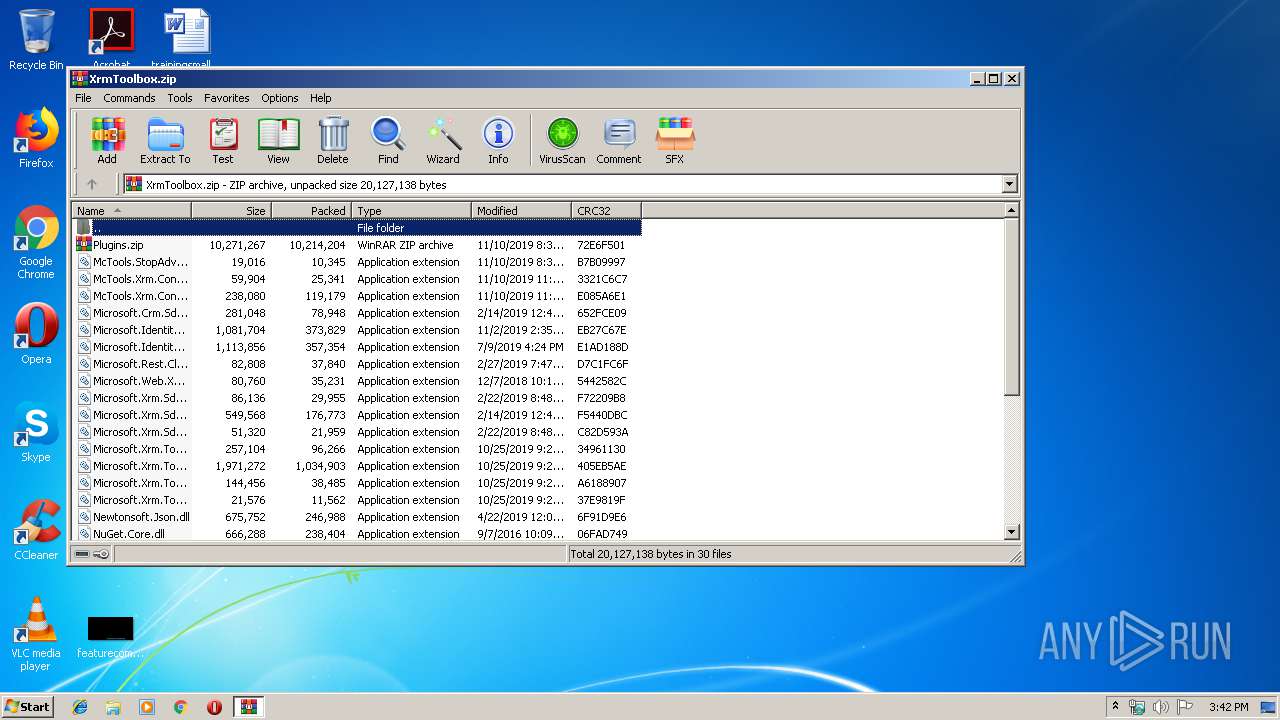
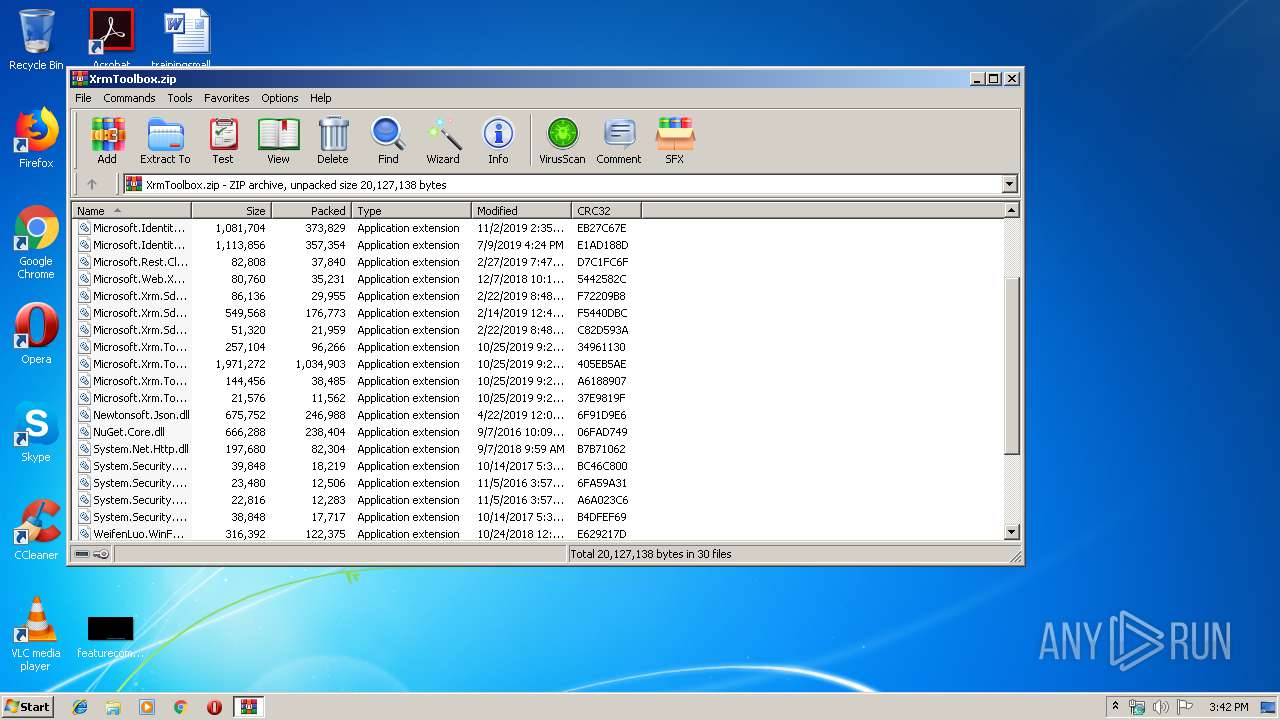
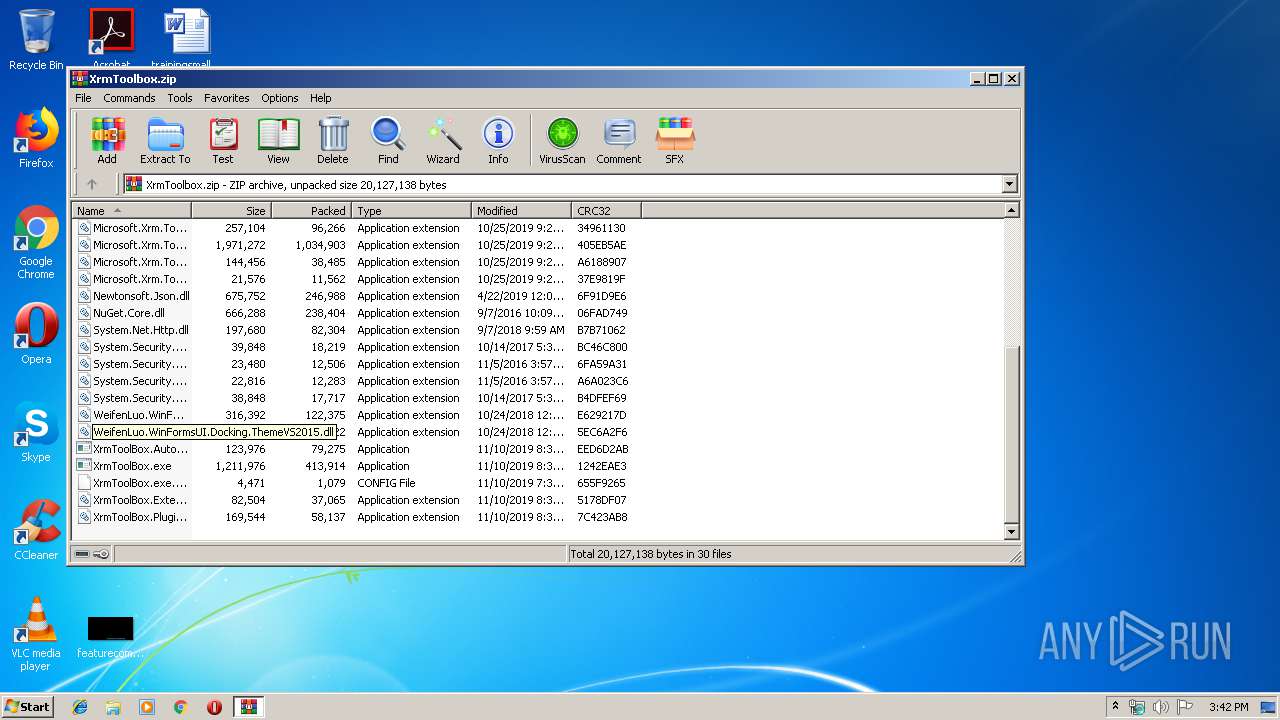
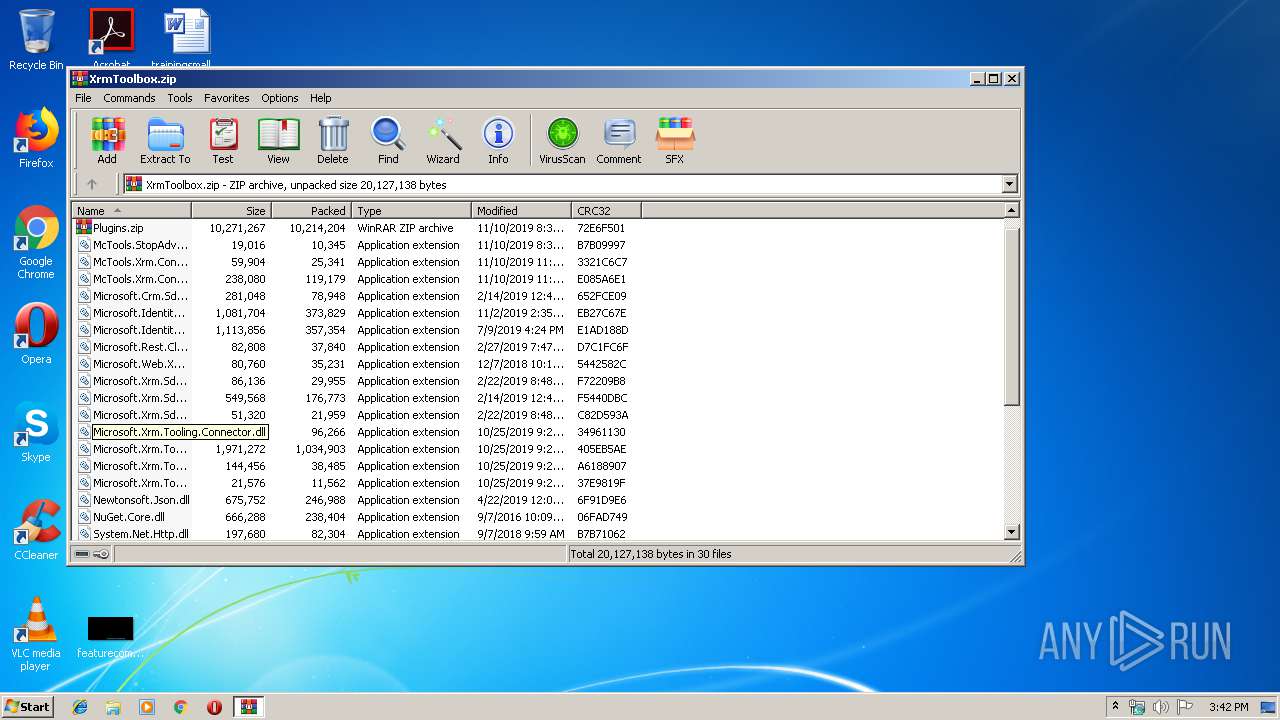
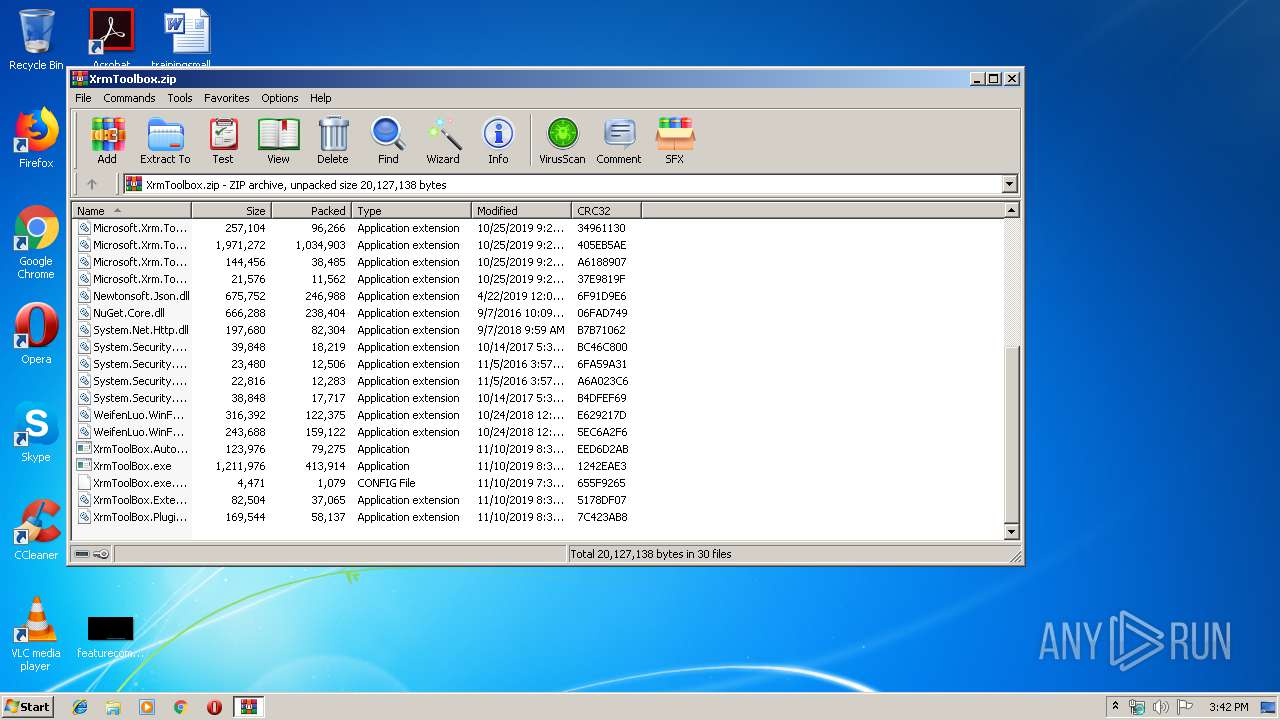
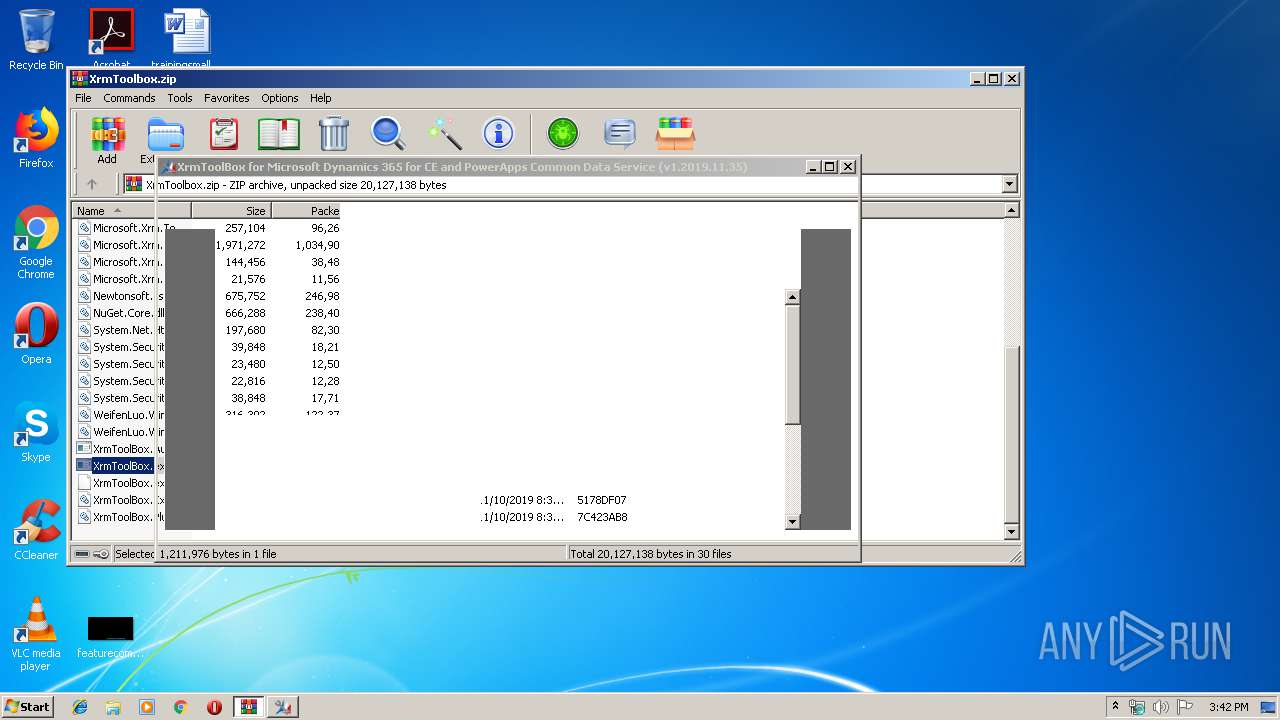
| download: | XrmToolbox.zip |
| Full analysis: | https://app.any.run/tasks/985db970-f3f0-4f5d-9227-7cf50c14150a |
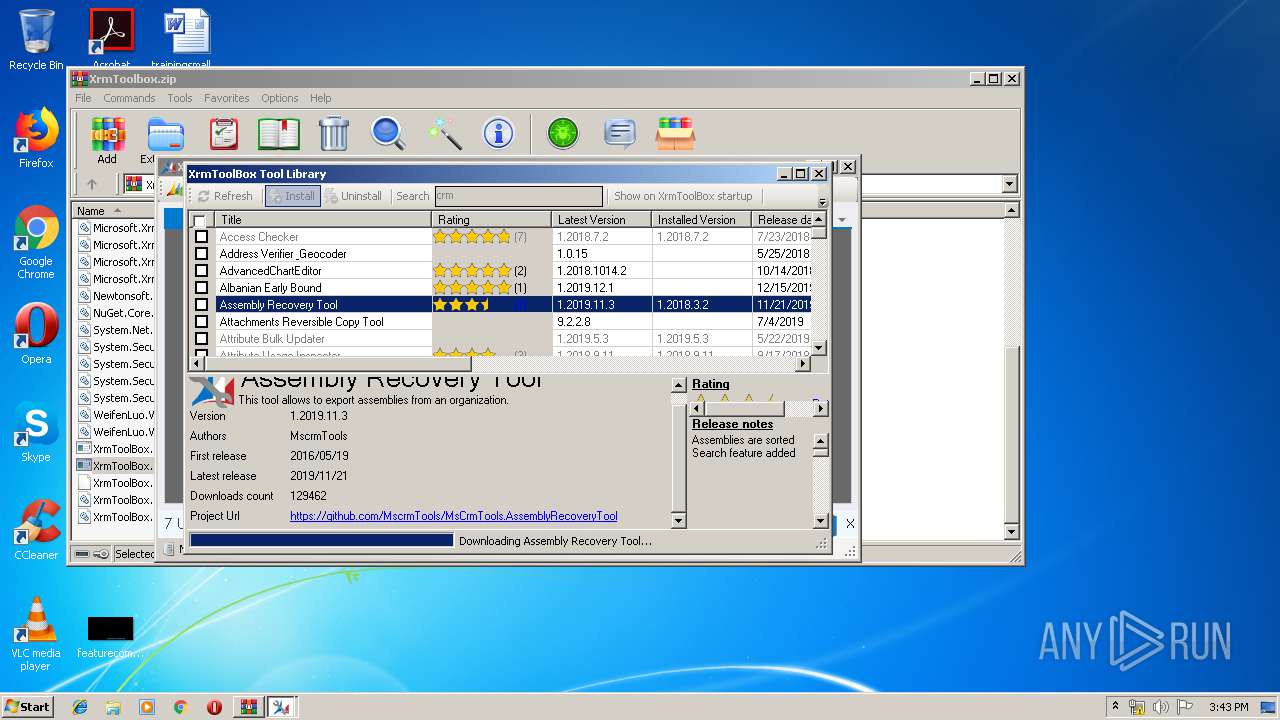
| Verdict: | Malicious activity |
| Analysis date: | January 07, 2020, 15:41:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 179BD4638A55719168786DD22A673FE1 |
| SHA1: | 0008142227F716DB6235CBD1B499021BE1FAE1B5 |
| SHA256: | 3D671772668CF9F53A45932A48D7FFCCA95FC6DB5E2380DDDD7659952DC5B26F |
