| File name: | Test2.exe |
| Full analysis: | https://app.any.run/tasks/18e04358-4ac8-42eb-88a7-bbbedea6823d |
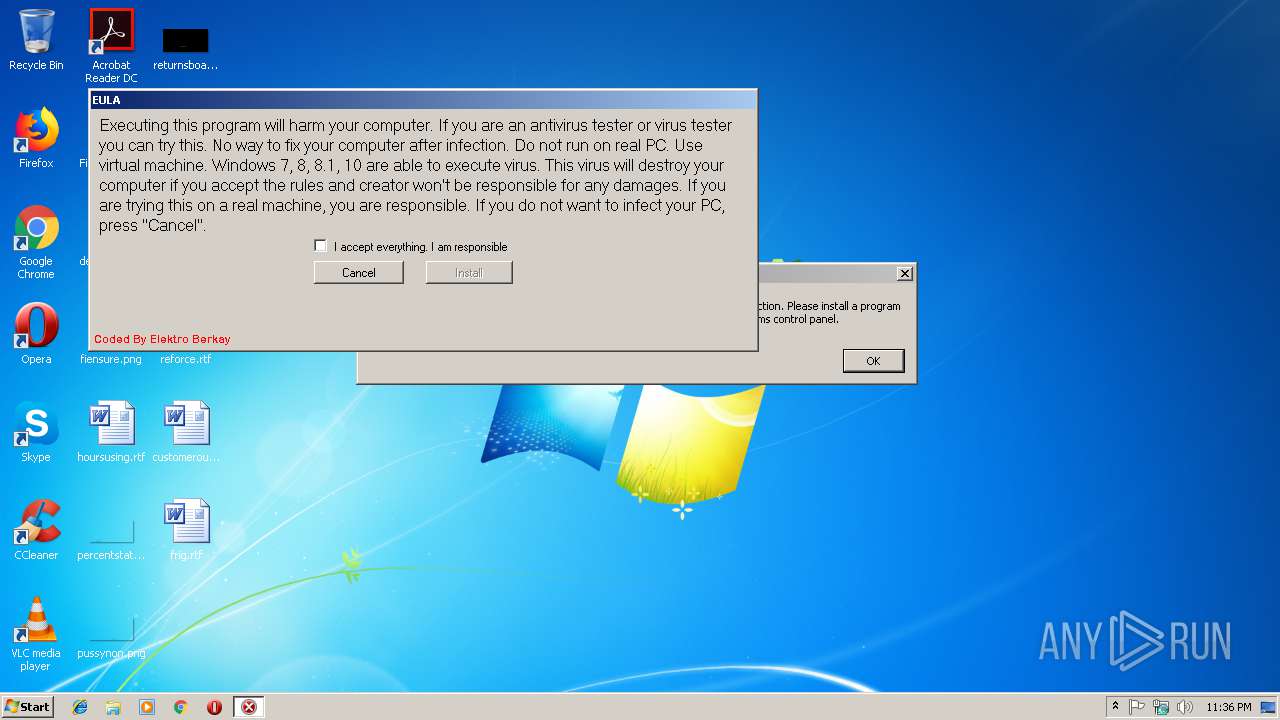
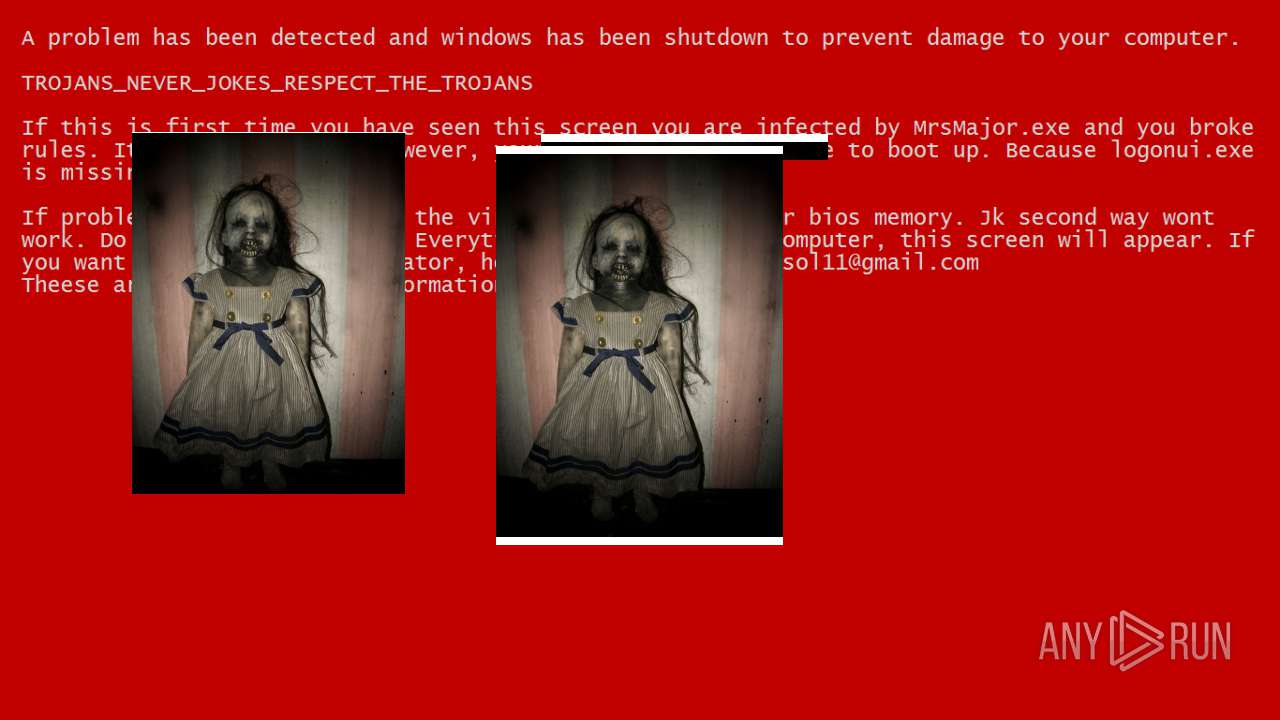
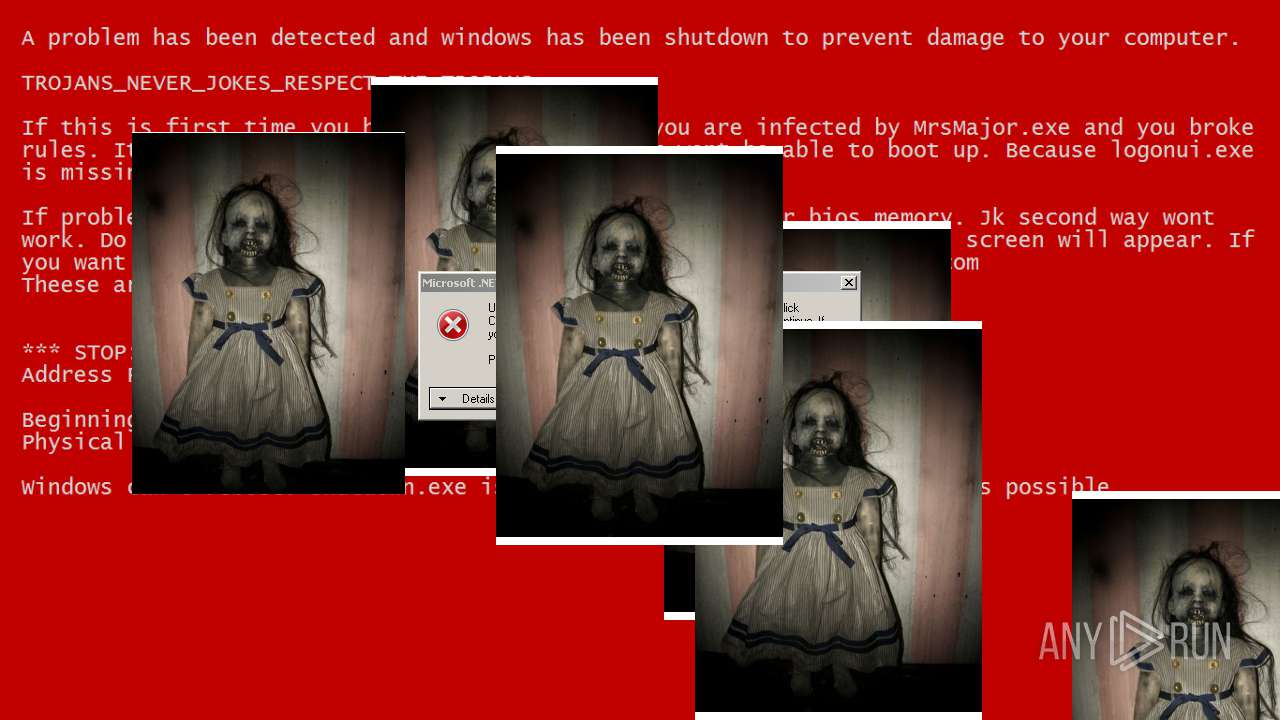
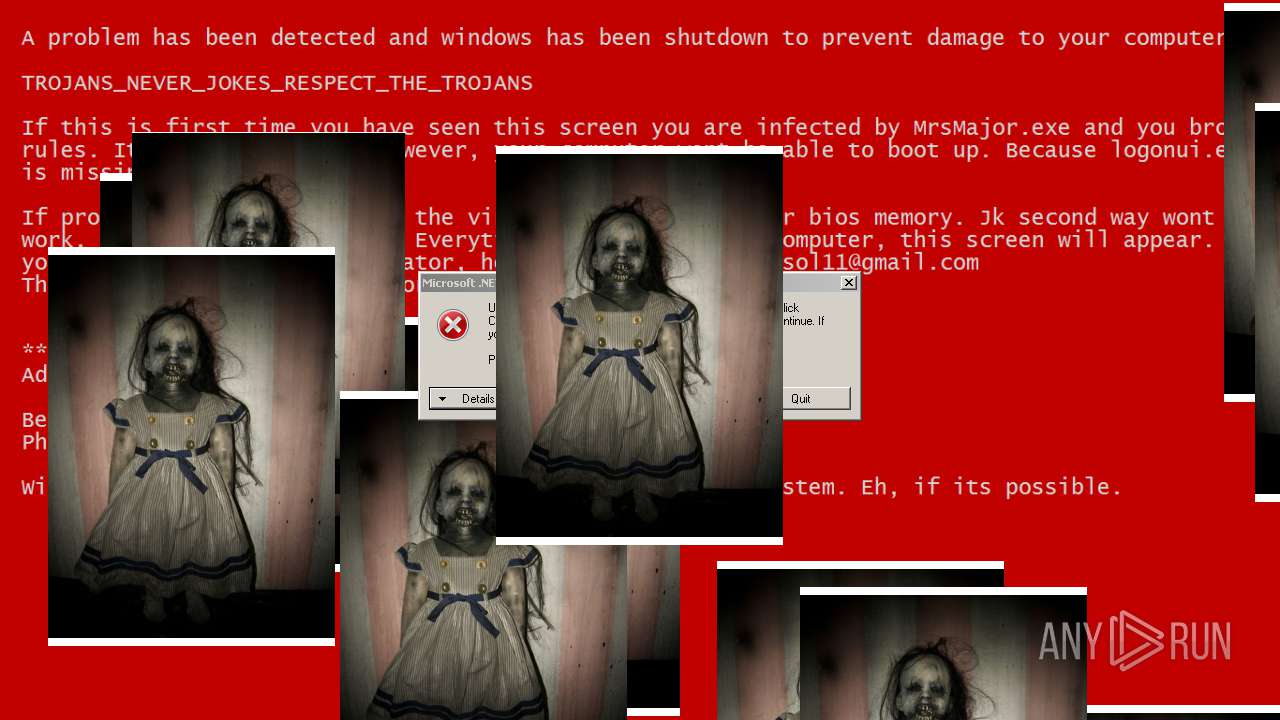
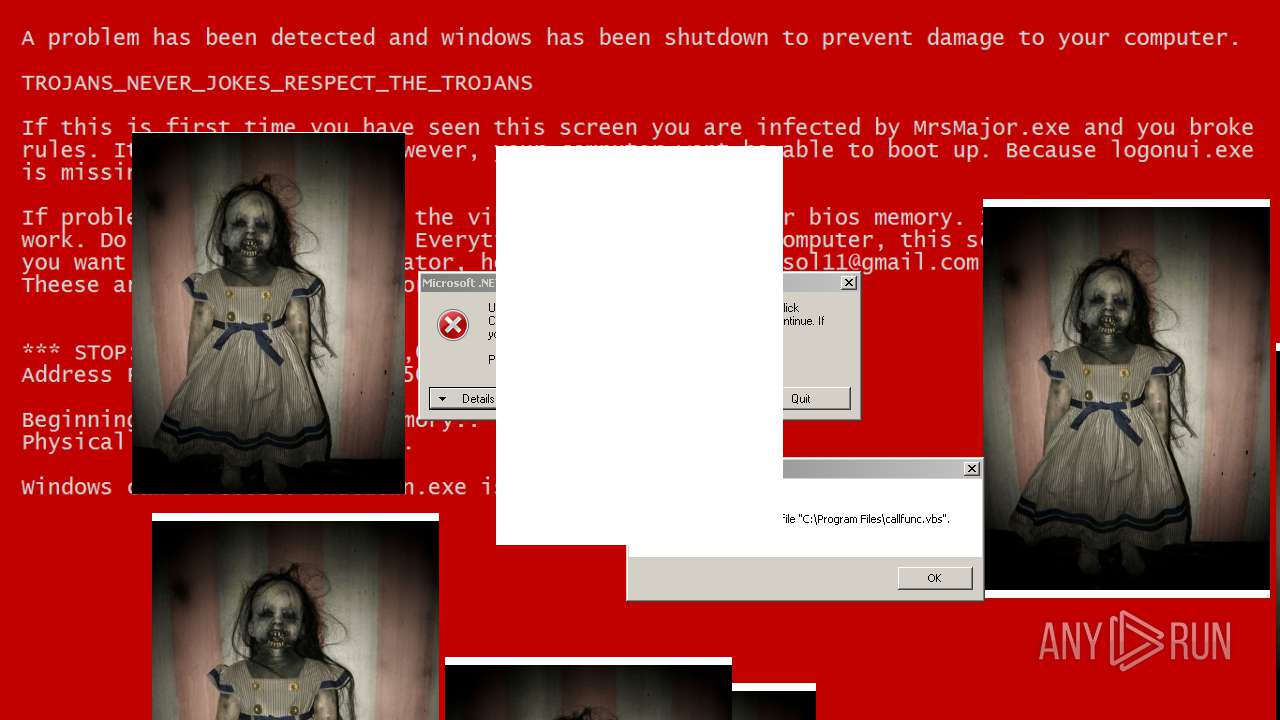
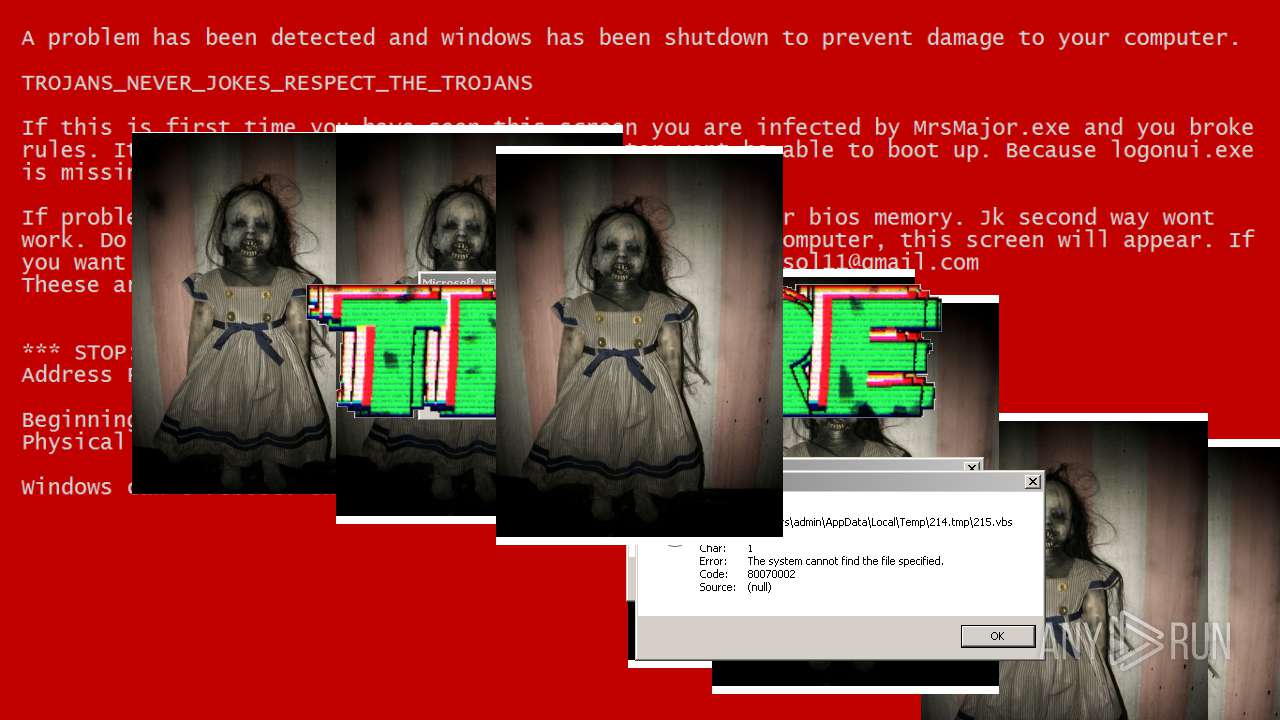
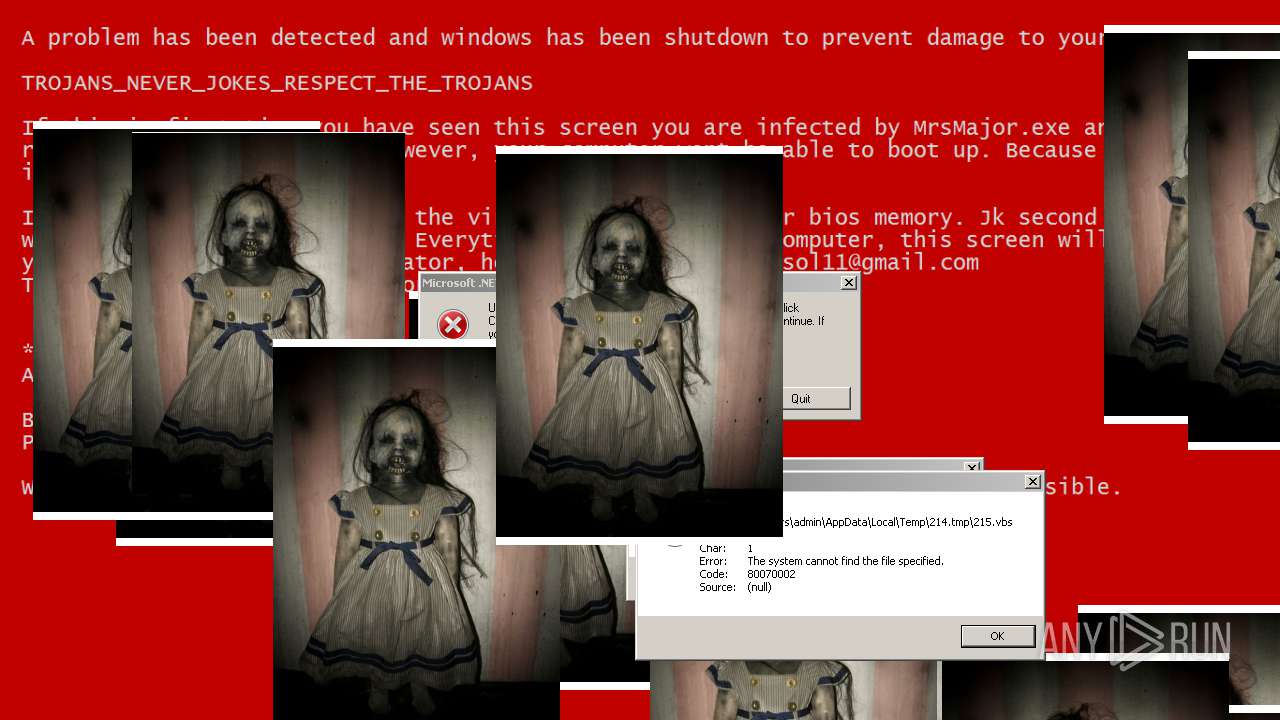
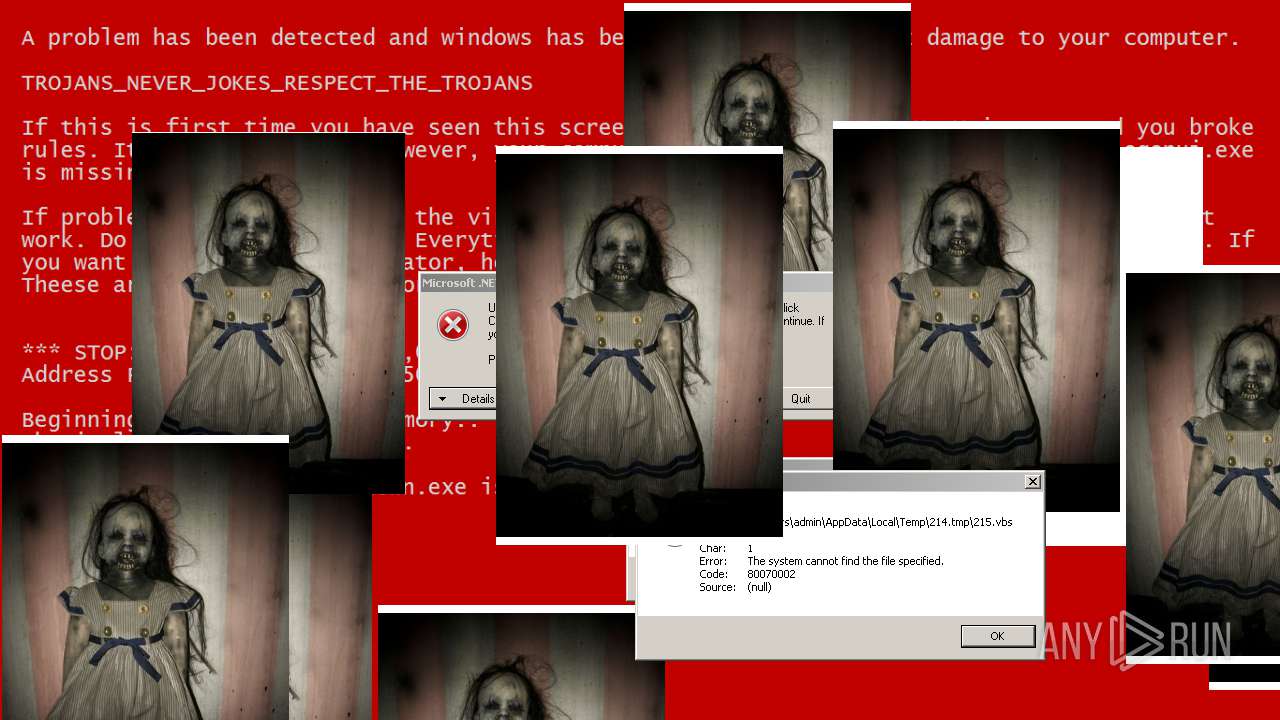
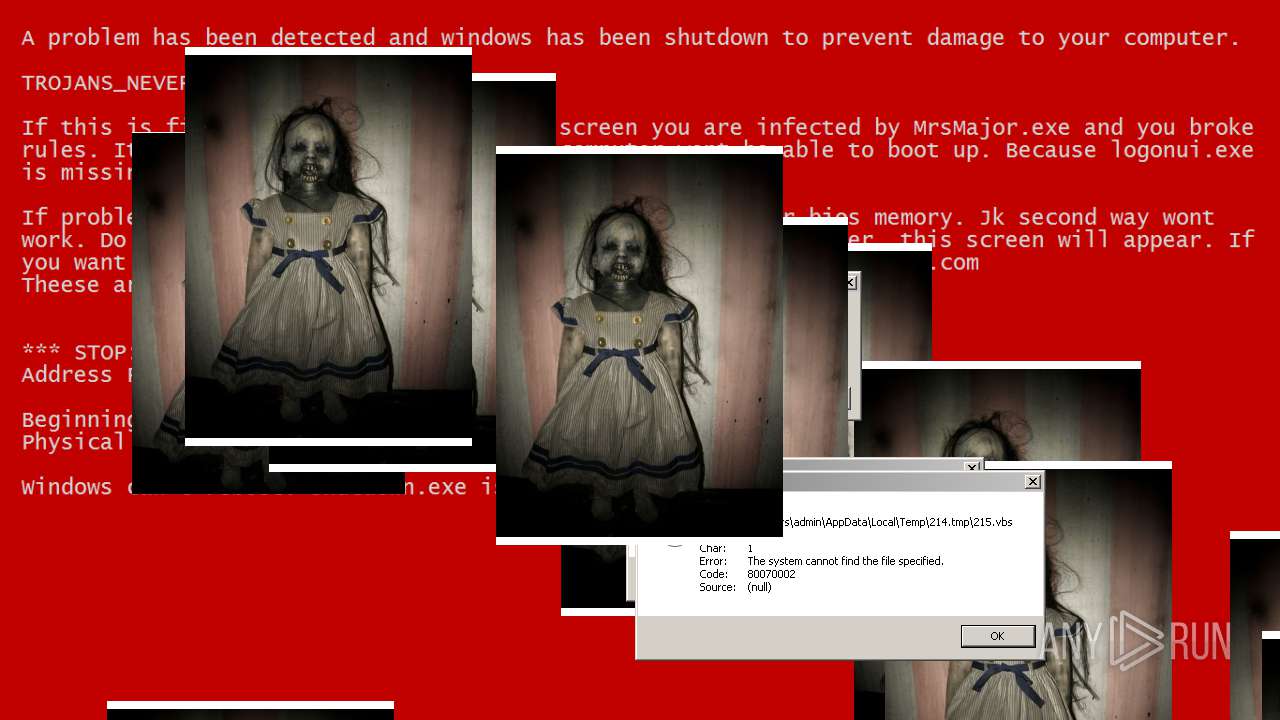
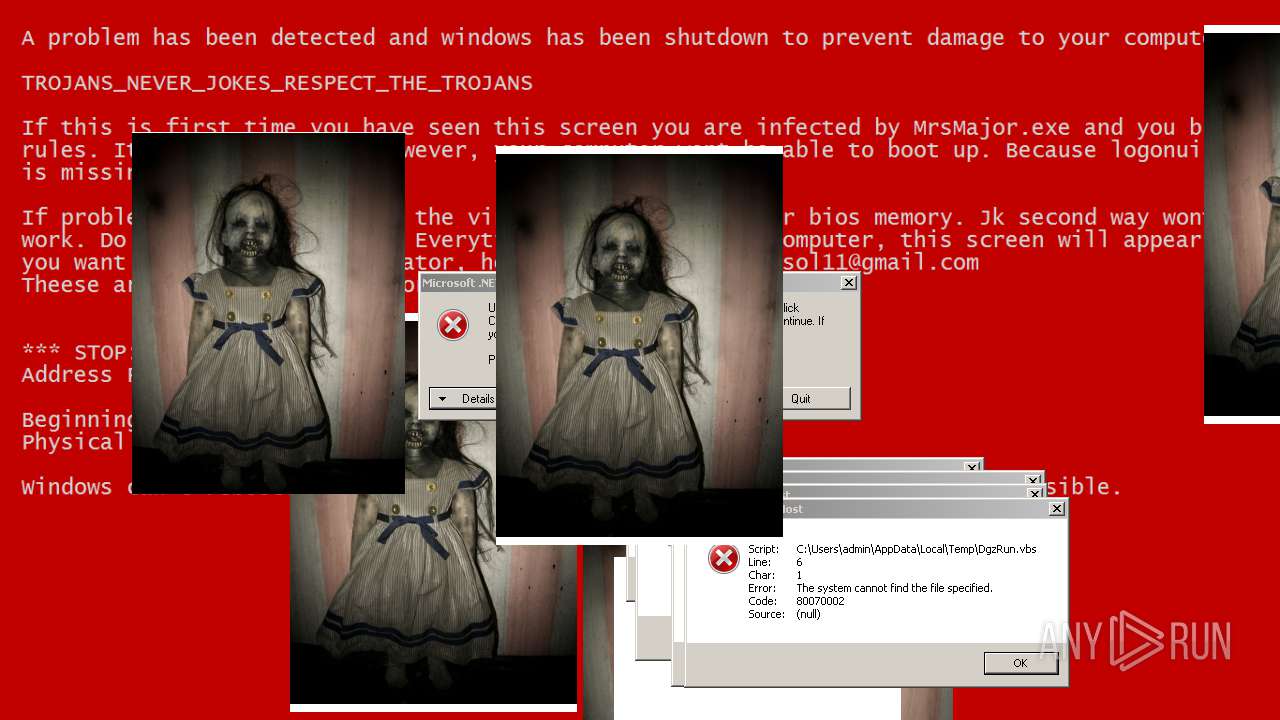
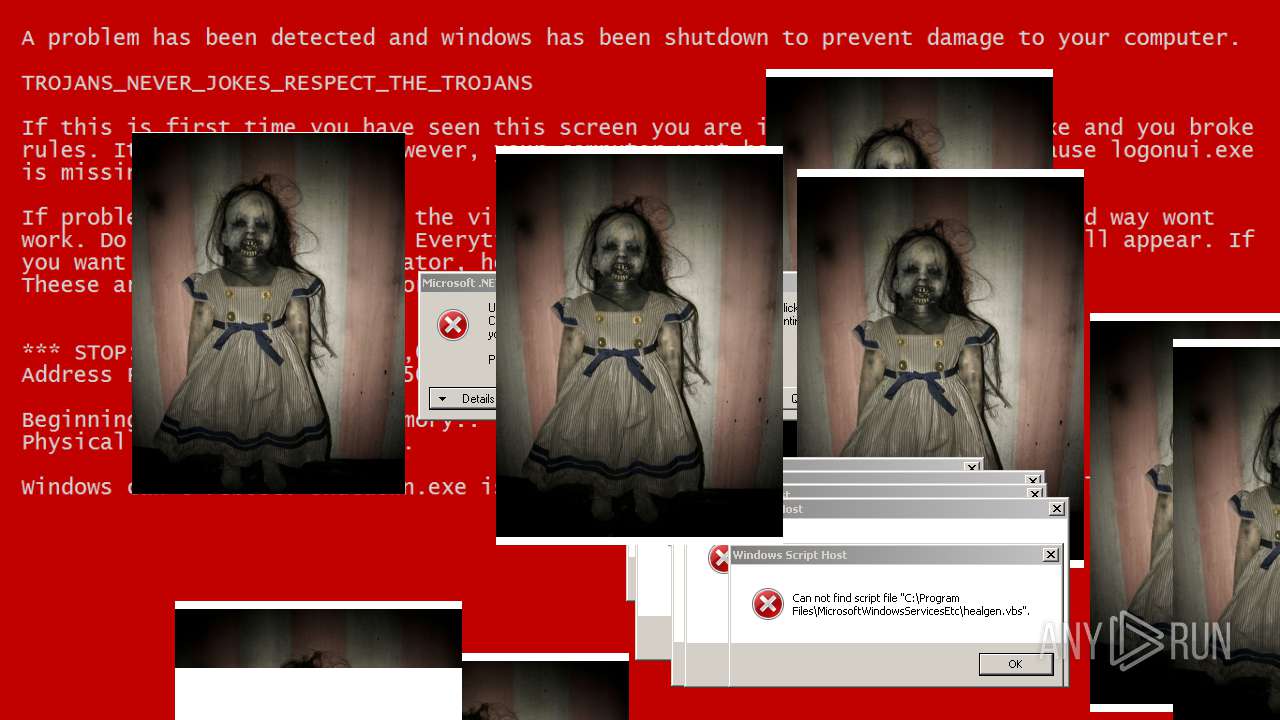
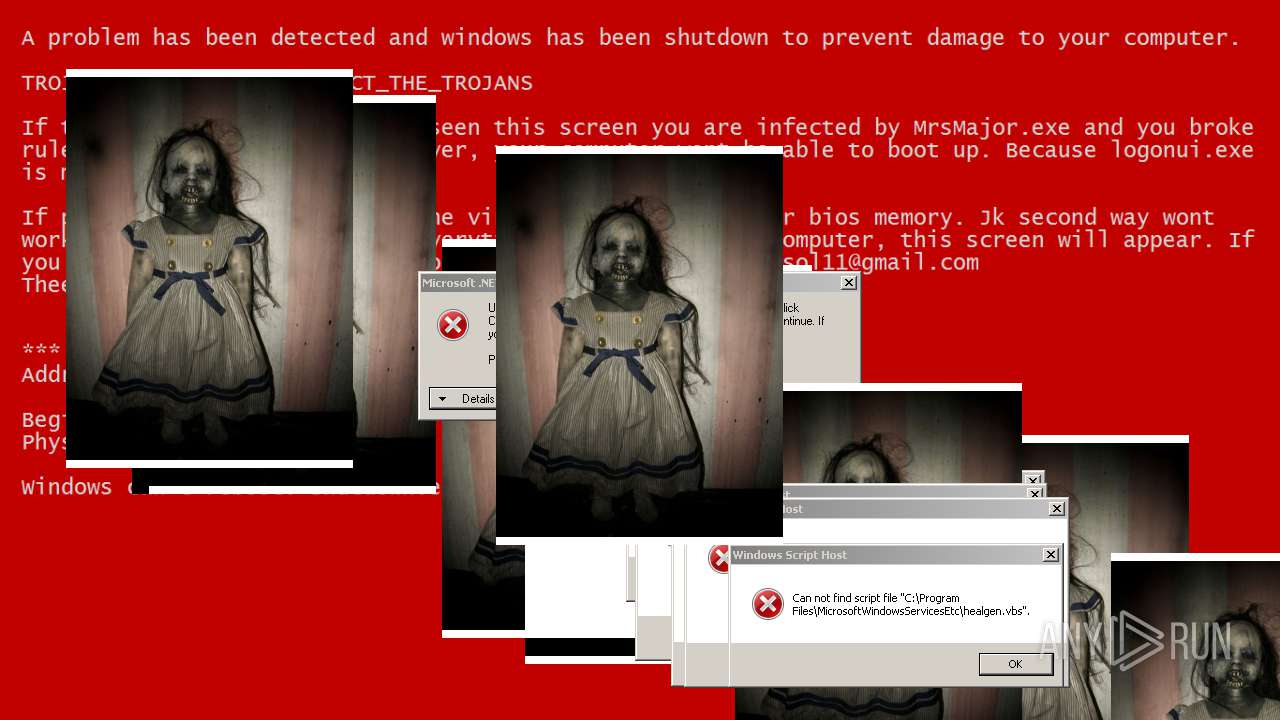
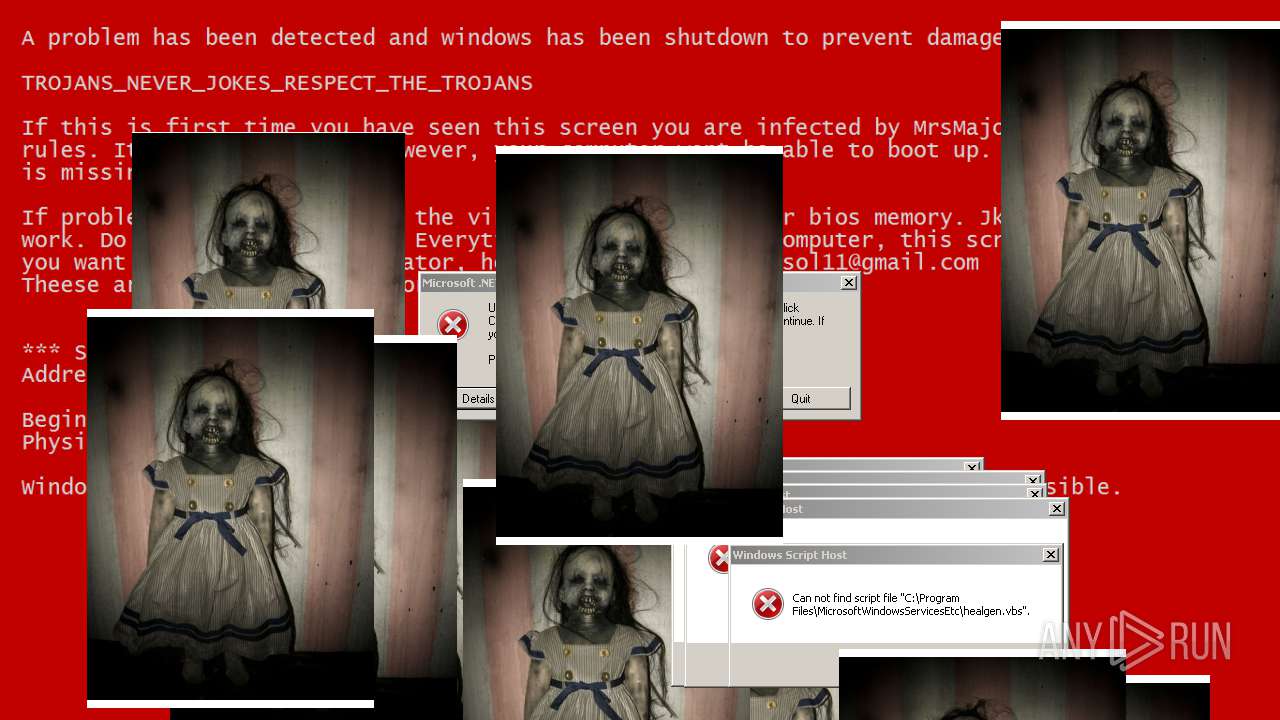
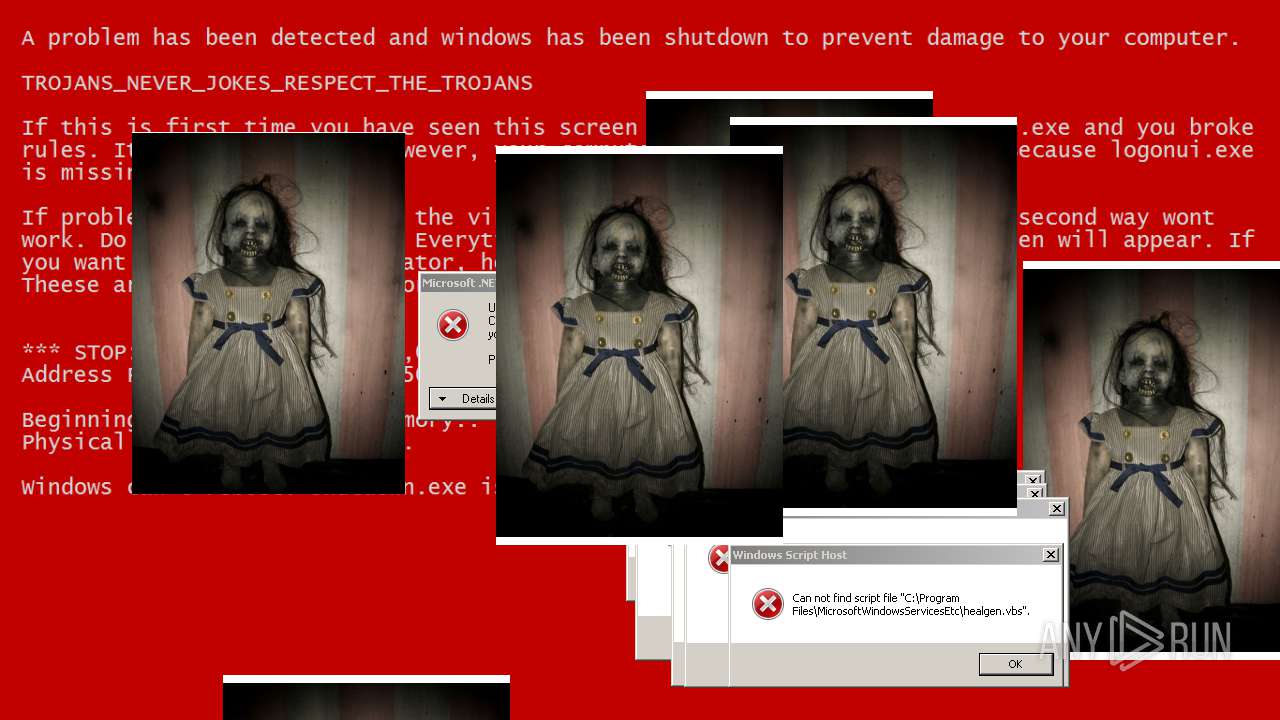
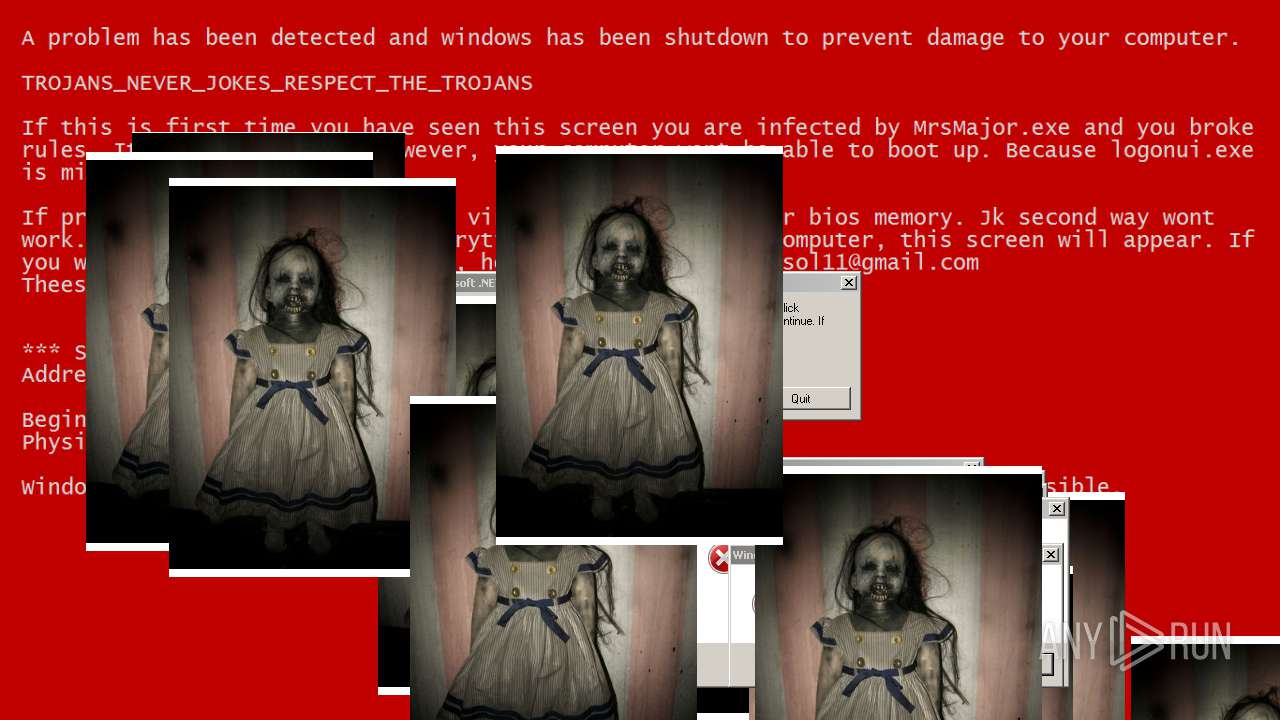
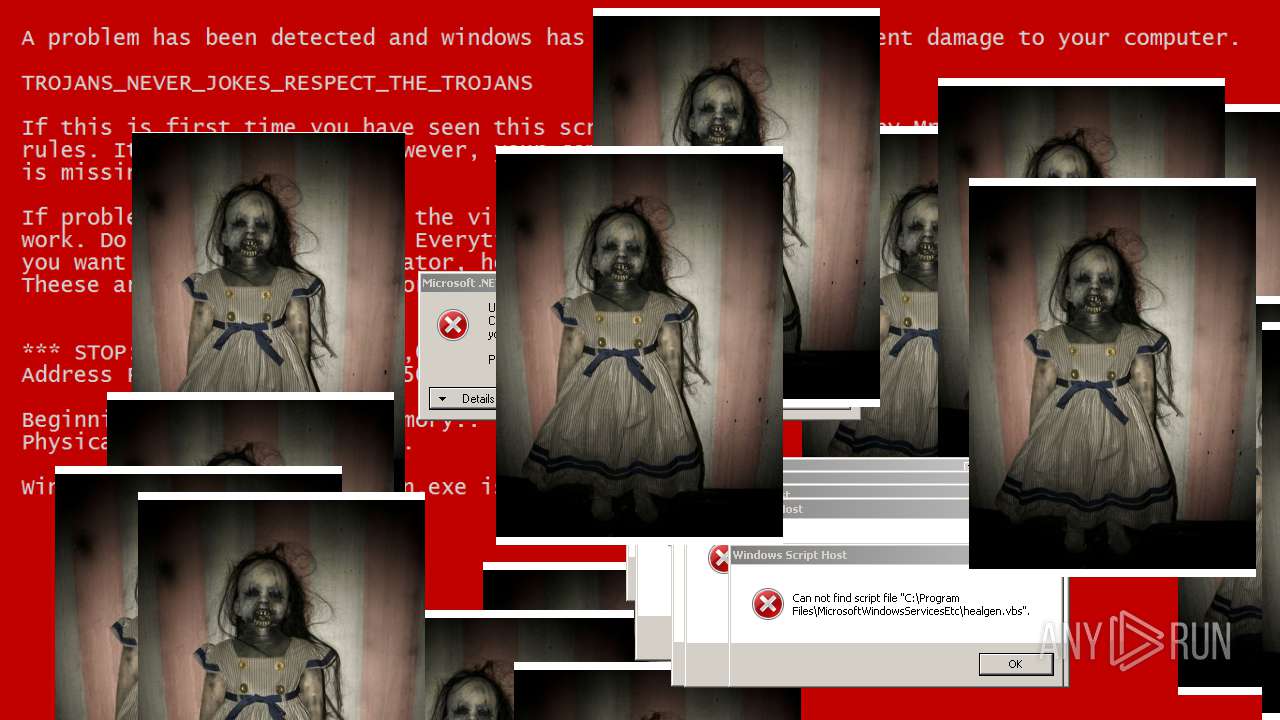
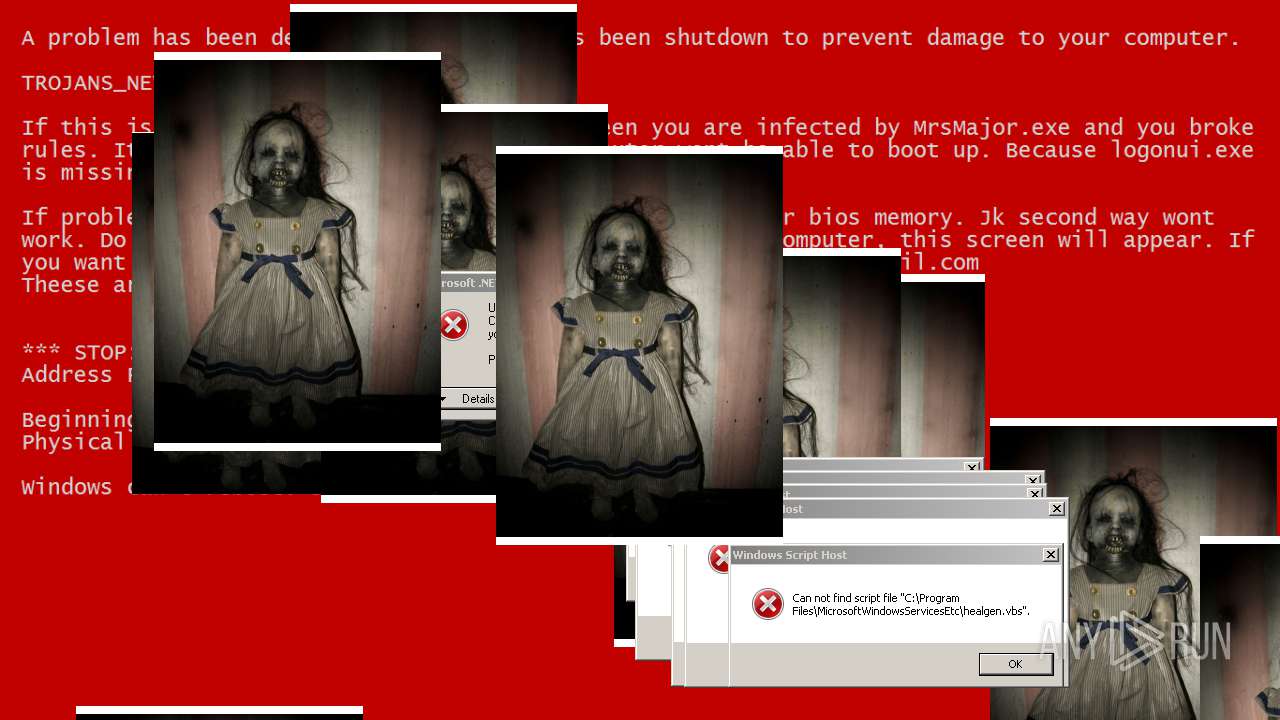
| Verdict: | Malicious activity |
| Analysis date: | January 14, 2019, 23:35:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | CD2B185F47E5DF6B4D91955C33905B28 |
| SHA1: | 152E32219A27988C1C963C9C636A19B6D44DD1C7 |
| SHA256: | 3D69490BC435E67CE4E207D0F7D303E9F6B21A8E5B37D07F46EC46E71351ABD2 |
| SSDEEP: | 196608:I0ptmTLSdWuRc+F/vzCbAnMNVcngNAXKgIKDG8J1uzPECyQ5GnwjTnBSalqt7FoI:ImtmawuRcurGIgNCiQ1F/3wjzUano7Jz |
MALICIOUS
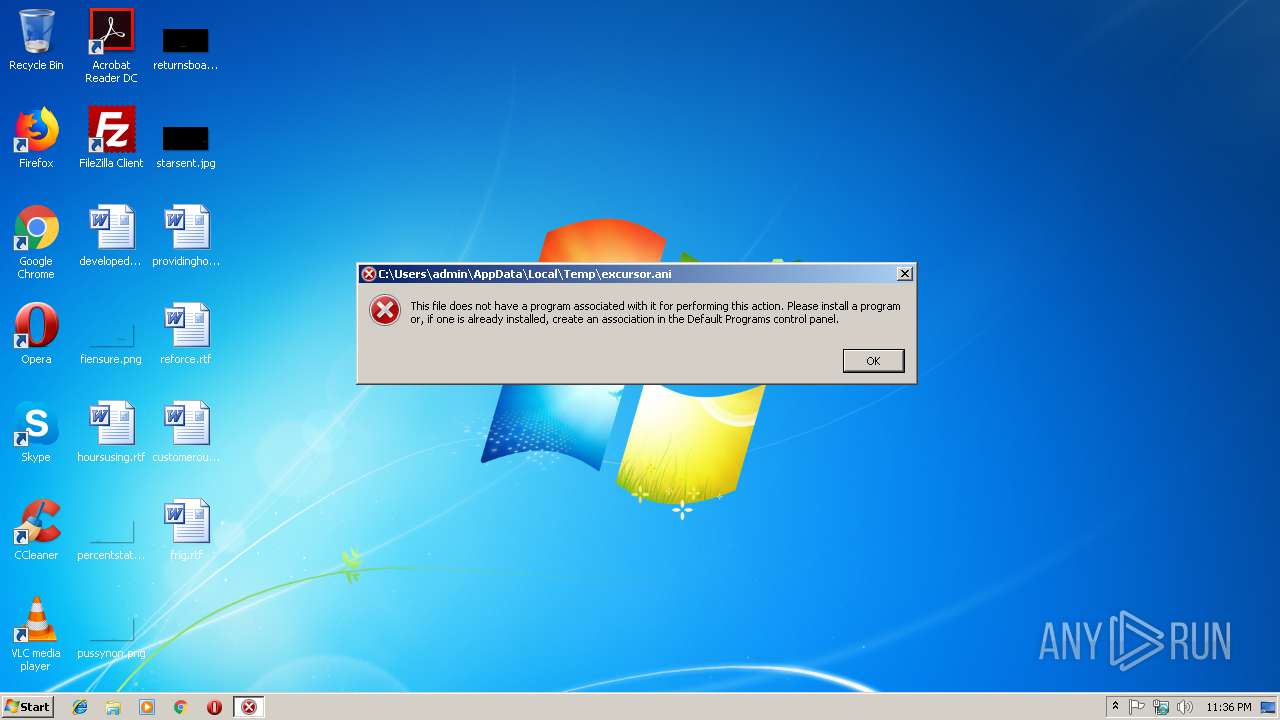
