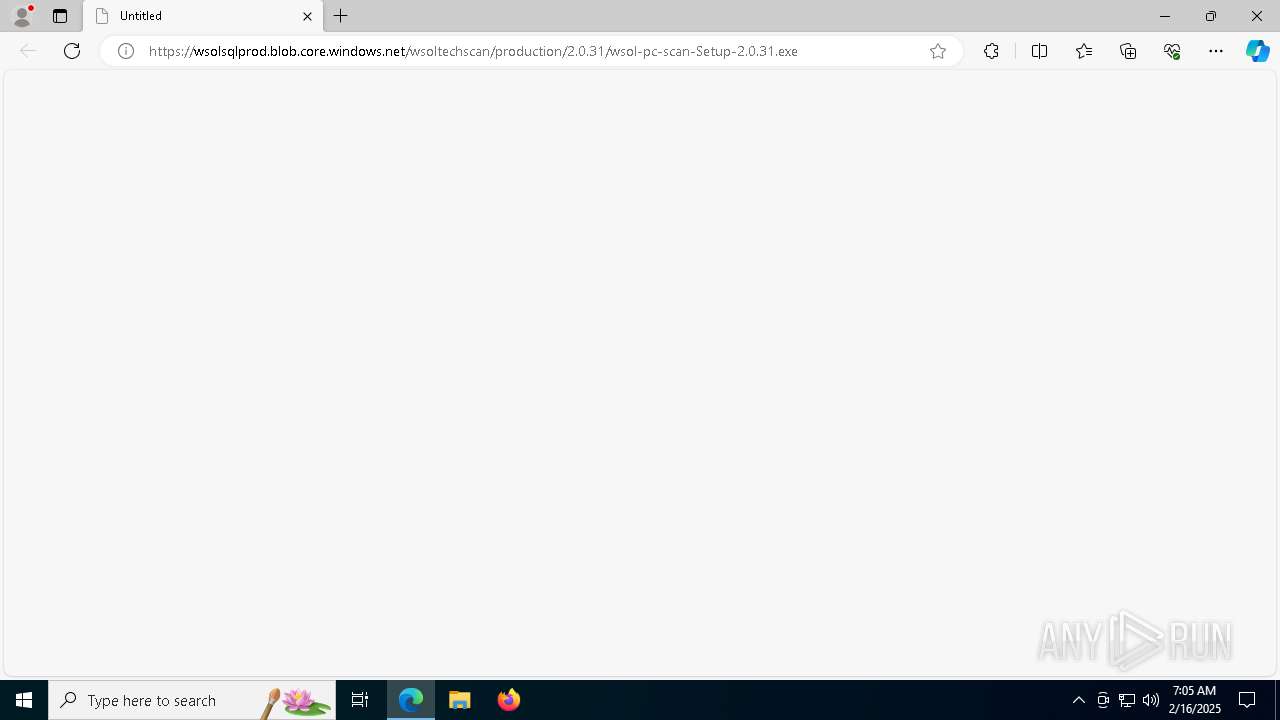
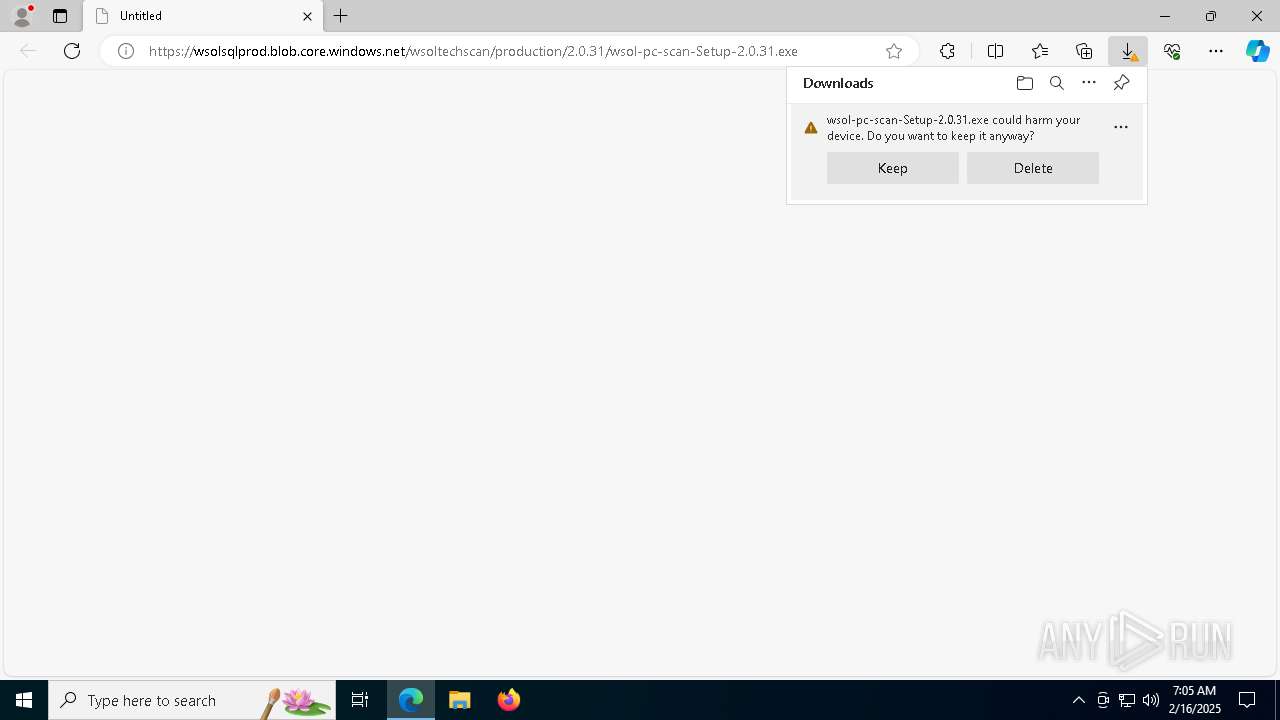
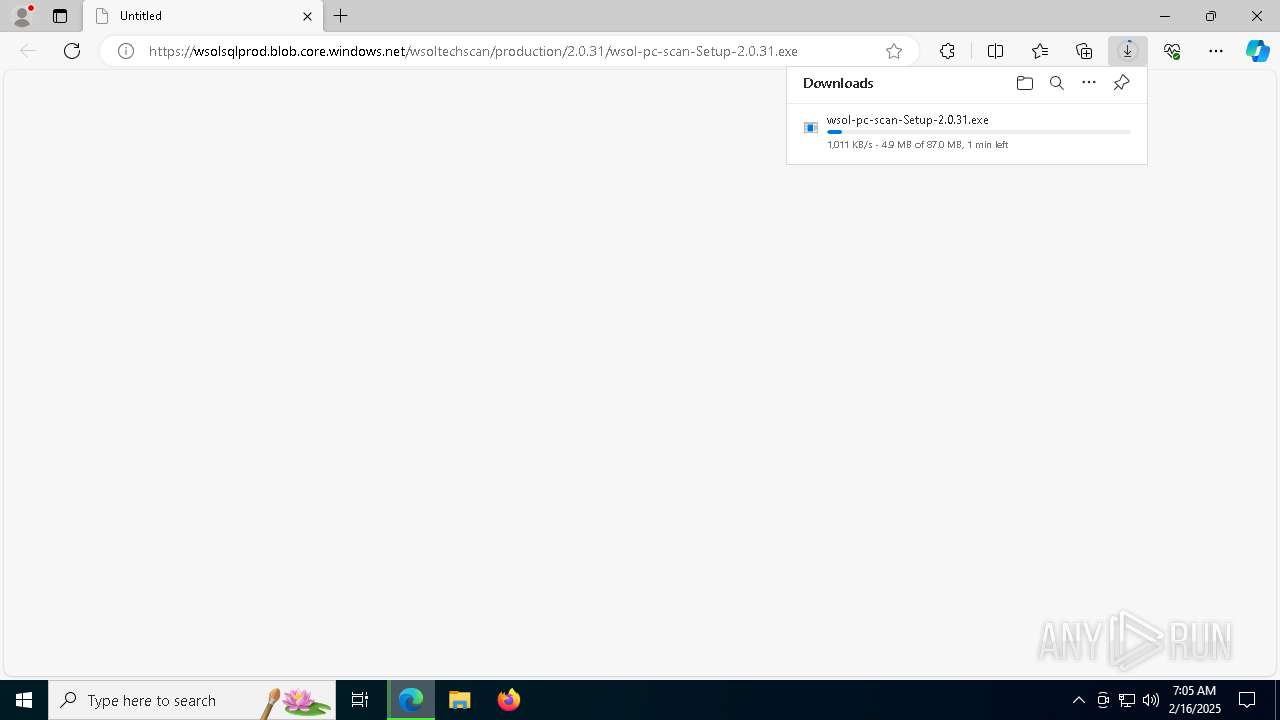
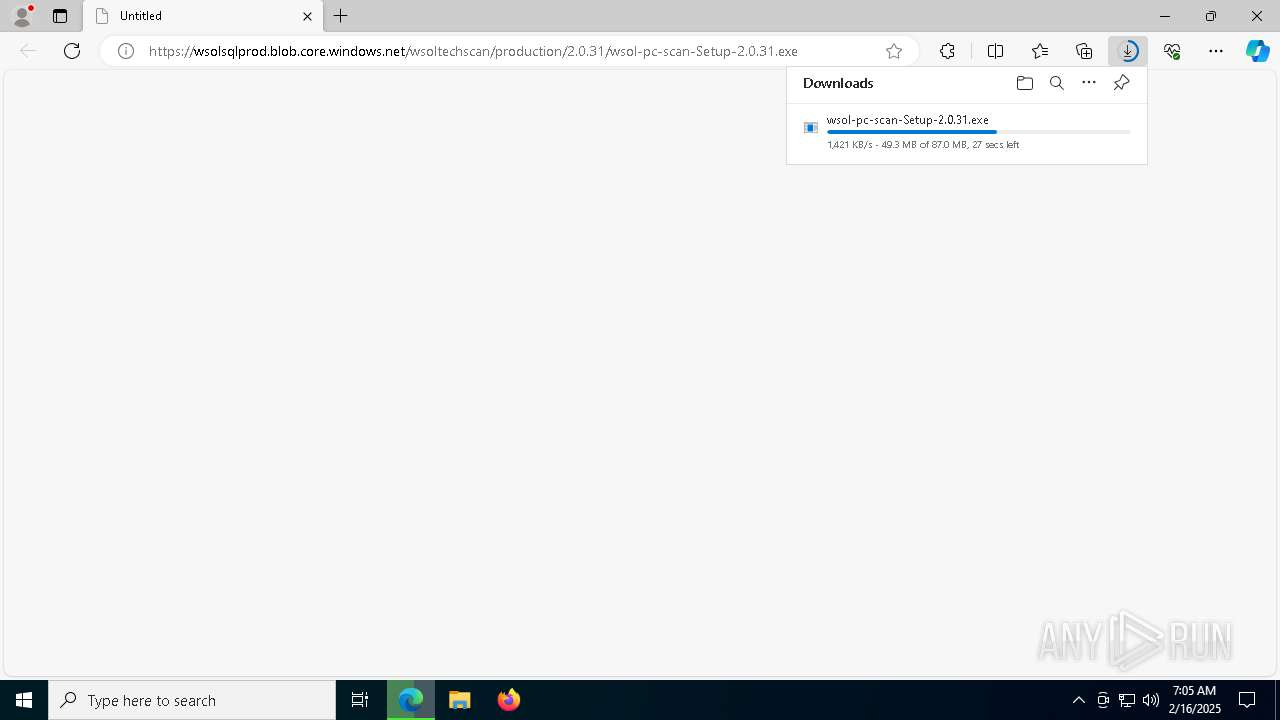
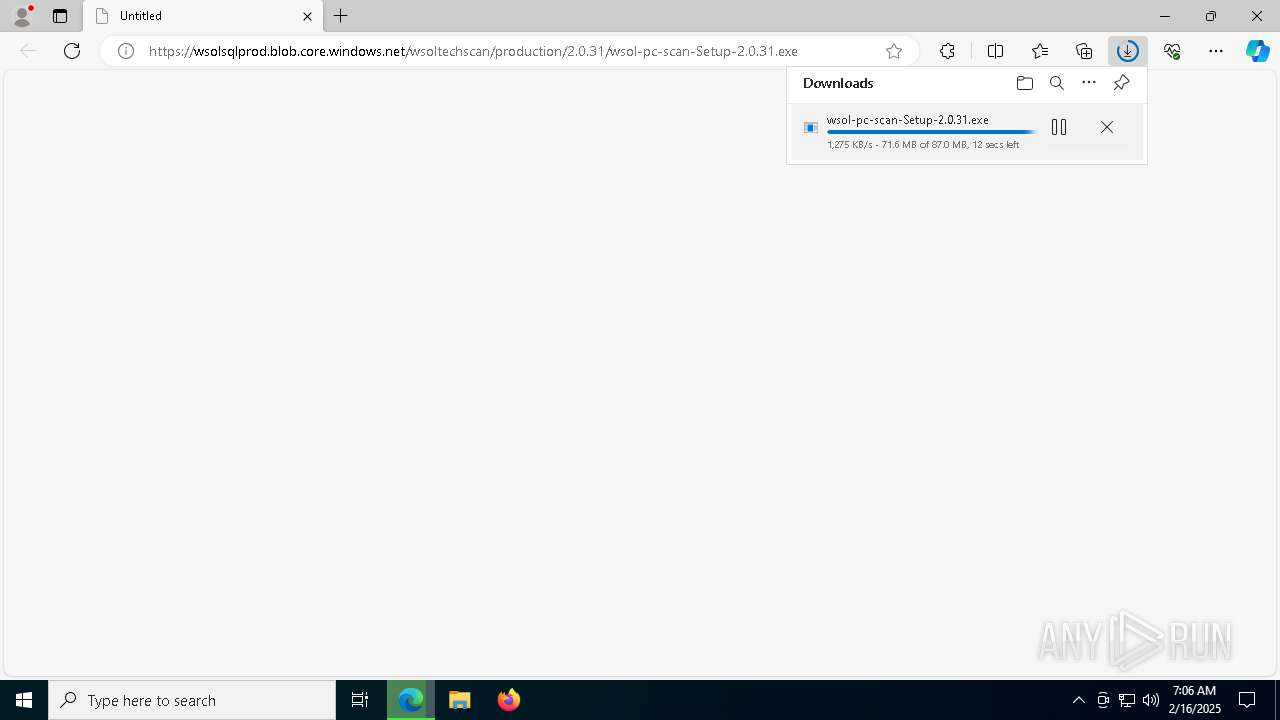
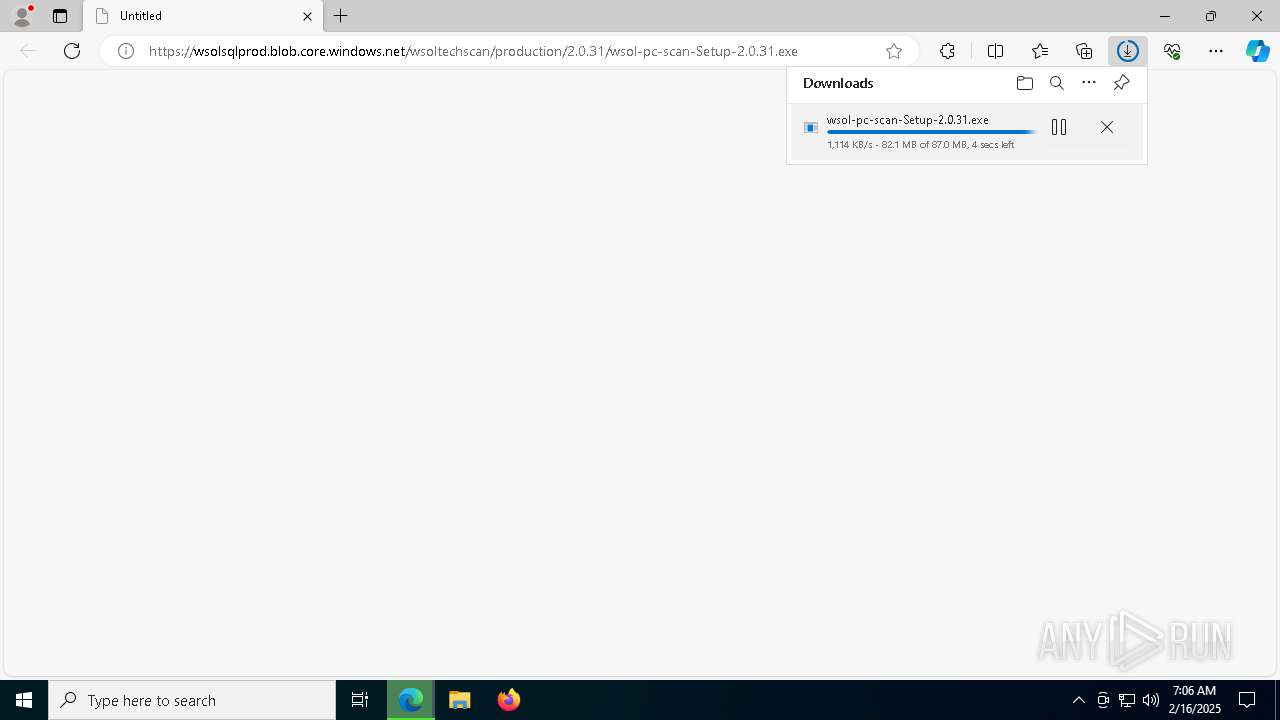
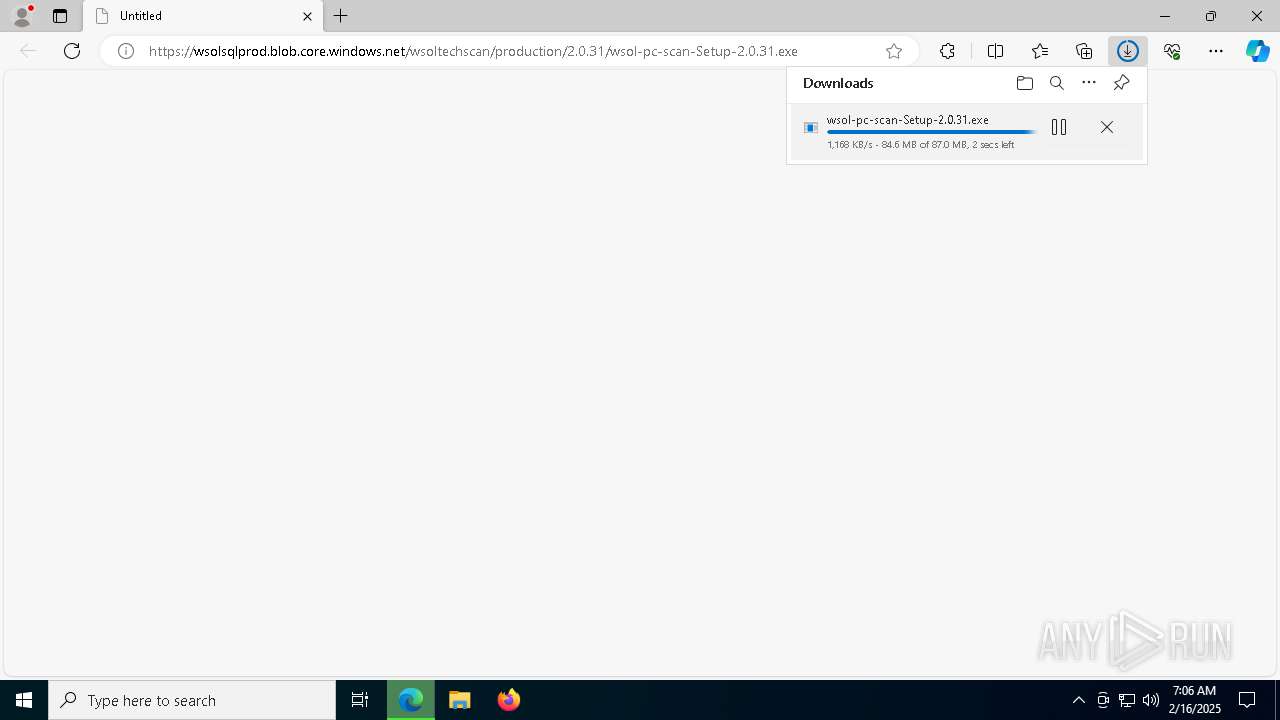
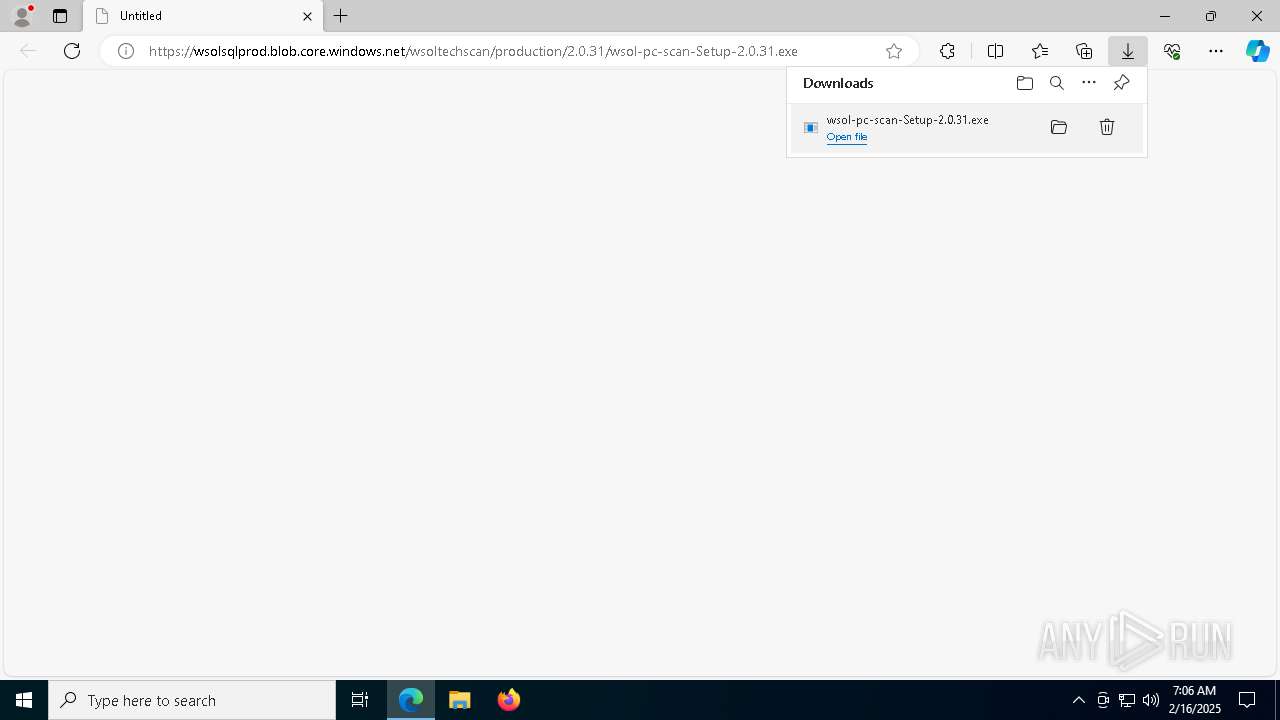
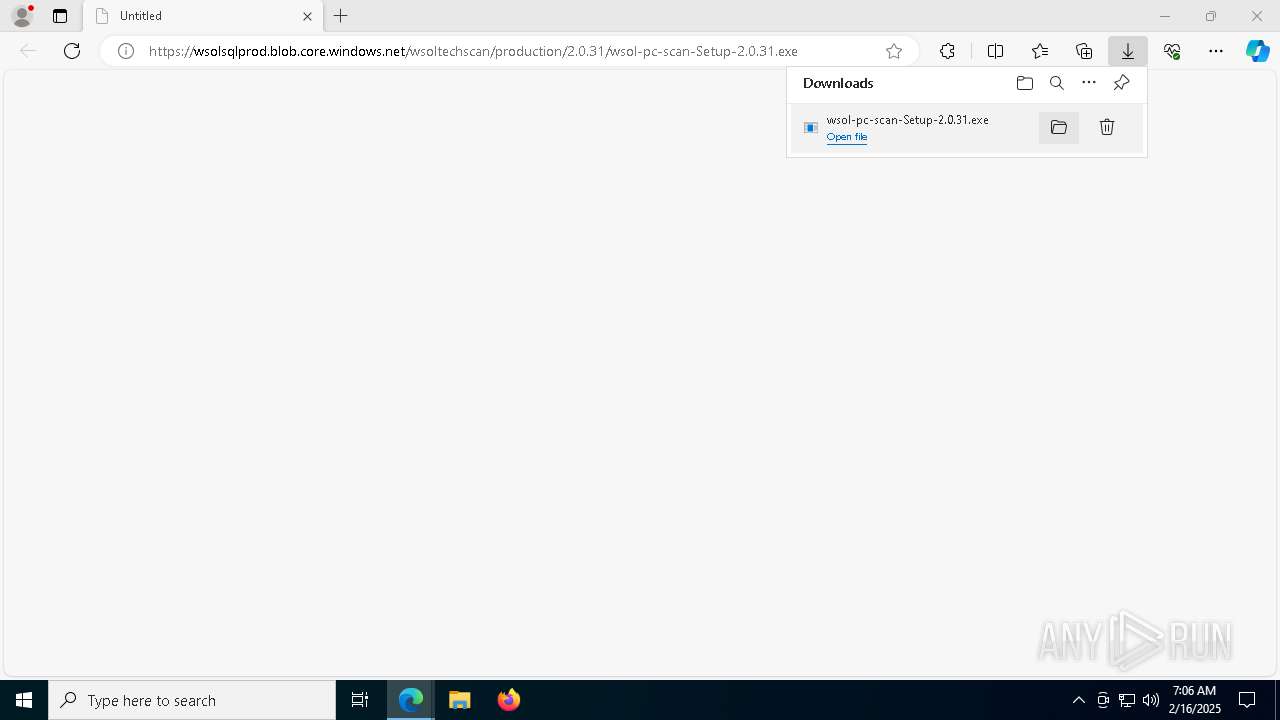
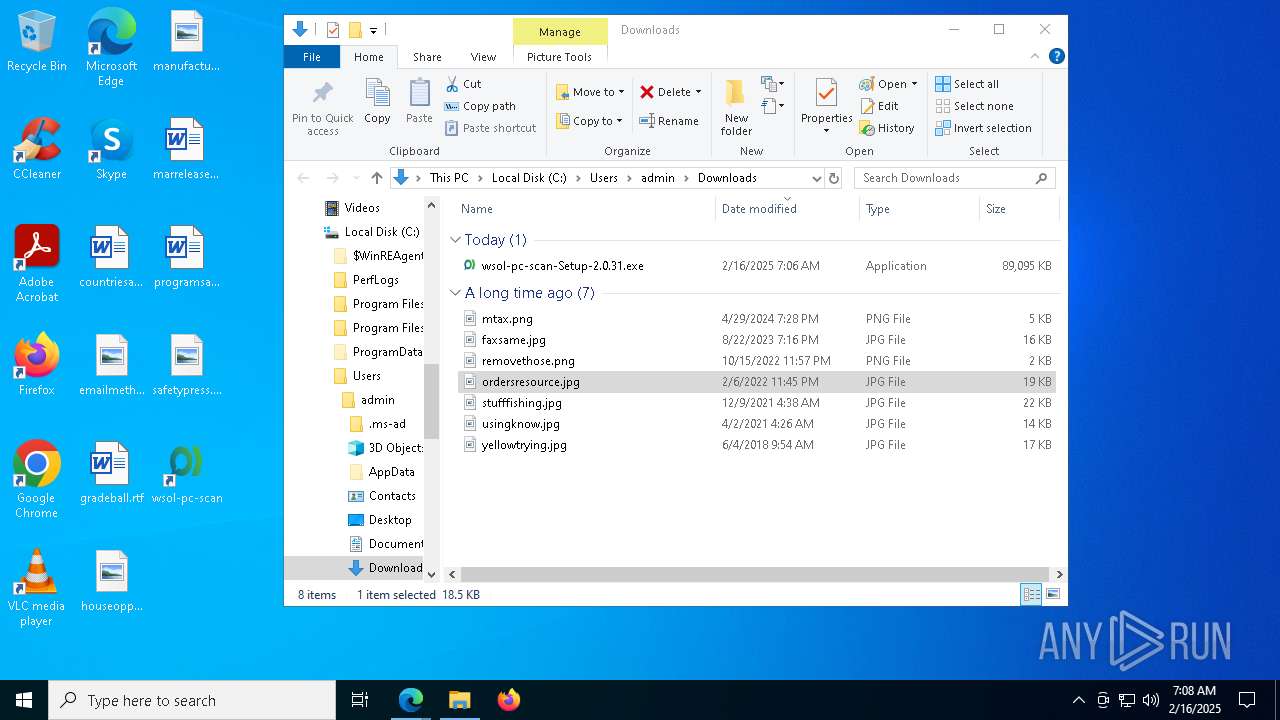
| URL: | https://wsolsqlprod.blob.core.windows.net/wsoltechscan/production/2.0.31/wsol-pc-scan-Setup-2.0.31.exe |
| Full analysis: | https://app.any.run/tasks/f99407e5-56ec-4f3a-b1c9-4b76a674d40b |
| Verdict: | Malicious activity |
| Analysis date: | February 16, 2025, 07:05:11 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 0986A254EBF3A885AEE8BE99EBD40205 |
| SHA1: | EA4DD174D021B4E7D3BE30CBDCAFEE3E3CA16F94 |
| SHA256: | 3D6EE20E4509245FFEA44207A5CF7FB3F03244AF528000DEE2FAFDF8FD0BF76A |
| SSDEEP: | 3:N8HKJW/l6Gw5SiGpVyRMfbAUYETLuT0dAn:2qJWr7yRMfbacLQ |
MALICIOUS
Changes powershell execution policy (Unrestricted)
- wsol-pc-scan.exe (PID: 8)
Bypass execution policy to execute commands
- powershell.exe (PID: 8136)
- powershell.exe (PID: 5236)
- powershell.exe (PID: 6920)
- powershell.exe (PID: 7024)
- powershell.exe (PID: 2996)
- powershell.exe (PID: 1612)
- powershell.exe (PID: 5244)
- powershell.exe (PID: 4544)
SUSPICIOUS
The process creates files with name similar to system file names
- wsol-pc-scan-Setup-2.0.31.exe (PID: 3876)
Executable content was dropped or overwritten
- wsol-pc-scan-Setup-2.0.31.exe (PID: 3876)
Starts CMD.EXE for commands execution
- wsol-pc-scan-Setup-2.0.31.exe (PID: 3876)
