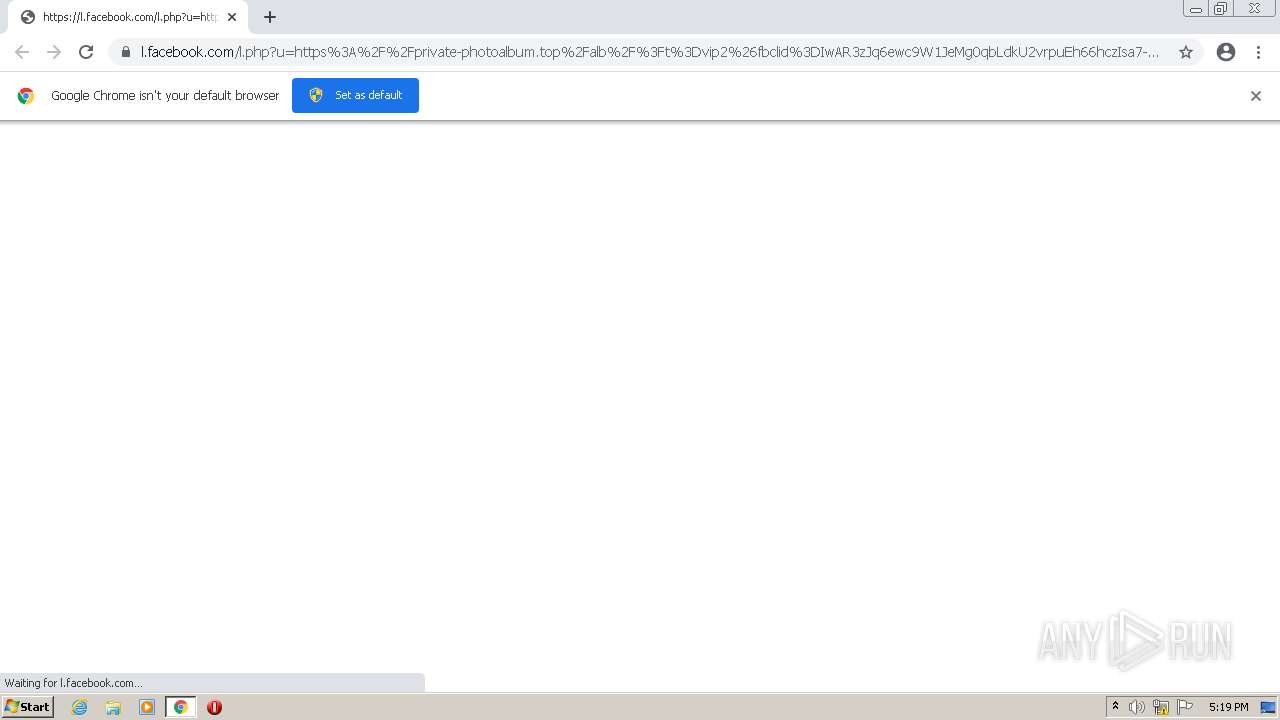
| URL: | https://l.facebook.com/l.php?u=https%3A%2F%2Fprivate-photoalbum.top%2Falb%2F%3Ft%3Dvip2%26fbclid%3DIwAR3zJq6ewc9W1JeMg0qbLdkU2vrpuEh66hczIsa7-g5Utw7Y3GlBTCBiM5E&h=AT0vvf5HGH2czwRIswDcneyCzY0TD8j3BpIBq_NdYYXrlmyE5m-56KQYrANsSmRCoiwtI-Cp1vEVyQzuOpm7NcC6G2N7FScjCafyKY9WvFsffoCqo1ypQly6AgK4g8YXtO_2u-_mwW0I5FRyI_s&__tn__=H-R&c[0]=AT1z_XPiAz6I0vsCLmU4RLWEiPI39CfP8_jMNgrXmmvTiX9k9jm9AdKTSYEaZEAYF91wcY-gyQllwJUHGbEFNy0ILLTOAHh6LwMDMJiTr4mqQGm2W8dwo9hgLIy2I7mU_tJA83qnJ0qBiBJr1oM8HPeblXzj9r3TMI03D9sxdzy-lgo8RpgSXjNoCFPS5L9Xdz_7MKmIBr1kzwEisXuUF1BZvQ |
| Full analysis: | https://app.any.run/tasks/4d5b331b-c04a-488e-8a5a-40ee76faff5c |
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2023, 16:19:40 |
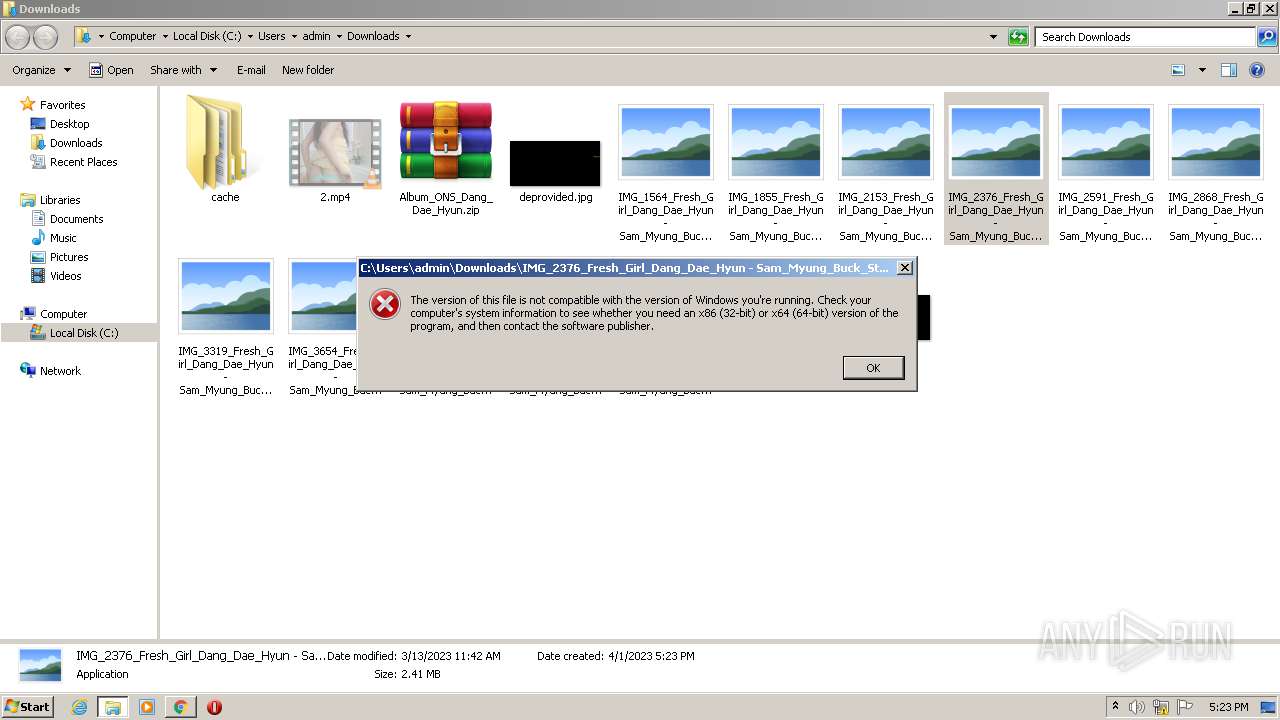
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | FDB2BBA853061CF337319BEEF83888CD |
| SHA1: | 96C641348C4E556AFE44C6FB8A3C3268F12B7BF5 |
| SHA256: | 3D34697680B373765849BA0E3E3DF35137057ADFA742232148FEB6B7C0A3E963 |
| SSDEEP: | 12:20wHDJMljYfssHhipzQDRiKxX7GaALqbi5fmzF7:2ljJWYfsfpzK17yLROF7 |
MALICIOUS
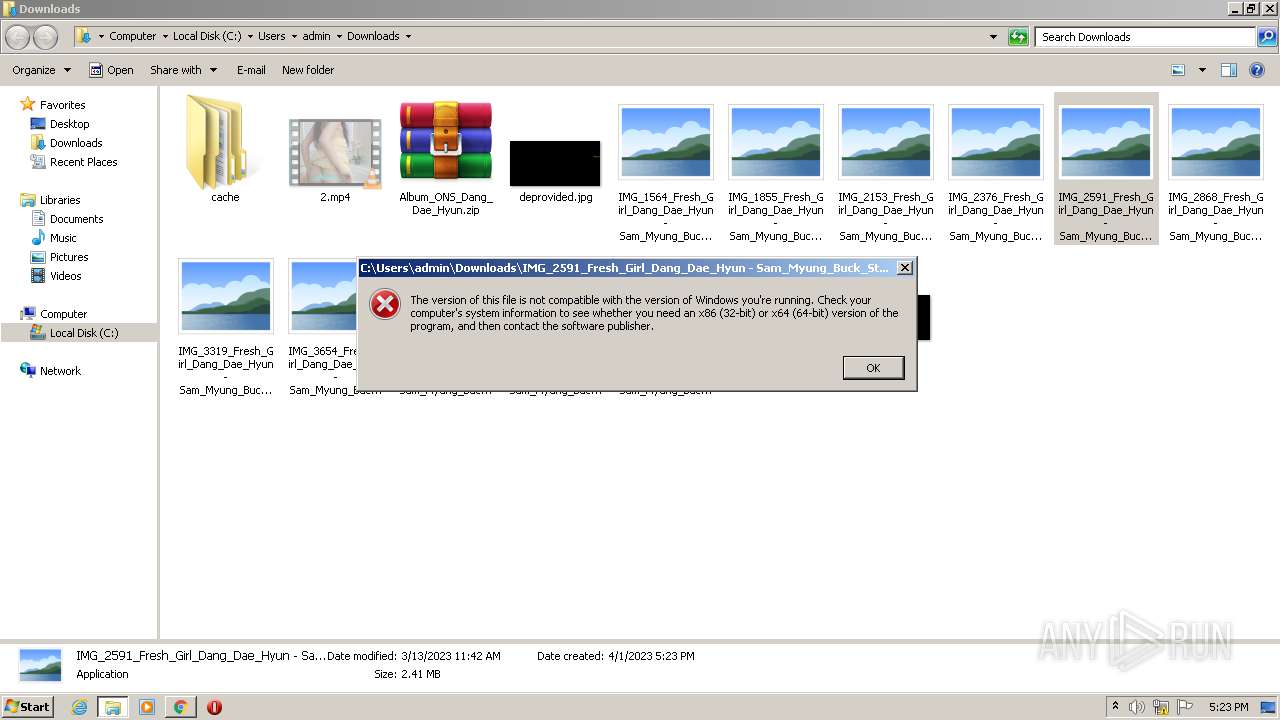
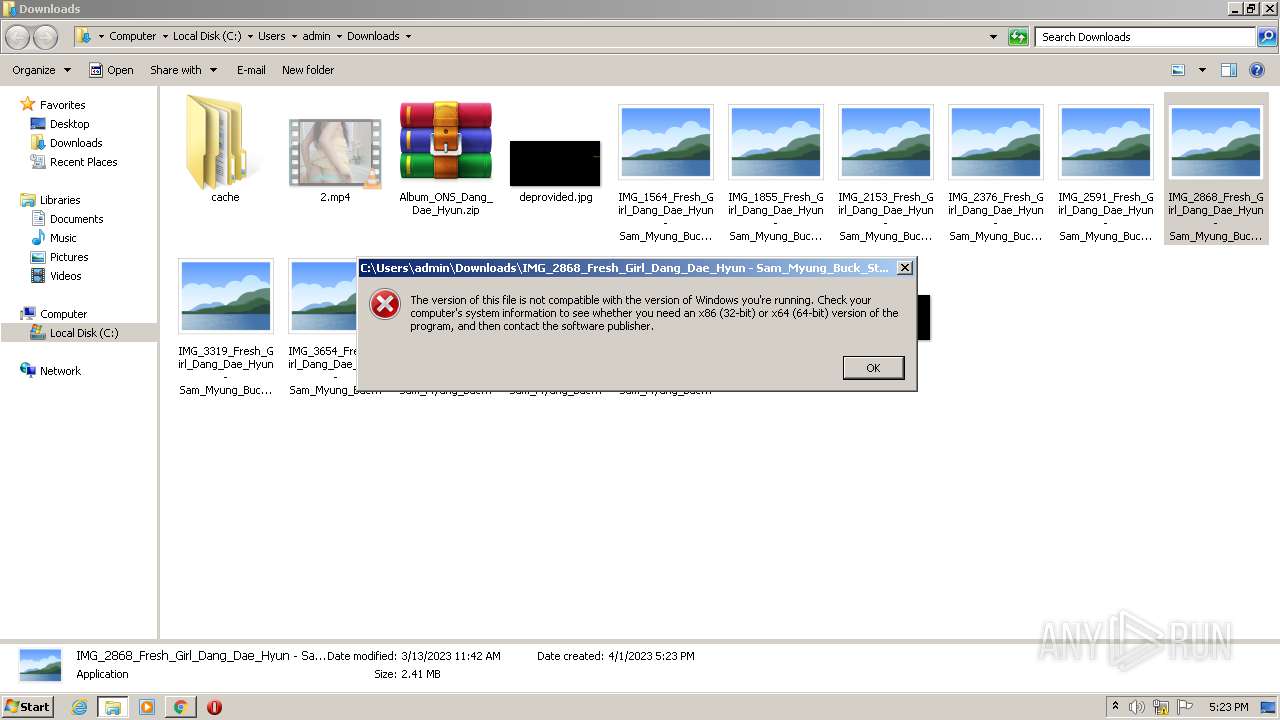
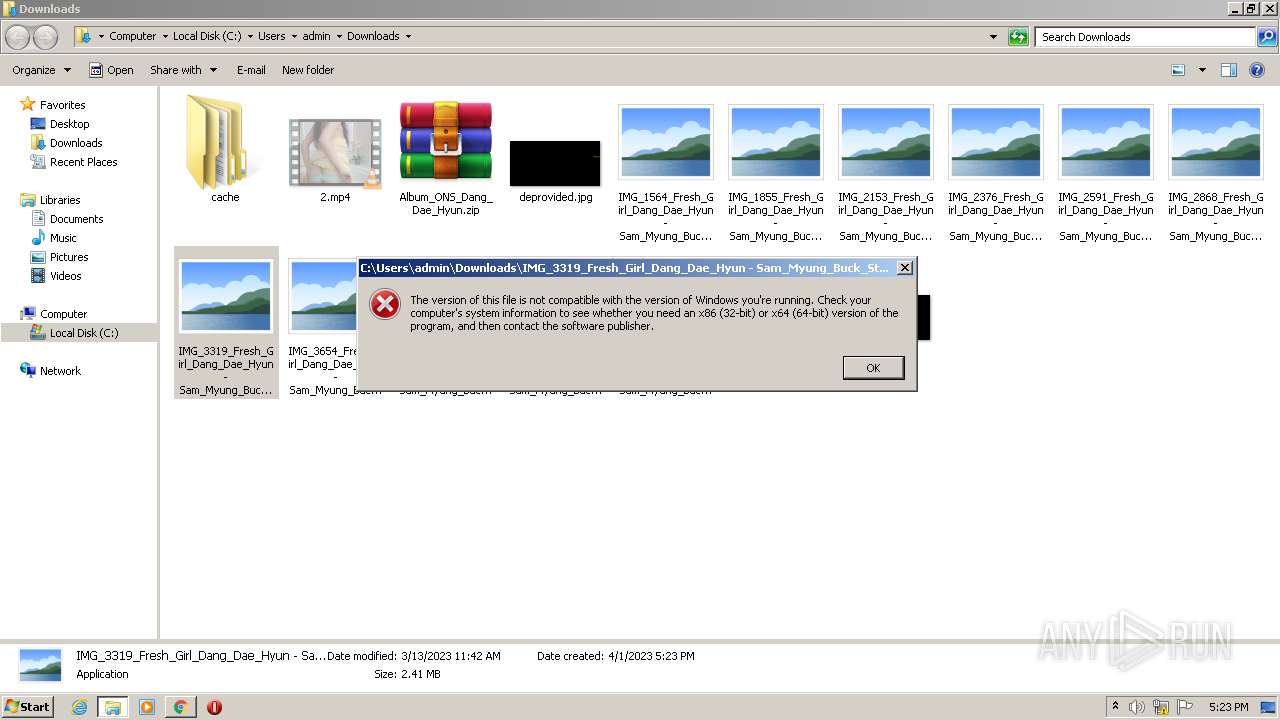
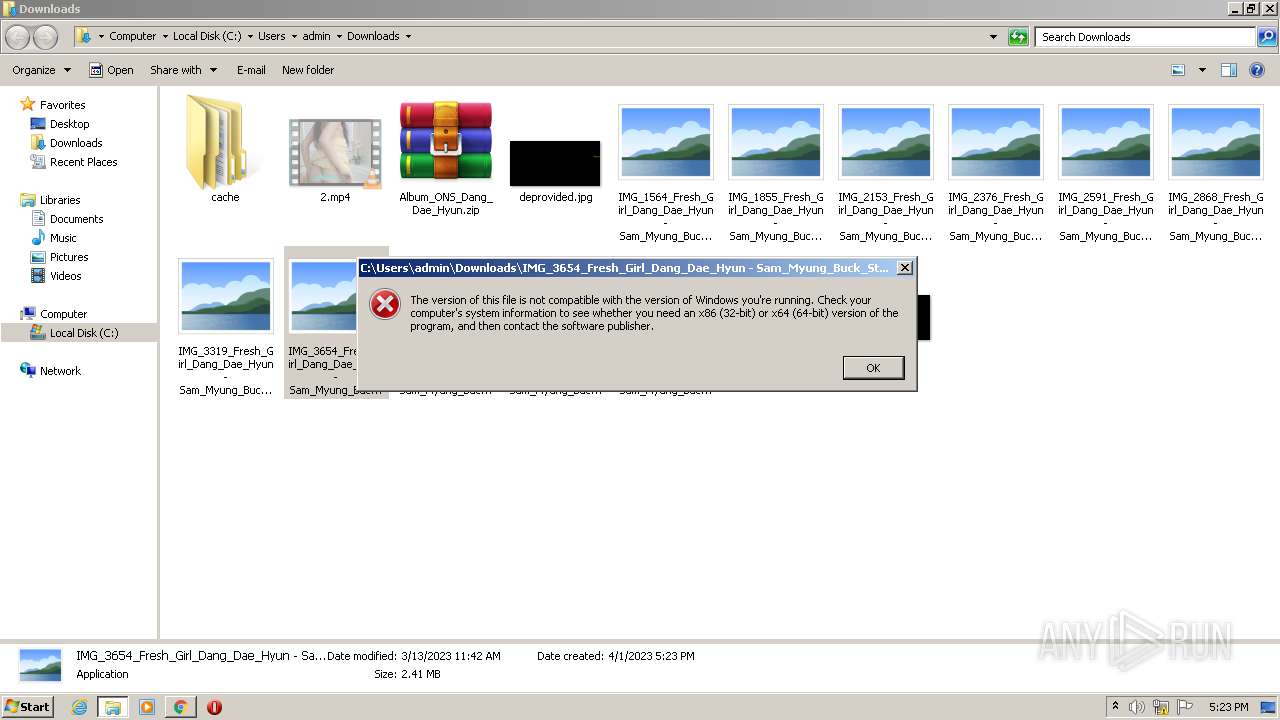
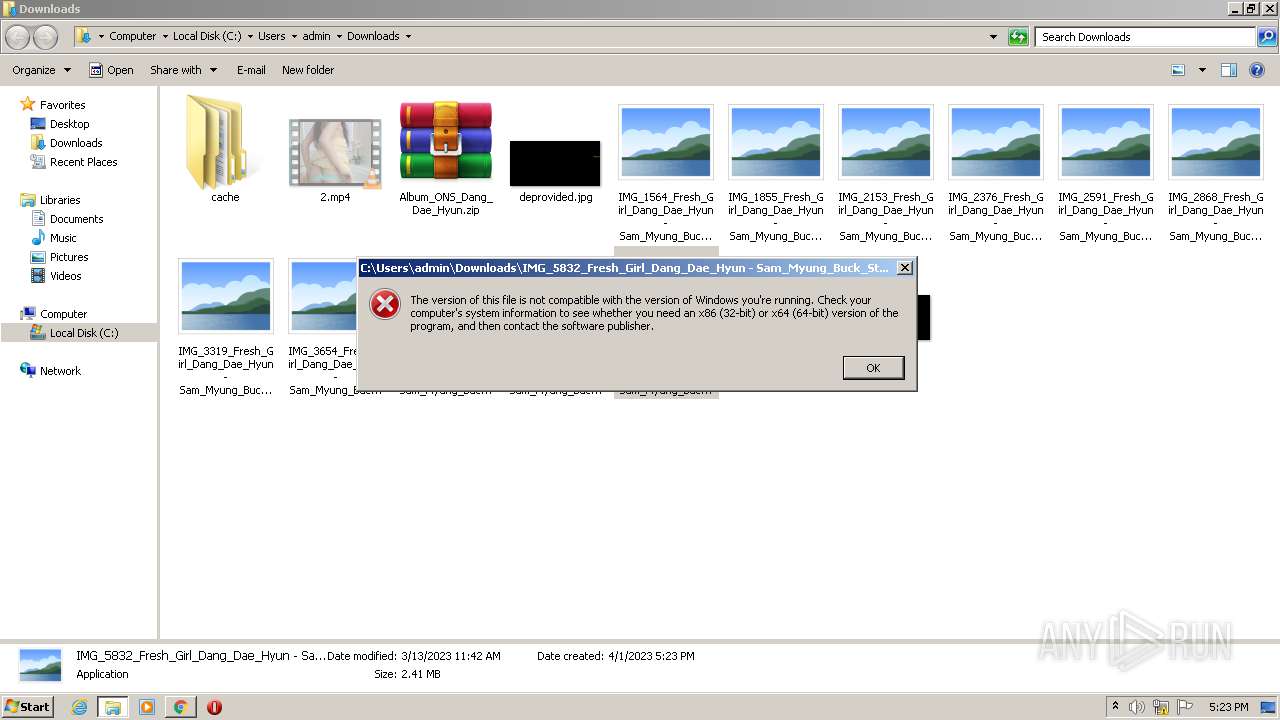
Starts Visual C# compiler
