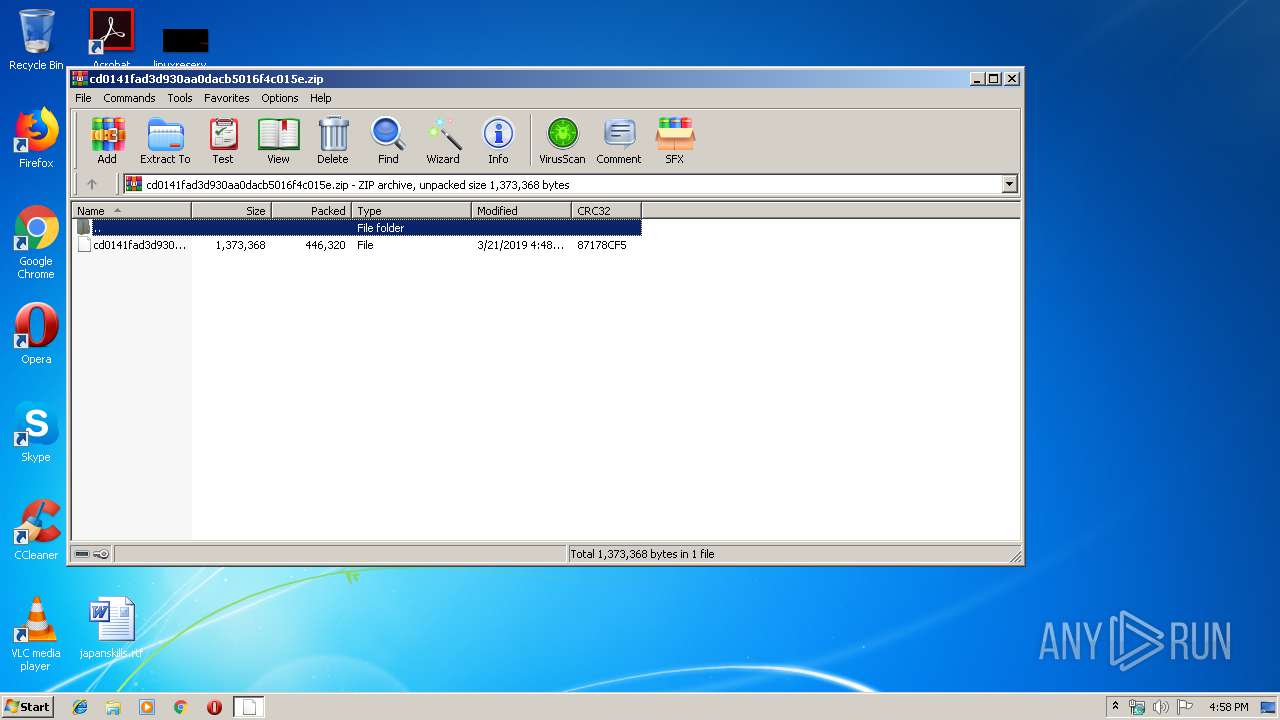
| File name: | cd0141fad3d930aa0dacb5016f4c015e.zip |
| Full analysis: | https://app.any.run/tasks/83691bfa-82f9-45ce-8062-055992d24775 |
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2019, 16:58:06 |
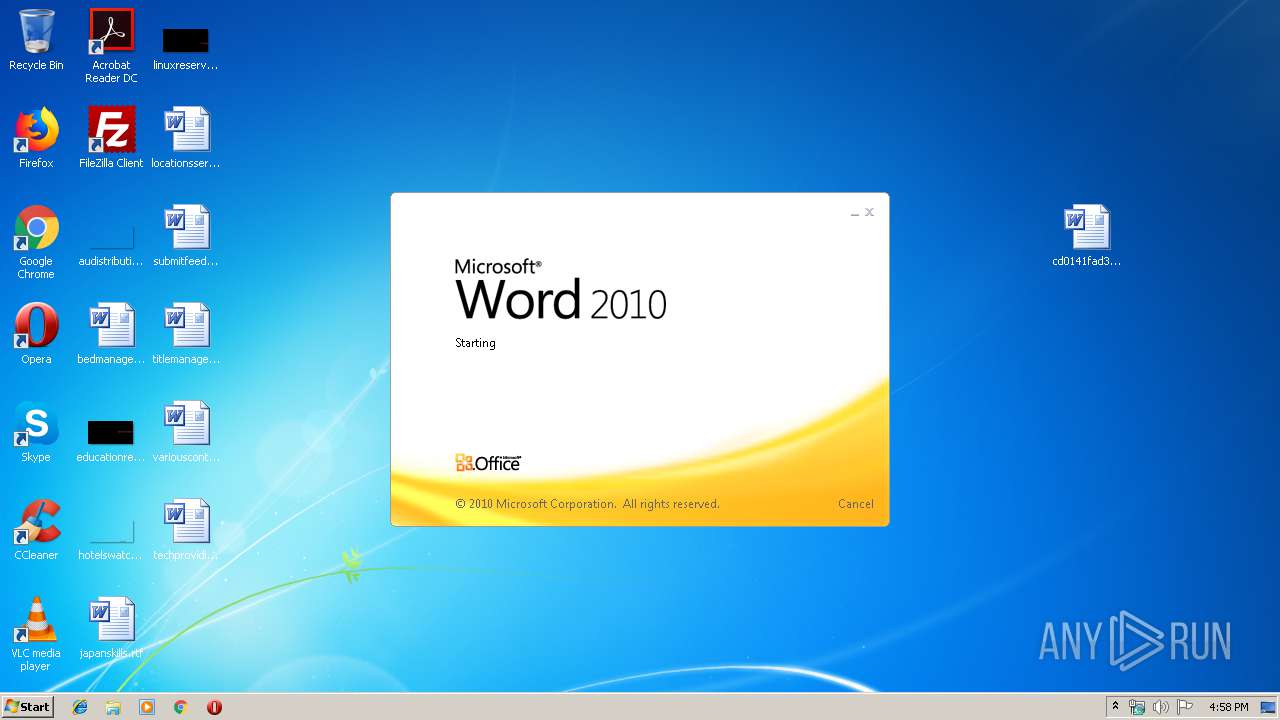
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 292ECA29D908473B746E60FC4F1DEA42 |
| SHA1: | 724708EB49DD51DF2462DA4EE2544E1BF12DC24B |
| SHA256: | 3D614725D31E05C5999F752A2EEF347B372B5C4894891729A73D9835547752A7 |
| SSDEEP: | 6144:hc+8lPUcgf82eg9x1WDwaobeBkTYrEtdj7R10RRZP5Xo+9H7tIbaZUdx5sNkU9Tm:1gp21ewab8hjoDP5Xok7tyaONM9RikP8 |
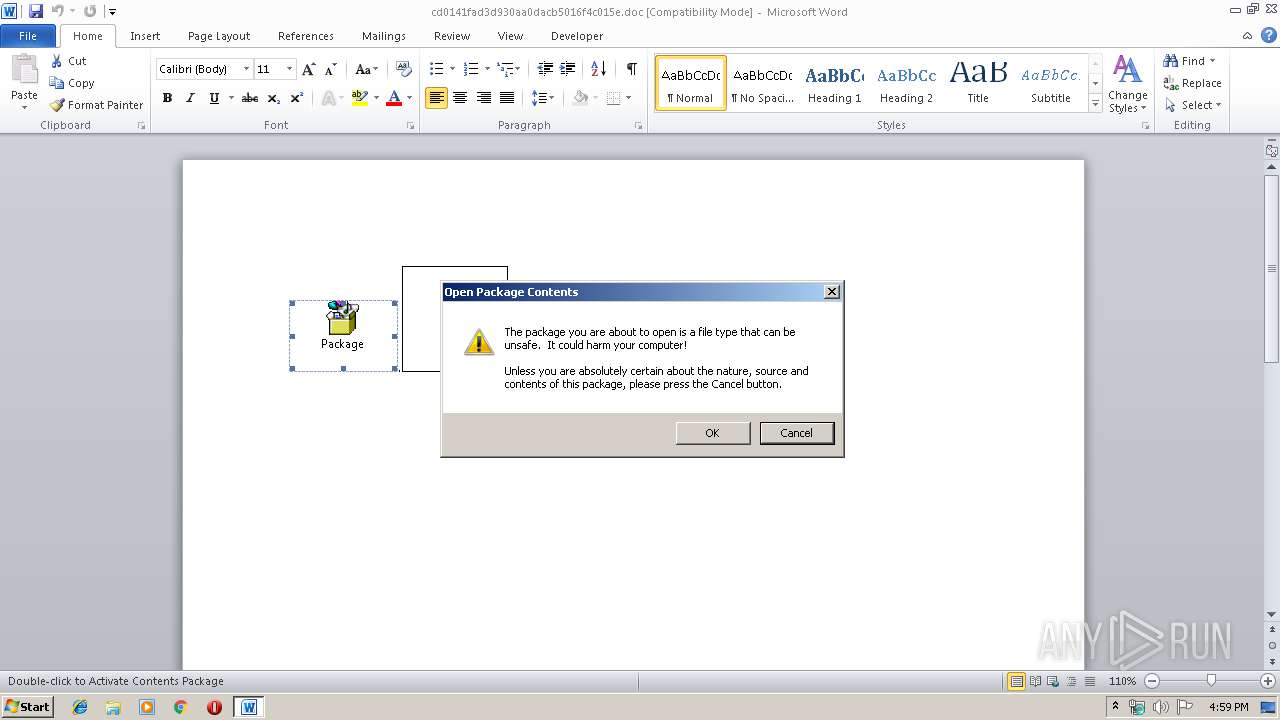
MALICIOUS
Suspicious connection from the Equation Editor
- EQNEDT32.EXE (PID: 2376)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 2876)
- cmd.exe (PID: 2280)
- cmd.exe (PID: 2260)
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 2376)
Application was dropped or rewritten from another process
- ~AFER125419.tmp (PID: 3204)
- ~AFER125419.tmp (PID: 3048)
- ~AFER125419.tmp (PID: 2340)
- ~AFER125419.tmp (PID: 3840)