- wsol-pc-scan.exe (PID: 8)
- speedtest.exe (PID: 904)
Get information on the list of running processes
- wsol-pc-scan-Setup-2.0.31.exe (PID: 3876)
- cmd.exe (PID: 7568)
Malware-specific behavior (creating "System.dll" in Temp)
- wsol-pc-scan-Setup-2.0.31.exe (PID: 3876)
Drops 7-zip archiver for unpacking
- wsol-pc-scan-Setup-2.0.31.exe (PID: 3876)
Process drops legitimate windows executable
- wsol-pc-scan-Setup-2.0.31.exe (PID: 3876)
There is functionality for taking screenshot (YARA)
- wsol-pc-scan-Setup-2.0.31.exe (PID: 3876)
Reads security settings of Internet Explorer
- wsol-pc-scan-Setup-2.0.31.exe (PID: 3876)
Creates a software uninstall entry
- wsol-pc-scan-Setup-2.0.31.exe (PID: 3876)
Starts application with an unusual extension
- cmd.exe (PID: 6488)
- cmd.exe (PID: 5968)
- cmd.exe (PID: 4872)
- cmd.exe (PID: 4024)
- cmd.exe (PID: 8044)
- cmd.exe (PID: 7964)
- cmd.exe (PID: 4804)
Application launched itself
- wsol-pc-scan.exe (PID: 8)
The process hides Powershell's copyright startup banner
- wsol-pc-scan.exe (PID: 8)
Starts POWERSHELL.EXE for commands execution
- wsol-pc-scan.exe (PID: 8)
Uses WMIC.EXE to obtain CPU information
- cmd.exe (PID: 4872)
Uses WMIC.EXE
- cmd.exe (PID: 5968)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 4024)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7148)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 8044)
Uses WMIC.EXE to obtain desktop monitor information
- cmd.exe (PID: 7964)
Checks for Java to be installed
- java.exe (PID: 4308)
The process bypasses the loading of PowerShell profile settings
- wsol-pc-scan.exe (PID: 8)
Uses WMIC.EXE to obtain data on the virtual memory file swapping
