| download: | /1.5.1/VoicemodInstaller_1.5.1-hw3sms.exe |
| Full analysis: | https://app.any.run/tasks/c6c4365d-1018-4b58-8355-2c501ba60546 |
| Verdict: | Malicious activity |
| Analysis date: | July 25, 2025, 02:39:01 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 10 sections |
| MD5: | 0EF7BAD28BD38C1EA3EF6084D18CFC62 |
| SHA1: | 7E42477CF66B8E406E15ED9BCE382DBD05166371 |
| SHA256: | 3D50CE7693B23CD3D1F05682D0FEC9958AB1329A2D01E6D6C79BDB2E6505984C |
| SSDEEP: | 98304:qbUZdqZ3FWMo0iHNEGRltHg5YZz/6Pf8FMdJDxDBwcMSdObOS/Hro1e4Kv+BG/6C:L/NTan4 |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 3948)
Changes the autorun value in the registry
- VoicemodInstaller_1.5.1-hw3sms.tmp (PID: 1300)
SUSPICIOUS
Executable content was dropped or overwritten
- VoicemodInstaller_1.5.1-hw3sms.exe (PID: 2964)
- VoicemodInstaller_1.5.1-hw3sms.exe (PID: 5432)
- VoicemodInstaller_1.5.1-hw3sms.tmp (PID: 1300)
- voicemodcon.exe (PID: 4200)
- drvinst.exe (PID: 2120)
- drvinst.exe (PID: 6756)
- Voicemod.exe (PID: 6756)
Reads security settings of Internet Explorer
- VoicemodInstaller_1.5.1-hw3sms.tmp (PID: 4444)
- voicemodcon.exe (PID: 4200)
- Voicemod.exe (PID: 6756)
- Voicemod.exe (PID: 1192)
Reads the Windows owner or organization settings
- VoicemodInstaller_1.5.1-hw3sms.tmp (PID: 1300)
Get information on the list of running processes
- VoicemodInstaller_1.5.1-hw3sms.tmp (PID: 1300)
- cmd.exe (PID: 3964)
Starts CMD.EXE for commands execution
- VoicemodInstaller_1.5.1-hw3sms.tmp (PID: 1300)
- cmd.exe (PID: 5244)
- powershell.exe (PID: 3948)
- cmd.exe (PID: 2532)
- cmd.exe (PID: 5744)
- Voicemod.exe (PID: 1192)
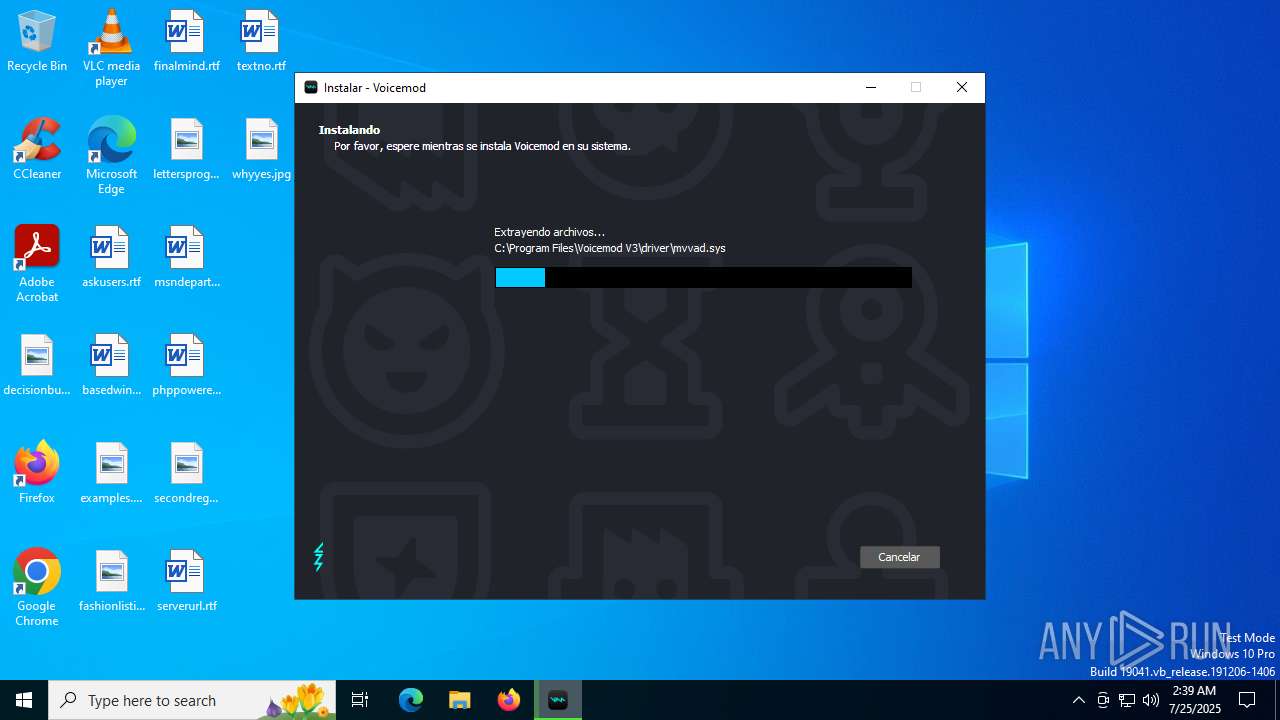
Drops a system driver (possible attempt to evade defenses)
- VoicemodInstaller_1.5.1-hw3sms.tmp (PID: 1300)
- voicemodcon.exe (PID: 4200)
- drvinst.exe (PID: 2120)
- drvinst.exe (PID: 6756)
Executing commands from a ".bat" file
- VoicemodInstaller_1.5.1-hw3sms.tmp (PID: 1300)
- powershell.exe (PID: 3948)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1564)
- cmd.exe (PID: 3160)
Application launched itself
- cmd.exe (PID: 5244)
- cmd.exe (PID: 2532)
- cmd.exe (PID: 5744)
Starts process via Powershell
- powershell.exe (PID: 3948)
Creates or modifies Windows services
- drvinst.exe (PID: 2120)
Creates files in the driver directory
- drvinst.exe (PID: 2120)
- drvinst.exe (PID: 6756)
Uses DRIVERQUERY.EXE to obtain a list of installed device drivers
- cmd.exe (PID: 1100)
