| File name: | GWSetup.bin |
| Full analysis: | https://app.any.run/tasks/2ead596f-491d-410a-a456-4c28fd42bf42 |
| Verdict: | Malicious activity |
| Analysis date: | October 28, 2021, 16:43:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, InstallShield self-extracting archive |
| MD5: | DC4161731DA54D451F1163BA43D46AF1 |
| SHA1: | 2C1305B8D37FA2268F555D5D43E7E0C96C3734FB |
| SHA256: | 3D59469806071C13089B1CD358F31B365E8B59C0612529AF926868B377179481 |
| SSDEEP: | 196608:/P65nYy4V/EtsxzQ9mBZ5QrrqpjrTluuZ:aFtQwsxzQID5Q3aNu |
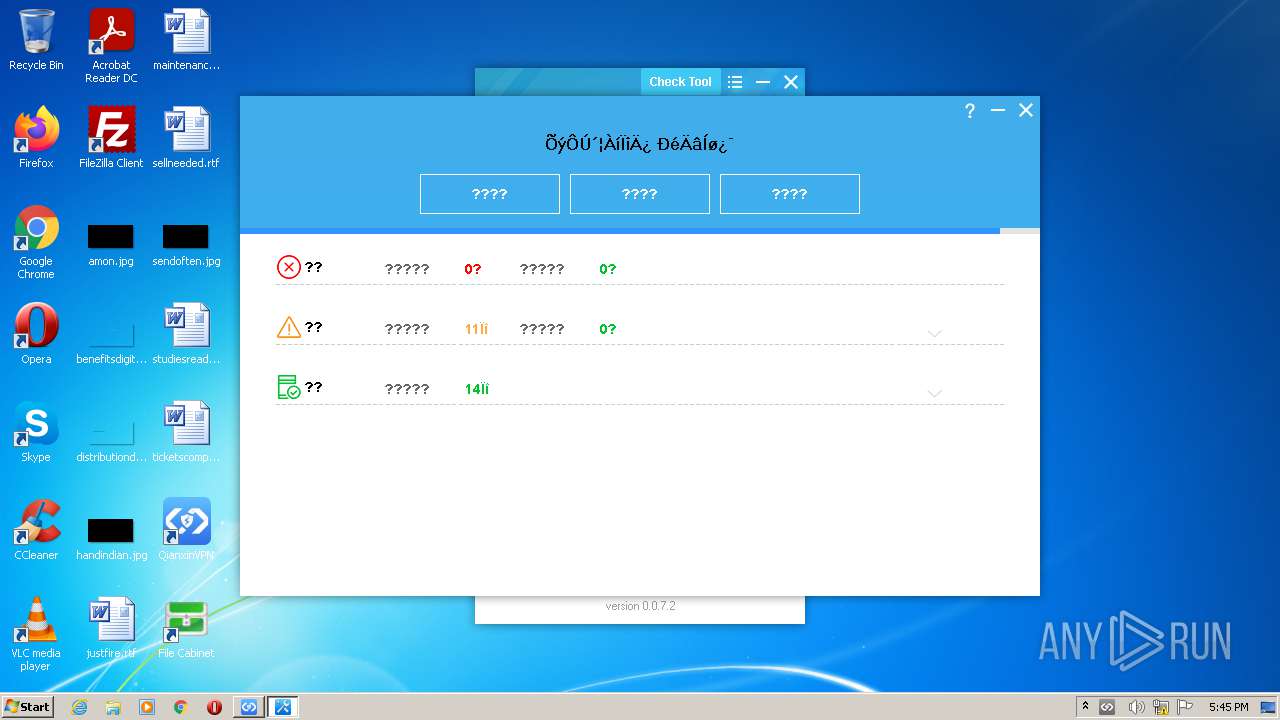
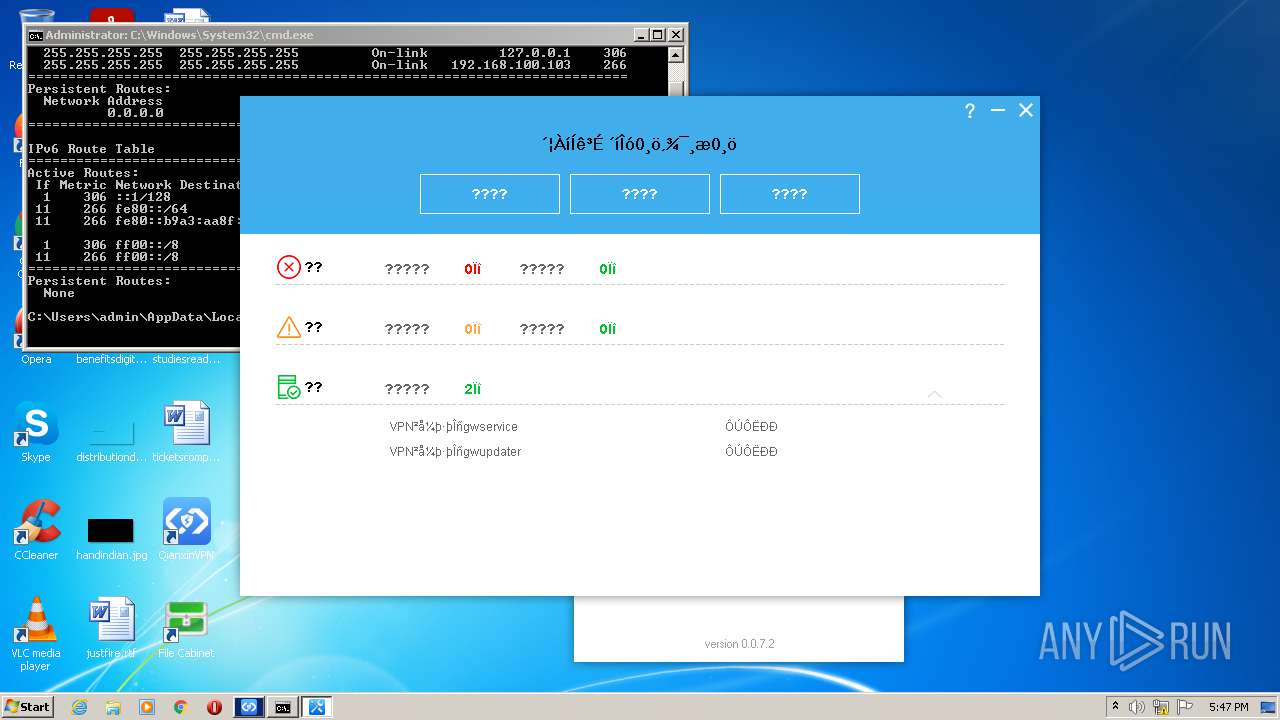
MALICIOUS
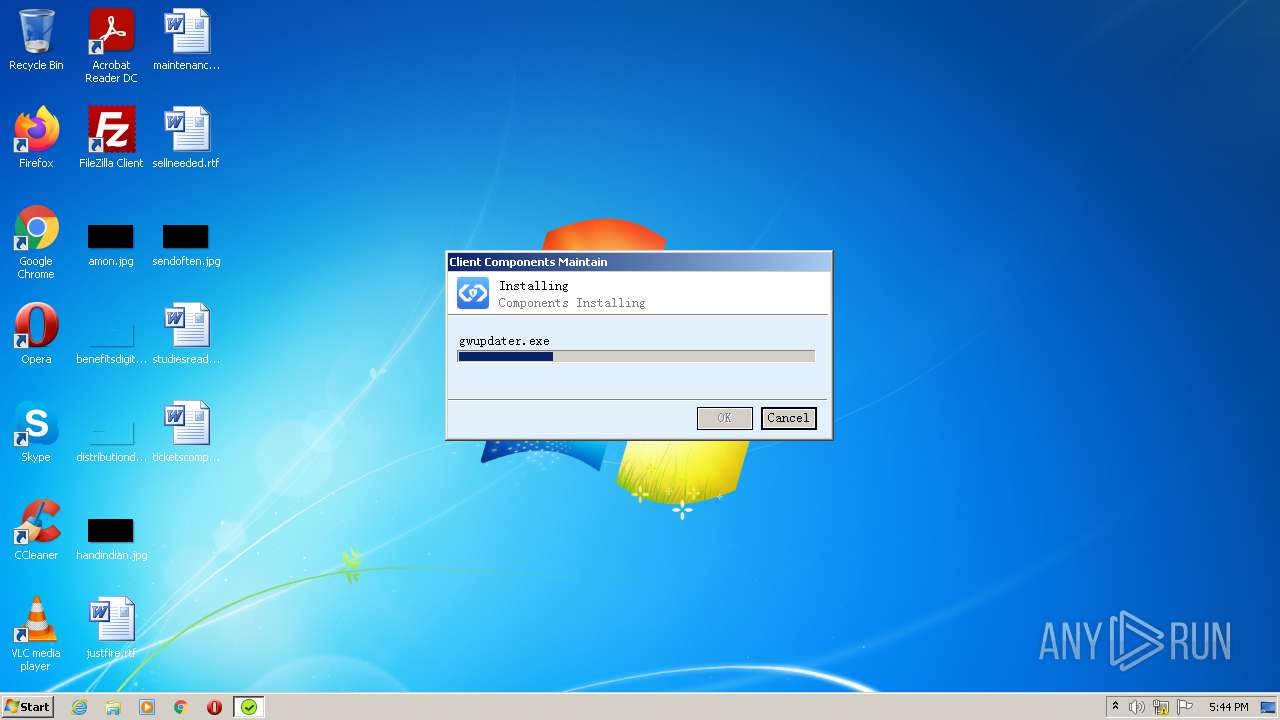
Drops executable file immediately after starts
- GWSetup.bin.exe (PID: 2036)
Loads dropped or rewritten executable
- gwservice.exe (PID: 3216)
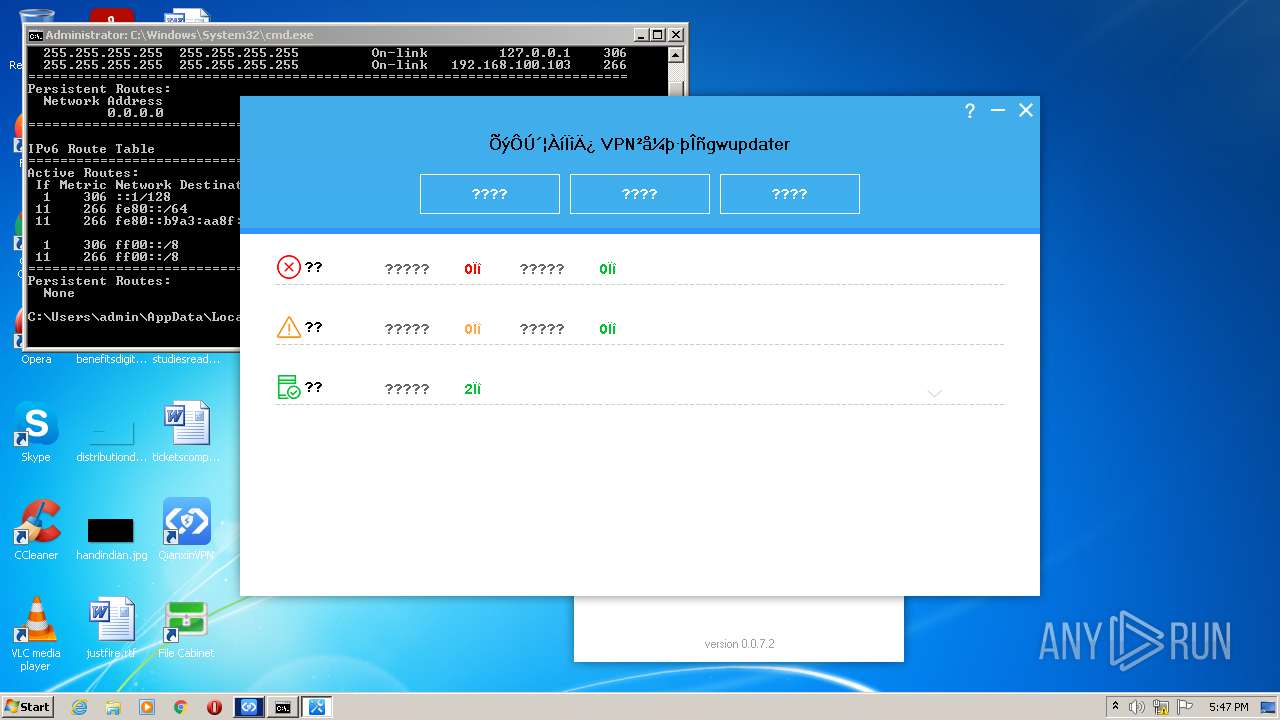
- gwupdater.exe (PID: 304)
- GWSetup.bin.exe (PID: 2036)
Application was dropped or rewritten from another process
- gwupdater.exe (PID: 304)
- gwservice.exe (PID: 3216)
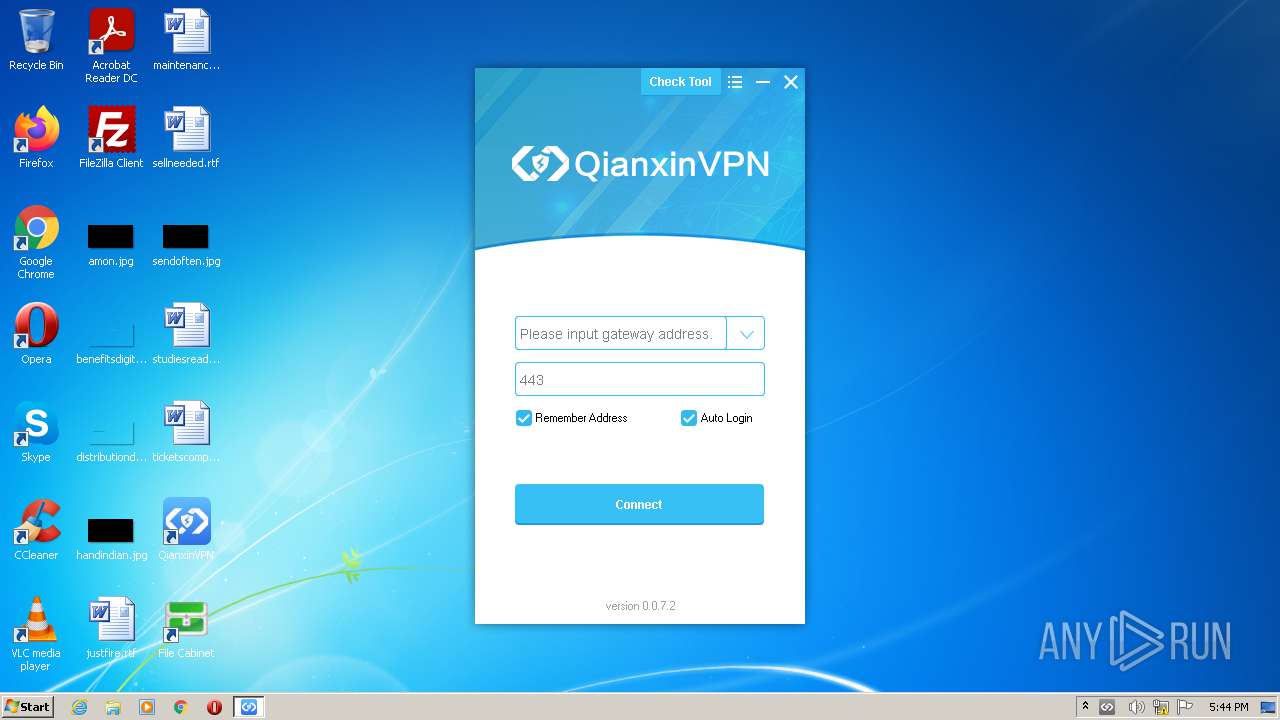
- gwclient.exe (PID: 2932)
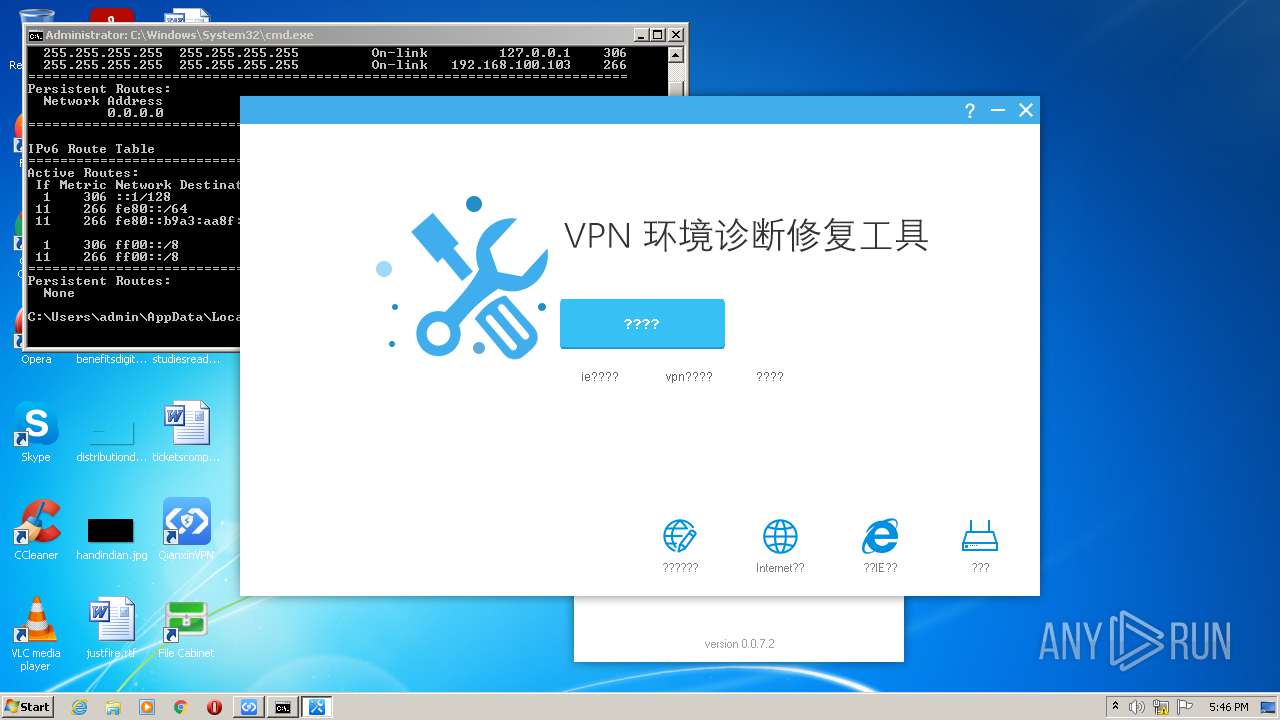
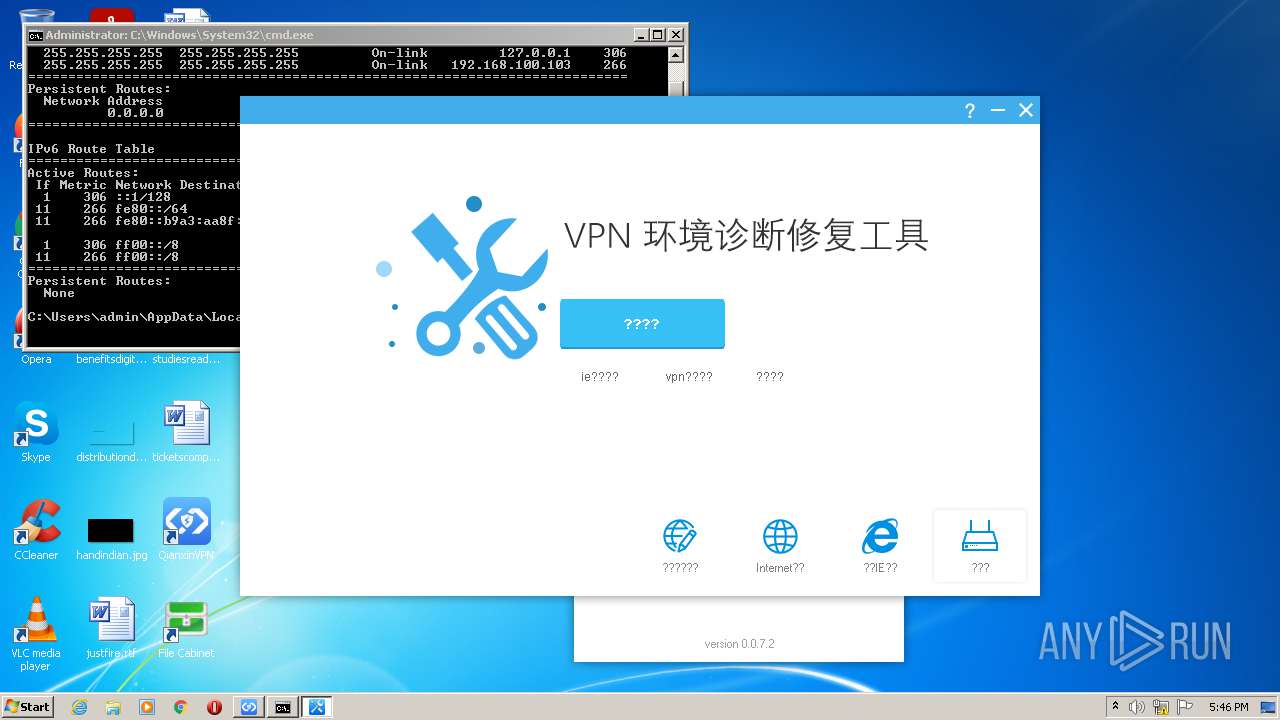
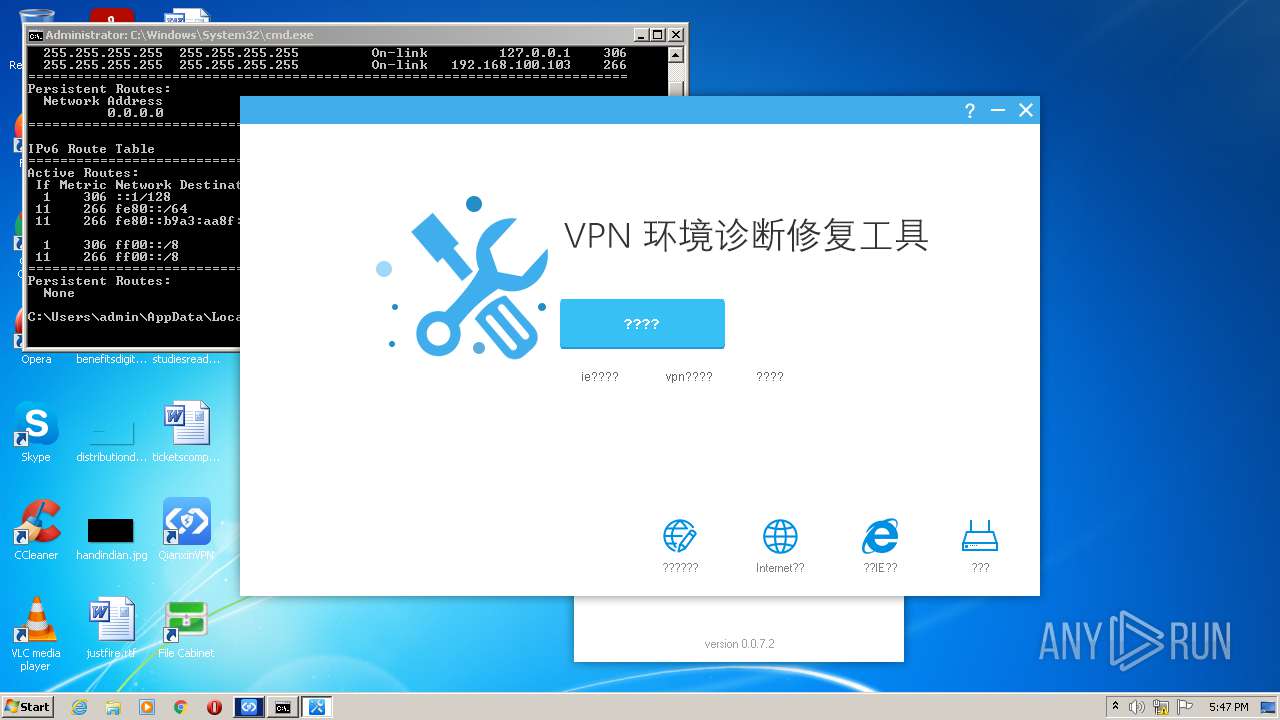
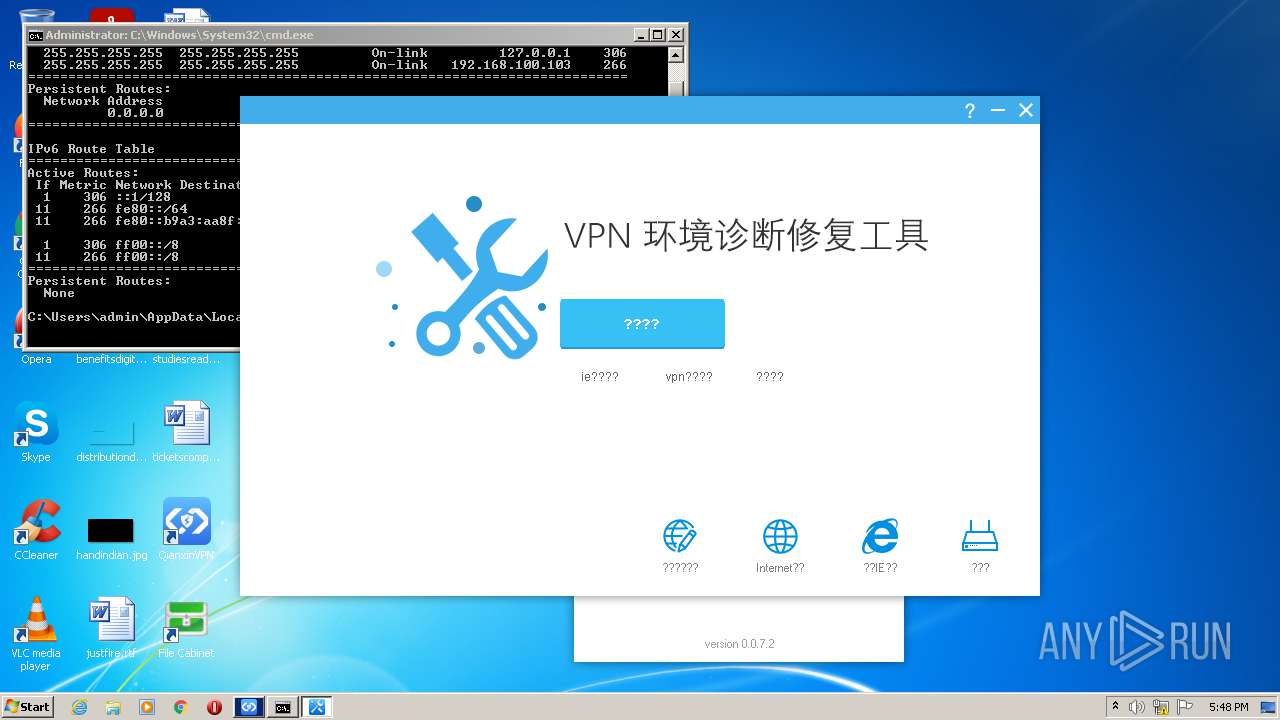
- GWVPNDoctor.exe (PID: 2320)
- GWVPNDoctor.exe (PID: 1576)
Writes to a start menu file
- GWSetup.bin.exe (PID: 2036)
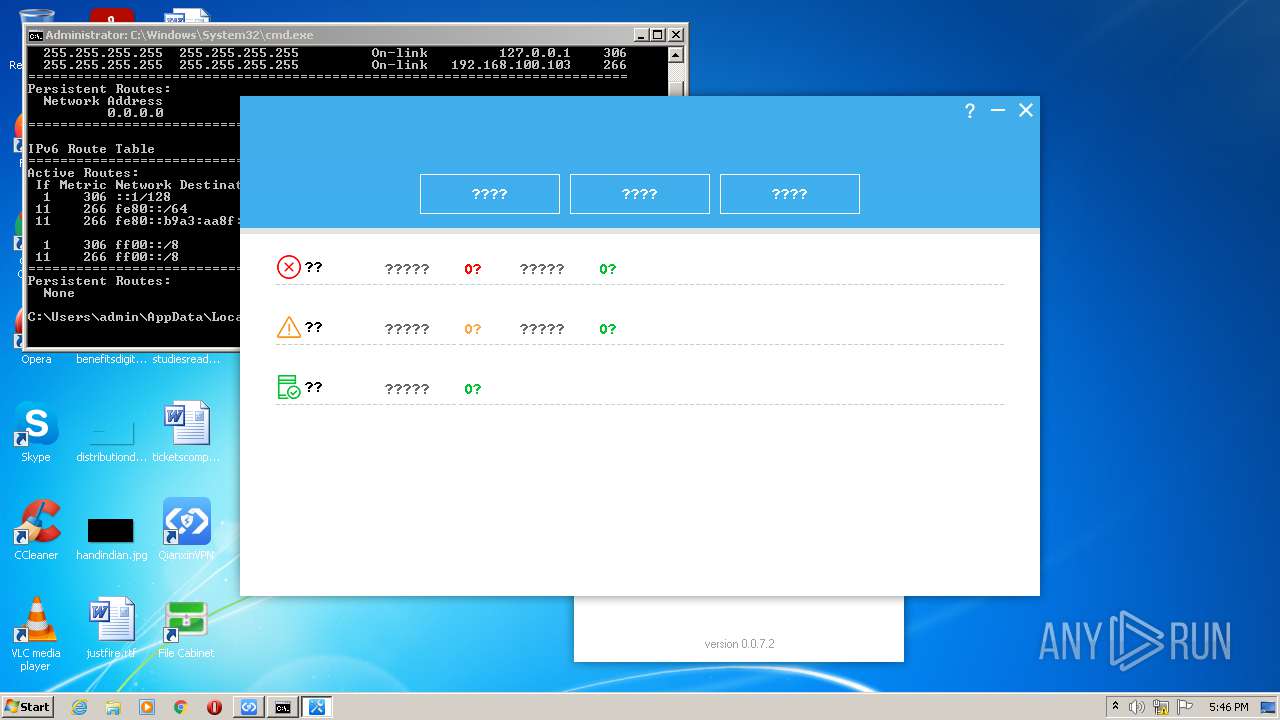
Changes settings of System certificates
- GWVPNDoctor.exe (PID: 2320)
Loads the Task Scheduler COM API
- rundll32.exe (PID: 2408)
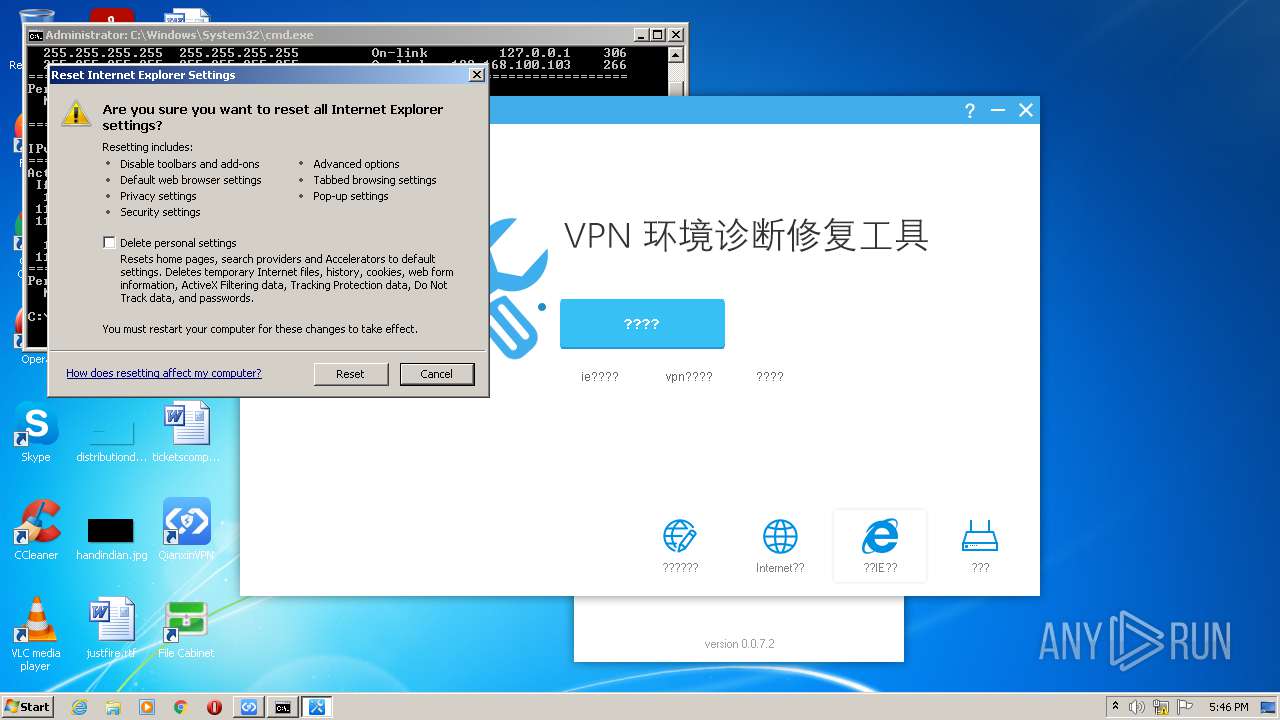
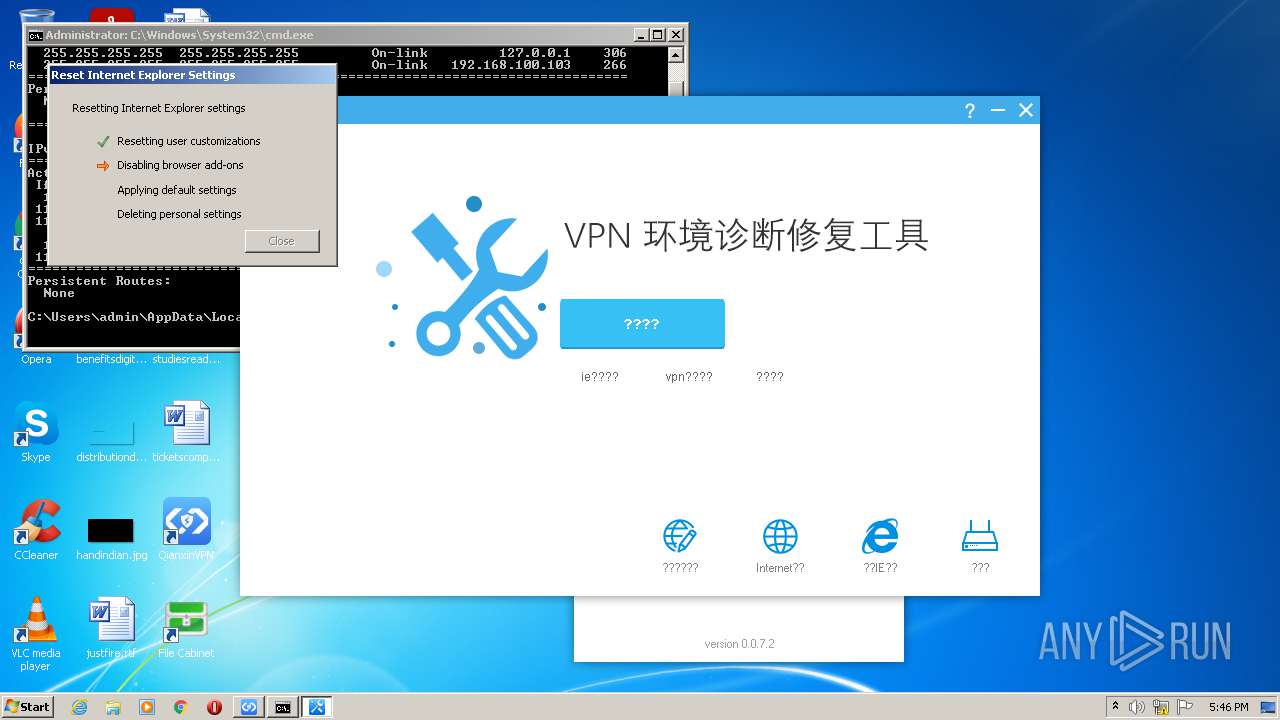
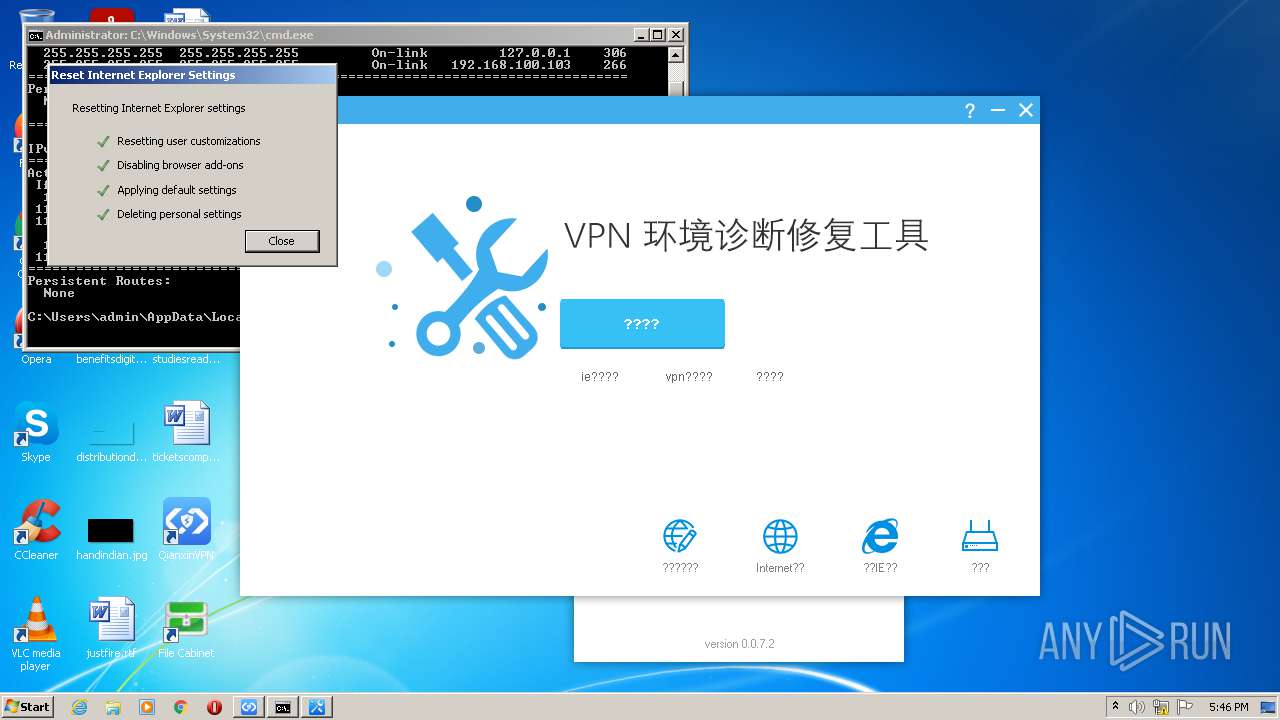
Modifies the Internet Explorer registry keys for privacy or tracking
- reg.exe (PID: 2960)
- reg.exe (PID: 2628)
Changes internet zones settings
- rundll32.exe (PID: 1268)
SUSPICIOUS
Drops a file with a compile date too recent
- GWSetup.bin.exe (PID: 2036)
Executable content was dropped or overwritten
- GWSetup.bin.exe (PID: 2036)
Checks supported languages
- GWSetup.bin.exe (PID: 2036)
- gwupdater.exe (PID: 304)
- gwservice.exe (PID: 3216)