- cmd.exe (PID: 4804)
INFO
Checks supported languages
- identity_helper.exe (PID: 7740)
- wsol-pc-scan-Setup-2.0.31.exe (PID: 3876)
- wsol-pc-scan.exe (PID: 8)
- chcp.com (PID: 7816)
- wsol-pc-scan.exe (PID: 5912)
- wsol-pc-scan.exe (PID: 6184)
- wsol-pc-scan.exe (PID: 7244)
- speedtest.exe (PID: 904)
- chcp.com (PID: 736)
- chcp.com (PID: 7768)
- chcp.com (PID: 6228)
- chcp.com (PID: 2392)
- chcp.com (PID: 7424)
- chcp.com (PID: 5572)
- java.exe (PID: 4308)
Reads the computer name
- identity_helper.exe (PID: 7740)
- wsol-pc-scan-Setup-2.0.31.exe (PID: 3876)
- wsol-pc-scan.exe (PID: 8)
- wsol-pc-scan.exe (PID: 5912)
- wsol-pc-scan.exe (PID: 6184)
- speedtest.exe (PID: 904)
Reads Environment values
- identity_helper.exe (PID: 7740)
- wsol-pc-scan.exe (PID: 8)
Executable content was dropped or overwritten
- msedge.exe (PID: 6264)
- msedge.exe (PID: 644)
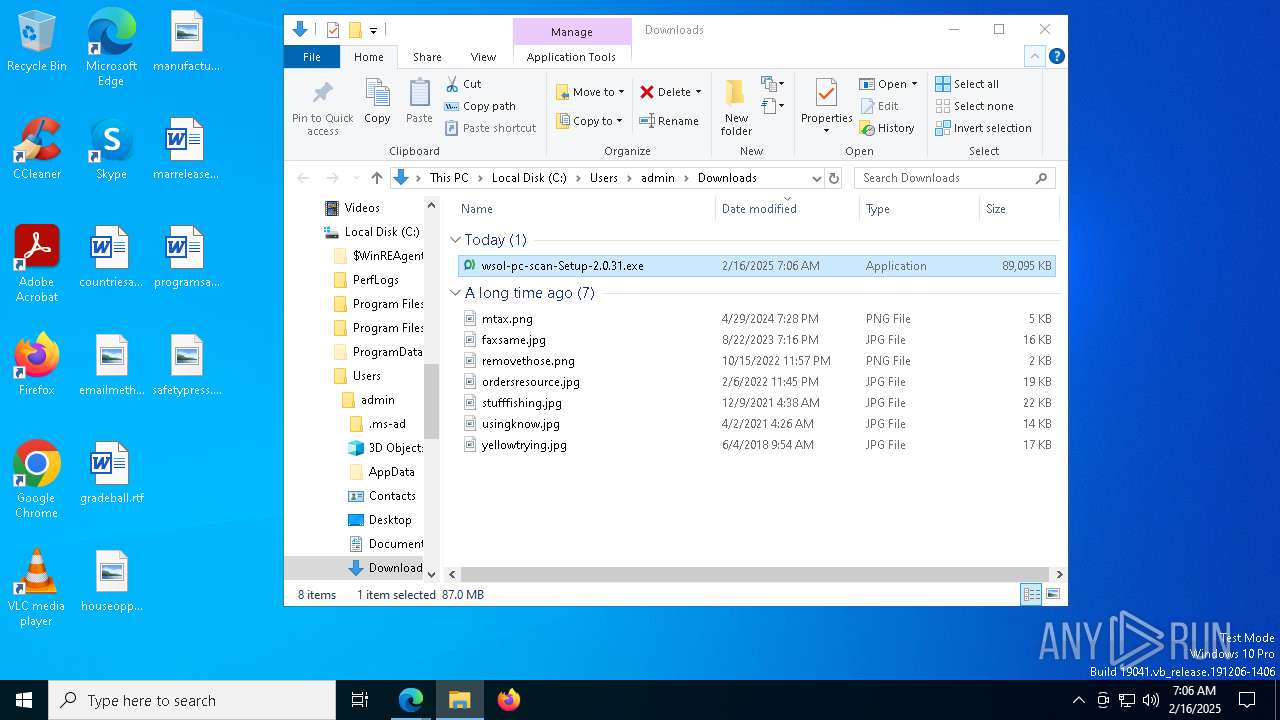
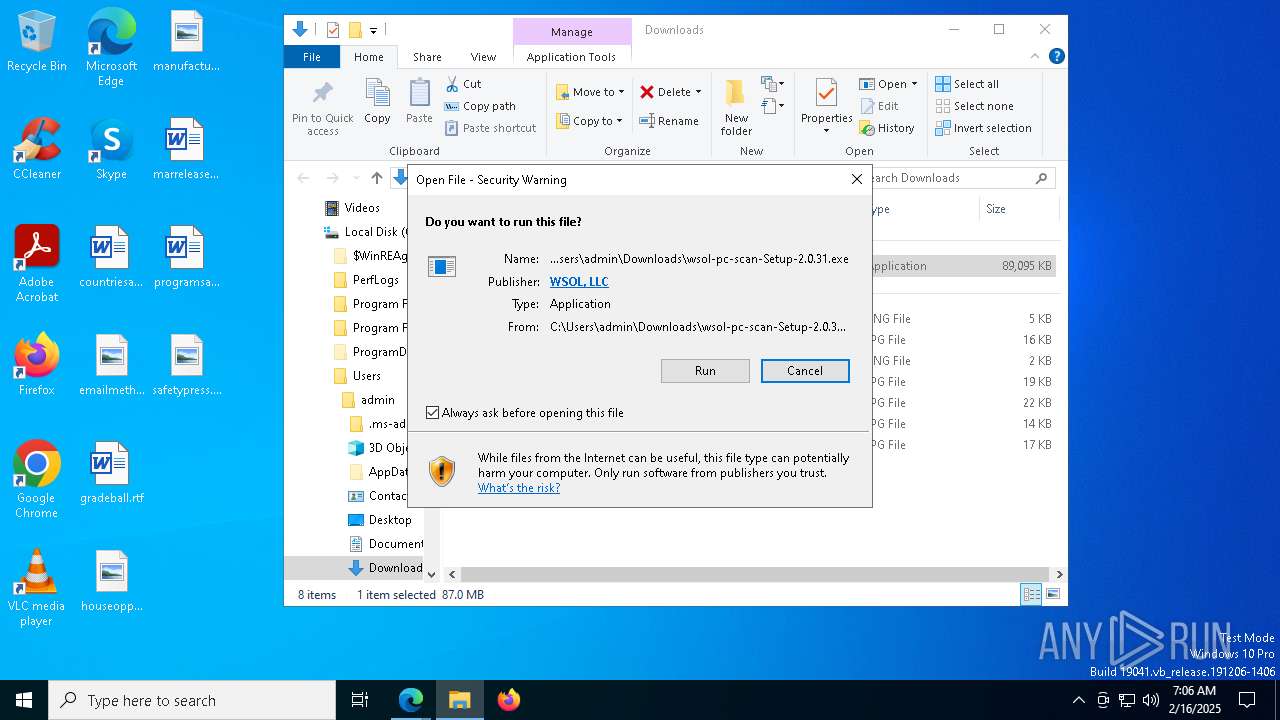
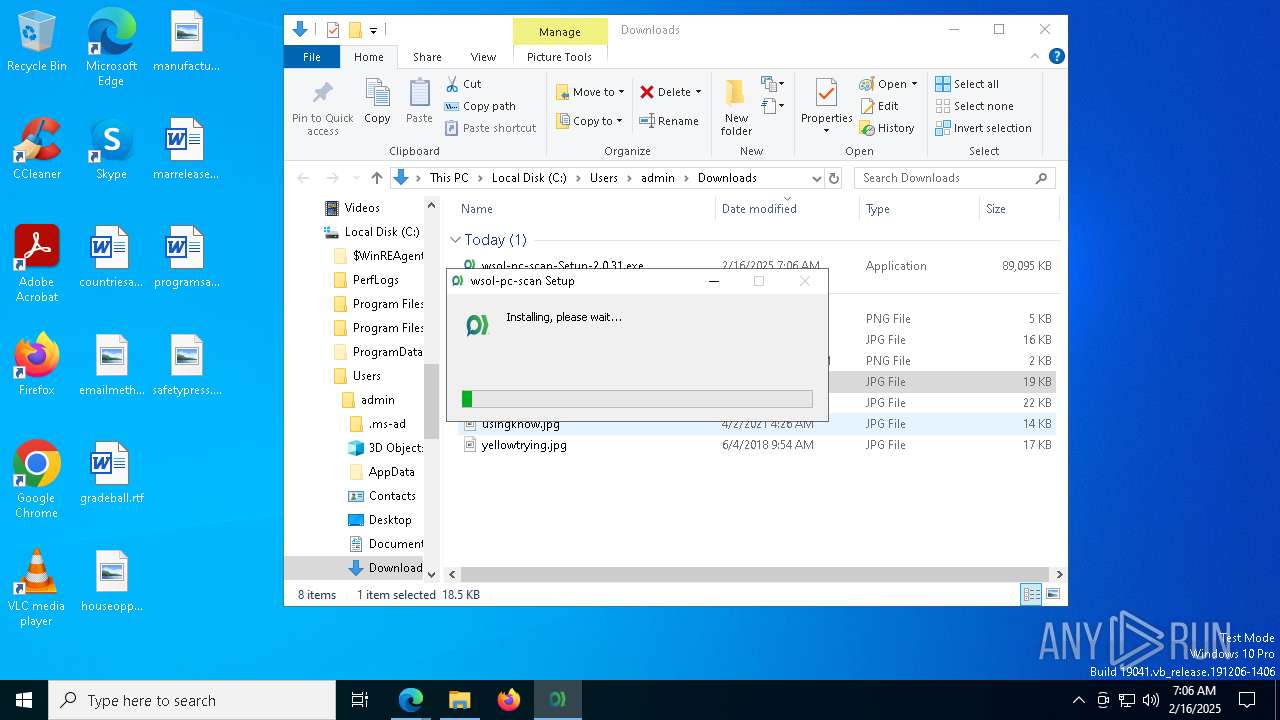
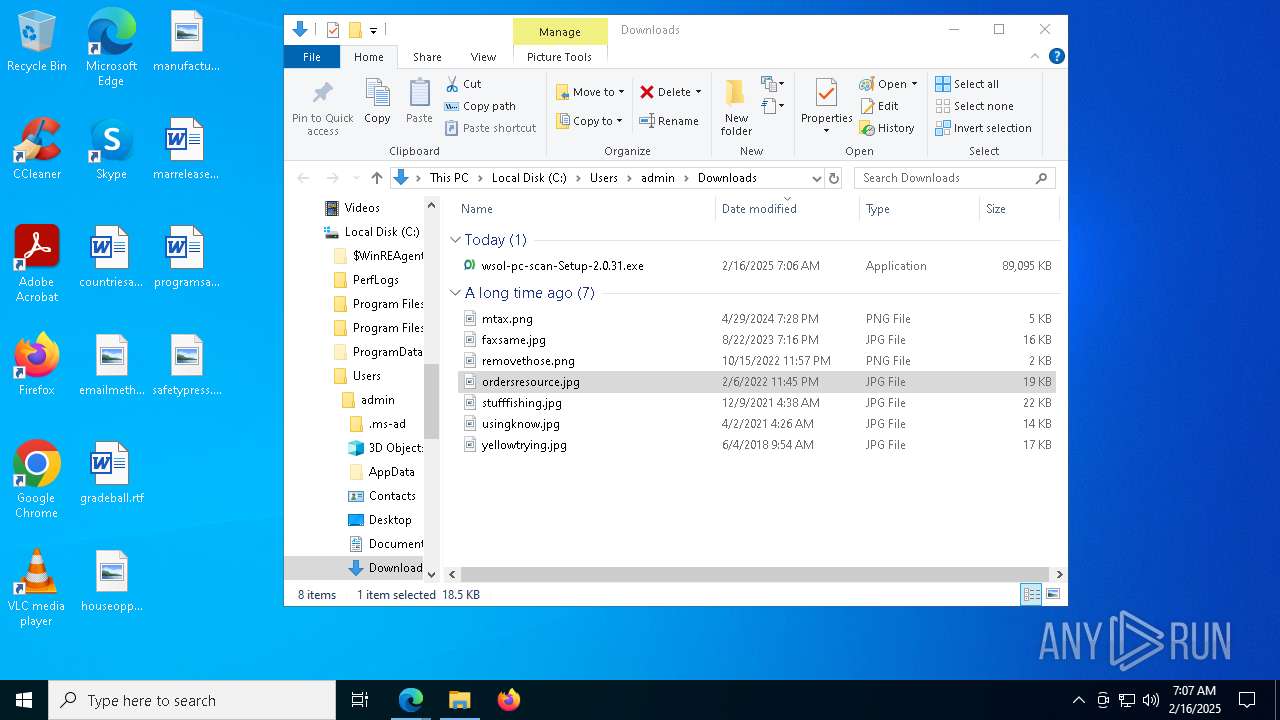
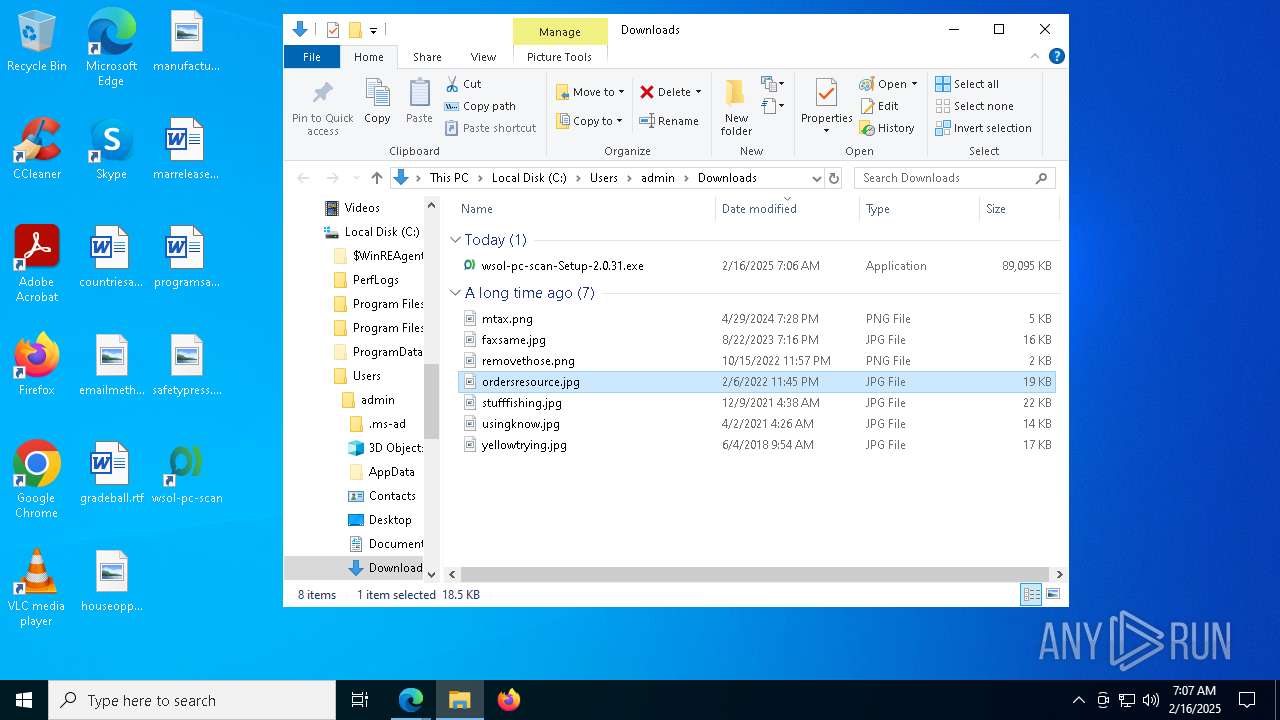
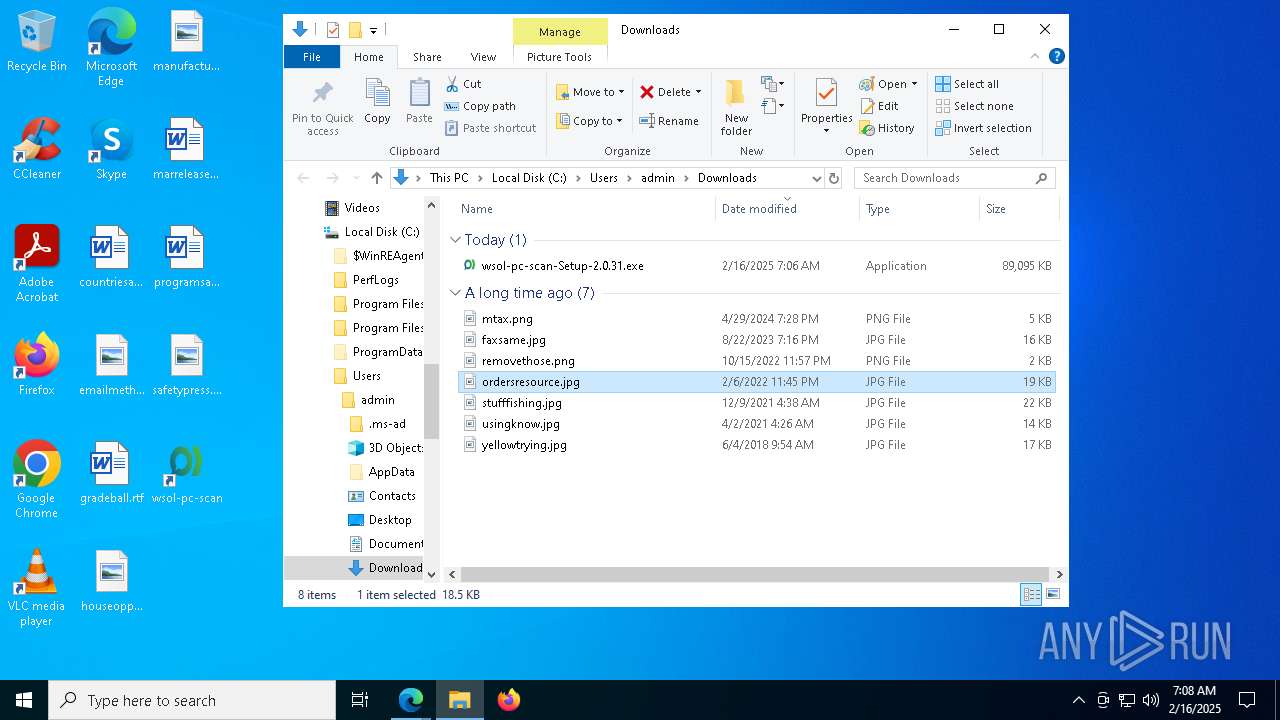
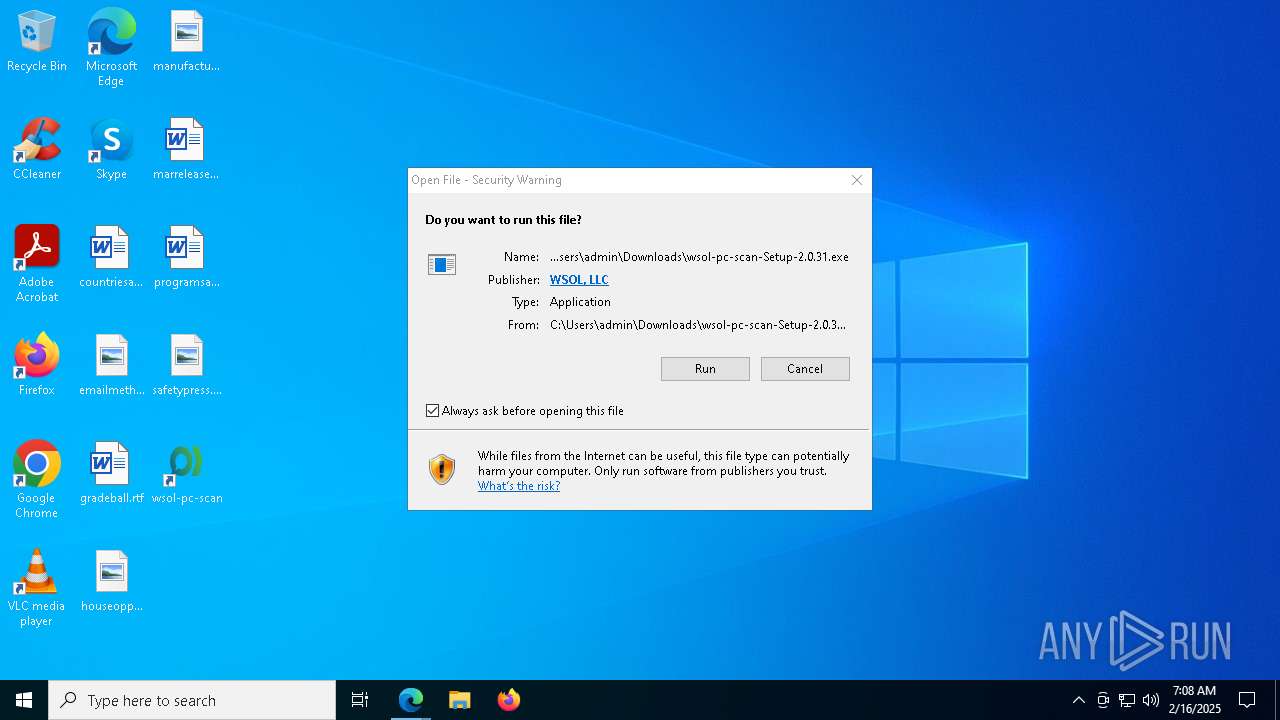
Manual execution by a user
- wsol-pc-scan-Setup-2.0.31.exe (PID: 3876)
- wsol-pc-scan.exe (PID: 8)
The sample compiled with english language support
- wsol-pc-scan-Setup-2.0.31.exe (PID: 3876)
- msedge.exe (PID: 644)
Create files in a temporary directory
- wsol-pc-scan-Setup-2.0.31.exe (PID: 3876)
- wsol-pc-scan.exe (PID: 8)
- java.exe (PID: 4308)
Application launched itself
- msedge.exe (PID: 6264)
Creates files or folders in the user directory
- wsol-pc-scan-Setup-2.0.31.exe (PID: 3876)