Application was dropped or rewritten from another process
- eula32.exe (PID: 3848)
- runner32s.exe (PID: 2468)
- WinScrew.exe (PID: 3764)
- runner32s.exe (PID: 2200)
- RuntimeChecker.exe (PID: 2324)
- WinScrew.exe (PID: 4092)
- runner32s.exe (PID: 4064)
- rsod.exe (PID: 3508)
- RuntimeChecker.exe (PID: 3096)
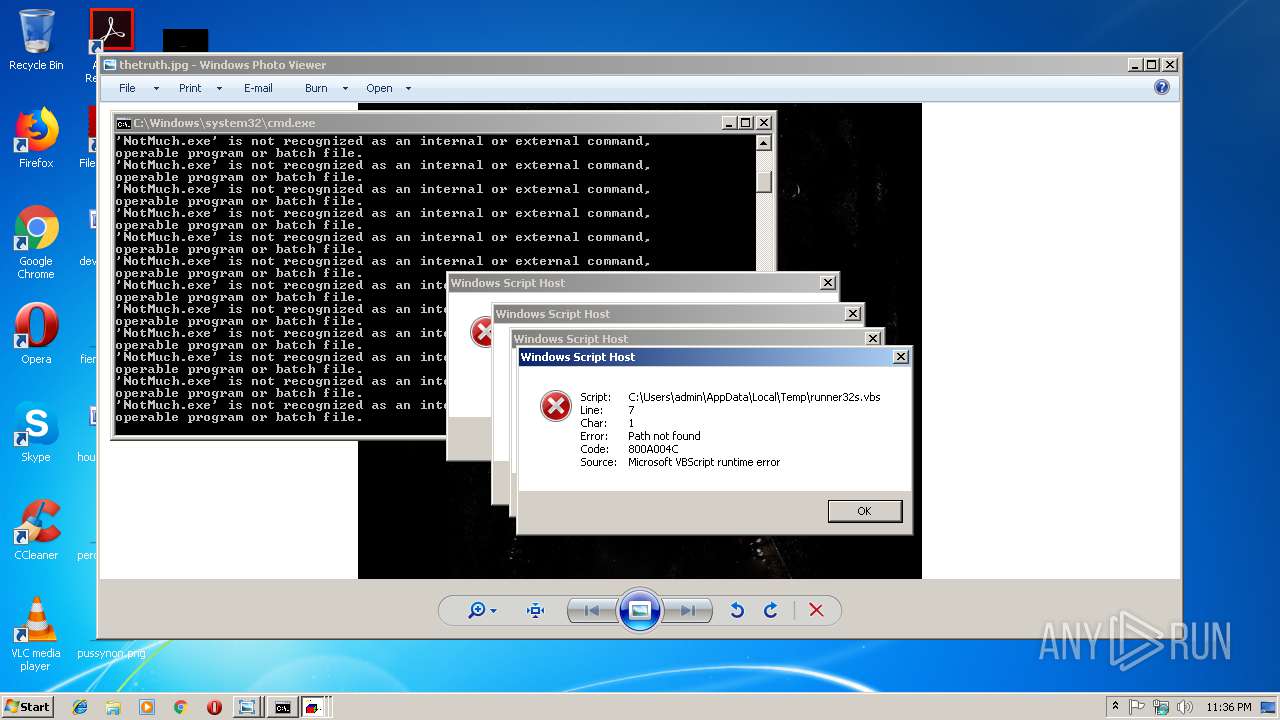
- NotMuch.exe (PID: 4012)
- majorlist.exe (PID: 2624)
- Major.exe (PID: 3676)
- runner32s.exe (PID: 3080)
- majordared.exe (PID: 3828)
- Major.exe (PID: 2628)
- runner32s.exe (PID: 3344)
- BossDaMajor.exe (PID: 3752)
- majorlist.exe (PID: 2396)
- BossDaMajor.exe (PID: 2796)
- bsod.exe (PID: 3764)
- GetReady.exe (PID: 2540)
- majorsod.exe (PID: 3392)
- GetReady.exe (PID: 3344)
- breakrule.exe (PID: 3792)
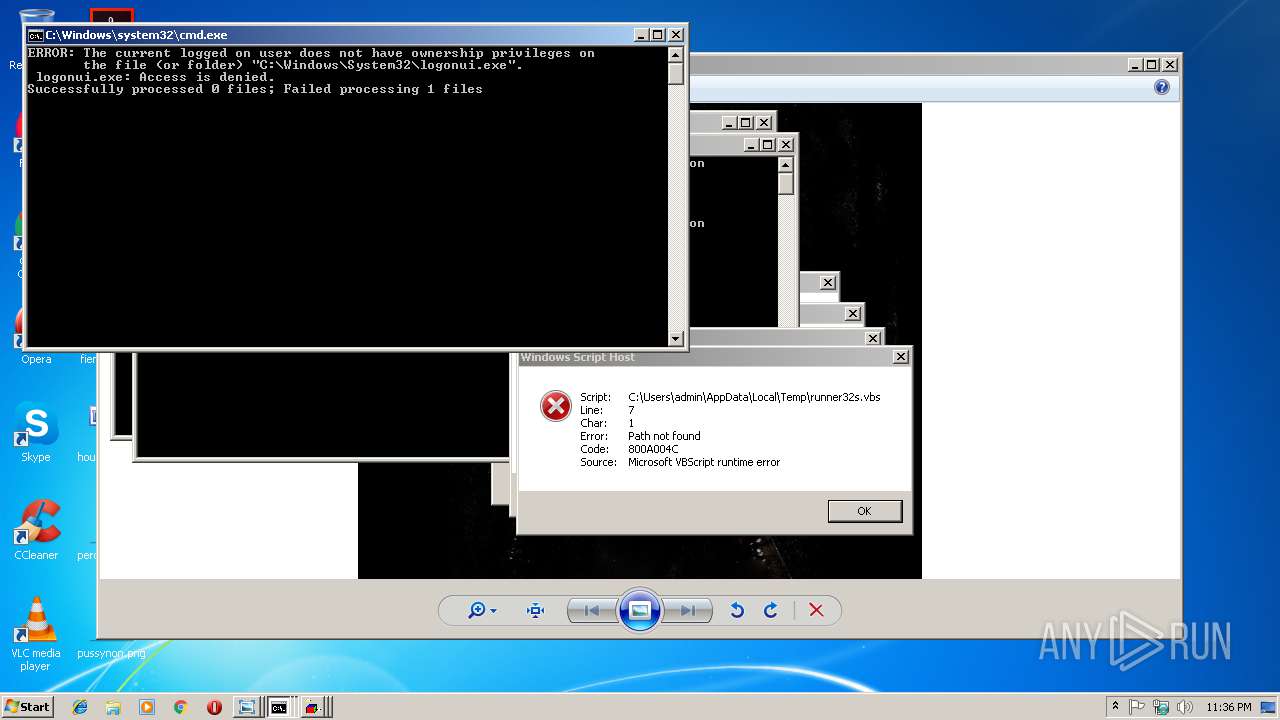
Uses TASKKILL.EXE to kill security tools
- cmd.exe (PID: 2552)
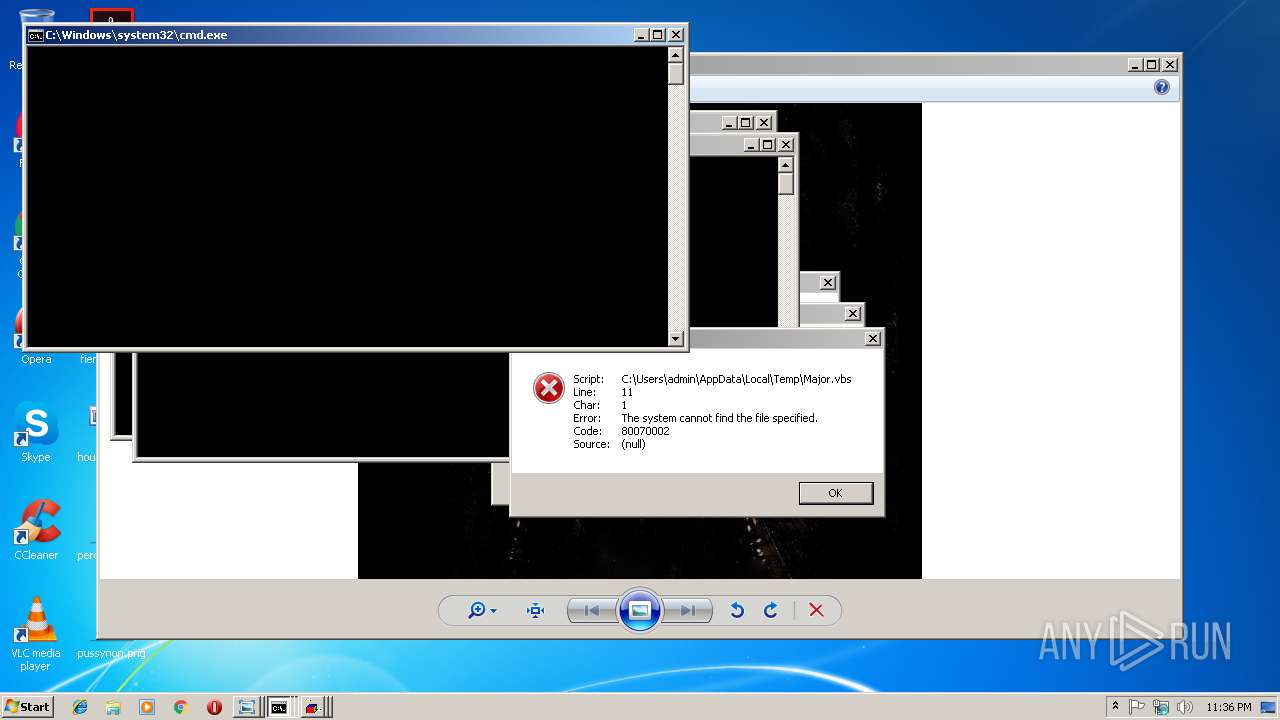
Disables registry editing tools (regedit)
- wscript.exe (PID: 3740)
Task Manager has been disabled (taskmgr)
- wscript.exe (PID: 3740)
Changes the login/logoff helper path in the registry
- wscript.exe (PID: 3740)
SUSPICIOUS
Executable content was dropped or overwritten
- Test2.exe (PID: 3548)
- BossDaMajor.exe (PID: 2796)
- wscript.exe (PID: 3576)
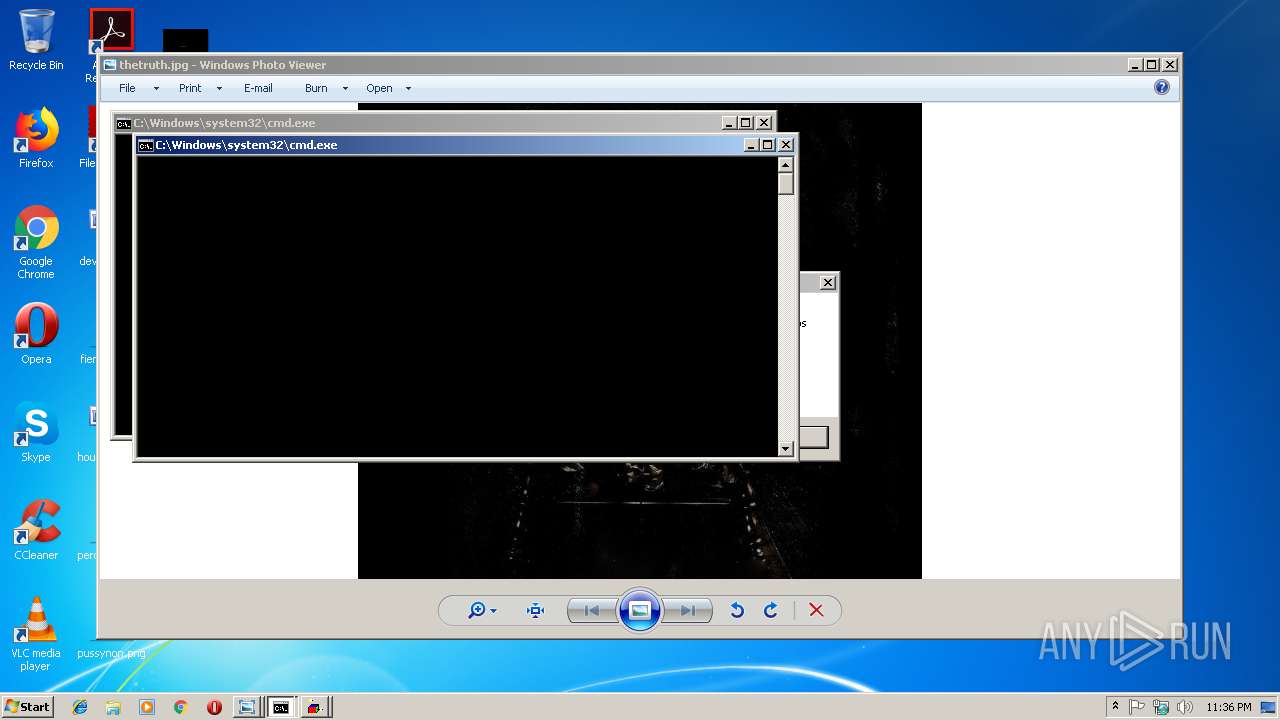