- GWVPNDoctor.exe (PID: 2320)
- gwclient.exe (PID: 2932)
- cmd.exe (PID: 3024)
- GWVPNDoctor.exe (PID: 1576)
- cmd.exe (PID: 1180)
Creates a directory in Program Files
- GWSetup.bin.exe (PID: 2036)
Creates files in the Windows directory
- GWSetup.bin.exe (PID: 2036)
- ieunatt.exe (PID: 2608)
Creates/Modifies COM task schedule object
- GWSetup.bin.exe (PID: 2036)
Drops a file with too old compile date
- GWSetup.bin.exe (PID: 2036)
Creates files in the program directory
- gwupdater.exe (PID: 304)
- GWSetup.bin.exe (PID: 2036)
- gwservice.exe (PID: 3216)
- gwclient.exe (PID: 2932)
- rundll32.exe (PID: 1268)
Creates or modifies windows services
- GWSetup.bin.exe (PID: 2036)
Reads the computer name
- gwupdater.exe (PID: 304)
- GWSetup.bin.exe (PID: 2036)
- gwservice.exe (PID: 3216)
- gwclient.exe (PID: 2932)
- GWVPNDoctor.exe (PID: 2320)
- GWVPNDoctor.exe (PID: 1576)
Drops a file that was compiled in debug mode
- GWSetup.bin.exe (PID: 2036)
Executed as Windows Service
- gwservice.exe (PID: 3216)
- gwupdater.exe (PID: 304)
Creates a software uninstall entry
- GWSetup.bin.exe (PID: 2036)
Uses REG.EXE to modify Windows registry
- GWVPNDoctor.exe (PID: 2320)
- GWVPNDoctor.exe (PID: 1576)
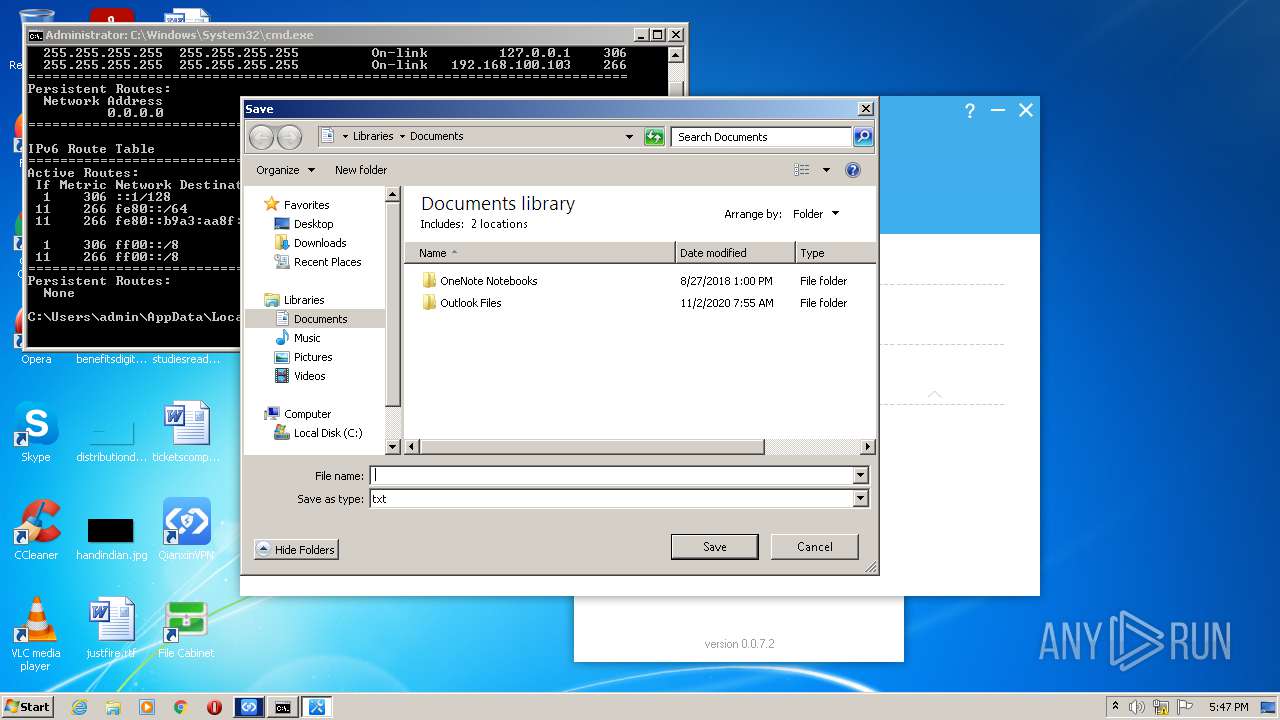
Creates files in the user directory
- GWSetup.bin.exe (PID: 2036)
- rundll32.exe (PID: 3004)
- rundll32.exe (PID: 2408)
Starts SC.EXE for service management
- GWVPNDoctor.exe (PID: 2320)
- GWVPNDoctor.exe (PID: 1576)
Adds / modifies Windows certificates
- GWVPNDoctor.exe (PID: 2320)
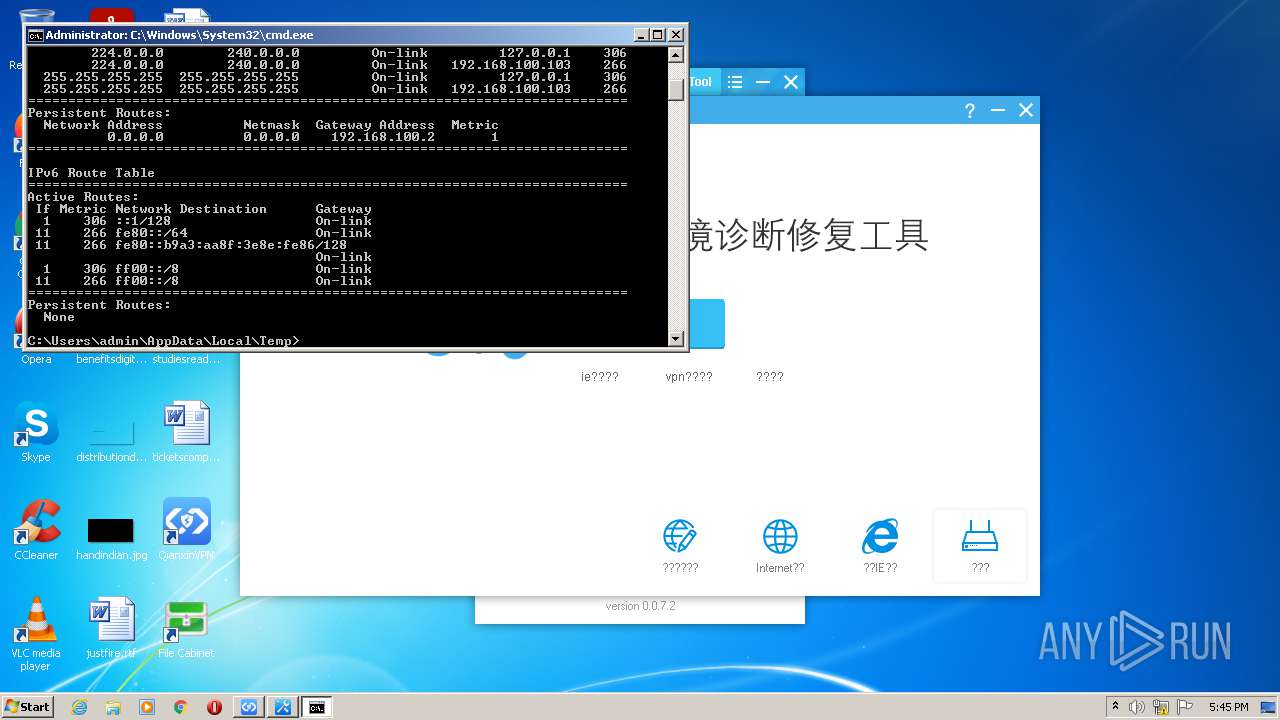
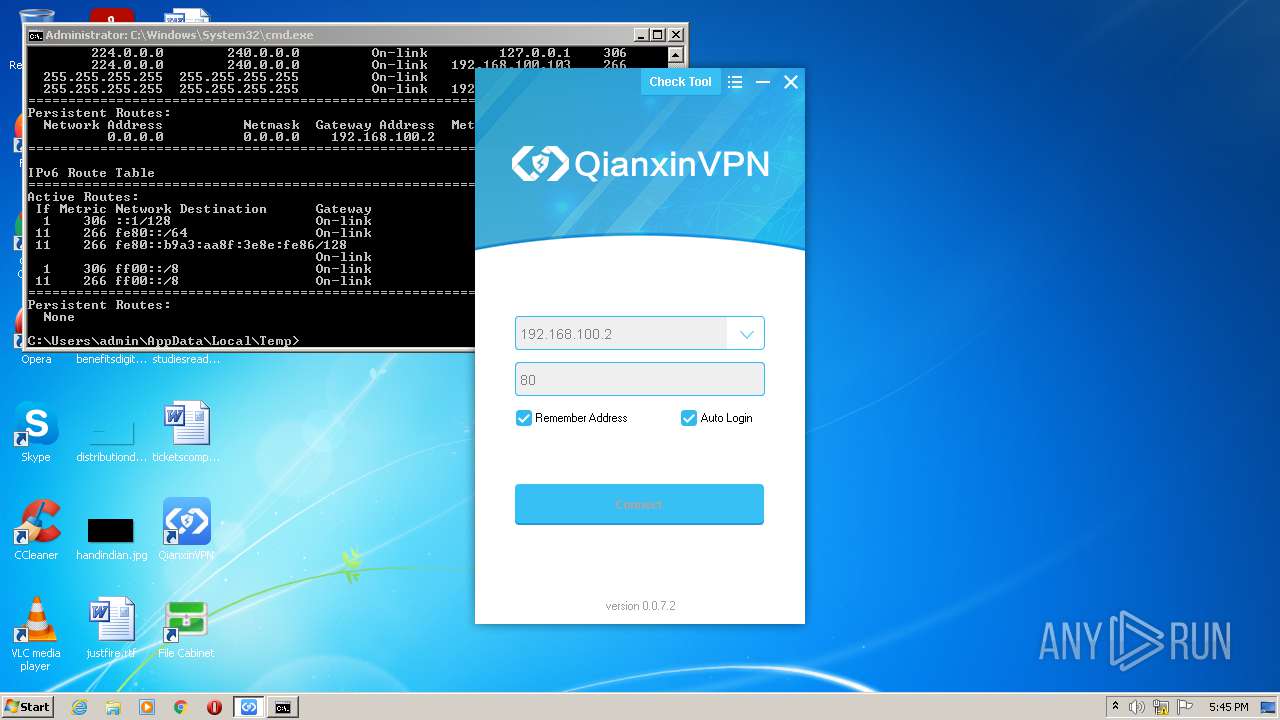
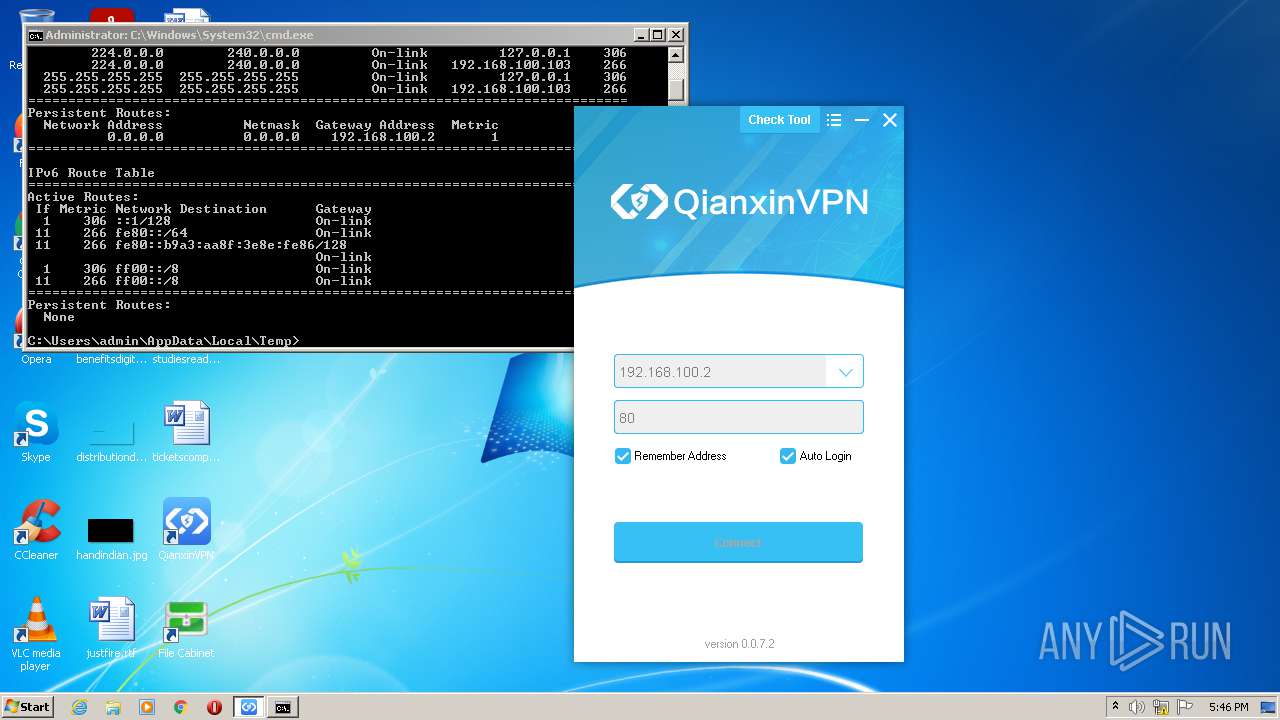
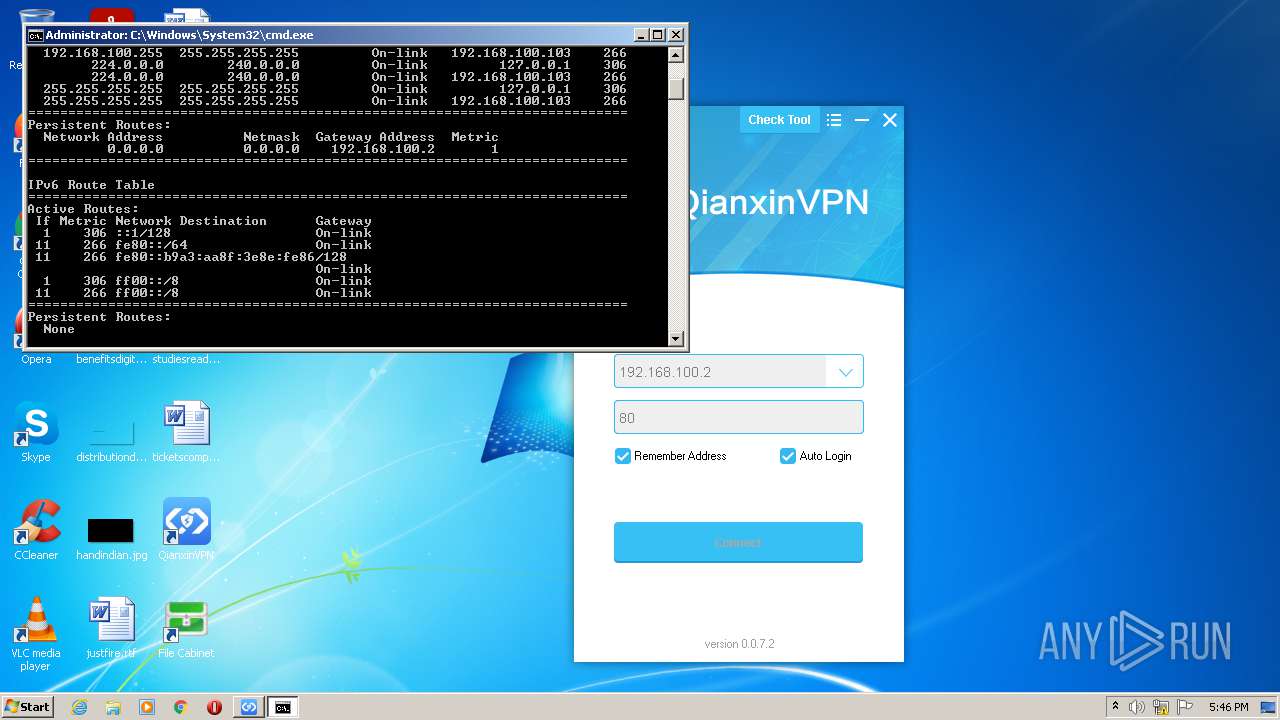
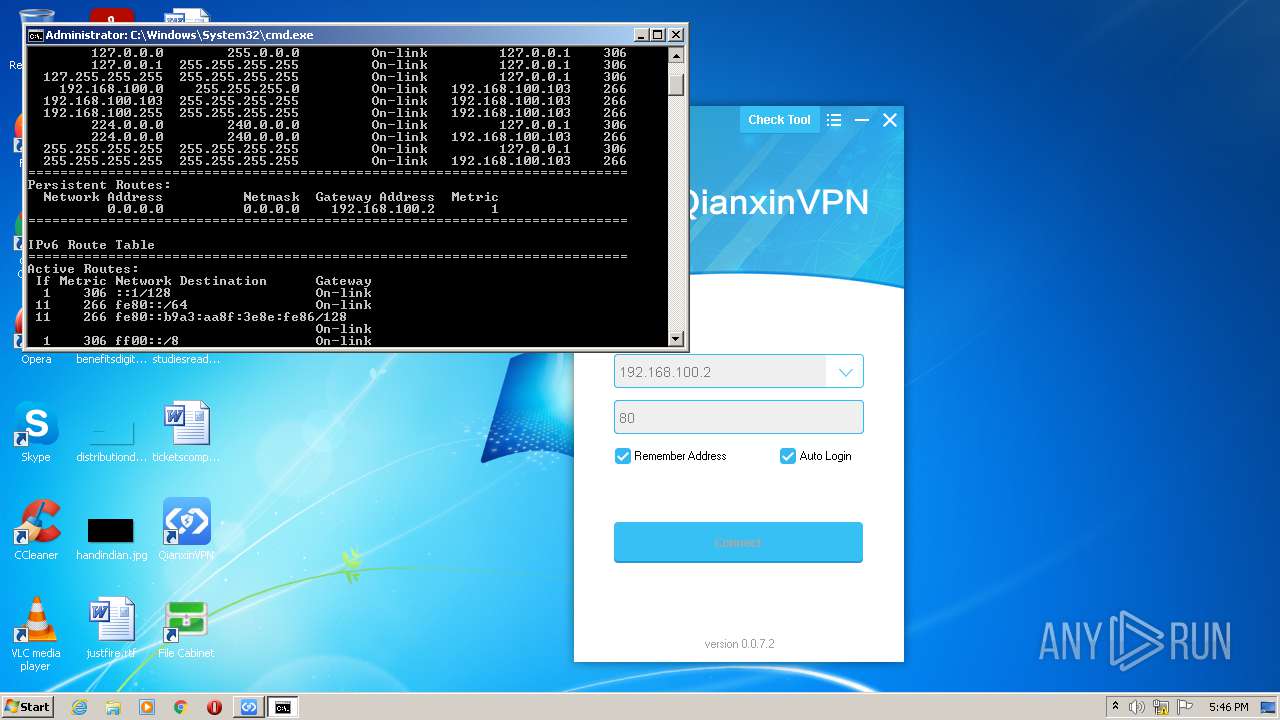
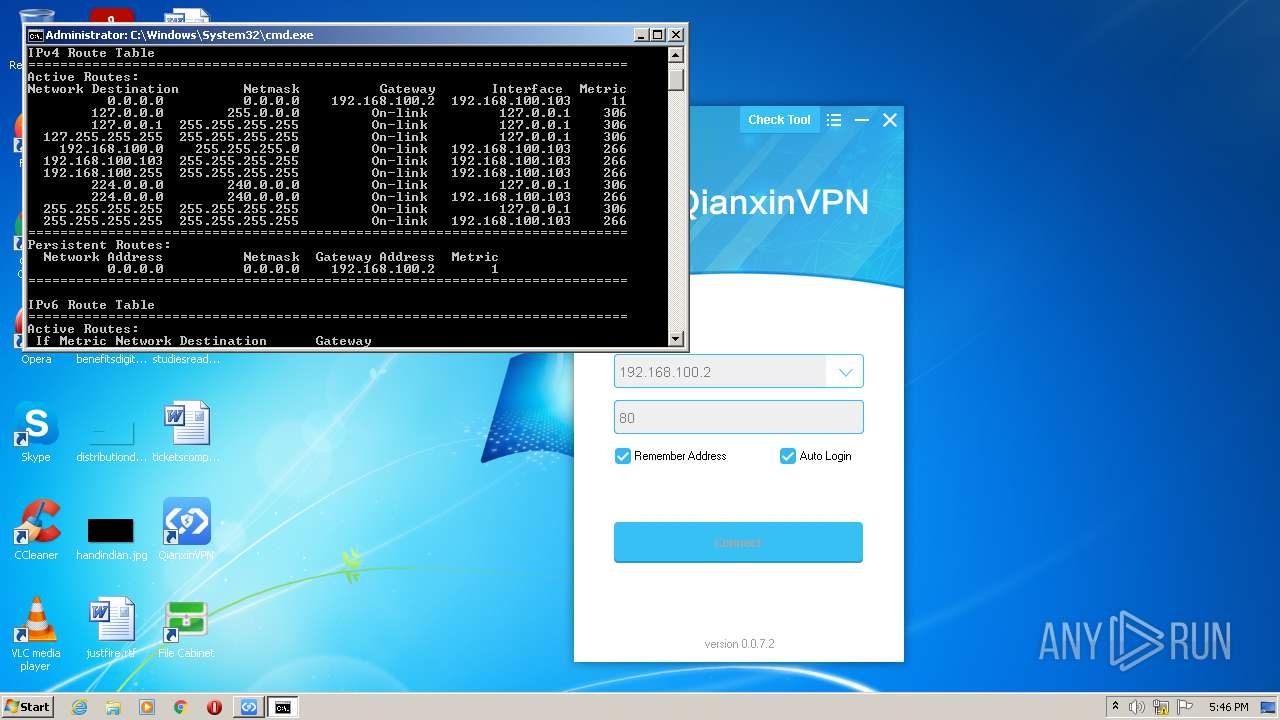
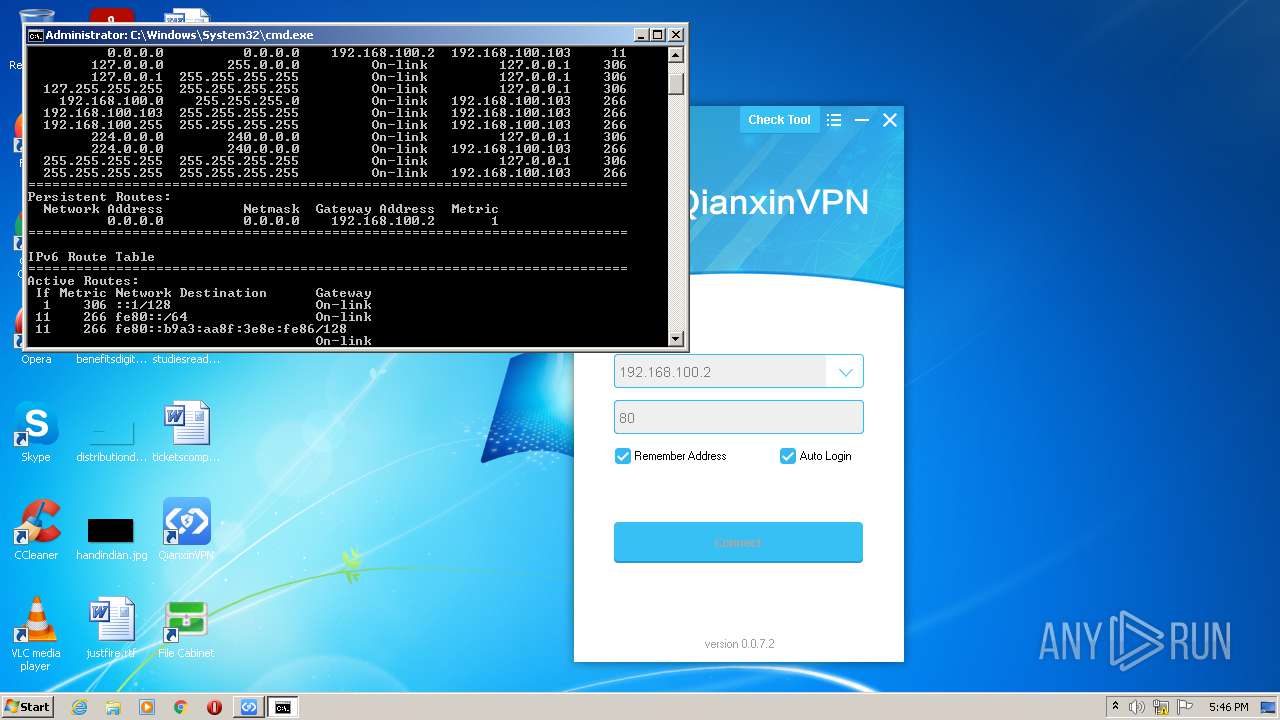
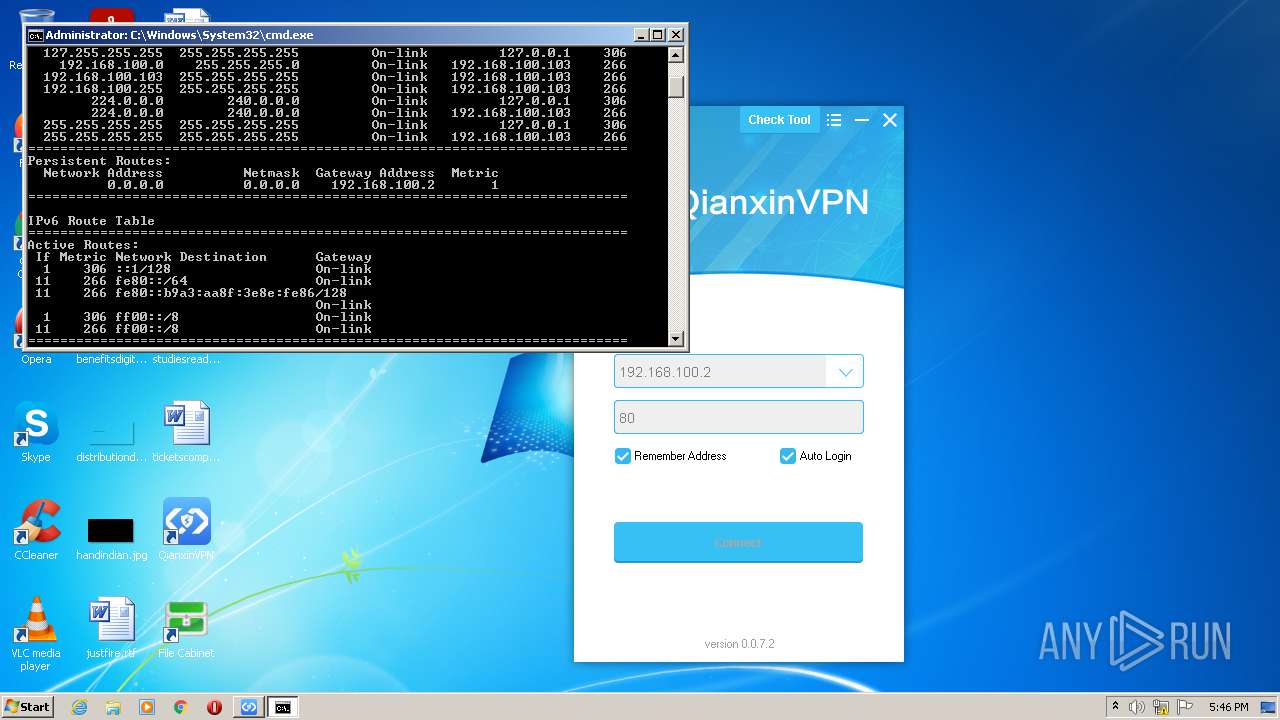
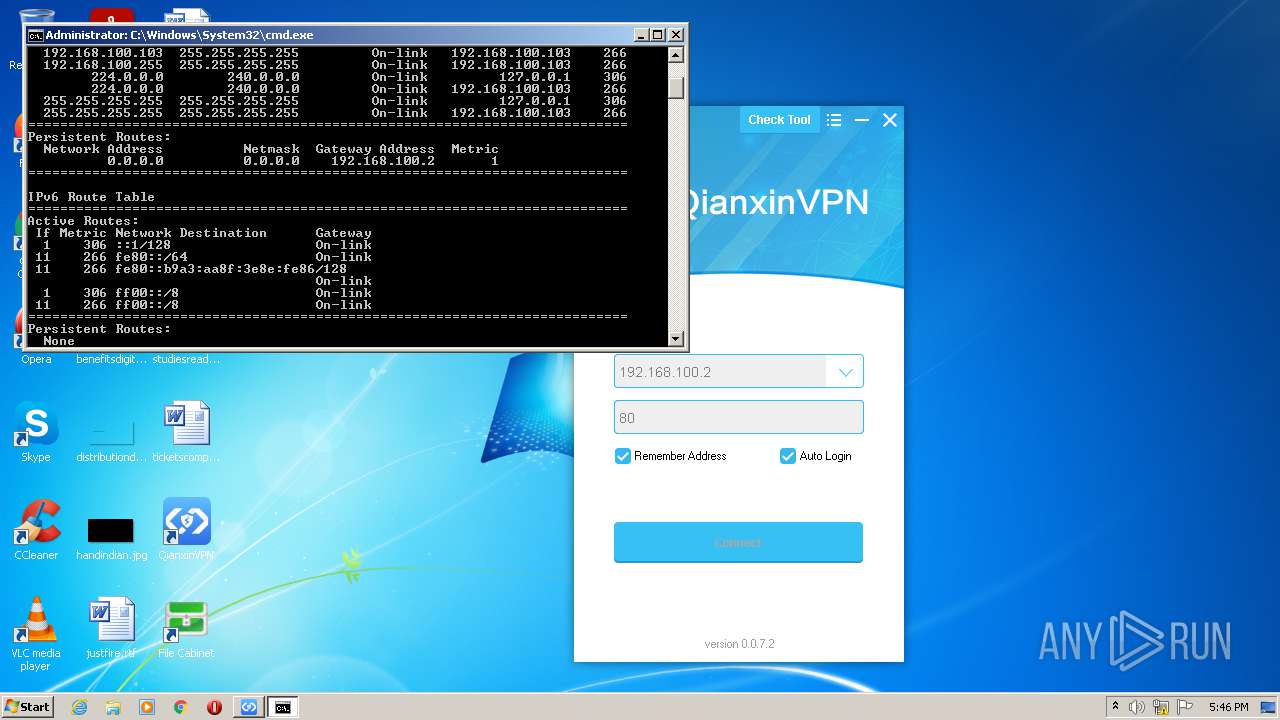
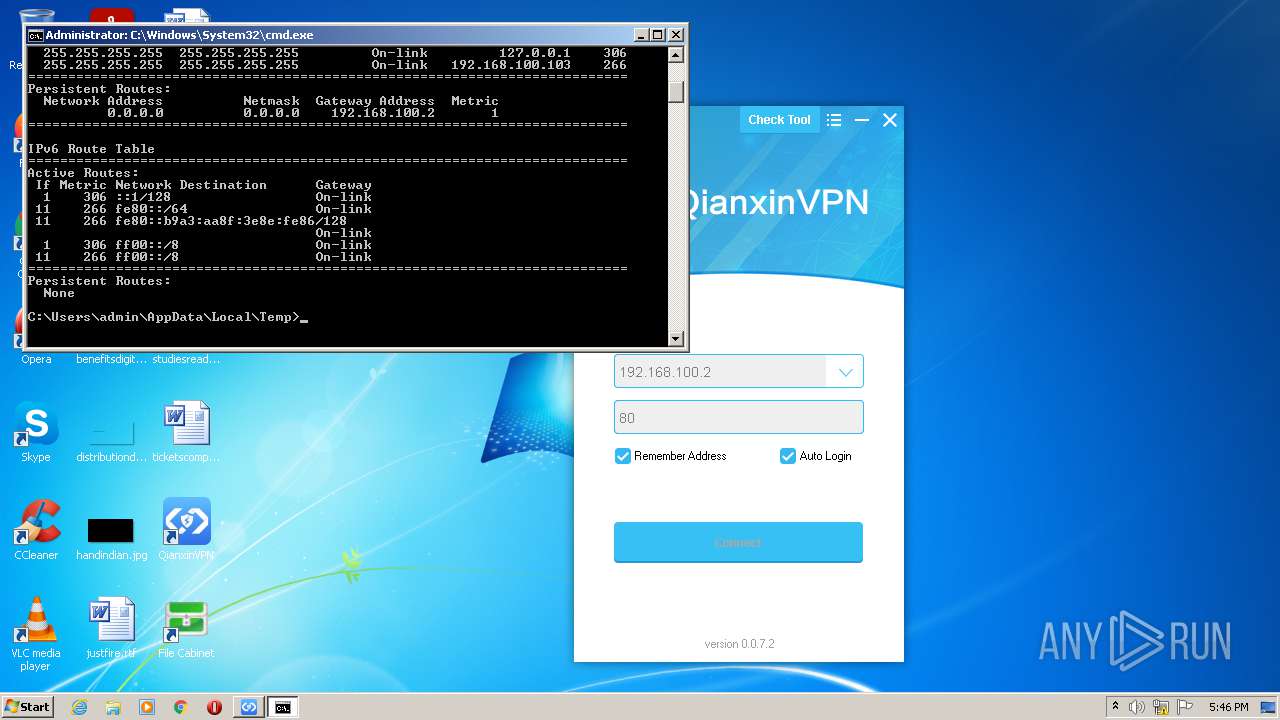
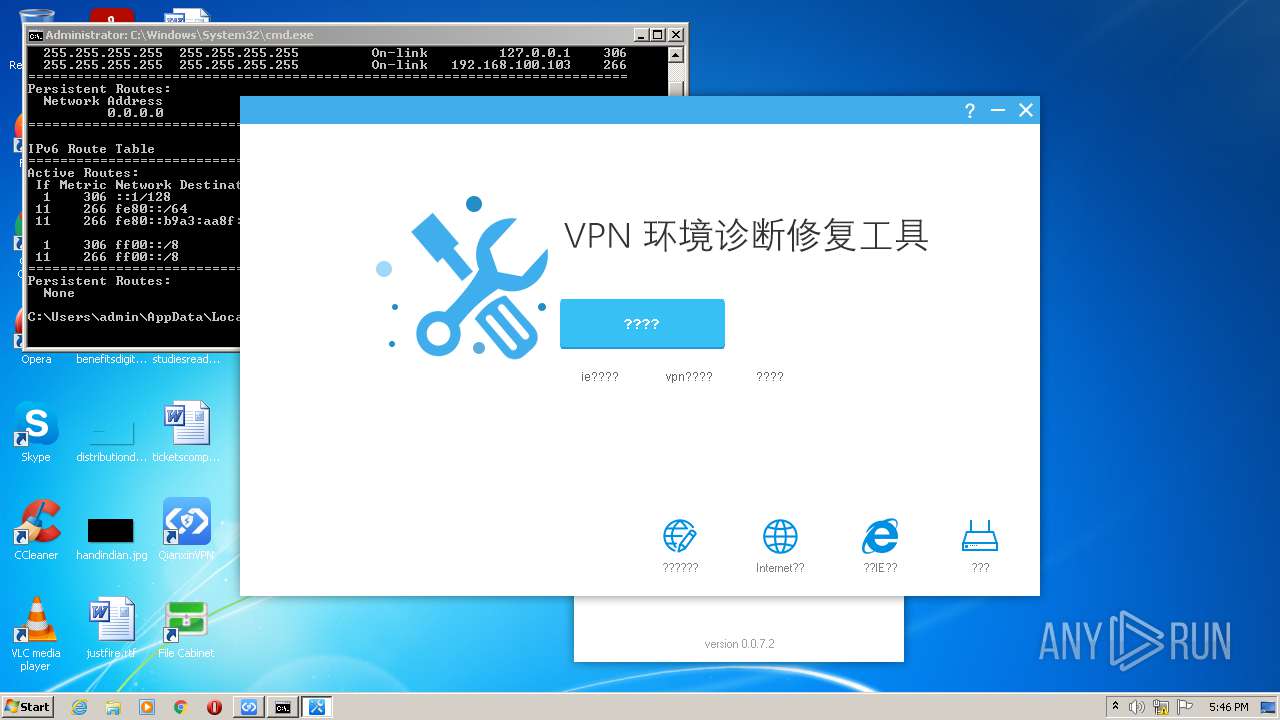
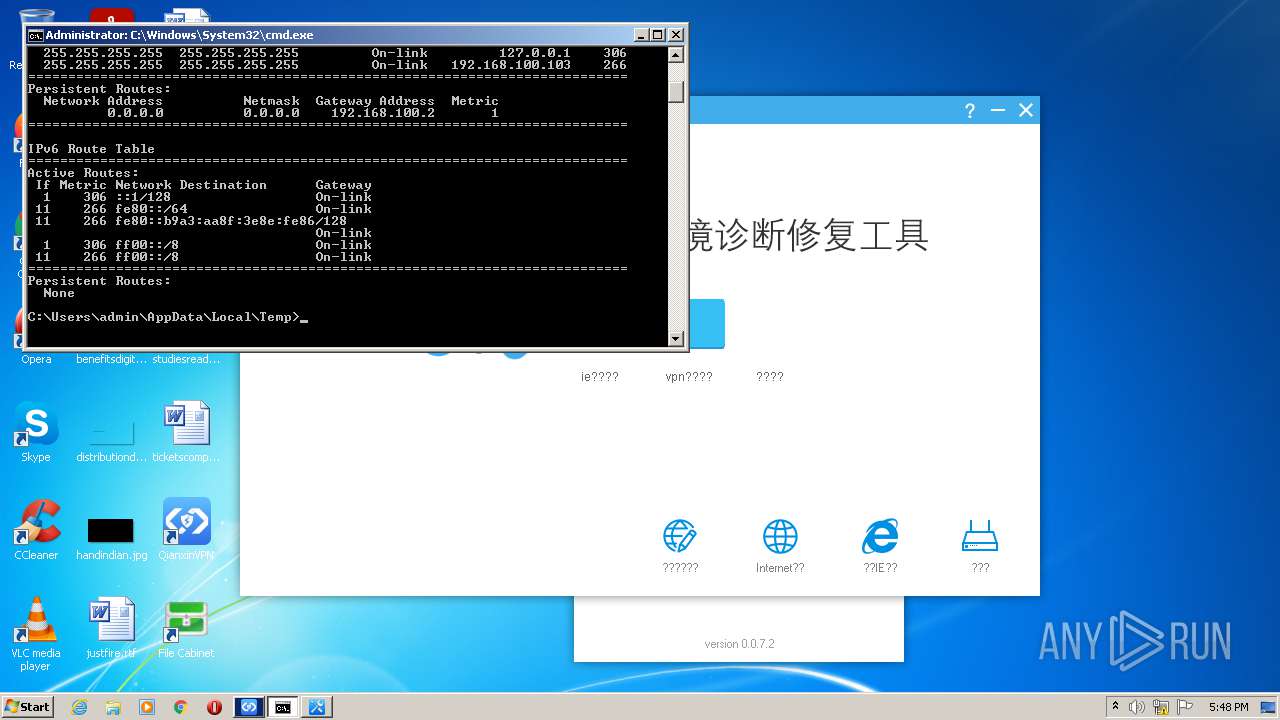
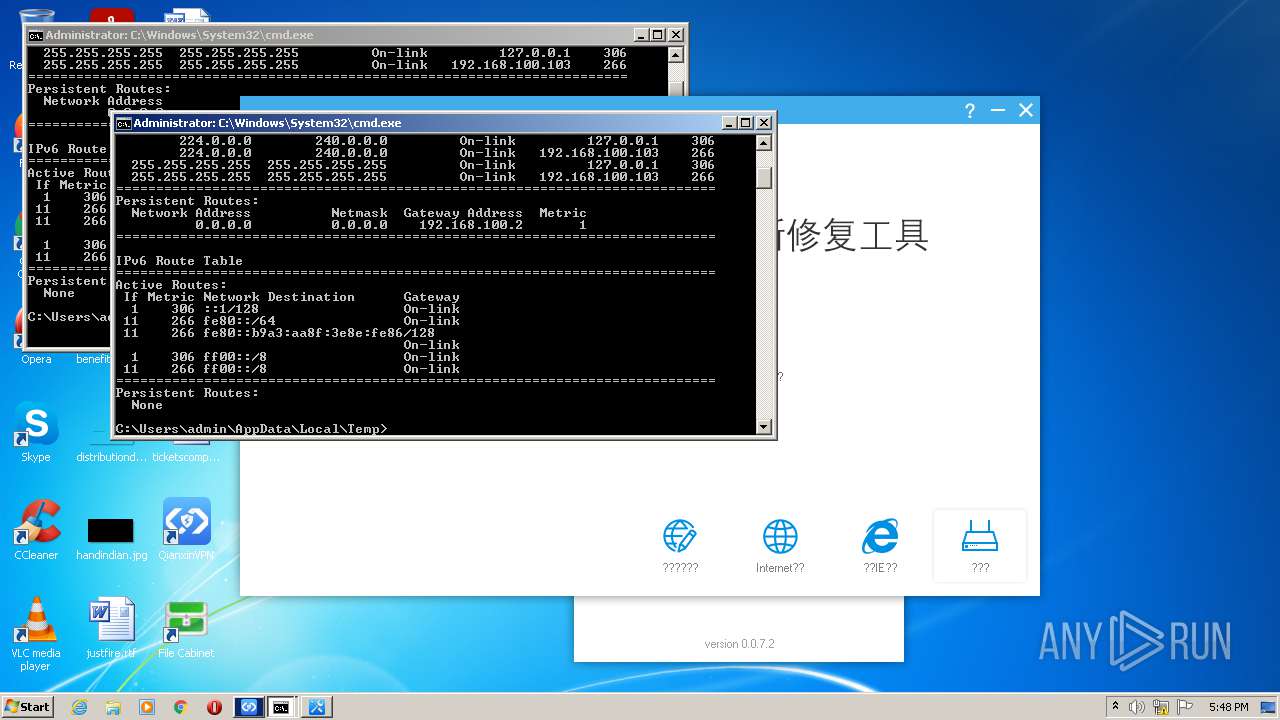
Uses IPCONFIG.EXE to discover IP address
- GWVPNDoctor.exe (PID: 2320)