- ~AFER125419.tmp (PID: 3328)
- ~AFER125419.tmp (PID: 1480)
Writes to a start menu file
- cmd.exe (PID: 2972)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2884)
SUSPICIOUS
Reads internet explorer settings
- EQNEDT32.EXE (PID: 2376)
Creates files in the user directory
- cmd.exe (PID: 2972)
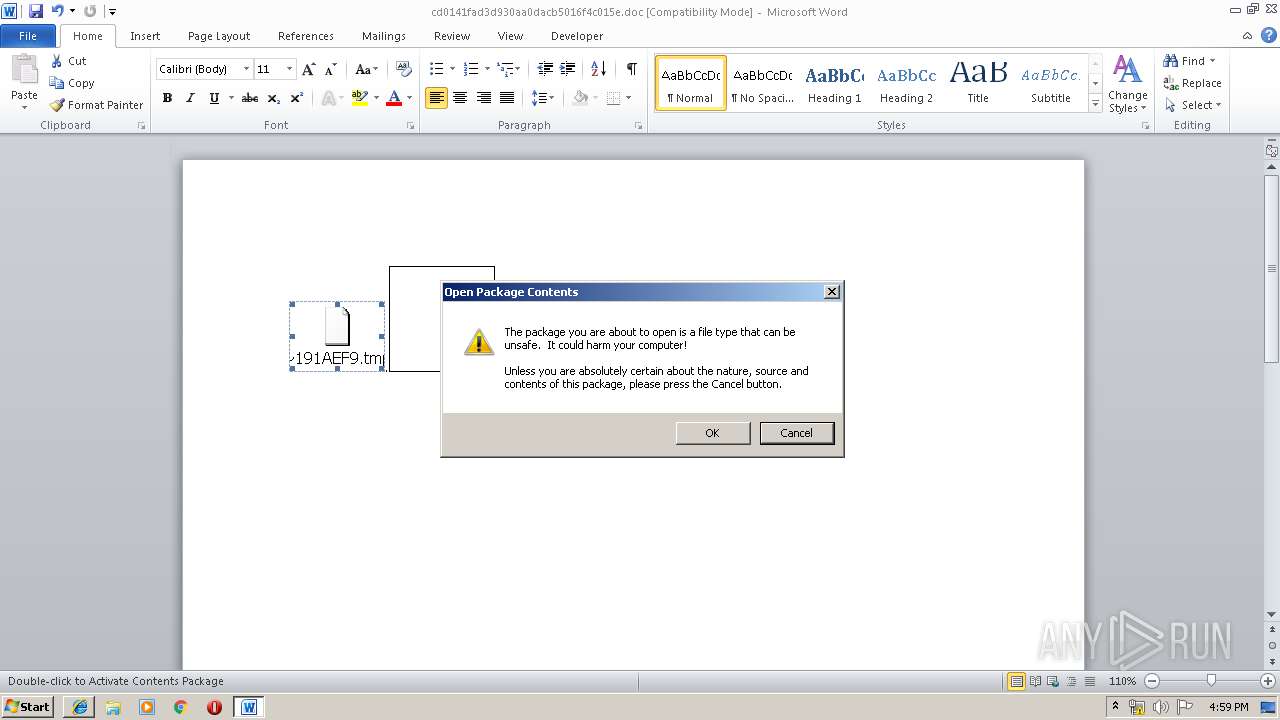
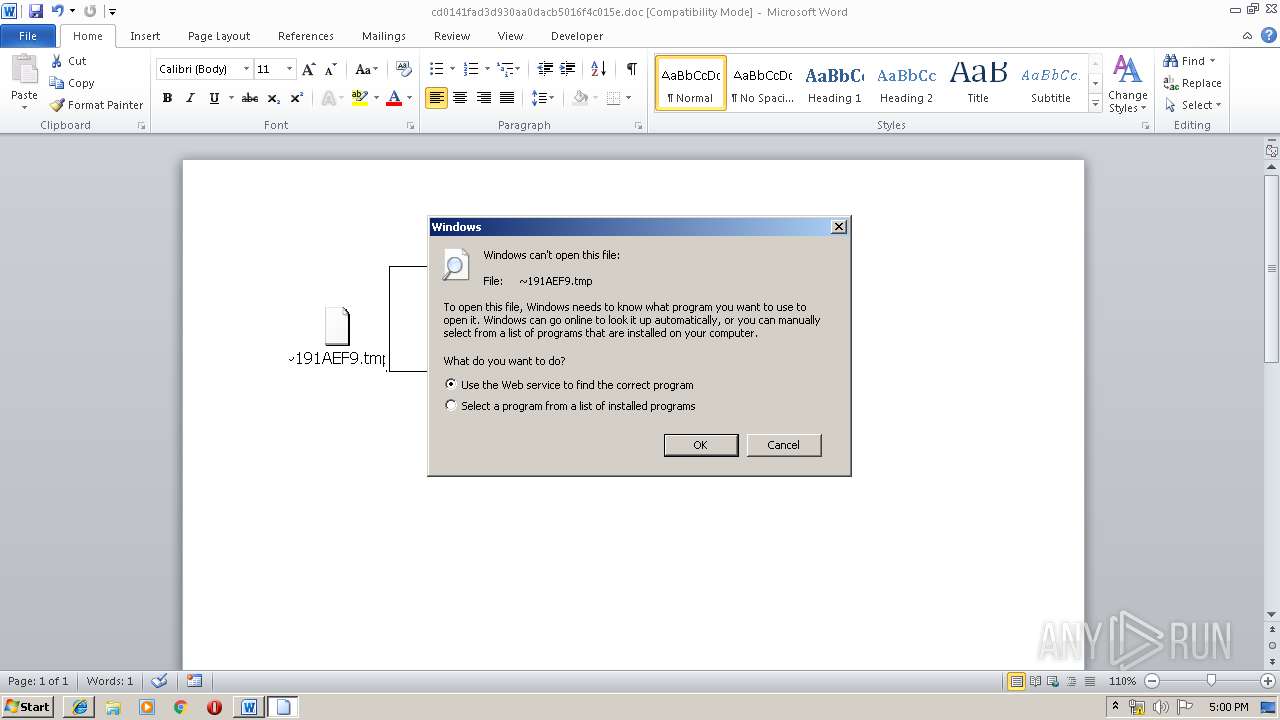
Starts application with an unusual extension
- cmd.exe (PID: 1812)
- ~AFER125419.tmp (PID: 3204)
Executable content was dropped or overwritten
- cmd.exe (PID: 1560)
- cmd.exe (PID: 2972)
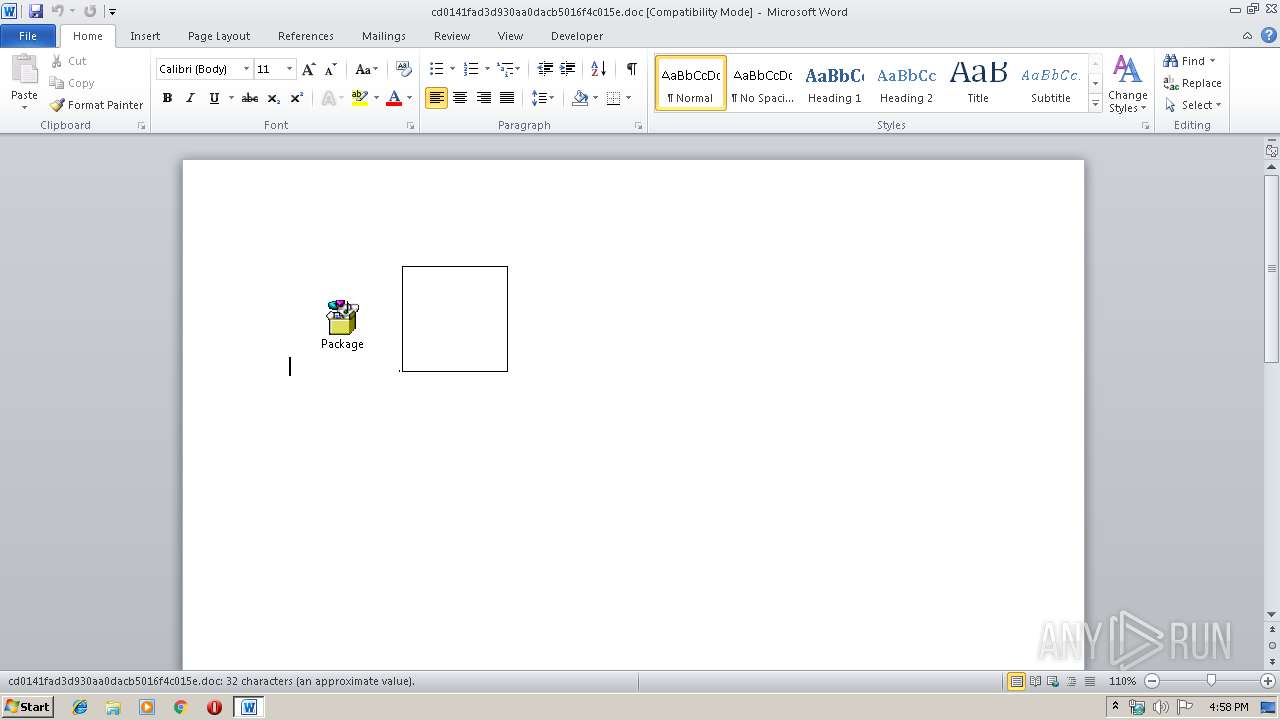
Uses RUNDLL32.EXE to load library
- WINWORD.EXE (PID: 2884)
- iexplore.exe (PID: 2196)
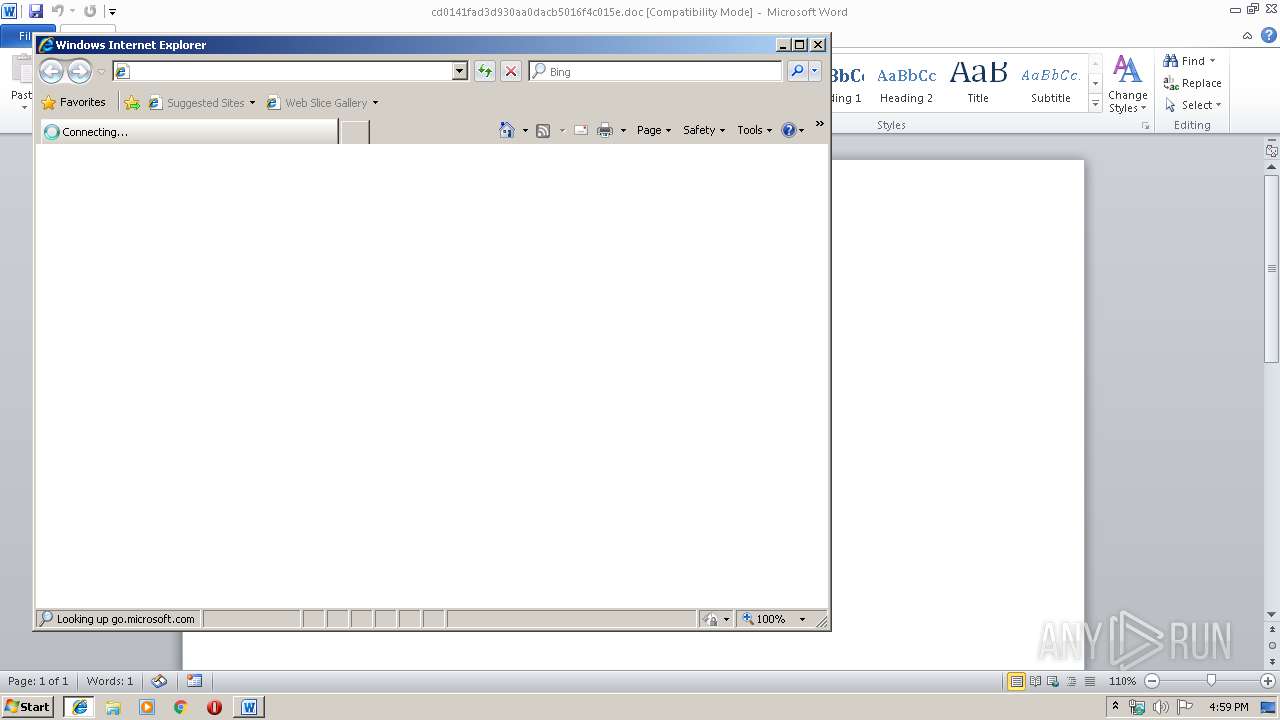
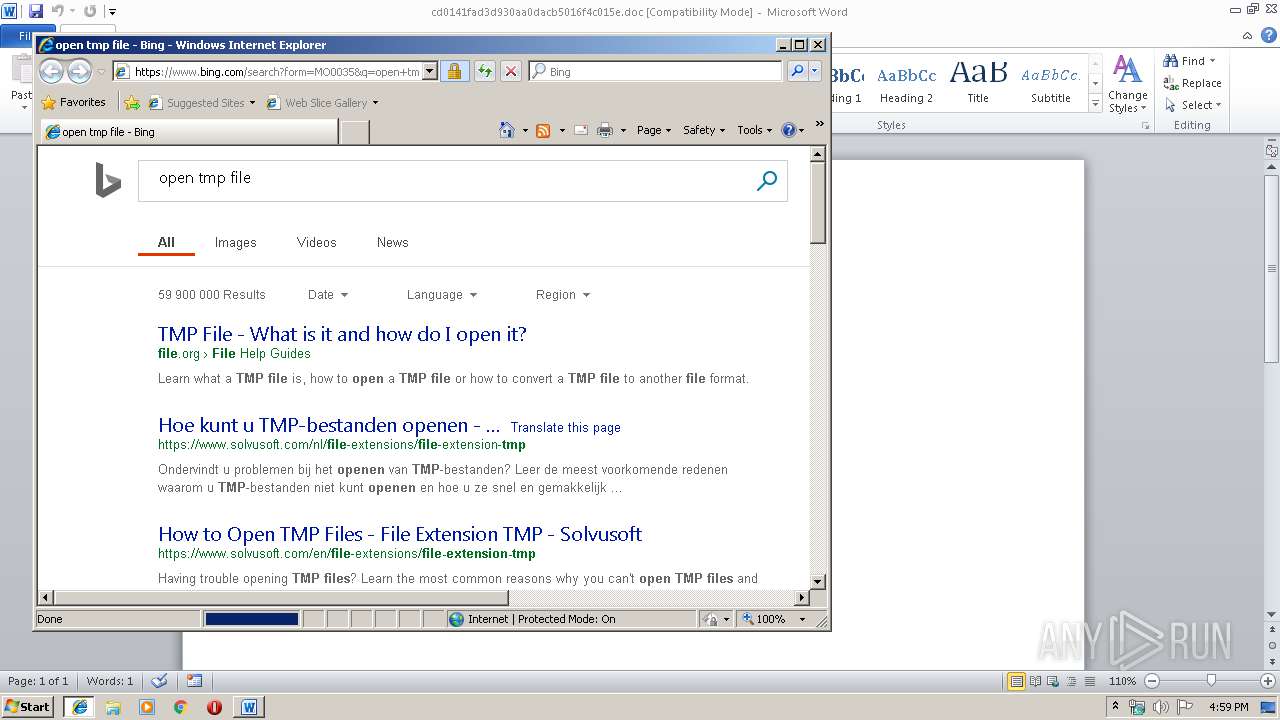
Starts Internet Explorer
- rundll32.exe (PID: 3516)
- rundll32.exe (PID: 2132)
Application launched itself
- ~AFER125419.tmp (PID: 3204)
Reads Internet Cache Settings
- WINWORD.EXE (PID: 2884)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3484)