- cmd.exe (PID: 72)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 1100)
- cmd.exe (PID: 72)
- cmd.exe (PID: 2064)
- cmd.exe (PID: 5644)
- cmd.exe (PID: 2492)
Uses WMIC.EXE to obtain CPU information
- cmd.exe (PID: 5644)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 2064)
Uses WMIC.EXE
- cmd.exe (PID: 2492)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 6392)
- cmd.exe (PID: 1132)
- cmd.exe (PID: 3960)
- cmd.exe (PID: 6736)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- cmd.exe (PID: 592)
- cmd.exe (PID: 5288)
Process drops legitimate windows executable
- Voicemod.exe (PID: 6756)
Uses ICACLS.EXE to modify access control lists
- Voicemod.exe (PID: 6756)
INFO
Process checks computer location settings
- VoicemodInstaller_1.5.1-hw3sms.tmp (PID: 4444)
- QtWebEngineProcess.exe (PID: 5768)
- QtWebEngineProcess.exe (PID: 4800)
- Voicemod.exe (PID: 1192)
Create files in a temporary directory
- VoicemodInstaller_1.5.1-hw3sms.exe (PID: 5432)
- VoicemodInstaller_1.5.1-hw3sms.exe (PID: 2964)
- VoicemodInstaller_1.5.1-hw3sms.tmp (PID: 1300)
- curl.exe (PID: 1488)
- curl.exe (PID: 5184)
- curl.exe (PID: 1564)
- curl.exe (PID: 1808)
- curl.exe (PID: 1568)
- curl.exe (PID: 4032)
- curl.exe (PID: 1040)
- curl.exe (PID: 6012)
- curl.exe (PID: 6540)
- AudioEndPointTool.exe (PID: 5424)
- AudioEndPointTool.exe (PID: 620)
- voicemodcon.exe (PID: 828)
- AudioEndPointTool.exe (PID: 7152)
- AudioEndPointTool.exe (PID: 2292)
- AudioEndPointTool.exe (PID: 1488)
- voicemodcon.exe (PID: 4200)
- AudioEndPointTool.exe (PID: 4644)
- AudioEndPointTool.exe (PID: 2692)
- AudioEndPointTool.exe (PID: 4032)
- AudioEndPointTool.exe (PID: 2312)
- AudioEndPointTool.exe (PID: 3788)
- AudioEndPointTool.exe (PID: 5576)
- AudioEndPointTool.exe (PID: 7052)
- curl.exe (PID: 6372)
- curl.exe (PID: 6344)
- curl.exe (PID: 3288)
- crashpad_handler.exe (PID: 6688)
- Voicemod.exe (PID: 6756)
- curl.exe (PID: 4744)
- Voicemod.exe (PID: 1192)
- crashpad_handler.exe (PID: 5540)
- curl.exe (PID: 6388)
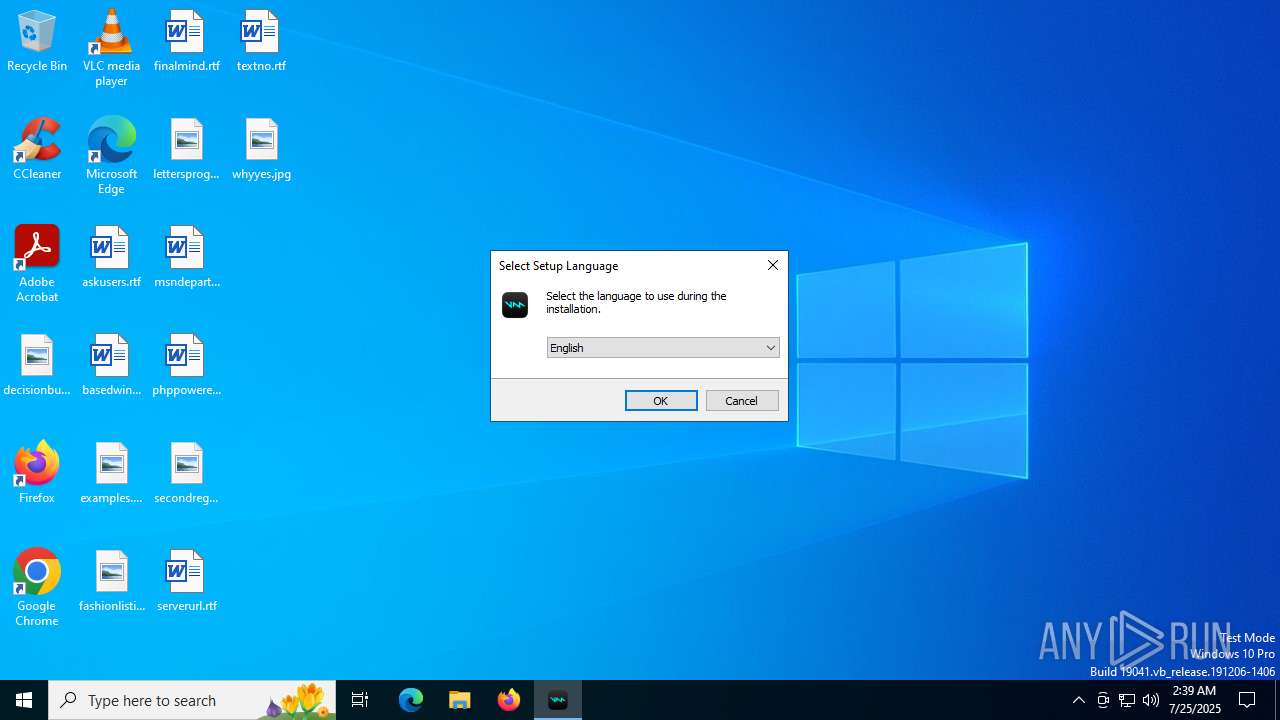
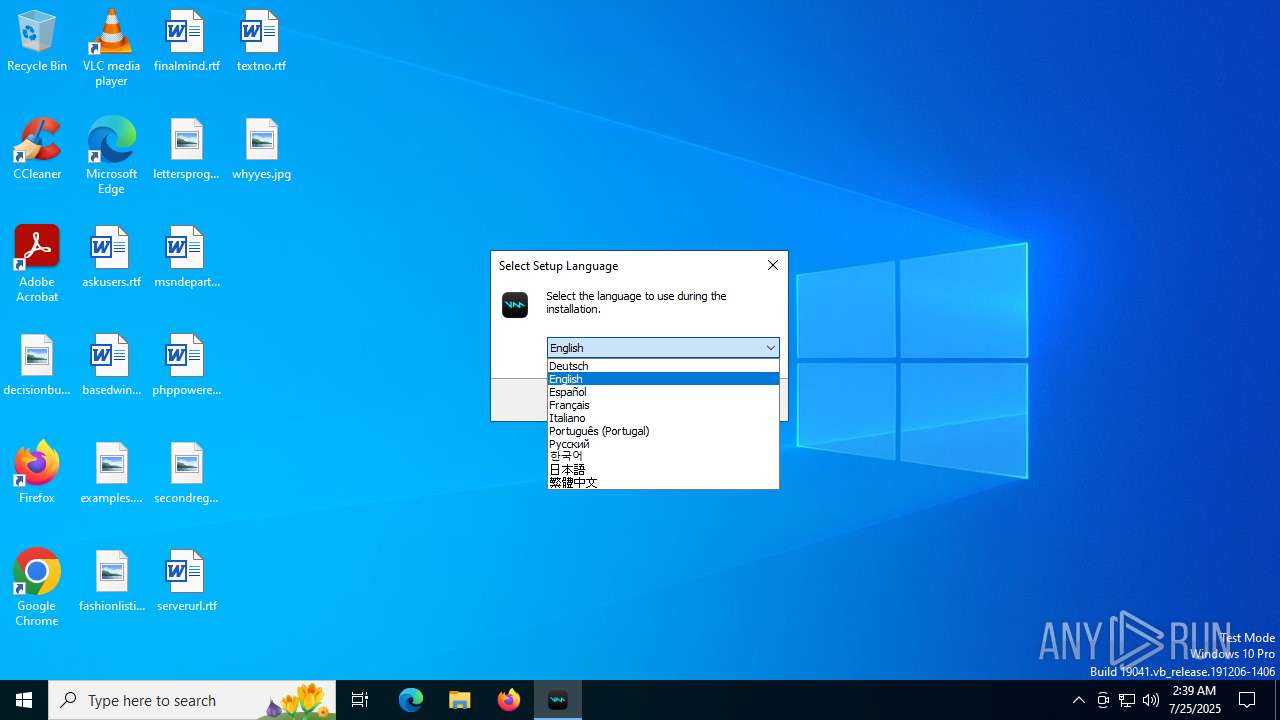
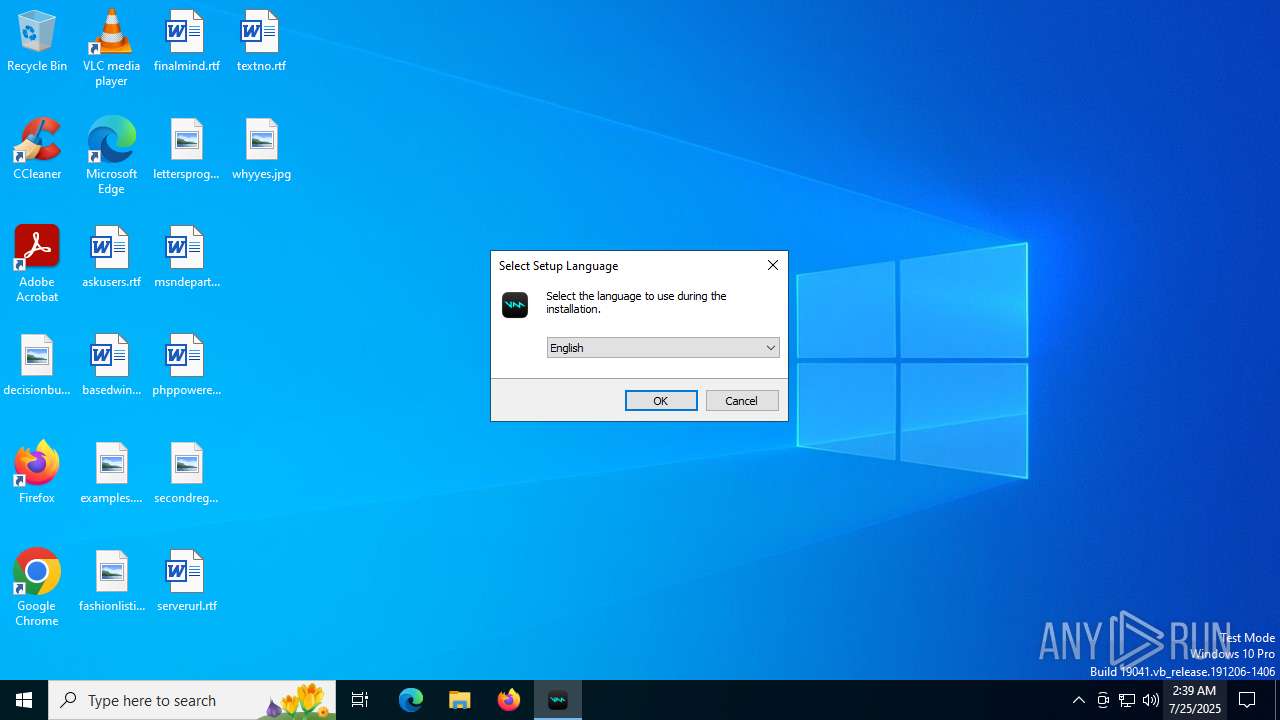
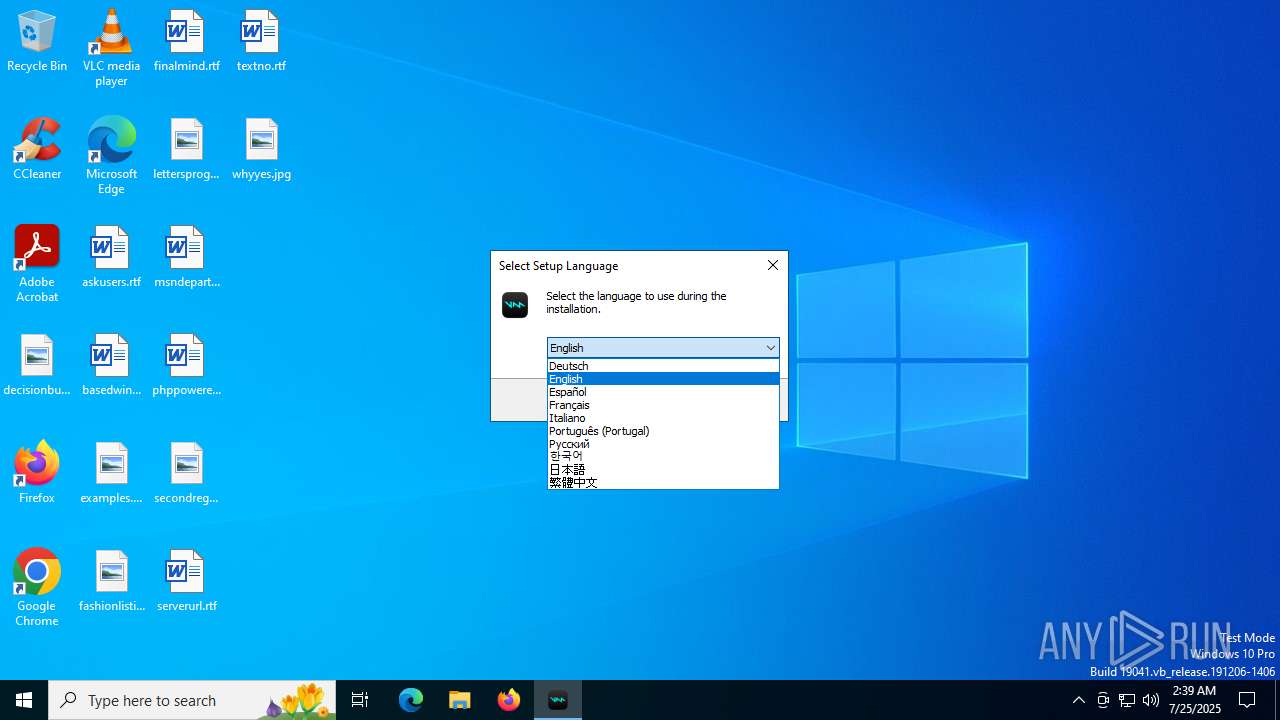
Checks supported languages
- VoicemodInstaller_1.5.1-hw3sms.exe (PID: 2964)
- VoicemodInstaller_1.5.1-hw3sms.tmp (PID: 4444)
- VoicemodInstaller_1.5.1-hw3sms.exe (PID: 5432)
- VoicemodInstaller_1.5.1-hw3sms.tmp (PID: 1300)
- curl.exe (PID: 1488)
- curl.exe (PID: 1576)
- curl.exe (PID: 5184)