- GWVPNDoctor.exe (PID: 1576)
Starts CMD.EXE for commands execution
- GWVPNDoctor.exe (PID: 2320)
- GWVPNDoctor.exe (PID: 1576)
Reads Microsoft Outlook installation path
- rundll32.exe (PID: 312)
- rundll32.exe (PID: 2756)
- rundll32.exe (PID: 3308)
- rundll32.exe (PID: 3364)
- rundll32.exe (PID: 2408)
- rundll32.exe (PID: 3004)
- rundll32.exe (PID: 1268)
- GWVPNDoctor.exe (PID: 1576)
Modifies the phishing filter of IE
- rundll32.exe (PID: 1268)
Changes the started page of IE
- rundll32.exe (PID: 1268)
Uses RUNDLL32.EXE to load library
- rundll32.exe (PID: 1268)
- GWVPNDoctor.exe (PID: 1576)
Starts Internet Explorer
- rundll32.exe (PID: 3004)
- rundll32.exe (PID: 2408)
Application launched itself
- rundll32.exe (PID: 1268)
INFO
Checks supported languages
- reg.exe (PID: 616)
- reg.exe (PID: 3944)
- reg.exe (PID: 1580)
- reg.exe (PID: 3320)
- reg.exe (PID: 3532)
- reg.exe (PID: 3788)
- sc.exe (PID: 4008)
- sc.exe (PID: 3964)
- sc.exe (PID: 852)
- ipconfig.exe (PID: 928)
- ROUTE.EXE (PID: 3392)
- rundll32.exe (PID: 1268)
- rundll32.exe (PID: 2756)
- rundll32.exe (PID: 312)
- rundll32.exe (PID: 3308)
- ieunatt.exe (PID: 2608)
- rundll32.exe (PID: 3364)
- rundll32.exe (PID: 3004)
- rundll32.exe (PID: 2408)
- iexplore.exe (PID: 2012)
- iexplore.exe (PID: 1200)
- ipconfig.exe (PID: 884)
- reg.exe (PID: 448)
- reg.exe (PID: 2720)
- reg.exe (PID: 4024)
- reg.exe (PID: 2960)
- reg.exe (PID: 2448)
- reg.exe (PID: 3084)
- reg.exe (PID: 2340)
- reg.exe (PID: 1044)
- sc.exe (PID: 2468)
- sc.exe (PID: 3572)
- ipconfig.exe (PID: 2056)
- reg.exe (PID: 2208)
- reg.exe (PID: 2364)
- reg.exe (PID: 3928)
- reg.exe (PID: 2104)
- reg.exe (PID: 3796)
- reg.exe (PID: 3396)
- reg.exe (PID: 1996)
- reg.exe (PID: 3264)
- reg.exe (PID: 3148)
- reg.exe (PID: 3168)
- reg.exe (PID: 3552)
- ROUTE.EXE (PID: 4068)
- reg.exe (PID: 2628)
Reads the computer name
- sc.exe (PID: 4008)
- sc.exe (PID: 3964)
- sc.exe (PID: 852)
- ipconfig.exe (PID: 928)
- ROUTE.EXE (PID: 3392)
- rundll32.exe (PID: 1268)
- rundll32.exe (PID: 312)
- rundll32.exe (PID: 2756)
- rundll32.exe (PID: 3308)
- rundll32.exe (PID: 3364)
