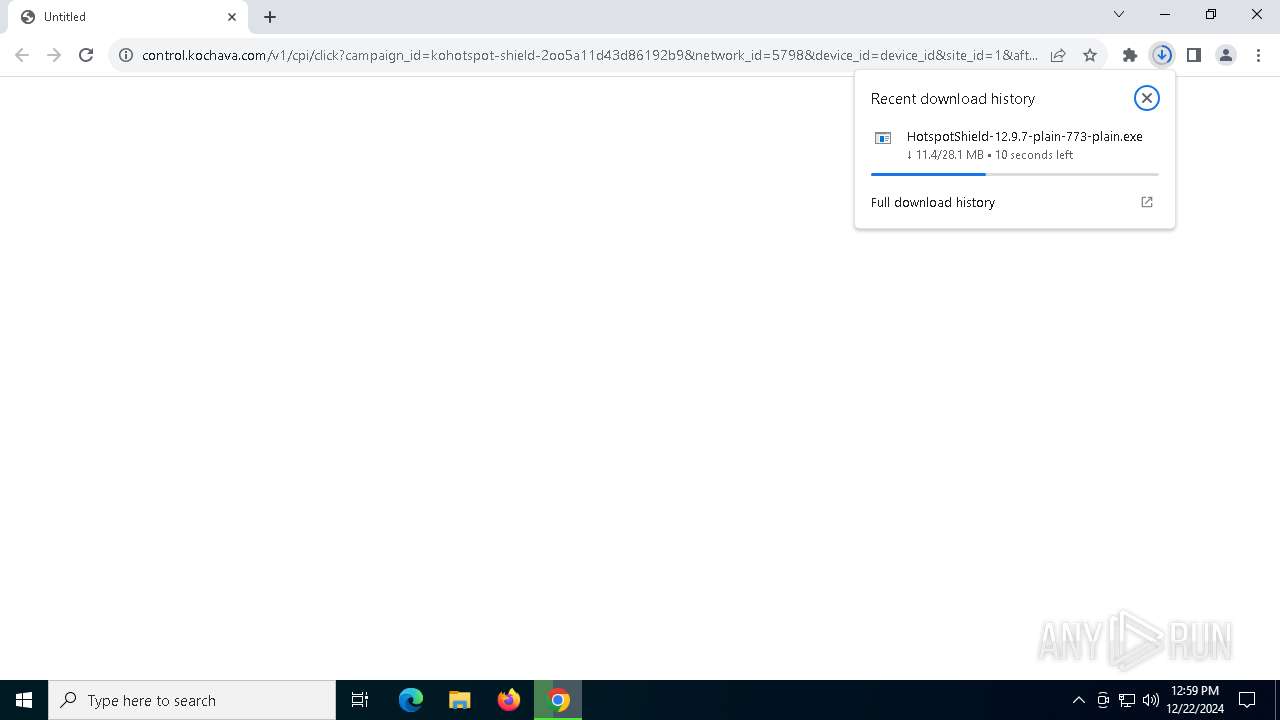
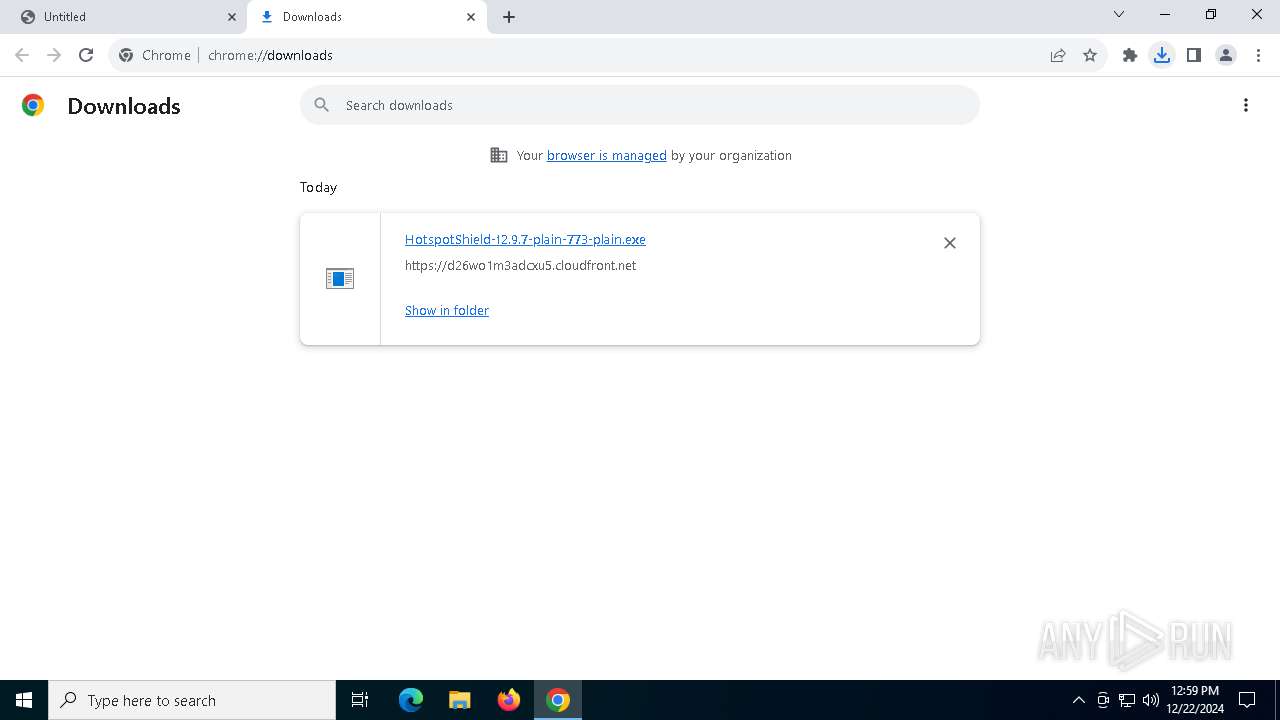
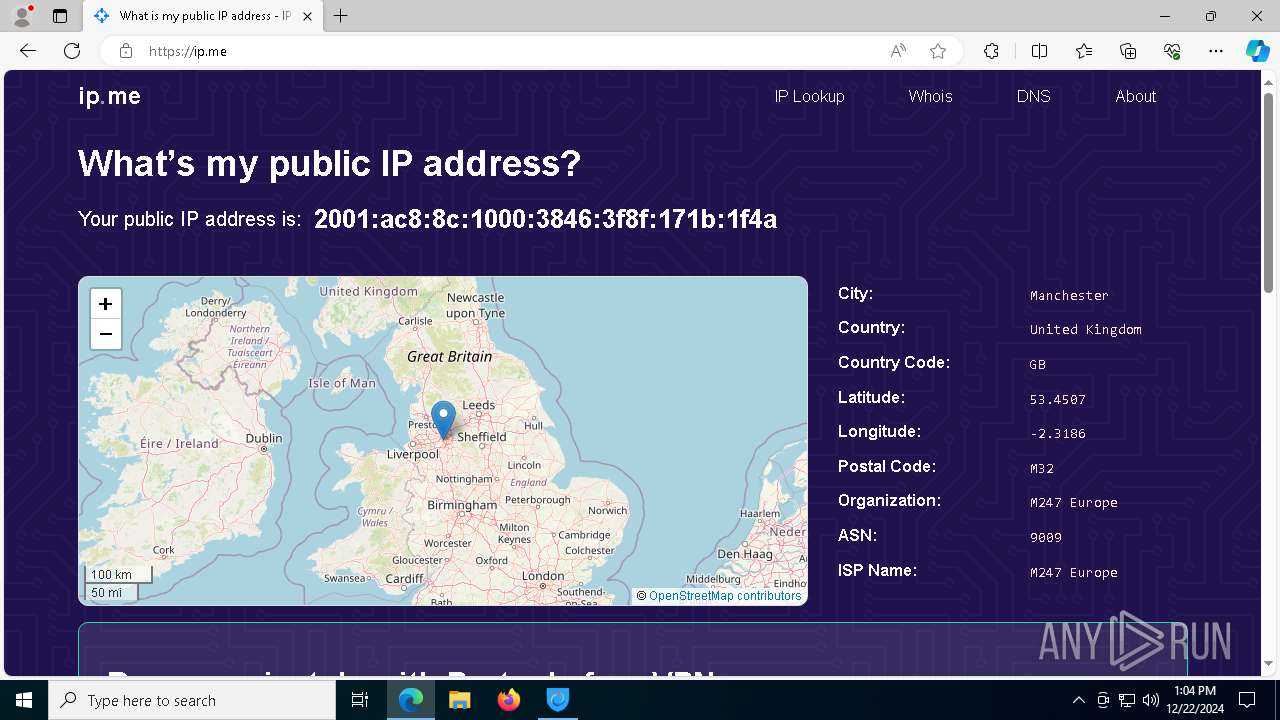
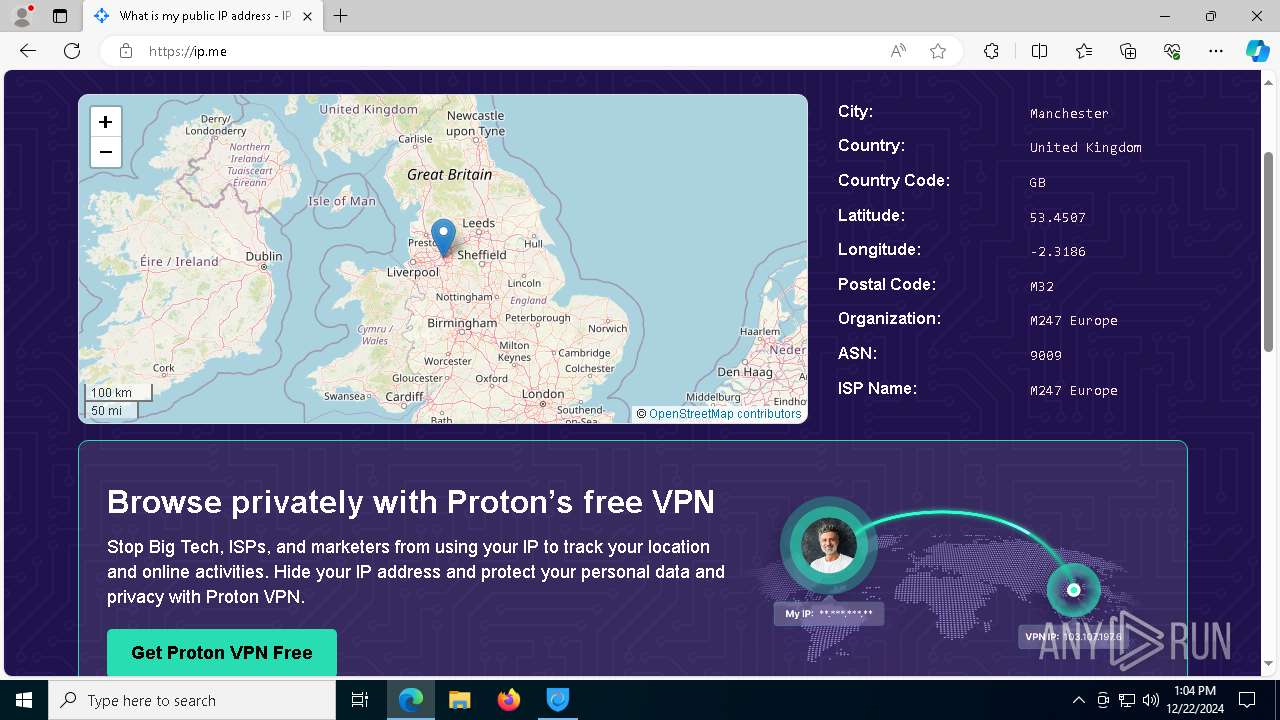
| URL: | https://control.kochava.com/v1/cpi/click?campaign_id=kohotspot-shield-2oo5a11d43d86192b9&network_id=5798&device_id=device_id&site_id=1&aftr=%7B%22vh%22%3A%22ext8b1a3d70-c064-11ef-8302-6dda36d6ee79%22%2C%22referrer%22%3A%22https%3A%2F%2Fwww.qwant.com%2F%22%7D&aftr_source=%2Ffree-vpn%2F |
| Full analysis: | https://app.any.run/tasks/d3041c43-6520-4ddd-b302-6d05feb53e60 |
| Verdict: | Malicious activity |
| Analysis date: | December 22, 2024, 12:59:24 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | B030580E3A78D316EA24EF9E8C942BB4 |
| SHA1: | 359CFDAEDE146BC7674FADD7B5E25EEAEA8638CF |
| SHA256: | 3D7CCBF2E263524A80686F8EBBDED163841E1A3BD0EC9AA564E0053D009FA67A |
| SSDEEP: | 6:27UbdgqyYwrxXr6GIFouG9w49NhwvBhFim1zCgXr:2Eqqqhu71Gub1im1zr |
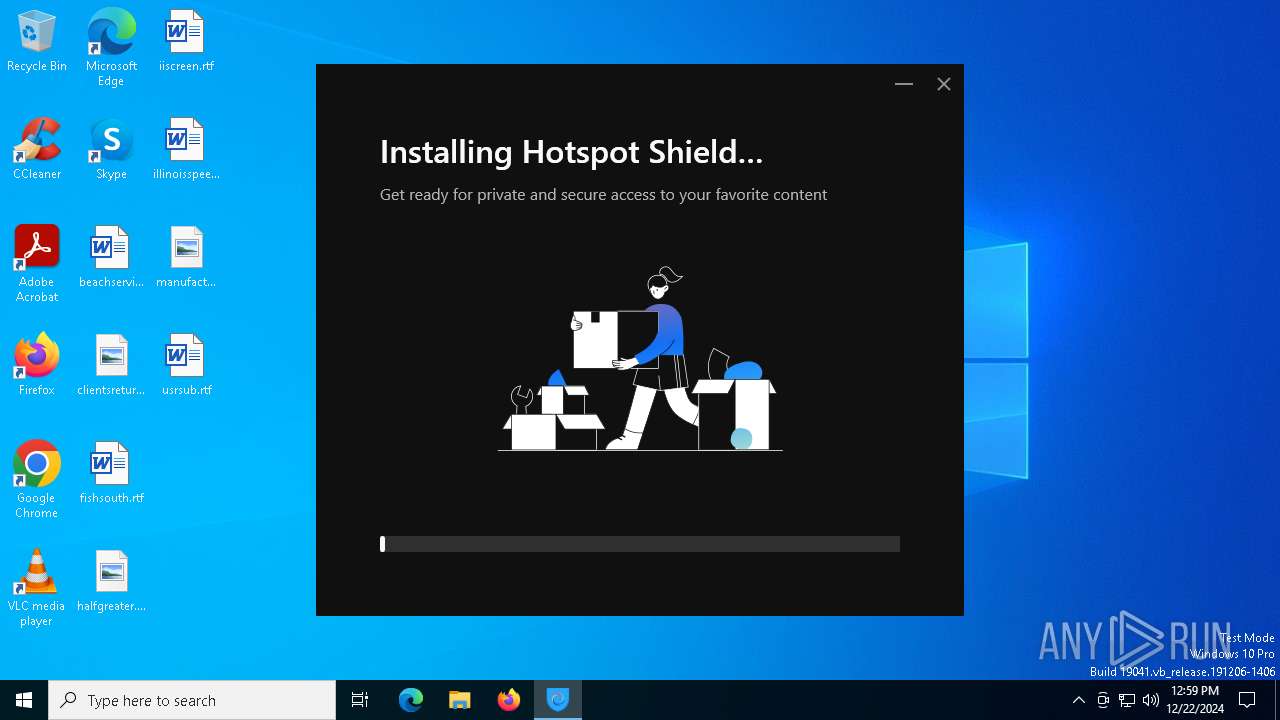
MALICIOUS
Changes the autorun value in the registry
- HSS-12.9.7-install-plain-773-plain.exe (PID: 6656)
SUSPICIOUS
Executable content was dropped or overwritten
- HotspotShield-12.9.7-plain-773-plain.exe (PID: 3808)
- HotspotShield-12.9.7-plain-773-plain.exe (PID: 7084)
- HSS-12.9.7-install-plain-773-plain.exe (PID: 6656)
- rundll32.exe (PID: 4540)
- rundll32.exe (PID: 6824)
- rundll32.exe (PID: 6500)
- rundll32.exe (PID: 6684)
- rundll32.exe (PID: 6436)
- rundll32.exe (PID: 4864)
- rundll32.exe (PID: 2260)
- hsstap-windows-9.24.4-I601-Win10.exe (PID: 3628)
- drvinst.exe (PID: 5244)
- drvinst.exe (PID: 6432)
- rundll32.exe (PID: 5112)
- rundll32.exe (PID: 6180)
- rundll32.exe (PID: 2600)
- rundll32.exe (PID: 6644)
- rundll32.exe (PID: 6500)
- rundll32.exe (PID: 3620)
- rundll32.exe (PID: 6392)
- rundll32.exe (PID: 6416)
- WebView2Bootstrapper.exe (PID: 6160)
- rundll32.exe (PID: 6460)
Process drops legitimate windows executable
- HotspotShield-12.9.7-plain-773-plain.exe (PID: 7084)