- EQNEDT32.EXE (PID: 2376)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2884)
Creates files in the user directory
- WINWORD.EXE (PID: 2884)
- iexplore.exe (PID: 4028)
Changes internet zones settings
- iexplore.exe (PID: 3636)
- iexplore.exe (PID: 3980)
Reads Internet Cache Settings
- iexplore.exe (PID: 4028)
- iexplore.exe (PID: 3064)
Reads internet explorer settings
- iexplore.exe (PID: 4028)
Reads settings of System Certificates
- iexplore.exe (PID: 3636)
Changes settings of System certificates
- iexplore.exe (PID: 3636)
Application was crashed
- WINWORD.EXE (PID: 2884)
Application launched itself
- iexplore.exe (PID: 3980)
- iexplore.exe (PID: 3636)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3636)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:03:21 12:48:19 |
| ZipCRC: | 0x87178cf5 |
| ZipCompressedSize: | 446320 |
| ZipUncompressedSize: | 1373368 |
| ZipFileName: | cd0141fad3d930aa0dacb5016f4c015e |
Total processes
76
Monitored processes
30
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | ping localhost -n 2 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 948 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | — | svchost.exe | |||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
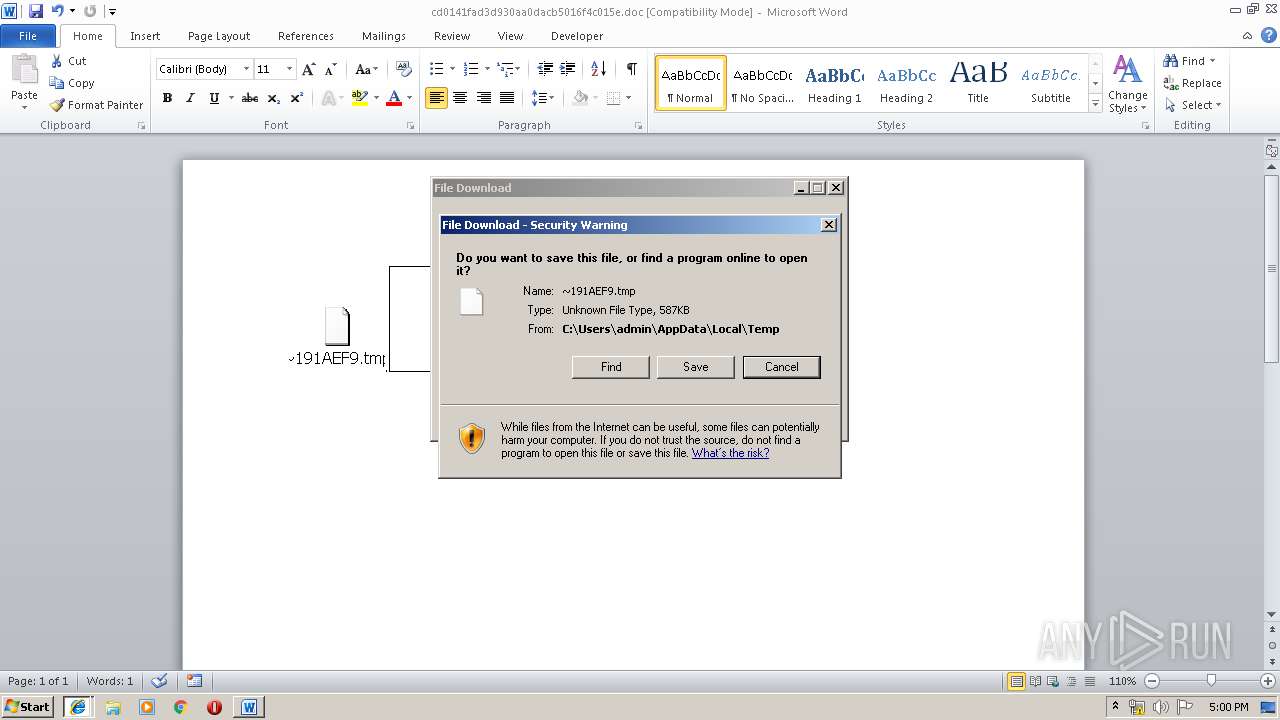
| 1472 | C:\Windows\system32\cmd.exe /S /D /c" set /p "=MZ" 1>C:\Users\admin\AppData\Local\Temp\~F9.TMP" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1480 | "C:\Users\admin\AppData\Local\Temp\~AFER125419.tmp" | C:\Users\admin\AppData\Local\Temp\~AFER125419.tmp | — | ~AFER125419.tmp | |||||||||||
User: admin Integrity Level: MEDIUM Description: retries Exit code: 3221225758 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1560 | cmd /c copy /B %temp%\~F9.tmp+%temp%\~191AEF9.tmp %temp%\~AFER125419.tmp | C:\Windows\system32\cmd.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1812 | cmd /c %temp%\~AFER125419.tmp | C:\Windows\system32\cmd.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
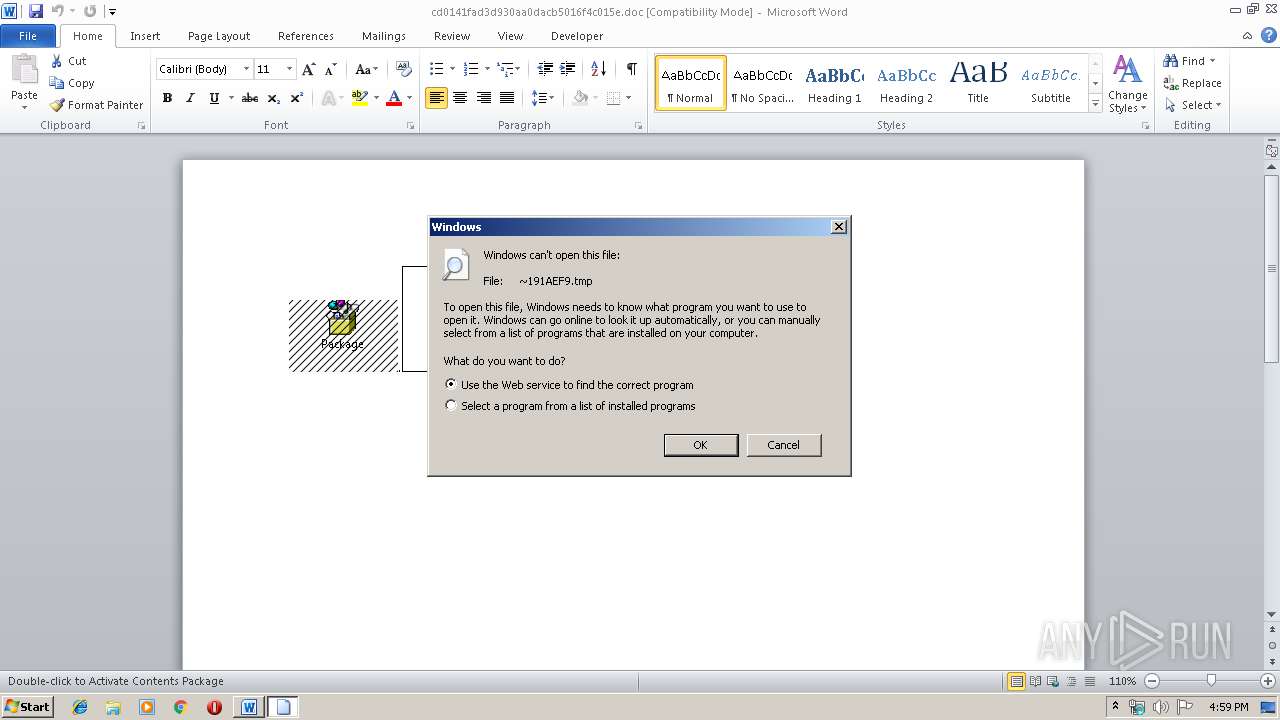
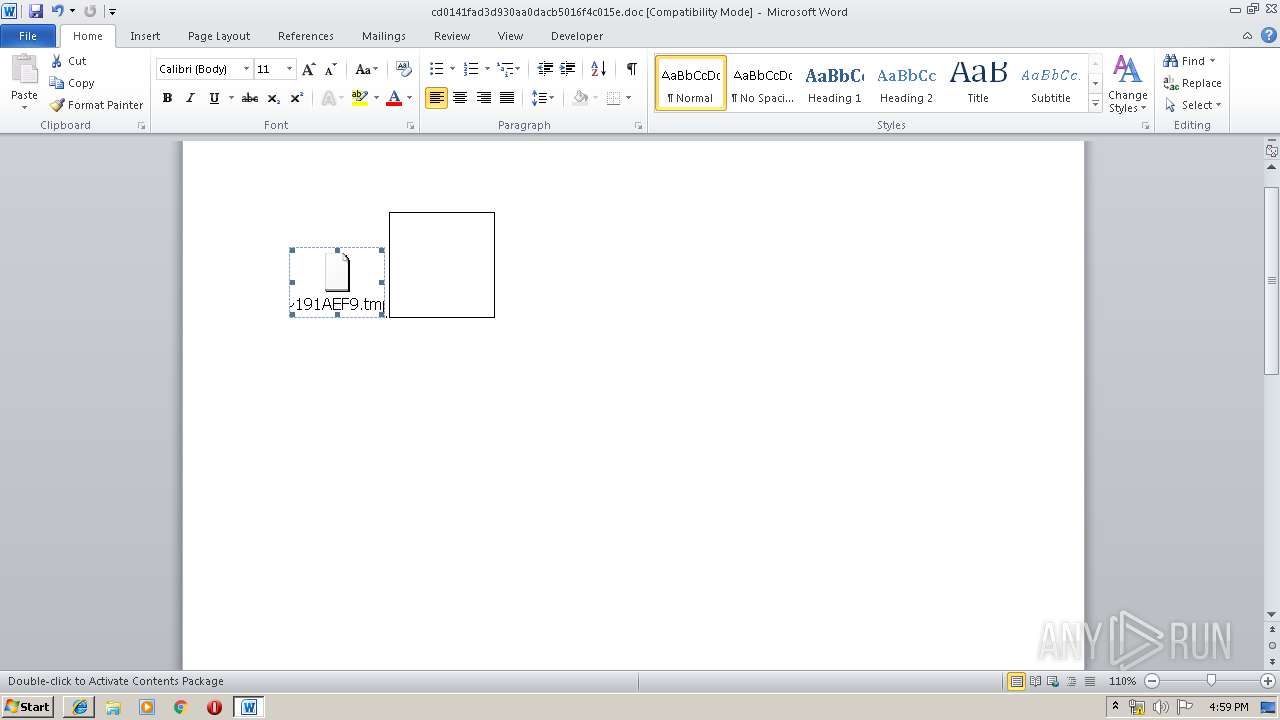
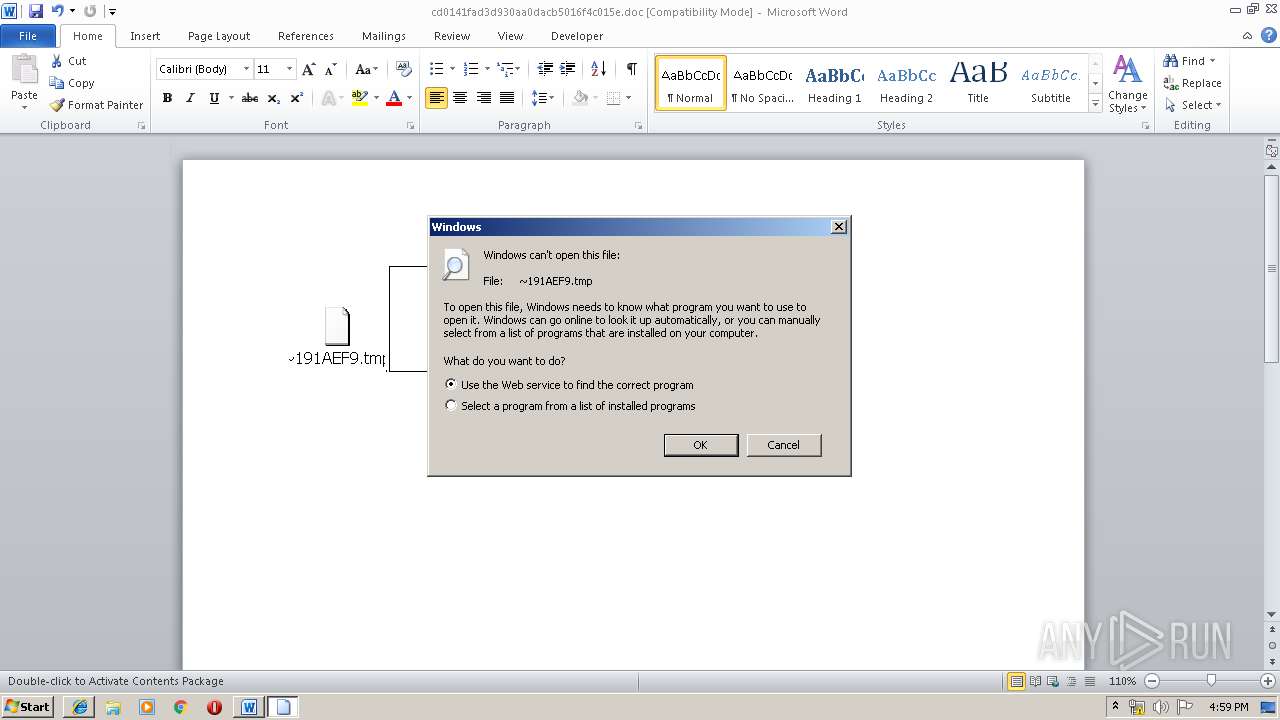
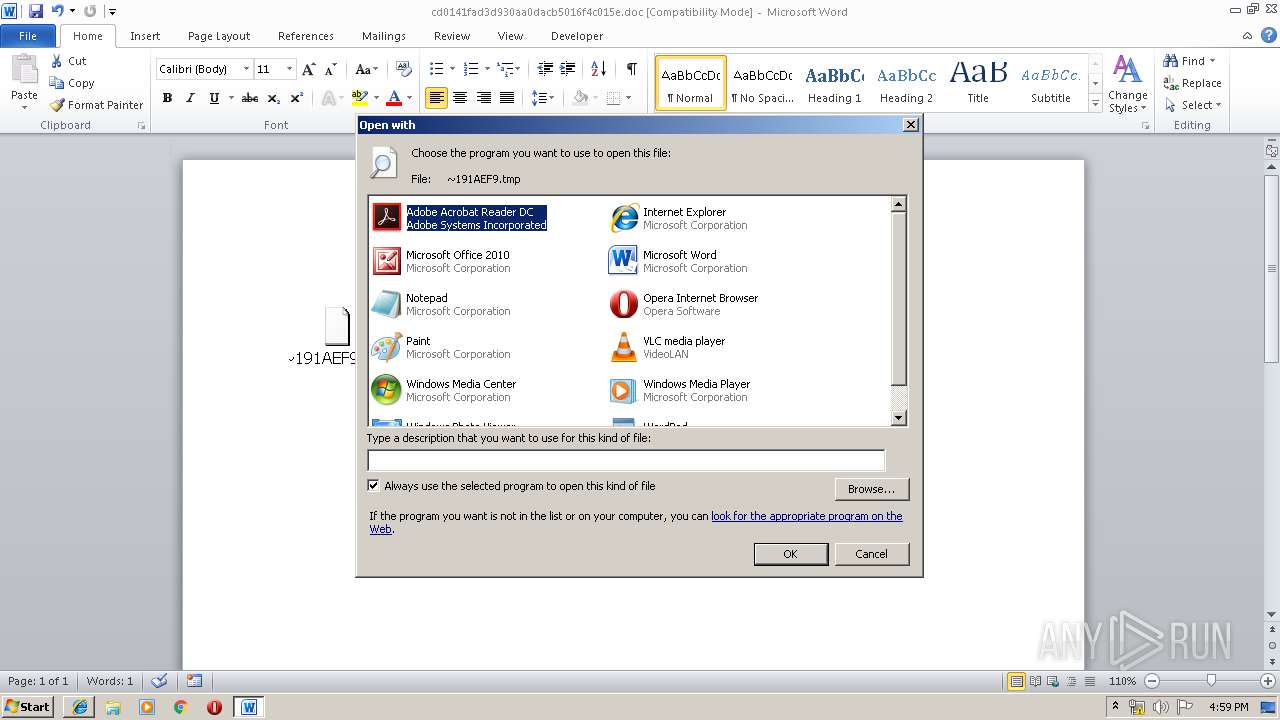
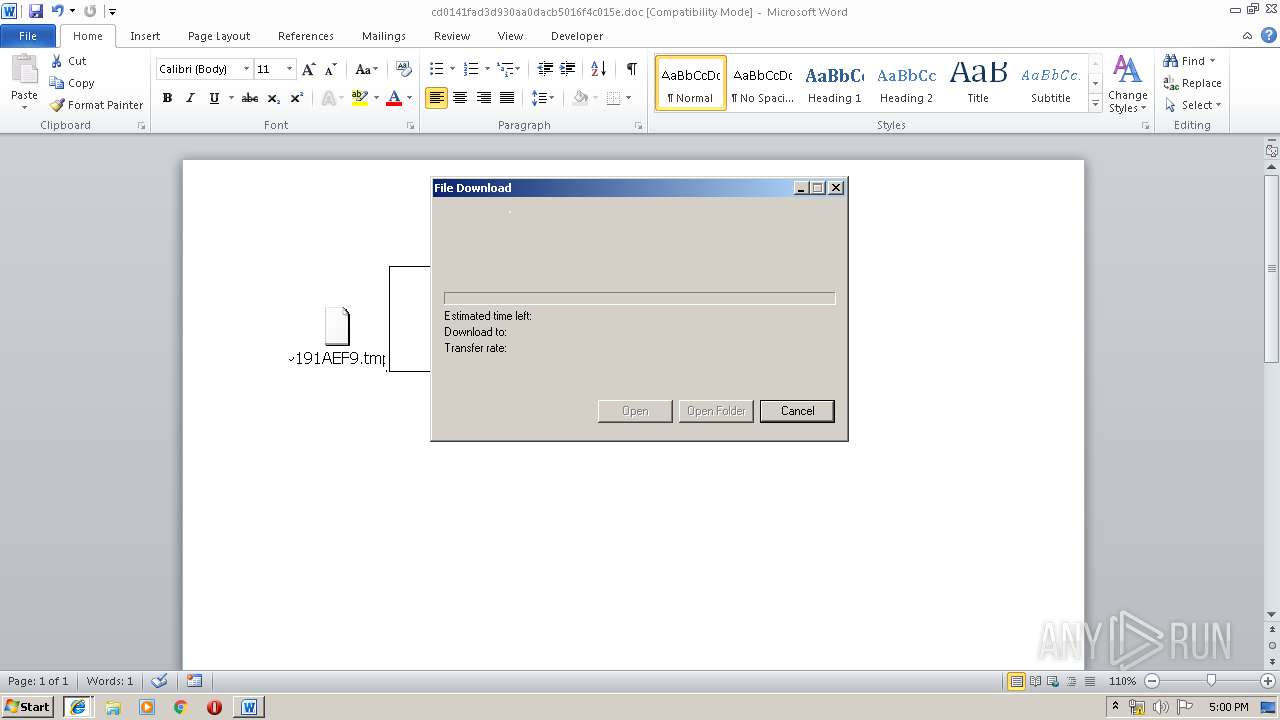