- wsol-pc-scan.exe (PID: 8)
- speedtest.exe (PID: 904)
- wsol-pc-scan.exe (PID: 6184)
Reads product name
- wsol-pc-scan.exe (PID: 8)
Changes the display of characters in the console
- cmd.exe (PID: 6488)
- cmd.exe (PID: 5968)
- cmd.exe (PID: 4872)
- cmd.exe (PID: 4024)
- cmd.exe (PID: 8044)
- cmd.exe (PID: 7964)
- cmd.exe (PID: 4804)
Reads CPU info
- wsol-pc-scan.exe (PID: 8)
Process checks computer location settings
- wsol-pc-scan.exe (PID: 8)
- wsol-pc-scan.exe (PID: 7244)
Checks proxy server information
- wsol-pc-scan.exe (PID: 8)
Checks operating system version
- speedtest.exe (PID: 904)
Reads the machine GUID from the registry
- wsol-pc-scan.exe (PID: 8)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 8064)
- WMIC.exe (PID: 8024)
- WMIC.exe (PID: 2976)
- WMIC.exe (PID: 6912)
- WMIC.exe (PID: 3992)
- WMIC.exe (PID: 2756)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7036)
- powershell.exe (PID: 7600)
Displays MAC addresses of computer network adapters
- getmac.exe (PID: 3288)
Creates files in the program directory
- java.exe (PID: 4308)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
280
Monitored processes
141
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 8 | "C:\Users\admin\AppData\Local\Programs\wsol-pc-scan\wsol-pc-scan.exe" | C:\Users\admin\AppData\Local\Programs\wsol-pc-scan\wsol-pc-scan.exe | explorer.exe | ||||||||||||
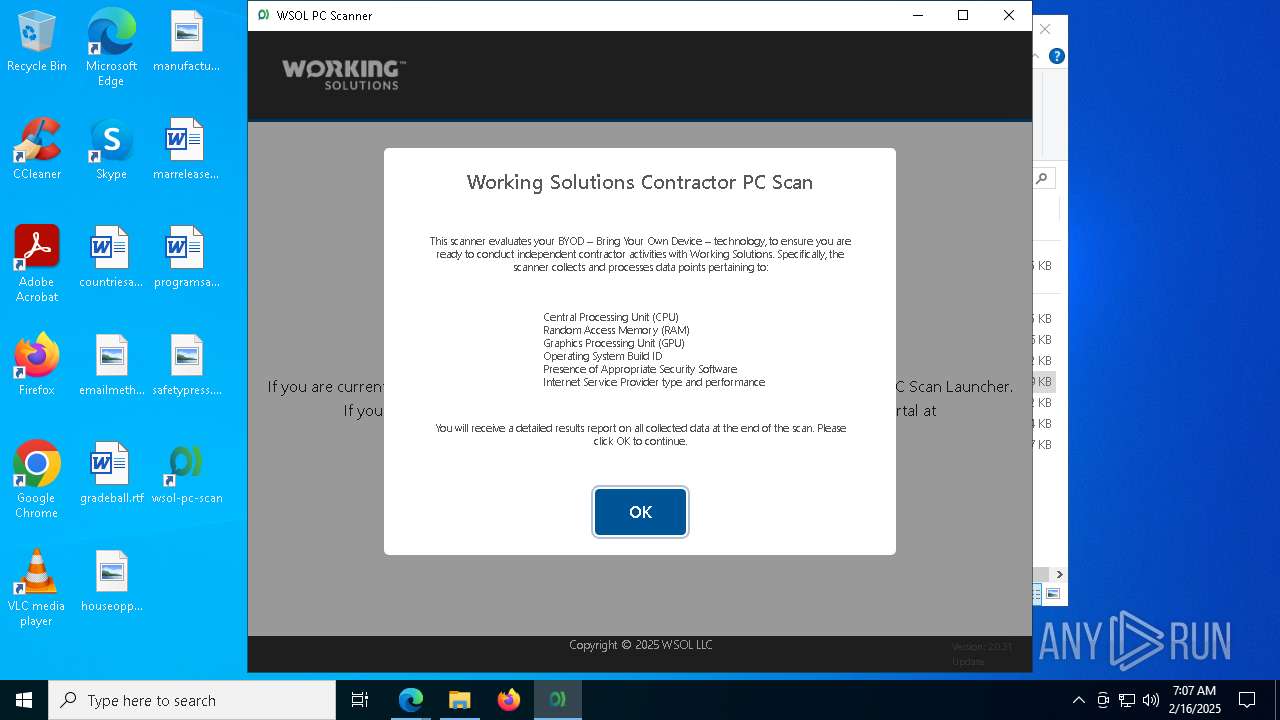
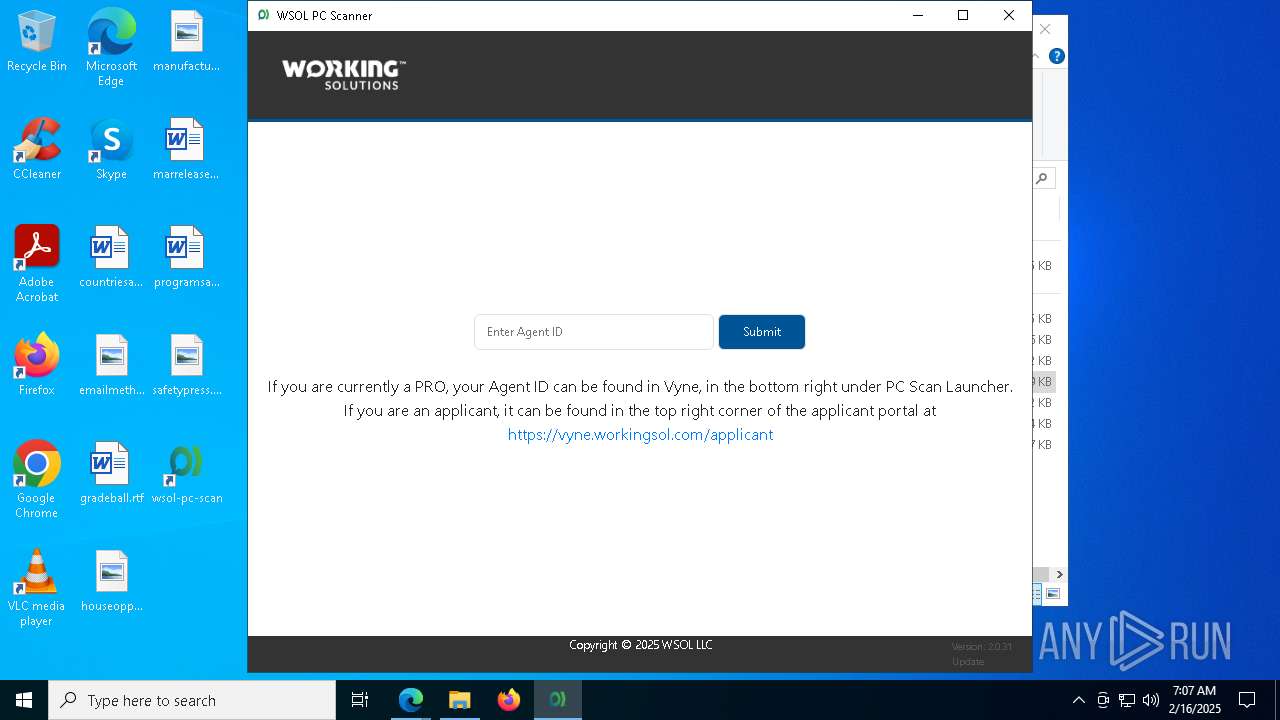
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: Working Solution PC Scan App, Used to Collect Agents Computer Specifications. Exit code: 0 Version: 2.0.31 Modules