- msiexec.exe (PID: 6856)
- WebView2Bootstrapper.exe (PID: 6160)
- MicrosoftEdgeUpdate.exe (PID: 6604)
The process creates files with name similar to system file names
- HotspotShield-12.9.7-plain-773-plain.exe (PID: 7084)
- msiexec.exe (PID: 6856)
- hsstap-windows-9.24.4-I601-Win10.exe (PID: 3628)
Searches for installed software
- HotspotShield-12.9.7-plain-773-plain.exe (PID: 7084)
- rundll32.exe (PID: 2260)
Checks Windows Trust Settings
- HotspotShield-12.9.7-plain-773-plain.exe (PID: 7084)
- tapinstall.exe (PID: 6620)
- msiexec.exe (PID: 6856)
- drvinst.exe (PID: 5244)
- cmw_srv.exe (PID: 4516)
Reads security settings of Internet Explorer
- HotspotShield-12.9.7-plain-773-plain.exe (PID: 7084)
- cmw_srv.exe (PID: 4516)
- hsscp.exe (PID: 2084)
- MicrosoftEdgeUpdate.exe (PID: 6604)
- hsscp.exe (PID: 6468)
Starts itself from another location
- HotspotShield-12.9.7-plain-773-plain.exe (PID: 7084)
Creates a software uninstall entry
- HSS-12.9.7-install-plain-773-plain.exe (PID: 6656)
- hsstap-windows-9.24.4-I601-Win10.exe (PID: 3628)
- rundll32.exe (PID: 2260)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6856)
Uses ICACLS.EXE to modify access control lists
- msiexec.exe (PID: 6736)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 6856)
- rundll32.exe (PID: 4864)
- hsstap-windows-9.24.4-I601-Win10.exe (PID: 3628)
- drvinst.exe (PID: 5244)
- drvinst.exe (PID: 6432)
Malware-specific behavior (creating "System.dll" in Temp)
- hsstap-windows-9.24.4-I601-Win10.exe (PID: 3628)
Creates files in the driver directory
- tapinstall.exe (PID: 6620)
- drvinst.exe (PID: 5244)
- drvinst.exe (PID: 6432)
Creates or modifies Windows services
- drvinst.exe (PID: 6432)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 5680)
- cmd.exe (PID: 6824)
- cmd.exe (PID: 6088)
- msiexec.exe (PID: 6768)
- cmd.exe (PID: 5592)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 5680)
- cmd.exe (PID: 6088)