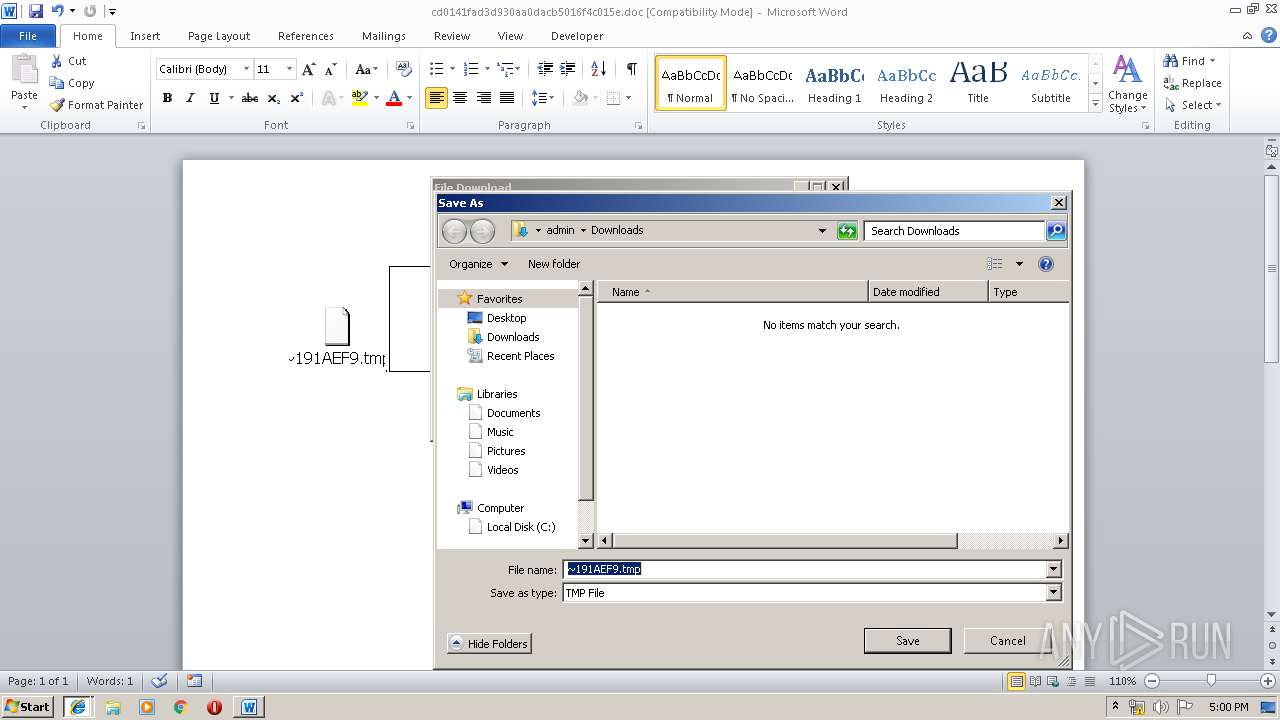
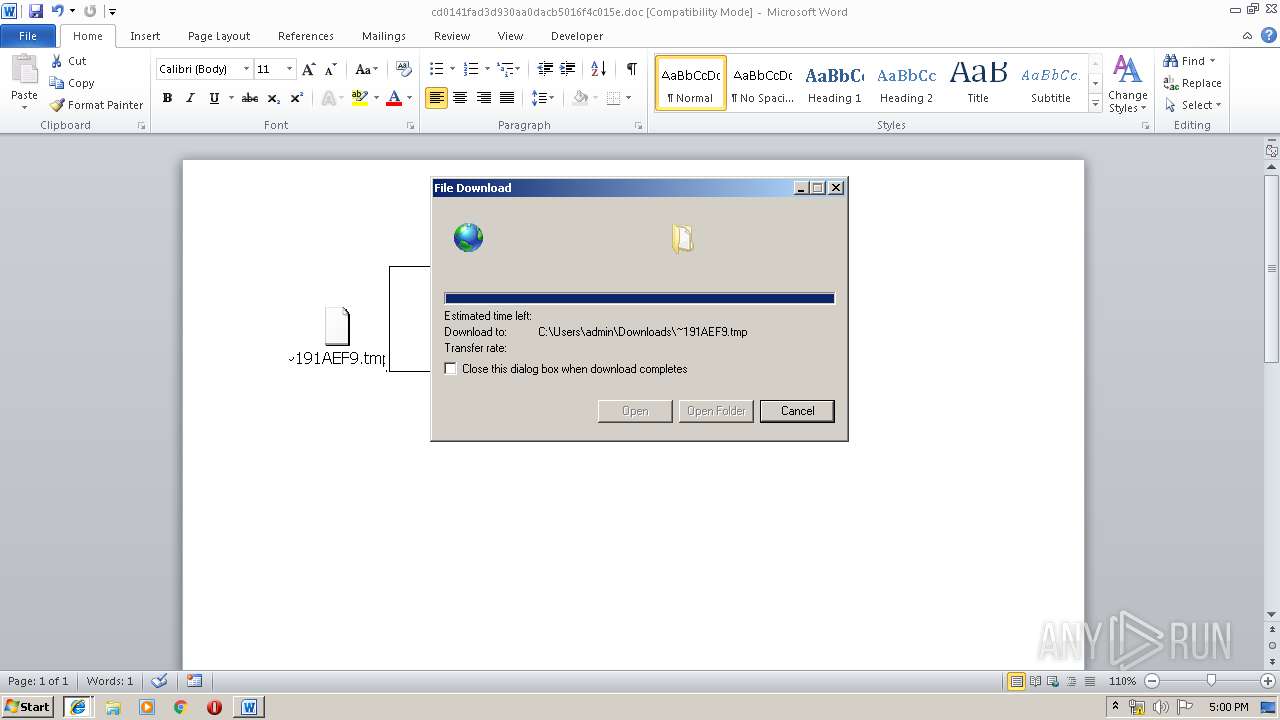
| 2132 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\~191AEF9.tmp | C:\Windows\system32\rundll32.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2176 | ping localhost -n 2 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2196 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3980 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2260 | "C:\Windows\System32\cmd.exe" /c ping localhost -n 2 | C:\Windows\System32\cmd.exe | — | EQNEDT32.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
3 687
Read events
3 013
Write events
661
Delete events
13
Modification events
| (PID) Process: | (3340) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3340) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3340) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3340) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\cd0141fad3d930aa0dacb5016f4c015e.zip | |||