| SSDEEP: | 393216:IL/umzFCBFhSQHWBXdM/y378snH3zUdL5:Ibu9FhSQHWBNME80XY15 |
MALICIOUS
Loads dropped or rewritten executable
- XrmToolBox.exe (PID: 2144)
Application was dropped or rewritten from another process
- XrmToolBox.exe (PID: 2144)
SUSPICIOUS
Executable content was dropped or overwritten
- XrmToolBox.exe (PID: 2144)
- WinRAR.exe (PID: 2076)
Creates files in the user directory
- XrmToolBox.exe (PID: 2144)
Reads internet explorer settings
- XrmToolBox.exe (PID: 2144)
Creates files in the program directory
- XrmToolBox.exe (PID: 2144)
Reads Environment values
- XrmToolBox.exe (PID: 2144)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:11:10 21:35:23 |
| ZipCRC: | 0xb7b09997 |
| ZipCompressedSize: | 10345 |
| ZipUncompressedSize: | 19016 |
| ZipFileName: | McTools.StopAdvertisement.dll |
Total processes
34
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
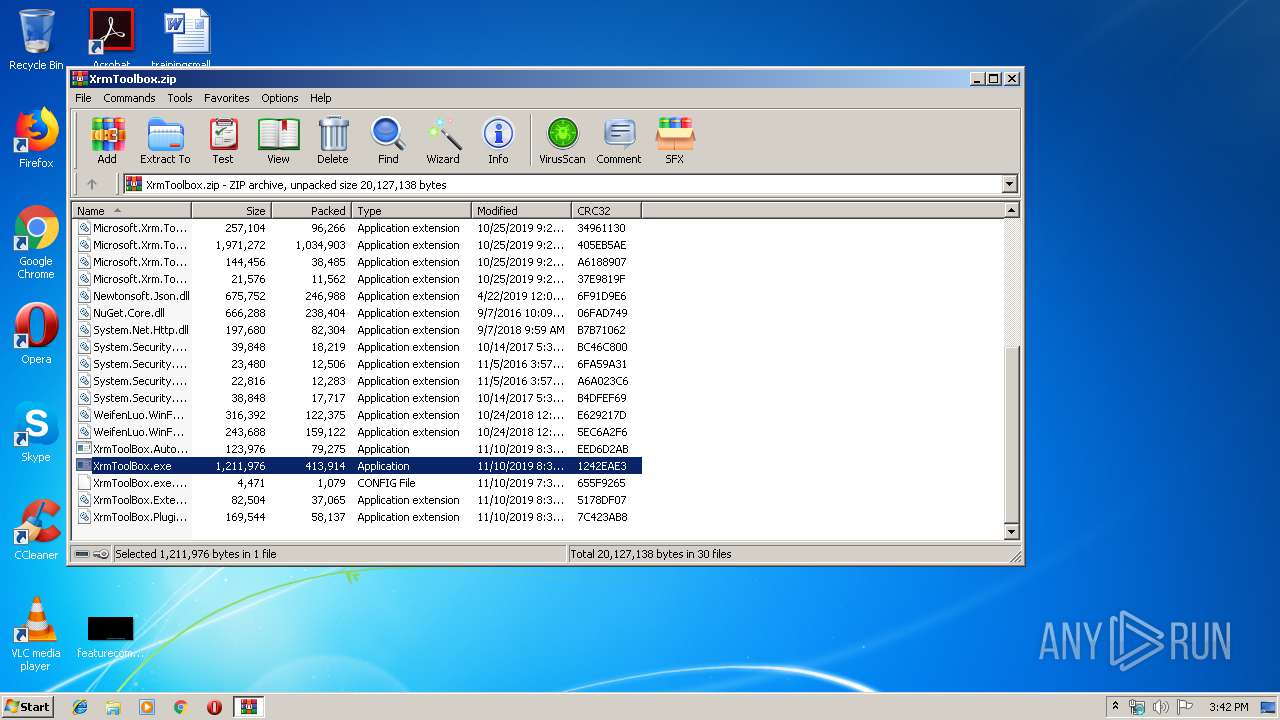
| 2076 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\XrmToolbox.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
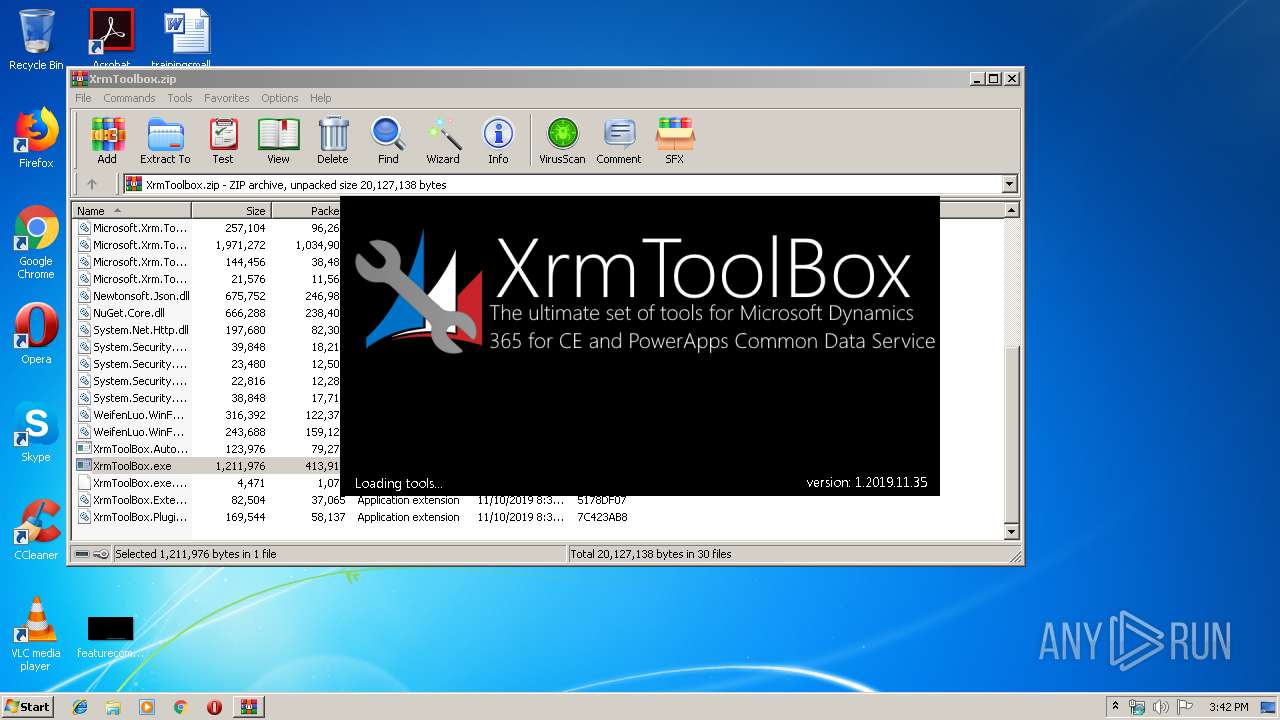
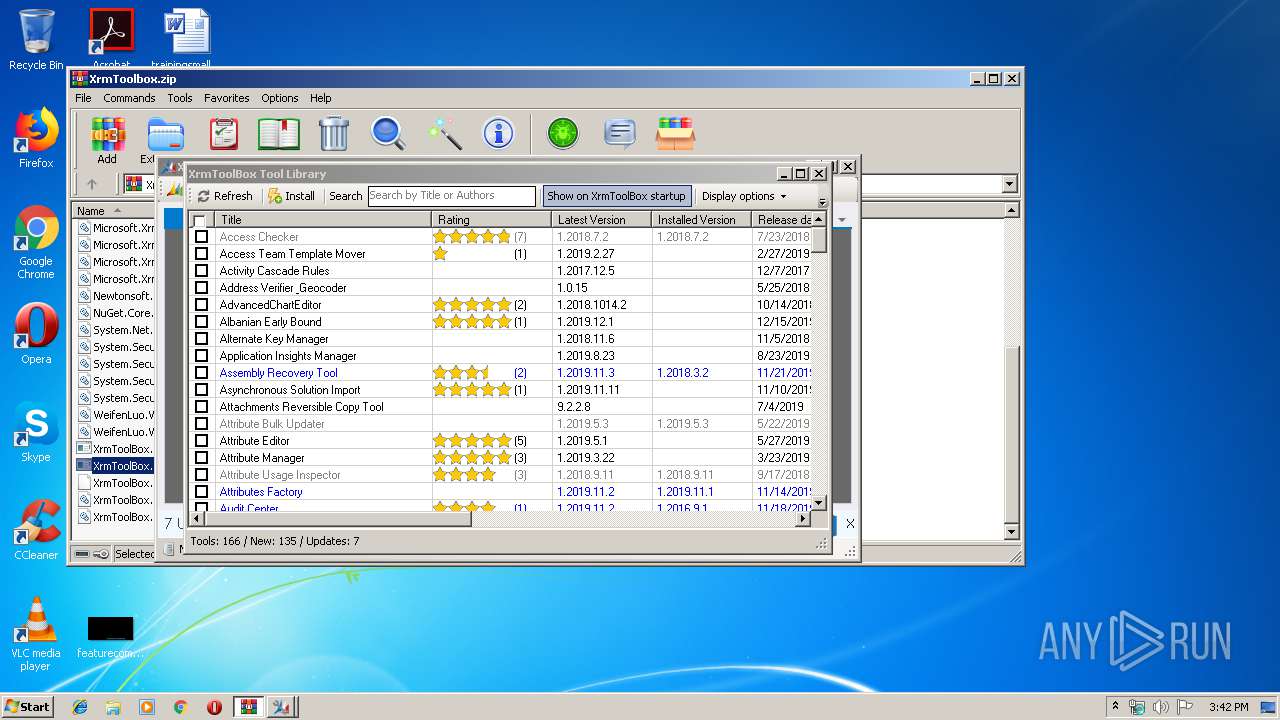
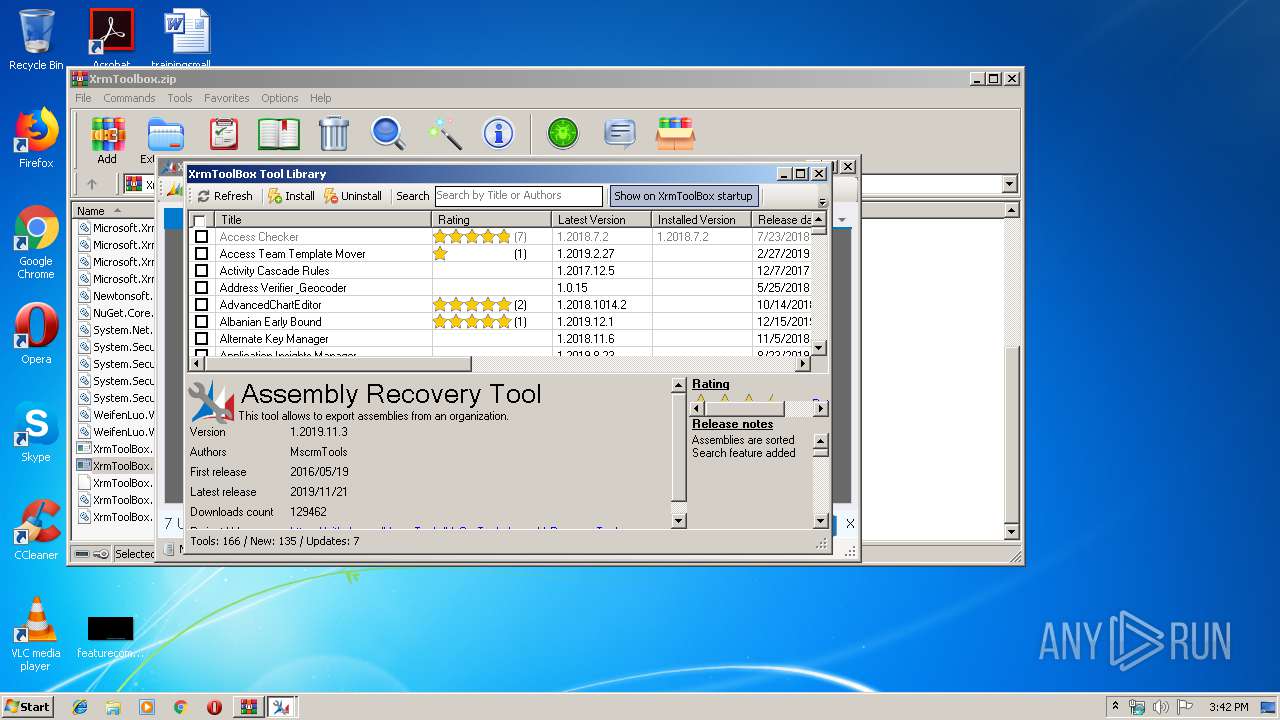
| 2144 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2076.25818\XrmToolBox.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2076.25818\XrmToolBox.exe | WinRAR.exe | ||||||||||||