- sdiagnhost.exe (PID: 2800)
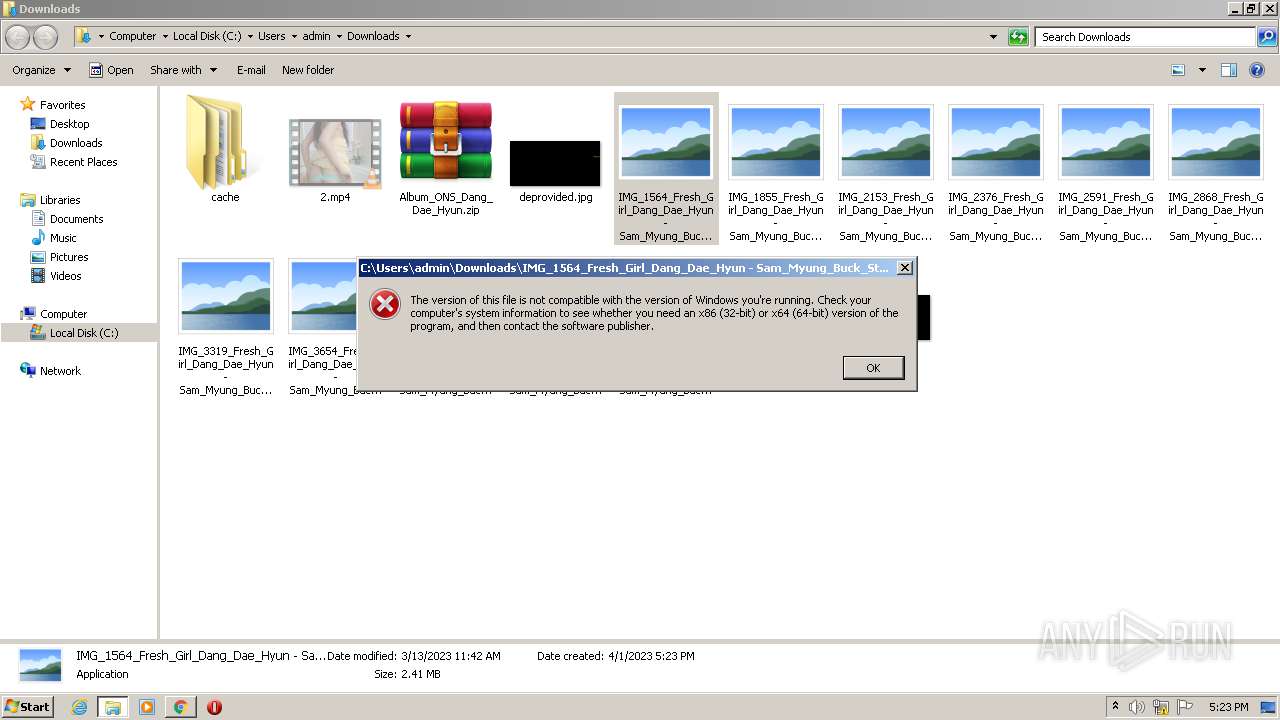
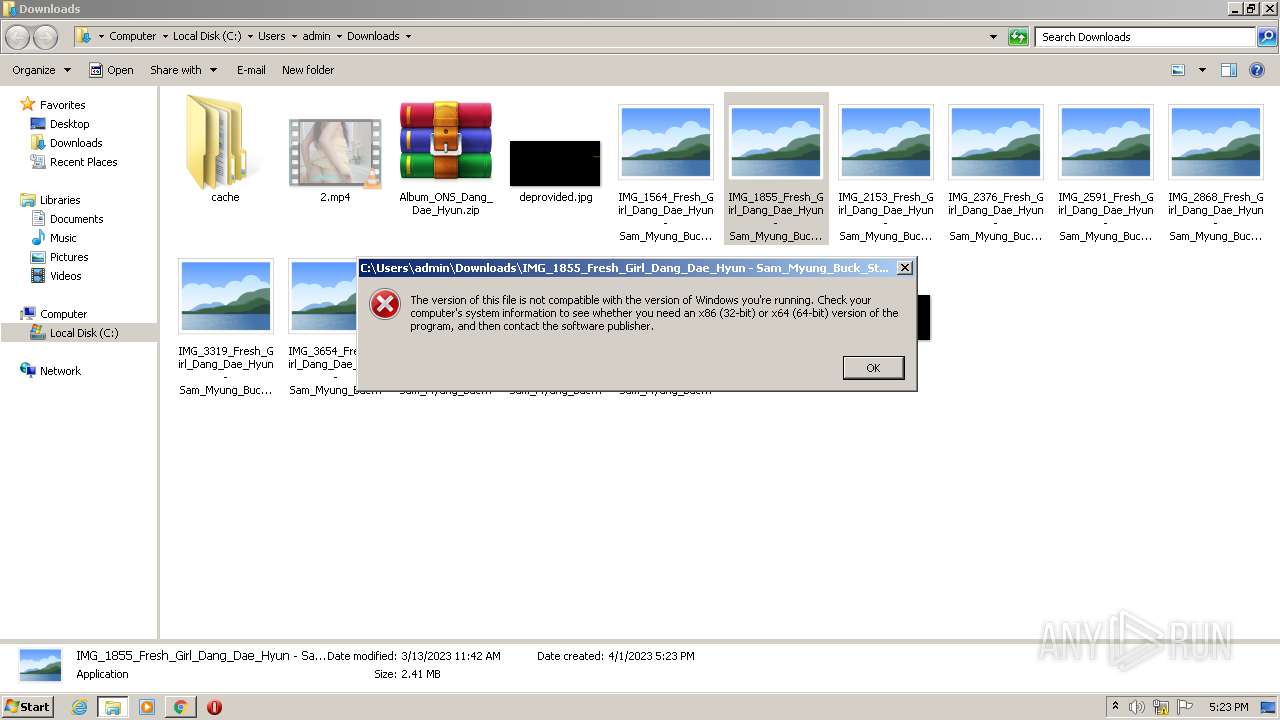
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3104)
SUSPICIOUS
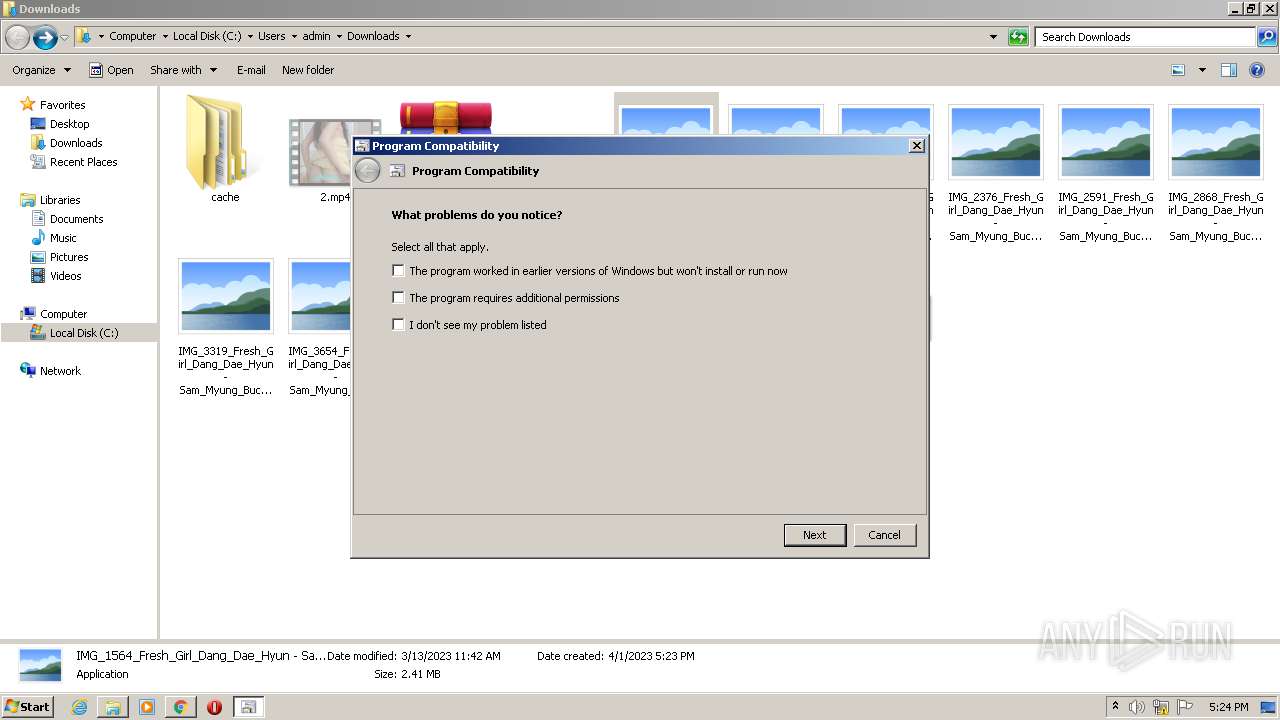
Reads security settings of Internet Explorer
- msdt.exe (PID: 568)
- sdiagnhost.exe (PID: 2800)
Reads settings of System Certificates
- msdt.exe (PID: 568)
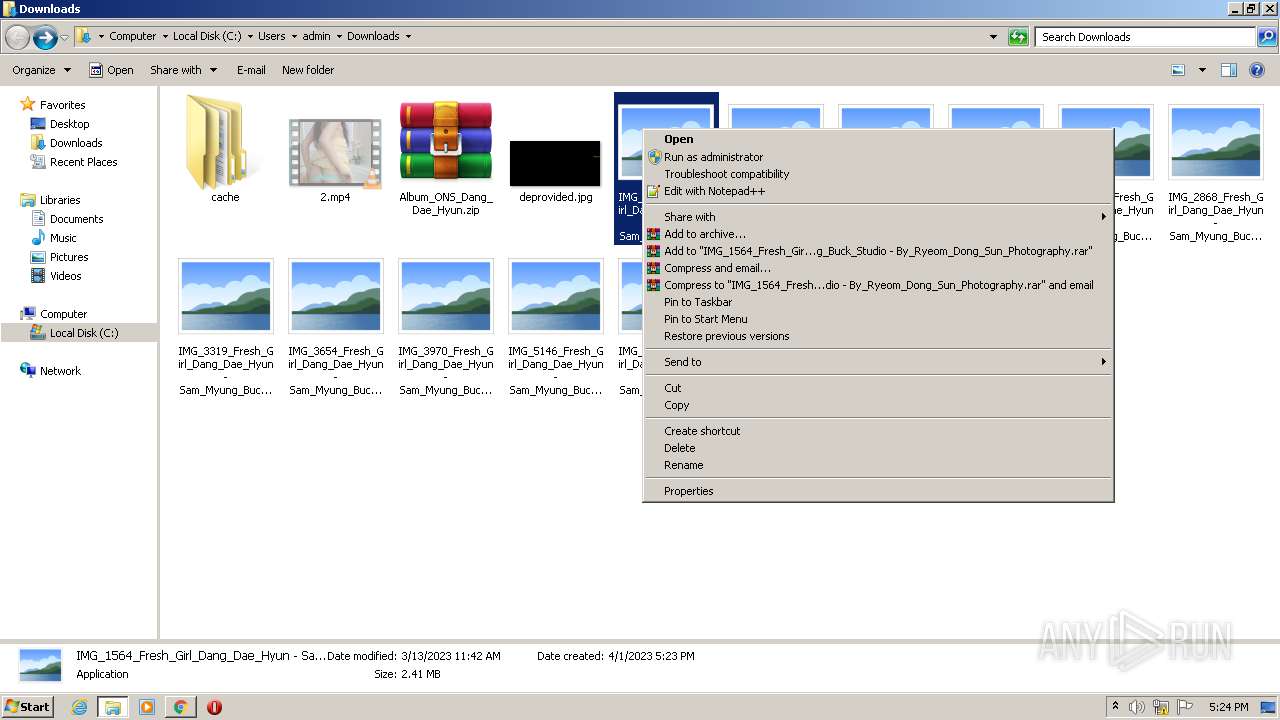
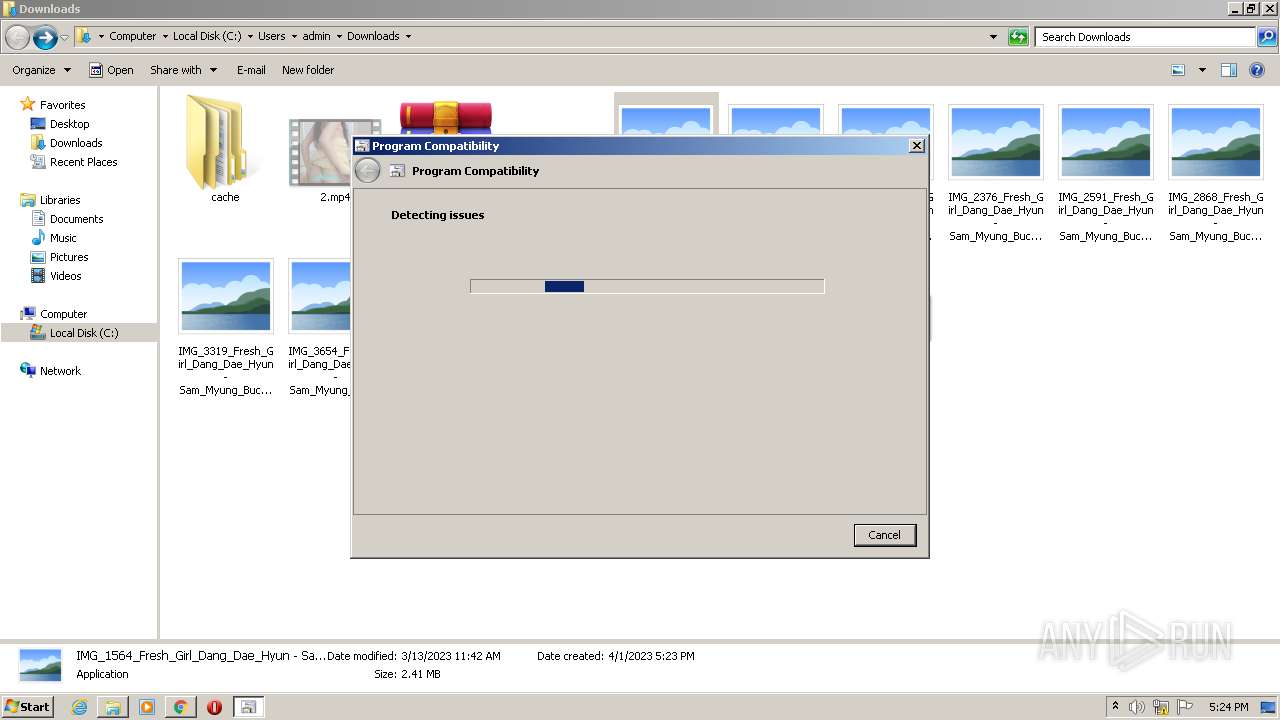
Probably uses Microsoft diagnostics tool to execute malicious payload
- pcwrun.exe (PID: 3904)
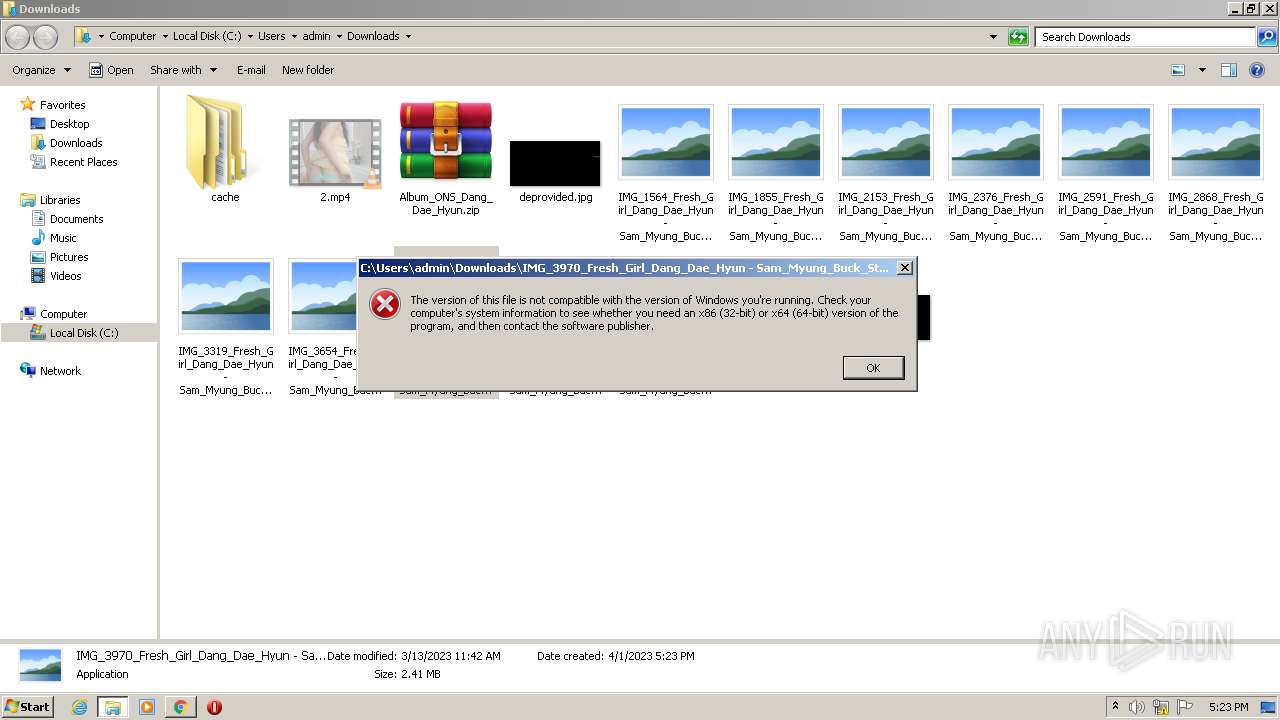
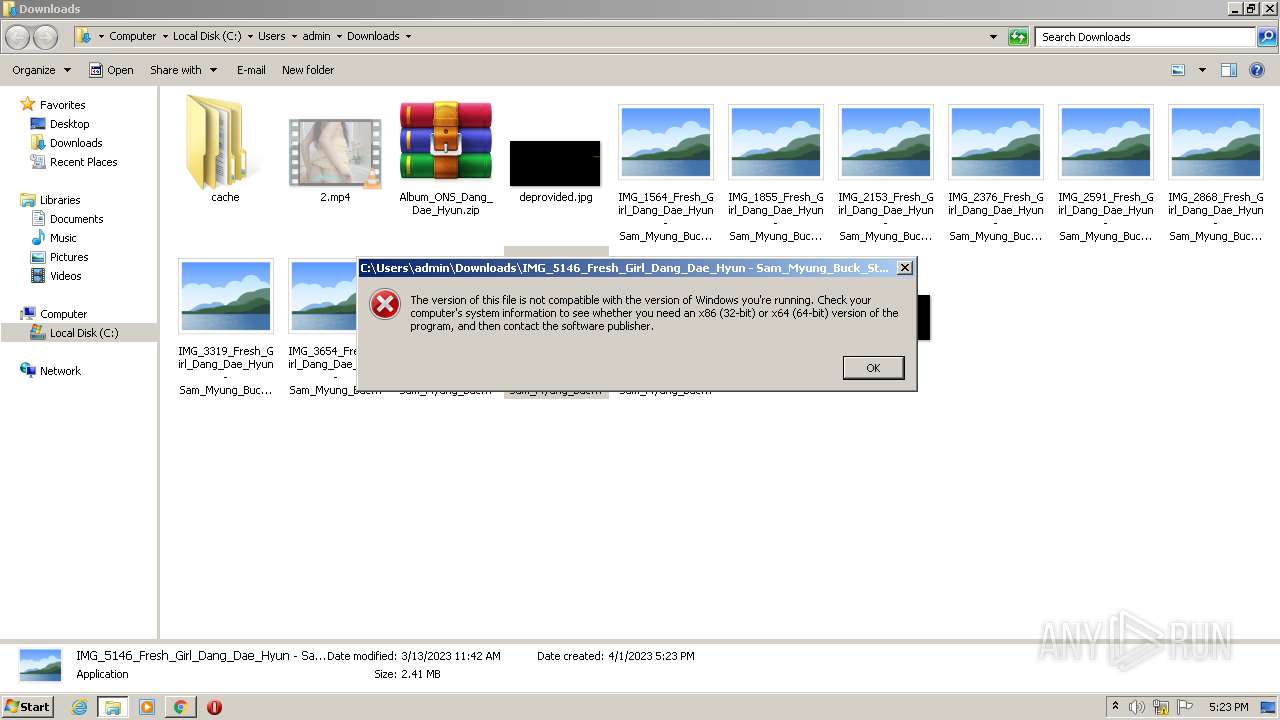
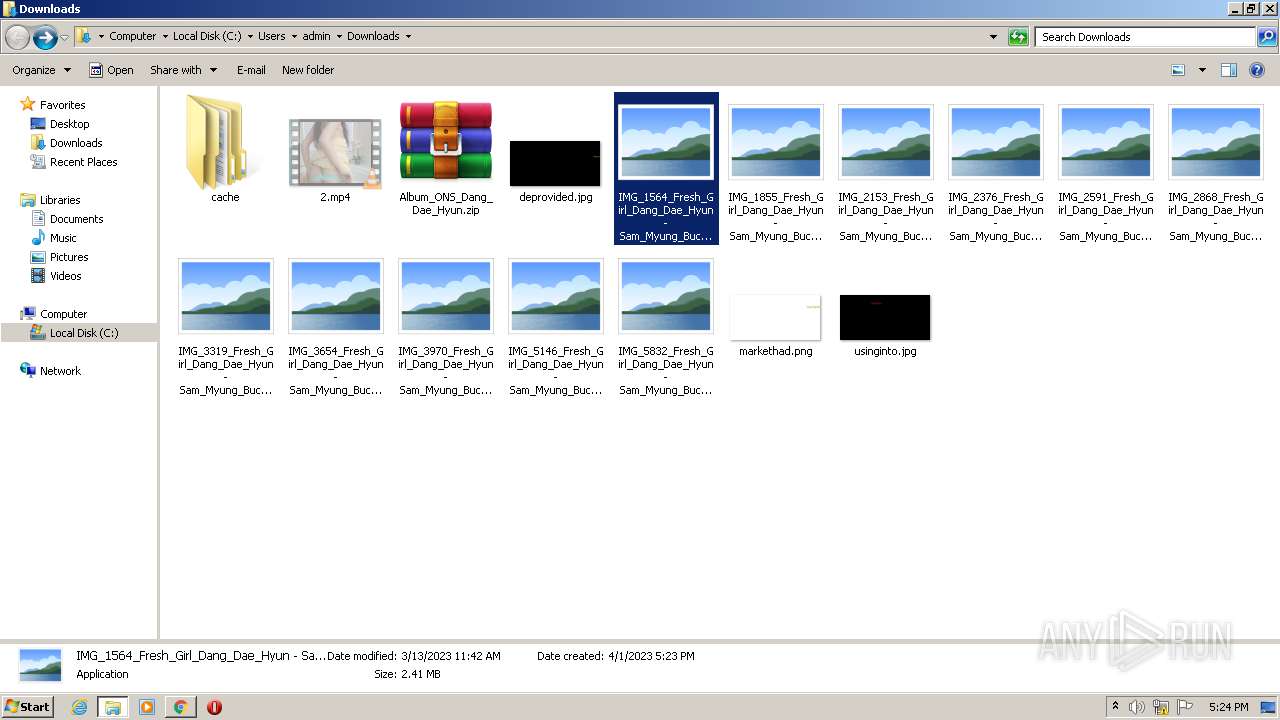
Executable content was dropped or overwritten
- msdt.exe (PID: 568)
- csc.exe (PID: 1852)
- csc.exe (PID: 3912)
- csc.exe (PID: 3480)
Reads the Internet Settings
- sdiagnhost.exe (PID: 2800)
Uses .NET C# to load dll
- sdiagnhost.exe (PID: 2800)
INFO
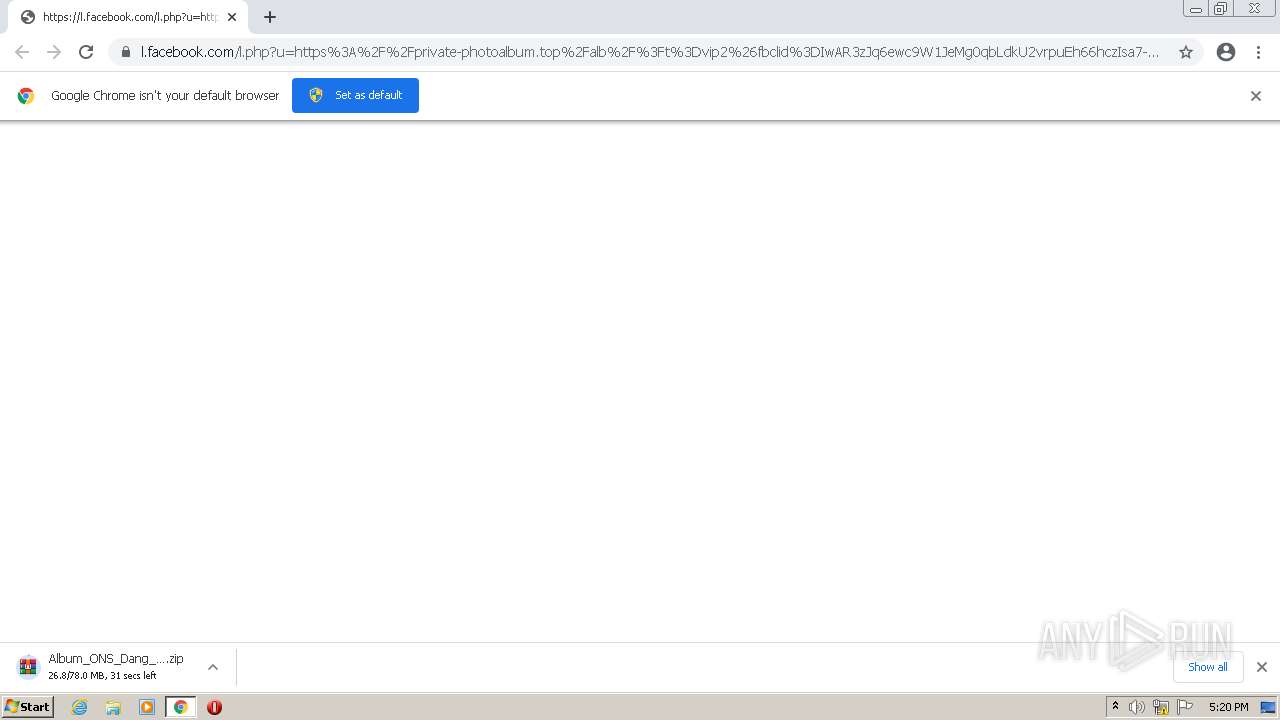
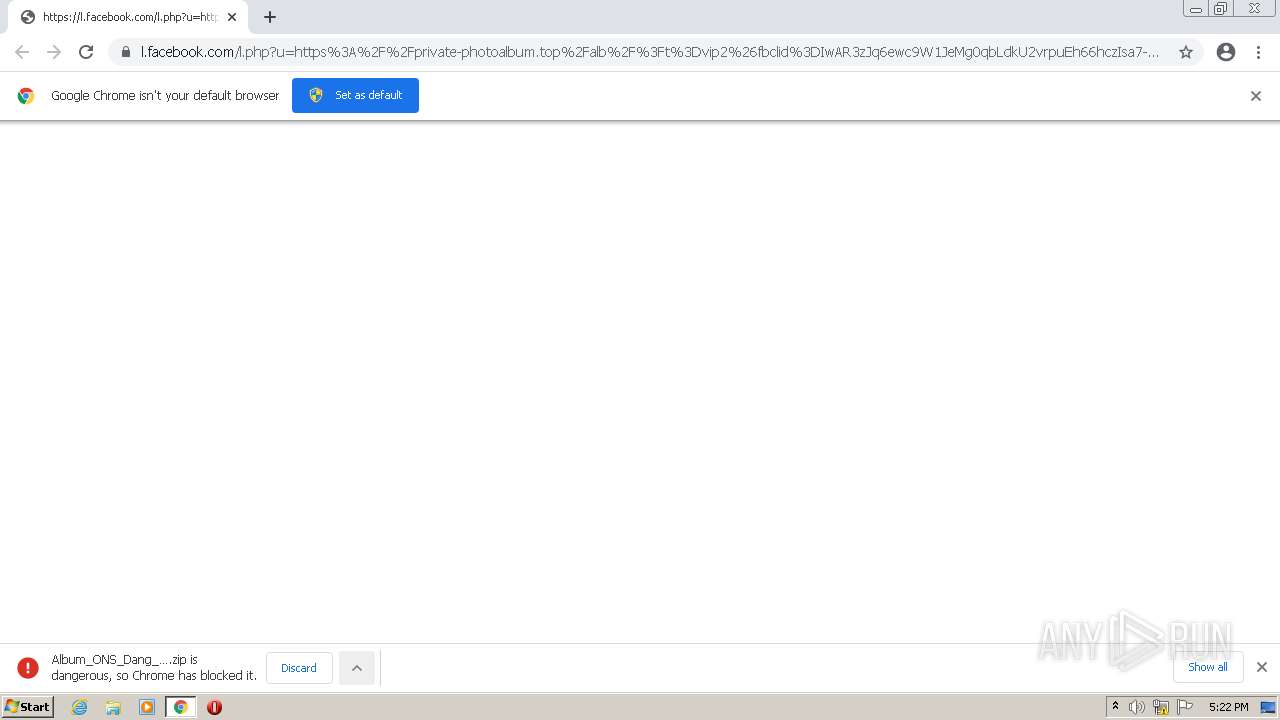
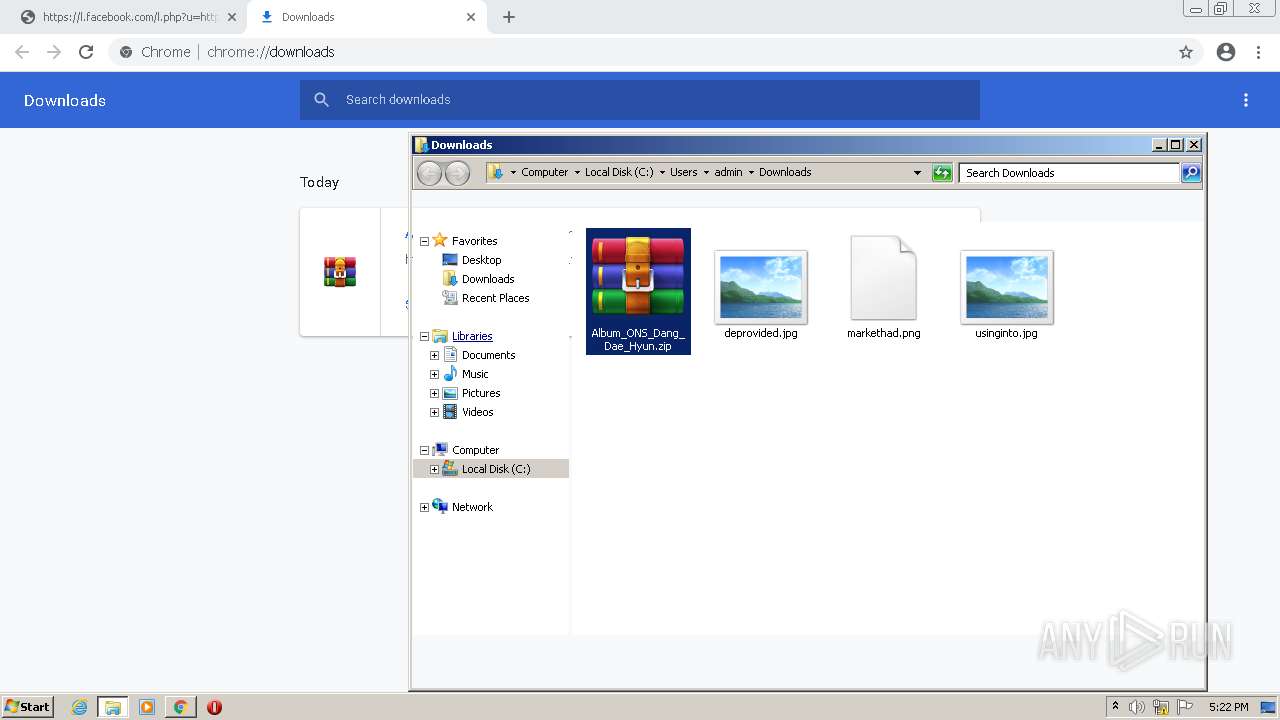
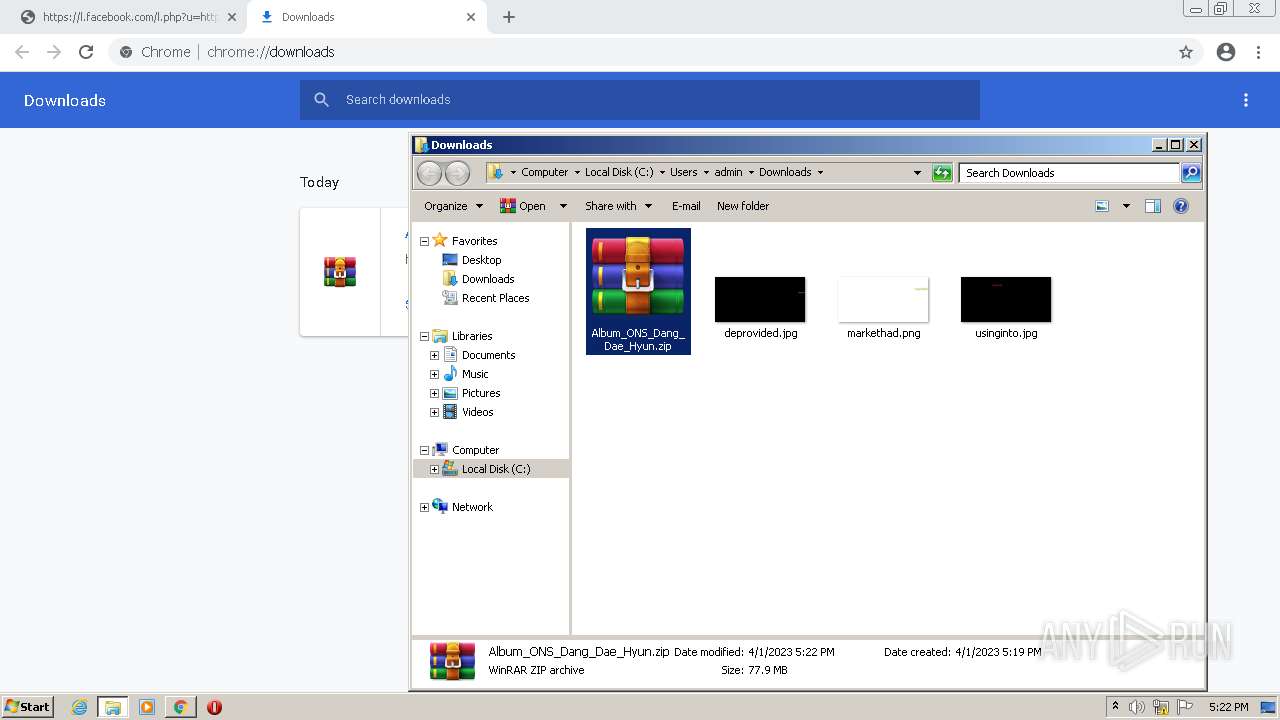
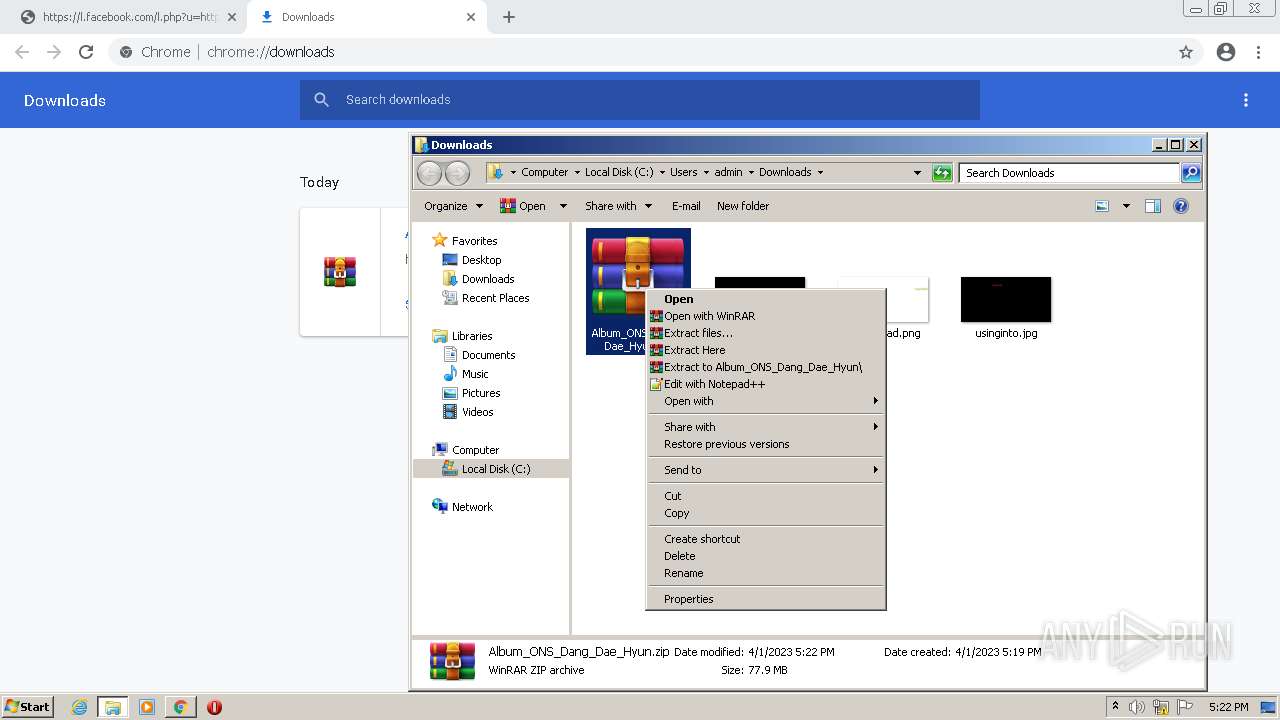
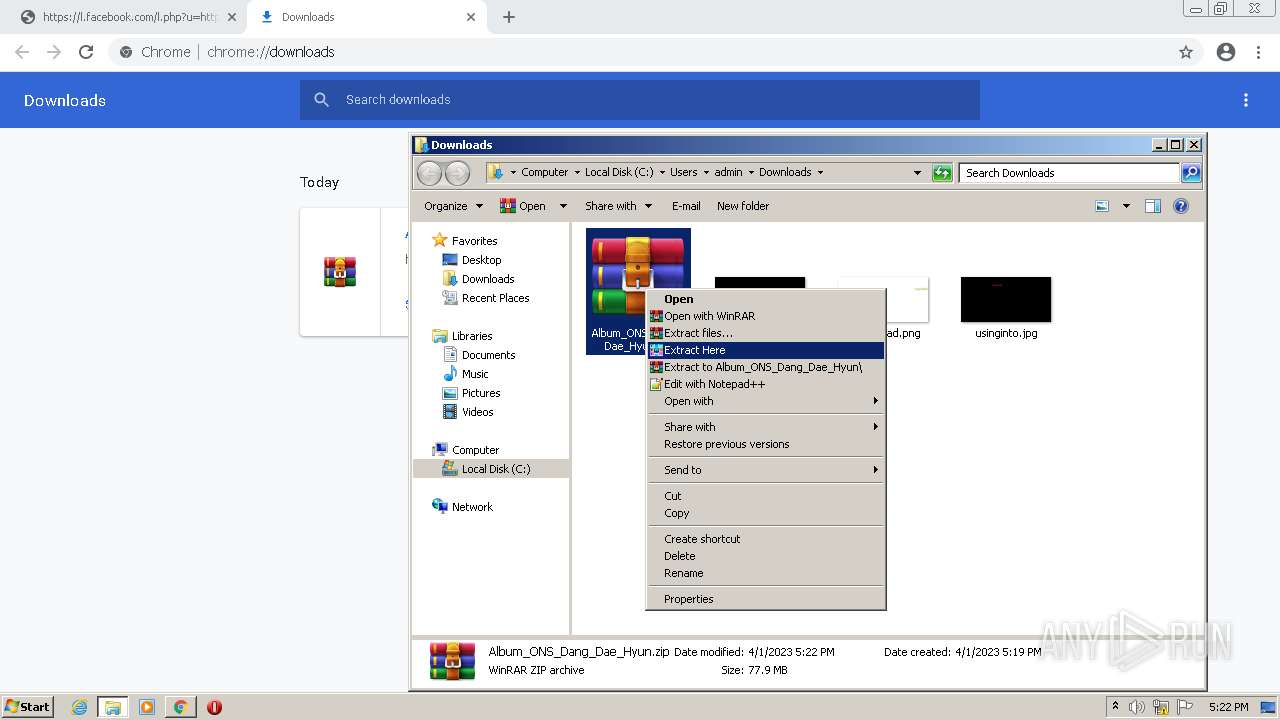
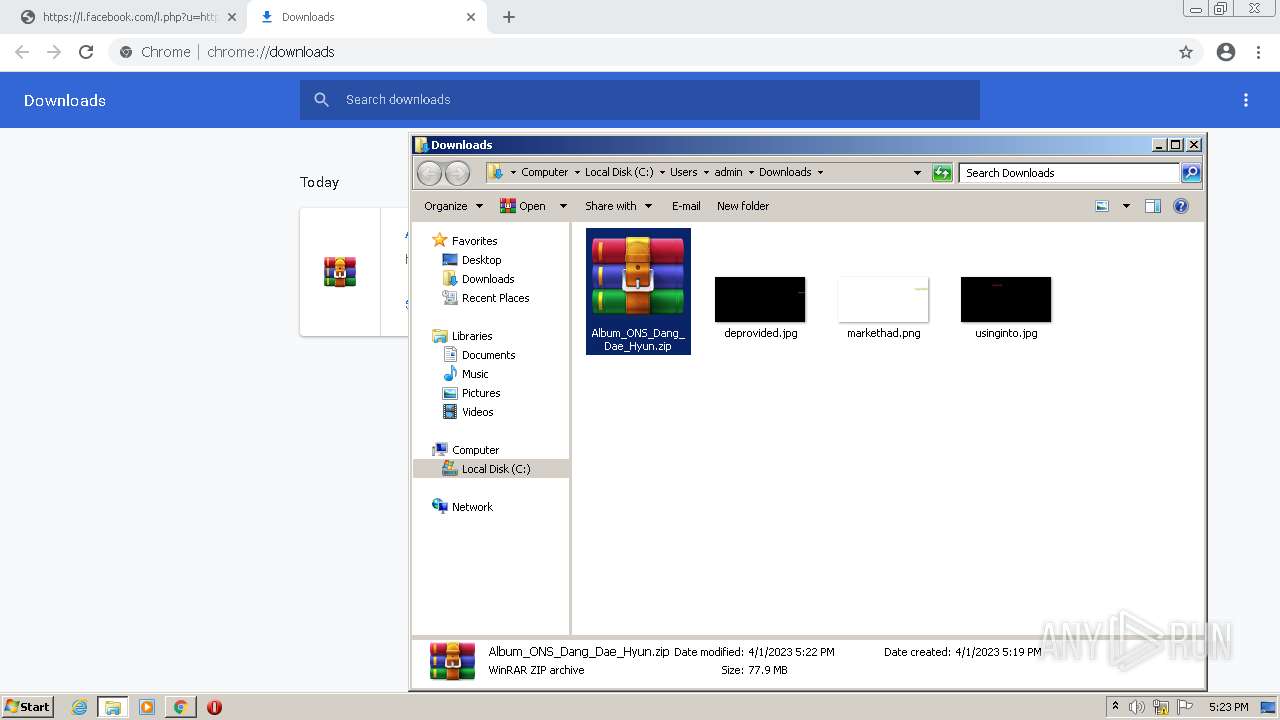
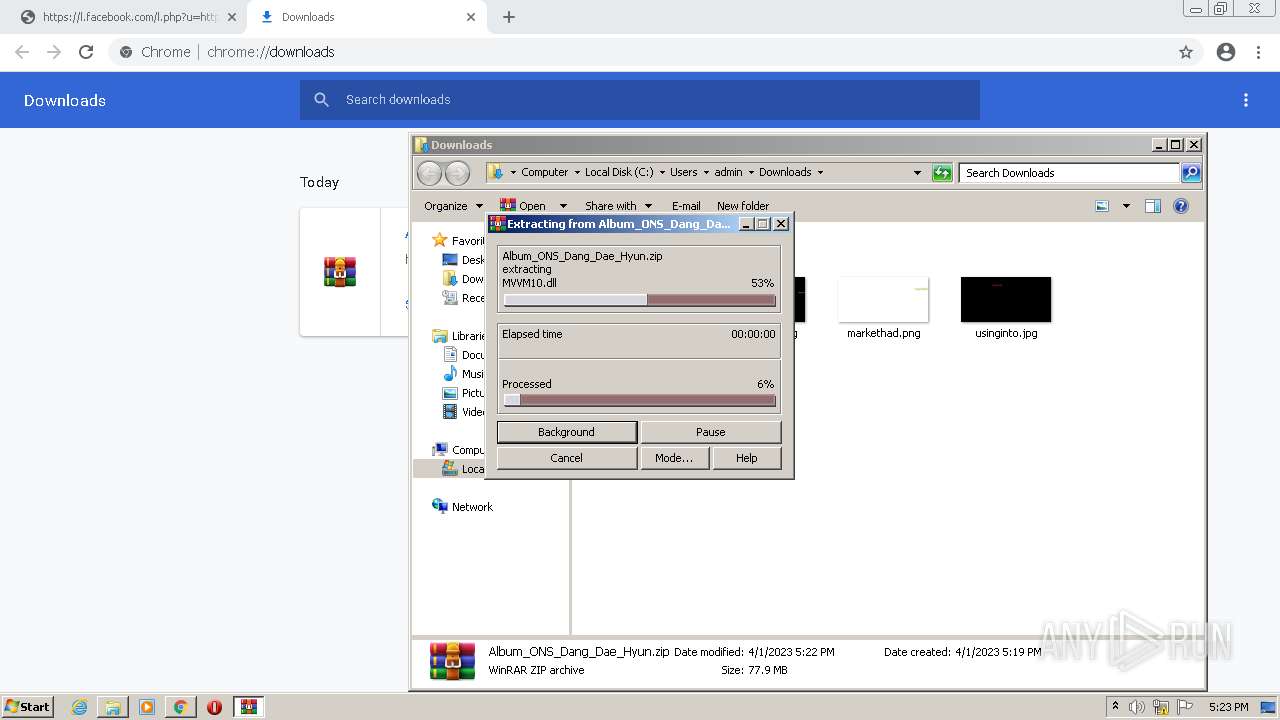
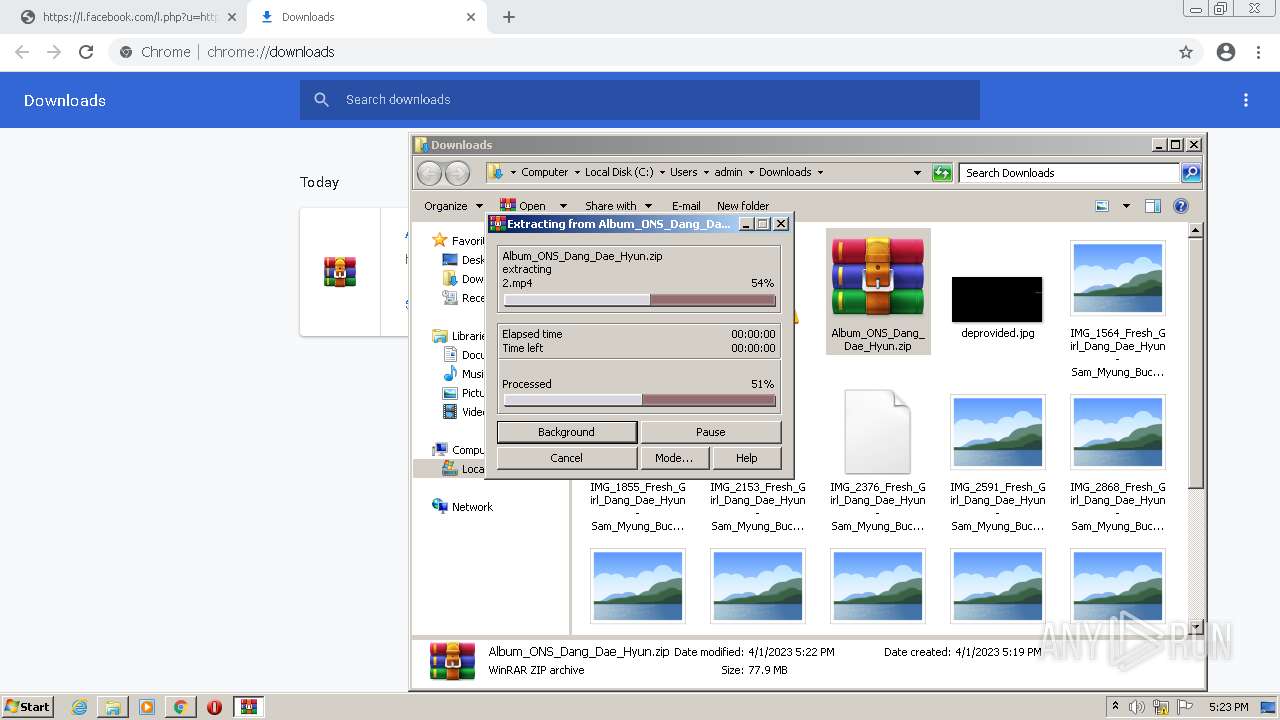
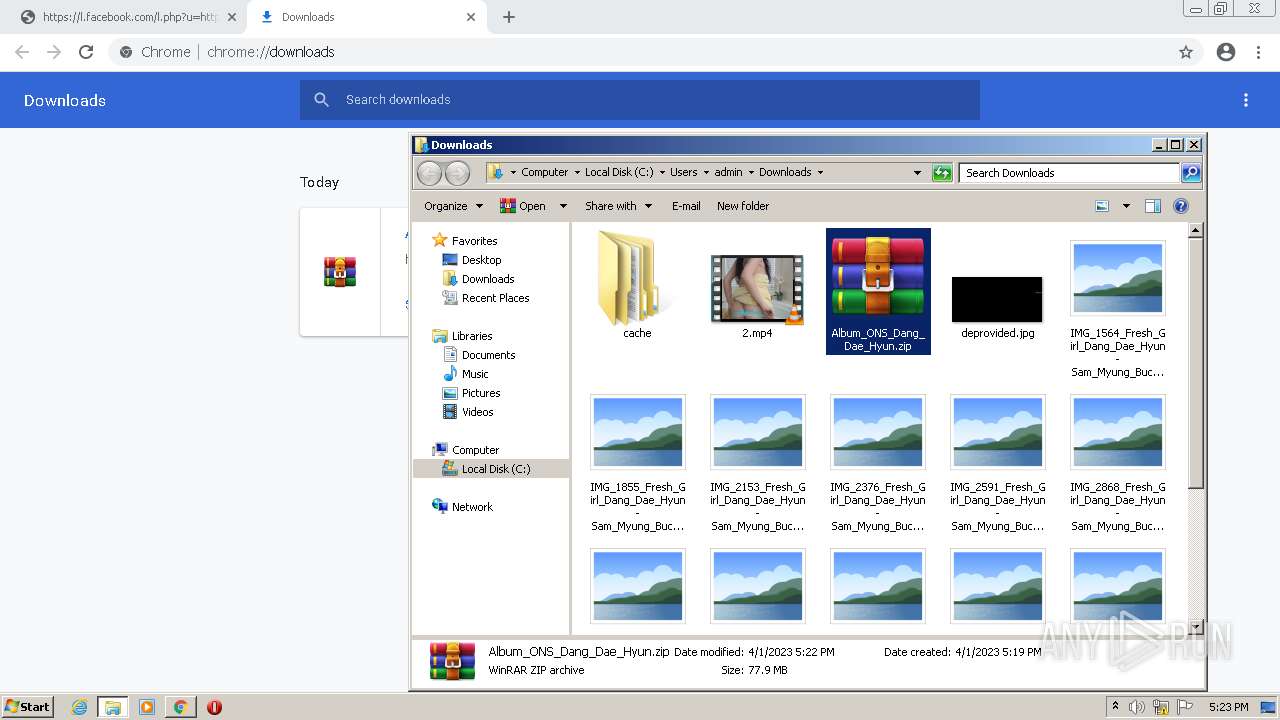
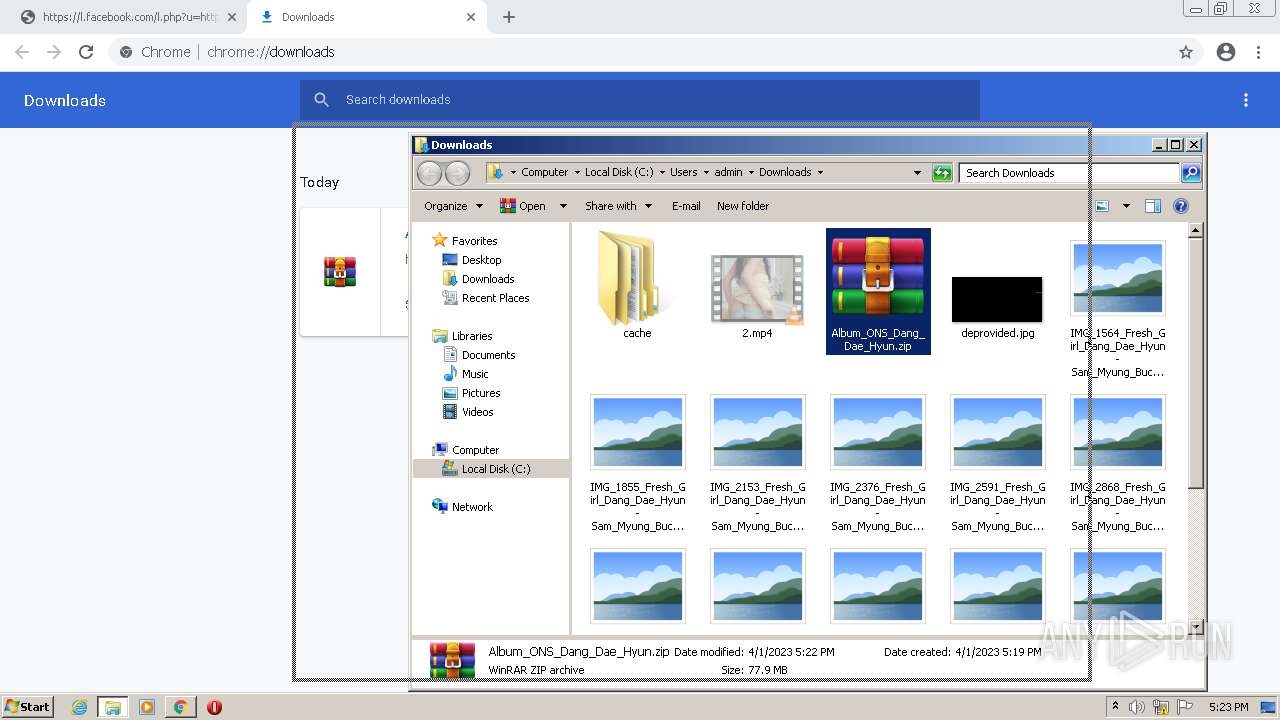
