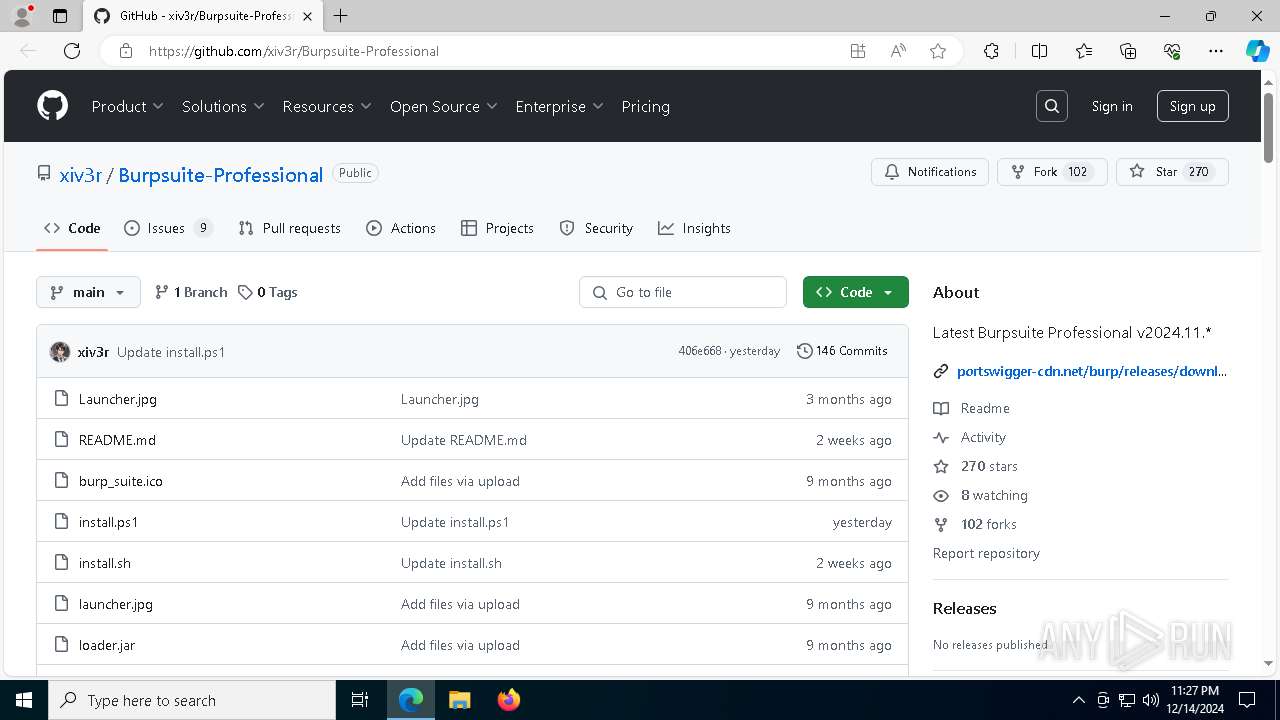
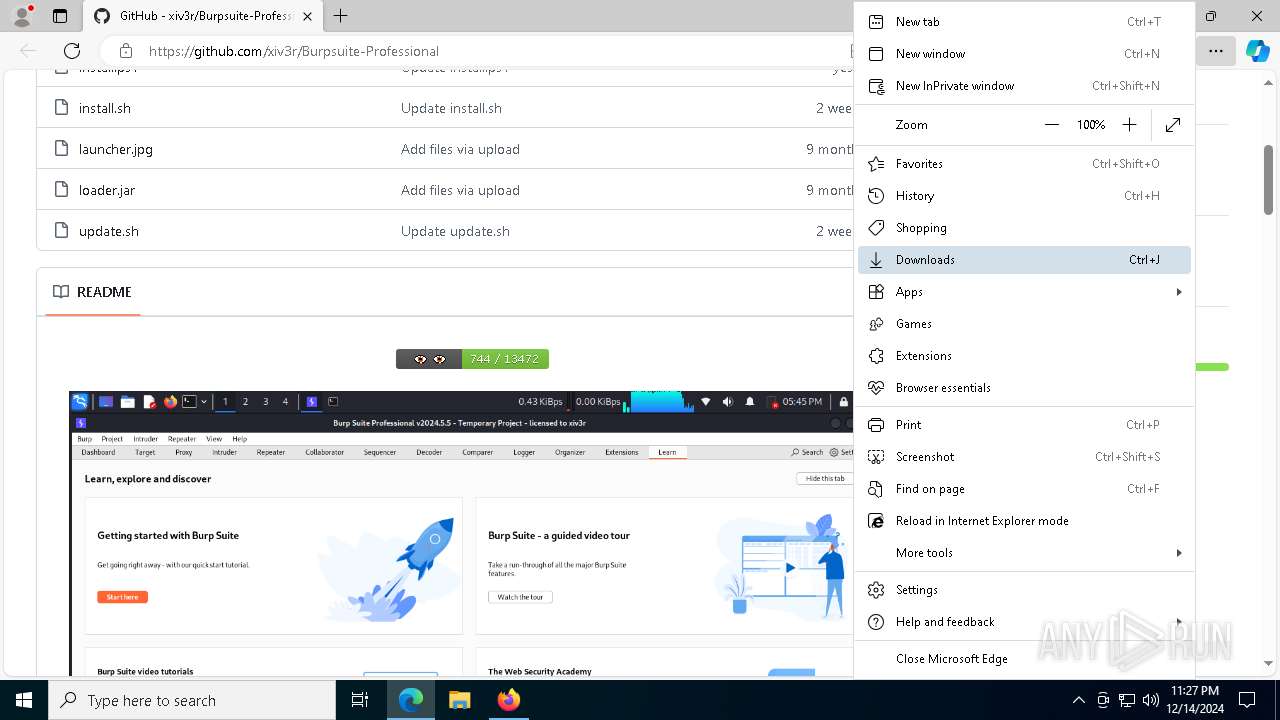
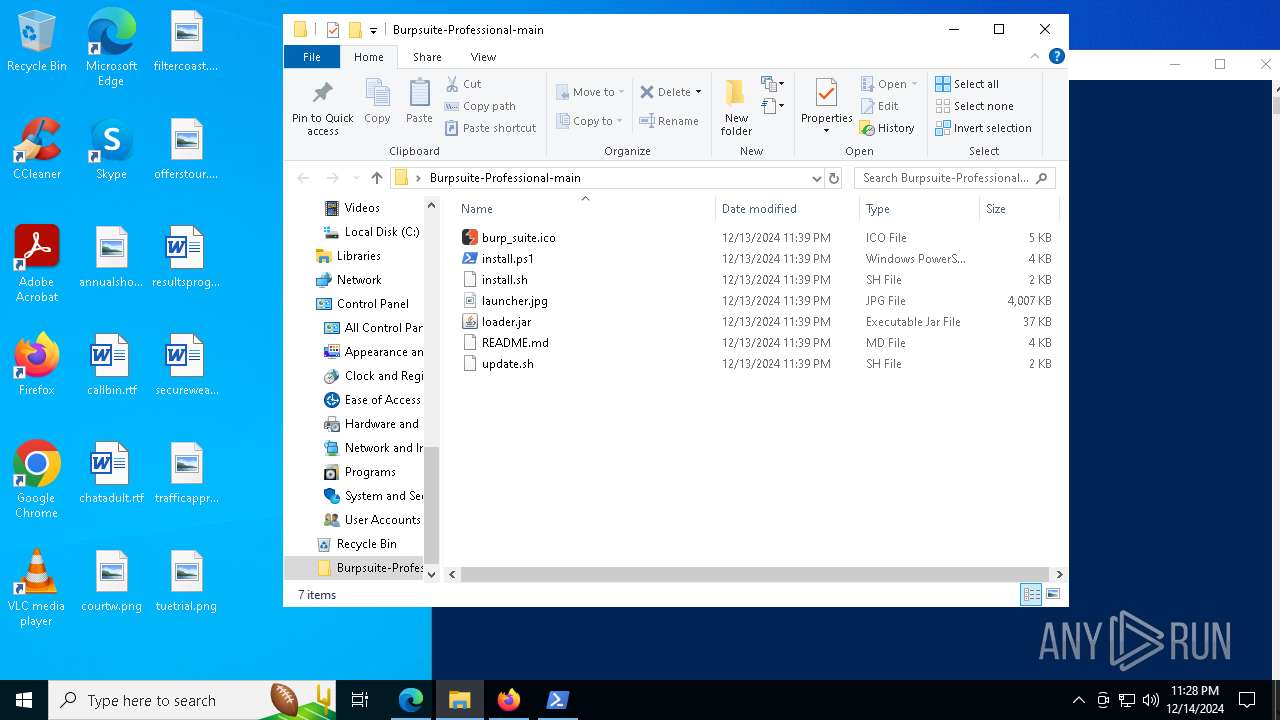
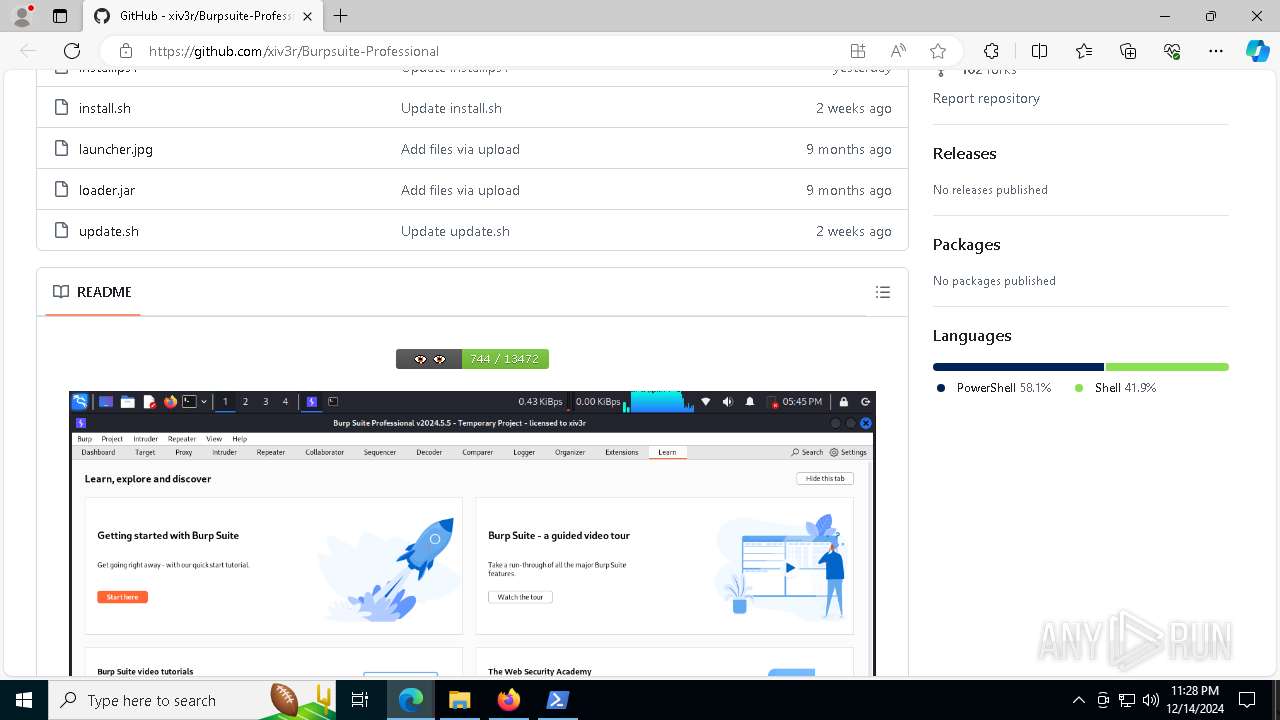
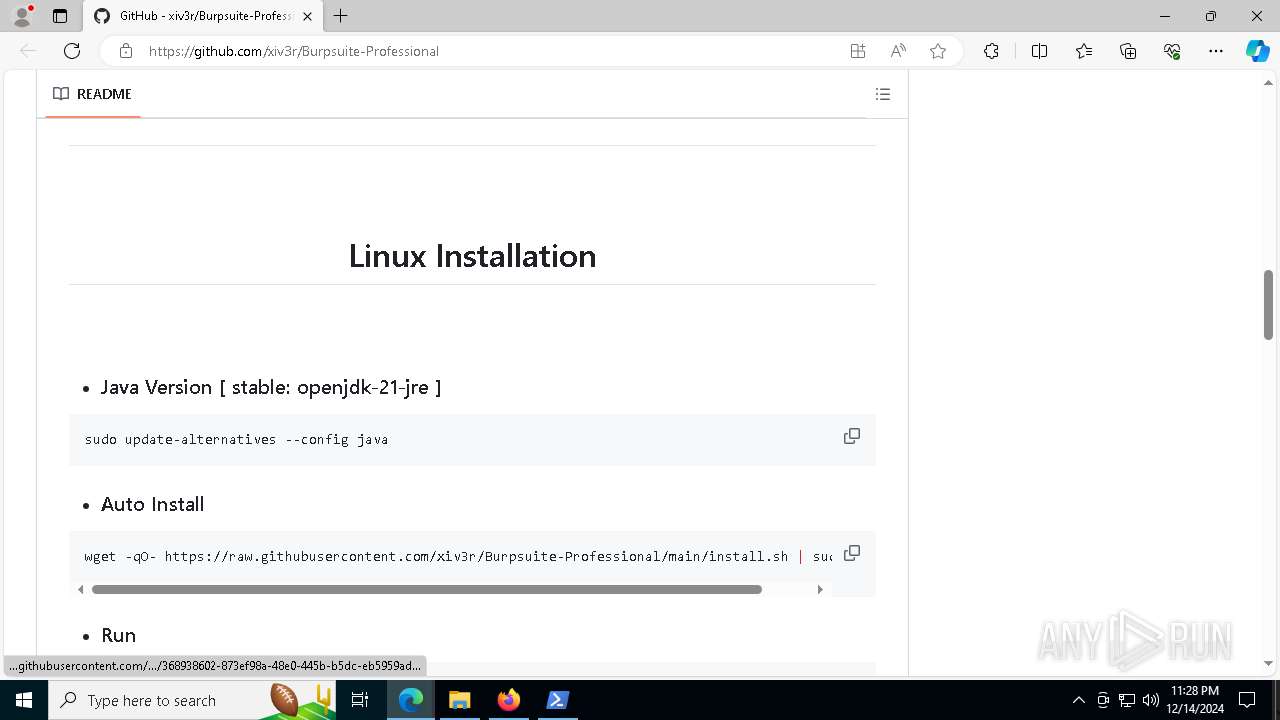
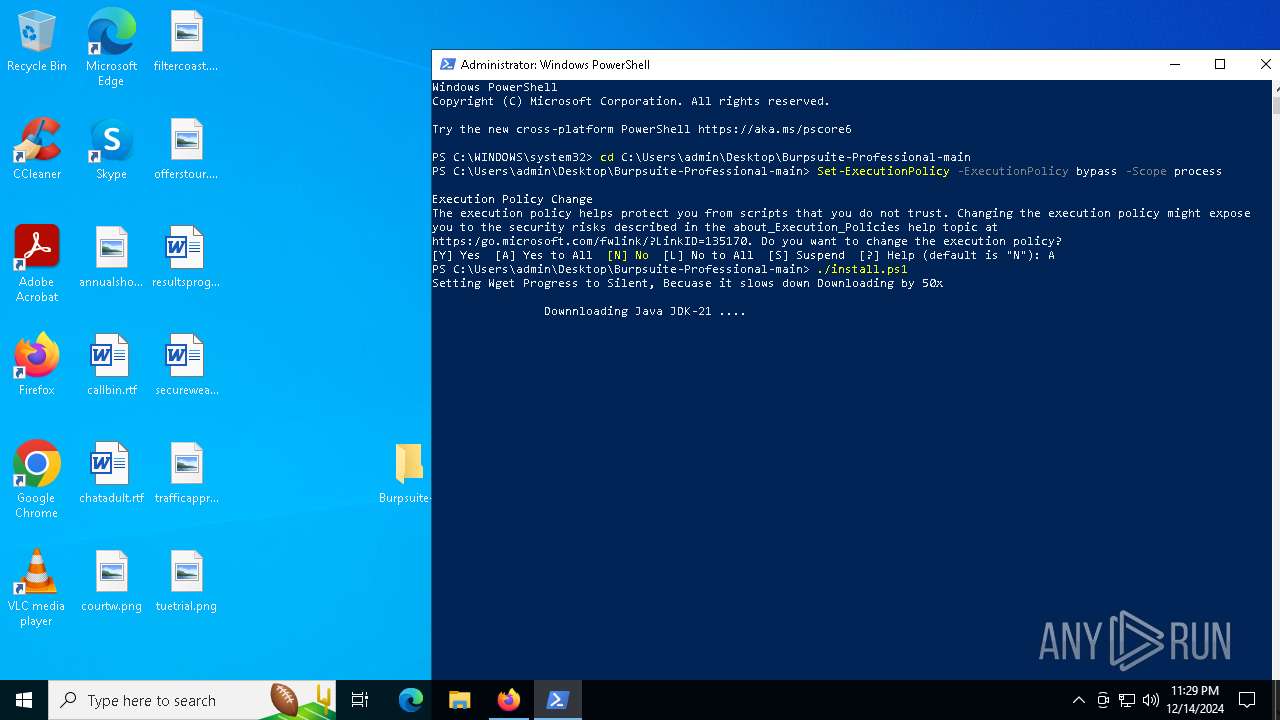
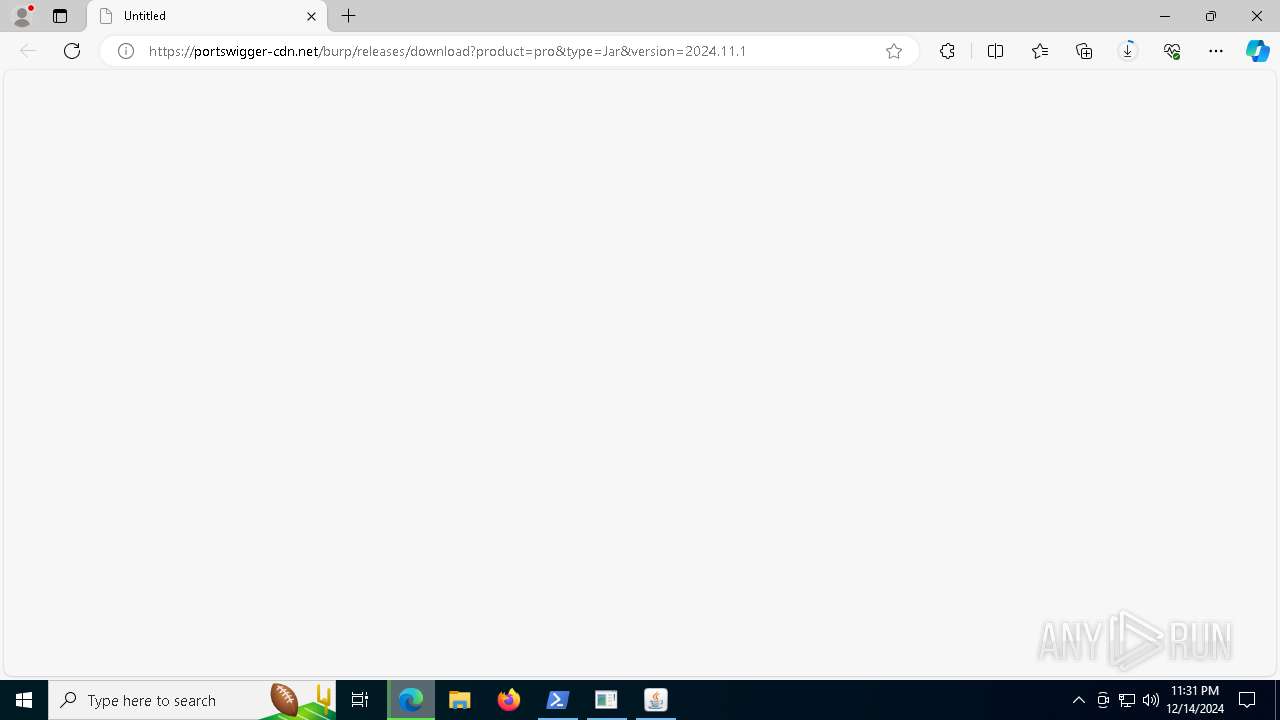
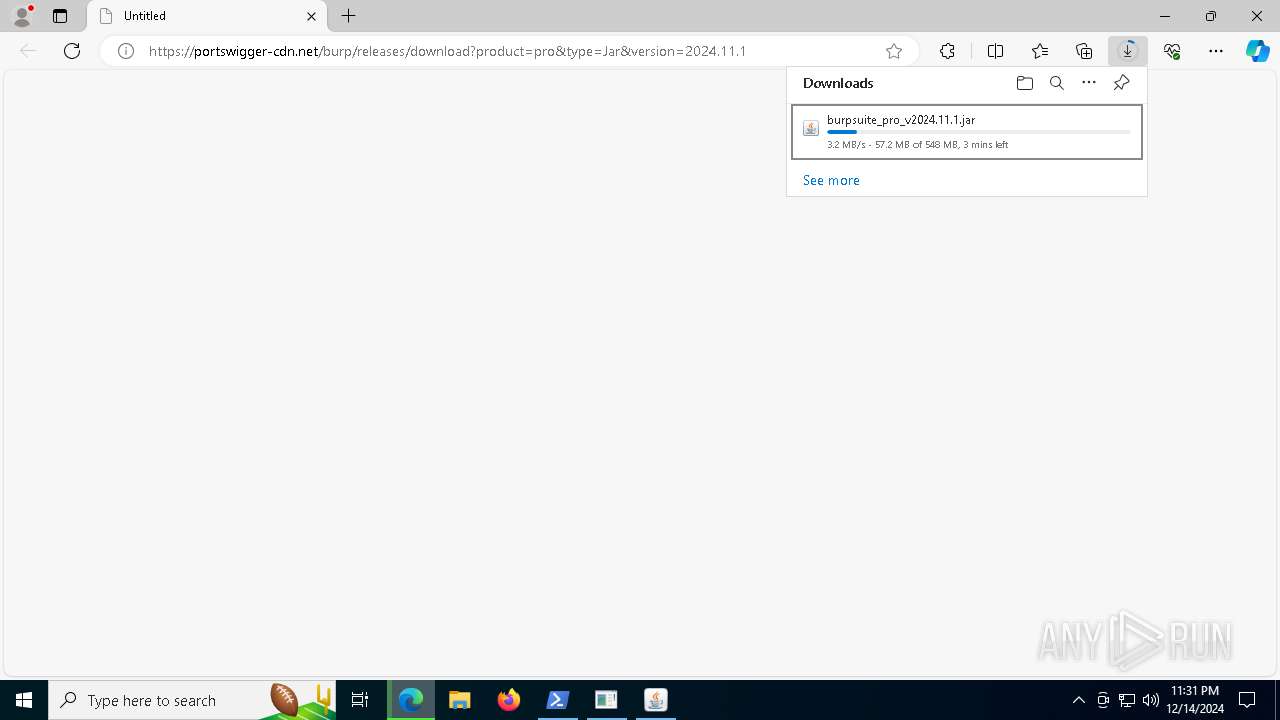
| URL: | https://github.com/xiv3r/Burpsuite-Professional |
| Full analysis: | https://app.any.run/tasks/871f65f5-7b75-4026-8c40-b0c309df7c98 |
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2024, 23:27:13 |
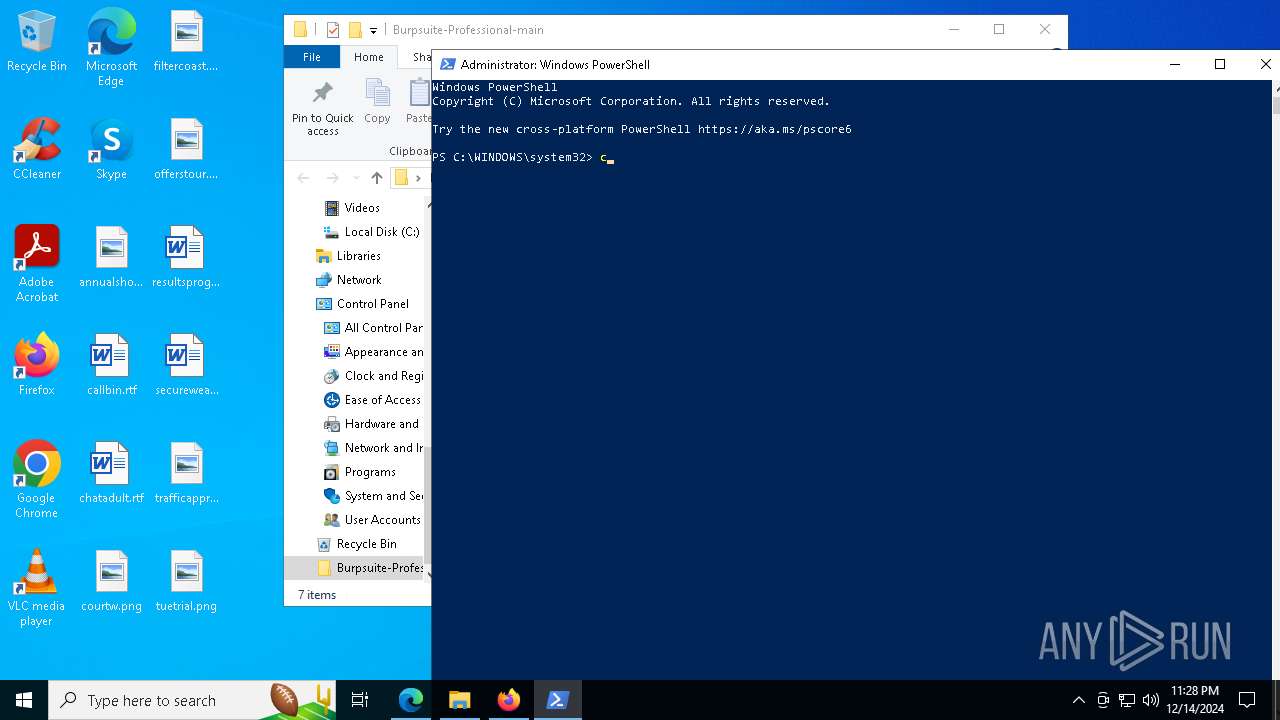
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 5F3A28B68ECD450C66BD33EFBB3F2989 |
| SHA1: | 4BB165B6F3922BE23ACA1244E71FDEBD87380266 |
| SHA256: | 3D9C865C5373BB810D7C91E667CE66878084B986B04998DF6D748302320B072A |
| SSDEEP: | 3:N8tEdtMc8CrIIDzLQgn:2uIc8C50gn |
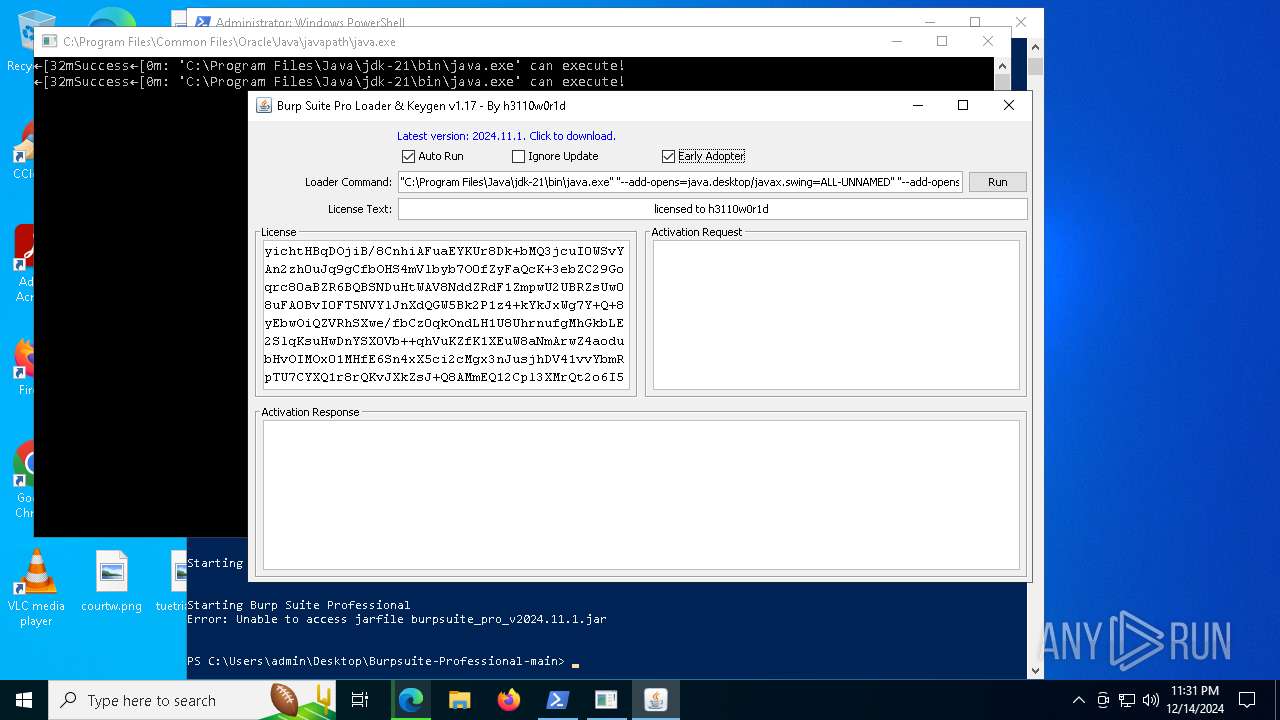
MALICIOUS
No malicious indicators.SUSPICIOUS
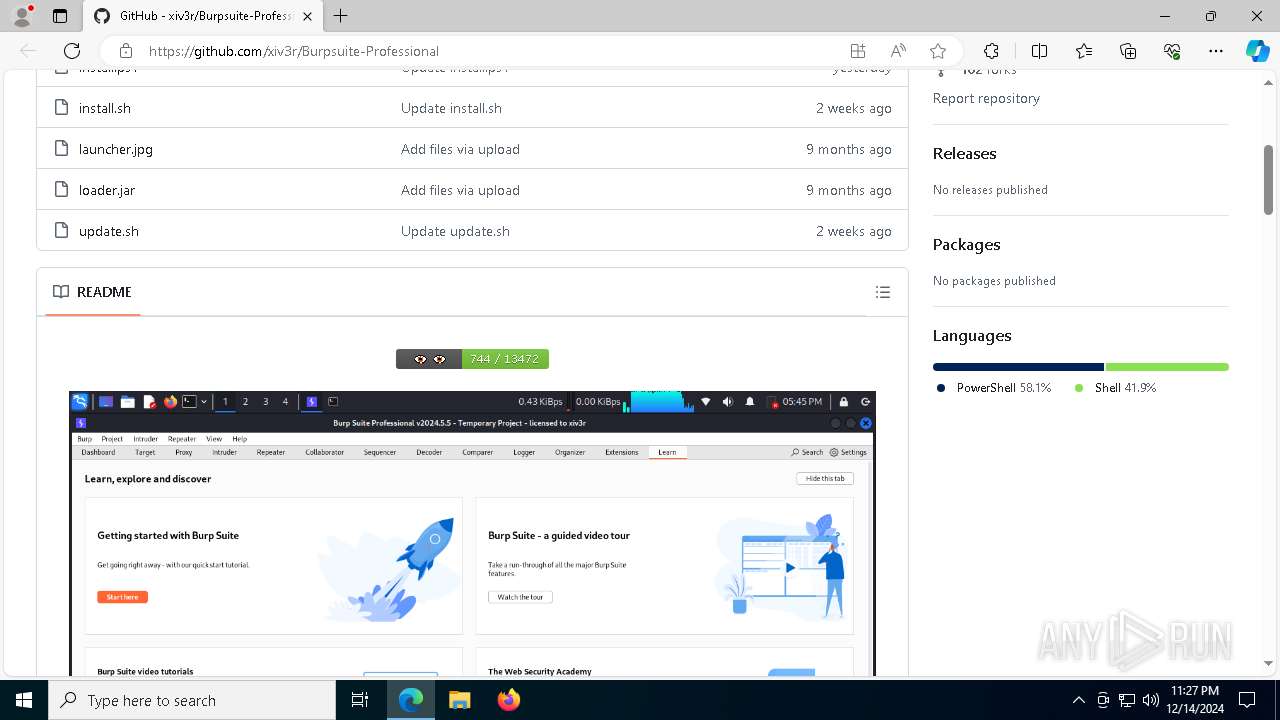
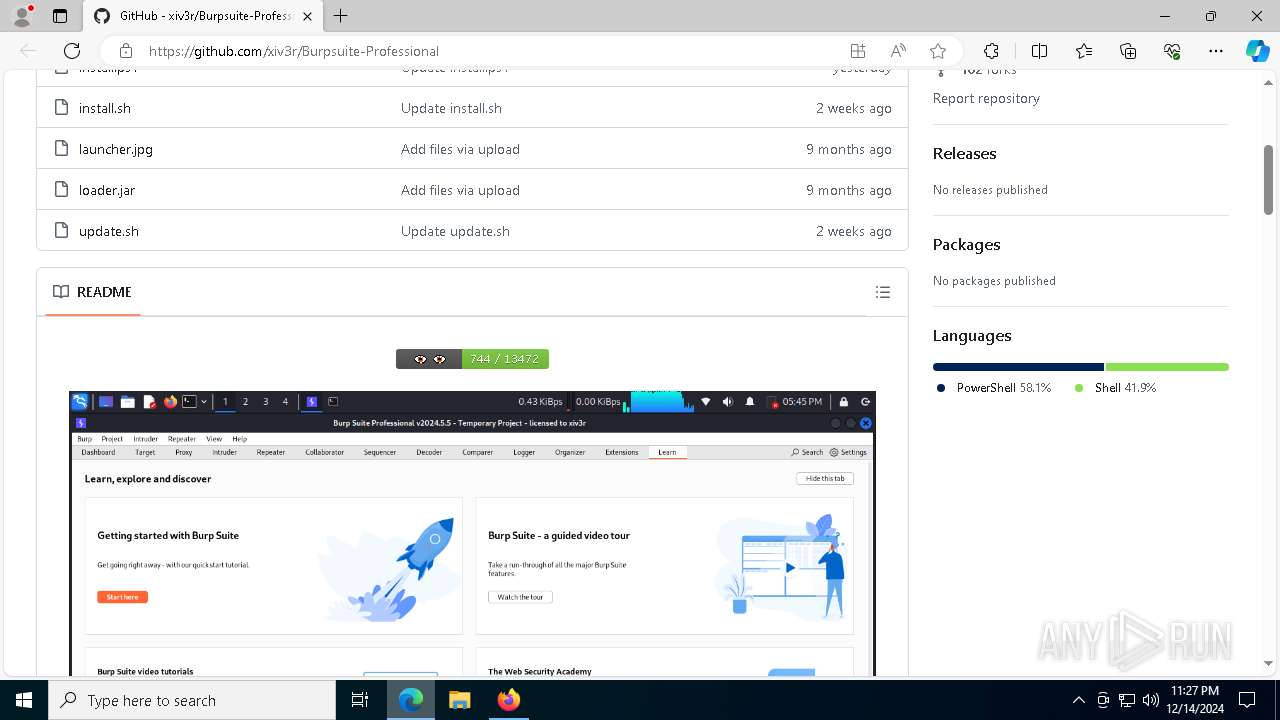
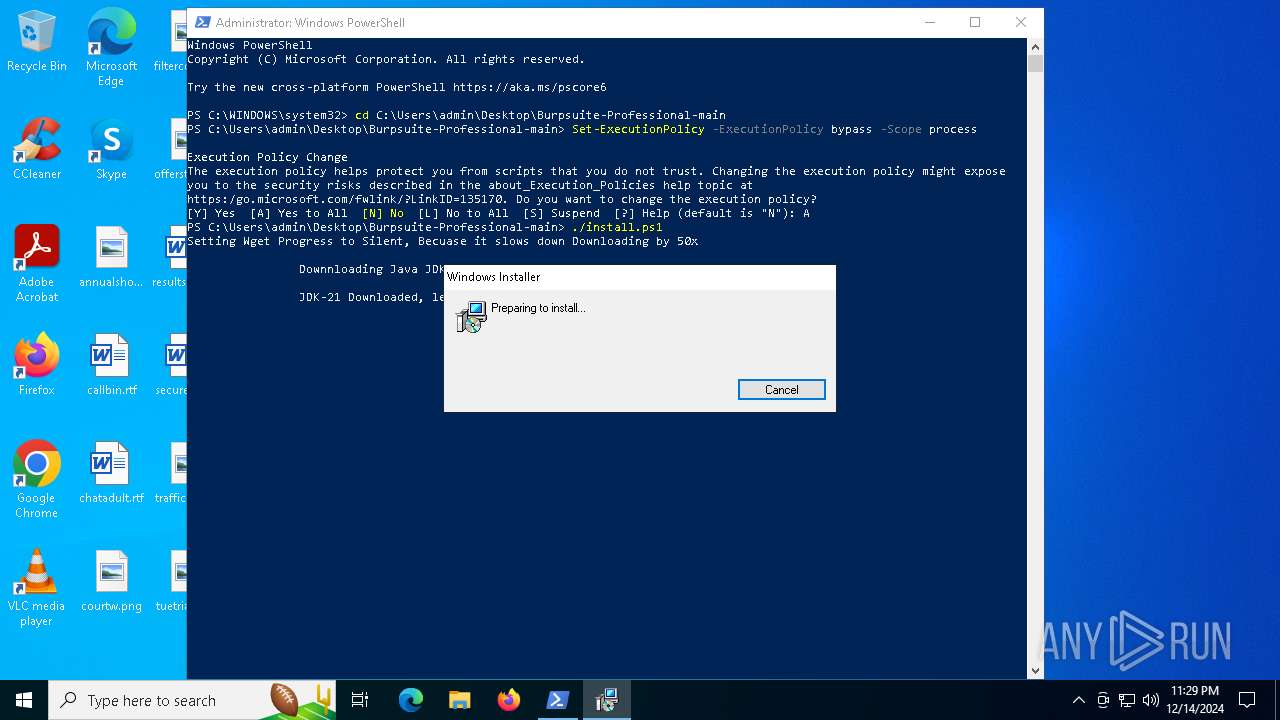
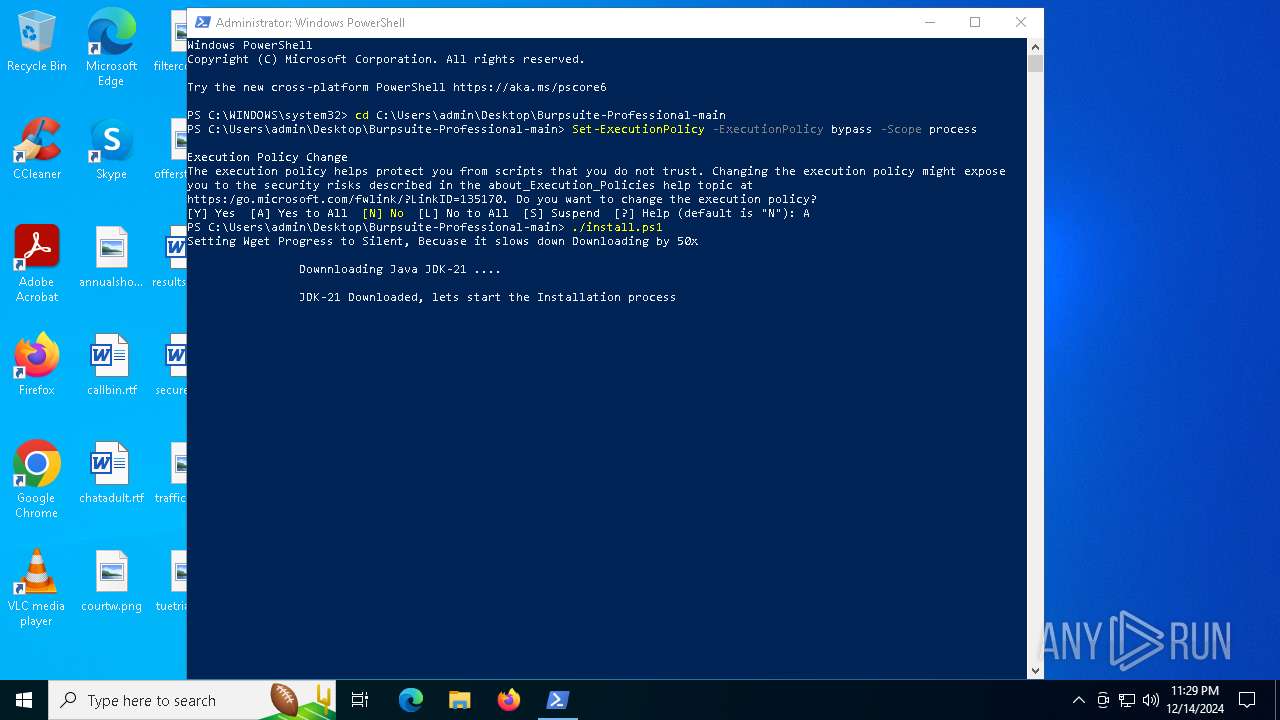
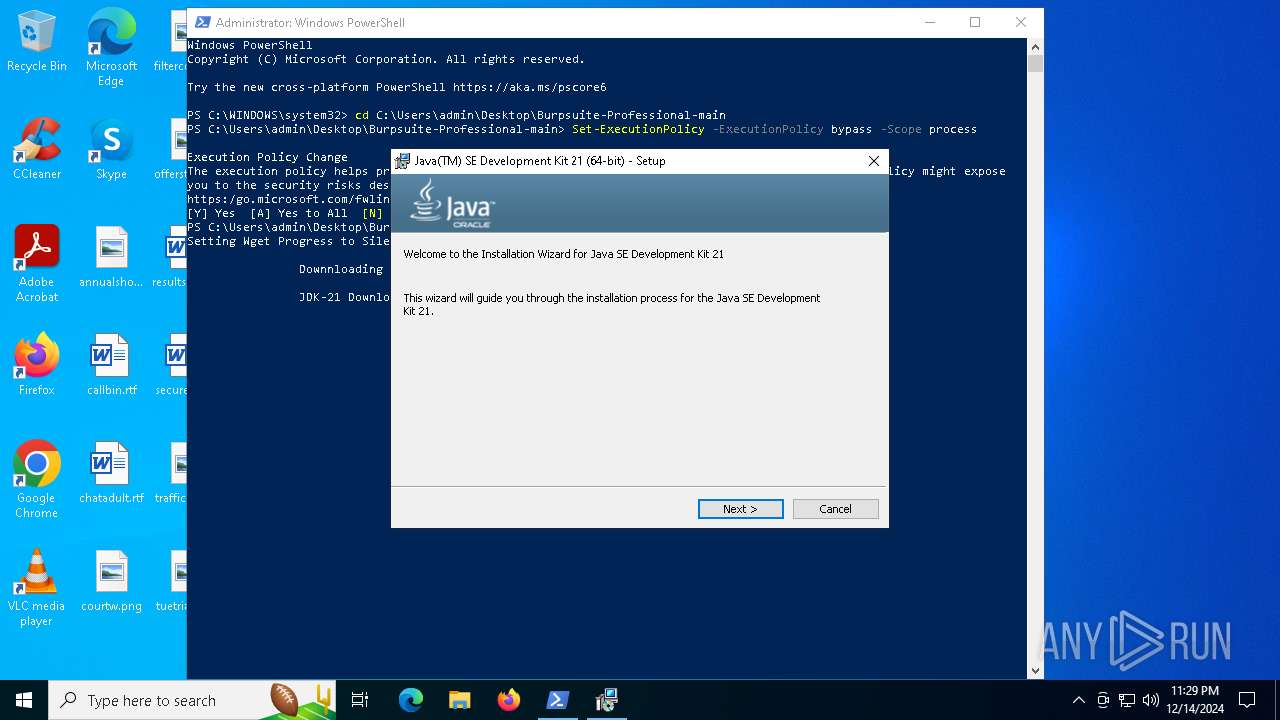
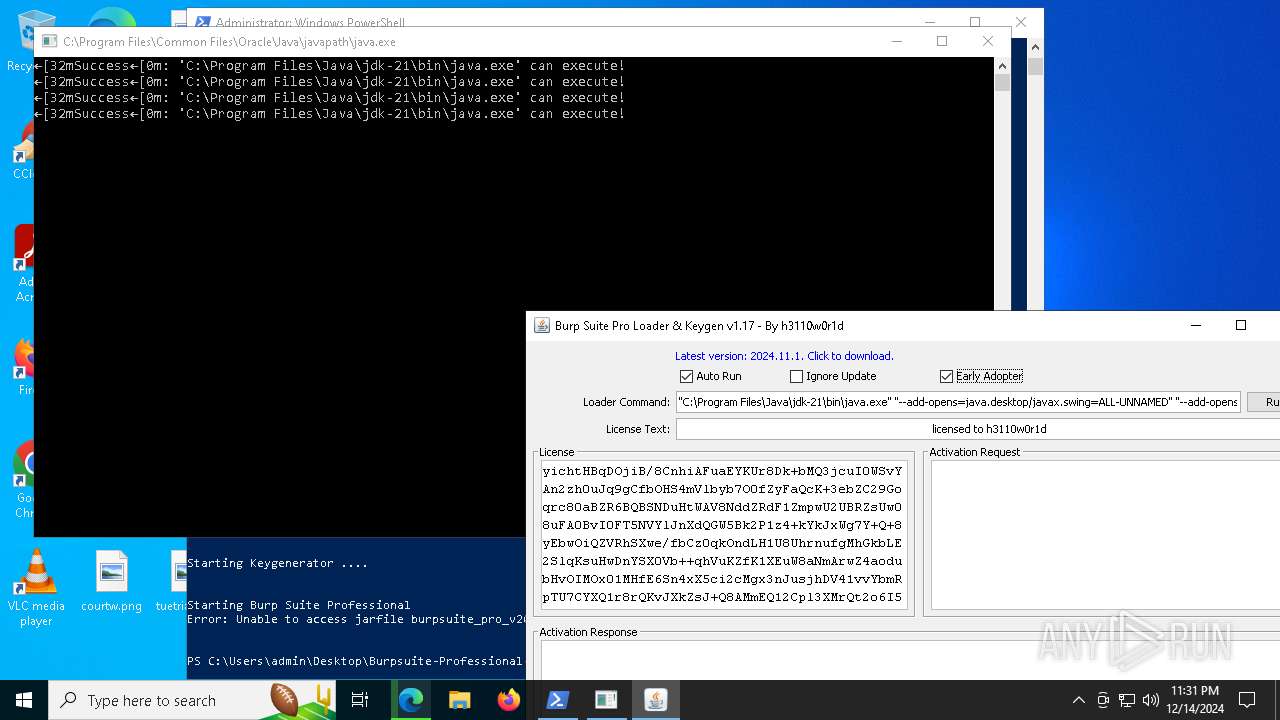
Checks for Java to be installed
- jdk-21.exe (PID: 7688)
- msiexec.exe (PID: 6452)
- msiexec.exe (PID: 7512)
- msiexec.exe (PID: 7144)
- msiexec.exe (PID: 7500)
Executes as Windows Service
- VSSVC.exe (PID: 6320)
Checks Windows Trust Settings
- msiexec.exe (PID: 7144)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 7144)