User: admin Company: MscrmTools Integrity Level: MEDIUM Description: XrmToolBox Exit code: 0 Version: 1.2019.11.35 Modules
| |||||||||||||||
Total events
525
Read events
482
Write events
43
Delete events
0
Modification events
| (PID) Process: | (2076) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2076) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2076) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2076) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\XrmToolbox.zip | |||
| (PID) Process: | (2076) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2076) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2076) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2076) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2076) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2076) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
78
Suspicious files
1
Text files
8
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2076 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2076.25818\McTools.Xrm.Connection.WinForms.dll | executable | |
MD5:— | SHA256:— | |||
| 2076 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2076.25818\Microsoft.Crm.Sdk.Proxy.dll | executable | |
MD5:— | SHA256:— | |||
| 2076 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2076.25818\Microsoft.IdentityModel.Clients.ActiveDirectory.dll | executable | |
MD5:— | SHA256:— | |||
| 2076 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2076.25818\Microsoft.Xrm.Sdk.Deployment.dll | executable | |
MD5:— | SHA256:— | |||
| 2076 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2076.25818\Microsoft.Xrm.Sdk.dll | executable | |
MD5:— | SHA256:— | |||
| 2076 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2076.25818\Microsoft.Xrm.Sdk.Workflow.dll | executable | |
MD5:— | SHA256:— | |||
| 2076 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2076.25818\Microsoft.Xrm.Tooling.WebResourceUtility.dll | executable | |
MD5:— | SHA256:— | |||
| 2076 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2076.25818\Microsoft.Xrm.Tooling.CrmConnectControl.dll | odttf | |
MD5:— | SHA256:— | |||