- rundll32.exe (PID: 2408)
- rundll32.exe (PID: 3004)
- iexplore.exe (PID: 2012)
- iexplore.exe (PID: 1200)
- ipconfig.exe (PID: 884)
- sc.exe (PID: 3572)
- ipconfig.exe (PID: 2056)
- sc.exe (PID: 2468)
- ROUTE.EXE (PID: 4068)
Checks Windows Trust Settings
- GWVPNDoctor.exe (PID: 2320)
- GWVPNDoctor.exe (PID: 1576)
Reads settings of System Certificates
- GWVPNDoctor.exe (PID: 2320)
- GWVPNDoctor.exe (PID: 1576)
Reads CPU info
- rundll32.exe (PID: 3364)
- rundll32.exe (PID: 3004)
- rundll32.exe (PID: 2408)
Creates files in the user directory
- iexplore.exe (PID: 2012)
- iexplore.exe (PID: 1200)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:04:20 08:38:53+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 31232 |
| InitializedDataSize: | 32768 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x87f0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.1.3 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | GWSetup |
| FileVersion: | 0, 0, 1, 3 |
| InternalName: | GWSetup |
| LegalCopyright: | Copyright 2020 |
| LegalTrademarks: | - |
| OriginalFileName: | SetupStub.exe |
| PrivateBuild: | - |
| ProductName: | - |
| ProductVersion: | 1, 0, 0, 0 |
| SpecialBuild: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Apr-2021 06:38:53 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | GWSetup |
| FileVersion: | 0, 0, 1, 3 |
| InternalName: | GWSetup |
| LegalCopyright: | Copyright 2020 |
| LegalTrademarks: | - |
| OriginalFilename: | SetupStub.exe |
| PrivateBuild: | - |
| ProductName: | - |
| ProductVersion: | 1, 0, 0, 0 |
| SpecialBuild: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 20-Apr-2021 06:38:53 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000079DA | 0x00007A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.40656 |
.rdata | 0x00009000 | 0x000019BC | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.38161 |
.data | 0x0000B000 | 0x000025A0 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.51636 |
.rsrc | 0x0000E000 | 0x00003F38 | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.22134 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.31028 | 768 | UNKNOWN | Chinese - PRC | RT_VERSION |
