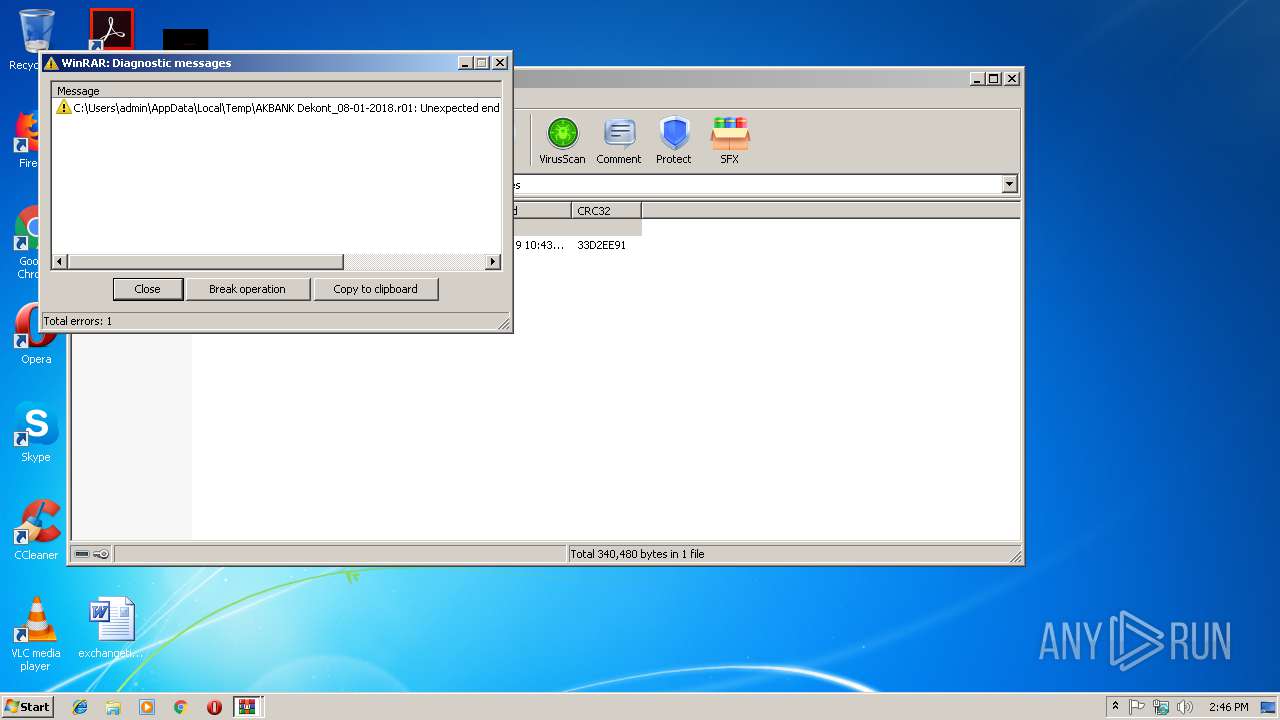
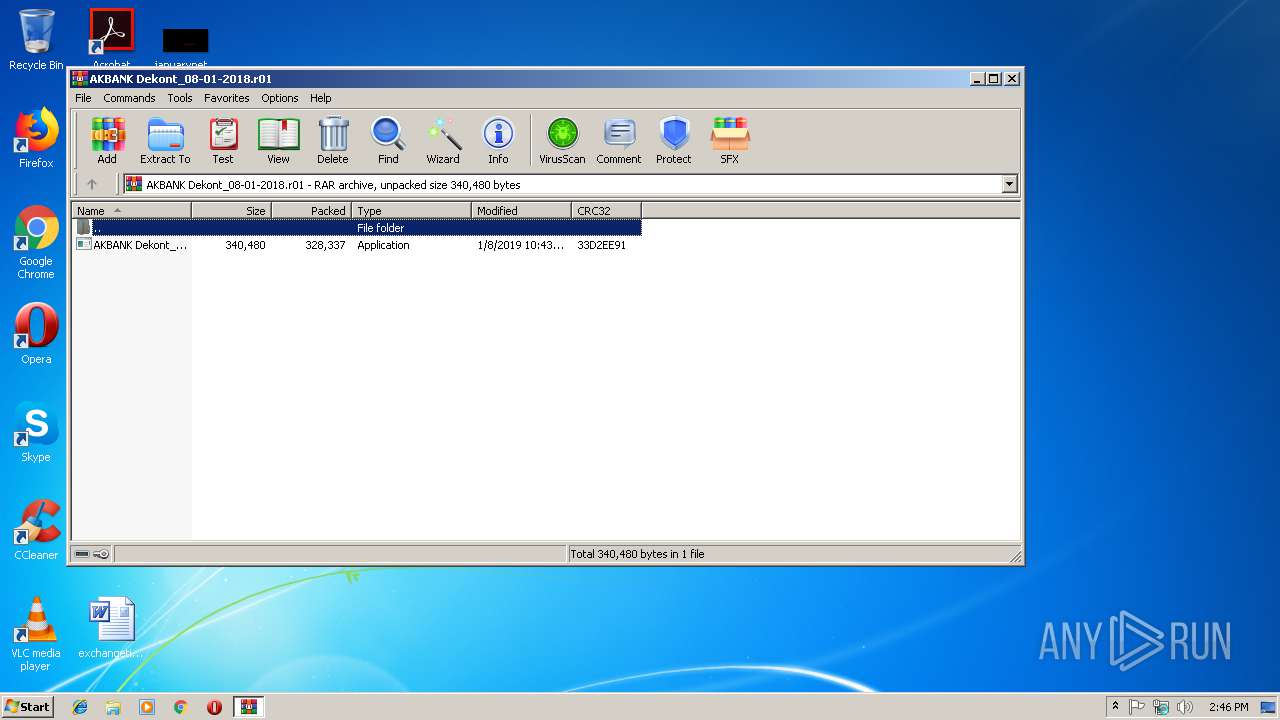
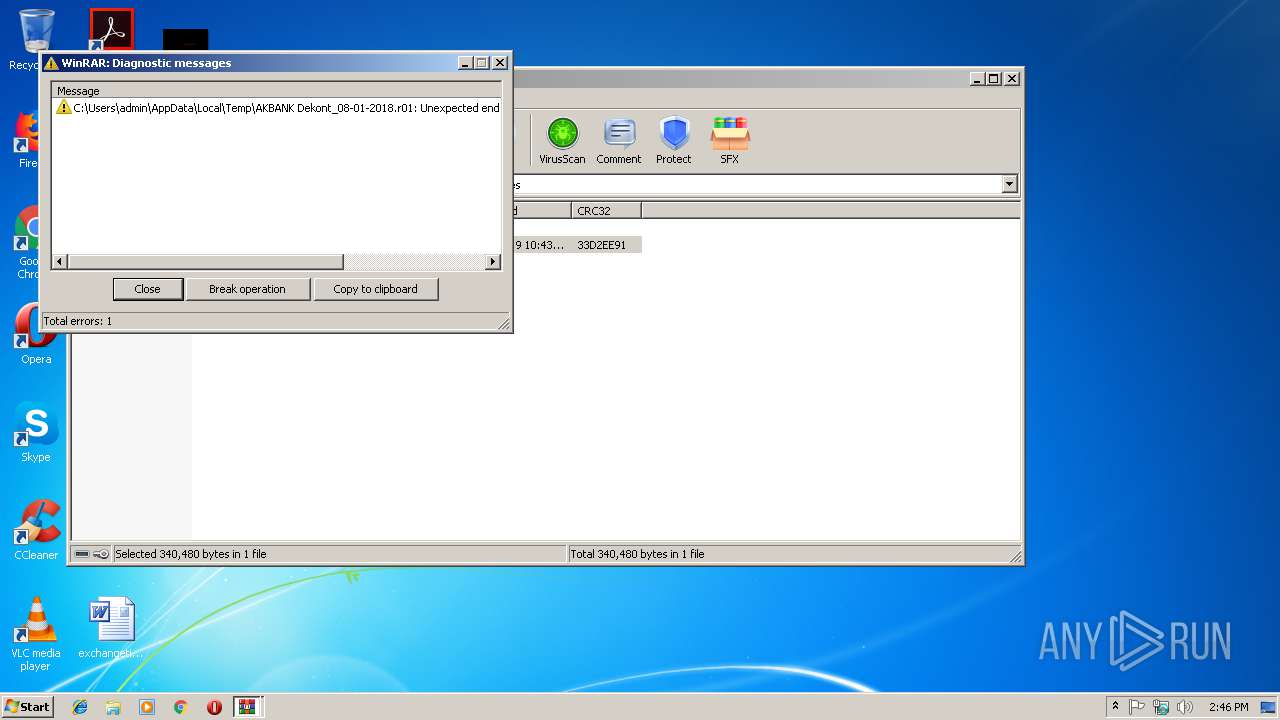
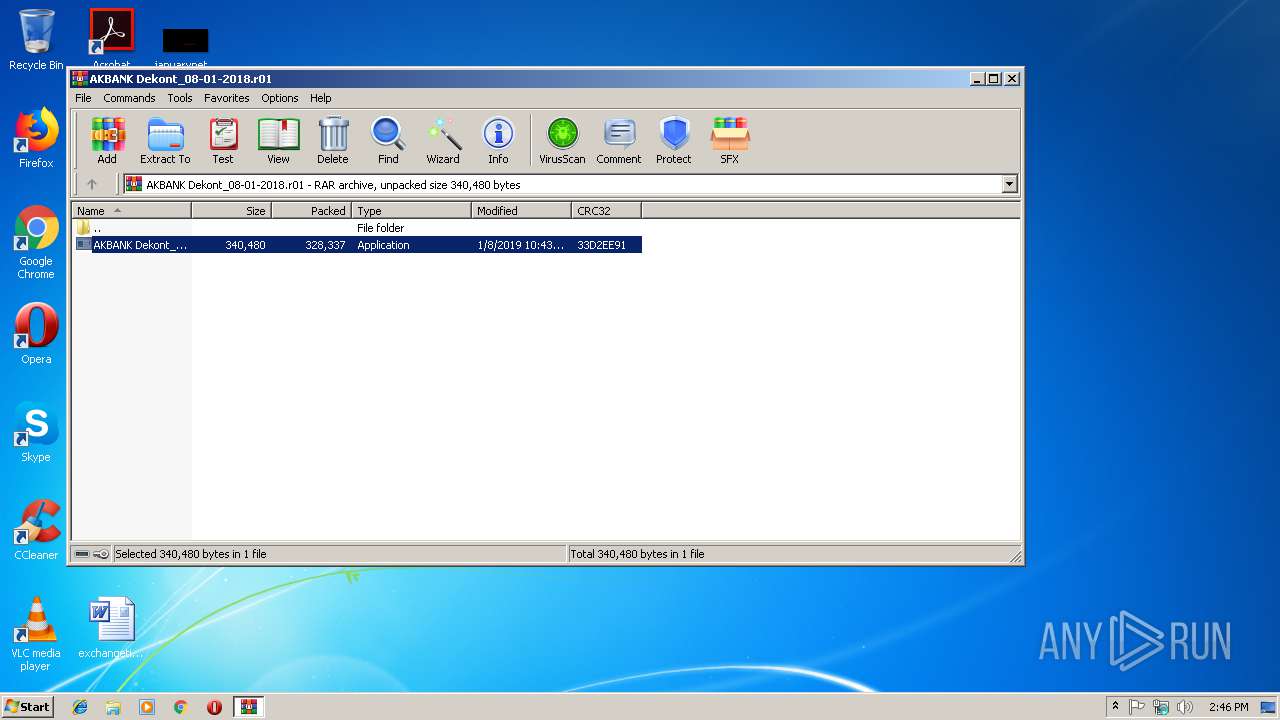
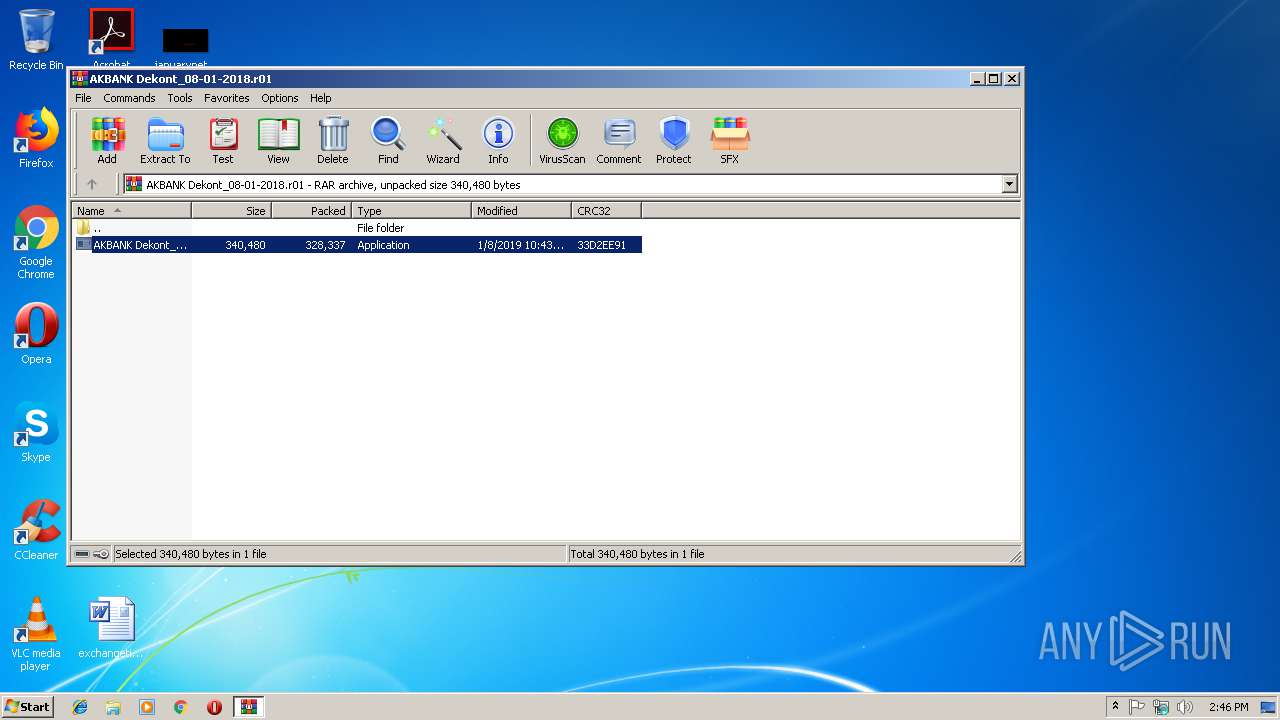
| File name: | AKBANK Dekont_08-01-2018.r01 |
| Full analysis: | https://app.any.run/tasks/3fd29956-65c4-4899-85c5-60b820a9dc51 |
| Verdict: | Malicious activity |
| Analysis date: | January 10, 2019, 14:45:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 06BE47007C2254846CE6CF87D21EAD70 |
| SHA1: | 7069F53D68B2AE2AB6F7321376E487059F5BAFCF |
| SHA256: | 3D4E4384088076FED1A9729473B194C979596B44292CF8AEAB4C1A57719CDC04 |
| SSDEEP: | 6144:B0ROlc6H0UqfWqZBLeinCC7m5ehJEpErj6hLPRv6n/34Khg1nWve:g6UUqfWinb7PhGCj6Py/o1Wve |
MALICIOUS
Application was dropped or rewritten from another process
- AKBANK Dekont_08-01-2018.exe (PID: 3612)
- AKBANK Dekont_08-01-2018.exe (PID: 2948)