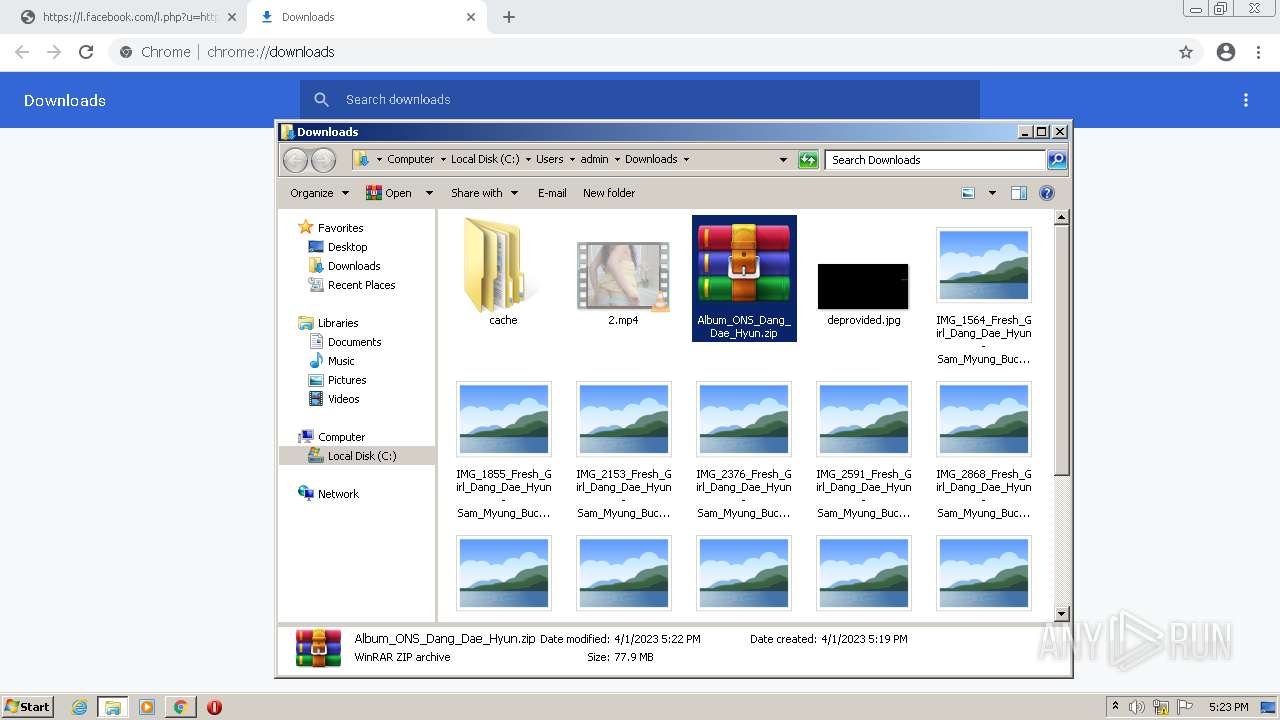
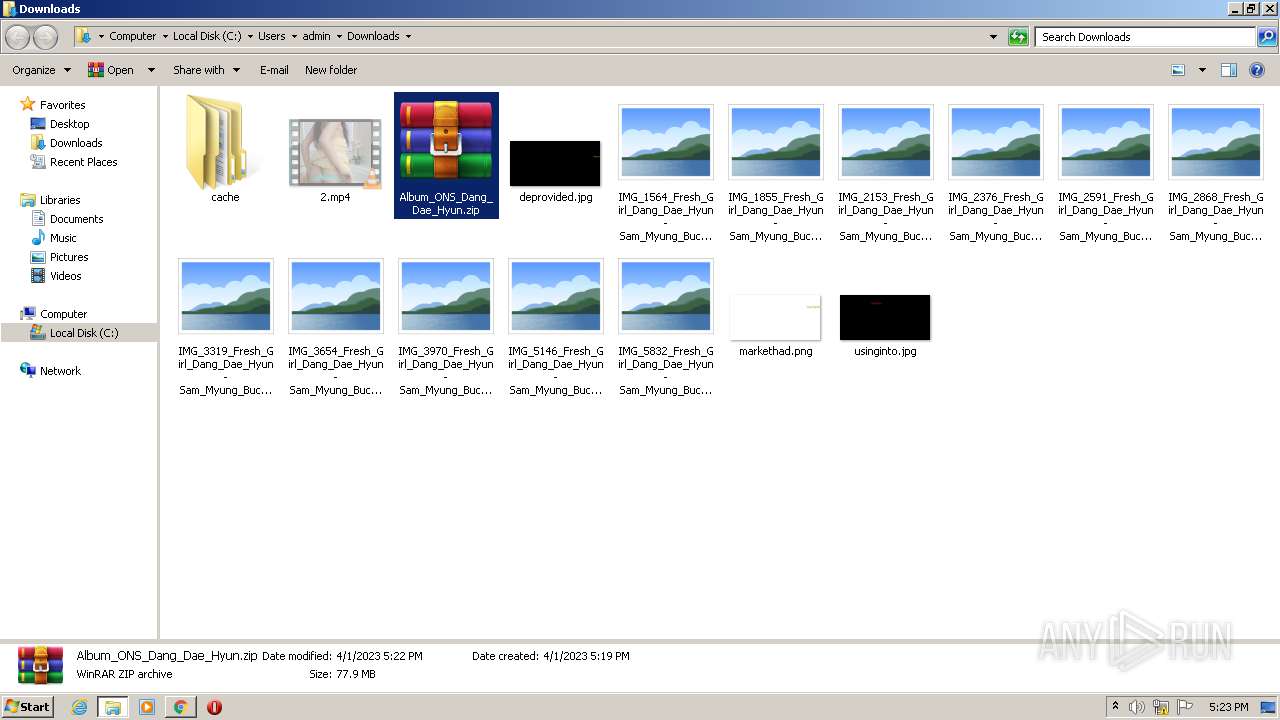
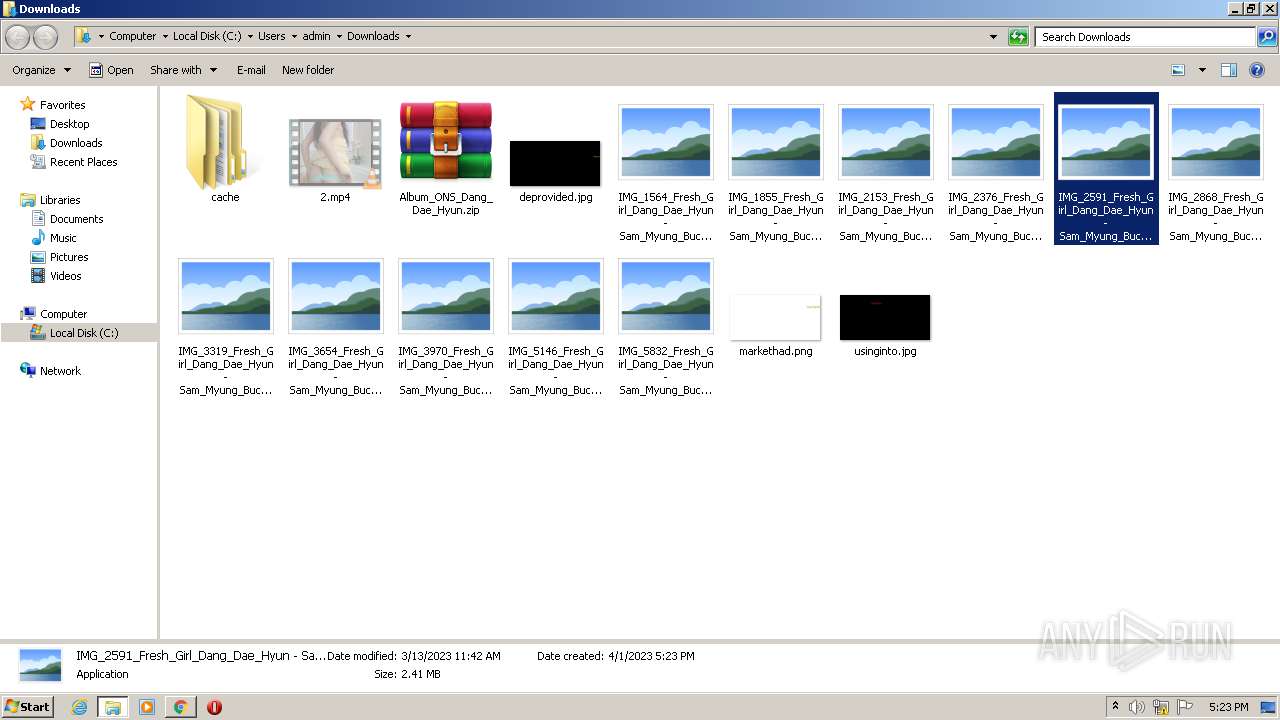
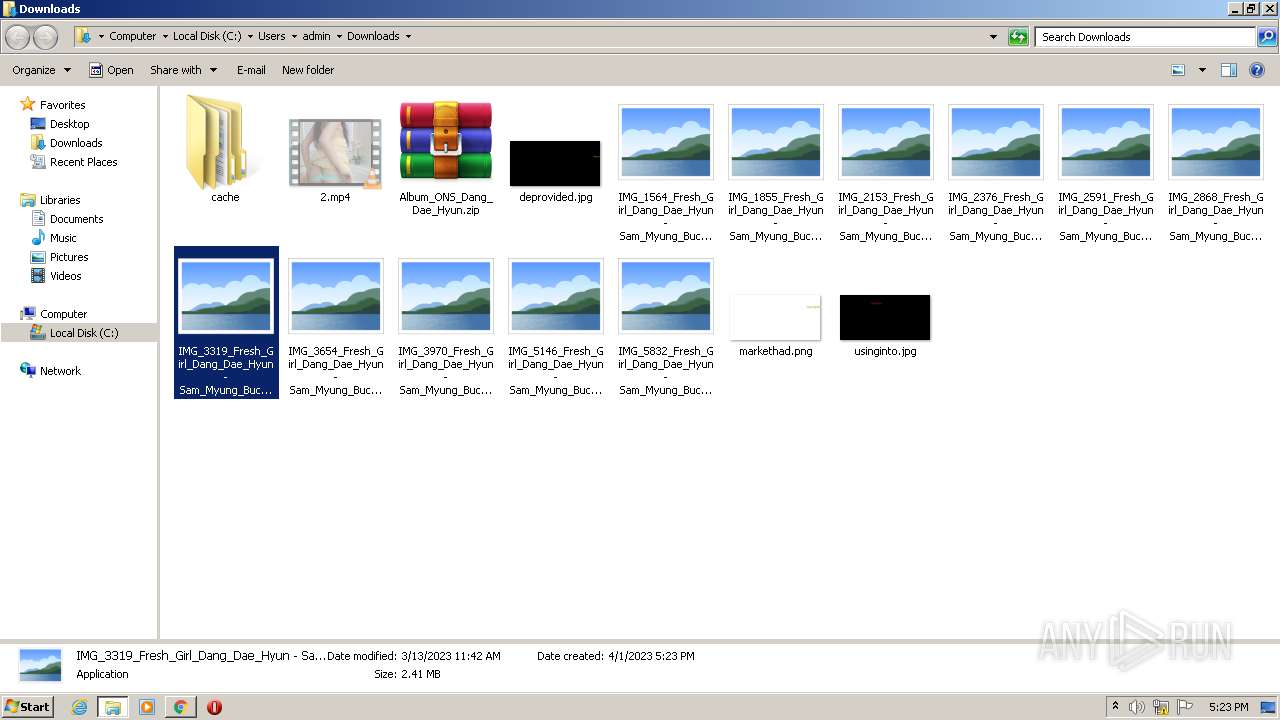
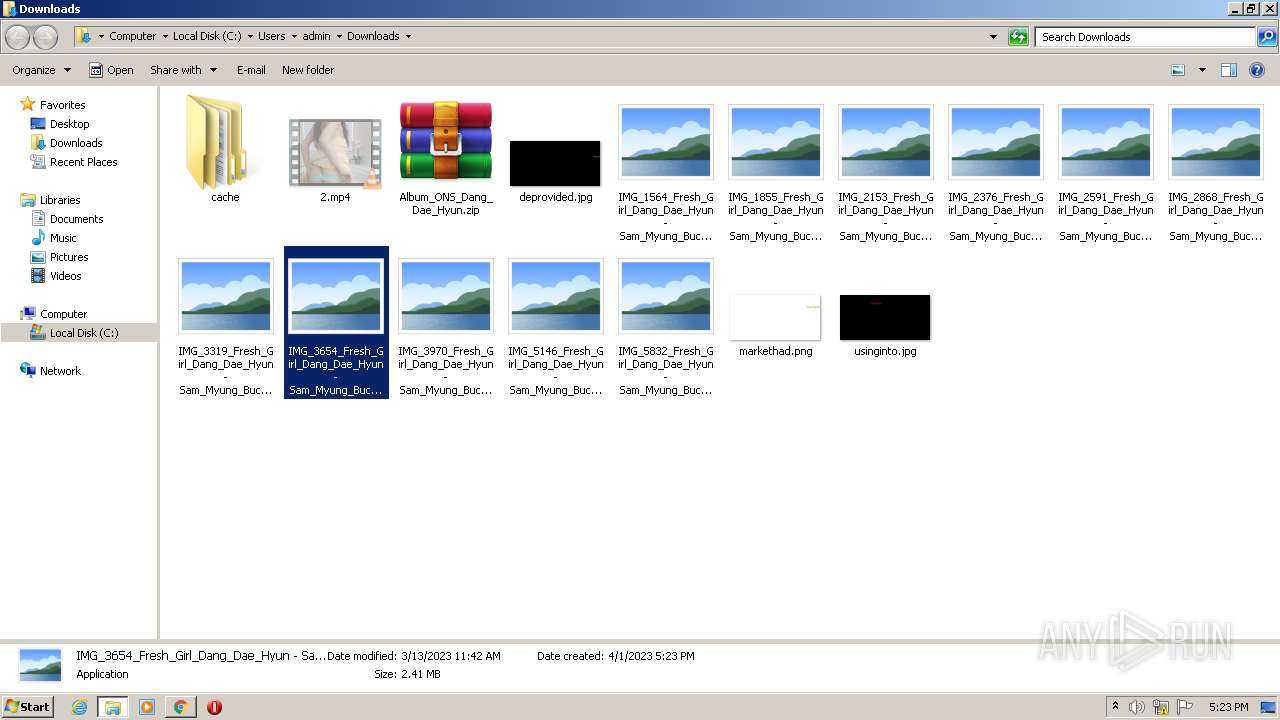
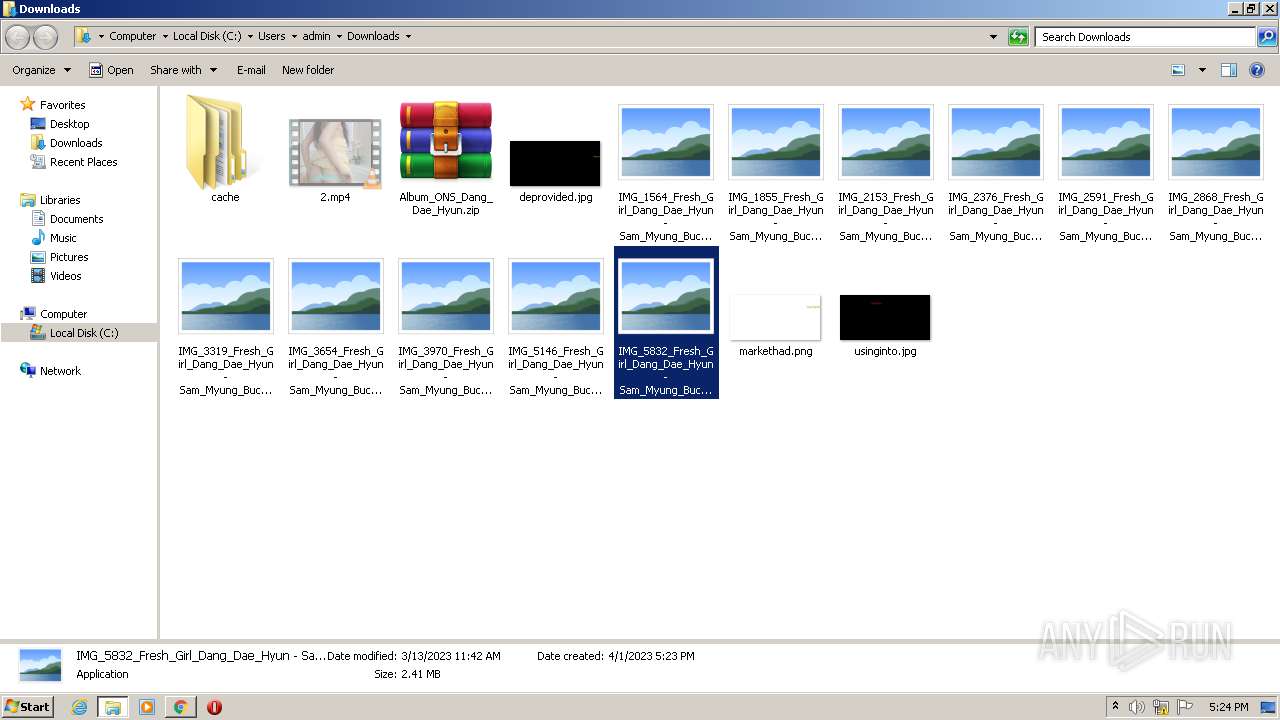
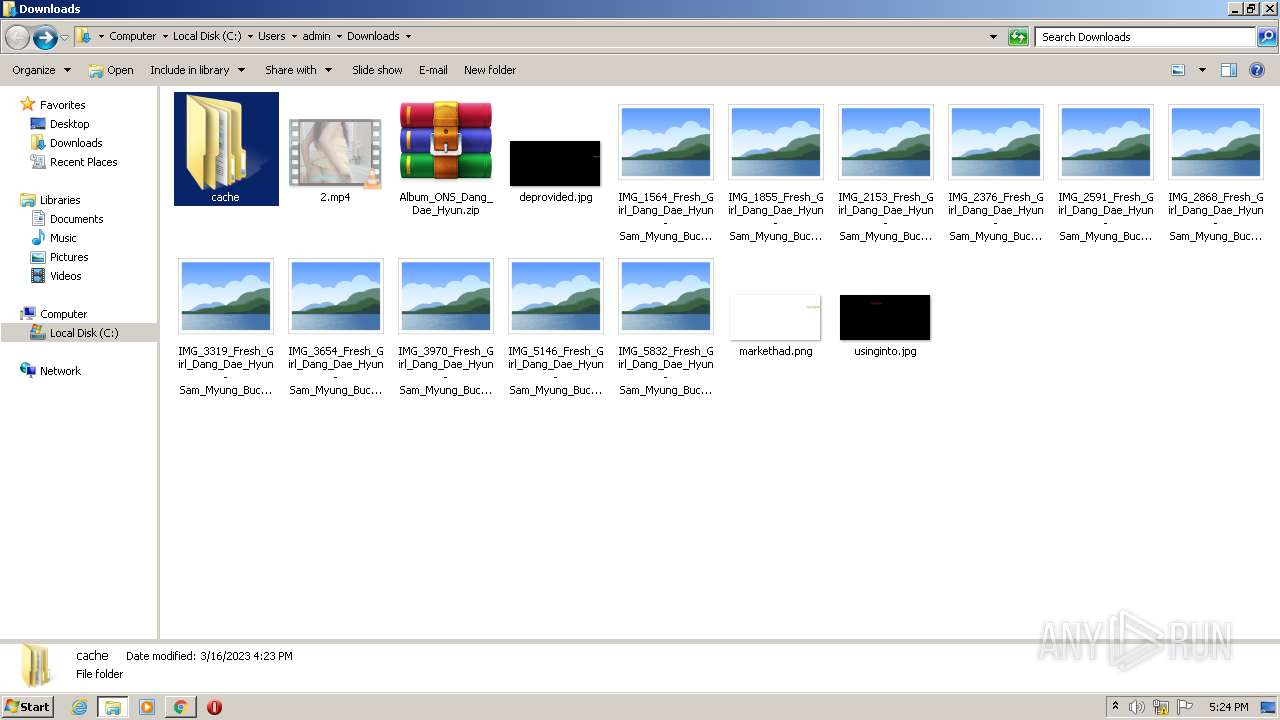
The process uses the downloaded file
- WinRAR.exe (PID: 752)
- chrome.exe (PID: 3936)
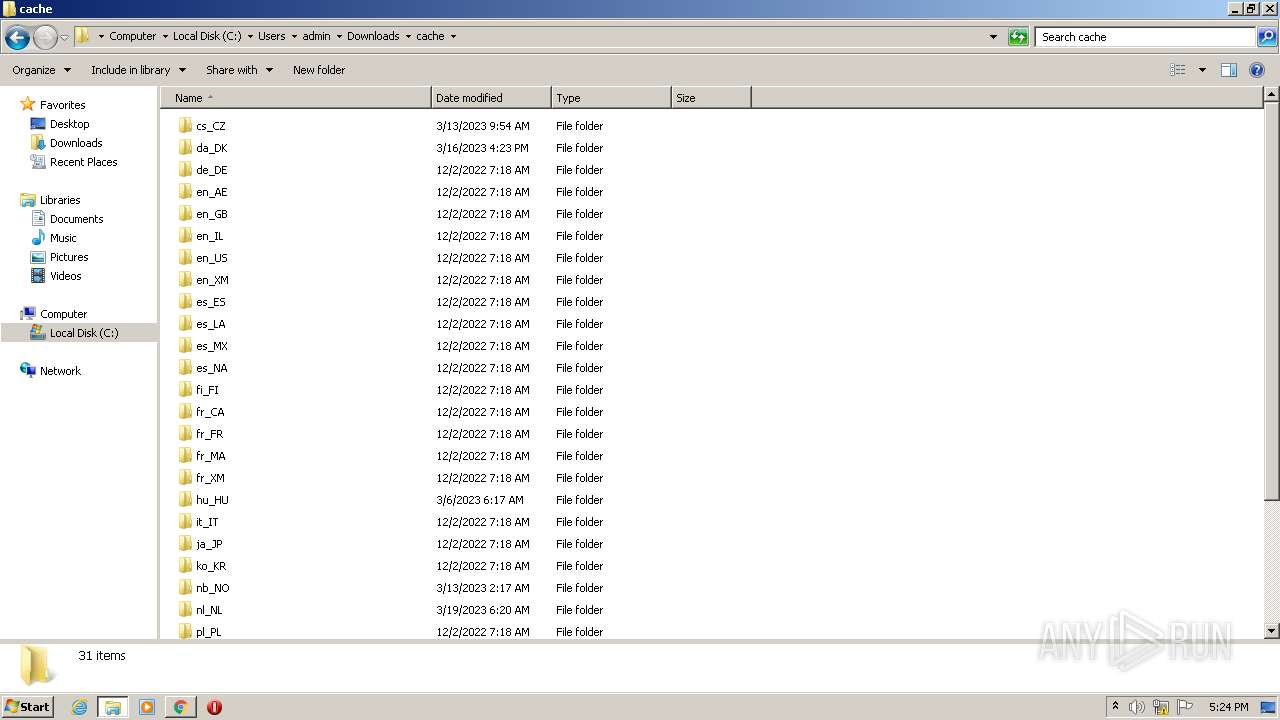
Create files in a temporary directory
- chrome.exe (PID: 1488)
- pcwrun.exe (PID: 3904)
- msdt.exe (PID: 568)
- sdiagnhost.exe (PID: 2800)
- cvtres.exe (PID: 3580)
- csc.exe (PID: 1852)
- csc.exe (PID: 3912)
- cvtres.exe (PID: 3984)
- csc.exe (PID: 3480)
- cvtres.exe (PID: 1660)
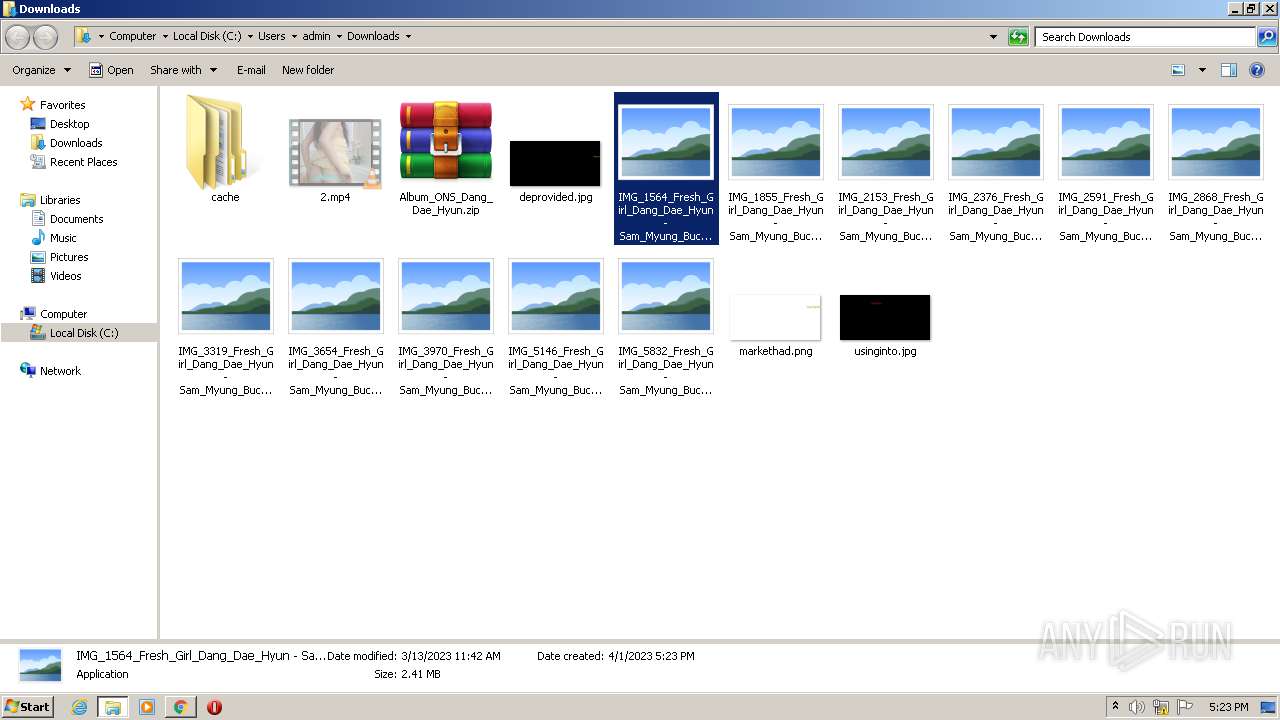
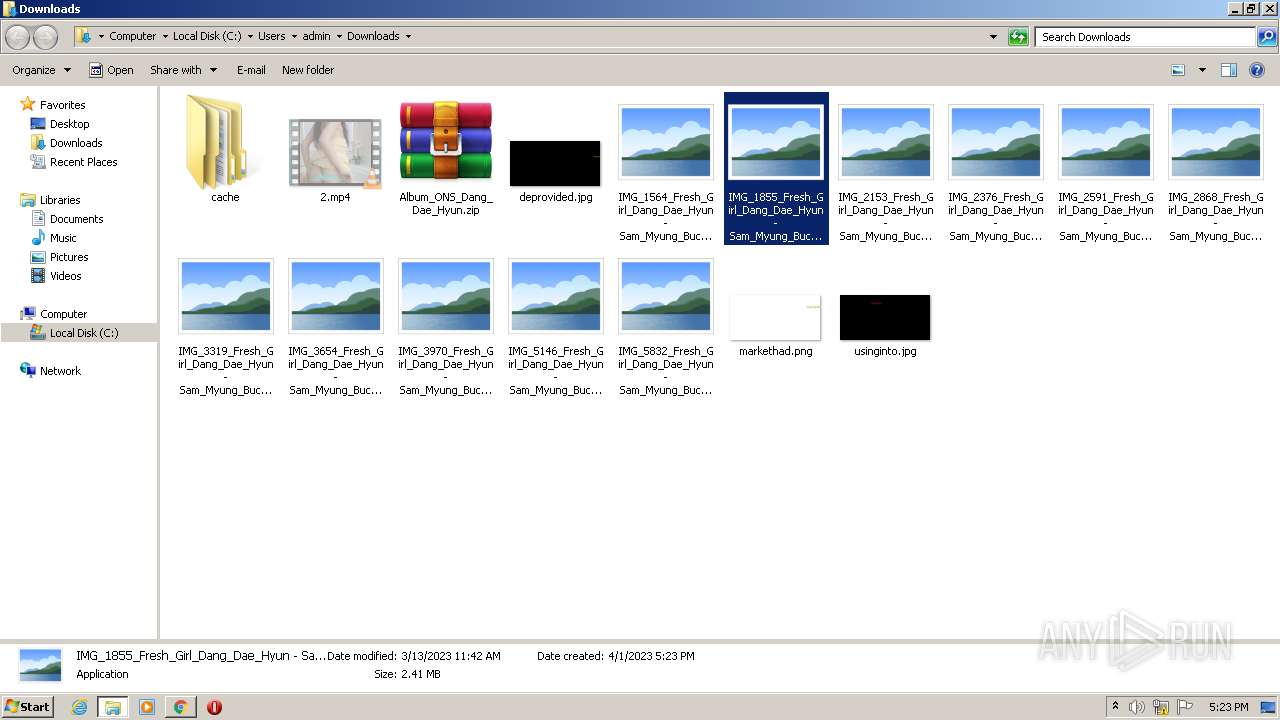
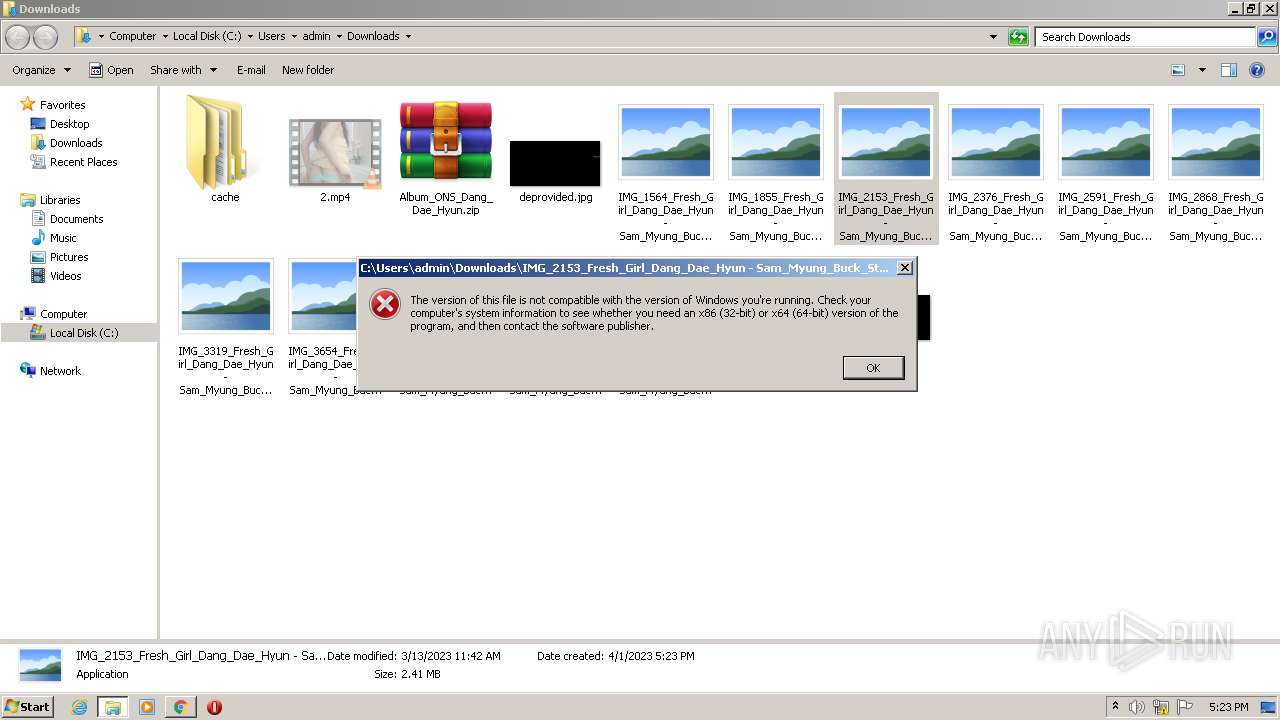
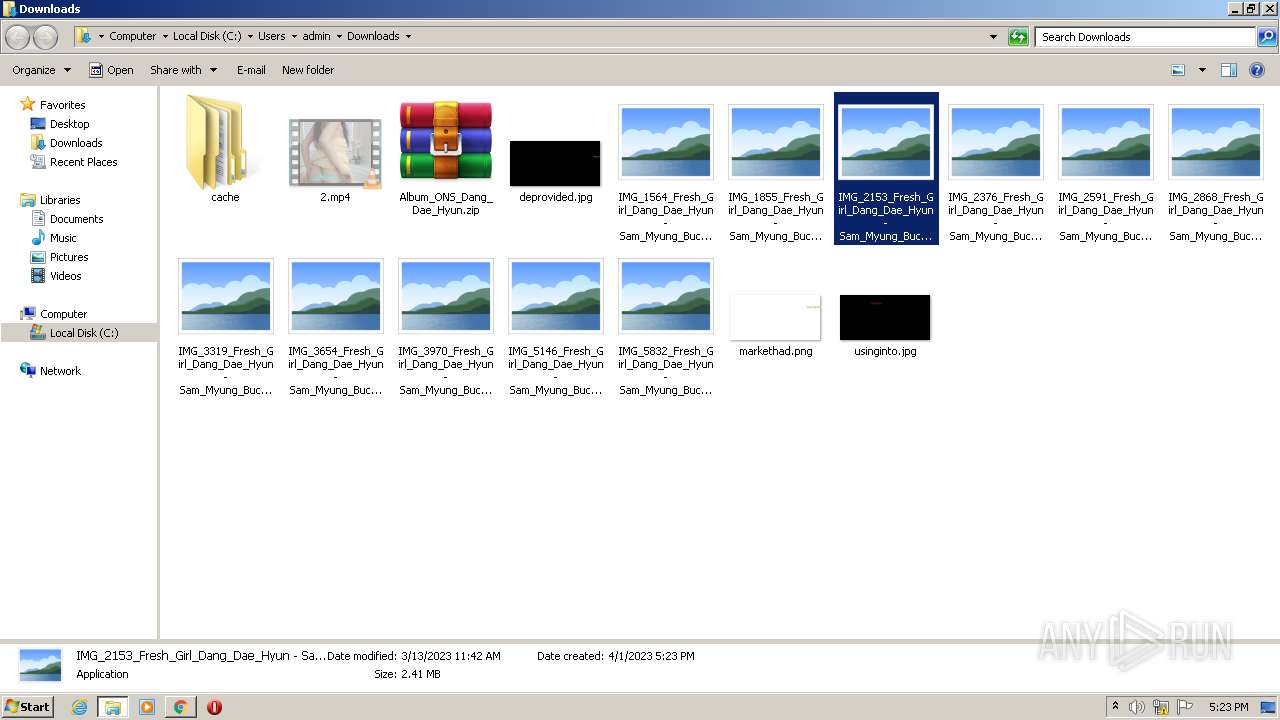
Manual execution by a user
- WinRAR.exe (PID: 752)
- pcwrun.exe (PID: 3904)
The process checks LSA protection
- SearchProtocolHost.exe (PID: 3104)
- sdiagnhost.exe (PID: 2800)
- msdt.exe (PID: 568)
- csc.exe (PID: 1852)
- cvtres.exe (PID: 3580)
- csc.exe (PID: 3912)
- cvtres.exe (PID: 1660)
- csc.exe (PID: 3480)
- cvtres.exe (PID: 3984)
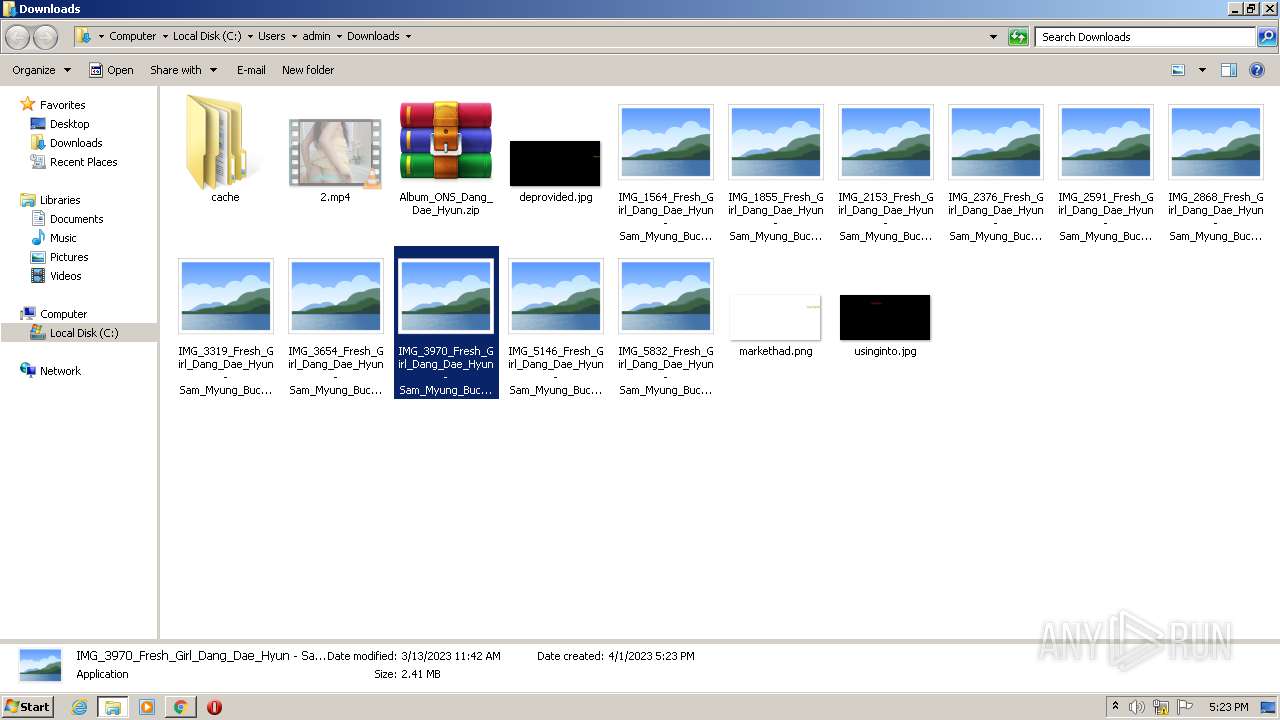
Executable content was dropped or overwritten
- WinRAR.exe (PID: 752)
Application launched itself