- curl.exe (PID: 1564)
- curl.exe (PID: 3628)
- curl.exe (PID: 1808)
- curl.exe (PID: 3400)
- curl.exe (PID: 4032)
- curl.exe (PID: 6688)
- curl.exe (PID: 7084)
- curl.exe (PID: 1040)
- curl.exe (PID: 2596)
- curl.exe (PID: 1568)
- curl.exe (PID: 5504)
- curl.exe (PID: 6540)
- curl.exe (PID: 1636)
- curl.exe (PID: 6012)
- curl.exe (PID: 3480)
- AudioEndPointTool.exe (PID: 5424)
- AudioEndPointTool.exe (PID: 620)
- SaveDefaultDevices.exe (PID: 2276)
- AudioEndPointTool.exe (PID: 7152)
- voicemodcon.exe (PID: 828)
- AudioEndPointTool.exe (PID: 2292)
- AudioEndPointTool.exe (PID: 1488)
- voicemodcon.exe (PID: 4200)
- drvinst.exe (PID: 6756)
- drvinst.exe (PID: 2120)
- AudioEndPointTool.exe (PID: 4644)
- AudioEndPointTool.exe (PID: 5576)
- AudioEndPointTool.exe (PID: 2692)
- AudioEndPointTool.exe (PID: 2312)
- AudioEndPointTool.exe (PID: 3788)
- AudioEndPointTool.exe (PID: 4032)
- curl.exe (PID: 6372)
- curl.exe (PID: 1160)
- AudioEndPointTool.exe (PID: 7052)
- curl.exe (PID: 2120)
- curl.exe (PID: 6344)
- curl.exe (PID: 3288)
- curl.exe (PID: 3888)
- curl.exe (PID: 4744)
- curl.exe (PID: 5348)
- curl.exe (PID: 6388)
- Voicemod.exe (PID: 6756)
- crashpad_handler.exe (PID: 6688)
- crashpad_handler.exe (PID: 5540)
- Voicemod.exe (PID: 1192)
- curl.exe (PID: 4860)
- QtWebEngineProcess.exe (PID: 6364)
- QtWebEngineProcess.exe (PID: 4800)
- identity_helper.exe (PID: 7852)
- QtWebEngineProcess.exe (PID: 5768)
Reads the computer name
- VoicemodInstaller_1.5.1-hw3sms.tmp (PID: 1300)
- VoicemodInstaller_1.5.1-hw3sms.tmp (PID: 4444)
- curl.exe (PID: 1488)
- curl.exe (PID: 1576)
- curl.exe (PID: 5184)
- curl.exe (PID: 3628)
- curl.exe (PID: 1564)
- curl.exe (PID: 2596)
- curl.exe (PID: 3400)
- curl.exe (PID: 1568)
- curl.exe (PID: 6688)
- curl.exe (PID: 4032)
- curl.exe (PID: 7084)
- curl.exe (PID: 1040)
- curl.exe (PID: 1808)
- curl.exe (PID: 6012)
- curl.exe (PID: 3480)
- curl.exe (PID: 1636)
- curl.exe (PID: 5504)
- curl.exe (PID: 6540)
- AudioEndPointTool.exe (PID: 5424)
- SaveDefaultDevices.exe (PID: 2276)
- AudioEndPointTool.exe (PID: 620)
- AudioEndPointTool.exe (PID: 2292)
- AudioEndPointTool.exe (PID: 7152)
- AudioEndPointTool.exe (PID: 1488)
- voicemodcon.exe (PID: 4200)
- drvinst.exe (PID: 6756)
- drvinst.exe (PID: 2120)
- AudioEndPointTool.exe (PID: 4644)
- AudioEndPointTool.exe (PID: 2692)
- AudioEndPointTool.exe (PID: 2312)
- AudioEndPointTool.exe (PID: 4032)
- AudioEndPointTool.exe (PID: 3788)
- AudioEndPointTool.exe (PID: 5576)
- curl.exe (PID: 6372)
- AudioEndPointTool.exe (PID: 7052)
- curl.exe (PID: 6344)
- curl.exe (PID: 3288)
- curl.exe (PID: 2120)
- curl.exe (PID: 3888)
- curl.exe (PID: 1160)
- curl.exe (PID: 5348)
- Voicemod.exe (PID: 6756)
- curl.exe (PID: 6388)
- curl.exe (PID: 4744)
- Voicemod.exe (PID: 1192)
- curl.exe (PID: 4860)
- QtWebEngineProcess.exe (PID: 5768)
- QtWebEngineProcess.exe (PID: 4800)
- QtWebEngineProcess.exe (PID: 6364)
- identity_helper.exe (PID: 7852)
Detects InnoSetup installer (YARA)
- VoicemodInstaller_1.5.1-hw3sms.tmp (PID: 4444)
- VoicemodInstaller_1.5.1-hw3sms.exe (PID: 2964)
- VoicemodInstaller_1.5.1-hw3sms.tmp (PID: 1300)
- VoicemodInstaller_1.5.1-hw3sms.exe (PID: 5432)
Compiled with Borland Delphi (YARA)
- VoicemodInstaller_1.5.1-hw3sms.tmp (PID: 1300)
- VoicemodInstaller_1.5.1-hw3sms.tmp (PID: 4444)
Execution of CURL command
- VoicemodInstaller_1.5.1-hw3sms.tmp (PID: 1300)
Reads the machine GUID from the registry
- VoicemodInstaller_1.5.1-hw3sms.tmp (PID: 1300)
- voicemodcon.exe (PID: 4200)
- drvinst.exe (PID: 6756)
- Voicemod.exe (PID: 6756)
- Voicemod.exe (PID: 1192)
The sample compiled with russian language support
- VoicemodInstaller_1.5.1-hw3sms.tmp (PID: 1300)
The sample compiled with english language support
- VoicemodInstaller_1.5.1-hw3sms.tmp (PID: 1300)
- voicemodcon.exe (PID: 4200)
- drvinst.exe (PID: 2120)
- drvinst.exe (PID: 6756)
- Voicemod.exe (PID: 6756)
Creates files in the program directory
- VoicemodInstaller_1.5.1-hw3sms.tmp (PID: 1300)
- SaveDefaultDevices.exe (PID: 2276)
- cmd.exe (PID: 5244)
Creates files or folders in the user directory
- VoicemodInstaller_1.5.1-hw3sms.tmp (PID: 1300)
- Voicemod.exe (PID: 6756)
- Voicemod.exe (PID: 1192)
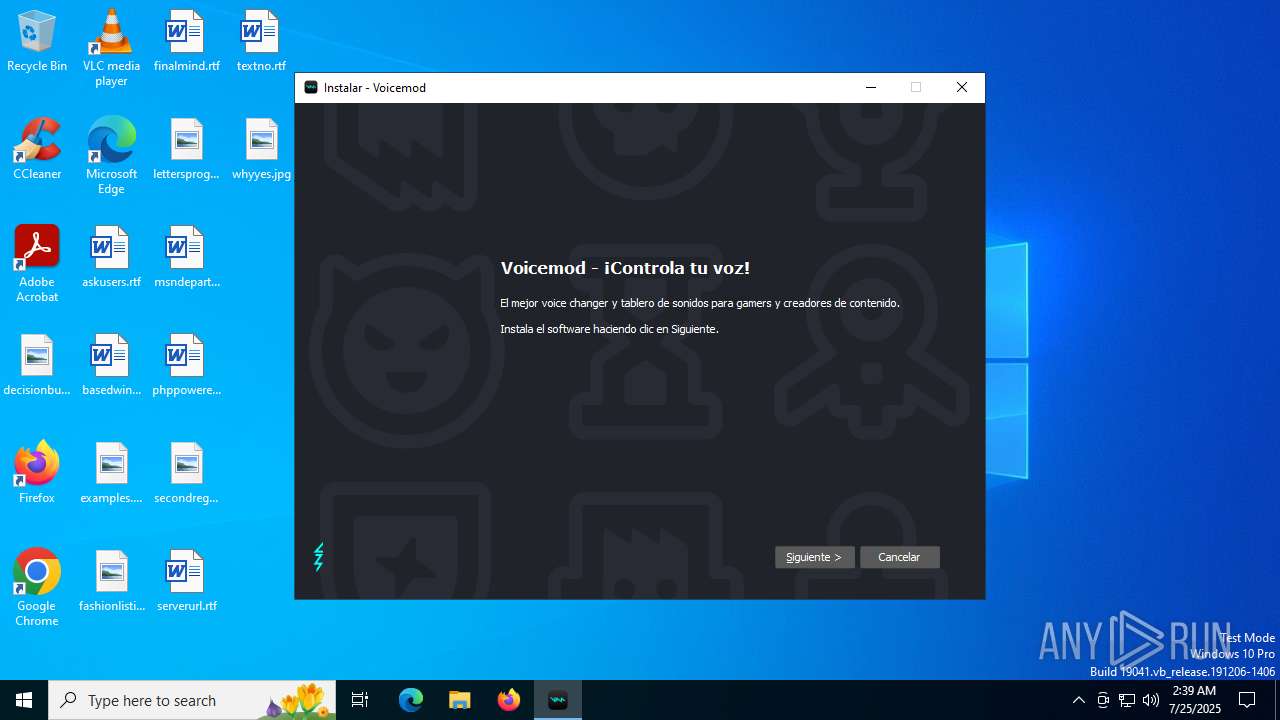
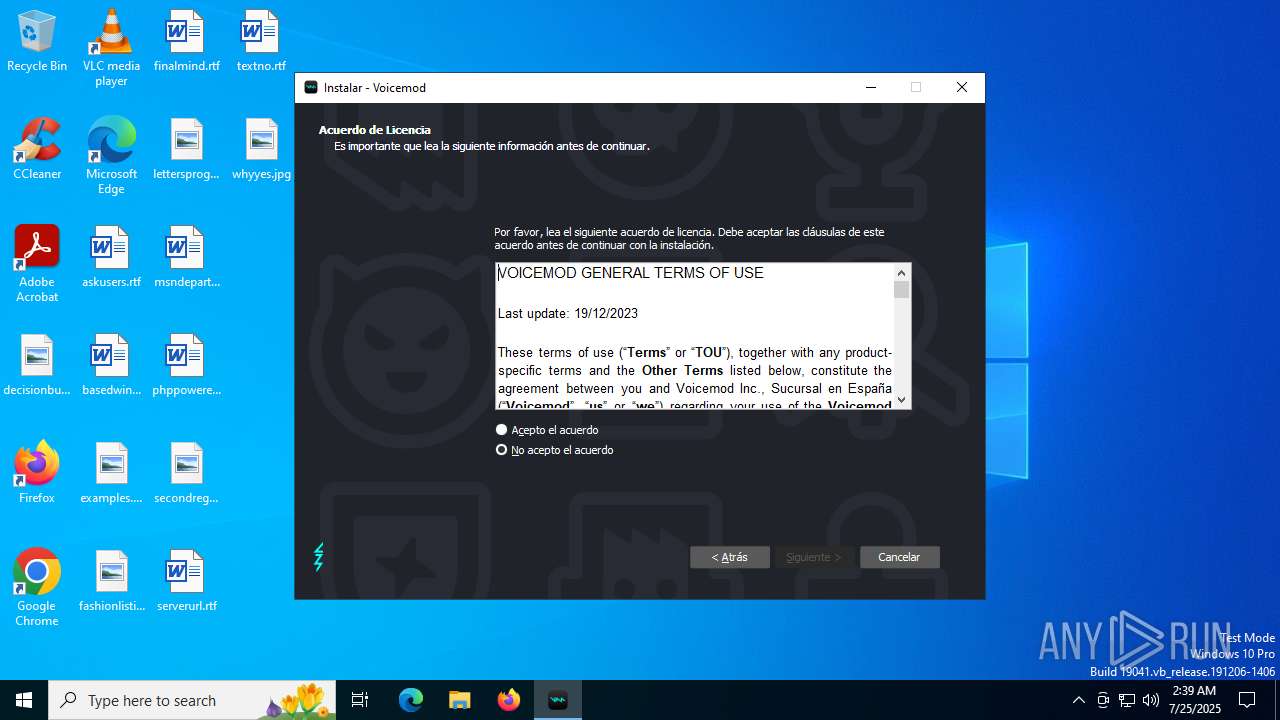
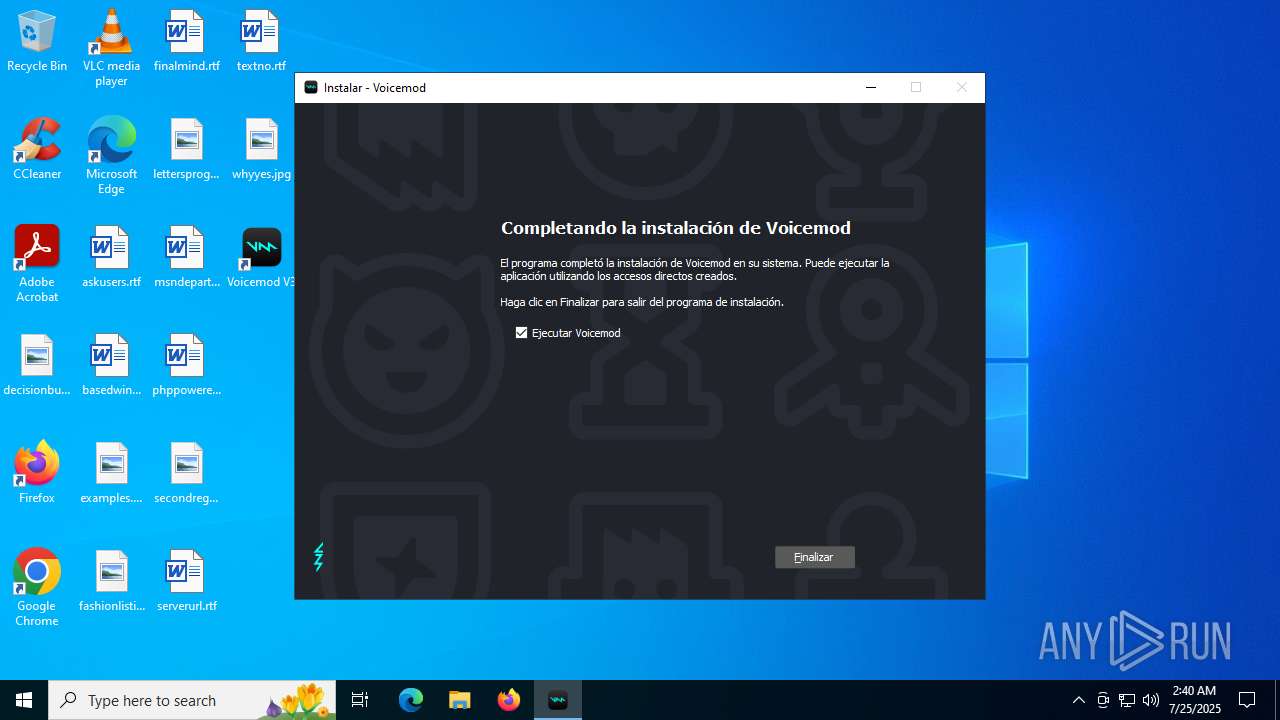
Creates a software uninstall entry
- VoicemodInstaller_1.5.1-hw3sms.tmp (PID: 1300)
Launching a file from a Registry key
- VoicemodInstaller_1.5.1-hw3sms.tmp (PID: 1300)
Reads the software policy settings
- voicemodcon.exe (PID: 4200)
- drvinst.exe (PID: 6756)
- Voicemod.exe (PID: 6756)
- Voicemod.exe (PID: 1192)
- slui.exe (PID: 4160)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 2028)
- WMIC.exe (PID: 5556)
- WMIC.exe (PID: 6400)
Checks proxy server information
- Voicemod.exe (PID: 6756)
- Voicemod.exe (PID: 1192)
- slui.exe (PID: 4160)
Reads Environment values
- Voicemod.exe (PID: 6756)
- Voicemod.exe (PID: 1192)
- identity_helper.exe (PID: 7852)
Reads CPU info
- Voicemod.exe (PID: 6756)
- Voicemod.exe (PID: 1192)
Reads the time zone
- Voicemod.exe (PID: 1192)
Application launched itself
- msedge.exe (PID: 6636)
- msedge.exe (PID: 3480)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (67.7) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (25.6) |
| .exe | | | Win32 Executable (generic) (2.7) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:11:17 06:07:00+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 682496 |
| InitializedDataSize: | 156160 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa7ed0 |
| OSVersion: | 6 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Voicemod Inc., Sucursal en España |
| FileDescription: | Voicemod Setup |
| FileVersion: | |
| LegalCopyright: | © 2025 Voicemod Inc., Sucursal en España - Version 1.5.1 |
| OriginalFileName: | |
| ProductName: | Voicemod |
| ProductVersion: | 1.5.1 |
Total processes
307
Monitored processes
164
Malicious processes
6
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 72 | "cmd.exe" /C driverquery /V /FO LIST | findstr /I "Voicemod" > "C:\Users\admin\AppData\Local\Temp\is-MVI8D.tmp\output_ansi.log" | C:\Windows\System32\cmd.exe | — | VoicemodInstaller_1.5.1-hw3sms.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2244,i,4238436932894988553,9914073003749848911,262144 --variations-seed-version --mojo-platform-channel-handle=2528 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 440 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 480 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x290,0x294,0x298,0x288,0x2a0,0x7ffc3f2ff208,0x7ffc3f2ff214,0x7ffc3f2ff220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 592 | "C:\WINDOWS\system32\cmd.exe" /C netsh advfirewall firewall delete rule name=all program="C:\Program Files\Voicemod V3\Voicemod.exe" | C:\Windows\System32\cmd.exe | — | VoicemodInstaller_1.5.1-hw3sms.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 620 | AudioEndPointTool.exe get --name Voicemod --flow Render --format Raw --fields ID | C:\Program Files\Voicemod V3\driver\AudioEndPointTool.exe | — | cmd.exe | |||||||||||
User: admin Company: Voicemod Inc. Integrity Level: HIGH Description: Voicemod tools Exit code: 13 Modules
| |||||||||||||||
| 828 | voicemodcon.exe dp_enum | C:\Program Files\Voicemod V3\driver\voicemodcon.exe | — | cmd.exe | |||||||||||
User: admin Company: Windows (R) Win 7 DDK provider Integrity Level: HIGH Description: Windows Setup API Exit code: 0 Version: 10.0.10011.16384 Modules
| |||||||||||||||
| 864 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | icacls.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1040 | "C:\WINDOWS\system32\curl.exe" https://api.voicemod.net/ip -H "Content-Type: application/json" -o "C:\Users\admin\AppData\Local\Temp\\ipaddress.info" | C:\Windows\System32\curl.exe | VoicemodInstaller_1.5.1-hw3sms.tmp | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: HIGH Description: The curl executable Exit code: 0 Version: 8.4.0 Modules
| |||||||||||||||
| 1100 | "cmd.exe" /C driverquery /V /FO LIST | findstr /I "Voicemod" > "C:\Users\admin\AppData\Local\Temp\is-MVI8D.tmp\output_ansi.log" | C:\Windows\System32\cmd.exe | — | VoicemodInstaller_1.5.1-hw3sms.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
53 490
Read events
52 810
Write events
673
Delete events
7
Modification events
| (PID) Process: | (1300) VoicemodInstaller_1.5.1-hw3sms.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Voicemod\Voicemod V3 |
| Operation: | write | Name: | DownloadId |
Value: hw3sms | |||
| (PID) Process: | (1300) VoicemodInstaller_1.5.1-hw3sms.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Voicemod V3 |
| Operation: | write | Name: | TermsAcceptedDate |
Value: 2025/07/25 | |||
| (PID) Process: | (1300) VoicemodInstaller_1.5.1-hw3sms.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | VoicemodV3 |
Value: "C:\Program Files\Voicemod V3\Voicemod.exe" --boot | |||
| (PID) Process: | (1300) VoicemodInstaller_1.5.1-hw3sms.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Voicemod\Voicemod V3 |
| Operation: | write | Name: | InstallPath |
Value: C:\Program Files\Voicemod V3 | |||
| (PID) Process: | (1300) VoicemodInstaller_1.5.1-hw3sms.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Voicemod\Voicemod V3 |
| Operation: | write | Name: | Language |
Value: es | |||
| (PID) Process: | (1300) VoicemodInstaller_1.5.1-hw3sms.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\voicemod |
| Operation: | write | Name: | URL Protocol |
Value: | |||
| (PID) Process: | (1300) VoicemodInstaller_1.5.1-hw3sms.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{FE519A29-8B15-47C4-BCD6-A513277DC26F}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.0.3 (u) | |||
| (PID) Process: | (1300) VoicemodInstaller_1.5.1-hw3sms.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{FE519A29-8B15-47C4-BCD6-A513277DC26F}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\Voicemod V3 | |||
| (PID) Process: | (1300) VoicemodInstaller_1.5.1-hw3sms.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{FE519A29-8B15-47C4-BCD6-A513277DC26F}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\Voicemod V3\ | |||
| (PID) Process: | (1300) VoicemodInstaller_1.5.1-hw3sms.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{FE519A29-8B15-47C4-BCD6-A513277DC26F}_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: Voicemod V3 | |||
Executable files
86
Suspicious files
258
Text files
128
Unknown types
157
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1300 | VoicemodInstaller_1.5.1-hw3sms.tmp | C:\Users\admin\AppData\Local\Temp\is-MVI8D.tmp\mvvad.inf | ini | |
MD5:4BE77F8AFECFC2B935017E2B6C231E0F | SHA256:F89D88D74C7EFECBAFB48F88511E9ADF56856A45571CB66D77DE5494D0A19627 | |||
| 5432 | VoicemodInstaller_1.5.1-hw3sms.exe | C:\Users\admin\AppData\Local\Temp\is-JC84P.tmp\VoicemodInstaller_1.5.1-hw3sms.tmp | executable | |
MD5:433EE170B047E619E2990F43555FAE14 | SHA256:090CFF6129D0BBA6703FE88F1BADADF45E7F3E08E4FB4E24FCCB8CD535AB5620 | |||
| 1300 | VoicemodInstaller_1.5.1-hw3sms.tmp | C:\Users\admin\AppData\Local\Temp\is-MVI8D.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 1300 | VoicemodInstaller_1.5.1-hw3sms.tmp | C:\Users\admin\AppData\Local\Temp\is-MVI8D.tmp\bg-top.png | image | |
MD5:220FE6E00519A633D9AD7D1D50ADC4C7 | SHA256:BDC753B2B19EE8B573B8E676F18DAE42494B99B6BD738194DCDD67F244085F36 | |||
| 1300 | VoicemodInstaller_1.5.1-hw3sms.tmp | C:\Program Files\Voicemod V3\driver\mvvad.cat | cat | |
MD5:EF5A41F3D1570201C78C08B0112E175F | SHA256:F1A44FF4D1D73952A68547E697A3B9AB3E48809B53F1B1A199DE5103B7C49AA7 | |||
| 1300 | VoicemodInstaller_1.5.1-hw3sms.tmp | C:\Users\admin\AppData\Local\Temp\is-MVI8D.tmp\bg-inner.png | image | |
MD5:A034EEAF19BB82B2AE63F4FA10C26476 | SHA256:8FE4A3F95D5309E692C4142F460BEBE4E4E24844F5A2071D466BD964C5D04DCF | |||
| 1300 | VoicemodInstaller_1.5.1-hw3sms.tmp | C:\Program Files\Voicemod V3\unins000.exe | executable | |
MD5:433EE170B047E619E2990F43555FAE14 | SHA256:090CFF6129D0BBA6703FE88F1BADADF45E7F3E08E4FB4E24FCCB8CD535AB5620 | |||
| 1300 | VoicemodInstaller_1.5.1-hw3sms.tmp | C:\Users\admin\AppData\Local\Temp\is-MVI8D.tmp\bg-bottom.png | image | |
MD5:3ADA9688E90538E60978FB6EE09041FE | SHA256:FF17916663AF2E4B08DEF48861EB38E8CD2AB4E4317E64DDAB205803C9BDFAD8 | |||