- AKBANK Dekont_08-01-2018.exe (PID: 3444)
- AKBANK Dekont_08-01-2018.exe (PID: 4004)
- AKBANK Dekont_08-01-2018.exe (PID: 2912)
- CASH.exe (PID: 1520)
- AKBANK Dekont_08-01-2018.exe (PID: 3012)
- CASH.exe (PID: 3268)
Known privilege escalation attack
- AKBANK Dekont_08-01-2018.exe (PID: 3612)
- AKBANK Dekont_08-01-2018.exe (PID: 3012)
Changes the autorun value in the registry
- AKBANK Dekont_08-01-2018.exe (PID: 2912)
- AKBANK Dekont_08-01-2018.exe (PID: 3012)
SUSPICIOUS
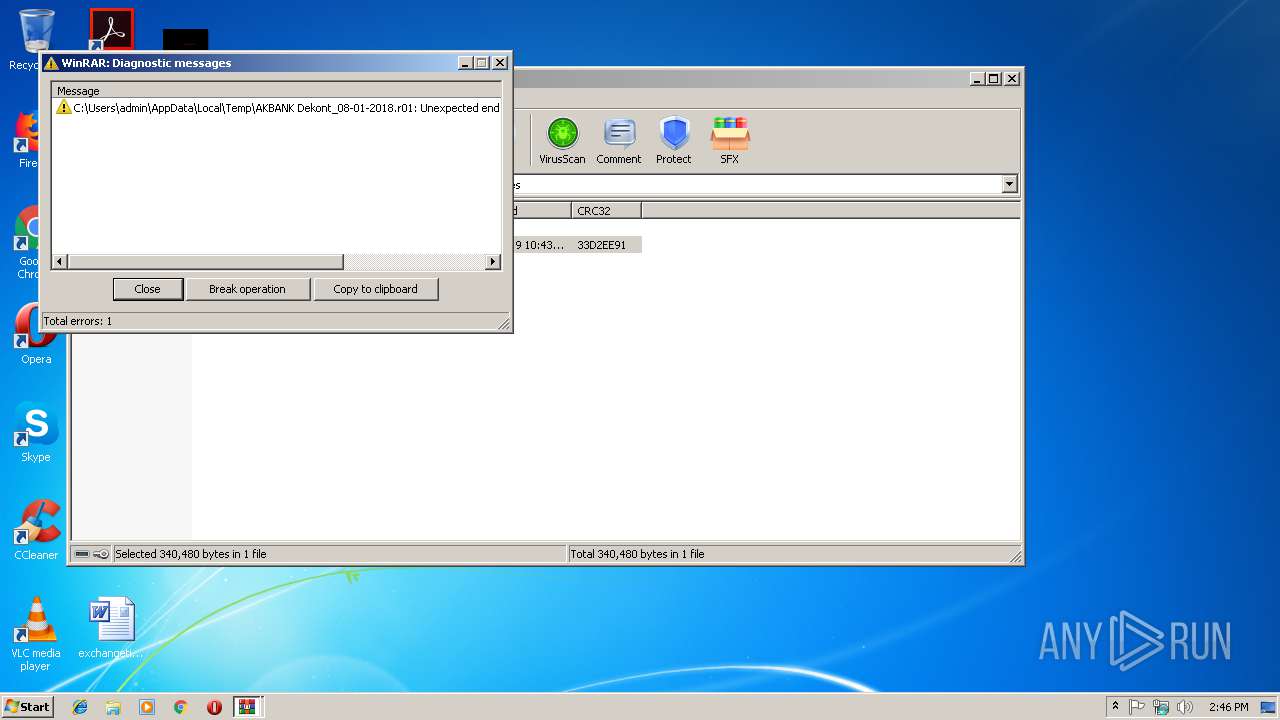
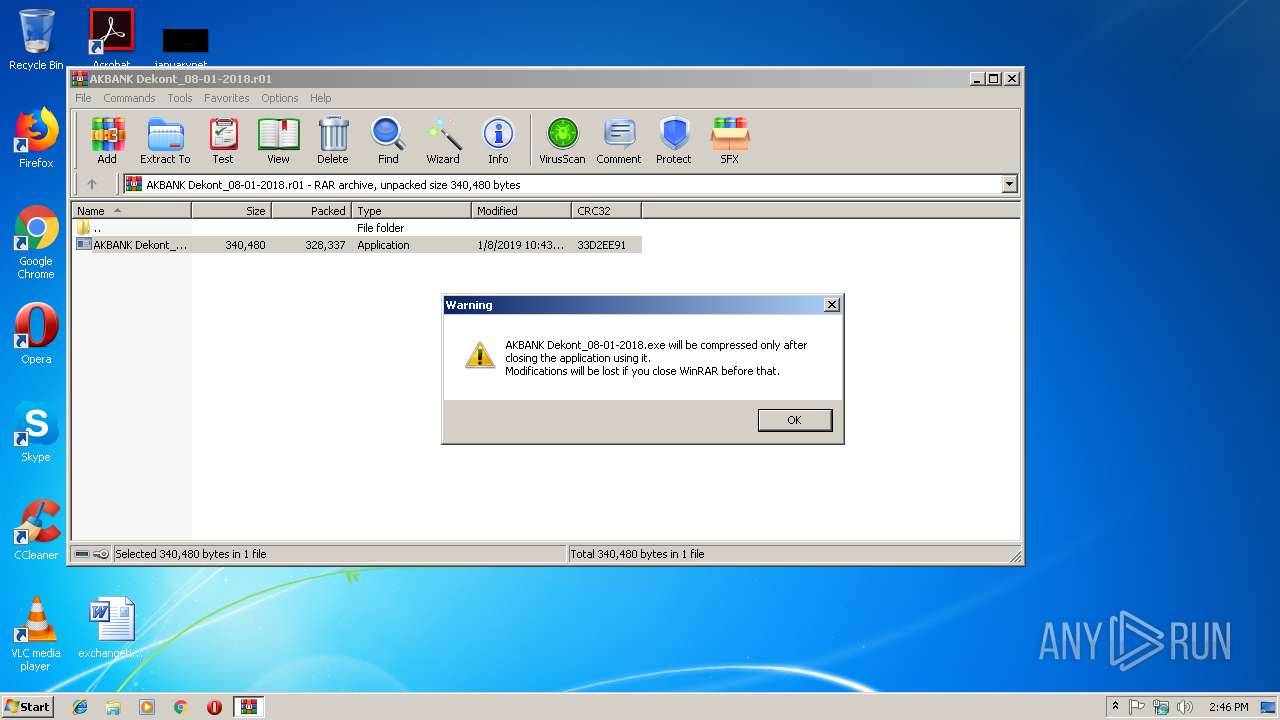
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3488)
- AKBANK Dekont_08-01-2018.exe (PID: 2912)
Modifies the open verb of a shell class
- AKBANK Dekont_08-01-2018.exe (PID: 3612)
- AKBANK Dekont_08-01-2018.exe (PID: 3012)
Application launched itself
- AKBANK Dekont_08-01-2018.exe (PID: 3444)
- AKBANK Dekont_08-01-2018.exe (PID: 2948)
- AKBANK Dekont_08-01-2018.exe (PID: 4004)