The process drops C-runtime libraries
- msiexec.exe (PID: 7500)
Process drops legitimate windows executable
- msiexec.exe (PID: 7500)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 7500)
- java.exe (PID: 1732)
The process creates files with name similar to system file names
- msiexec.exe (PID: 7500)
Application launched itself
- java.exe (PID: 1732)
INFO
Application launched itself
- msedge.exe (PID: 2796)
- firefox.exe (PID: 7496)
- firefox.exe (PID: 7524)
- msedge.exe (PID: 7072)
- msiexec.exe (PID: 7144)
Reads the computer name
- identity_helper.exe (PID: 8160)
- identity_helper.exe (PID: 2040)
- msiexec.exe (PID: 7144)
- identity_helper.exe (PID: 7256)
- jdk-21.exe (PID: 1476)
- jdk-21.exe (PID: 7688)
- msiexec.exe (PID: 6452)
- msiexec.exe (PID: 7500)
- msiexec.exe (PID: 7512)
- java.exe (PID: 1732)
Checks supported languages
- identity_helper.exe (PID: 2040)
- identity_helper.exe (PID: 8160)
- msiexec.exe (PID: 7144)
- jdk-21.exe (PID: 1476)
- identity_helper.exe (PID: 7256)
- jdk-21.exe (PID: 7688)
- msiexec.exe (PID: 6452)
- msiexec.exe (PID: 7512)
- msiexec.exe (PID: 7500)
- java.exe (PID: 7424)
- java.exe (PID: 7708)
- java.exe (PID: 8012)
- java.exe (PID: 7764)
- java.exe (PID: 1732)
- java.exe (PID: 7720)
- java.exe (PID: 6392)
- java.exe (PID: 4204)
- java.exe (PID: 6360)
- java.exe (PID: 6816)
- java.exe (PID: 7388)
Reads Environment values
- identity_helper.exe (PID: 8160)
- identity_helper.exe (PID: 2040)
- identity_helper.exe (PID: 7256)