- cmd.exe (PID: 6824)
- cmd.exe (PID: 5592)
Suspicious use of NETSH.EXE
- rundll32.exe (PID: 6500)
- rundll32.exe (PID: 2600)
- hydra.exe (PID: 1292)
- hydra.exe (PID: 488)
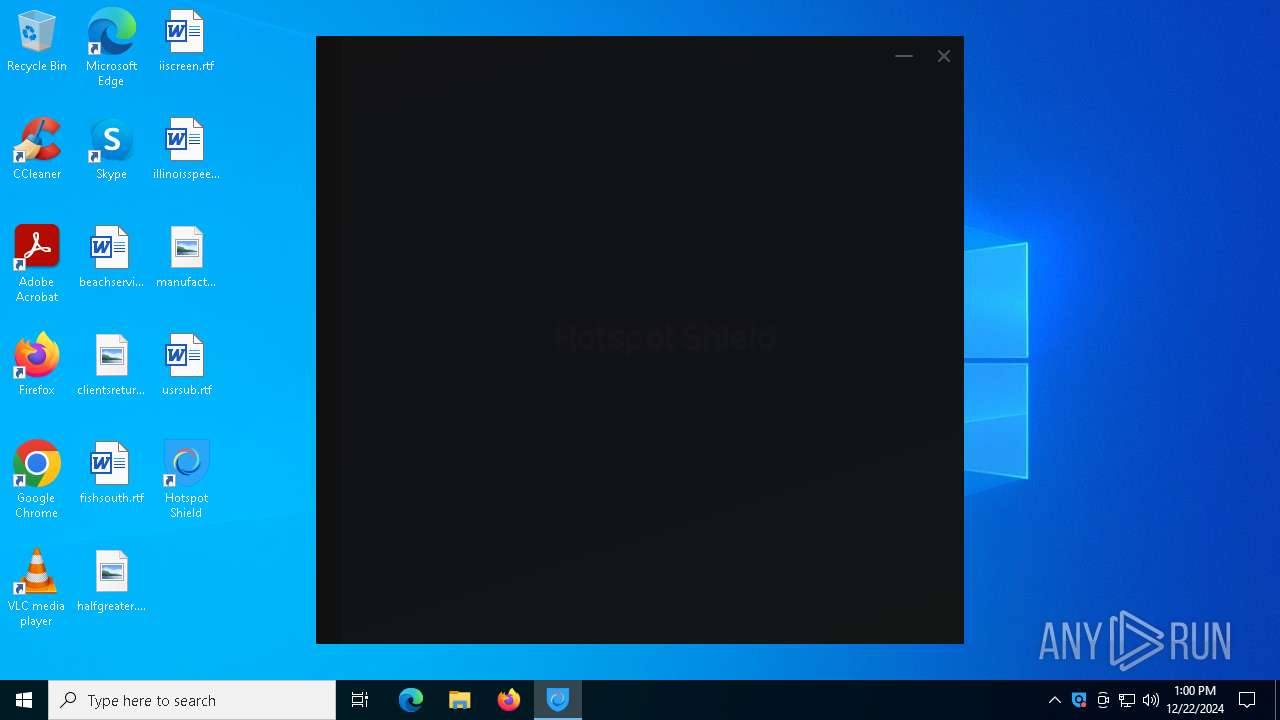
Application launched itself
- cmd.exe (PID: 5680)
- cmd.exe (PID: 6824)
- cmd.exe (PID: 6088)
- cmd.exe (PID: 5592)
Executes as Windows Service
- cmw_srv.exe (PID: 4516)
Windows service management via SC.EXE
- sc.exe (PID: 3628)
Starts a Microsoft application from unusual location
- MicrosoftEdgeUpdate.exe (PID: 6604)
Disables SEHOP
- MicrosoftEdgeUpdate.exe (PID: 6604)
INFO
Application launched itself
- chrome.exe (PID: 1476)
- msedge.exe (PID: 7024)
Executable content was dropped or overwritten
- chrome.exe (PID: 1476)
- msiexec.exe (PID: 6856)
The sample compiled with english language support
- chrome.exe (PID: 1476)
- HotspotShield-12.9.7-plain-773-plain.exe (PID: 3808)
- HotspotShield-12.9.7-plain-773-plain.exe (PID: 7084)
- HSS-12.9.7-install-plain-773-plain.exe (PID: 6656)
- msiexec.exe (PID: 6856)
- rundll32.exe (PID: 4864)
- hsstap-windows-9.24.4-I601-Win10.exe (PID: 3628)
- drvinst.exe (PID: 5244)
- drvinst.exe (PID: 6432)
- WebView2Bootstrapper.exe (PID: 6160)
- MicrosoftEdgeUpdate.exe (PID: 6604)
- rundll32.exe (PID: 6416)
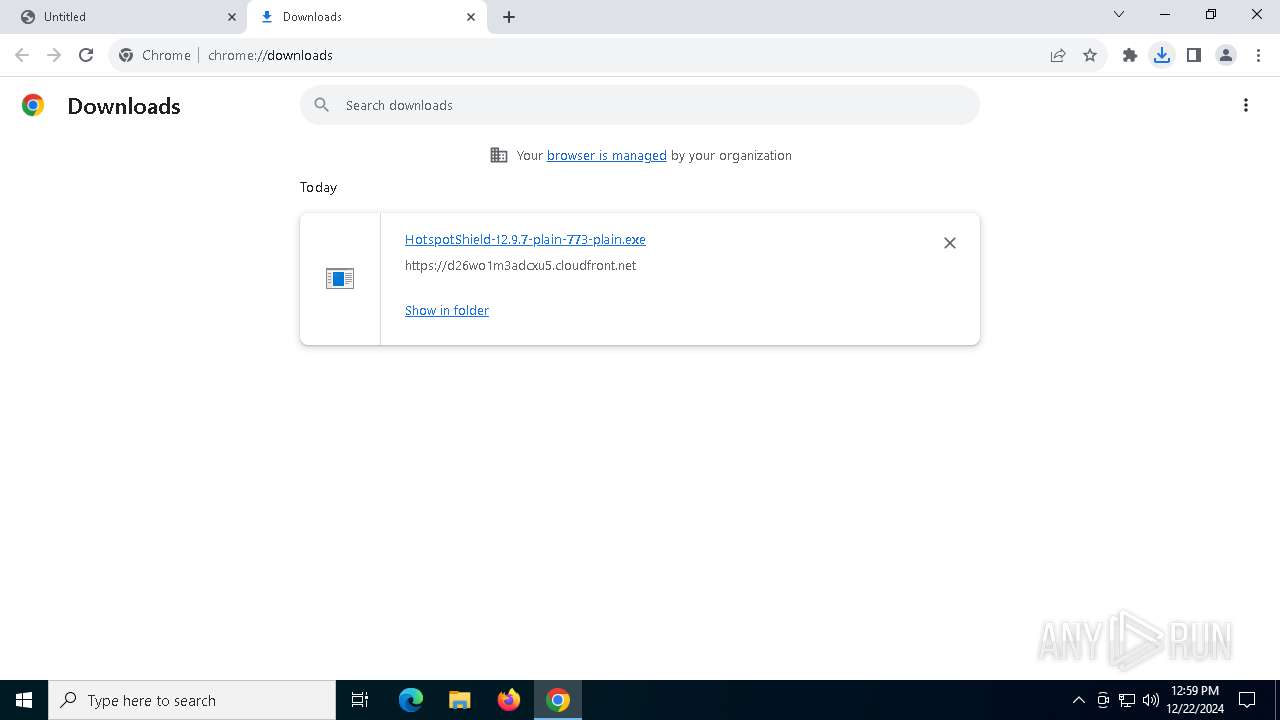
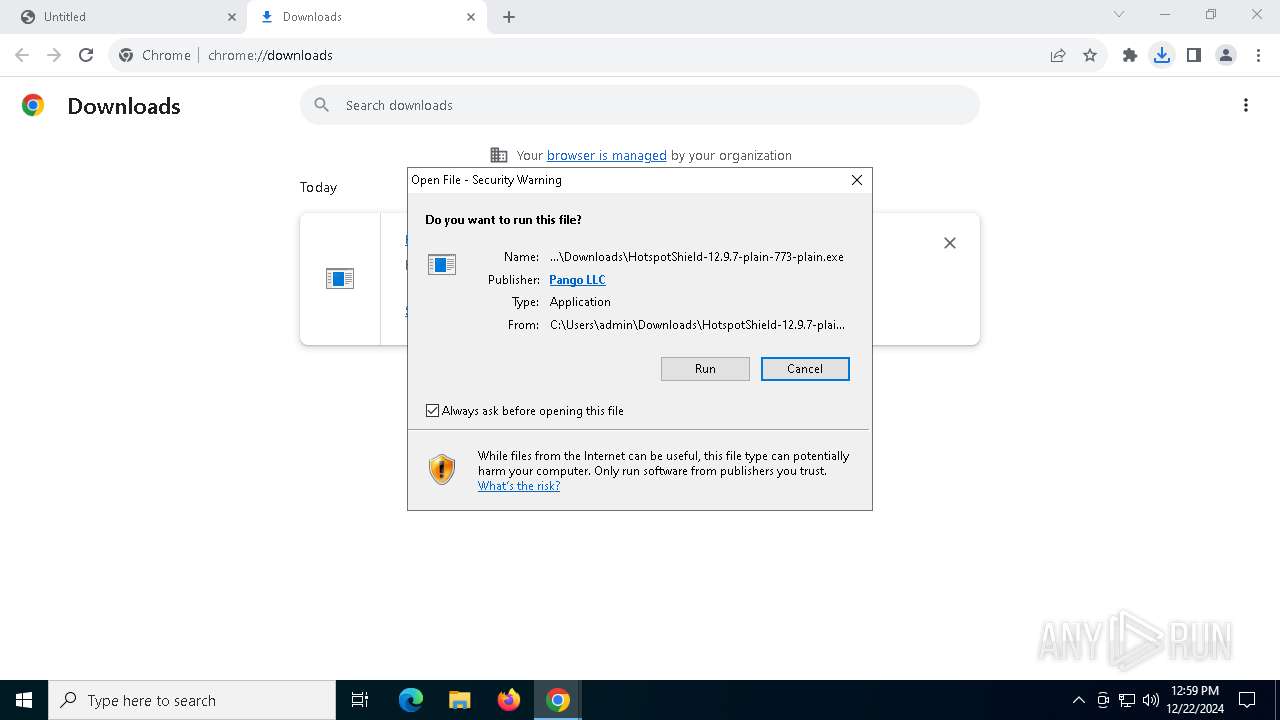
The process uses the downloaded file
- chrome.exe (PID: 6012)
- chrome.exe (PID: 1476)
- HotspotShield-12.9.7-plain-773-plain.exe (PID: 7084)
- cmw_srv.exe (PID: 4516)
- hsscp.exe (PID: 2084)
- rundll32.exe (PID: 6416)
- hsscp.exe (PID: 6468)
Checks supported languages
- HotspotShield-12.9.7-plain-773-plain.exe (PID: 3808)
- HotspotShield-12.9.7-plain-773-plain.exe (PID: 7084)
- HSS-12.9.7-install-plain-773-plain.exe (PID: 6656)
- msiexec.exe (PID: 6856)
- msiexec.exe (PID: 6736)
- msiexec.exe (PID: 6768)
- nfregdrv.exe (PID: 6692)
- hsstap-windows-9.24.4-I601-Win10.exe (PID: 3628)