| 1300 | VoicemodInstaller_1.5.1-hw3sms.tmp | C:\Program Files\Voicemod V3\driver\is-3HB6I.tmp | executable | |
MD5:EDD104527F5F56C8F890ABD915BB636C | SHA256:BA6C3BBB1BFFC04409983F4EAAFF103F8F9F8E044F35A0589F969113BBDB96DE | |||
| 1300 | VoicemodInstaller_1.5.1-hw3sms.tmp | C:\Program Files\Voicemod V3\is-JV020.tmp | executable | |
MD5:433EE170B047E619E2990F43555FAE14 | SHA256:090CFF6129D0BBA6703FE88F1BADADF45E7F3E08E4FB4E24FCCB8CD535AB5620 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
139
DNS requests
89
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1044 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.55.110.211:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7016 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7016 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
764 | lsass.exe | GET | 200 | 104.18.21.213:80 | http://r11.c.lencr.org/16.crl | unknown | — | — | whitelisted |
764 | lsass.exe | GET | 200 | 92.204.85.1:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | unknown | — | — | whitelisted |
764 | lsass.exe | GET | 200 | 92.204.85.1:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | unknown | — | — | whitelisted |
764 | lsass.exe | GET | 200 | 92.204.85.1:80 | http://ocsp.godaddy.com//MEowSDBGMEQwQjAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCQC5WUWZ6L4kTw%3D%3D | unknown | — | — | whitelisted |
6756 | Voicemod.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1636 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1044 | svchost.exe | 40.126.32.76:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1044 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 23.55.110.211:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
api.voicemod.net |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
— | — | Potential Corporate Privacy Violation | ET INFO Outgoing Basic Auth Base64 HTTP Password detected unencrypted |
188 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
188 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
188 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
188 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
188 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
188 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
188 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
188 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
Process | Message |
|---|---|
Voicemod.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|