- chrome.exe (PID: 1488)
Reads the machine GUID from the registry
- csc.exe (PID: 1852)
- cvtres.exe (PID: 3580)
- csc.exe (PID: 3480)
- cvtres.exe (PID: 1660)
- cvtres.exe (PID: 3984)
- csc.exe (PID: 3912)
Checks supported languages
- csc.exe (PID: 1852)
- cvtres.exe (PID: 3580)
- csc.exe (PID: 3912)
- cvtres.exe (PID: 1660)
- csc.exe (PID: 3480)
- cvtres.exe (PID: 3984)
Creates files or folders in the user directory
- msdt.exe (PID: 568)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
71
Monitored processes
30
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 568 | C:\Windows\System32\msdt.exe -path C:\Windows\diagnostics\index\PCWDiagnostic.xml -af C:\Users\admin\AppData\Local\Temp\PCW1CD7.xml /skip TRUE | C:\Windows\System32\msdt.exe | pcwrun.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
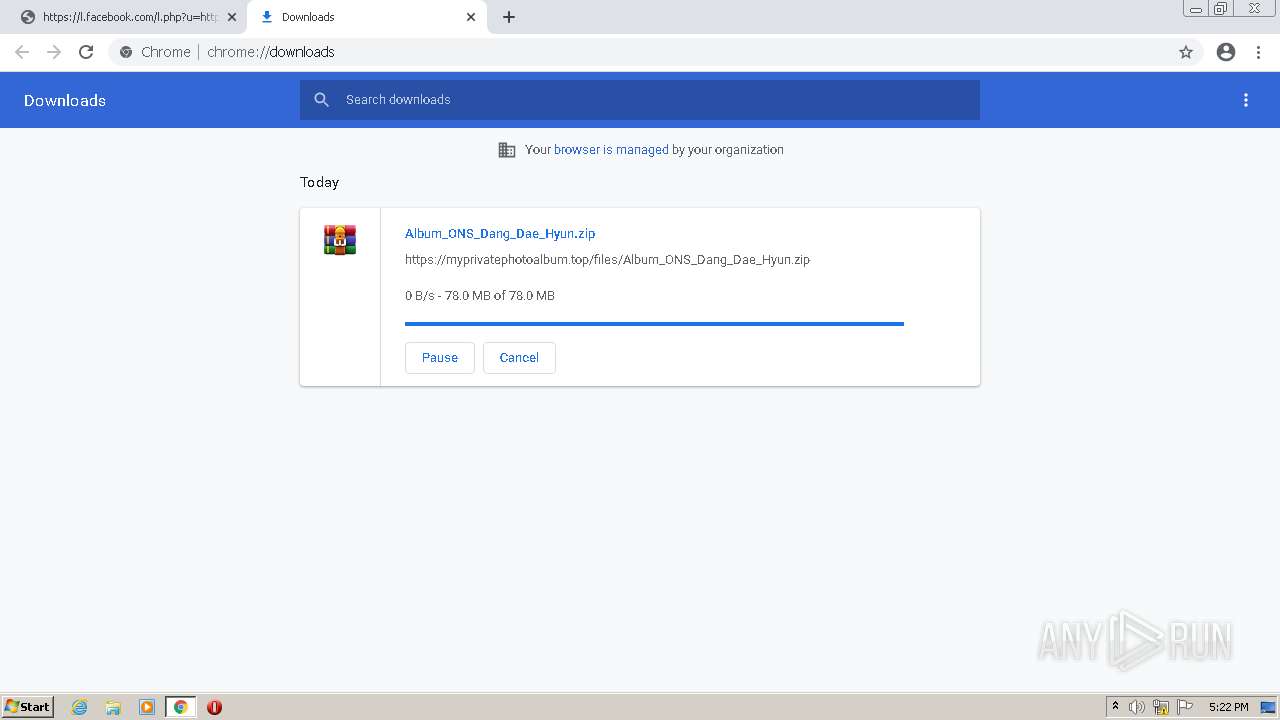
| 752 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\Album_ONS_Dang_Dae_Hyun.zip" C:\Users\admin\Downloads\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,3325507531616185300,16402543278735259835,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2100 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://l.facebook.com/l.php?u=https%3A%2F%2Fprivate-photoalbum.top%2Falb%2F%3Ft%3Dvip2%26fbclid%3DIwAR3zJq6ewc9W1JeMg0qbLdkU2vrpuEh66hczIsa7-g5Utw7Y3GlBTCBiM5E&