- tapinstall.exe (PID: 6620)
- tapinstall.exe (PID: 836)
- drvinst.exe (PID: 5244)
- drvinst.exe (PID: 6432)
- cmw_srv.exe (PID: 4516)
- hsscp.exe (PID: 2084)
- MicrosoftEdgeUpdate.exe (PID: 6604)
- hsscp.exe (PID: 6468)
- hydra.exe (PID: 1292)
- hydra.exe (PID: 488)
- identity_helper.exe (PID: 6288)
- WebView2Bootstrapper.exe (PID: 6160)
Create files in a temporary directory
- HotspotShield-12.9.7-plain-773-plain.exe (PID: 3808)
- HotspotShield-12.9.7-plain-773-plain.exe (PID: 7084)
- HSS-12.9.7-install-plain-773-plain.exe (PID: 6656)
- rundll32.exe (PID: 4864)
- hsstap-windows-9.24.4-I601-Win10.exe (PID: 3628)
- rundll32.exe (PID: 2260)
Creates files in the program directory
- HotspotShield-12.9.7-plain-773-plain.exe (PID: 7084)
- HSS-12.9.7-install-plain-773-plain.exe (PID: 6656)
- rundll32.exe (PID: 4864)
- hsstap-windows-9.24.4-I601-Win10.exe (PID: 3628)
- cmw_srv.exe (PID: 4516)
- WebView2Bootstrapper.exe (PID: 6160)
- hsscp.exe (PID: 6468)
- hydra.exe (PID: 1292)
- hydra.exe (PID: 488)
Reads the machine GUID from the registry
- HotspotShield-12.9.7-plain-773-plain.exe (PID: 7084)
- HSS-12.9.7-install-plain-773-plain.exe (PID: 6656)
- msiexec.exe (PID: 6856)
- tapinstall.exe (PID: 6620)
- drvinst.exe (PID: 5244)
- cmw_srv.exe (PID: 4516)
- hsscp.exe (PID: 2084)
- hsscp.exe (PID: 6468)
- hydra.exe (PID: 1292)
- hydra.exe (PID: 488)
Checks proxy server information
- HotspotShield-12.9.7-plain-773-plain.exe (PID: 7084)
- hsscp.exe (PID: 6468)
Process checks computer location settings
- HotspotShield-12.9.7-plain-773-plain.exe (PID: 7084)
- MicrosoftEdgeUpdate.exe (PID: 6604)
Reads the software policy settings
- HotspotShield-12.9.7-plain-773-plain.exe (PID: 7084)
- msiexec.exe (PID: 6856)
- tapinstall.exe (PID: 6620)
- drvinst.exe (PID: 5244)
- rundll32.exe (PID: 6416)
- cmw_srv.exe (PID: 4516)
- MicrosoftEdgeUpdate.exe (PID: 6604)
- wermgr.exe (PID: 5868)
- hsscp.exe (PID: 6468)
Reads the computer name