2 | 5.49816 | 4264 | UNKNOWN | Chinese - PRC | RT_ICON |
3 | 5.50034 | 1128 | UNKNOWN | Chinese - PRC | RT_ICON |
102 | 2.45849 | 48 | UNKNOWN | Chinese - PRC | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
CRYPT32.dll |
KERNEL32.dll |
MSVCP60.dll |
MSVCRT.dll |
PSAPI.DLL |
SETUPAPI.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
136
Monitored processes
55
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Windows\system32\gwupdater.exe" | C:\Windows\system32\gwupdater.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: gwservice Exit code: 0 Version: 0, 0, 1, 55 Modules
| |||||||||||||||
| 312 | C:\Windows\system32\rundll32.exe C:\Windows\system32\inetcpl.cpl,ClearMyTracksByProcess Flags:1641728 WinX:0 WinY:0 IEFrame:00000000 | C:\Windows\system32\rundll32.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 448 | reg add "HKCU\Software\Microsoft\Internet Explorer\Privacy" /v ClearBrowsingHistoryOnExit /t REG_DWORD /d 1 /f | C:\Windows\system32\reg.exe | — | GWVPNDoctor.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 616 | reg query "HKCU\Software\Microsoft\Internet Explorer\Approved Extensions" -v {761497BB-D6F0-462C-B6EB-D4DAF1D92D43} | C:\Windows\system32\reg.exe | — | GWVPNDoctor.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 852 | sc query Dhcp | C:\Windows\system32\sc.exe | — | GWVPNDoctor.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 884 | ipconfig /flushdns | C:\Windows\system32\ipconfig.exe | — | GWVPNDoctor.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 928 | ipconfig /all | C:\Windows\system32\ipconfig.exe | — | GWVPNDoctor.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1044 | reg add "HKCU\Software\Microsoft\Internet Explorer\Privacy" /v CleanPassword /t REG_DWORD /d 1 /f | C:\Windows\system32\reg.exe | — | GWVPNDoctor.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1180 | "C:\Windows\System32\cmd.exe" /k route print | C:\Windows\System32\cmd.exe | — | GWVPNDoctor.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1200 | "C:\Program Files\Internet Explorer\iexplore.exe" -ResetDestinationList | C:\Program Files\Internet Explorer\iexplore.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