h=AT0vvf5HGH2czwRIswDcneyCzY0TD8j3BpIBq_NdYYXrlmyE5m-56KQYrANsSmRCoiwtI-Cp1vEVyQzuOpm7NcC6G2N7FScjCafyKY9WvFsffoCqo1ypQly6AgK4g8YXtO_2u-_mwW0I5FRyI_s&__tn__=H-R&c[0]=AT1z_XPiAz6I0vsCLmU4RLWEiPI39CfP8_jMNgrXmmvTiX9k9jm9AdKTSYEaZEAYF91wcY-gyQllwJUHGbEFNy0ILLTOAHh6LwMDMJiTr4mqQGm2W8dwo9hgLIy2I7mU_tJA83qnJ0qBiBJr1oM8HPeblXzj9r3TMI03D9sxdzy-lgo8RpgSXjNoCFPS5L9Xdz_7MKmIBr1kzwEisXuUF1BZvQ" | C:\Program Files\Google\Chrome\Application\chrome.exe | — | explorer.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1036,3325507531616185300,16402543278735259835,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1728 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1036,3325507531616185300,16402543278735259835,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1056 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1660 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES26CB.tmp" "c:\Users\admin\AppData\Local\Temp\CSC26CA.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.5003 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 1852 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\ekqekpbg.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 2336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,3325507531616185300,16402543278735259835,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2004 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6f3dd988,0x6f3dd998,0x6f3dd9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