| |||||||||||||||
| 524 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6696 --field-trial-handle=2300,i,10782130568225736782,11097406015734672496,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 736 | C:\WINDOWS\system32\chcp.com 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 904 | C:\Users\admin\AppData\Local\Programs\wsol-pc-scan\resources\bin\speedtest.exe --format=json --accept-license --accept-gdpr | C:\Users\admin\AppData\Local\Programs\wsol-pc-scan\resources\bin\speedtest.exe | wsol-pc-scan.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1172 | powershell.exe -NoLogo -InputFormat Text -NoExit -ExecutionPolicy Unrestricted -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wsol-pc-scan.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1612 | powershell.exe -ExecutionPolicy Bypass -NoProfile -NoLogo -NoExit -InputFormat Text -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wsol-pc-scan.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1616 | C:\WINDOWS\system32\cmd.exe /d /s /c "echo %COMPUTERNAME%.%USERDNSDOMAIN%" | C:\Windows\System32\cmd.exe | — | wsol-pc-scan.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2392 | C:\WINDOWS\system32\chcp.com 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
98 873
Read events
98 828
Write events
27
Delete events
18
Modification events
| (PID) Process: | (6264) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6264) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6264) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6264) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6264) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 88CE4750D38C2F00 | |||
| (PID) Process: | (6264) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D2AE5950D38C2F00 | |||
| (PID) Process: | (6264) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393896 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {70DCC68E-CD7C-40D2-8CB8-E26AD459110B} | |||
| (PID) Process: | (6264) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393896 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {CD03D480-EE6F-462E-A6E5-6E65EA607E69} | |||
| (PID) Process: | (6264) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: AC709450D38C2F00 | |||
| (PID) Process: | (6264) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
39
Suspicious files
548
Text files
108
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6264 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF13645b.TMP | — | |
MD5:— | SHA256:— | |||
| 6264 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6264 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF136489.TMP | — | |
MD5:— | SHA256:— | |||
| 6264 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6264 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF136489.TMP | — | |
MD5:— | SHA256:— | |||
| 6264 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6264 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF136489.TMP | — | |
MD5:— | SHA256:— | |||
| 6264 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6264 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF136489.TMP | — | |
MD5:— | SHA256:— | |||
| 6264 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
56
TCP/UDP connections
110
DNS requests
93