- HSS-12.9.7-install-plain-773-plain.exe (PID: 6656)
- msiexec.exe (PID: 6736)
- msiexec.exe (PID: 6768)
- HotspotShield-12.9.7-plain-773-plain.exe (PID: 7084)
- nfregdrv.exe (PID: 6692)
- tapinstall.exe (PID: 6620)
- msiexec.exe (PID: 6856)
- drvinst.exe (PID: 6432)
- drvinst.exe (PID: 5244)
- cmw_srv.exe (PID: 4516)
- hsscp.exe (PID: 2084)
- MicrosoftEdgeUpdate.exe (PID: 6604)
- hsscp.exe (PID: 6468)
- hydra.exe (PID: 1292)
- hydra.exe (PID: 488)
- identity_helper.exe (PID: 6288)
Creates files or folders in the user directory
- HotspotShield-12.9.7-plain-773-plain.exe (PID: 7084)
- rundll32.exe (PID: 6416)
Disables trace logs
- HotspotShield-12.9.7-plain-773-plain.exe (PID: 7084)
- netsh.exe (PID: 4628)
- netsh.exe (PID: 3620)
- rundll32.exe (PID: 6416)
- netsh.exe (PID: 3992)
- cmw_srv.exe (PID: 4516)
- netsh.exe (PID: 4528)
- netsh.exe (PID: 1488)
- netsh.exe (PID: 6180)
- netsh.exe (PID: 4528)
- hsscp.exe (PID: 6468)
The sample compiled with japanese language support
- msiexec.exe (PID: 6856)
The sample compiled with korean language support
- msiexec.exe (PID: 6856)
The sample compiled with spanish language support
- msiexec.exe (PID: 6856)
The sample compiled with french language support
- msiexec.exe (PID: 6856)
Creates files in the driver directory
- rundll32.exe (PID: 4864)
Creates a software uninstall entry
- msiexec.exe (PID: 6856)
.NET Reactor protector has been detected
- HotspotShield-12.9.7-plain-773-plain.exe (PID: 7084)
- cmw_srv.exe (PID: 4516)
- hsscp.exe (PID: 6468)
Reads Environment values
- cmw_srv.exe (PID: 4516)
- MicrosoftEdgeUpdate.exe (PID: 6604)
- identity_helper.exe (PID: 6288)
Reads product name
- cmw_srv.exe (PID: 4516)
Reads security settings of Internet Explorer
- rundll32.exe (PID: 6416)
Sends debugging messages
- hydra.exe (PID: 1292)
- hydra.exe (PID: 488)
Manual execution by a user
- msedge.exe (PID: 7024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
263
Monitored processes