| (PID) Process: | (3340) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3340) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3340) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3340) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
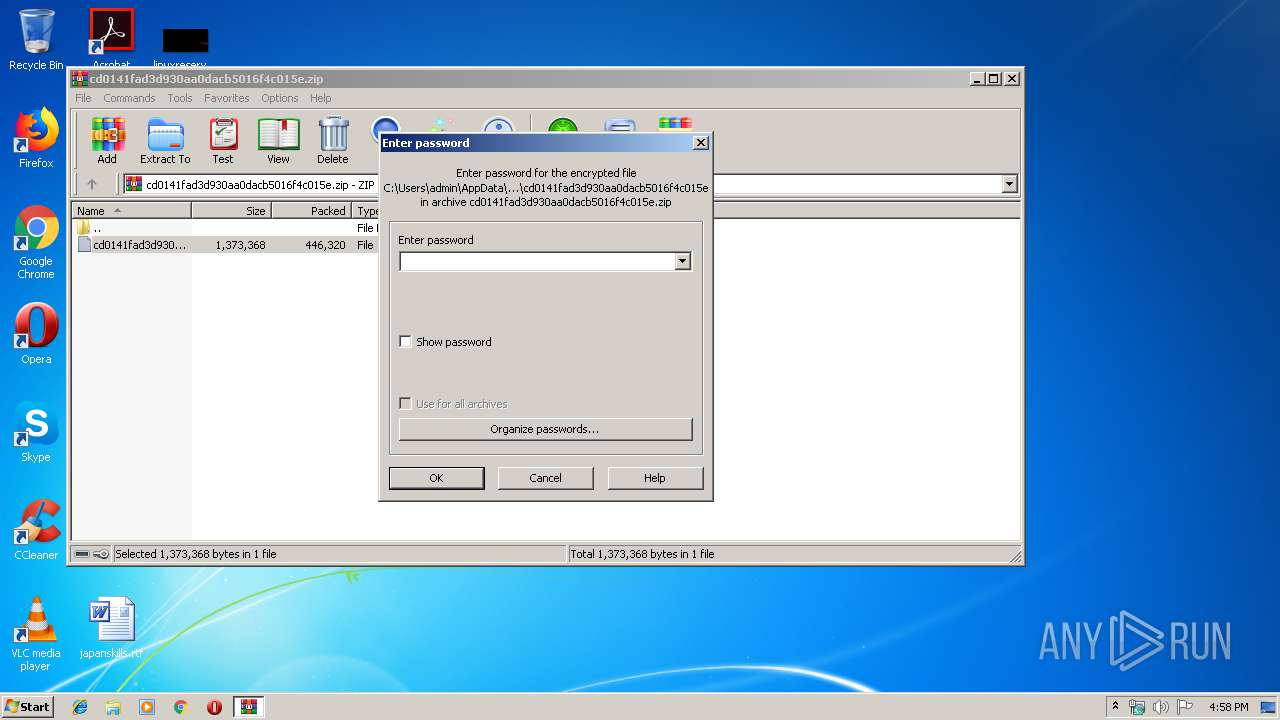
| (PID) Process: | (3340) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3340) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
2
Suspicious files
1
Text files
34
Unknown types
12
Dropped files
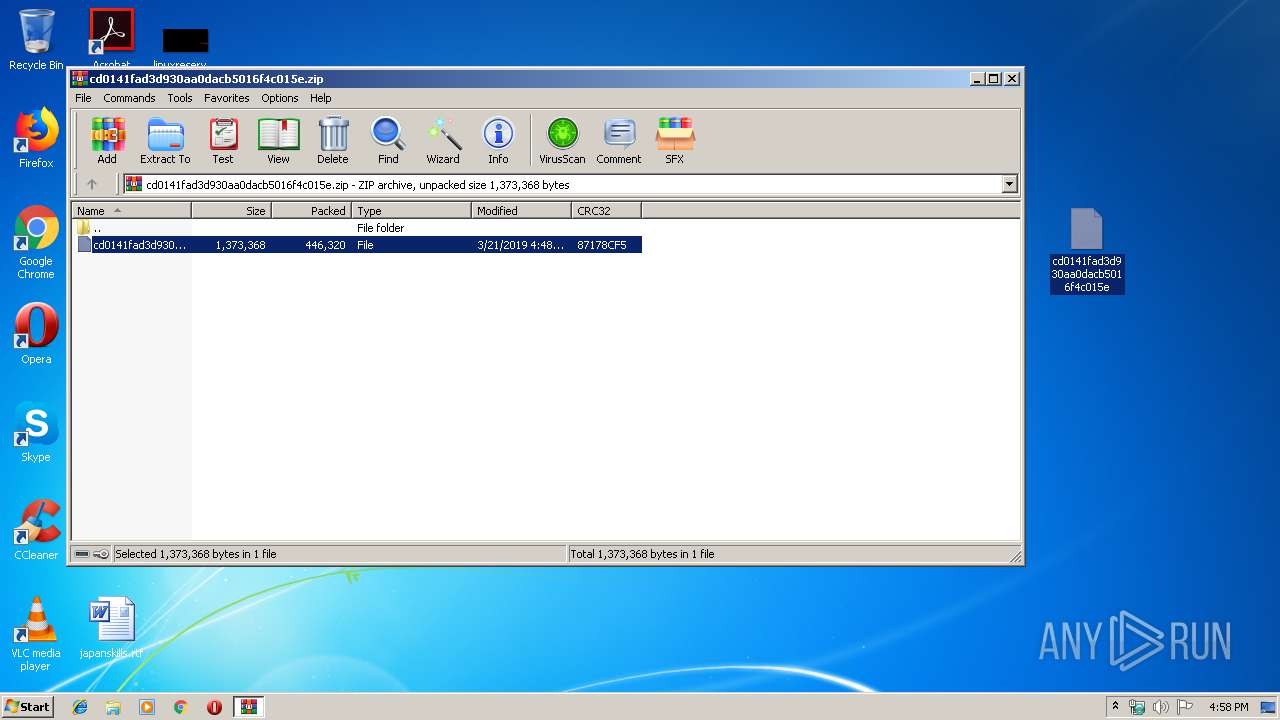
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3340 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3340.1231\cd0141fad3d930aa0dacb5016f4c015e | — | |
MD5:— | SHA256:— | |||
| 2884 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR5D25.tmp.cvr | — | |
MD5:— | SHA256:— | |||
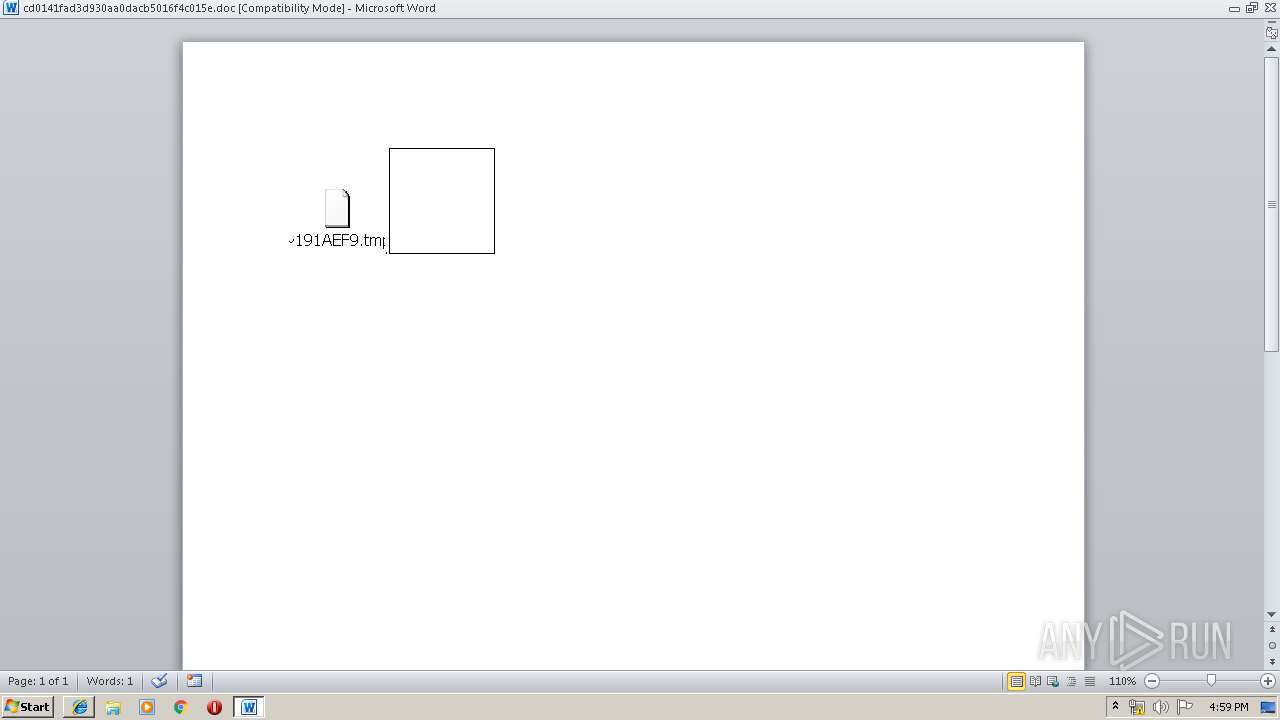
| 2884 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~191AEF9.tmp | image | |
MD5:— | SHA256:— | |||
| 2884 | WINWORD.EXE | C:\Users\admin\Desktop\~$0141fad3d930aa0dacb5016f4c015e.doc | pgc | |
MD5:— | SHA256:— | |||
| 3636 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2884 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\7E697AD4.emf | emf | |