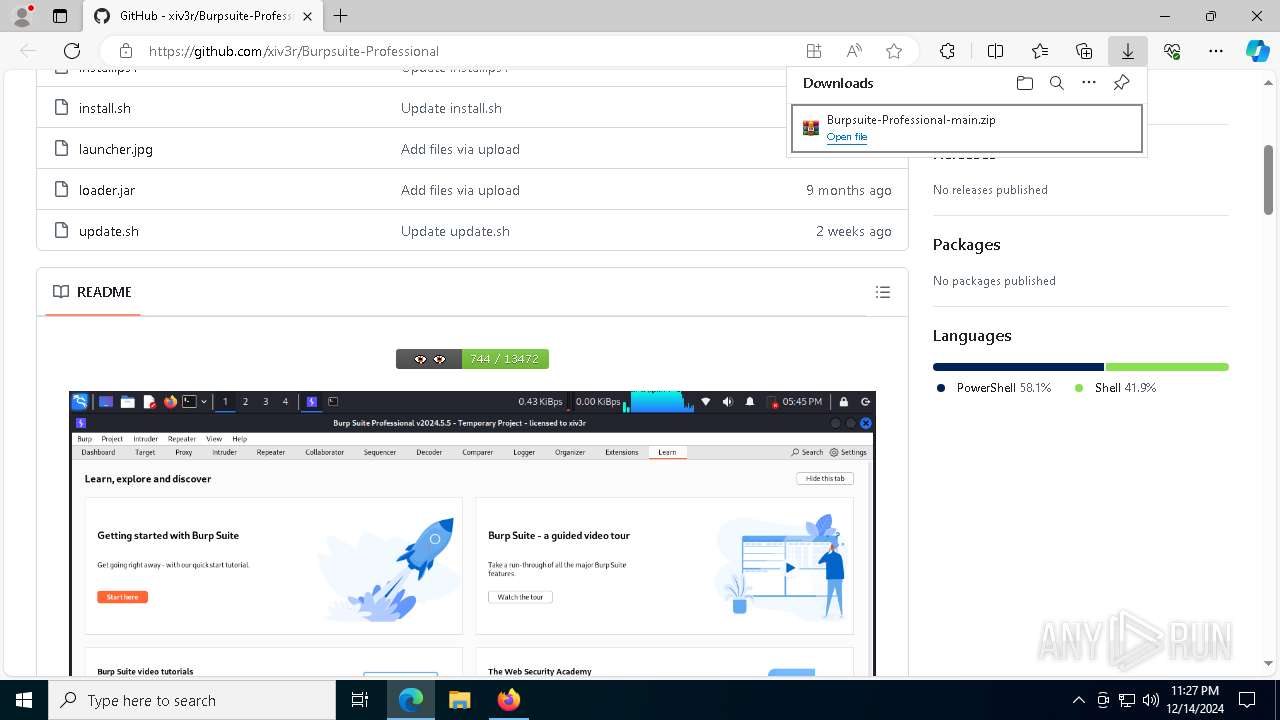
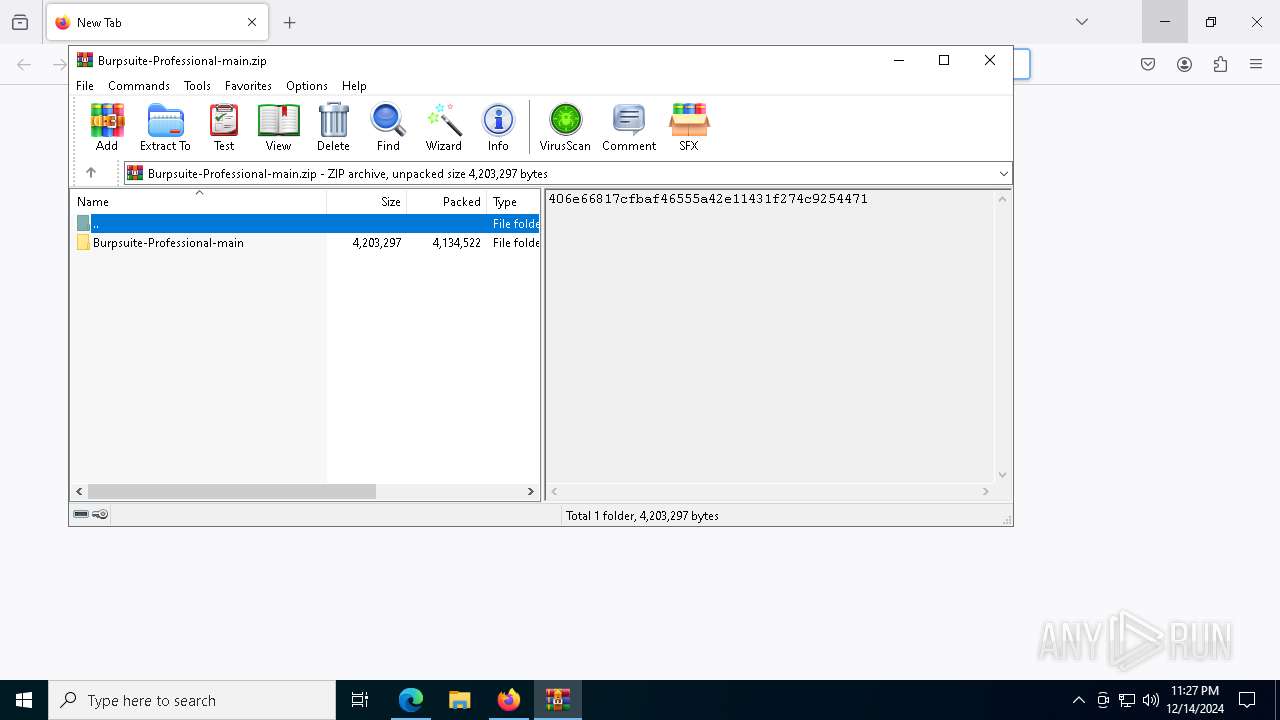
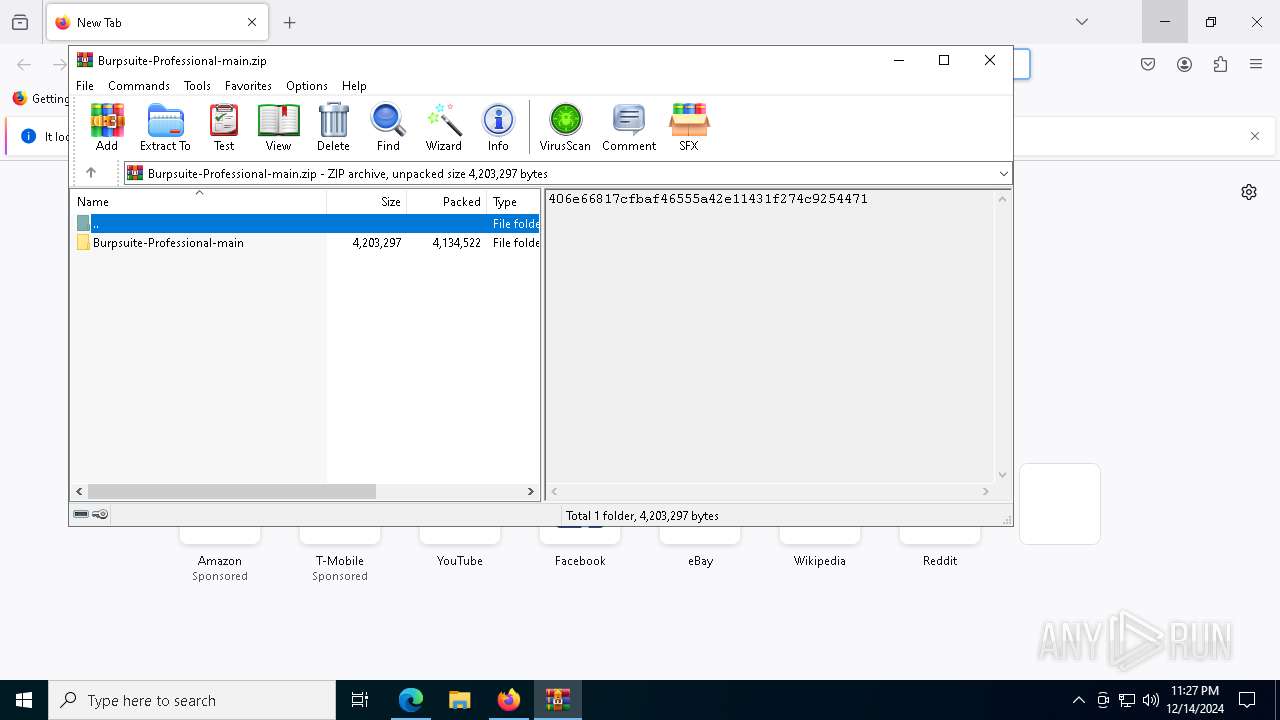
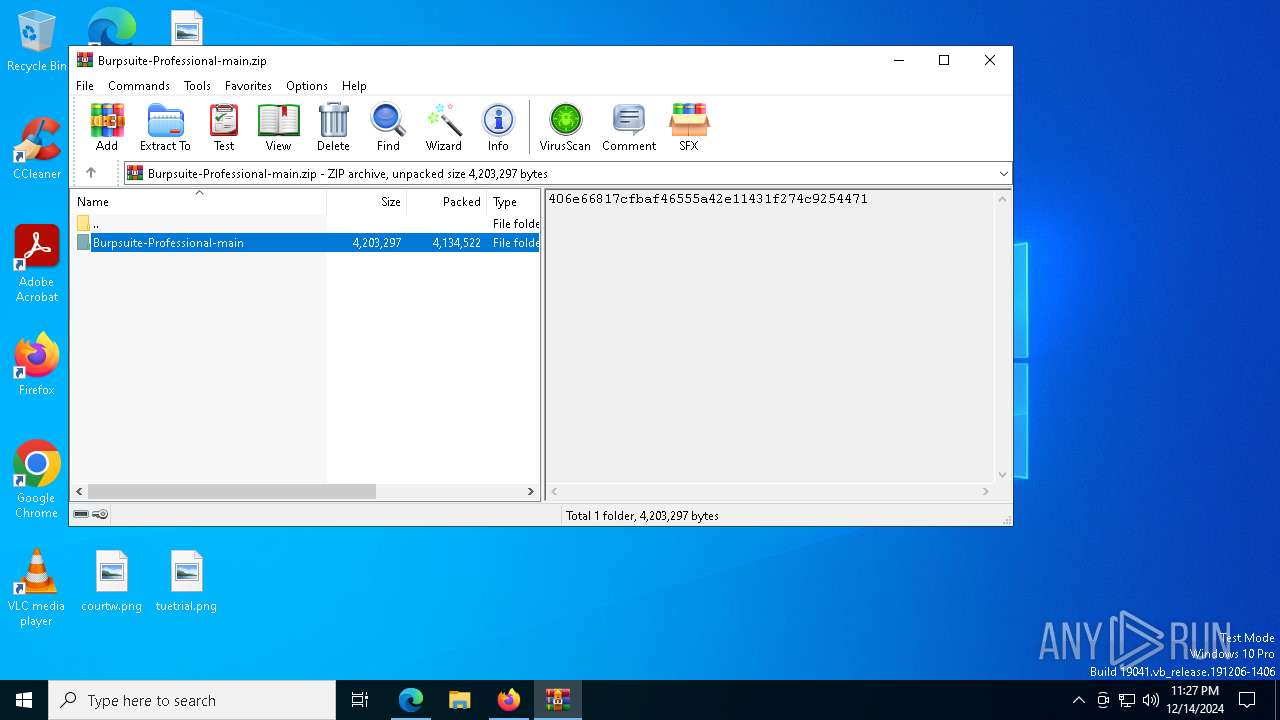
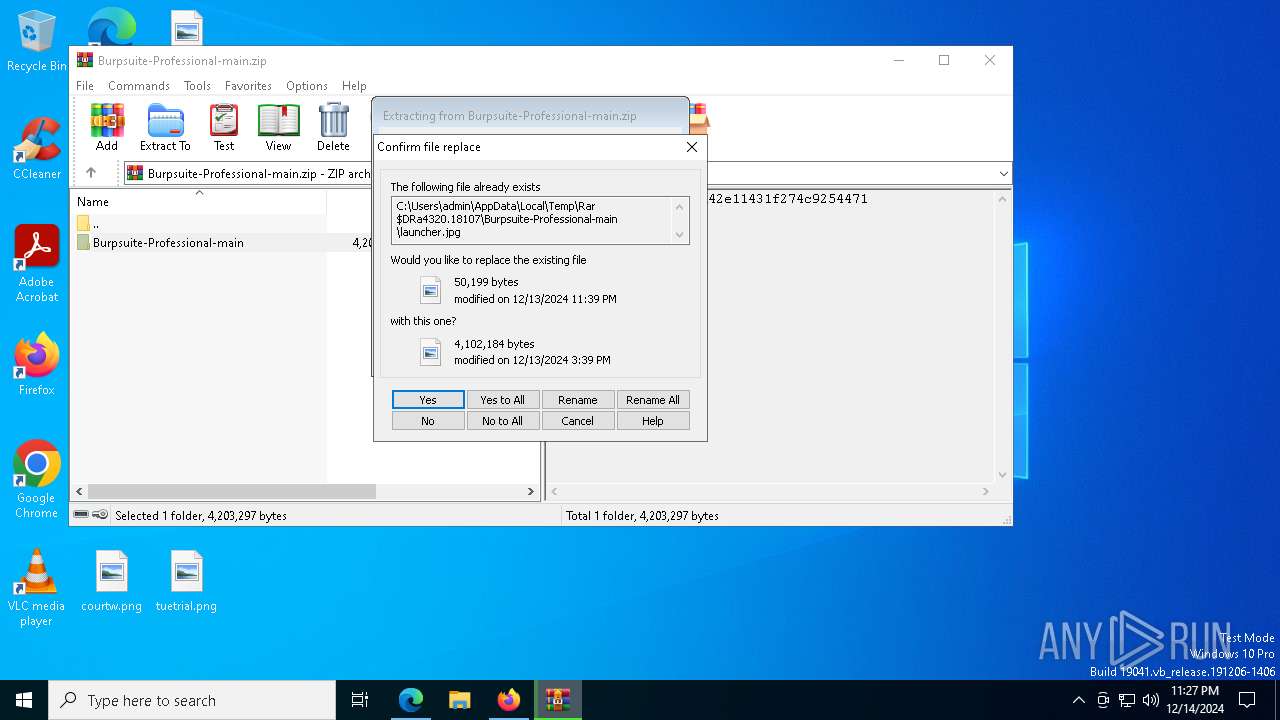
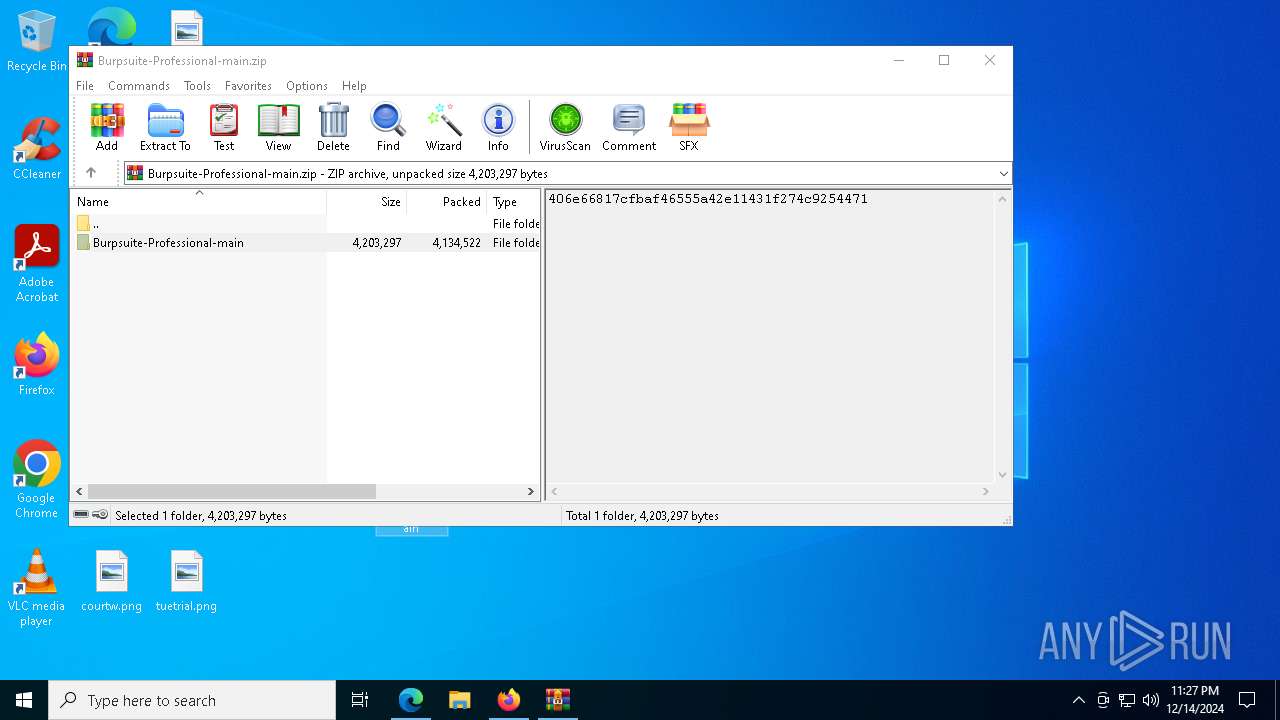
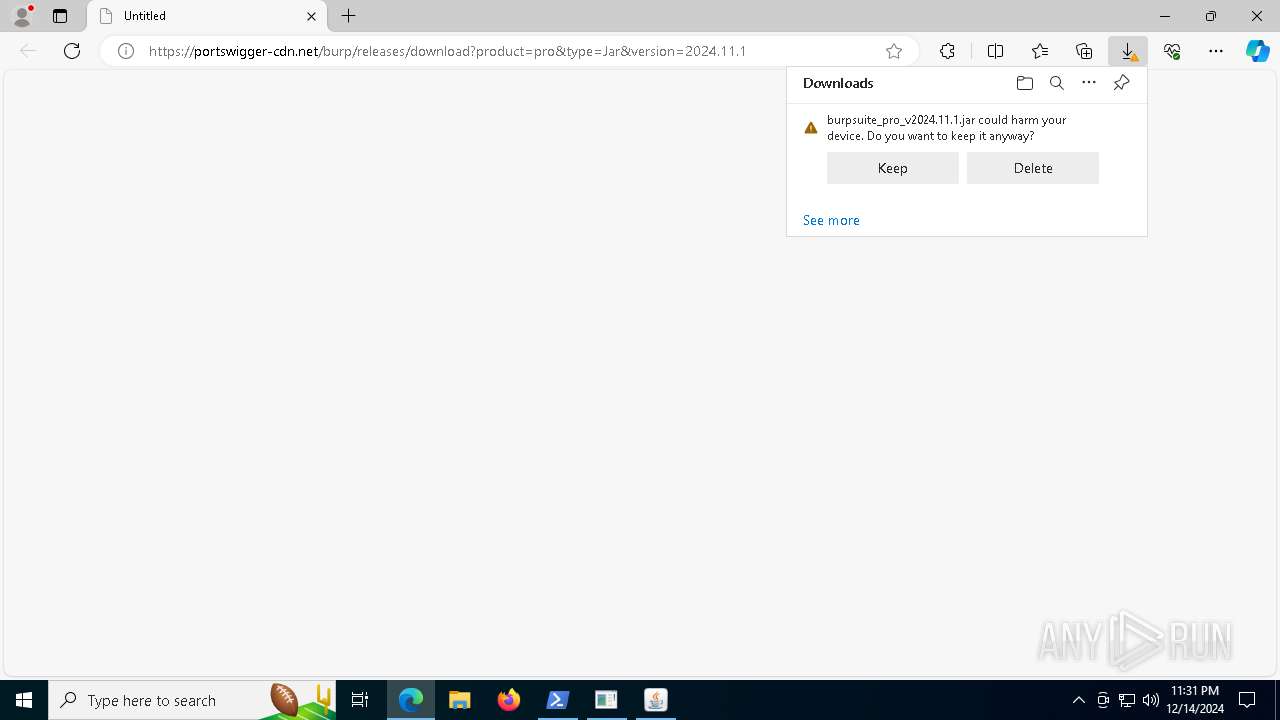
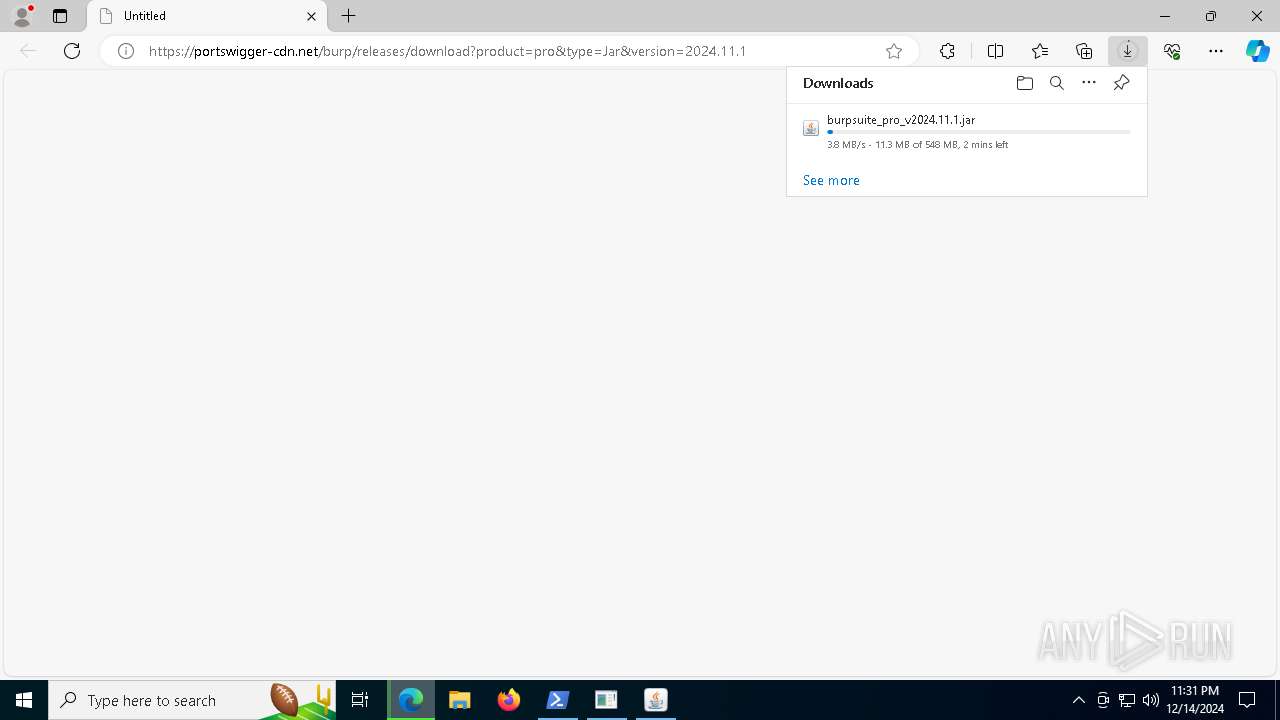
The process uses the downloaded file
- msedge.exe (PID: 7348)
- msedge.exe (PID: 2796)
- WinRAR.exe (PID: 4320)
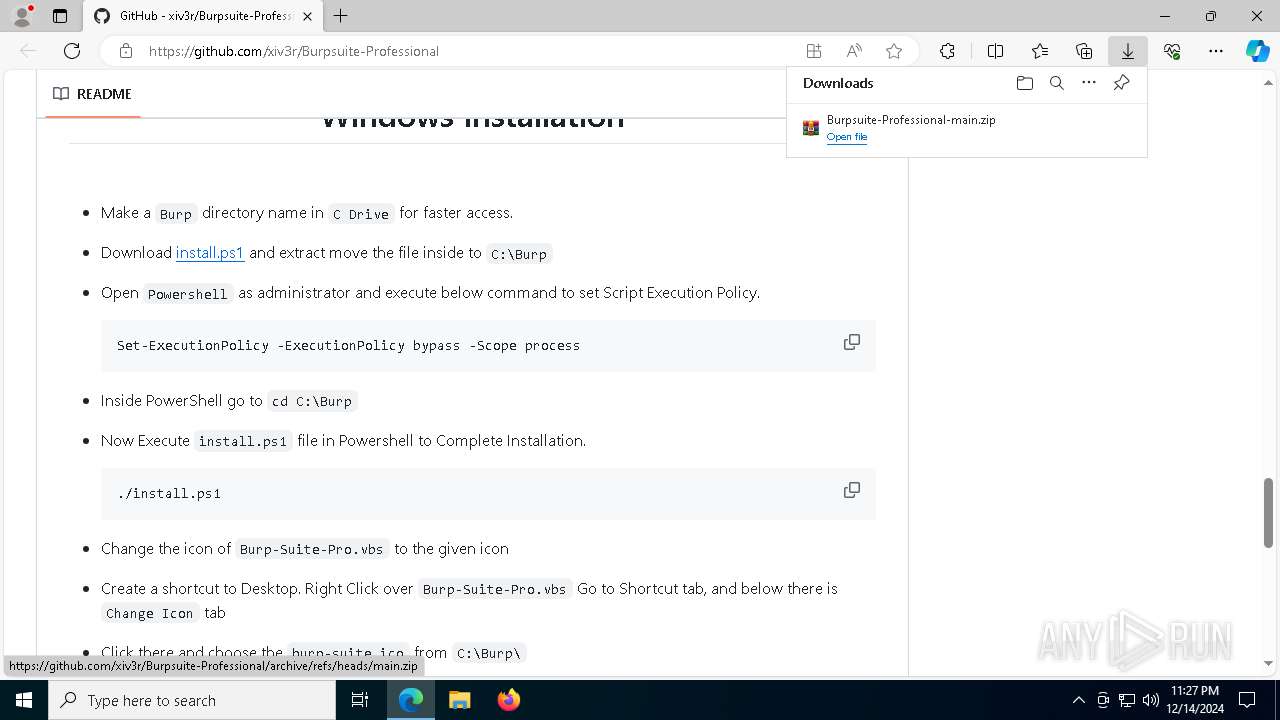
- powershell.exe (PID: 7916)
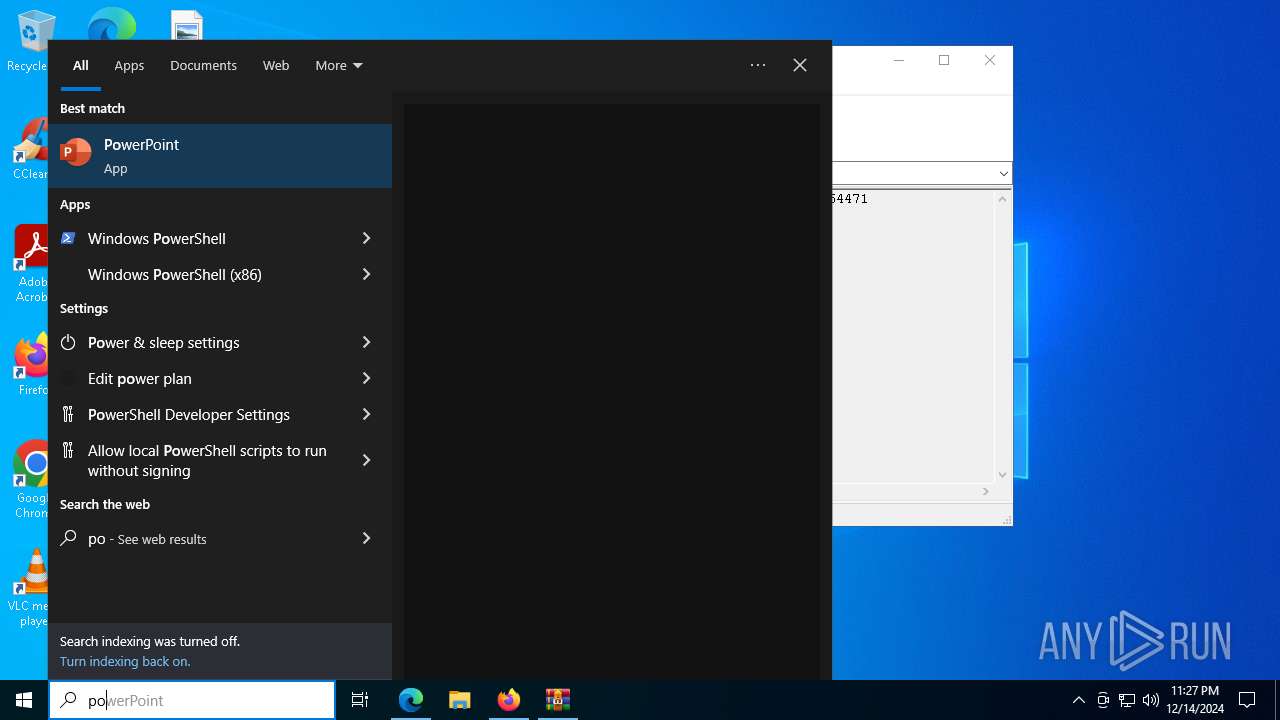
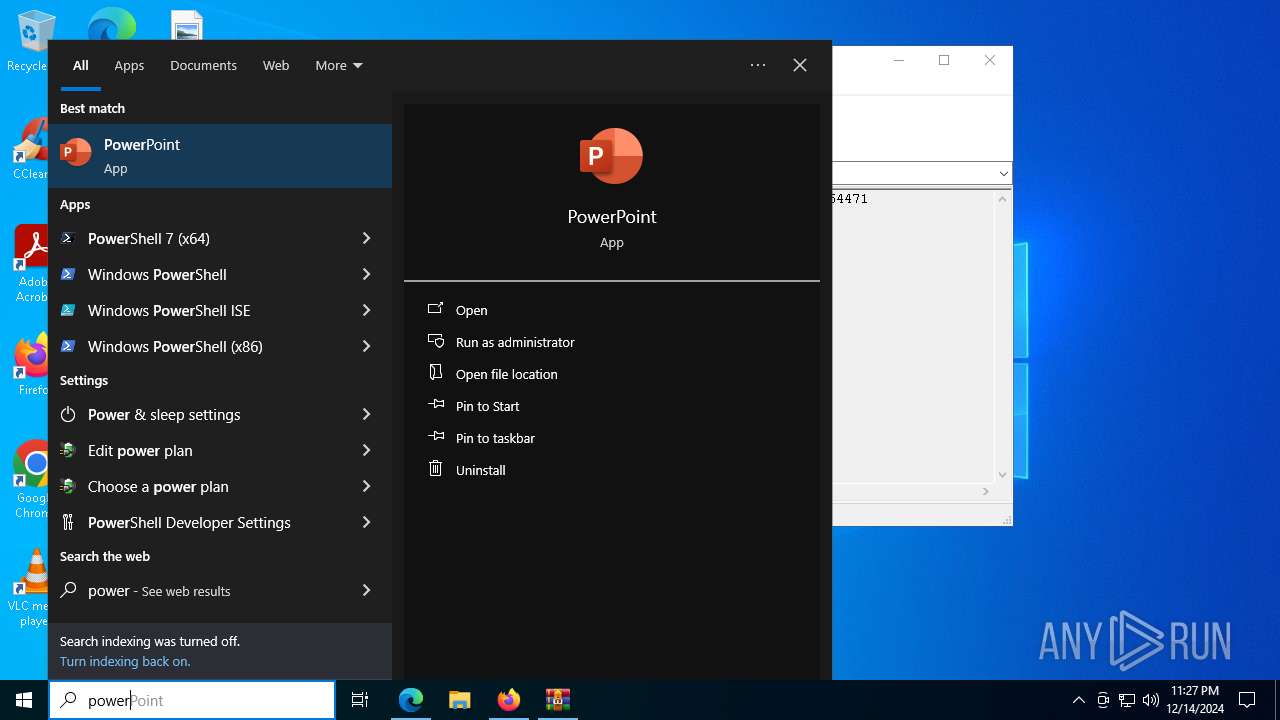
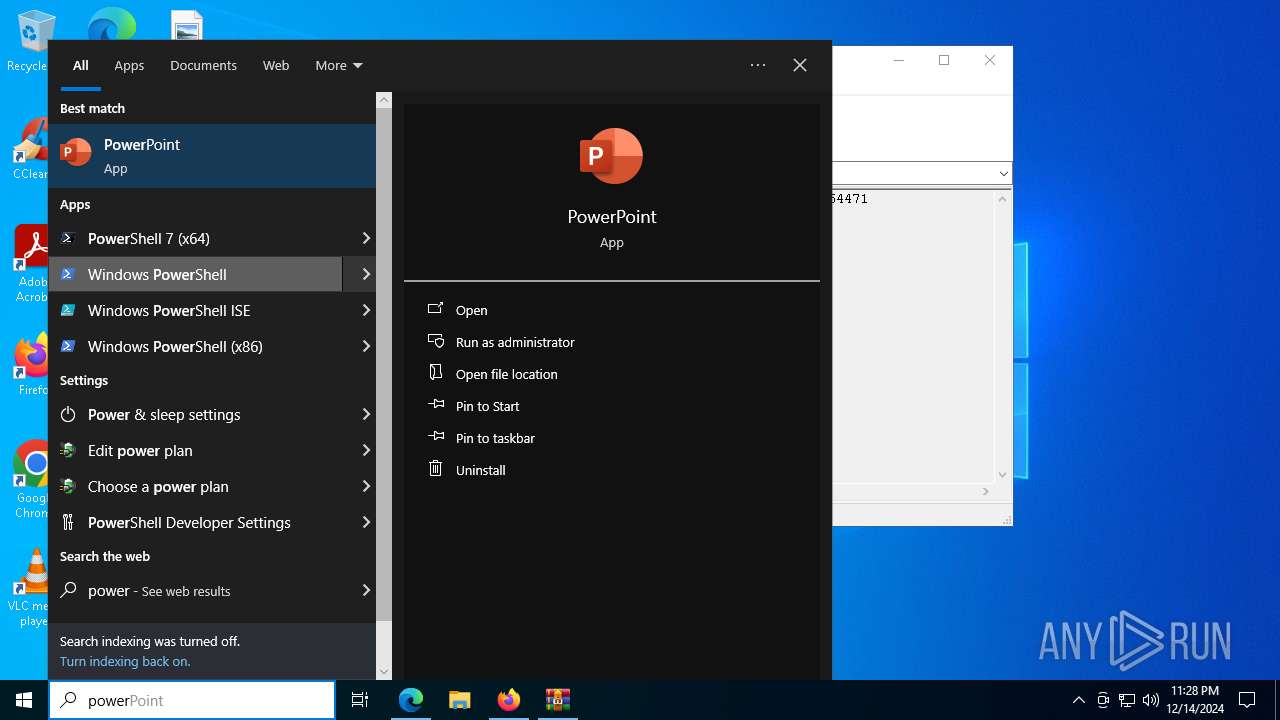
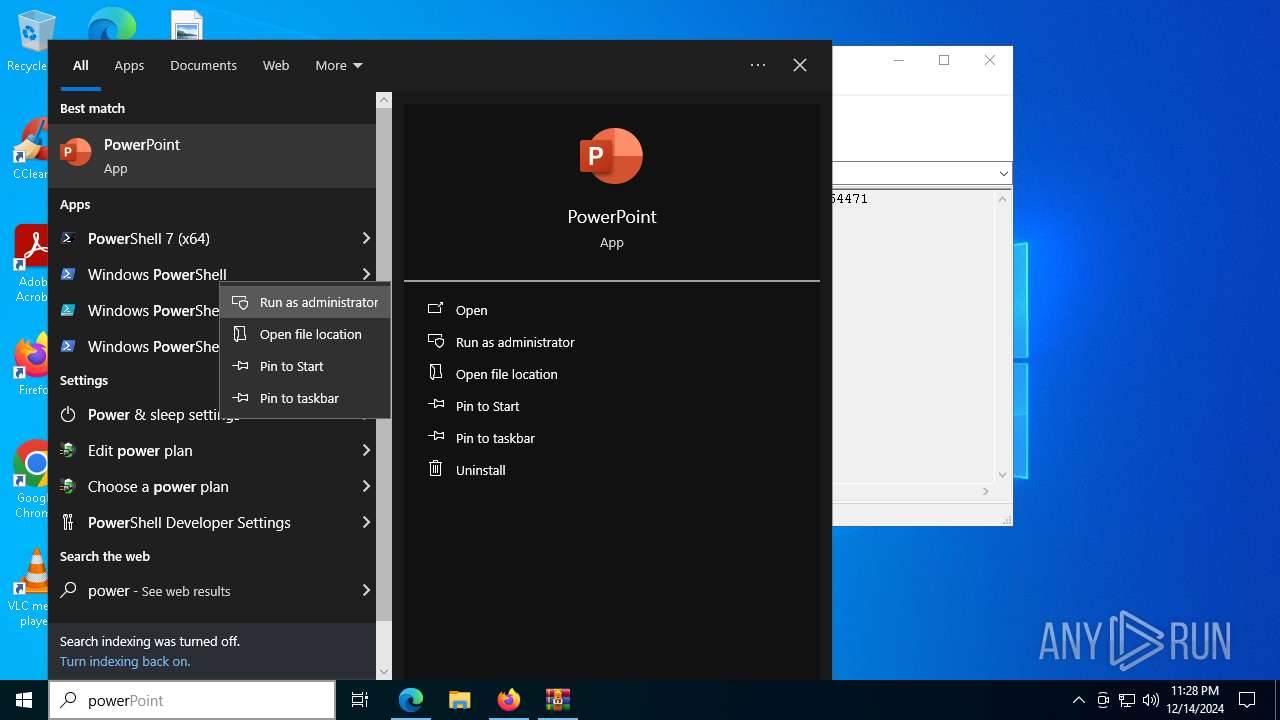
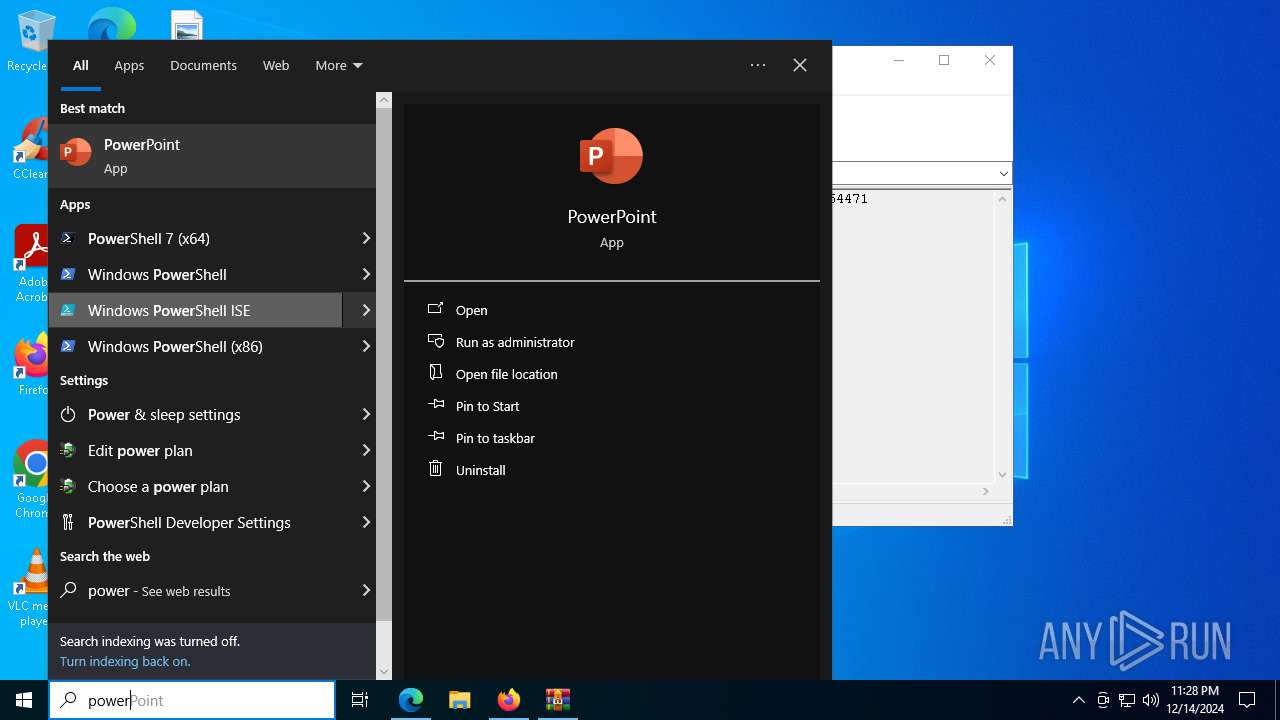
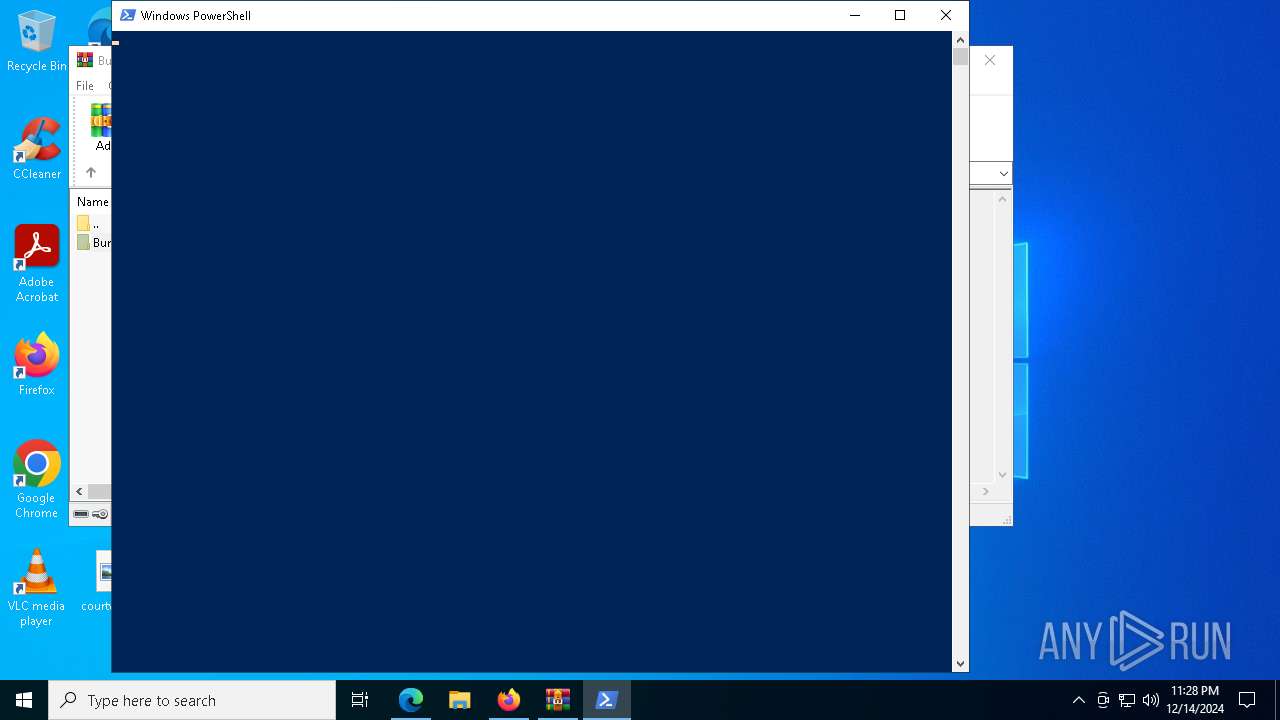
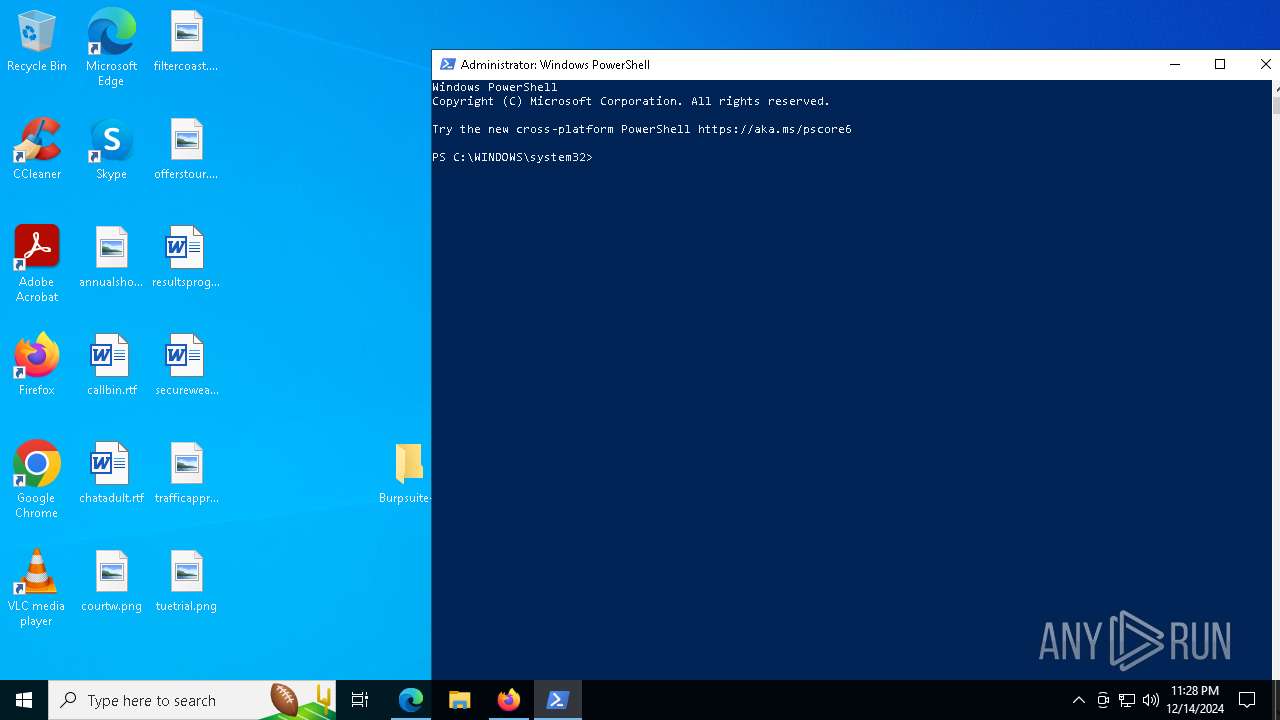
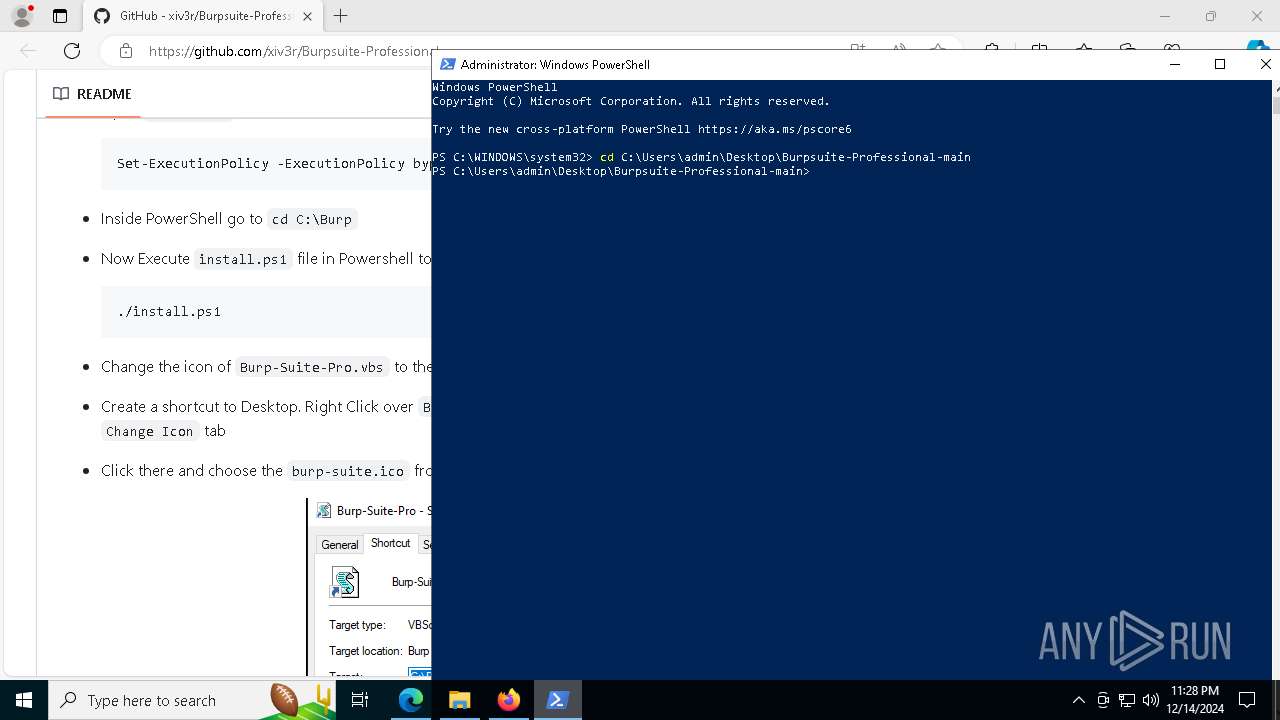
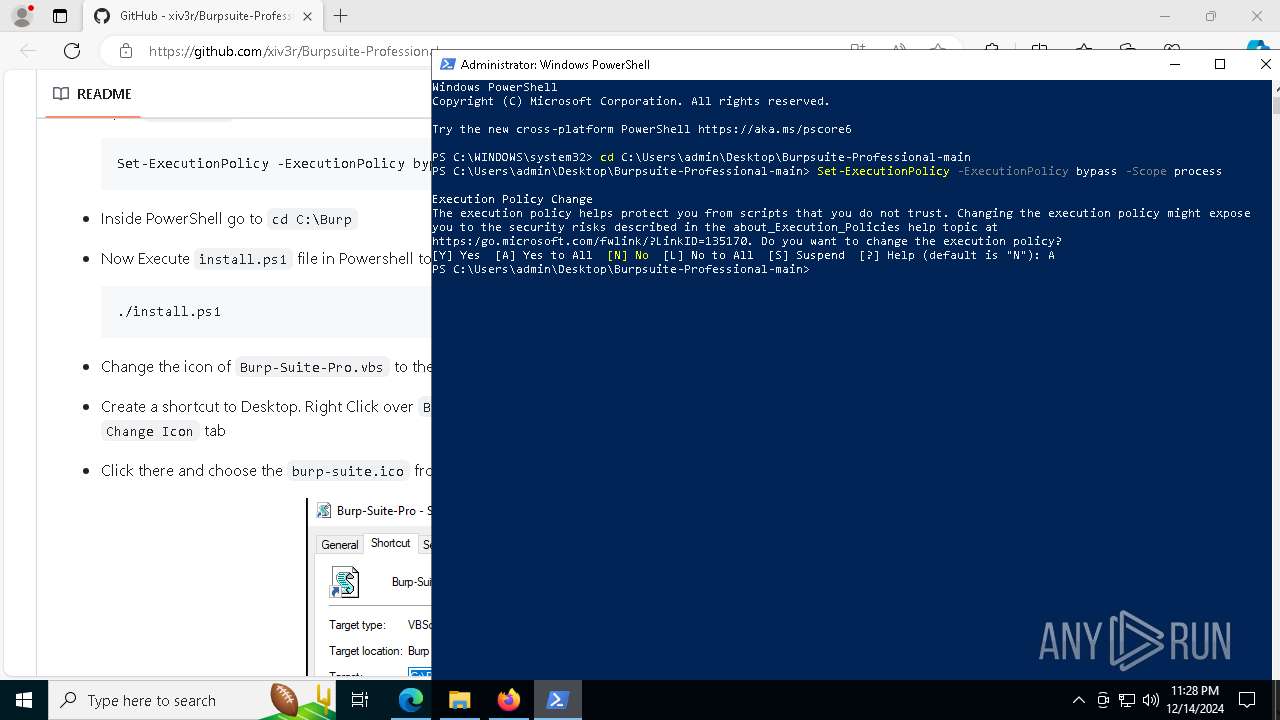
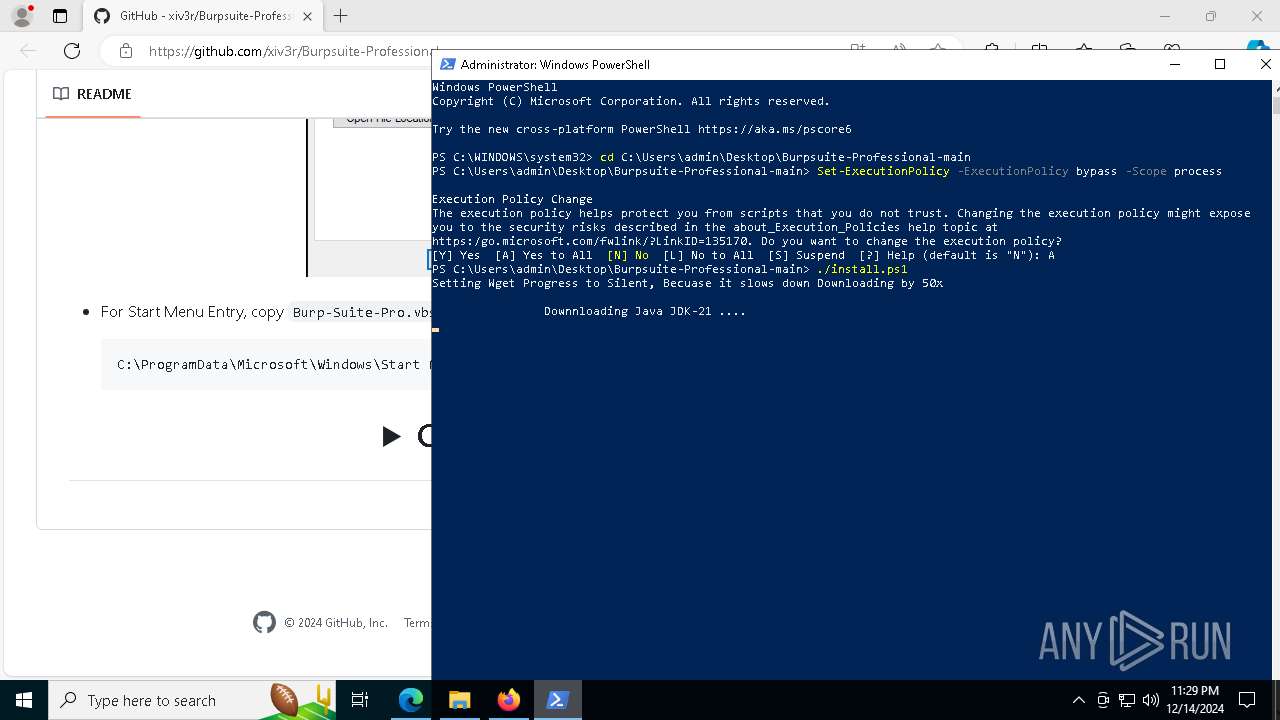
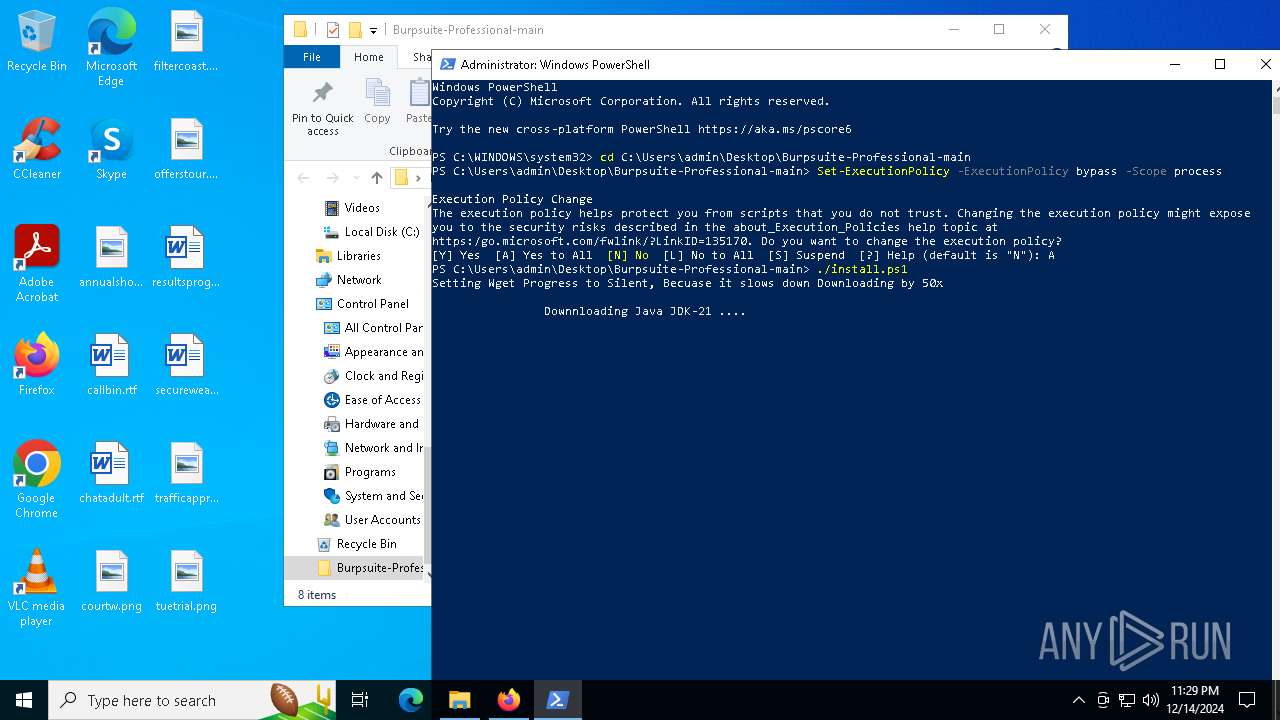
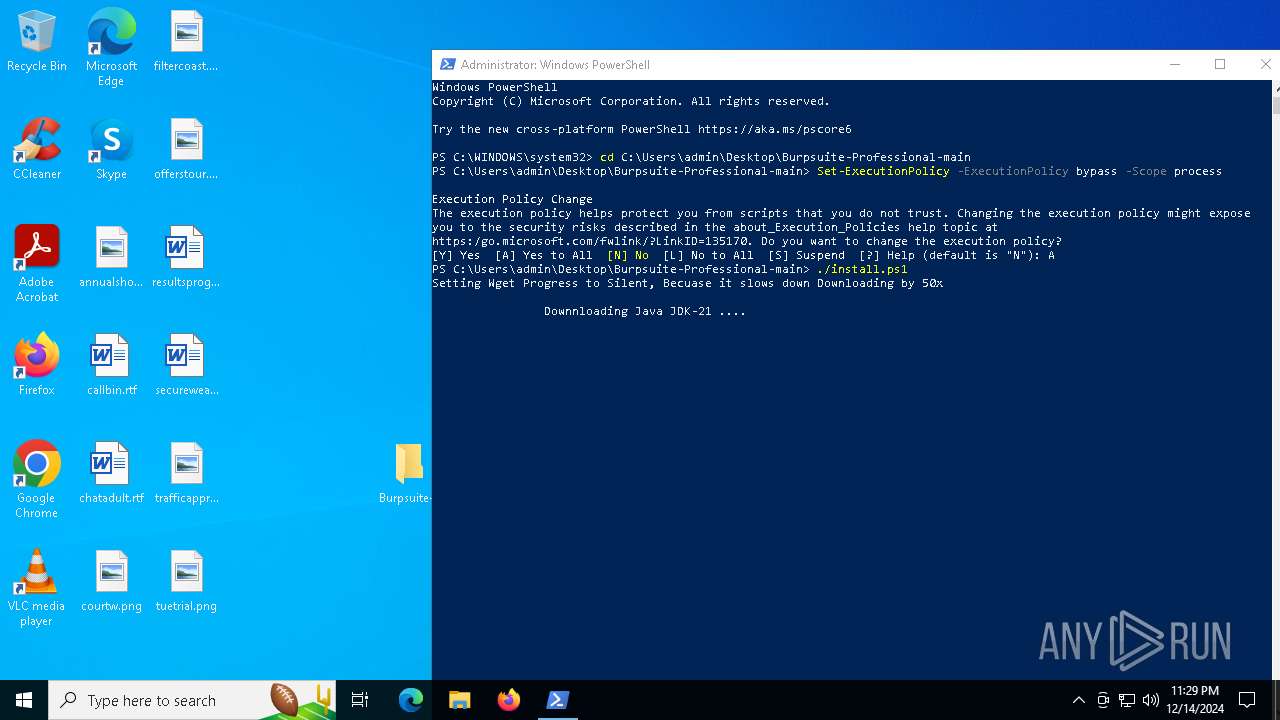
Manual execution by a user
- firefox.exe (PID: 7496)
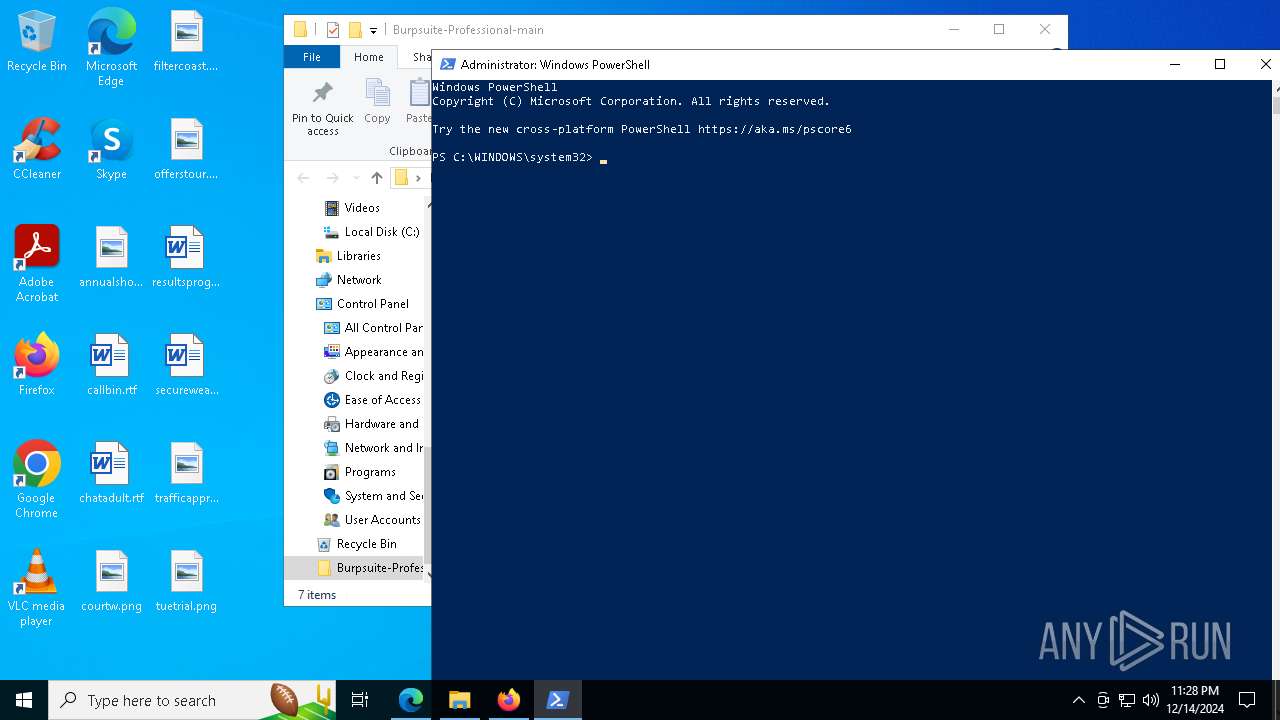
- powershell.exe (PID: 7916)
Reads Microsoft Office registry keys
- msedge.exe (PID: 2796)
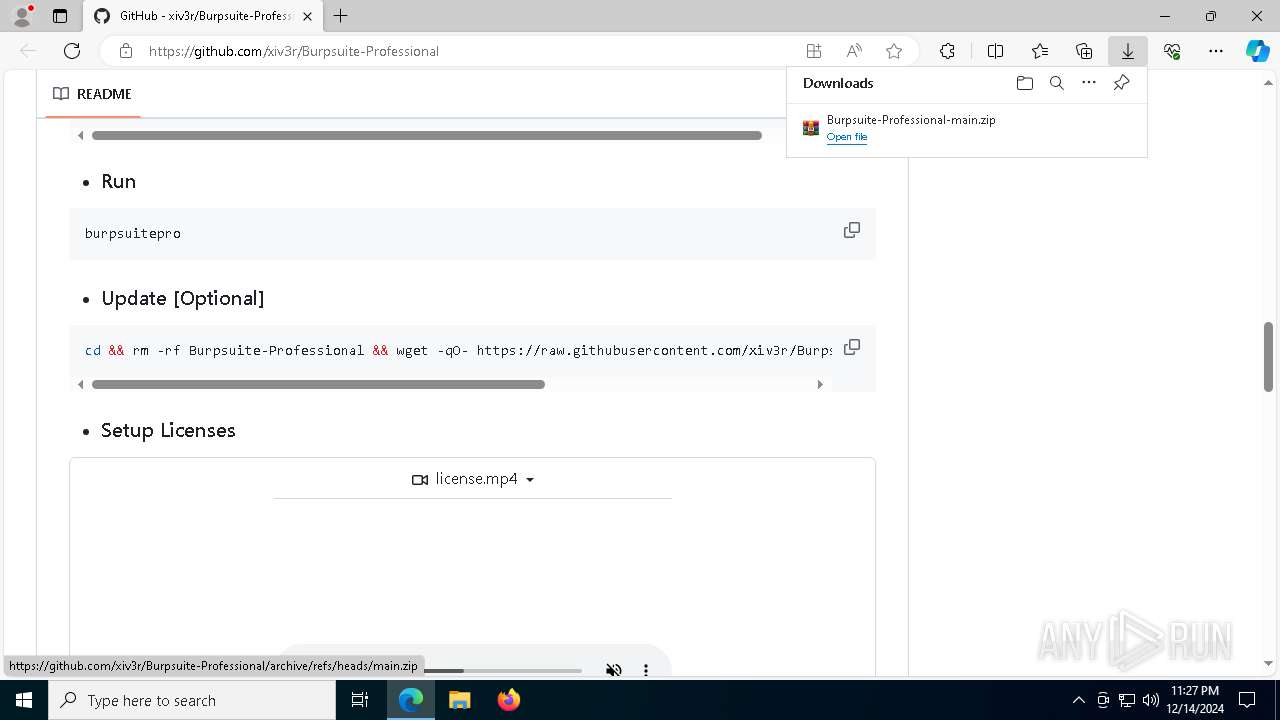
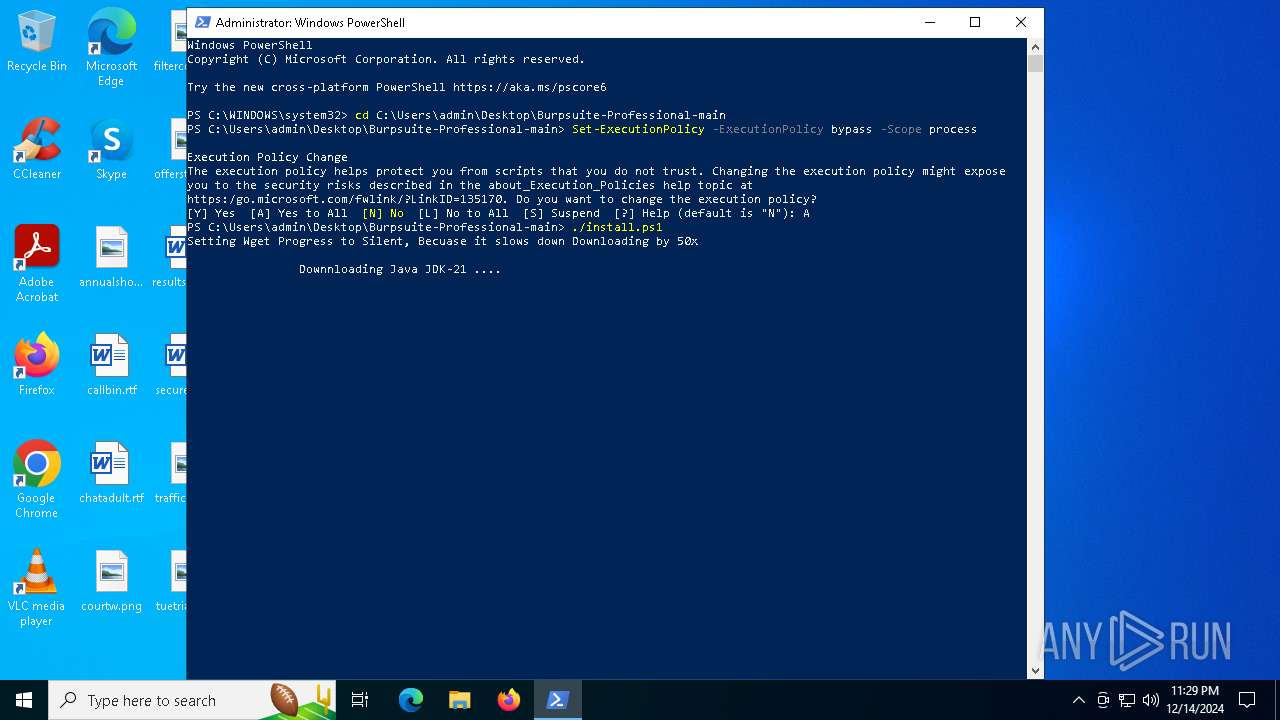
Checks current location (POWERSHELL)
- powershell.exe (PID: 7916)
Disables trace logs
- powershell.exe (PID: 7916)
Checks proxy server information
- powershell.exe (PID: 7916)
- msiexec.exe (PID: 6328)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6328)