123
Malicious processes
13
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 68 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6672 --field-trial-handle=2344,i,2573851333234518177,9630208325097922293,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 488 | "C:\Program Files (x86)\Hotspot Shield\12.9.7\bin\x64\hydra.exe" --rdy 0A1B53F0CD49BA69 | C:\Program Files (x86)\Hotspot Shield\12.9.7\bin\x64\hydra.exe | cmw_srv.exe | ||||||||||||
User: SYSTEM Company: Aura Inc. Integrity Level: SYSTEM Version: 1.1.1.23 Modules
| |||||||||||||||
| 512 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3488 --field-trial-handle=2344,i,2573851333234518177,9630208325097922293,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 512 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6832 --field-trial-handle=2344,i,2573851333234518177,9630208325097922293,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 836 | "C:\Program Files\HotspotShield TAP-Windows\bin\tapinstall.exe" hwids hsstap | C:\Program Files\HotspotShield TAP-Windows\bin\tapinstall.exe | — | hsstap-windows-9.24.4-I601-Win10.exe | |||||||||||
User: SYSTEM Company: Windows (R) Win 7 DDK provider Integrity Level: SYSTEM Description: Windows Setup API Exit code: 0 Version: 10.0.10011.16384 Modules
| |||||||||||||||
| 848 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1292 | "C:\Program Files (x86)\Hotspot Shield\12.9.7\bin\x64\hydra.exe" --rdy E2583BD33AFA1CEF | C:\Program Files (x86)\Hotspot Shield\12.9.7\bin\x64\hydra.exe | cmw_srv.exe | ||||||||||||
User: SYSTEM Company: Aura Inc. Integrity Level: SYSTEM Exit code: 0 Version: 1.1.1.23 Modules
| |||||||||||||||