25 088
Read events
20 246
Write events
4 679
Delete events
163
Modification events
| (PID) Process: | (2036) GWSetup.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\GWClient\Install |
| Operation: | write | Name: | UpdaterFlag |
Value: 0 | |||
| (PID) Process: | (2036) GWSetup.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\GWClient\Install |
| Operation: | write | Name: | UIOption |
Value: 0 | |||
| (PID) Process: | (2036) GWSetup.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\GWClient\Install |
| Operation: | write | Name: | InstallPath |
Value: C:\Program Files\Gateway\SSLVPN | |||
| (PID) Process: | (2036) GWSetup.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\GWClient\Install |
| Operation: | write | Name: | InstallPath64 |
Value: | |||
| (PID) Process: | (2036) GWSetup.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{100C2765-1362-4CCF-AB02-56D916BB8732}\InprocServer32 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2036) GWSetup.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{100C2765-1362-4CCF-AB02-56D916BB8732} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2036) GWSetup.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{4A2B7DF6-7E36-4A71-8169-D790C00DFCD3}\InprocServer32 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2036) GWSetup.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{4A2B7DF6-7E36-4A71-8169-D790C00DFCD3} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2036) GWSetup.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\GWClient\Install\Shortcut |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2036) GWSetup.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\GWClient\Debug |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
87
Suspicious files
101
Text files
26
Unknown types
34
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2036 | GWSetup.bin.exe | C:\Users\admin\AppData\Local\Temp\gwtemp\gwupdater.dll.cab | compressed | |
MD5:— | SHA256:— | |||