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7136 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1739985685&P2=404&P3=2&P4=CknX3YTr4ajjHdpRi45zNayFEwdF5YGYE%2f5KQS%2f%2bteXdidKskcSSTNps6ek%2fvA3ebx334y4t8i%2f04nIXaSHm7g%3d%3d | US | binary | 1.09 Kb | whitelisted |
6264 | msedge.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | US | binary | 471 b | whitelisted |
6264 | msedge.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | US | binary | 727 b | whitelisted |
7136 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1739985685&P2=404&P3=2&P4=CknX3YTr4ajjHdpRi45zNayFEwdF5YGYE%2f5KQS%2f%2bteXdidKskcSSTNps6ek%2fvA3ebx334y4t8i%2f04nIXaSHm7g%3d%3d | US | binary | 4.36 Kb | whitelisted |
6264 | msedge.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAgZbb7jDo7FgOVZIXD3Lwo%3D | US | binary | 727 b | whitelisted |
7136 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1739985686&P2=404&P3=2&P4=WKHPqPyU2lTy3UukXX7ZbCLg07dOelnhxg0RlO2747mqwZJcSVy%2f%2b5fv3x4DFtwejpSfuGKpfNk62SkvvixA1Q%3d%3d | US | compressed | 7.21 Kb | whitelisted |
7136 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1739985685&P2=404&P3=2&P4=CknX3YTr4ajjHdpRi45zNayFEwdF5YGYE%2f5KQS%2f%2bteXdidKskcSSTNps6ek%2fvA3ebx334y4t8i%2f04nIXaSHm7g%3d%3d | US | binary | 9.60 Kb | whitelisted |
7136 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1739985686&P2=404&P3=2&P4=WKHPqPyU2lTy3UukXX7ZbCLg07dOelnhxg0RlO2747mqwZJcSVy%2f%2b5fv3x4DFtwejpSfuGKpfNk62SkvvixA1Q%3d%3d | US | binary | 43.2 Kb | whitelisted |
7136 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1739985685&P2=404&P3=2&P4=CknX3YTr4ajjHdpRi45zNayFEwdF5YGYE%2f5KQS%2f%2bteXdidKskcSSTNps6ek%2fvA3ebx334y4t8i%2f04nIXaSHm7g%3d%3d | US | compressed | 7.21 Kb | whitelisted |
7136 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1739985686&P2=404&P3=2&P4=WKHPqPyU2lTy3UukXX7ZbCLg07dOelnhxg0RlO2747mqwZJcSVy%2f%2b5fv3x4DFtwejpSfuGKpfNk62SkvvixA1Q%3d%3d | US | binary | 176 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4992 | svchost.exe | 2.16.164.34:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4992 | svchost.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6264 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6584 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6584 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6584 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6584 | msedge.exe | 20.60.240.33:443 | wsolsqlprod.blob.core.windows.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
wsolsqlprod.blob.core.windows.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6584 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Blob Storage (.blob .core .windows .net) |
6584 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Blob Storage (.blob .core .windows .net) |
6184 | wsol-pc-scan.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6184 | wsol-pc-scan.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6184 | wsol-pc-scan.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
6184 | wsol-pc-scan.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
6184 | wsol-pc-scan.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
6184 | wsol-pc-scan.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
2192 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.from-ks .com Domain |