| 1476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://control.kochava.com/v1/cpi/click?campaign_id=kohotspot-shield-2oo5a11d43d86192b9&network_id=5798&device_id=device_id&site_id=1&aftr=%7B%22vh%22%3A%22ext8b1a3d70-c064-11ef-8302-6dda36d6ee79%22%2C%22referrer%22%3A%22https%3A%2F%2Fwww.qwant.com%2F%22%7D&aftr_source=%2Ffree-vpn%2F" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1488 | "C:\WINDOWS\SysWOW64\icacls.exe" "C:\ProgramData\Hotspot Shield\system" /inheritance:r /grant *S-1-5-32-544:(OI)(CI)(F) /grant *S-1-5-18:(OI)(CI)(F) | C:\Windows\SysWOW64\icacls.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1488 | "C:\WINDOWS\system32\netsh.exe" interface ip set dns "HotspotShield Network Adapter" static 8.8.8.8 | C:\Windows\System32\netsh.exe | hydra.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
102 371
Read events
101 650
Write events
691
Delete events
30
Modification events
| (PID) Process: | (1476) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1476) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1476) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1476) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1476) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6012) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 01000000000000009E47DB607154DB01 | |||
| (PID) Process: | (1476) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (1476) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | GoogleChromeAutoLaunch_A822CA3D40D4B8944864CFEA751D8D57 |
Value: | |||
| (PID) Process: | (7084) HotspotShield-12.9.7-plain-773-plain.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\HotspotShield-12_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7084) HotspotShield-12.9.7-plain-773-plain.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\HotspotShield-12_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
762
Suspicious files
660
Text files
200
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF13696b.TMP | — | |
MD5:— | SHA256:— | |||
| 1476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF13697b.TMP | — | |
MD5:— | SHA256:— | |||
| 1476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF13697b.TMP | — | |
MD5:— | SHA256:— | |||