- msiexec.exe (PID: 7144)
- msiexec.exe (PID: 7500)
- msedge.exe (PID: 5548)
Create files in a temporary directory
- jdk-21.exe (PID: 1476)
- msiexec.exe (PID: 6452)
- java.exe (PID: 7424)
- java.exe (PID: 1732)
- java.exe (PID: 7764)
- java.exe (PID: 7720)
- java.exe (PID: 4204)
- java.exe (PID: 6360)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 6328)
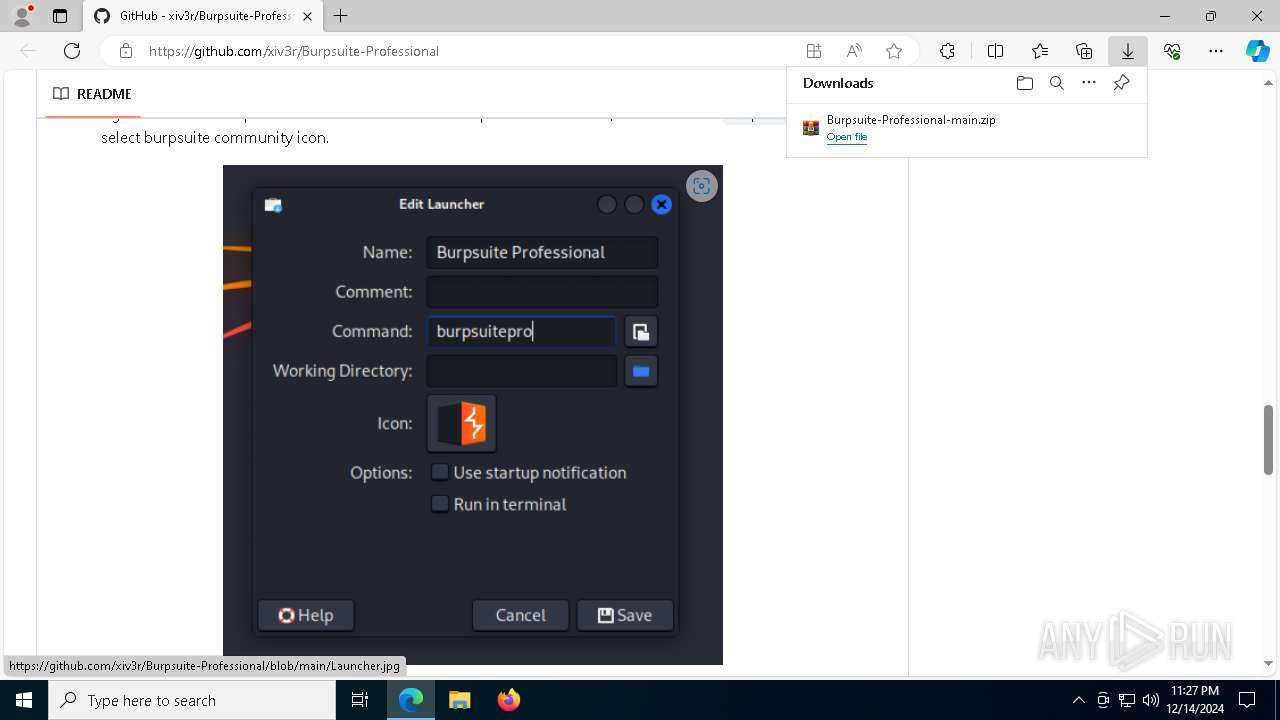
Creates files in the program directory
- jdk-21.exe (PID: 7688)
Creates files or folders in the user directory
- msiexec.exe (PID: 6328)
- jdk-21.exe (PID: 7688)
- java.exe (PID: 1732)
Reads the software policy settings
- msiexec.exe (PID: 6328)
- msiexec.exe (PID: 7144)
The sample compiled with english language support
- msiexec.exe (PID: 6328)
- msiexec.exe (PID: 7144)
- msiexec.exe (PID: 7500)
- msedge.exe (PID: 5548)
Manages system restore points
- SrTasks.exe (PID: 3532)
Reads the machine GUID from the registry
- msiexec.exe (PID: 7144)
- java.exe (PID: 8012)
- java.exe (PID: 7424)
- java.exe (PID: 1732)
Creates a software uninstall entry
- msiexec.exe (PID: 7144)
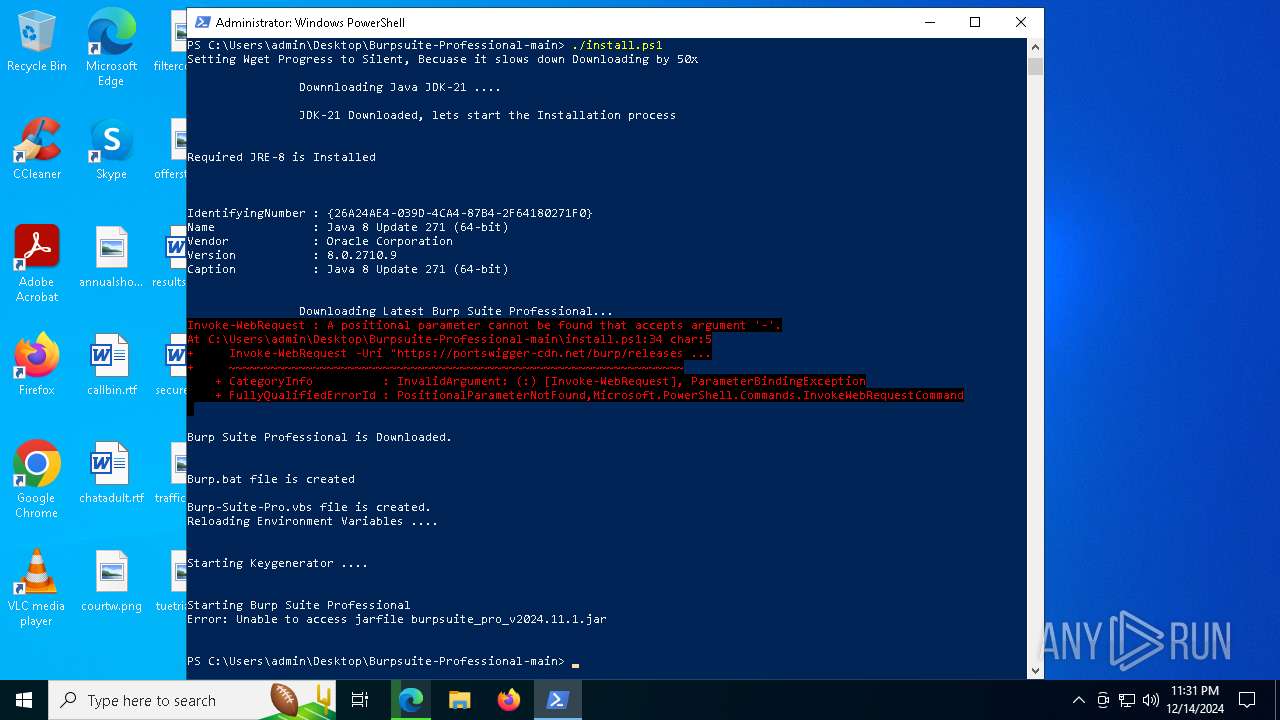
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7916)
Reads CPU info
- java.exe (PID: 1732)
- java.exe (PID: 7764)
- java.exe (PID: 7720)
- java.exe (PID: 4204)
- java.exe (PID: 6360)
Process checks computer location settings
- java.exe (PID: 1732)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
266
Monitored processes
125