Starts CMD.EXE for commands execution
- WScript.exe (PID: 3464)
- Test2.exe (PID: 3548)
- WScript.exe (PID: 3148)
- WScript.exe (PID: 3956)
- WinScrew.exe (PID: 4092)
- majorlist.exe (PID: 2624)
- wscript.exe (PID: 2492)
- GetReady.exe (PID: 2540)
- majorlist.exe (PID: 2396)
Uses ICACLS.EXE to modify access control list
- cmd.exe (PID: 2740)
- cmd.exe (PID: 3120)
- cmd.exe (PID: 2584)
- cmd.exe (PID: 2268)
Executes scripts
- runner32s.exe (PID: 2200)
- Test2.exe (PID: 3548)
- RuntimeChecker.exe (PID: 3096)
- runner32s.exe (PID: 3080)
- WScript.exe (PID: 1224)
- breakrule.exe (PID: 3792)
- WScript.exe (PID: 3616)
- cmd.exe (PID: 2756)
- Major.exe (PID: 2628)
- majorsod.exe (PID: 3392)
- BossDaMajor.exe (PID: 2796)
- wscript.exe (PID: 3576)
Uses TASKKILL.EXE to kill Browsers
- cmd.exe (PID: 2552)
Application launched itself
- WScript.exe (PID: 3616)
- wscript.exe (PID: 3576)
- WScript.exe (PID: 1224)
Creates files in the program directory
- wscript.exe (PID: 3740)
- wscript.exe (PID: 3576)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2552)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:09:30 20:01:44+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 190976 |