40 854
Read events
40 540
Write events
304
Delete events
10
Modification events
| (PID) Process: | (1488) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1488) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1488) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1488) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1488) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1488) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1488) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1488) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (1488) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
| (PID) Process: | (1488) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
Executable files
86
Suspicious files
84
Text files
210
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-642859A2-5D0.pma | — | |
MD5:— | SHA256:— | |||
| 1488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f6ee86a9-ca14-4d6c-8030-5de09df82712.tmp | text | |
MD5:— | SHA256:— | |||
| 2340 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 1488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 1488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 1488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF250173.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 1488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 1488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF2503f3.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
| 1488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 1488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old~RF250be3.TMP | text | |
MD5:D097F8EB2230B3F32C41C5D75790508C | SHA256:ADDF87D20CD455CFB4AACB6B76719629C0277A4CF70B496343047BB73ABBAEF5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
14
DNS requests
12
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
860 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | US | — | — | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | US | binary | 8.03 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | US | binary | 8.02 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | US | binary | 7.96 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | US | binary | 8.48 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | US | binary | 8.27 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | US | binary | 8.02 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | US | binary | 8.51 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | US | binary | 8.27 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | US | binary | 8.25 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3116 | chrome.exe | 157.240.20.36:443 | l.facebook.com | FACEBOOK | DE | whitelisted |