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 900 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6564 --field-trial-handle=2332,i,9650496776468952998,2237112273956231222,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1140 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x290,0x294,0x298,0x288,0x2a0,0x7ff818615fd8,0x7ff818615fe4,0x7ff818615ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1348 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=1264 --field-trial-handle=2456,i,5045187356742599012,11132622453140863408,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
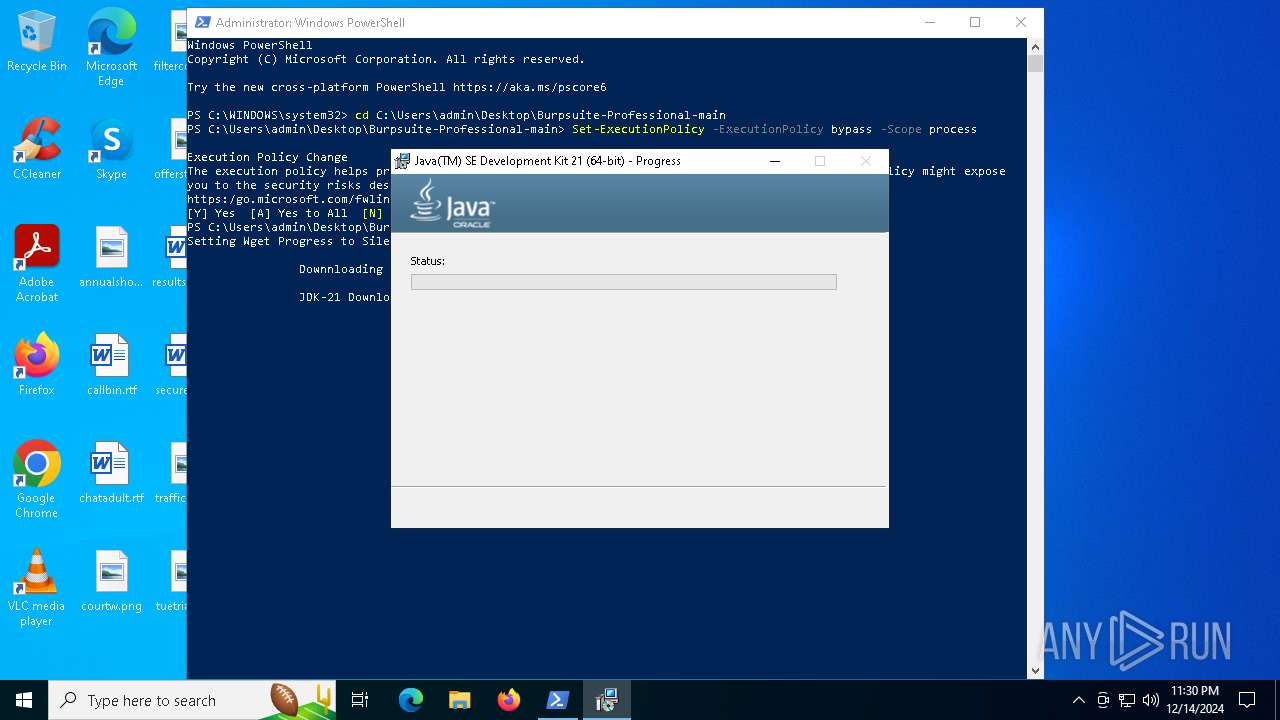
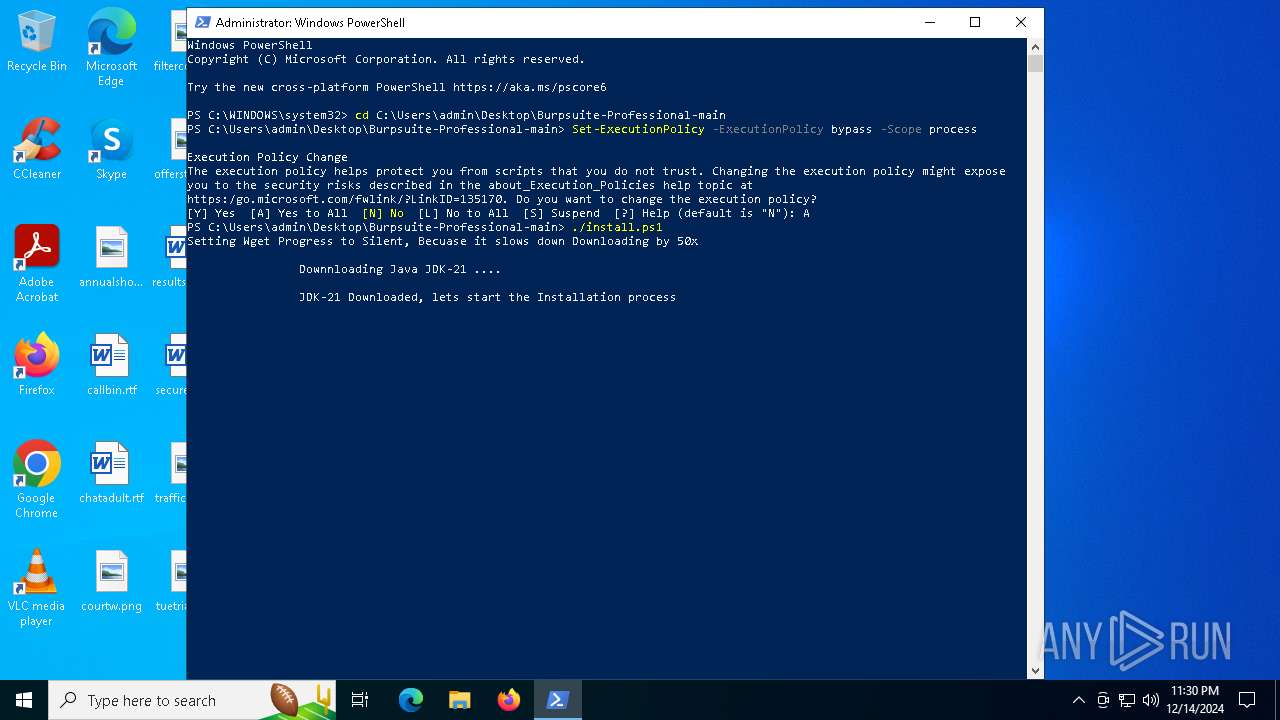
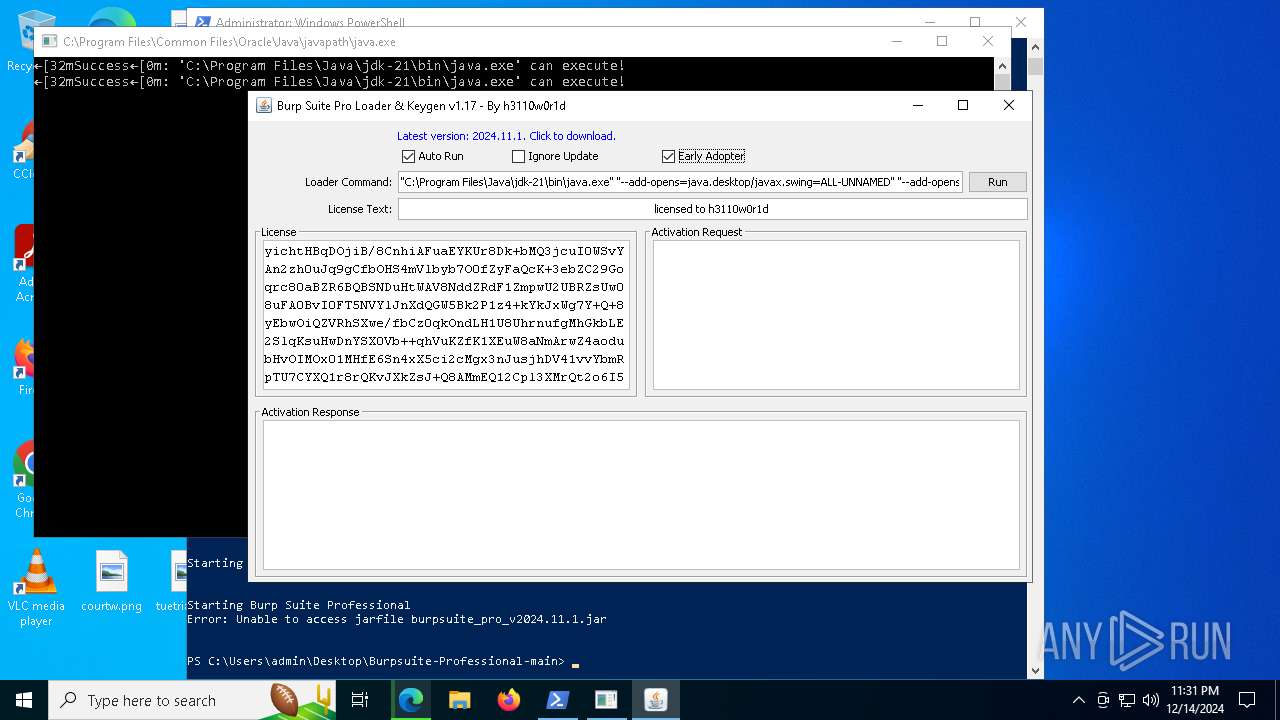
| 1476 | "C:\Users\admin\Desktop\Burpsuite-Professional-main\jdk-21.exe" | C:\Users\admin\Desktop\Burpsuite-Professional-main\jdk-21.exe | — | powershell.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 21.0.0.0 Modules
| |||||||||||||||
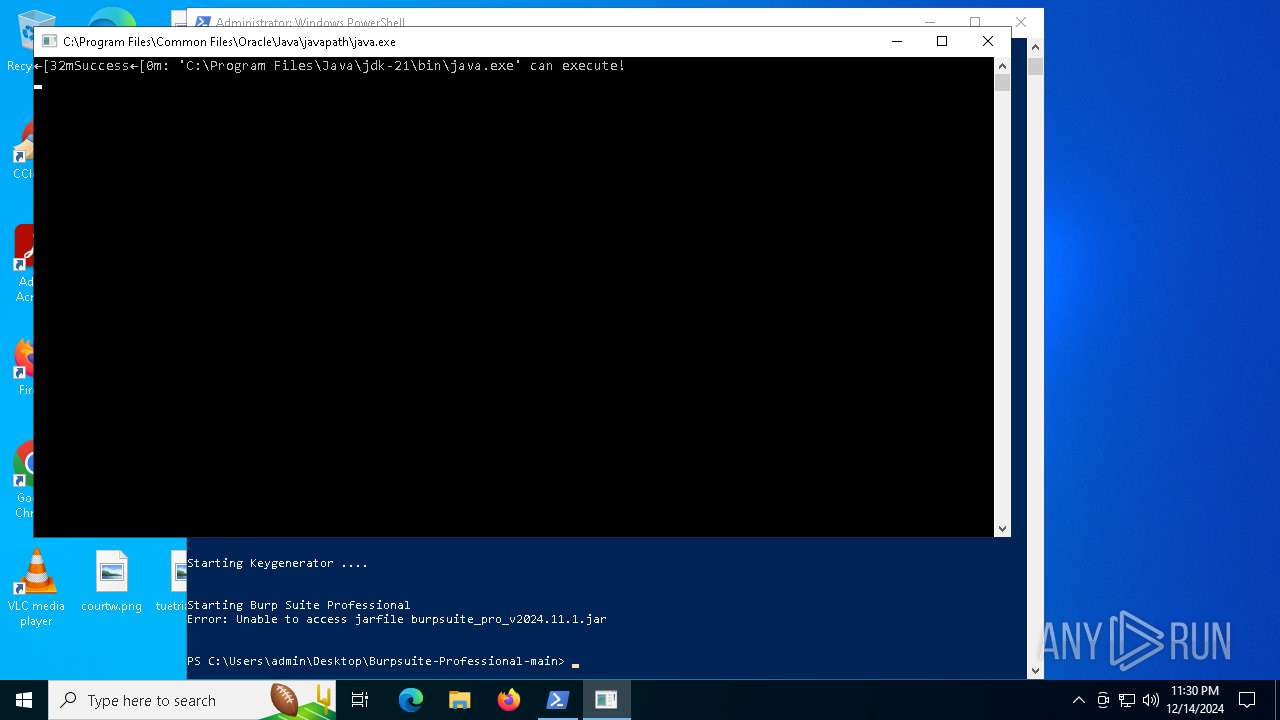
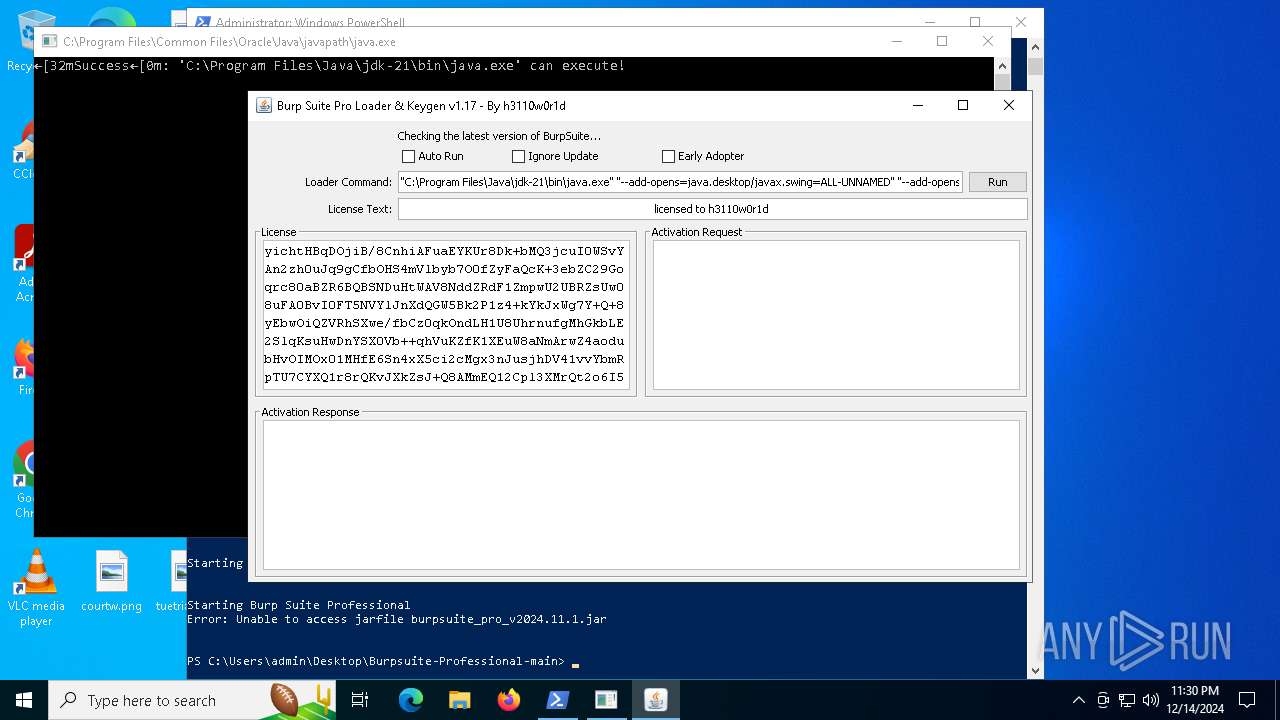
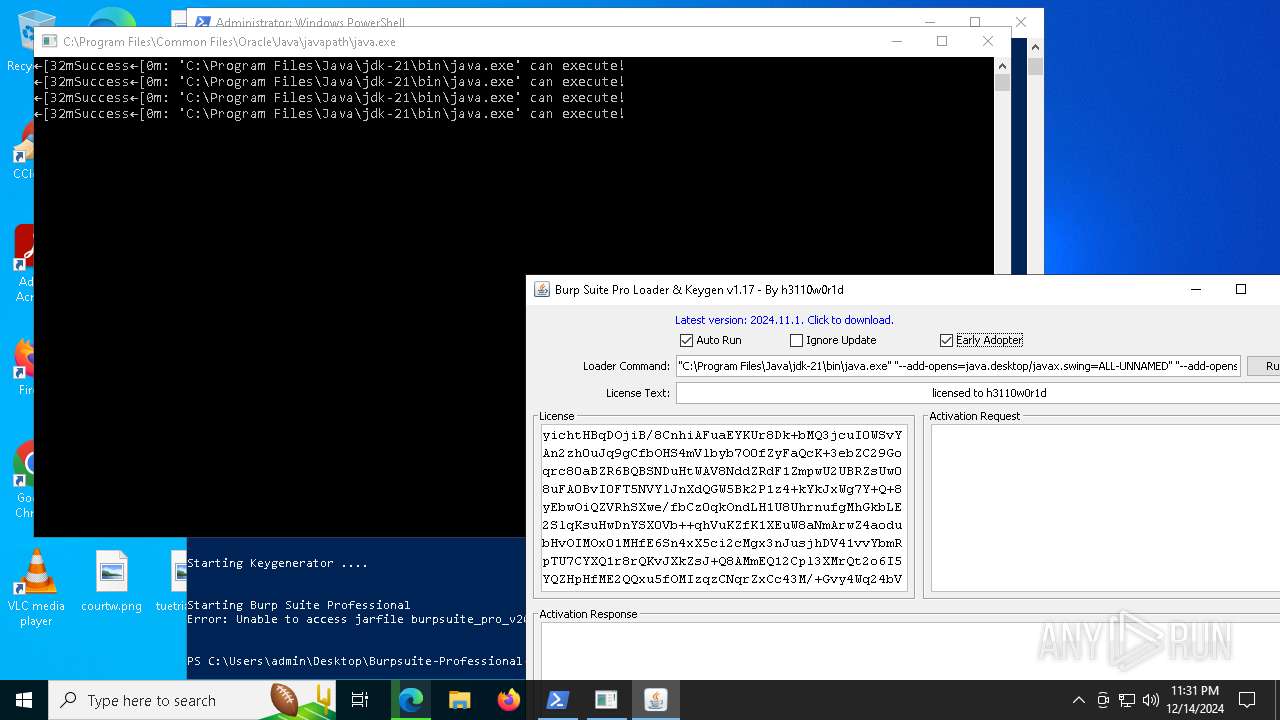
| 1732 | "C:\\Program Files\\Java\\jdk-21\\bin\\java.exe" -jar loader.jar | C:\Program Files\Java\jdk-21\bin\java.exe | java.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 21.0.0.0 Modules
| |||||||||||||||
| 1740 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5704 --field-trial-handle=2456,i,5045187356742599012,11132622453140863408,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1828 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6864 --field-trial-handle=2456,i,5045187356742599012,11132622453140863408,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2040 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6864 --field-trial-handle=2456,i,5045187356742599012,11132622453140863408,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2424 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2164 -parentBuildID 20240213221259 -prefsHandle 2156 -prefMapHandle 2152 -prefsLen 31031 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {cb51b8be-0511-4d68-b359-01a59cae4b16} 7524 "\\.\pipe\gecko-crash-server-pipe.7524" 26e4dd80710 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2572 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2248 --field-trial-handle=2332,i,9650496776468952998,2237112273956231222,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
40 881
Read events
40 506
Write events
350
Delete events
25
Modification events
| (PID) Process: | (2796) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2796) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2796) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2796) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2796) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: EF584B92D9872F00 | |||
| (PID) Process: | (2796) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 12685492D9872F00 | |||
| (PID) Process: | (2796) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262814 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {995005E8-4D9D-4662-98B6-660C7E920633} | |||
| (PID) Process: | (2796) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262814 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {647D4B00-8B23-495F-A3A0-693BAC74A4A2} | |||
| (PID) Process: | (2796) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262814 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {5022D476-A62B-4475-B38C-94409D90E6F8} | |||
| (PID) Process: | (2796) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262814 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {2B7A6305-C595-428D-A938-5058973C694E} | |||
Executable files
166
Suspicious files
826
Text files
396
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2796 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF13517e.TMP | — | |
MD5:— | SHA256:— | |||
| 2796 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2796 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF13517e.TMP | — | |
MD5:— | SHA256:— | |||
| 2796 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2796 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF13517e.TMP | — | |
MD5:— | SHA256:— | |||
| 2796 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2796 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF13518e.TMP | — | |
MD5:— | SHA256:— | |||
| 2796 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2796 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF13518e.TMP | — | |
MD5:— | SHA256:— | |||
| 2796 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
86
TCP/UDP connections
177
DNS requests
212
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
640 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
6900 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 418 b | whitelisted |
4872 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | US | binary | 471 b | whitelisted |
6900 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
7524 | firefox.exe | POST | 200 | 184.24.77.67:80 | http://r11.o.lencr.org/ | DE | binary | 504 b | whitelisted |
7524 | firefox.exe | POST | 200 | 142.250.185.99:80 | http://o.pki.goog/s/wr3/yvU | US | binary | 472 b | whitelisted |
7524 | firefox.exe | POST | 200 | 184.24.77.67:80 | http://r11.o.lencr.org/ | DE | binary | 504 b | whitelisted |
7524 | firefox.exe | POST | 200 | 184.24.77.67:80 | http://r11.o.lencr.org/ | DE | binary | 504 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
640 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
640 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 104.126.37.131:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6472 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2796 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| shared |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6472 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
6472 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
6472 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
6472 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |