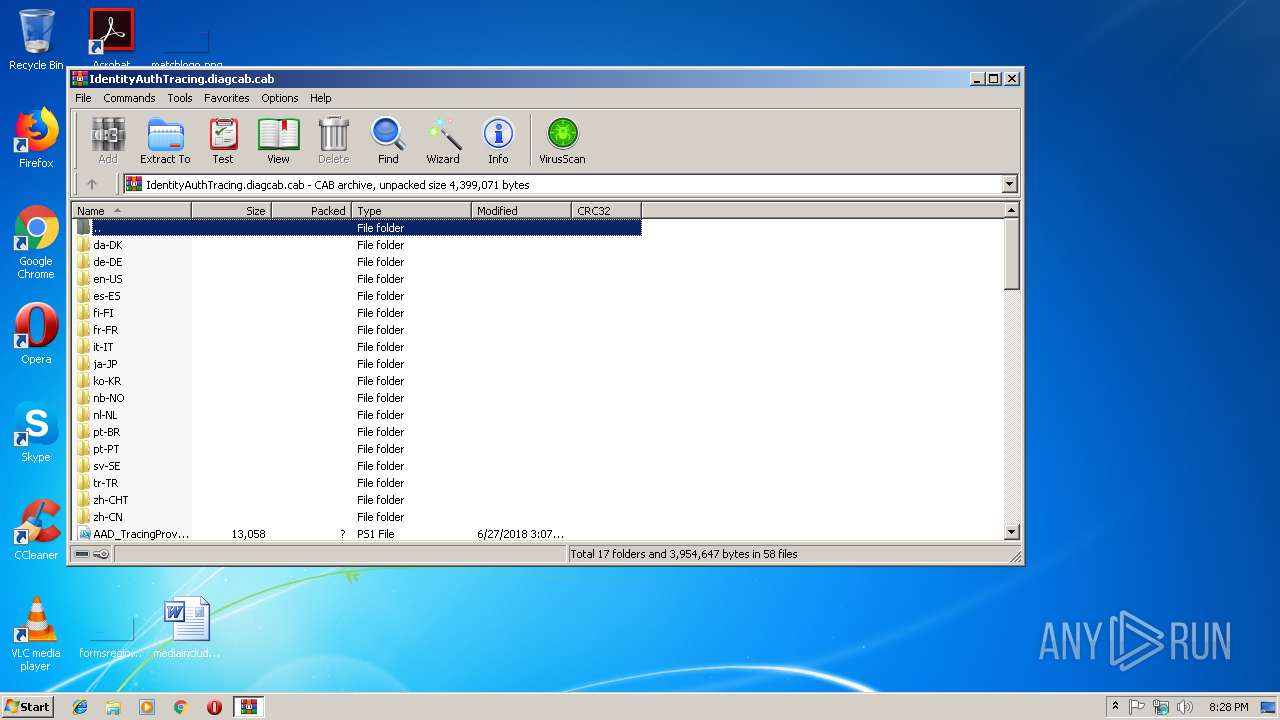
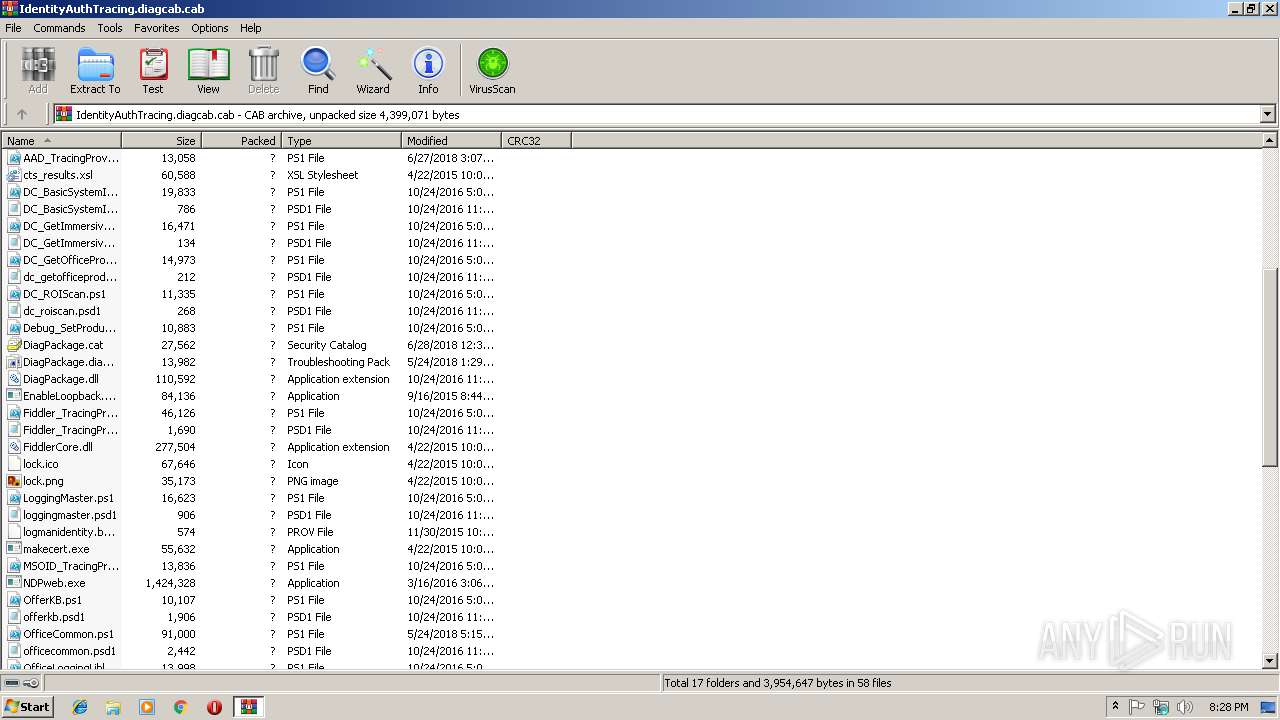
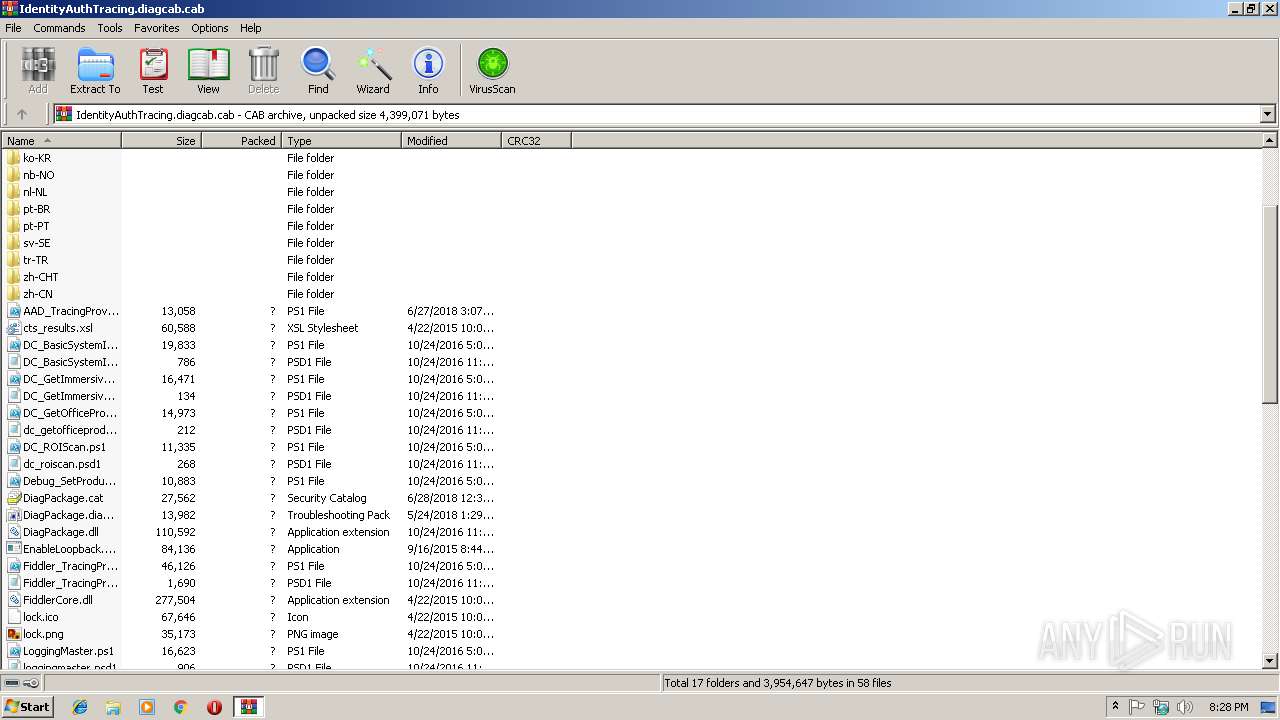
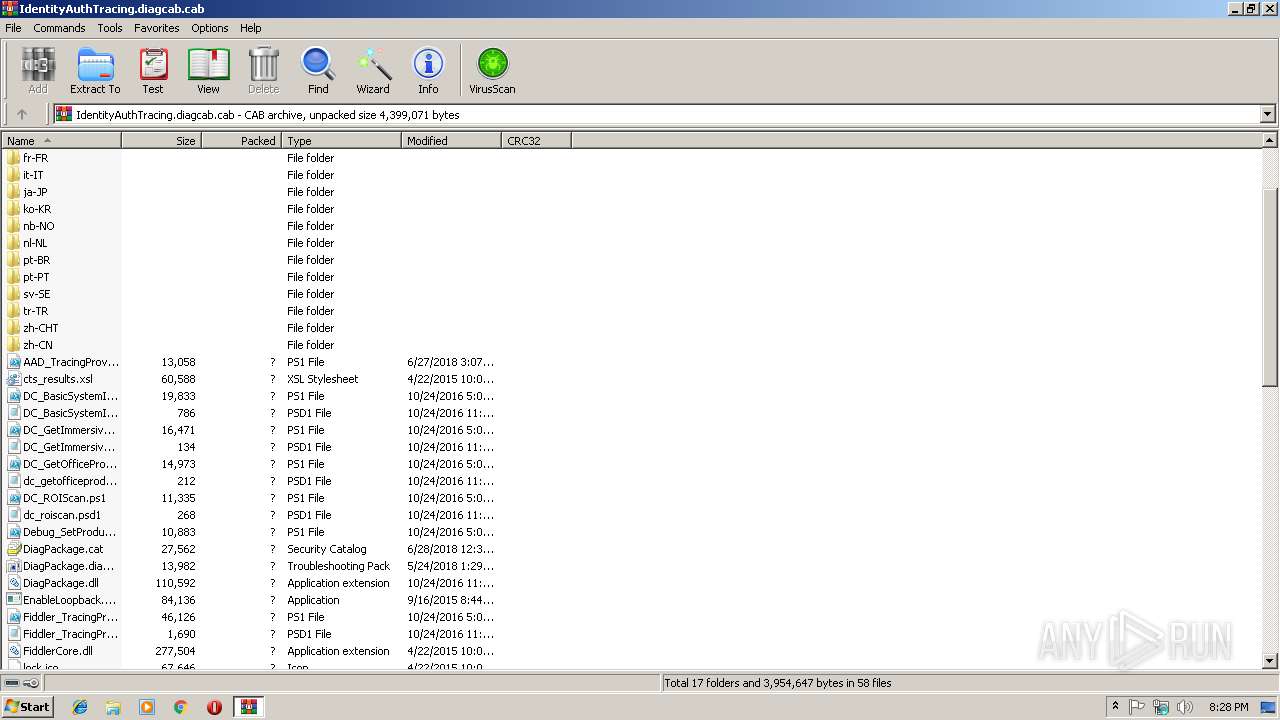
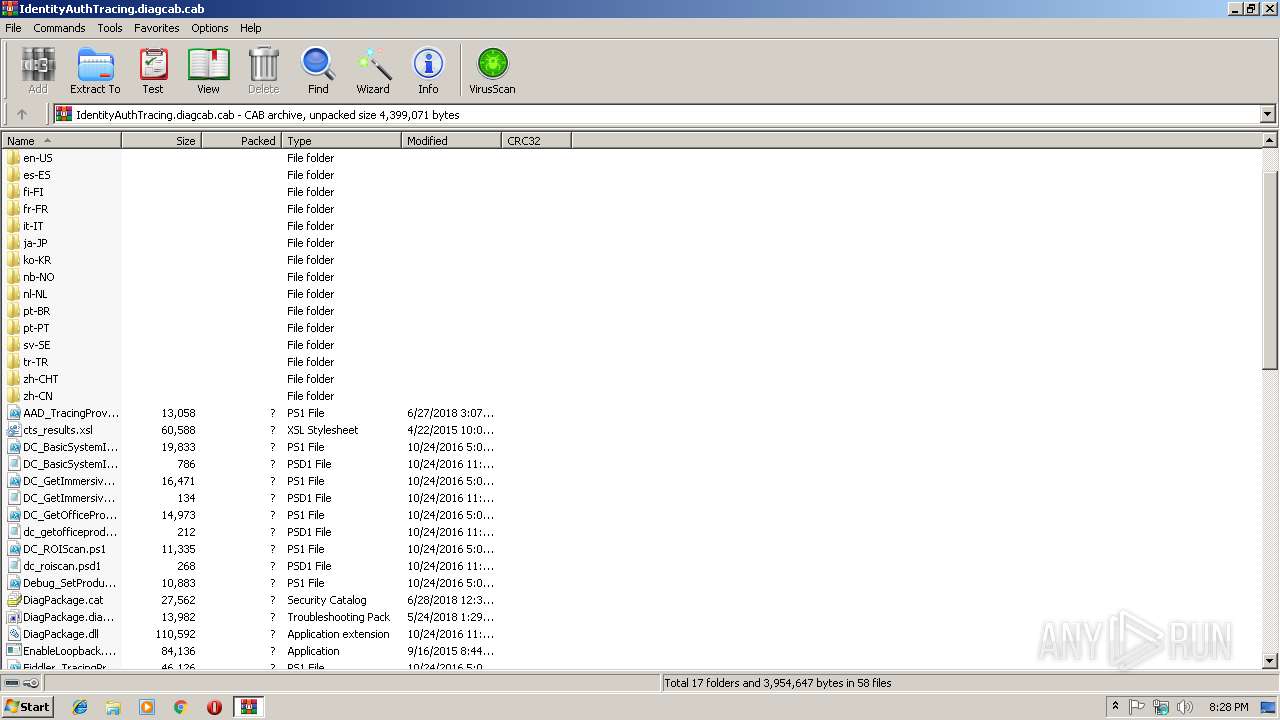
| File name: | IdentityAuthTracing.diagcab |
| Full analysis: | https://app.any.run/tasks/16212a92-4583-4b7b-94fa-96dcdb188a8c |
| Verdict: | No threats detected |
| Analysis date: | January 02, 2019, 20:27:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
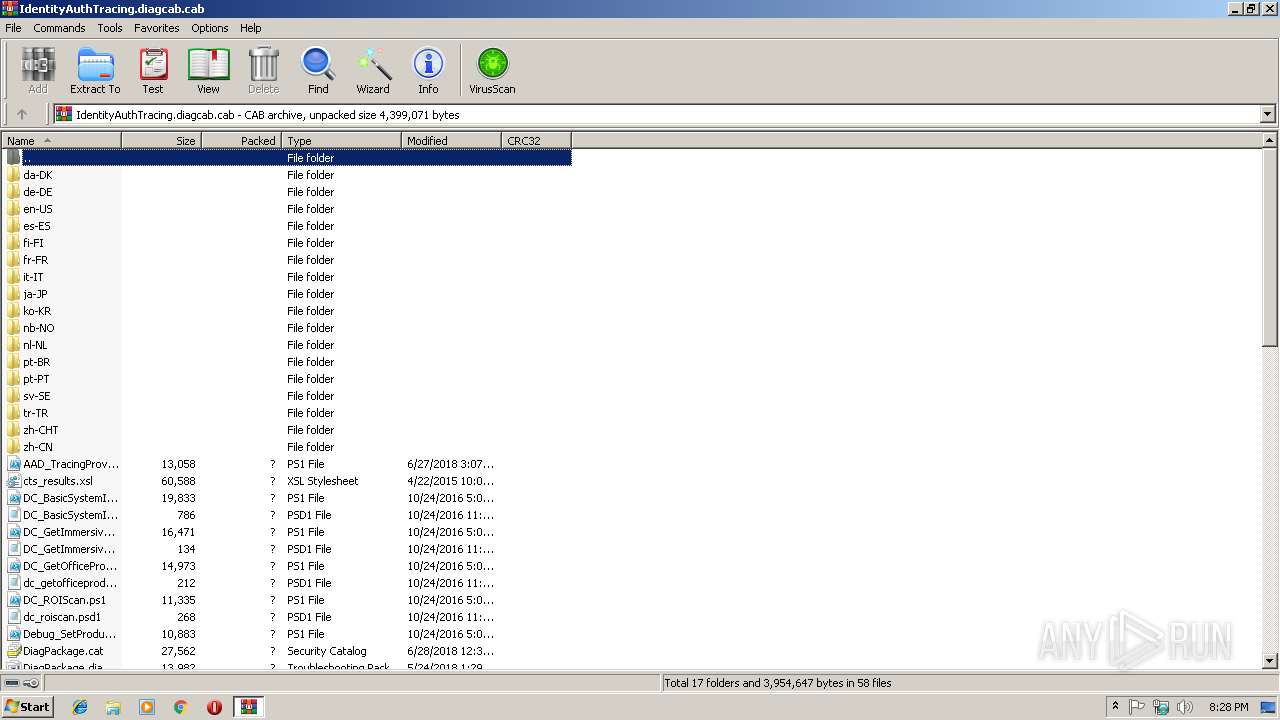
| MIME: | application/vnd.ms-cab-compressed |
| File info: | Microsoft Cabinet archive data, 2168772 bytes, 296 files |
| MD5: | 47E5152CAA0A057B9E1E653895D9266D |
| SHA1: | 2BDFE2636854EB16ADD3E1EECE00A8561B7838AD |
| SHA256: | 3D951C7964FBA008DE2B8CCEDDD74F4A4B015C70787D4922E46E37E7C75E19E0 |
| SSDEEP: | 49152:StH4g53E/AiD117wxF8Ae24iEIvKM6xVAo4OW452Cet:StfM77+FrEmKdxVAau |
MALICIOUS
Application was dropped or rewritten from another process
- NDPweb.exe (PID: 3932)
- Setup.exe (PID: 2596)
- NDPweb.exe (PID: 2628)
Loads dropped or rewritten executable
- Setup.exe (PID: 2596)
SUSPICIOUS
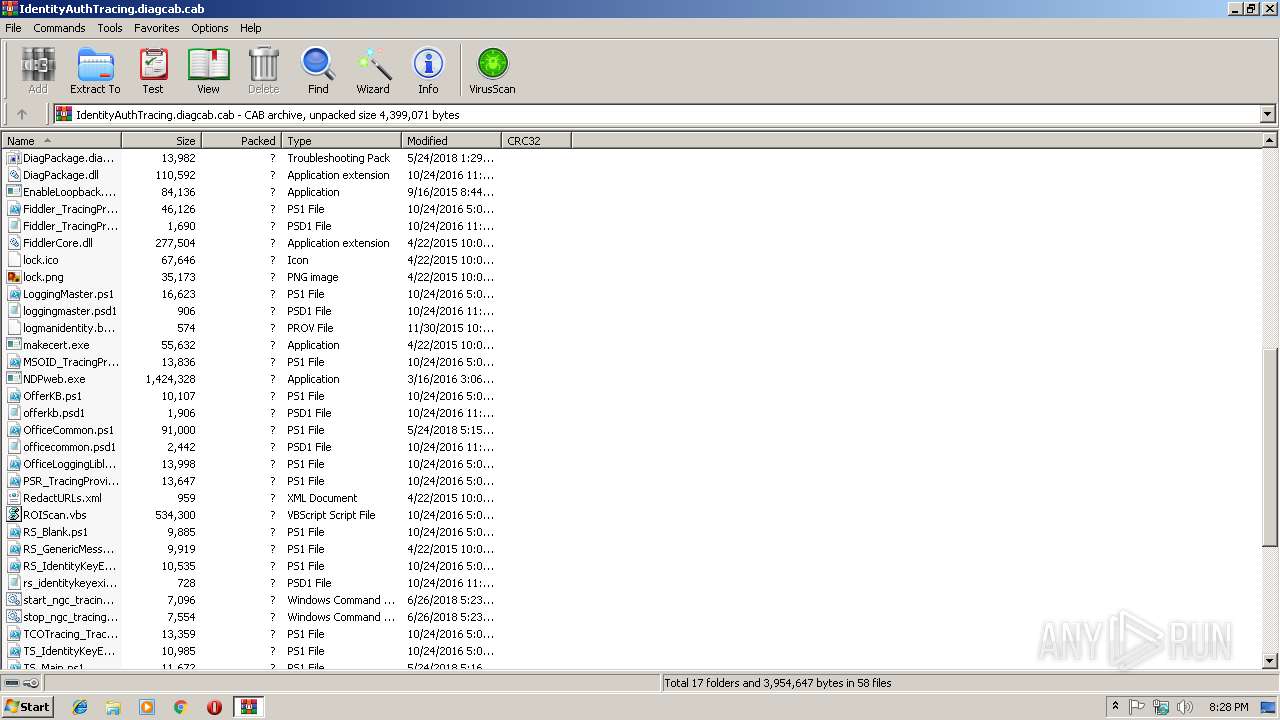
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3040)
- NDPweb.exe (PID: 2628)
INFO
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 3040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .cab | | | Microsoft Cabinet Archive (100) |
|---|
Total processes
36
Monitored processes
4
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
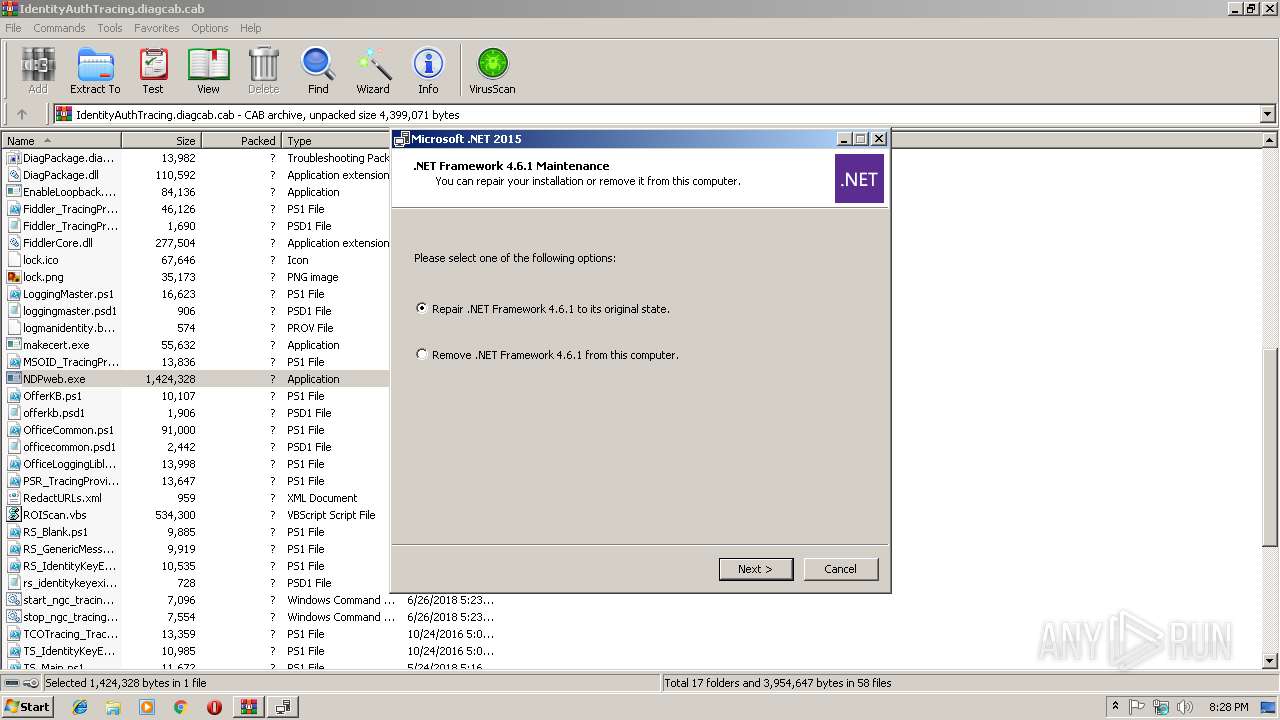
| 2596 | C:\ace965adc7056d2ea87c602cea\\Setup.exe /x86 /x64 /web | C:\ace965adc7056d2ea87c602cea\Setup.exe | — | NDPweb.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Setup Installer Exit code: 0 Version: 14.0.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 2628 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3040.42829\NDPweb.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3040.42829\NDPweb.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Framework 4.6.1 Setup Exit code: 0 Version: 4.6.01055.00 Modules
| |||||||||||||||
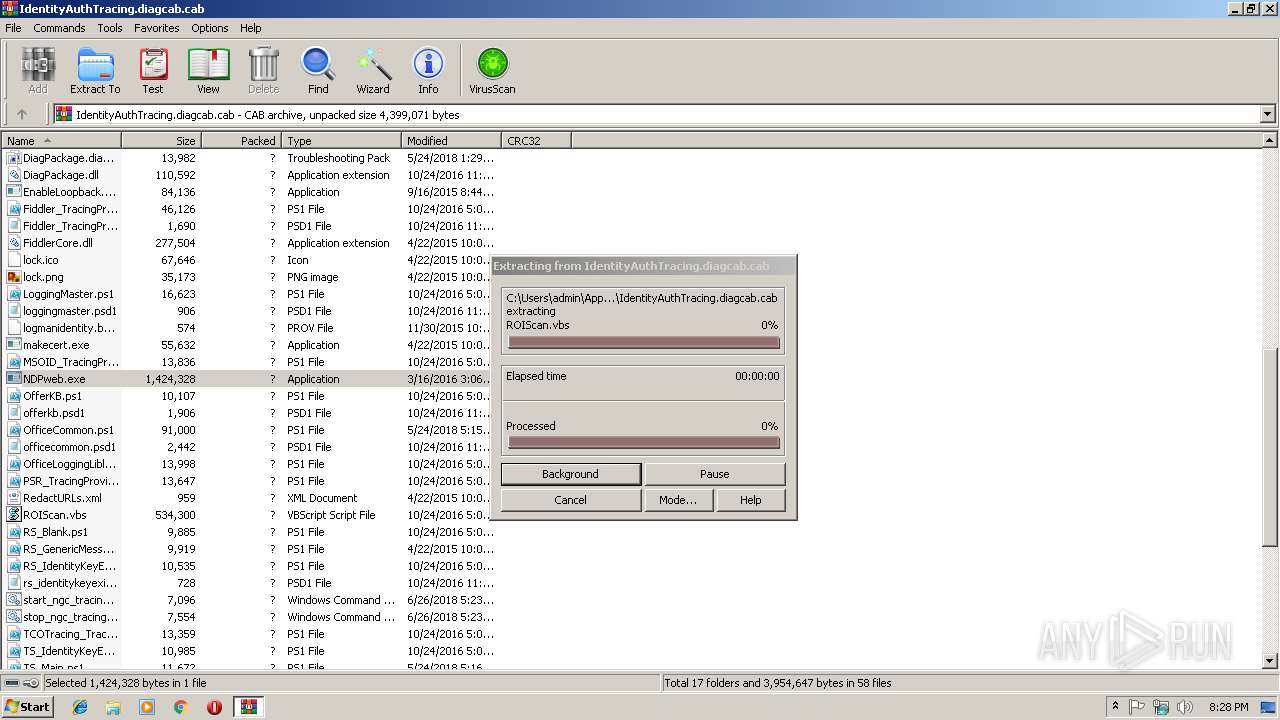
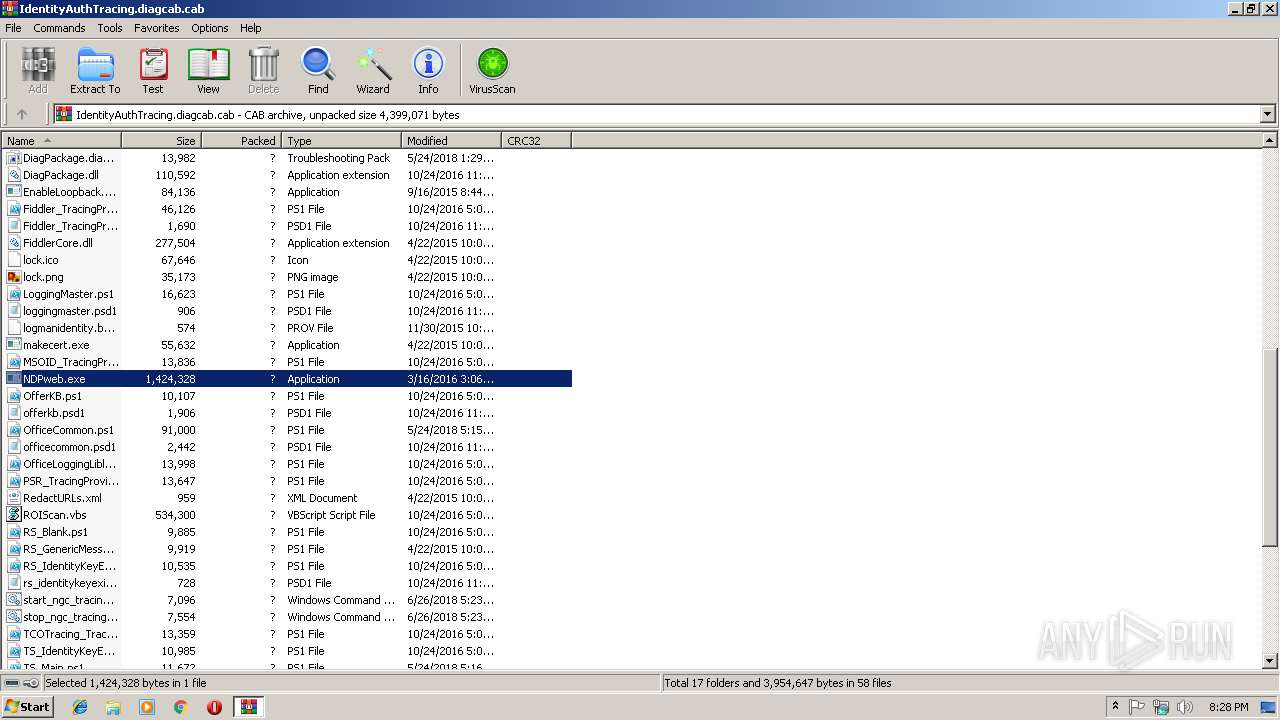
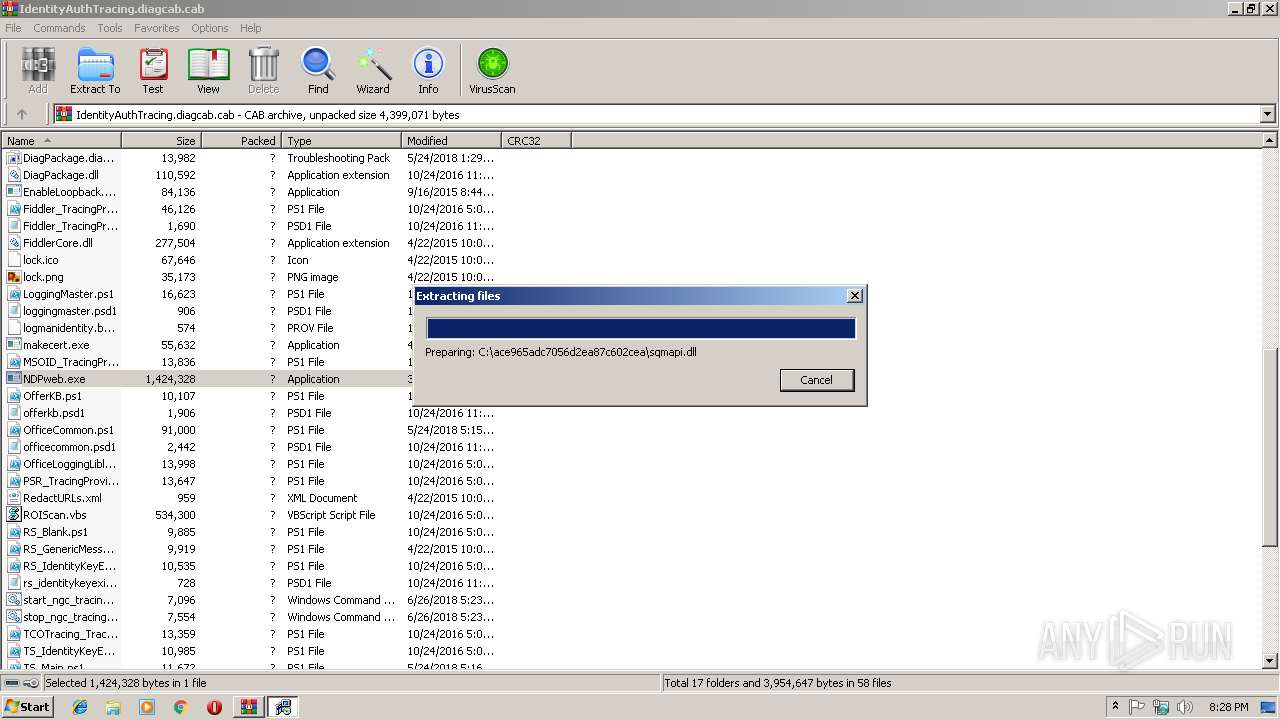
| 3040 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\IdentityAuthTracing.diagcab.cab" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3932 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3040.42829\NDPweb.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3040.42829\NDPweb.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Framework 4.6.1 Setup Exit code: 3221226540 Version: 4.6.01055.00 Modules
| |||||||||||||||
Total events
454
Read events
431
Write events
23
Delete events
0
Modification events
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\IdentityAuthTracing.diagcab.cab | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\msxml3r.dll,-2 |
Value: XSL Stylesheet | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @cryptext.dll,-6145 |
Value: Security Catalog | |||
Executable files
38
Suspicious files
0
Text files
345
Unknown types
18
Dropped files
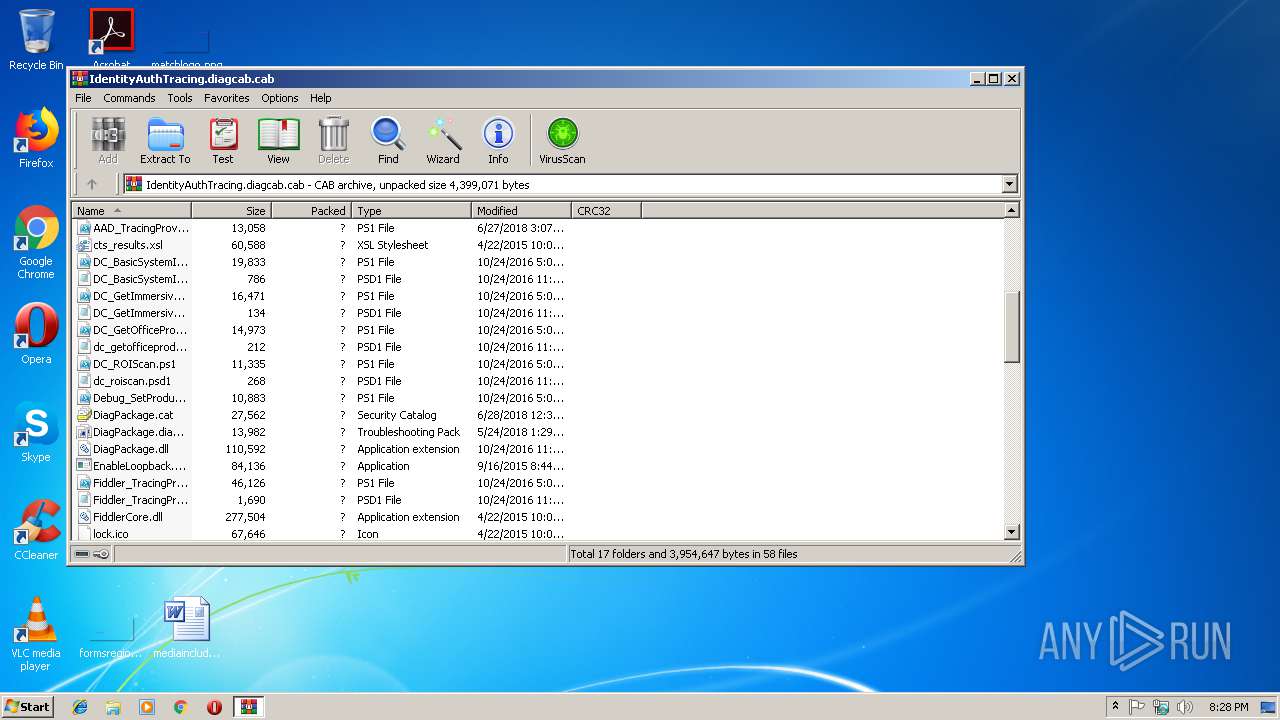
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3040 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3040.42829\DC_BasicSystemInformation.ps1 | text | |
MD5:— | SHA256:— | |||
| 3040 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3040.42829\DC_GetImmersiveSettingsData.ps1 | text | |
MD5:— | SHA256:— | |||
| 3040 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3040.42829\dc_getofficeproductsinstalled.psd1 | text | |
MD5:— | SHA256:— | |||
| 3040 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3040.42829\DC_GetImmersiveSettingsData.psd1 | text | |
MD5:— | SHA256:— | |||
| 3040 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3040.42829\DC_ROIScan.ps1 | text | |
MD5:— | SHA256:— | |||
| 3040 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3040.42829\DiagPackage.cat | cat | |
MD5:— | SHA256:— | |||
| 3040 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3040.42829\Debug_SetProduct.ps1 | text | |
MD5:— | SHA256:— | |||
| 3040 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3040.42829\DiagPackage.diagpkg | xml | |
MD5:— | SHA256:— | |||
| 3040 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3040.42829\DiagPackage.dll | executable | |
MD5:— | SHA256:— | |||
| 3040 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3040.42829\AAD_TracingProvider.ps1 | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report