| InitializedDataSize: | 239616 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d549 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Sep-2018 18:01:44 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 30-Sep-2018 18:01:44 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002E924 | 0x0002EA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.69845 |
.rdata | 0x00030000 | 0x00009A8C | 0x00009C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.13014 |
.data | 0x0003A000 | 0x000203A0 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.23545 |
.gfids | 0x0005B000 | 0x000000E8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.09308 |
.rsrc | 0x0005C000 | 0x0000E4E3 | 0x0000E600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.5802 |
.reloc | 0x0006B000 | 0x00001FDC | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.67876 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.10026 | 2216 | UNKNOWN | English - United States | RT_ICON |
3 | 5.25868 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 5.02609 | 1128 | UNKNOWN | English - United States | RT_ICON |
5 | 5.18109 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 5.04307 | 9640 | UNKNOWN | English - United States | RT_ICON |
7 | 3.23498 | 564 | UNKNOWN | German - Germany | RT_STRING |
8 | 3.21532 | 616 | UNKNOWN | German - Germany | RT_STRING |
9 | 3.20126 | 604 | UNKNOWN | German - Germany | RT_STRING |
10 | 3.20175 | 416 | UNKNOWN | German - Germany | RT_STRING |
Imports
KERNEL32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
155
Monitored processes
100
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 560 | takeown /f taskmgr.exe | C:\Windows\System32\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Takes ownership of a file Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1224 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\healgen.vbs" | C:\Windows\System32\WScript.exe | — | Test2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1624 | "C:\Windows\System32\notepad.exe" | C:\Windows\System32\notepad.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2188 | icacls sethc.exe /granted "admin":F | C:\Windows\System32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 5 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2200 | "C:\Users\admin\AppData\Local\Temp\runner32s.exe" | C:\Users\admin\AppData\Local\Temp\runner32s.exe | Test2.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2248 | taskkill /f /im protogent.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2256 | taskkill /f /im chrome.