| 2076 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2076.25818\McTools.StopAdvertisement.dll | executable | |
MD5:— | SHA256:— | |||
| 2076 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2076.25818\McTools.Xrm.Connection.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
9
DNS requests
7
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2144 | XrmToolBox.exe | 13.69.65.22:443 | dc.services.visualstudio.com | Microsoft Corporation | NL | unknown |
2144 | XrmToolBox.exe | 52.178.212.17:443 | www.xrmtoolbox.com | Microsoft Corporation | IE | suspicious |
2144 | XrmToolBox.exe | 151.101.0.133:443 | raw.githubusercontent.com | Fastly | US | malicious |
2144 | XrmToolBox.exe | 192.0.77.2:443 | i0.wp.com | Automattic, Inc | US | suspicious |
2144 | XrmToolBox.exe | 172.217.22.97:443 | 3.bp.blogspot.com | Google Inc. | US | whitelisted |
2144 | XrmToolBox.exe | 152.199.23.209:443 | globalcdn.nuget.org | MCI Communications Services, Inc. d/b/a Verizon Business | US | suspicious |
2144 | XrmToolBox.exe | 52.240.159.111:443 | packages.nuget.org | Microsoft Corporation | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dc.services.visualstudio.com |
| whitelisted |
www.xrmtoolbox.com |
| suspicious |
raw.githubusercontent.com |
| shared |
i0.wp.com |
| whitelisted |
3.bp.blogspot.com |
| whitelisted |
packages.nuget.org |
| unknown |
globalcdn.nuget.org |
| whitelisted |