| 2036 | GWSetup.bin.exe | C:\Users\admin\AppData\Local\Temp\gwtemp\GWVPNDoctor.exe.cab | compressed | |
MD5:— | SHA256:— | |||
| 2036 | GWSetup.bin.exe | C:\Users\admin\AppData\Local\Temp\gwtemp\gwclient.exe | executable | |
MD5:— | SHA256:— | |||
| 2036 | GWSetup.bin.exe | C:\Users\admin\AppData\Local\Temp\gwtemp\gwuninstall.exe.cab | compressed | |
MD5:— | SHA256:— | |||
| 2036 | GWSetup.bin.exe | C:\Users\admin\AppData\Local\Temp\gwtemp\gwuninstall.exe | executable | |
MD5:— | SHA256:— | |||
| 2036 | GWSetup.bin.exe | C:\Users\admin\AppData\Local\Temp\gwtemp\signcrack.exe.cab | compressed | |
MD5:— | SHA256:— | |||
| 2036 | GWSetup.bin.exe | C:\Users\admin\AppData\Local\Temp\gwtemp\GWVPNDoctor.exe | executable | |
MD5:— | SHA256:— | |||
| 2036 | GWSetup.bin.exe | C:\Users\admin\AppData\Local\Temp\gwtemp\gwsdk.dll | executable | |
MD5:— | SHA256:— | |||
| 2036 | GWSetup.bin.exe | C:\Users\admin\AppData\Local\Temp\gwtemp\gwtrayclient.exe.cab | compressed | |
MD5:— | SHA256:— | |||
| 2036 | GWSetup.bin.exe | C:\Users\admin\AppData\Local\Temp\gwtemp\gwrealsdk.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
17
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2320 | GWVPNDoctor.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/gsrsaovsslca2018/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBRrcGT%2BanRD3C1tW3nsrKeuXC7DPwQU%2BO9%2F8s14Z6jeb48kjYjxhwMCs%2BsCDCvBVMvJE3w6GrPEqA%3D%3D | US | der | 1.41 Kb | whitelisted |
2320 | GWVPNDoctor.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/rootr3/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCDQHuXyId%2FGI71DM6hVc%3D | US | der | 1.40 Kb | whitelisted |
2320 | GWVPNDoctor.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6b3c556cf4db204c | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
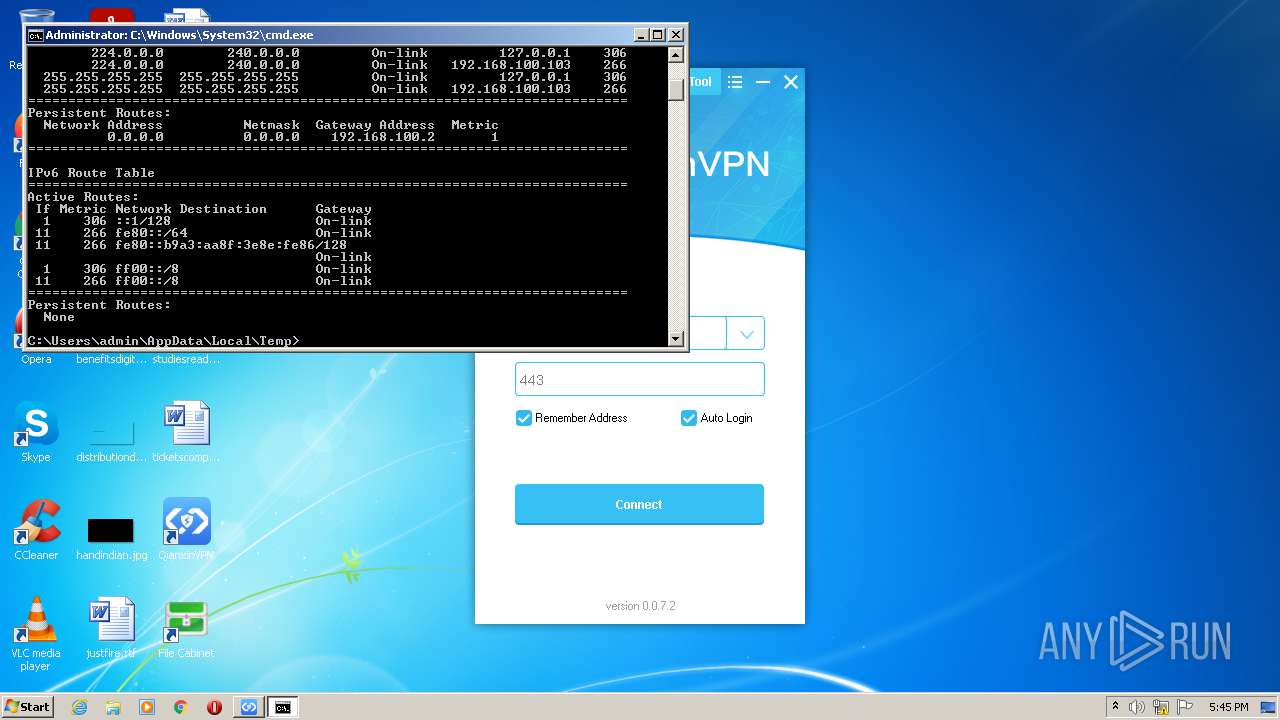
2320 | GWVPNDoctor.exe | 103.235.46.39:443 | www.baidu.com | Beijing Baidu Netcom Science and Technology Co., Ltd. | HK | unknown |
2320 | GWVPNDoctor.exe | 47.246.43.232:443 | www.taobao.com | — | US | unknown |
2320 | GWVPNDoctor.exe | 52.169.16.184:443 | www.sohu.com | Microsoft Corporation | IE | suspicious |