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2264 | "C:\Windows\System32\wscript.exe" "C:\Program Files\MicrosoftWindowsServicesEtc\healgen.vbs" RunAsAdministrator | C:\Windows\System32\wscript.exe | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 1 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2268 | "C:\Windows\system32\cmd.exe" /c "C:\Users\admin\AppData\Local\Temp\1\1EE3.bat C:\Users\admin\AppData\Local\Temp\GetReady.exe" | C:\Windows\system32\cmd.exe | — | GetReady.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2324 | "C:\Users\admin\AppData\Local\Temp\RuntimeChecker.exe" | C:\Users\admin\AppData\Local\Temp\RuntimeChecker.exe | — | Test2.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
3 133
Read events
3 008
Write events
125
Delete events
0
Modification events
| (PID) Process: | (3548) Test2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3548) Test2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3500) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: DllHost.exe | |||
| (PID) Process: | (3548) Test2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {FFE2A43C-56B9-4BF5-9A79-CC6D4285608A} {00000122-0000-0000-C000-000000000046} 0xFFFF |
Value: 010000000000000016E98AF561ACD401 | |||
| (PID) Process: | (3548) Test2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: Test2.exe | |||
| (PID) Process: | (2200) runner32s.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2200) runner32s.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3464) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3464) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3956) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
16
Suspicious files
0
Text files
106
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3548 | Test2.exe | C:\Users\admin\AppData\Local\Temp\xRunReg.vbs | text | |
MD5:8267192F547F8914FF36EFF80CA3F402 | SHA256:CDD4F356CA256C707960BC42B97649111A830E6F951CA6A3CF80853E3C342947 | |||
| 3548 | Test2.exe | C:\Users\admin\AppData\Local\Temp\WinScrew.bat | text | |
MD5:04067CA733EE8B2AB2F068EDC8B75A0F | SHA256:3AEF33C03777ABE62FEEF0A840AC6A087CAAFC05ADFE801464FD1C52EAC656A0 | |||
| 3548 | Test2.exe | C:\Users\admin\AppData\Local\Temp\xRun.vbs | text | |
MD5:26EC8D73E3F6C1E196CC6E3713B9A89F | SHA256:ED588FA361979F7F9C6DBB4E6A1AE6E075F2DB8D79EA6CA2007BA8E3423671B0 | |||
| 3548 | Test2.exe | C:\Users\admin\AppData\Local\Temp\AppKill.bat | text | |
MD5:D4E987817D2E5D6ED2C12633D6F11101 | SHA256:5549670EF8837C6E3C4E496C1EA2063670618249D4151DEA4D07D48AB456690C | |||
| 3548 | Test2.exe | C:\Users\admin\AppData\Local\Temp\BossDaMajor.exe | executable | |