- CASH.exe (PID: 1520)
Creates files in the user directory
- AKBANK Dekont_08-01-2018.exe (PID: 2912)
Executes scripts
- AKBANK Dekont_08-01-2018.exe (PID: 2912)
- AKBANK Dekont_08-01-2018.exe (PID: 3012)
Starts CMD.EXE for commands execution
- WScript.exe (PID: 4020)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
47
Monitored processes
14
Malicious processes
8
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1520 | C:\Users\admin\AppData\Roaming\remcos\CASH.exe | C:\Users\admin\AppData\Roaming\remcos\CASH.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2416 | "C:\Windows\System32\eventvwr.exe" | C:\Windows\System32\eventvwr.exe | — | AKBANK Dekont_08-01-2018.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Event Viewer Snapin Launcher Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2772 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\install.vbs" | C:\Windows\System32\WScript.exe | — | AKBANK Dekont_08-01-2018.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2912 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3488.9889\AKBANK Dekont_08-01-2018.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3488.9889\AKBANK Dekont_08-01-2018.exe | AKBANK Dekont_08-01-2018.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2948 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3488.9889\AKBANK Dekont_08-01-2018.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3488.9889\AKBANK Dekont_08-01-2018.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3012 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3488.8861\AKBANK Dekont_08-01-2018.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3488.8861\AKBANK Dekont_08-01-2018.exe | AKBANK Dekont_08-01-2018.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3236 | "C:\Windows\System32\eventvwr.exe" | C:\Windows\System32\eventvwr.exe | AKBANK Dekont_08-01-2018.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Event Viewer Snapin Launcher Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3268 | C:\Users\admin\AppData\Roaming\remcos\CASH.exe | C:\Users\admin\AppData\Roaming\remcos\CASH.exe | — | CASH.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 3420 | "C:\Windows\System32\cmd.exe" /c "C:\Users\admin\AppData\Roaming\remcos\CASH.exe" | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3444 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3488.8861\AKBANK Dekont_08-01-2018.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3488.8861\AKBANK Dekont_08-01-2018.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 288
Read events
1 250
Write events
37
Delete events
1
Modification events
| (PID) Process: | (3488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3488) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\AKBANK Dekont_08-01-2018.r01 | |||
| (PID) Process: | (3488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
3
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2912 | AKBANK Dekont_08-01-2018.exe | C:\Users\admin\AppData\Local\Temp\install.vbs | binary | |
MD5:— | SHA256:— | |||
| 3488 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3488.9889\AKBANK Dekont_08-01-2018.exe | executable | |
MD5:— | SHA256:— | |||
| 3012 | AKBANK Dekont_08-01-2018.exe | C:\Users\admin\AppData\Local\Temp\install.vbs | binary | |
MD5:— | SHA256:— | |||
| 3488 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3488.8861\AKBANK Dekont_08-01-2018.exe | executable | |
MD5:— | SHA256:— | |||
| 2912 | AKBANK Dekont_08-01-2018.exe | C:\Users\admin\AppData\Roaming\remcos\CASH.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report