MD5:— | SHA256:— | |||
| 3636 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1560 | cmd.exe | C:\Users\admin\AppData\Local\Temp\~AFER125419.tmp | executable | |
MD5:— | SHA256:— | |||
| 2376 | EQNEDT32.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\we[1].hta | html | |
MD5:— | SHA256:— | |||
| 4028 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@bing[2].txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
16
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4028 | iexplore.exe | GET | 302 | 104.109.80.115:80 | http://go.microsoft.com/fwlink/?LinkId=57426&Ext=tmp | NL | — | — | whitelisted |
4028 | iexplore.exe | GET | 301 | 2.16.186.24:80 | http://shell.windows.com/fileassoc/fileassoc.asp?Ext=tmp | unknown | — | — | whitelisted |
3980 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3636 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3064 | iexplore.exe | GET | 302 | 104.109.80.115:80 | http://go.microsoft.com/fwlink/?LinkId=57426&Ext=tmp | NL | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2376 | EQNEDT32.EXE | 173.198.217.123:443 | modernizingforeignassistance.net | Turnkey Internet Inc. | US | suspicious |
3636 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
4028 | iexplore.exe | 104.109.80.115:80 | go.microsoft.com | Akamai International B.V. | NL | whitelisted |
4028 | iexplore.exe | 2.16.186.24:80 | shell.windows.com | Akamai International B.V. | — | whitelisted |
4028 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3636 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
4028 | iexplore.exe | 65.55.163.78:443 | login.live.com | Microsoft Corporation | US | whitelisted |
3980 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3064 | iexplore.exe | 104.109.80.115:80 | go.microsoft.com | Akamai International B.V. | NL | whitelisted |
3064 | iexplore.exe | 2.16.186.24:80 | shell.windows.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
modernizingforeignassistance.net |
| suspicious |
www.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
shell.windows.com |
| whitelisted |
login.live.com |
| whitelisted |