2320 | GWVPNDoctor.exe | 104.18.21.226:80 | ocsp2.globalsign.com | Cloudflare Inc | US | shared |
2320 | GWVPNDoctor.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
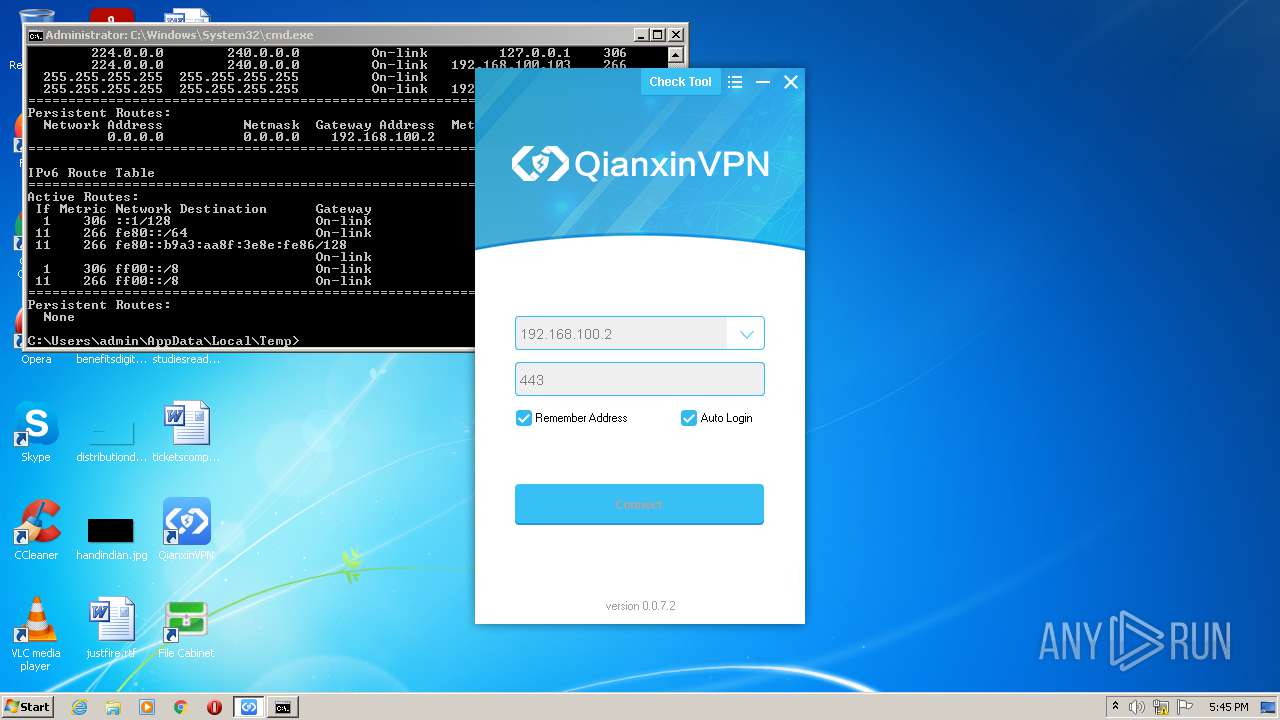
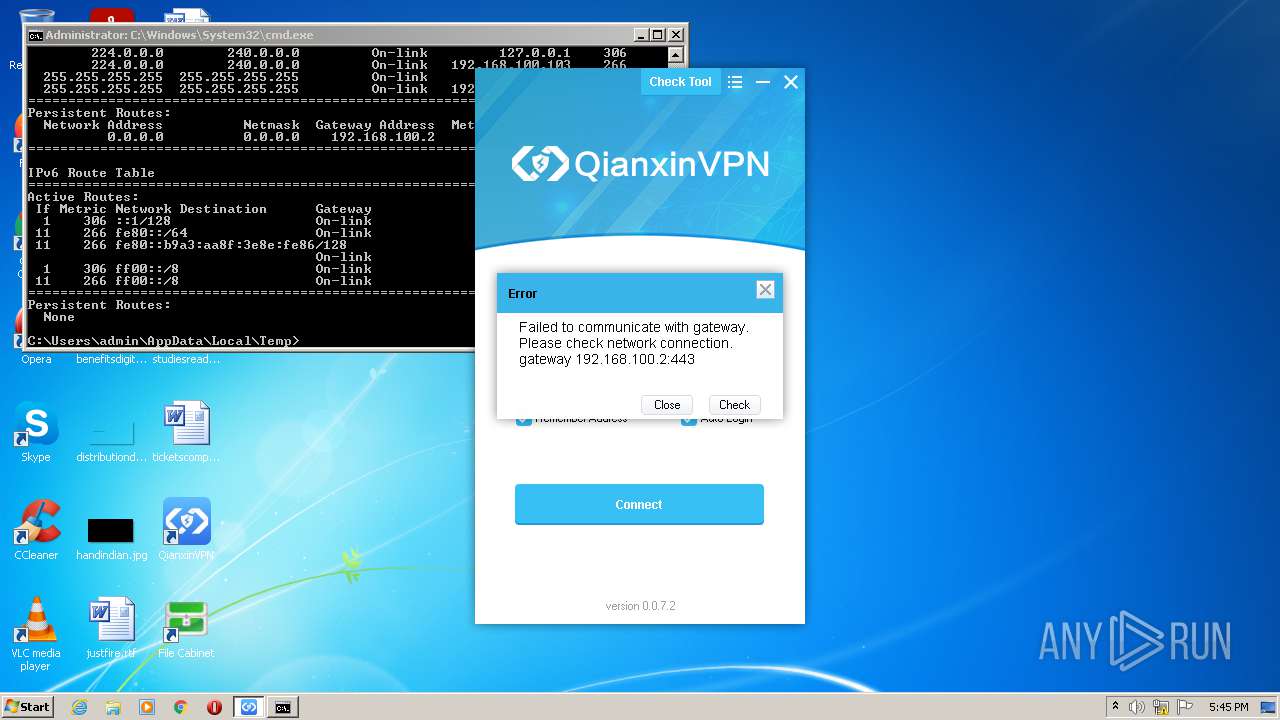
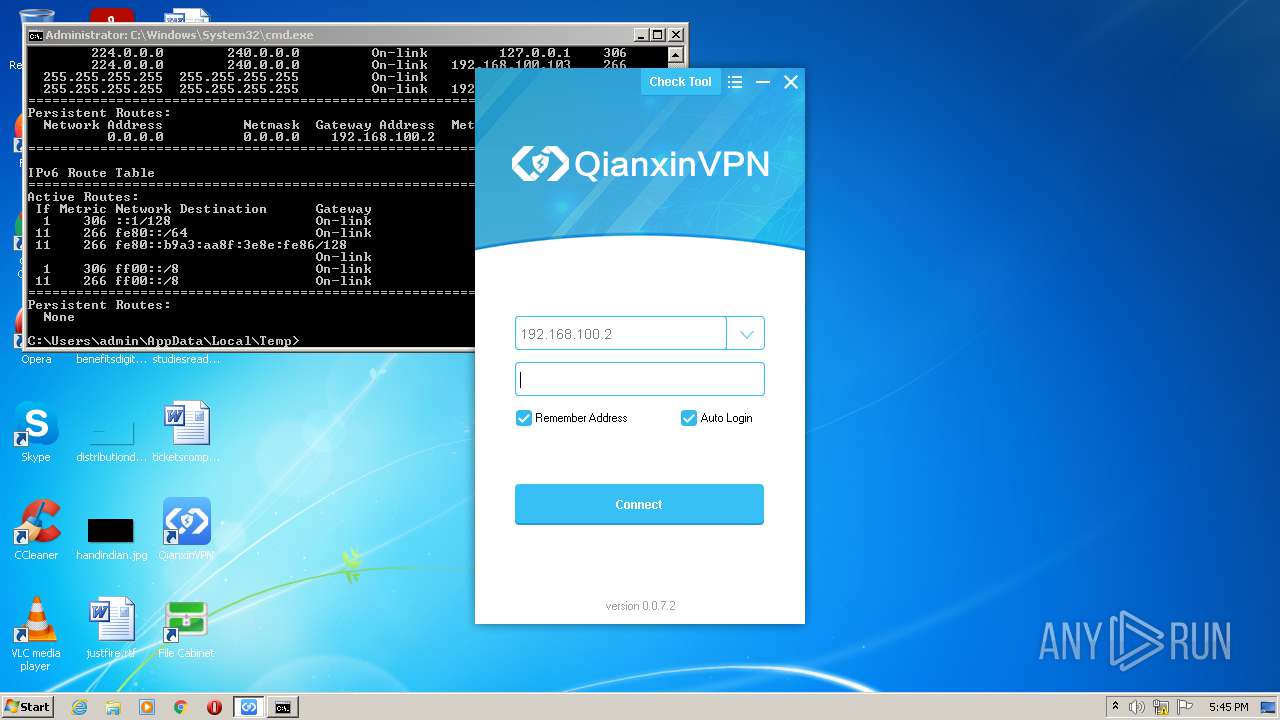
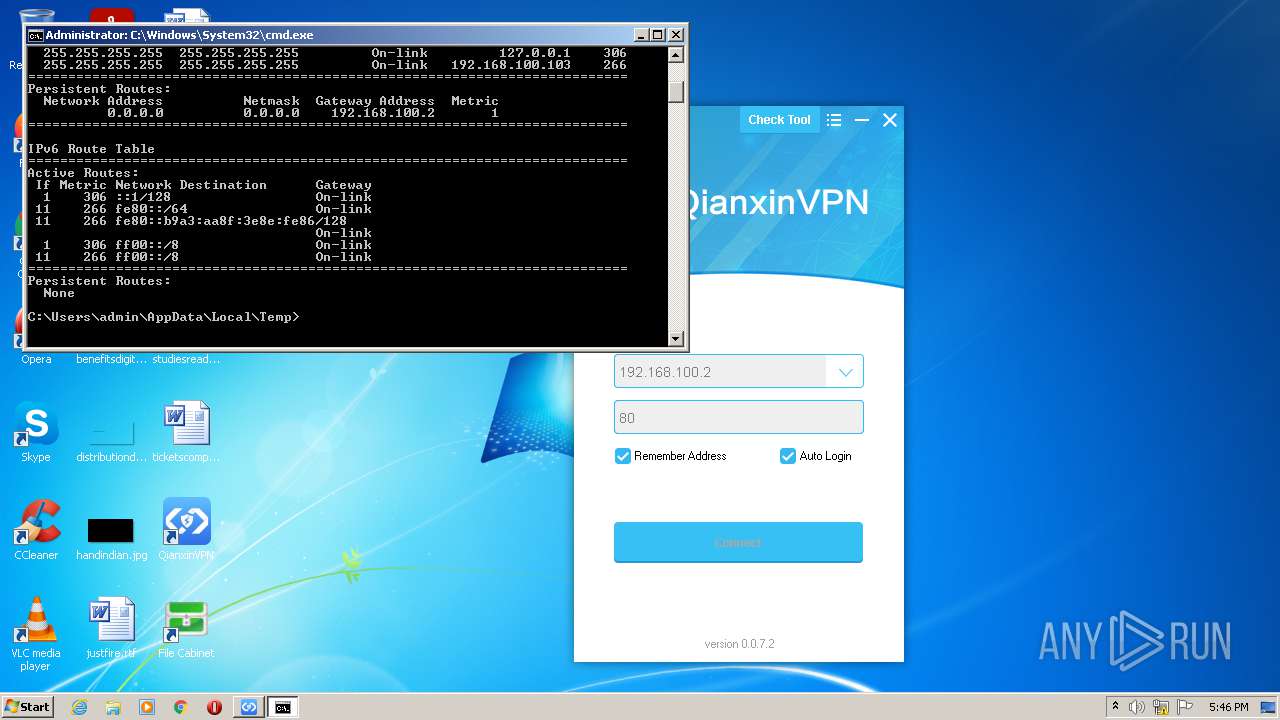
1576 | GWVPNDoctor.exe | 121.32.243.77:443 | appstore.qianxin.com | CHINANET Guangdong province network | CN | suspicious |
1576 | GWVPNDoctor.exe | 103.235.46.39:443 | www.baidu.com | Beijing Baidu Netcom Science and Technology Co., Ltd. | HK | unknown |
2320 | GWVPNDoctor.exe | 104.111.239.81:80 | www.qq.com | Akamai International B.V. | NL | unknown |
1576 | GWVPNDoctor.exe | 104.111.239.81:80 | www.qq.com | Akamai International B.V. | NL | unknown |
1576 | GWVPNDoctor.exe | 52.169.16.184:443 | www.sohu.com | Microsoft Corporation | IE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
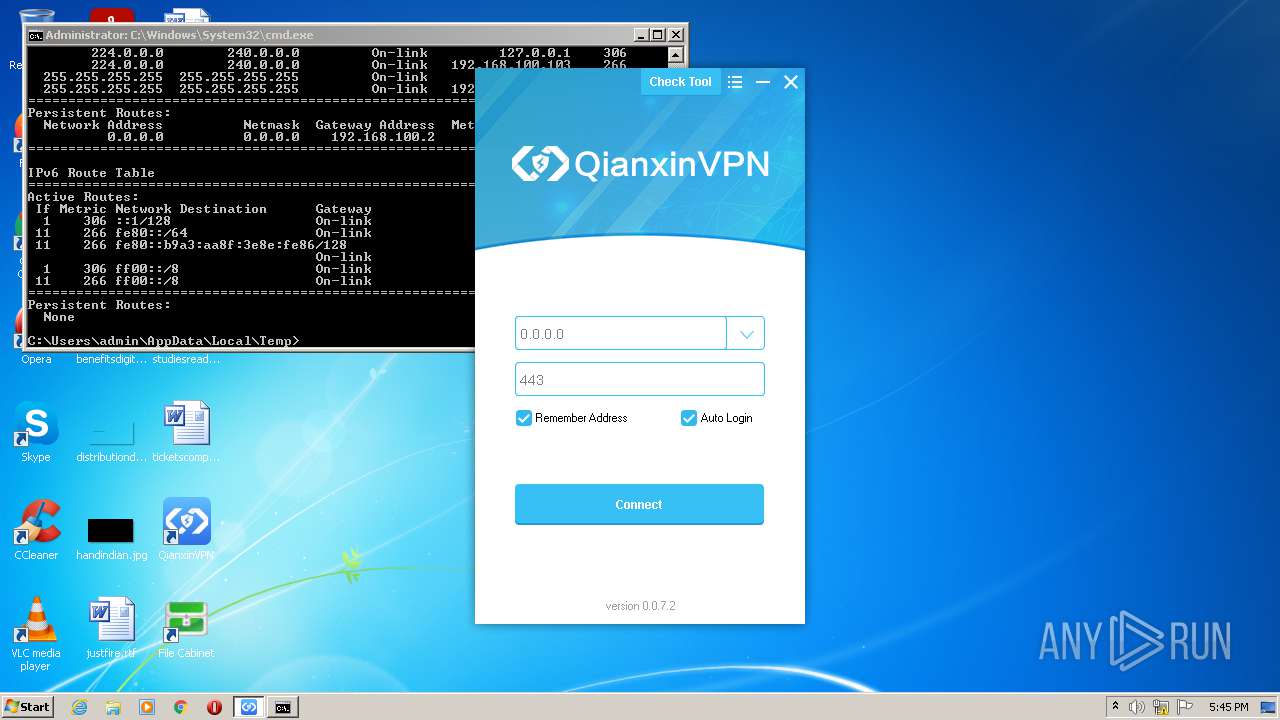
appstore.qianxin.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
www.sohu.com |
| malicious |
www.taobao.com |
| suspicious |
www.baidu.com |
| whitelisted |
www.qq.com |
| whitelisted |
Threats
Process | Message |
|---|---|
GWSetup.bin.exe | [10-28 17:44:12][INF][GWUPDLL]DLL_PROCESS_ATTACH
|
GWSetup.bin.exe | [10-28 17:44:12][INF][GWUPDLL]Load SSPI library(C:\Windows\system32\Secur32.dll).
|
GWSetup.bin.exe | [10-28 17:44:12][WAR][GWUPDLL]Name:GWVNIC10, Mask:win10, CurrentOS:win7,Filter Out!
|
GWSetup.bin.exe | [10-28 17:44:12][WAR][GWUPDLL]Name:VNICCAT10, Mask:win10, CurrentOS:win7,Filter Out!
|
GWSetup.bin.exe | [10-28 17:44:12][WAR][GWUPDLL]Name:VNICINF10, Mask:win10, CurrentOS:win7,Filter Out!
|
GWSetup.bin.exe | [10-28 17:44:12][DBG][GWUPDLL]check ver conf path:C:\Program Files\Gateway\SSLVPN\package.conf.bak
|
GWSetup.bin.exe | [10-28 17:44:12][WAR][GWUPDLL]file[C:\Program Files\Gateway\SSLVPN\package.conf.bak] md5:
|
GWSetup.bin.exe | [10-28 17:44:12][DBG][GWUPDLL]conf.bak check failed
|
GWSetup.bin.exe | VerifySign xp or win7 32 |
GWSetup.bin.exe | VerifySign xp or win7 32 |