MD5:38FF71C1DEE2A9ADD67F1EDB1A30FF8C | SHA256:730A41A7656F606A22E9F0D68782612D6E00AB8CFE1260160B9E0B00BC2E442A | |||
| 3548 | Test2.exe | C:\Users\admin\AppData\Local\Temp\eula32.exe | executable | |
MD5:— | SHA256:— | |||
| 3548 | Test2.exe | C:\Users\admin\AppData\Local\Temp\breakrule.vbs | text | |
MD5:2609FDE7A9604C73BE5083E4BCFA0E20 | SHA256:17D014CB4ABBACED3ACCE9B6D7A1B595CD6E2DD814E41F06CEDDCDC08E93EEBE | |||
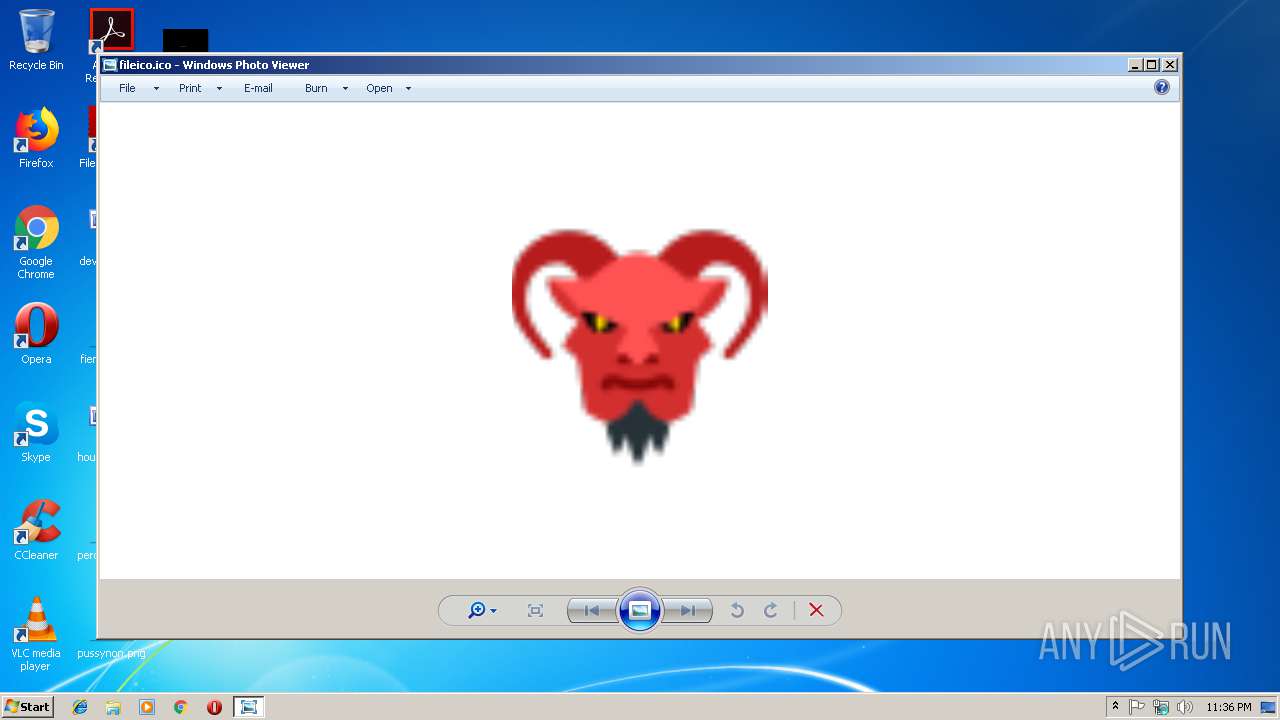
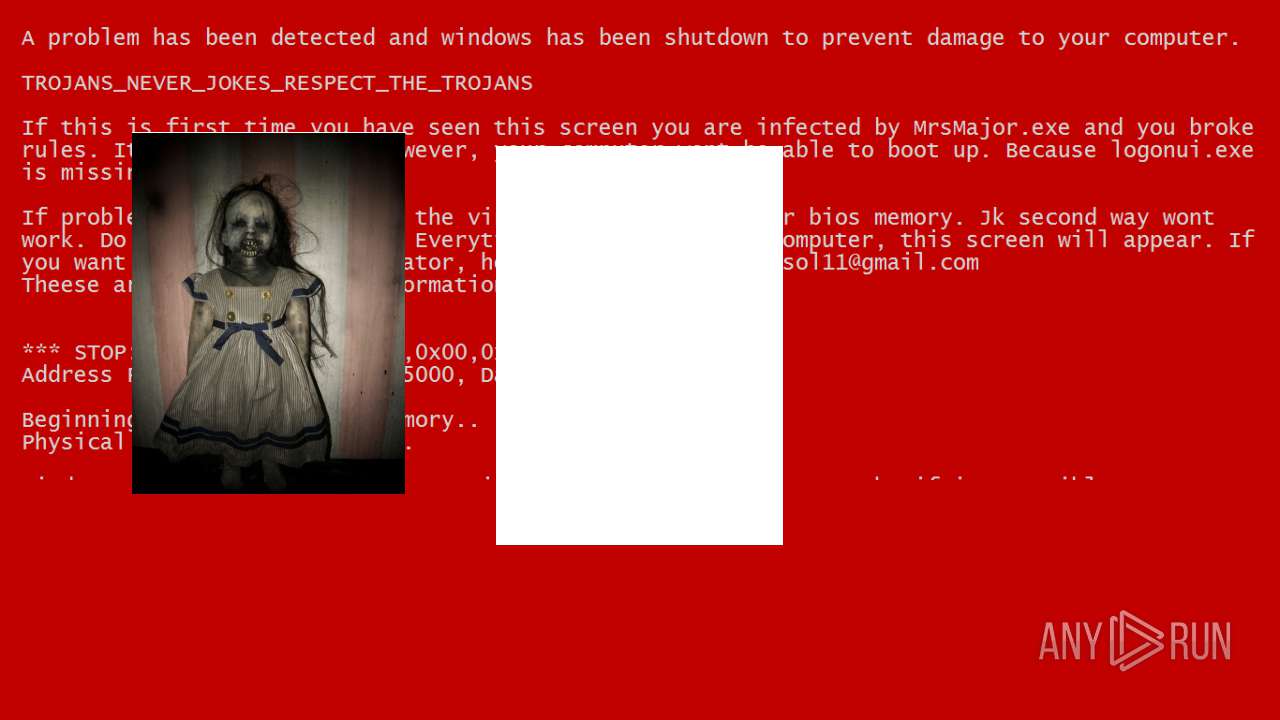
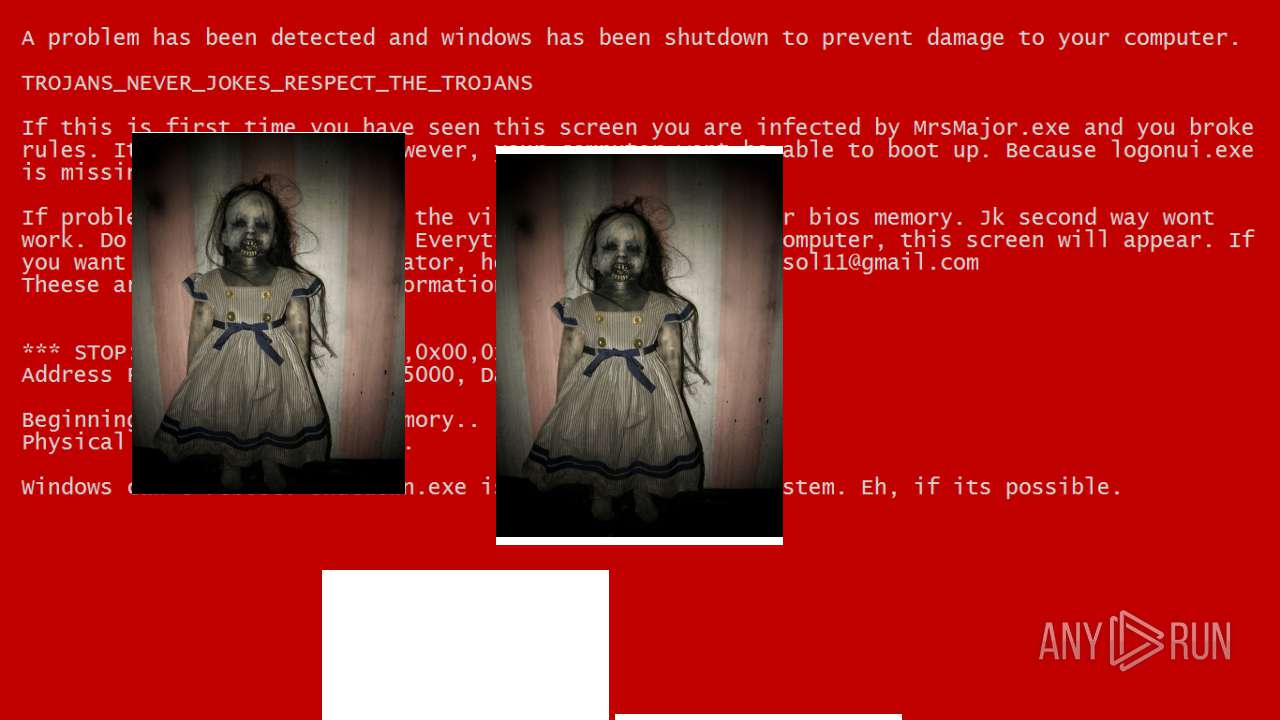
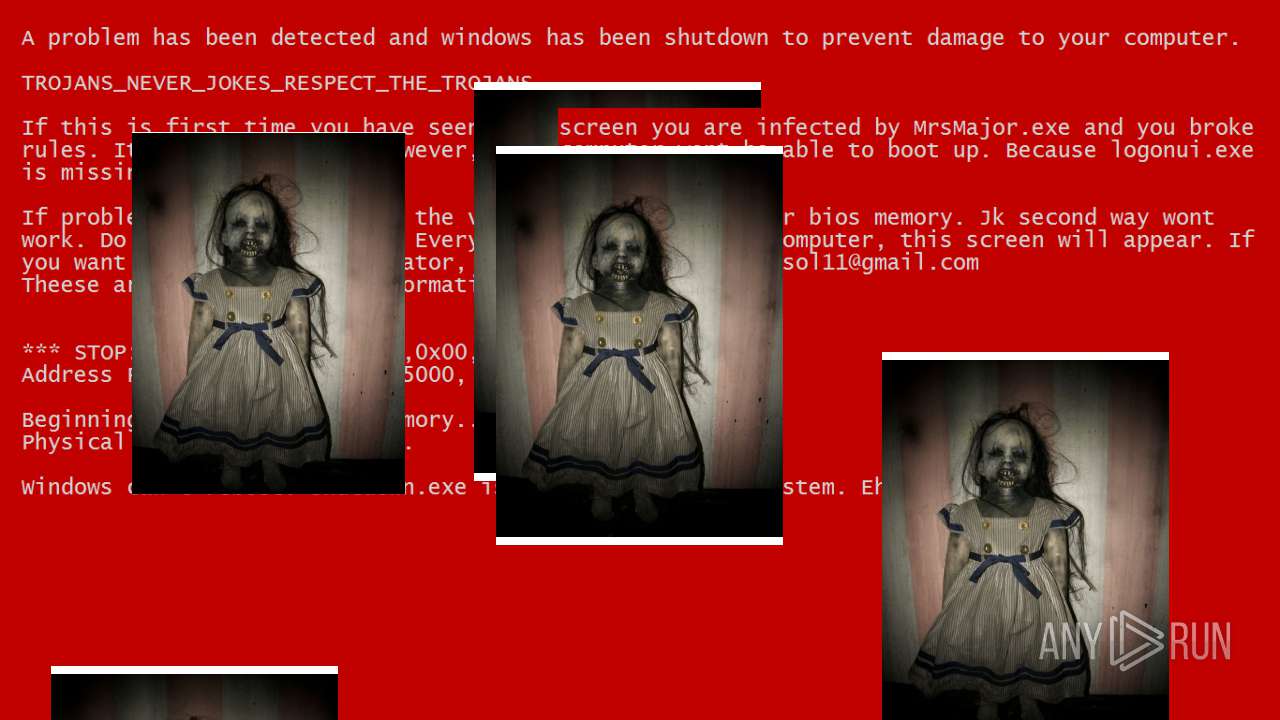
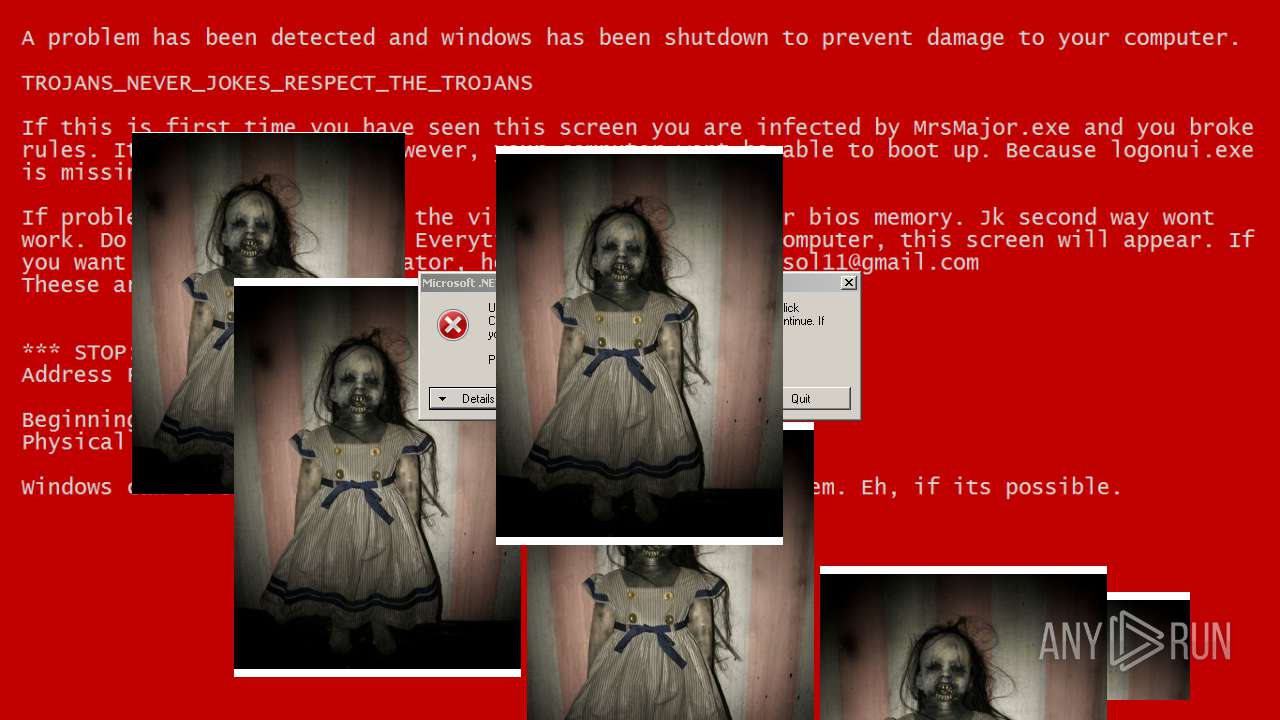
| 3548 | Test2.exe | C:\Users\admin\AppData\Local\Temp\thetruth.jpg | image | |
MD5:7907845316BDBD32200B82944D752D9C | SHA256:4E3BAEA3D98C479951F9EA02E588A3B98B1975055C1DFDF67AF4DE6E7B41E476 | |||
| 3548 | Test2.exe | C:\Users\admin\AppData\Local\Temp\breakrule.exe | executable | |
MD5:BCB0AC4822DE8AEB86EA8A83CD74D7CA | SHA256:5EAFEBD52FBF6D0E8ABD0CC9BF42D36E5B6E4D85B8EBE59F61C9F2D6DCCC65E4 | |||
| 3548 | Test2.exe | C:\Users\admin\AppData\Local\Temp\CallFunc.vbs | text | |
MD5:5F9737F03289963A6D7A71EFAB0813C4 | SHA256:A767894A68EBC490CB5AB2B7B04DD12B7465553CE7BA7E41E1EA45F1EAEF5275 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report