| 1476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF13699a.TMP | — | |
MD5:— | SHA256:— | |||
| 1476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF13698b.TMP | — | |
MD5:— | SHA256:— | |||
| 1476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
113
DNS requests
81
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1476 | chrome.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAh59X5aQVgSPUL%2BCUVfQzY%3D | unknown | — | — | whitelisted |
1476 | chrome.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
1476 | chrome.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
7084 | HotspotShield-12.9.7-plain-773-plain.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAc2N7ckVHzYR6z9KGYqXls%3D | unknown | — | — | whitelisted |
7084 | HotspotShield-12.9.7-plain-773-plain.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTjzY2p9Pa8oibmj%2BNSMWsz63kmWgQUuhbZbU2FL3MpdpovdYxqII%2BeyG8CEAuuZrxaun%2BVh8b56QTjMwQ%3D | unknown | — | — | whitelisted |
7044 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7044 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4516 | cmw_srv.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
880 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 104.126.37.160:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1076 | svchost.exe | 23.35.238.131:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
1476 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
control.kochava.com |
| whitelisted |
accounts.google.com |
| whitelisted |
d26wo1m3adcxu5.cloudfront.net |
| whitelisted |
login.live.com |
| whitelisted |
Threats
Process | Message |
|---|---|
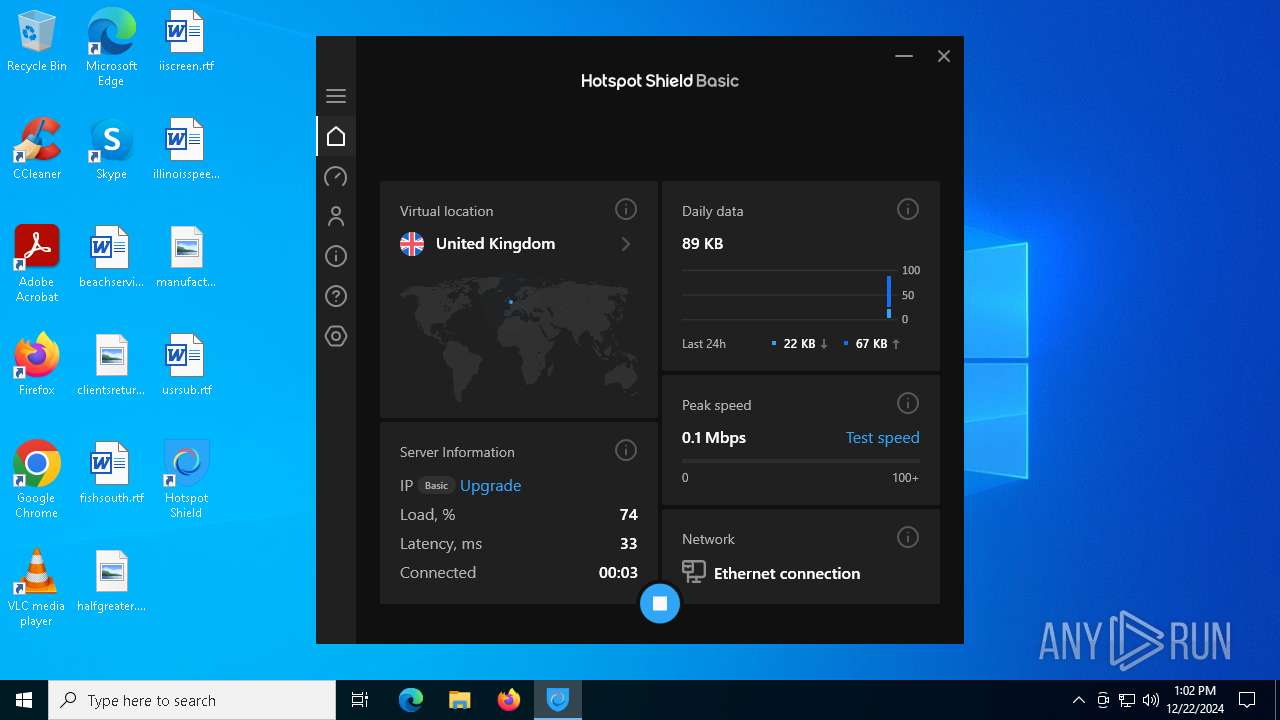
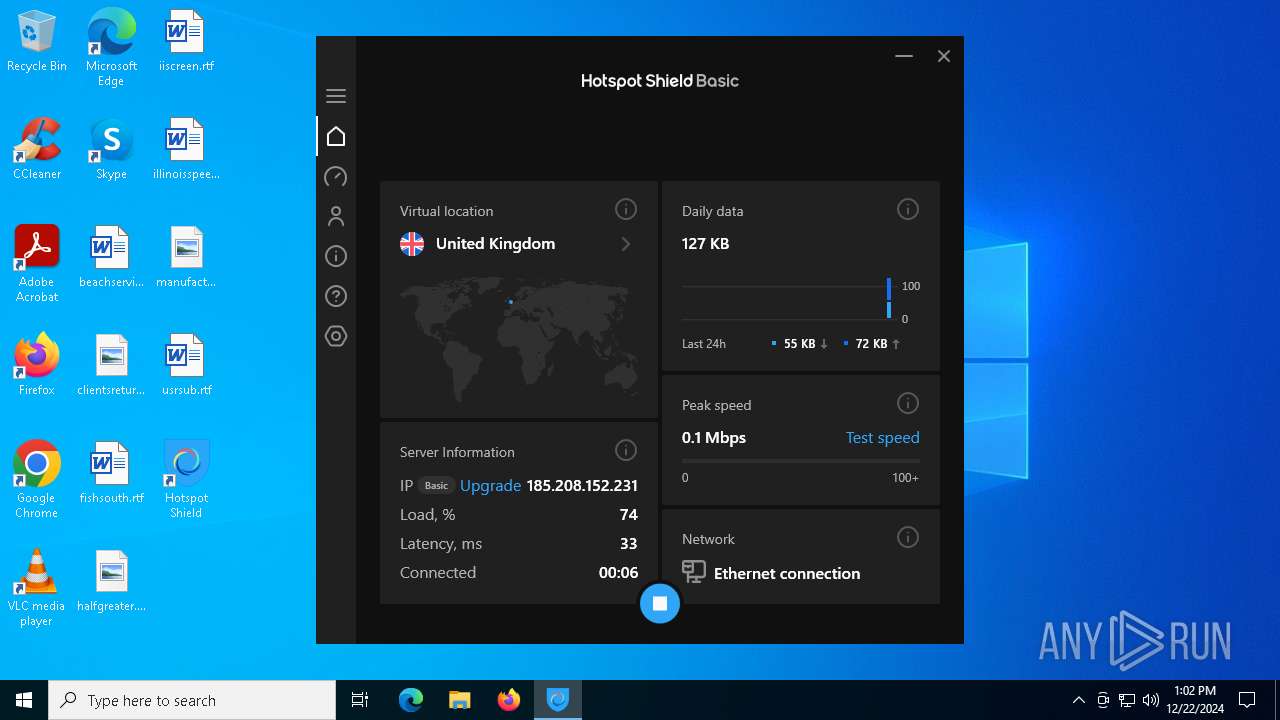
hydra.exe | HYDRA_STATE_CONNECTING
|
hydra.exe | HYDRA_STATE
|
hydra.exe | HYDRA_STATE_CONNECTED
|
hydra.exe | HYDRA_STATE_DISCONNECTED
|
hydra.exe | HYDRA_STATE
|
hydra.exe | HYDRA_STATE
|
hydra.exe | AFVpn::FinalRelease
|