3116 | chrome.exe | 216.58.212.174:443 | clients2.google.com | GOOGLE | US | whitelisted |
3116 | chrome.exe | 142.250.184.205:443 | accounts.google.com | GOOGLE | US | whitelisted |
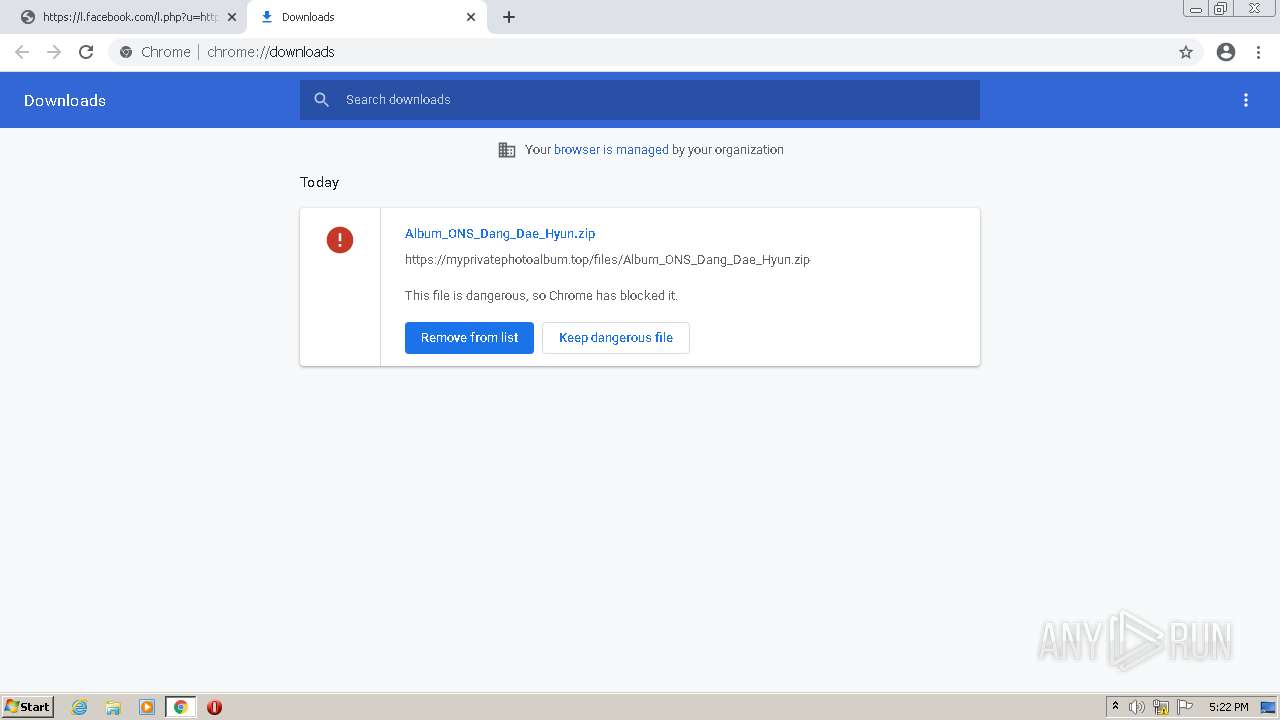
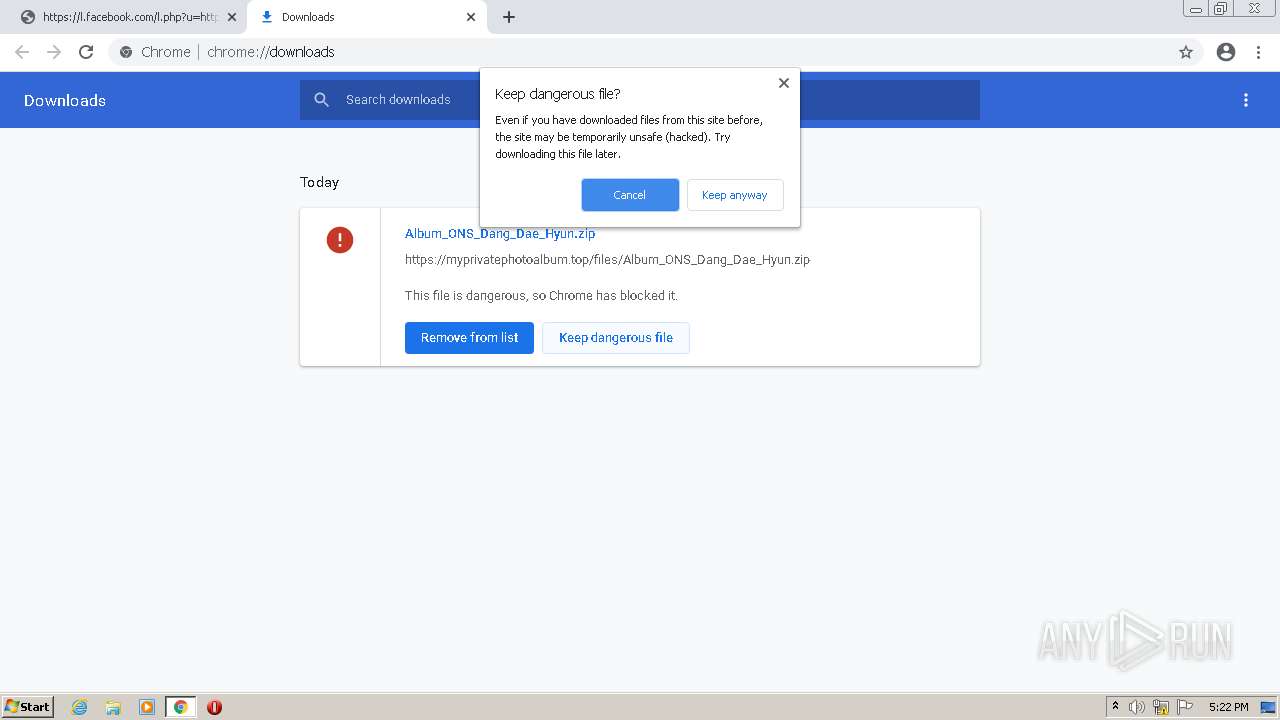
3116 | chrome.exe | 188.114.96.3:443 | myprivatephotoalbum.top | CLOUDFLARENET | NL | malicious |
3116 | chrome.exe | 142.250.185.97:443 | clients2.googleusercontent.com | GOOGLE | US | whitelisted |
3116 | chrome.exe | 142.250.184.206:443 | sb-ssl.google.com | GOOGLE | US | whitelisted |
— | — | 142.250.184.227:443 | update.googleapis.com | GOOGLE | US | whitelisted |
— | — | 142.250.185.238:443 | clients1.google.com | GOOGLE | US | whitelisted |
3116 | chrome.exe | 104.21.2.157:443 | private-photoalbum.top | CLOUDFLARENET | — | unknown |
3116 | chrome.exe | 142.250.184.195:443 | ssl.gstatic.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
l.facebook.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
private-photoalbum.top |
| unknown |
myprivatephotoalbum.top |
| malicious |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
Process | Message |
|---|---|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|